Abstract
Ciphertext-policy attribute-based encryption is a promising mechanism with fine-grained access control for cloud storage system. However, there is a long-lasting problem of key abuse that a user may share its decryption key and a semi-honest authority may illegally issue decryption keys for unauthorized users for profits. To address this problem, we propose an accountable ciphertext-policy attribute-based encryption scheme. In our construction, there are two authorities to issue keys for users, but they cannot decrypt any ciphertexts without collusion. A shared key can be effectively traced, and if the traced identity claims that it is innocent, an auditor can publicly audit who will be responsible for the shared key. Compared with existing accountable ciphertext-policy attribute-based encryption schemes, the proposed scheme is more practical from the two aspects: (1) a user can normally request for a decryption key along with a short signature, and no additional interaction between users and authorities is needed; and (2) the complexity of tracing a masked secret key is reduced to
Keywords
Introduction
Cloud storage is one of the most important services of cloud computing. More and more individuals (enterprises) are moving their private data to the cloud either for ease of sharing or for cost saving. While people enjoy the convenience of this new information technology (IT) architecture, their concerns about data security and privacy also arise.
Naturally, people want their sensitive data only accessible to authorized users. However, the cloud is semi-trusted, it cannot provide a fully trusted data access control service. To achieve access control on untrusted cloud servers, the data owner usually needs to encrypt the data before outsourcing, and only users holding decryption keys can recover the data. Traditional encryption schemes are no longer applicable to cloud systems, because there will be multiple encrypted copies of the same data for users with different keys and this will incur high computation overhead for the data owner and high storage overhead for the cloud.
Attribute-based Encryption (ABE), introduced by Sahai and Waters, 1 is a suitable solution for fine-grained access control in cloud storage systems. Generally, ABE can be classified into two main types: 2 (1) key-policy attribute-based encryption (KP-ABE): a user’s secret key is related to an access policy, while a ciphertext is labeled by a set of attributes; (2) ciphertext-policy attribute-based encryption (CP-ABE): a ciphertext is associated with an access policy, while the user’s decryption key is identified with a set of descriptive attributes.
In CP-ABE scheme, an authority manages the attribute universe and is responsible for issuing secret key for users according to attributes. The data owner defines an access policy and encrypts data under the access policy. A user can decrypt the ciphertexts if and only if the attributes related to its secret key satisfy the access policies in ciphertexts.
A motivating story
A data owner employs a cloud storage system and outsources its data after encrypting the data under access policy
However, in the CP-ABE system the secret key is related to attributes instead of identity, that is, users may have the same decryption privilege. In the above example, Alice and Ross have the same decryption privilege according to {B, C}. Then, a malicious user (e.g. Ross) is willing to share its secret key for profits without worrying about exposure because Alice has the same key. Thus, there should be a method to trace the owner of a shared secret key, that is, the CP-ABE system should support the property of traceability.
Furthermore, if the malicious user (e.g. Alice) is traced as the traitor (who shares her decryption key) but claims to be framed by the authority in the system, this case is possible in single authority CP-ABE system. There is only one authority that issues secret keys for all users, the authority can illegally generate arbitrary secret keys, and distribute it to an illegal user while this secret key may be associated with an honest user. For example, the authority generates a decryption key associated with Alice, and shares this key to Evil who is unauthorized. Then how to judge whether Alice is framed or not? If a user is traced to be malicious the CP-ABE system should provide accountability, that is, it is necessary to provide a method that enables an auditor to judge whether a traced user is innocent or not.
Related works
Cloud computing, such as computation model3,4 and application of blockchain 5 to cloud computing, is still an interesting and attractive research field. As to secure cloud storage, many ABE schemes6–15 aiming at better efficiency, security and expressiveness have been proposed.
As to ABE with white-box traceability which takes a well-formed decryption key as input, Li et al. 16 gave an accountable ABE supporting AND gate with wildcards access policy. However, it cannot achieve traceability as mentioned in Yu et al. 17 Liu et al. 18 proposed a traceable CP-ABE supporting any monotone access structures, Ning et al. 19 proposed a traceable CP-ABE scheme supporting large universe, a fully secure traceable CP-ABE scheme. 20
As to ABE with accountability, Ning et al. 21 proposed an accountable ABE supporting traceability and public auditing. The public auditing in scheme given by Ning et al. 21 is based on zero-knowledge proofs of knowledge (ZK-POK) of a random. However, if there is only one authority and there is not a public verifiable binding between the random and user’s identity, the authority still can generate an illegal secret key related to another random for an unauthorized user.
Yu et al. 17 proposed an traceable ABE supporting public verifiability which fails to support accountability owing to the fact that there is only one authority who knows secret keys of all users. Then, Yu et al. 22 proposed an accountable ABE based on two authorities, neither of whom can generate a valid secret key. However, in the scheme given by Yu et al., 22 the user needs two steps of interaction with the two authorities during the key generation phase. This is more complicated than traditional ABE schemes from the view of users. Furthermore, the malicious user can change the number of elements in secret keys before sharing them which will make the identity of the secret key more complicated to trace.
The concrete comparison of features with related works16–22 is shown in Table 1. According to Table 1, both the proposed traceable and undeniable ciphertext-policy attribute-based encryption (tuCP-ABE) scheme and the scheme by Yu et al.
22
can achieve accountability. However, the scheme by Yu et al.
22
needs an additional interaction with the two authorities during the key generation phase, and Table 2 shows that it needs to compute additional
Comparison of properties.

tuCP-ABE: traceable and undeniable ciphertext-policy attribute-based encryption.
Comparison of cost.
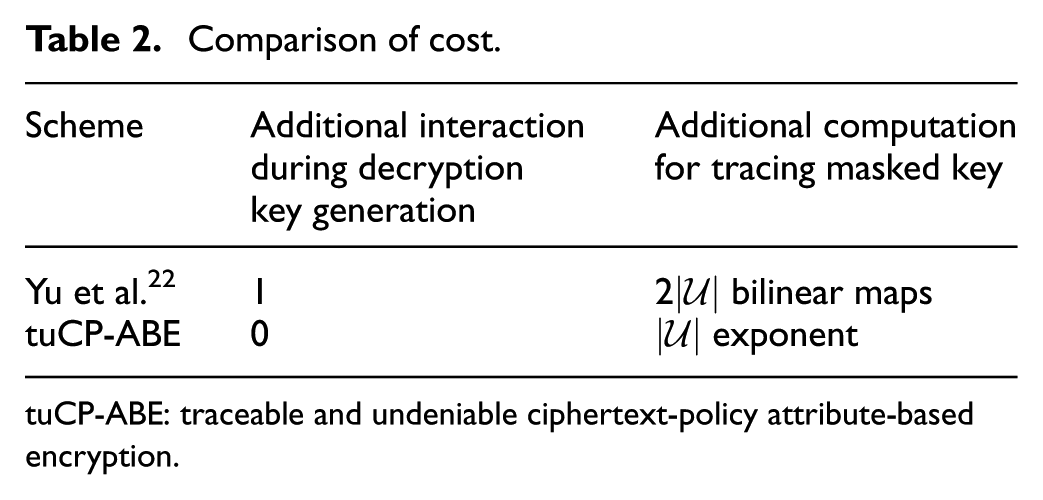
tuCP-ABE: traceable and undeniable ciphertext-policy attribute-based encryption.
Besides white-box traceability, there is another practical property called black-box traceability which takes a decryption device as input. The black-box device will hide the decryption key and the black-box trace algorithm should find the identity of decryption key that has been used in constructing the decryption device. Li et al.
10
proposed a black-box traceable ABE supporting AND gate with wildcards access policy. Liu et al.
23
proposed a black-box traceable CP-ABE system which supports any monotone access structures, and Liu et al.
24
gave a full secure black-box traceable CP-ABE system based on prime order groups, Ning et al.
25
proposed a black-box traceable CP-ABE scheme with shorter ciphertexts, and there are some researches on traceable CP-ABE in fog computing,26,27 and auditable
Our results
In this article, we investigate the key abuse problem and further propose a tuCP-ABE. To achieve traceability, the identity information of key owner is signed by the authority and inserted into the user’s secret key as a necessary part for successful decryption. To achieve accountability, two authorities are applied to avoid key escrow that neither of the two authorities knows the user’s secret key and a short signature of the user is used to achieve nonrepudiation. The main features of tuCP-ABE are as follows.
Practical key generation: In the decryption key generation algorithm of the scheme given by Yu et al.,
22
the authorities, central authority (CA) and outsourcing authority (OA) need to generate a one-time
Efficient traceability: If the user shares its secret key without a mask, the identity of a shared secret key in our tuCP-ABE can be easily traced with public verifiability because the identity is a part of shared key. Else, if the user shares a masked secret key, the CA will do
Accountability: The auditing in scheme given by Ning et al.
21
is based on
Public auditing: Note that the schemein Ning et al. 21 is privately auditable, only a fully trusted auditor can run the audit procedure because the auditor needs know the whole secret key of user. In the proposed tuCP-ABE, the user only needs to submit a part of the decryption key to the auditor. The auditor can publicly verify the validness of the submitted key, and the auditor cannot decrypt any ciphertexts using the received key.
Organization
Section “Background” introduces some preliminaries, including the bilinear map and related assumptions. Section “Accountable CP-ABE” gives the formal definition of the tuCP-ABE and its security model. The main construction of tuCP-ABE is given in section “The concrete tuCP-ABE scheme.” Section “Security and performance analysis” presents the security proof and the performance analysis. Finally, section “Conclusion” presents a brief conclusion and foresees our future work.
Background
Definition 1
Bilinear maps
Definition 2
Discrete logarithm problem
Inputting
Assumption 1
DL assumption
The advantage of an algorithm
Definition 3
Decisional q parallel-BDHE problem
Inputting
Assumption 2
Decisional
parallel-BDHE assumption
The advantage of an algorithm
Accountable CP-ABE
Definition
The traceable and undeniable CP-ABE, denoted by tuCP-ABE in brief, consists of 10 polynomial-time algorithms.
IND-s-CPA security
There are two authorities CA and OA. We assume that CA and OA are curious-but-honest, and CA is not allowed to collude with OA. The ciphertext indistinguishability under adaptive chosen plaintext attack in the selective model (IND-s-CPA) of accountable CP-ABE is described by following security game between a challenger
Init:
Setup:
Phase 1:
Challenge:
Phase 2:
Guess: At last,
Accountability
The accountability in tuCP-ABE scheme is based on two properties: the white-box traceability and the non-repudiation of user’s signature.
White-box traceability
The identity information is related to a decryption key by the signature of CA and OA. Thus, the white-box traceability game is similar to the unforgeability of signature. It can be described by following game between a challenger
Setup:
Query phase:
Forge: At last,
Non-repudiation of user
The non-repudiation of user is based on the unforgeability of the user’s signature, and we assume that at one period, a user has a unique random that relates to decryption key. The non-repudiation of user is defined by the following game between an adversary
Setup:
Query phase:
Forge: At last,
The concrete tuCP-ABE scheme
- - CA verifies the correctness of


Then, CA sends
- OA randomly chooses

OA stores
Let
- Chooses a random vector
- Computes
- For


If
If
Note that a malicious user may mask the secret key as
Suppose a shared key
Security and performance analysis
IND-CPA security
The confidentiality (IND-CPA security) of the proposed scheme can be presented directly based on the (decision)
Lemma 1
If the (decision)
Proof
The details of proof are referred to Waters. 8
Lemma 2
If CA and OA are regarded as one authority, then the confidentiality of the proposed tuCP-ABE scheme can be reduced to that of WCP-ABE scheme.
Proof
If CA and OA are regarded as one authority, then CA (for example) runs the
CA verifies the correctness of
If there is an adversary
Setup:
Phase 1:
Challenge:
Phase 2: Same with Phase 1.
Guess:
From the above simulation, the distributions of the public parameter, decryption keys and challenge ciphertext are indistinguishable from the real scheme (assuming CA and OA are regarded as one authority), we have
Lemma 3
A curious-but-honest CA (without collusion with OA and a valid key from user) cannot decrypt any ciphertext.
Proof
Here we give a heuristic analysis. A curious-but-honest CA needs to get
However, it is related to DL to compute
Lemma 4
A curious-but-honest OA (without collusion with CA and a valid key from user) cannot decrypt any ciphertext.
Proof
If OA is curious-but-honest, CA needs to recover
Theorem 1
If the (decision)
Proof
It follows from Lemma 1, Lemma 2, Lemma 3, and Lemma 4.
Lemma 5
If the
Proof
Actually, the
Theorem 2
If the
Proof
On one hand, from Lemma 5, the tuCP-ABE scheme is white-box traceability. On the other hand, the one-time random
Experimental results
Obviously, to achieve traceability and accountability the user secret key generation algorithm of the proposed tuCP-ABE scheme is more complicated than the pure CP-ABE scheme proposed by Waters. 8 However, it is more practical than the key generation algorithm of scheme by Yu et al. 22 Similar to scheme by Waters, 8 the time cost of encrypt algorithm is linear to the number of attributes evolved in an access structure, and the time cost of decrypt algorithm is linear to the number of attributes related to decryption key.
To evaluate the performance of the proposed tuCP-ABE scheme, we implement the tuCP-ABE scheme in java with the JPBC library and run the experiments on a Win 10 system equipped with a dual-core Intel CPU and 8 GB RAM. In an ABE system, the computational cost depends on the complexity of access policy. To illustrate this, we simulate the worst case that the access policy in the form of (
Figure 1(a) and (b) illustrate the time cost for encrypt, decrypt phases of our tuCP-ABE and the CP-ABE proposed by Waters. 8 As shown in Figure 1, the time consumption for encrypt and decrypt of the proposed tuCP-ABE scheme is comparable to the practical CP-ABE scheme proposed by Waters. 8

Time consumption for (a) encrypt and (b) decrypt.
Conclusion
In this article, we propose a CP-ABE scheme, called tuCP-ABE, which supports traceability and accountability. In the tuCP-ABE system, the identity related to a shared secret key can be traced, furthermore an auditor can publicly judge whether the traced identity is innocent or not. We also prove that the tuCP-ABE scheme is selectively secure in the standard model and give some experimental results.
Note that a user is willing to mask the decryption key before sharing. Although the complexity of tracing a masked secret key in our tuCP-ABE is reduced from
Footnotes
Handling Editor: Qingchen Zhang
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported in part by the National Natural Science Foundation of China (grant nos.: 61602512, 61632012, 61373154, 61371083, and 61672239), the Key Science and Technology Research Projects of Henan province (grant no.: 182102210575), the National Key Research and Development Program (grant nos.: 2016YFB0800101 and 2016YFB0800100), and the Innovative Research Groups of the National Natural Science Foundation of China (grant no.: 61521003).
