Abstract
Critical infrastructures are essential for national security, economy, and public safety. As an important part of security protection, response strategy making provides useful countermeasures to reduce the impacts of cyberattacks. However, there have been few researches in this domain that investigate the cyberattack propagation within a station and the incident spreading process in the critical infrastructure network simultaneously, let along analyzing the relationships between security strategy making for a station and scheduling strategy for the critical infrastructure network. To tackle this problem, a hierarchical colored Petri net–based cyberattacks response strategy making approach for critical infrastructures is presented. In this approach, the relationships among cyberattacks, security measures, devices, functions, and station capacity are analyzed and described in a hierarchical way, and the system loss is calculated with the input of abnormal station capacities. Then, based on the above model, the security strategy making for a station and the scheduling strategy making for the critical infrastructure network are investigated in depth. Finally, the effectiveness of the proposed approach is demonstrated on a simulated water supply system.
Keywords
Introduction
Critical infrastructures (CIs) are viewed as the foundation of crucial economic and social function, whose secure and reliable operation provides essential, continual good, or service to meet the country demand. 1 Nowadays, the wide adoption of developed information and communication technologies (ICT) improves the CIs operation efficiency, but it also makes CIs more vulnerable to cyber threats. In 2003, the worm virus “Slammer” invaded into the “Davies–Besse” nuclear plant and disabled the safety monitoring system in Ohio, USA. 2 Several relevant departments believed the blackout accident that occurred in northeast America and Canada in 2009 was caused by foreign cyberattacks. 3 In 2015, hackers attacked the Ukrainian grid and caused large-scale grid blackout. 4 Therefore, cybersecurity protection for CIs is important and essential.
CIs require high availability, which means the unexpected shutdown of these systems is not allowed. 5 Thus, detecting the cyberattacks and responding timely, which can improve the intrusion tolerance ability of CIs on runtime, are of significance. 6 Specifically, once the cyberattacks are detected by intrusion detection system (IDS), an appropriate response strategy should be made and executed to prevent the cyberattacks propagation. In addition, the cyberattack can propagate from cyber space to physical space, and the incidents due to cyberattacks may propagate in CIs network with the interdependence among stations. 7 Thus, an appropriate response strategy can prevent the propagation process and mitigate the impacts of cyberattacks.
Many researches on response strategy making have been done in the past decades. Yan et al. 8 proposed a response strategy based on the phasor measurement unit (PMU) attack graph which analyzed the attack paths in smart grid. Qin et al. 9 established a multi-model based on Bayesian Network for dynamic decision-making in industrial control systems (ICSs). Zonouz and Haghani 10 analyzed the grid situation and sorted the candidate incidents, which provided valuable information to security strategy makers. Wang et al. 11 defined the condition risk and the cost in smart grid and provided the decision-making approach with these definitions. Yan and Haimes 12 calculated the protection strategy cost–benefit in each subsystem and used linear programming model to obtain the optimal system strategy. Li et al. 13 provided a multi-objective optimization-based decision-making approach which considered the security benefit, system benefit, and state benefit in ICSs. These approaches focus on the attack propagation or the attacker–defender game process, contributing to CIs attack response making. But there exist several special factors in CIs cybersecurity protection, for example, attacks to CIs cannot only propagate from cyber space to physical space, but can also spread from station to stations through the CI network. In addition, security strategy making for the station and scheduling strategy making for CIs need to be cooperated with each other. Therefore, the existing works cannot be applied to CIs protection directly due to the neglect of the characteristics mentioned above.
Motivated by the above analysis, a hierarchical colored Petri net (HCPN)–based cyberattacks response strategy making approach for CIs is proposed in this article. In this approach, an HCPN modeling method which decouples a complex system into different layers and describes the relationship among these layers by colored Petri is proposed. It can be used to model the operation of a CI in a graphic way. Based on this method, the cyber-physical interaction within a station and material dependence among stations are modeled, which are used to analyze the consequences due to cyberattacks and response strategy. Also, a response strategy making approach is introduced to analyze the security strategy making for station and scheduling strategy making for system and then generates the optimize response strategy based on the above two types of strategies.
The rest of this article is organized as follows: section “Background and preliminary” discusses the characteristic of the cyberattacks response in CIs and puts forward the architecture of the proposed approach. Section “System modeling with HCPN” gives the definition and description of HCPN and then uses HCPN to model the attack propagation in CIs. The generation of the attack response is analyzed in section “Optimal response strategy making.” Section “Simulation and result analysis” verifies the effectiveness of proposed approach, and the conclusions and remarks are provided in section “Conclusion.”
Background and preliminary
Analysis of response strategy making in CIs
As a typical system-of-systems, 14 a CI usually consists of a control center and several types of stations, such as generation, transmission, customer. The characteristics of CIs are described as follows: 15 (1) each station is independent and useful in its own right, which can be divided into a cyber space and a physical space; (2) all stations are distributed geographically and form a complex network; (3) the control center manages all stations cooperatively to achieve an intended purpose.
The attackers generally acquire the following goals step by step: (1) compromising the station management authority by launching cyberattacks, 16 (2) reducing the station capacity using the compromised authority, (3) propagating the station incident in the CI network due to interdependences, 17 and (4) causing negative impact on society.18,19 On the contrary, the CI defenders need to perform the following operations: (1) making security strategy to prevent the authority compromise and capacity reduction within the station, (2) making scheduling strategy to prevent the incident propagating in the CI network, and (3) making policy to mitigate the negative impact on society. According to the above discussion, the station operation and CI states are changed with attacks propagating. Hence, an appropriate model for describing the changing process is important for cyberattacks response.
Demand analysis of system modeling
A Petri net (PN) is a graphical and mathematic modeling tool to describe the structure and behaviors of systems in a visual means. Specifically, the places with its own token can represent the properties of system components, and the transition between different places describes the dynamic process of the component states changing. These characteristics make PNs suitable for modeling the system operation process, such as ICS, telecommunication, and transportation.20,21
PN also contributes to response strategy making for CIs, the places and transitions in PN describe the behaviors of the attackers in IT system, 22 and then the defenders can prevent the propagating process by making appropriate security strategy. 23 However, the station capacity, which is changed with the attack propagation, is multi-variable and it cannot be described by the token property in PN. In addition, a station is a complex system that is decoupled into different types of objects, such as device, function, goal, which makes it difficult for PN to describe the interaction among these objects. To solve this problem, colored Petri net (CPN) 24 is combined with “hierarchical” knowledge in ontology to describe the attack behavior, defender behavior, device states, function states, and station capacity, which helps to analyze the incident spreading in the CI network and response strategy making for CIs.
Architecture of response strategy making approach
The architecture of response strategy making approach is shown in Figure 1, where the inputs are the attack evidences and the current system states, and the output is the optimal response strategy for the stations which has suffered cyberattacks.

Architecture of cyberattack response approach for CIs.
The approach consists of three main steps: (1) generating the candidate response strategies for the station which has suffered cyberattacks, then obtaining each strategy properties, such as theirs benefit and mapped station capacities; (2) making the optimal scheduling strategy for the CI, which uses the candidate security strategies of the stations and then distributes the control tasks to all stations; (3) selecting the optimal security strategy for the stations, which considers both the control task and the candidate response strategies. Note that the cyberattacks response strategy for CIs is constructed by the appropriate strategy for each station.
System modeling with HCPN
Description of HCPN
HCPN adopts the “Hierarchical” knowledge 25 to decouple a complex system into several related objects, such as goals, functions, and devices and then utilizes CPN to describe the state changing of each object and the relationships among them. As shown in Figure 2, each object can be viewed as a “part of” another object situated at a higher level, and the states changing of this object contribute to the property of higher object; on this basis, the above objects characteristics are modeled by CPN. The definition and description of these objects are introduced in the following.
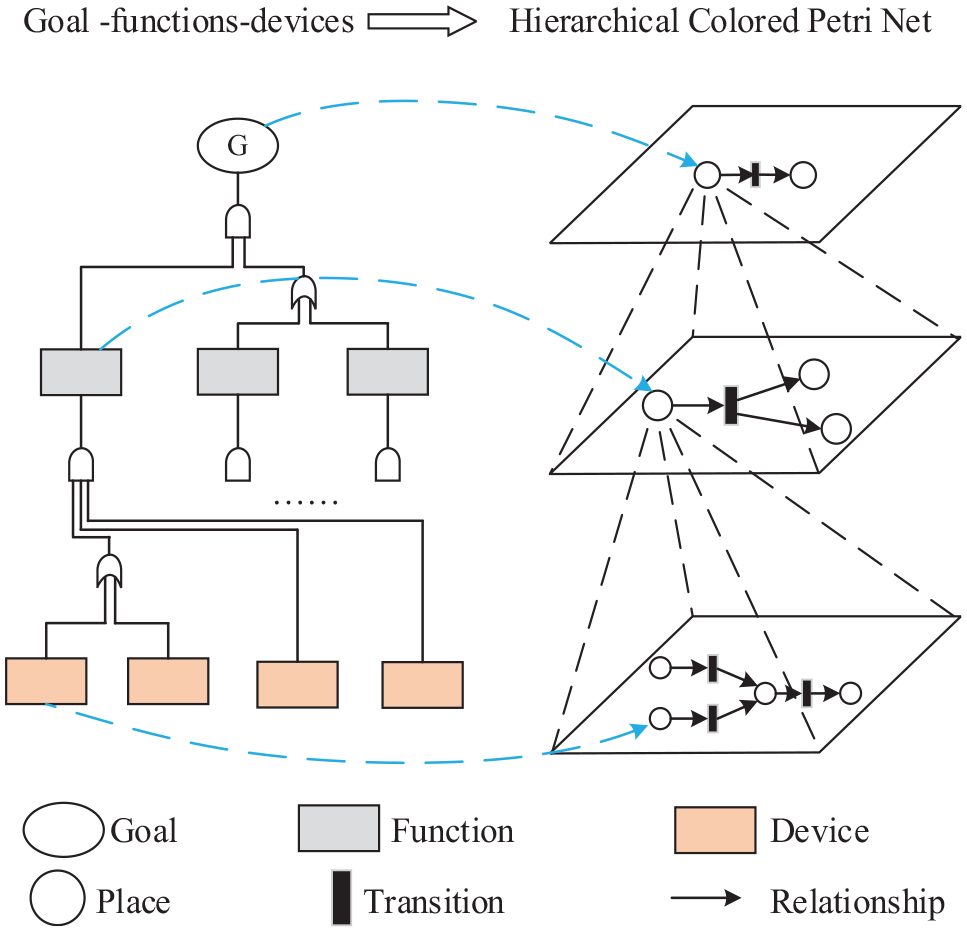
HCPN derived from a “goal–function–device” framework.
“Goal” represents the purpose of system, that is, what the operators want the system to reach. “Function” is a role played in the achievement of a goal, which is realized by related devices. “Device” denotes the component that constructs the system.
26
A five-tuple
Places set
Color set
Transition set
where
Input
Output
In general,
Modeling cyberattacks propagation within a station
As mentioned in section “Background and preliminary,” the cyberattacks to a station can propagate from cyber space to physical space, whose goal is to reduce the station capacity. In order to describe the process, HCPN is used to build the cyberattacks propagation model. Referring to the “goal–function–device” framework, a station can be decoupled into many types of objects, as shown in Table 1. In addition, a type of object called “behavior” which indicates the attacks and security measures is added into this table.
“Goal–function–device–behavior” for station.

HMI: human–machine interface; PLC: programmable logic controller.
Based on Table 1, cyberattacks propagation within a station can be modeled by an HCPN
where the place set
Description of places properties in HCPN.

HCPN: hierarchical colored Petri net.
The transition
Optimal response strategy making
Generation of candidate security strategies for stations
Cyberattacks are always launched to compromise the devices, disable the functions, and reduce the station capacity. In order to secure the operation safety, the security strategy is made to protect the devices, which maps to certain station capacity value. Considering the interaction between station and control center, candidate security strategies for the station are generated in this subsection.
A security strategy maps to certain station capacity, but certain station capacity may be caused by several security strategies. The candidate security strategies

where
A security strategy

where

Based on the above definition, the candidate security strategies

where
A security strategy


where the description of all the elements in equation (7) is listed as follows:
1. Benefit of executing security strategy

where
2. Cost of executing security strategy

where the value

In Algorithm 2, the population
The candidate security strategies for station are constructed by
Construction of optimal scheduling strategy for CIs
Assume that there exists

where
Because of the internal dependence and topology characteristic of CIs network,
28
the changing of a station capacity may impact on other stations. Hence, the scheduling strategy which consists of all station capacity setting can manage the CI network states.
29
In order to quantify the effect of scheduling strategy, we calculate the system loss when the scheduling strategy is executed. The system loss

where
If

where

In Algorithm 3, (1)
Algorithm 3 can generate the optimal scheduling strategy when a station has suffered cyberattacks, which can also be used to make optimal scheduling strategy when two or more stations have suffered cyberattacks simultaneously.
Making the optimal response strategy for CIs
The candidate security strategies set
Renewing the station capacities set
Selecting appropriate station capacity
Obtaining the appropriate security strategy for
Simulation and result analysis
Simulation platform and modeling process
Simulations are conducted on a simple water supply system which consists of six stations and a control center. As shown in Figure 3, the stations (

The structure of a water supply system.
The attackers scan the devices vulnerabilities in
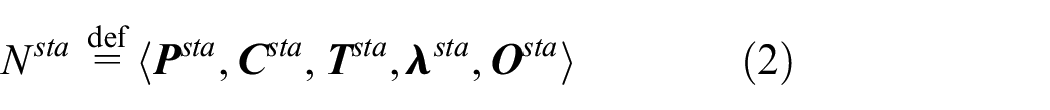
Goal–function–device in

PLC: programmable logic controller; PM: process management.
The relationships between these objects can be modeled by tree structure, and the modeling process is discussed in “ goal–function–devices” framework. 26 The tree structure is shown in Figure 4, where the attack and security measure are activated to change devices states.
Relationships between “goal–function–device–behavior.”
Each object in Table 3 can be mapped to a certain place, and the states of these objects can be represented by the colored token in places. Table 4 provides the definition of the colored token in each place, where
Description of colored token in

The places and their properties are provided in Table 4, and the transitions between these place can be obtained from Appendix 1; hence, attack propagation model for

The attack propagation model for
Result analysis
In order to verify the effectiveness of our approach, several simulations are carried out to analyze the security strategy making process when
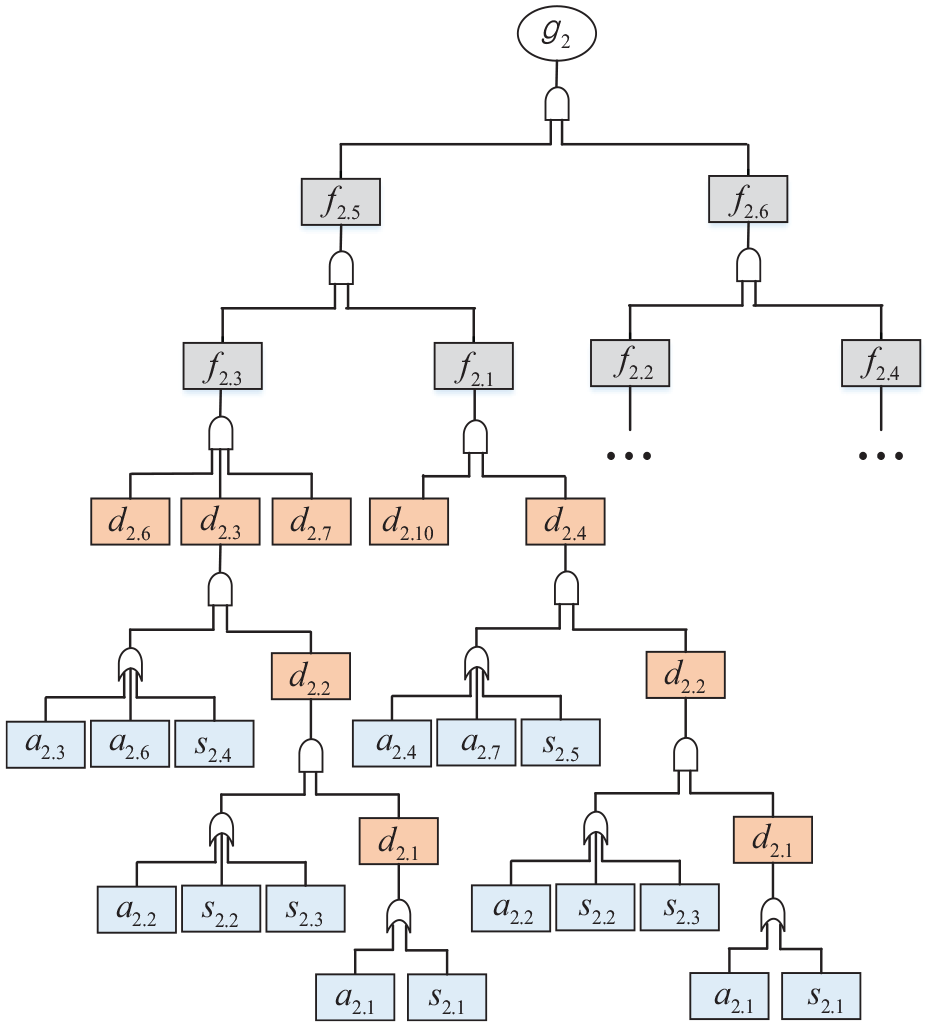
Properties of security measures.
As discussed in section “System modeling with HCPN,” the response strategies making process is divided into three sub-processes. The first is generating the candidate strategies for the station which has suffered cyberattacks. Table 6 shows the attack evidence
Description of attack evidences.

PLC: programmable logic controller; PM: process management.
Then the response strategy for

Candidate security strategy for

Table 7 provides the candidate security strategies for
Optimal scheduling strategies.

The optimal response strategy making for cyberattacks is depended on the cost constraint of
The optimal strategy for system.

Figure 6 shows the water output of

Outputs of
Figure 7 shows the net benefit of
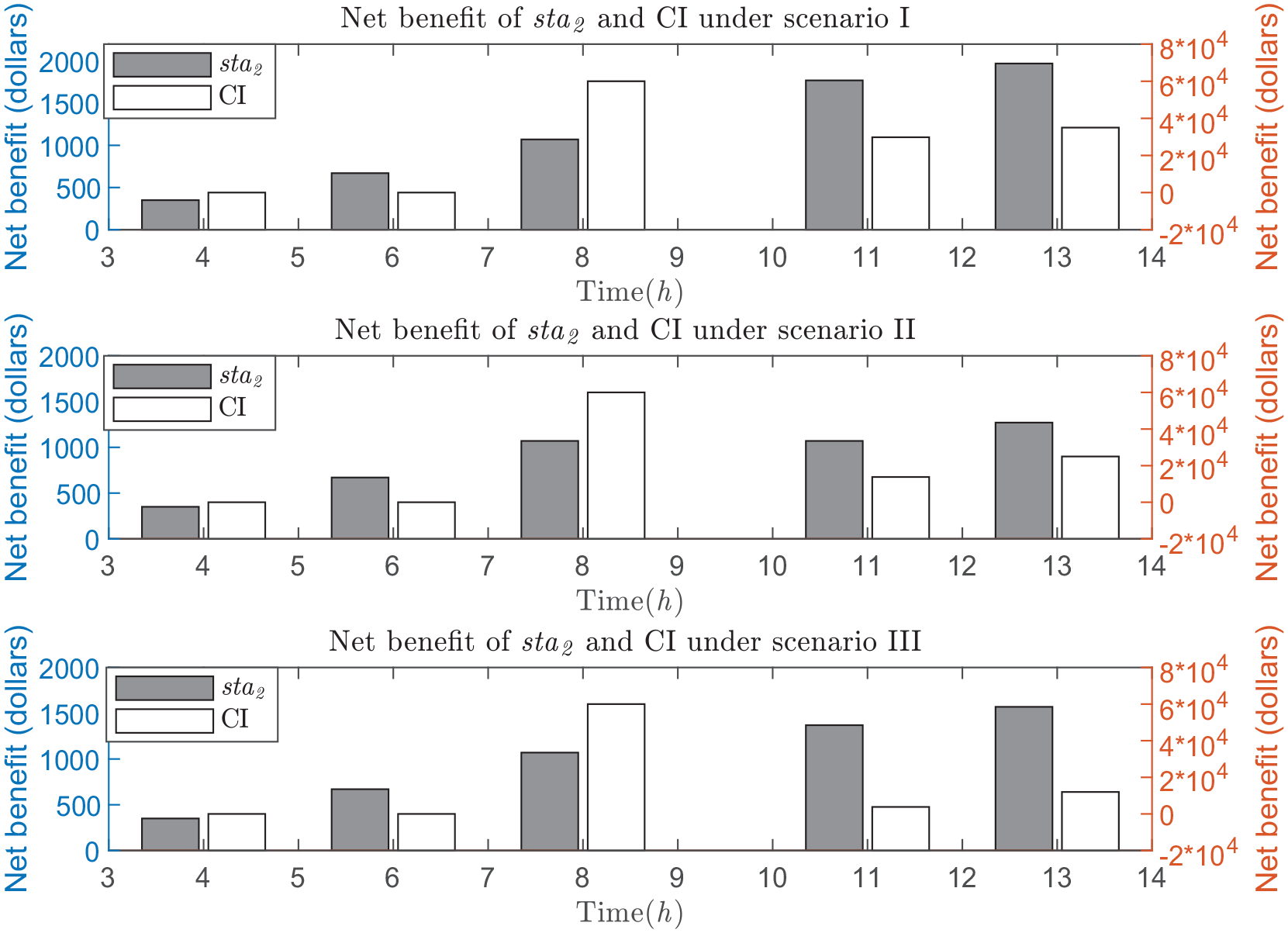
Net benefit of
In order to evaluate the real-time performance of our approach, the simulation for response strategy making at hour 13 is performed for 1000 times, where the simulation ran on a computer with Inter Core i3 at 3.90 GHz and 8 GB RAM. The execution time distribution of the simulation is shown in Figure 8. The execution time of our approach consists of three main parts: the time spent on Algorithm 2, Algorithm 3, and the system loss calculation. The complexity of Algorithm 2 is equal to

Execution time of response strategy making at hour 13.
The above simulations verify that our approach has the ability to making response strategy for CIs. In addition, this approach employs different perspectives, which makes it difficult to compare our approach with others. Therefore, we compare the approaches mentioned in section “Introduction” with ours from different aspects. Table 10 provides the approaches comparison.
Comparison of the response making approaches.

Conclusion
In this article, an HCPN-based cyberattacks response strategy making approach for CIs is proposed, which analyzes the relationships among cyberattacks, security measures, devices, functions, and station capacity in a graphical way and then investigates the interaction between response strategy making for station and the scheduling strategy making for CI network. The simulation verifies our approach can make an appropriate response strategy for cyberattacks in real time.
However, this approach needs to prepare the complete knowledge of all the cyberattacks and security measures before building the HCPN model and does not consider the probability attribute of the transition in HCPN. In our future work, the probabilities of attack paths in cyberattacks propagation are investigated, where the propagation process is analyzed with the input of incomplete knowledge of cyberattacks and systems.
Footnotes
Appendix 1
Two types of transitions in HCPN model are analyzed and obtained in this appendix.
In Figure 9, the “AND” and “OR” in the tree whose nodes are the objects can be described by the transitions in Petri net. Then, the detailed transitions are shown in Table 11.
Referring to the material flow mechanism, there exist a lemma about the structure of station physical space. If
Based on above contents, the transition between physical process and station goal can be calculated. A simple example is provided to explain the calculation process. As shown in Figure 10, the station consists of five material process
Where the token in
In Figure 10, the importance of function in serial structure and parallel structure is given by experts and is shown in Table 12.
With the above analysis, the importance of
Then it means the station capacity is changed from
Appendix 2
In order to analyze the relationship between stations capacities and system loss, several properties of station are listed in Table 13.
Then there exist several equations about the properties in Table 13
where
The
Then equation (19) can be described as follows
where the
Based on equation (21), equation (17) can be represented as follows
where
Therefore, the cyberattack on a station may cause the overload of other stations in CI network. Thus, we calculate the system loss based on the overloads. As shown in equation (24)
where
Handling Editor: Michele Amoretti
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the National Science Foundation of China (NSFC) under grant numbers 61433006, 61873103, and 61272204.

