Abstract
With the continuous and rapid development of cloud computing, it becomes more popular for users to outsource large-scale data files to cloud servers for storage and computation. However, data outsourcing brings convenience to users while it also causes certain security problems. The integrity of outsourced data needs to be periodically checked by users to protect their data. Also, the secure transfer of cloud data can avoid data losses to users. Aiming at solving these problems in the data outsourcing process, a provable data transfer scheme based on provable data possession and deletion is recently proposed by Xue et al. However, we found a security flaw in Xue et al.’s scheme. Concretely, the block tags can be forged in their scheme. In this article, we first give a brief review of Xue et al.’s scheme and then a detailed attack is shown. To remove the security flaw, an improved scheme is proposed. Furthermore, we replace the integrity checking protocol of their proposal with a more efficient protocol to improve the efficiency of data integrity auditing.
Introduction
Cloud computing, big data, and information security, as important means of information technology development, bear all aspects of social development today. Cloud computing has achieved blowout-like development since it was proposed in 2006 with its service mode and high performance in line with the needs of the times. It can be foreseen that in the next decade or more, cloud computing will be jointly moved as the core force of information technology and industry. Mobile Internet, Internet of things, artificial intelligence, and other technologies drive the information transformation of traditional industries, and promote the society to enter a more convenient and secure era. 1 Nowadays, the new normal of Internet is characterized by the exponential growth of business caused by decentralized users but instantaneous aggregation. Cloud computing solves the technical problem of flexible computing through distributed computing and distributed storage. With cloud computing coming out of the cloud and becoming a new Internet service accessible to everyone, the cloud computing industry has entered a large-scale commercial era.
The rapid development of cloud technology has greatly facilitated people’s lives. 2 People can use cloud to calculate and store efficiently and conveniently. The relationship between cloud and people’s daily life is more and more inseparable. More and more data need to be stored. Cloud disks with convenient storage and large capacity become the only choice for most people. However, the generation of massive data has brought great burden to users’ storage and computing. Therefore, designing a more simplified and efficient auditable cloud data transfer protocol can promote the application and development of cloud more effectively.
Cloud servers have emerged as the times require. They can provide secure, reliable, and efficient storage and computing services with flexible processing capabilities. Their management methods are simpler and more efficient than those of physical servers. Users only need to buy or rent storage and computing services from cloud servers and do not have to buy expensive hardware or software, which greatly reduces their own economic burden. 3 Data outsourcing brings convenience to users, but it also brings some trust problems. 4 The integrity and availability of data are challenged tremendously. 5 For the reason that users lose control of data after data outsourcing, data security auditing becomes particularly important.6,7
In real life, users need to periodically audit the outsourced data to protect their integrity. Using traditional methods, users need to download all the audited data, which brings huge communication cost and also causes huge storage burden to users locally. The idea to solve this problem is a provable data possession (PDP) protocol:8–13 users no longer need to download the audited data, instead they just need to send an integrity auditing request to the cloud. The cloud generates an integrity proof according to the request and returns the proof to the user. Users can complete the auditing task by verifying proofs. Many improved PDP protocols13,14 have been proposed to prove the integrity of outsourced data.
In addition, the services of different cloud storage providers are different, such as price, access speed, security, and reliability. Based on these different considerations, users may choose different cloud service providers to minimize costs and obtain high-quality services. Besides, different users may need to share data to complete a collaborative task. In fact, the secure transfer of data between private, public, and hybrid clouds can help enterprises to speed up cloud access, improve enterprise efficiency and productivity, reduce costs, and enable enterprises to enjoy the benefits of a multi-cloud environment without sacrificing performance. All these realistic requirements make the safe and effective transfer of outsourced data between two different cloud servers unavoidable. A secure transfer mechanism is needed urgently in this field. A brief description of the provable data transfer (PDT) protocol15,16 is as follows: the user sends a data transfer query to a cloud server, the cloud server executes the transfer query, and then, sends transferred data to the targeted cloud server. The targeted cloud server verifies the integrity of transferred data. If the validation passes, the transferred data will be stored locally and the message of successful data transfer will be informed to the user. Otherwise, the targeted cloud server refuses to store data and informs the user.
Besides, when outsourced data are transferred from one semi-trusted cloud to another semi-trusted cloud, users also need to check whether the cloud has deleted the complete transferred data. If the malicious cloud retains a copy of the transferred data, users’ privacy will be directly threatened. Therefore, the malicious cloud server may not delete the data as requested for some hidden economic benefits, the privacy-preserving of users will be challenged directly. 17 Behind the nude picture scandal is actually the information security. Stars had deleted their photos, but the malicious cloud retained a copy of the transferred data, which led to the occurrence of the event. So, how can we ensure that cloud servers have deleted the data securely and completely? The idea to solve this problem is a provable data deletion (PDD) protocol: 18 users send a deletion verification query to the cloud which is responsible for deleting data. If the cloud does not delete the data as required, the generated proof will not pass the verification of users. Xue et al. 19 combine these three protocols together for the first time and propose a new type of data tracking auditing scheme, which guarantees the security of outsourced data in the whole life cycle and fosters the development of secure cloud storage.
The bad thing is that there exists a security flaw in their scheme. Concretely, the corresponding tag of the tampered block
In this article, we learn from the idea of zero-knowledge proof (ZKP) and design an auditing scheme based on classical string alignment. ZKP was proposed by Goldwasser et al. 21 in the early 1980s. It means that the tester can convince the tester that an assertion is correct without providing any useful information to the tester. It is pointed out that with the application of block chain, ZKP develops rapidly.22,23 In that article, Yu et al. 24 introduced a privacy protection audit scheme based on ZKP. In his scheme, the cloud server can provide corresponding proof to make third-party auditor (TPA) believe that the data in the cloud server is complete, but it does not provide any information about data and signature.
Finally, with i7-6700hq CPU and 8GB RAM, we install Java Development Kit (JDK) and configure the related java virtual machine environment under Windows Operating System 10. The experiment is carried out in this setting following Chen et al.’s 20 work. From the experimental results, the delay of audit verification process and the additional communication cost is within the acceptable range of users. The results of audit and data transfer are in line with the expected objectives of the experiment, and the design meets the actual needs.
Organization
The rest of the article consists of the following parts. We give a review of their system model in section “Xue et al.’s system model,” and a brief description of their scheme is introduced in section “The construction of Xue et al.” In section “Our attack,” we demonstrate a detailed attack which shows that their scheme is insecure. In section “Our improved scheme I,” an improved scheme is given. The alternative auditing protocol and performance analysis are introduced in sections “Another alternative auditing scheme II” and “Performance analysis,” respectively. In section “Security analysis,” we give a security analysis of our new scheme. In the last part, we summarize the article.
Xue et al. ’s system model
The system model consists of the following four entities: Cloud A, Cloud B, users, and the TPA, as shown in Figure 1:
Cloud A or Cloud B: it provides data storage and computation services for users, and users can outsource their data to reduce their own burden.
User: there are many large-scale data files for them to store and compute.
TPA: it is believed by users and is in charge of verifying the outsourced data on behalf of users to reduce their burden further.
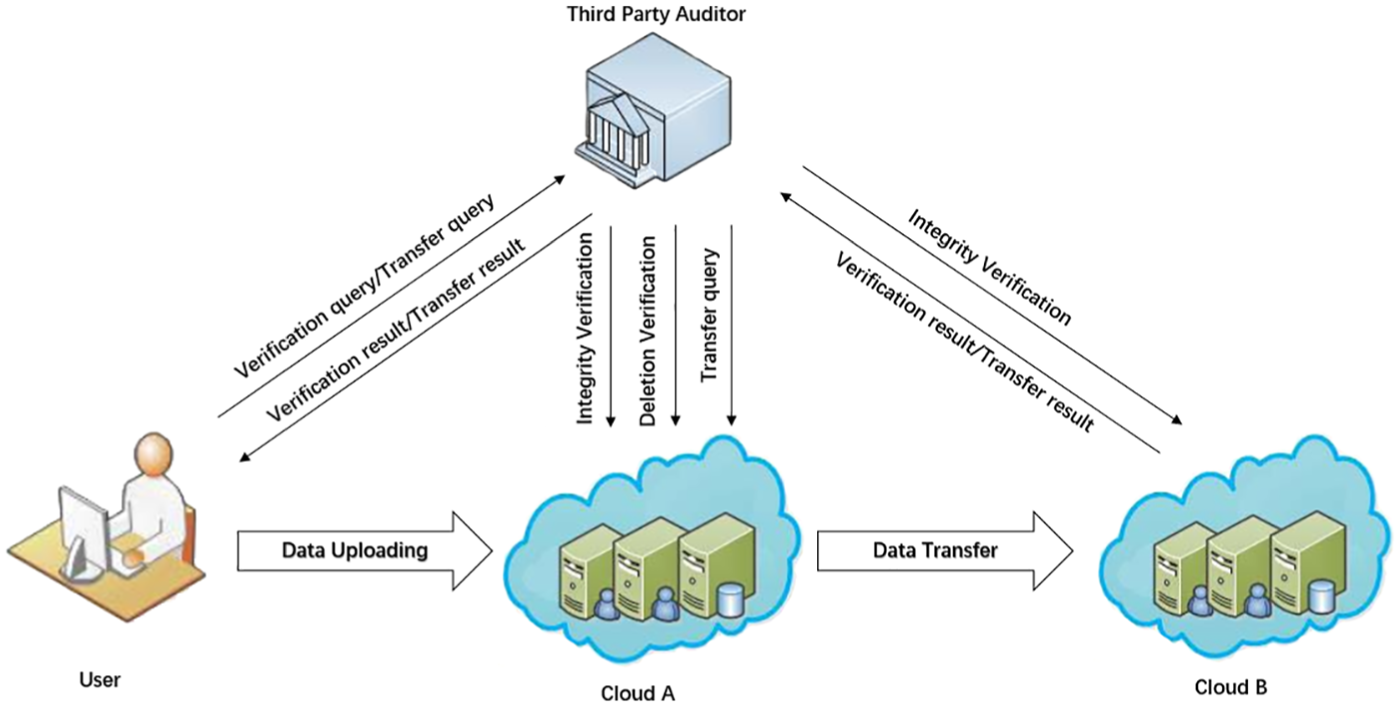
The system model.
Users can outsource their data to a cloud server for the services of storage and computation. Here, we assume that it is Cloud A. The user uploads his data files to Cloud A. When the user wants to change the storage location of outsourced data to Cloud B, Cloud B can send a transfer query to Cloud A. Then, Cloud A executes the transfer query, sends the transferred data to Cloud B, and deletes these data locally. To reduce the burden of users further, TPA is chosen to perform these tasks on behalf of them. Some tasks (such as data transfer, the verification of data integrity, and data deletion) can be executed by TPA. By verifying the returned result proof, TPA can complete the task authorized by the user.
The construction of Xue et al
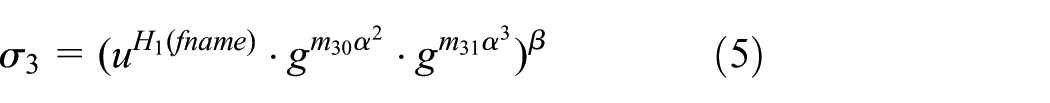
Based on the PDP thought with Ranked Merkle Hash Tree (RMHT) (Figure 2) of Yu et al. 16 and Yuan and Yu, 25 Xue et al. constructed a provable secure data tracking auditing scheme. The detailed structure is introduced as follows.

Rank-based Merkle hash tree.
Two multiplicative cyclic groups

KeyGen process.

Store process.
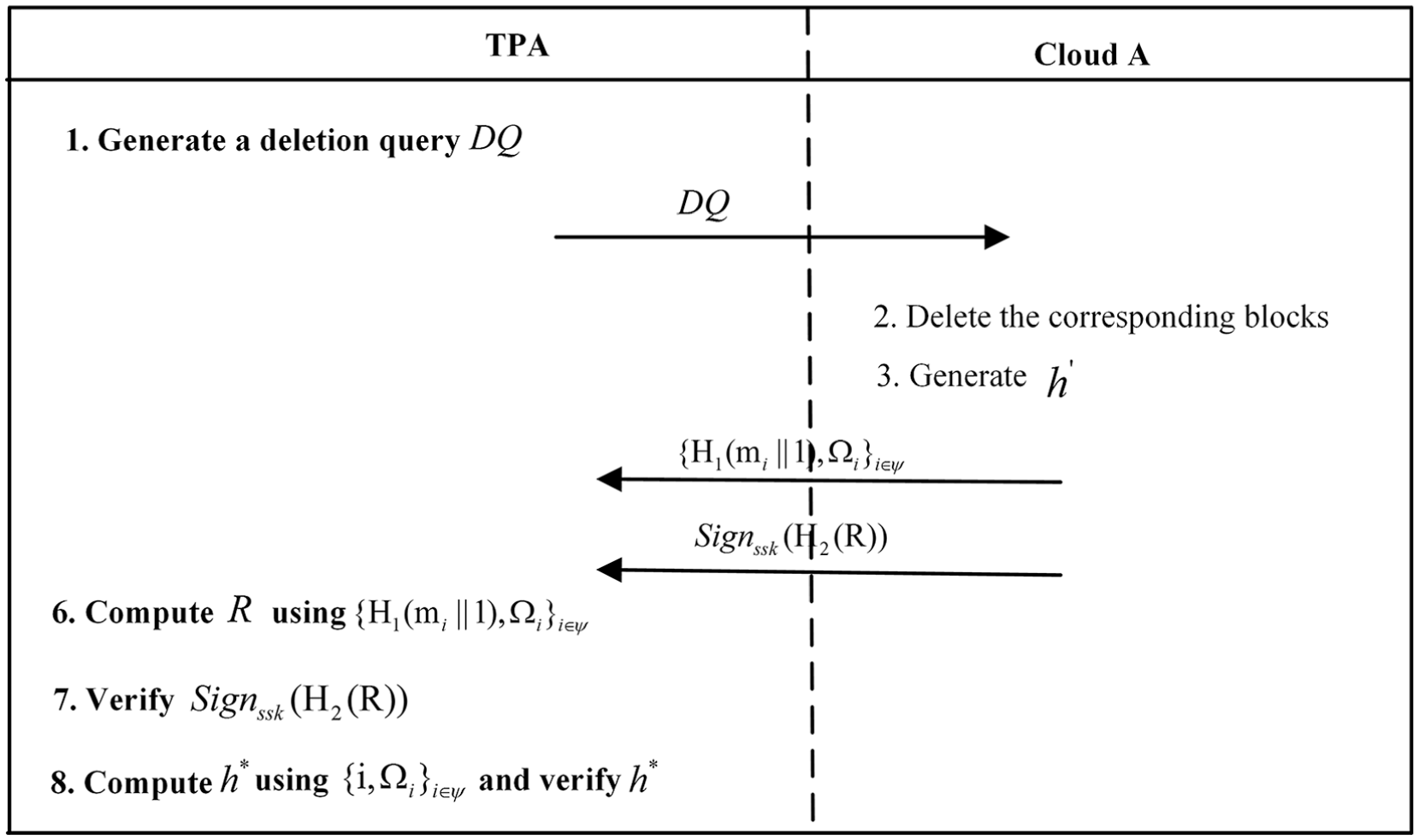
DeletCheck process.
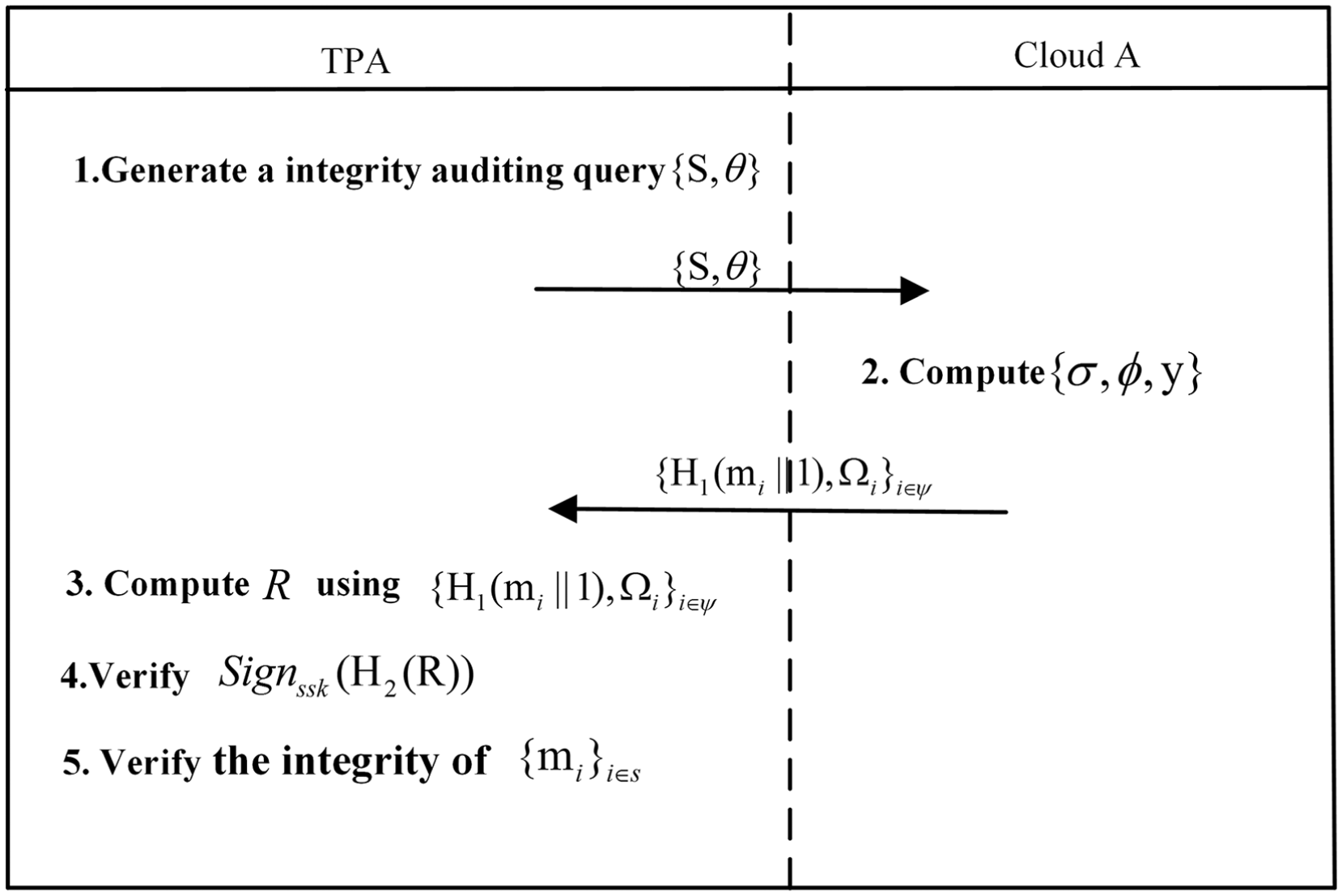
IntegCheck process.

Transfer process.
Our attack
For each file block

Let

After knowing some block tags equations as mentioned above,


Let



Because he knows the values of


Next, it computes


Let

thus

The value of
Our improved scheme I
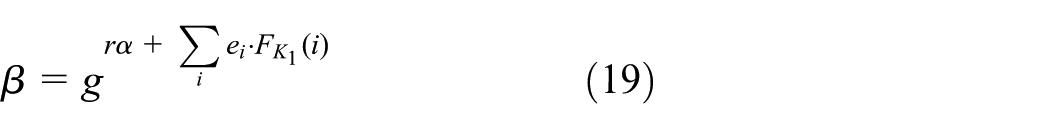
An improved scheme is introduced by us to make up for the security flaw of their scheme;
Given that

According to equation (15), it is difficult for the adversary to compute
Another alternative auditing scheme II
First, let’s review the classic string equality checking protocol:26,27 the purpose of this protocol is to determine whether the string
Alice chooses a string
Bob computes
This process is repeated by Alice and Bob 100 times. If
The theory of this protocol is as follows: if
Let Alice simulate the user and Bob simulate the cloud server, the following improvements of the above protocol are made to replace the integrity checking module of Xue et al.: 19
Two integers
The user chooses a
The workspace
A random string pool
TPA can use randomized auditing mode to audit the integrity of partial data stored on the cloud, the indexes


Then, the cloud returns the integrity proof to TPA, TPA can know the integrity of the audited data by verifying equation (18) or (19)

If the equation holds, return 1(true) to TPA; otherwise, return 0 (false). Finally, TPA tells the auditing result to the user (Figure 8).

The alternative auditing scheme (protocol) II.
Performance analysis
In the improved scheme I, the order of groups
Computation complexity of
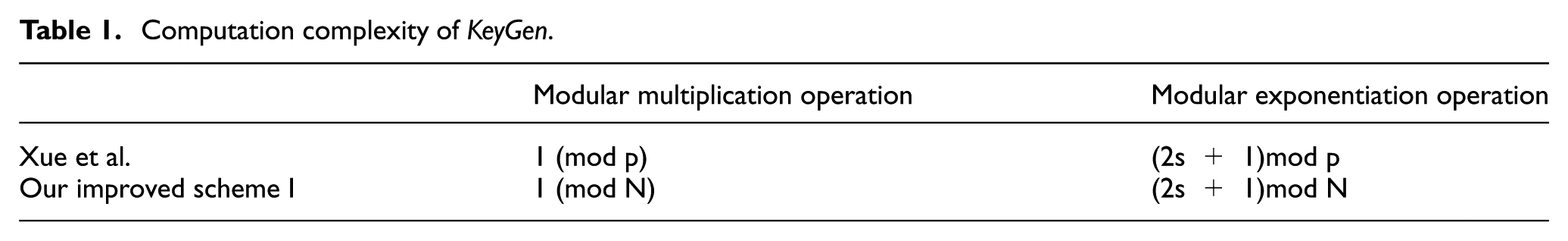
Computation complexity of
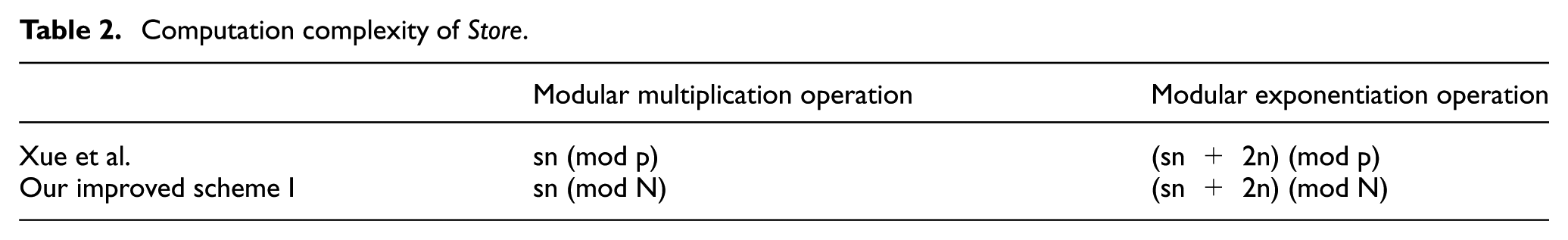
Computation complexity of

Now, we assume that
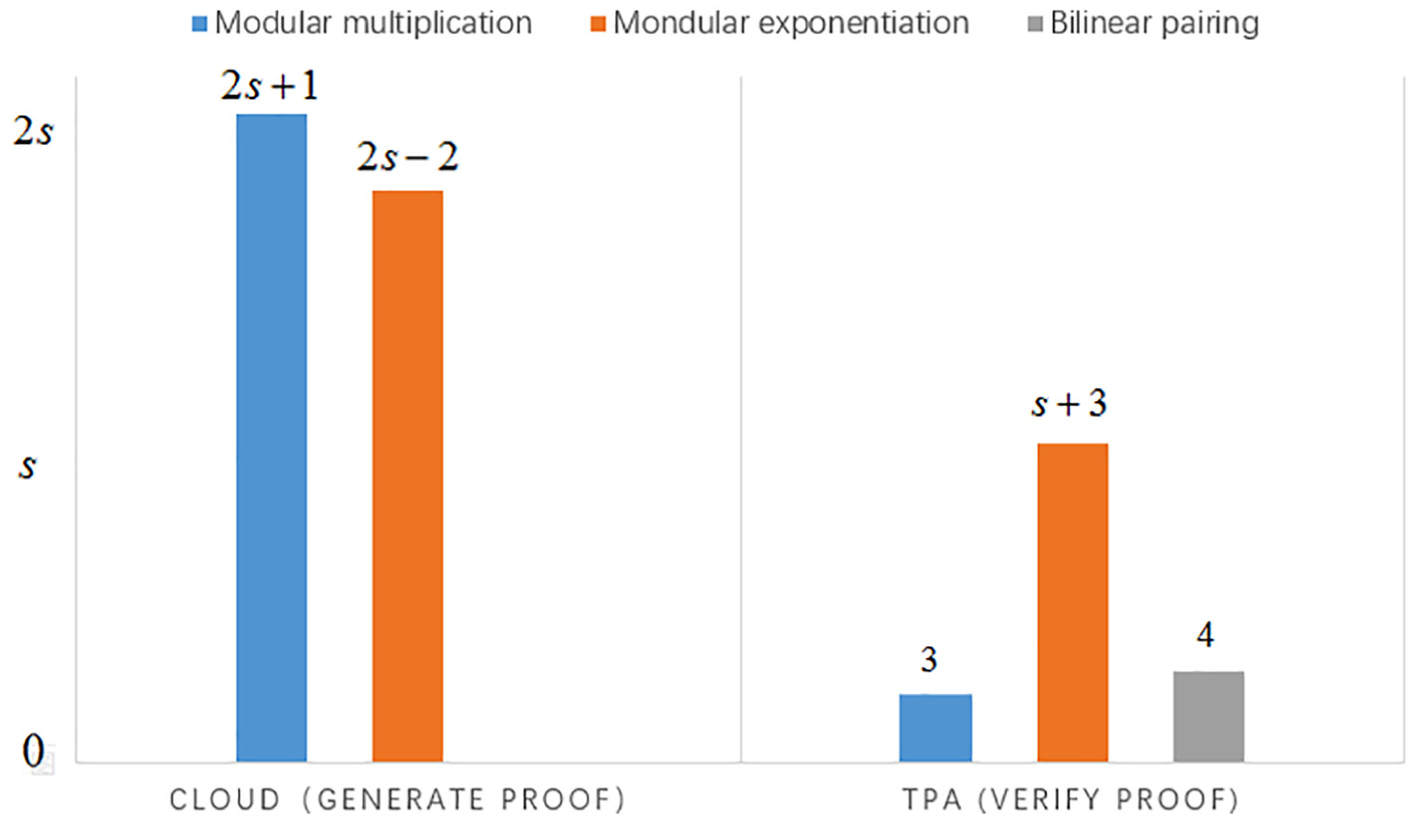
Computation complexity of the original protocol.

Computation complexity of the alternative scheme II.
Comparison of computation complexity.

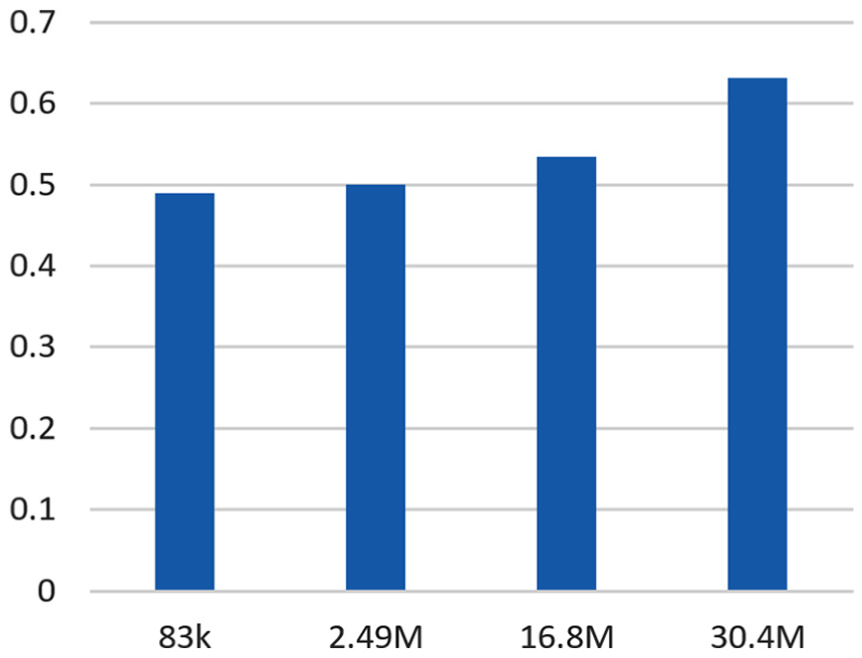
We evaluate the effectiveness of the alternative auditing scheme II using java and give its time running figures to express it intuitively, including the processes of key generation, outsourcing, auditing, certification, verification, and total running time (unit: ms). As can be seen from Figures 11–16, the time consumption of the software is mainly in the file outsourcing or file upload process, but the file can be audited multiple times after one upload, so the alternative protocol is practical.

Audit time.

Prove time.

KeyGen time.
Verifying time.

Outsouring time.

Total running time.
Security analysis
In this section, we mainly prove the security of the alternative auditing protocol because the security of other modules had been proved in the article of Xue et al. and the security flaw has been made up by us. For our alternative auditing protocol, the error probability of the alternative auditing protocol is
Step 1: when the data stored on the cloud is compromised, the cloud server cannot cheat the user with a non-negligible probability. First, if a true random function is used in our protocol, let
Step 2: we show that if
Conclusion
In this article, we first point out a security flaw in Xue et al.’s scheme. To optimize their scheme, an improved scheme is proposed for secure cloud storage; the security analysis shows that our improved scheme is more secure and can resist the attack which we have present. Besides, we propose a alternative protocol to improve the integrity auditing efficiency of their scheme. The performance analysis shows that our alternative protocol is more efficient and likely to be applied in cloud systems.
Footnotes
Acknowledgements
This paper is an extended work of a conference paper28 with significant extension including new proposal, new security analysis, and performance analysis. The authors thank Xiaoshuang Luo, Liqun Lv, and Zhenlin Li’s help on this paper.
Handling Editor: José Camacho
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the National Cryptography Development Fund of China (grant no. MMJJ20170112), Natural Science Basic Research Plan in Shaanxi Province of China (grant no. 2018JM6028), National Natural Science Foundation of China (grant nos 61772550, U1636114, and 61572521), and National Key Research and Development Program of China (grant no. 2017YFB08 02000). This work is also supported by Engineering University of PAP’s Funding for Scientific Research Innovation Team (grant no. KYTD201805).
