Abstract
Due to exponential growth in the daily usage of vehicles, the traffic congestion and roadside accidents are increasing day by day. The communication among vehicles is critical to avoid the emergencies and to address the issue of congestion of vehicles. Internet of vehicles provides the communication channel between the vehicles, but existing solutions require a centralized communication system to distribute the message and to authenticate the source. This centralized infrastructure is subject to disturb the vehicular communication in case of server breakdown or due to any natural disaster where hardware stops working. Also, the centralized system proves to be costly as the communication of each vehicle necessitates access to the central server resulting in the more resource requirement. A secure distributed system is required to avoid the emergencies and reduce the traffic rate. To address the issues, we proposed a secure distributed message-passing framework that does not require a centralized server, and it rates the credibility of message source using blockchain technology. The messages in the proposed system are forwarded through dedicated short-range communication protocol. To validate the proposed system, we have performed different simulations using SUMO, OMNET, and VEINS. The results demonstrated an increase in the average speed of vehicles that showed a reduced congestion rate. Moreover, our system identified the malicious vehicles with 77.1% accuracy.
Introduction
With the rapid and excessive growth in population, vehicular usage is increasing each day. This proliferation in the daily use of vehicles has given rise to two primary issues: traffic congestion and accidents. Hence, it is decreasing the efficiency of the transportation system 1 and causing 2% economic loss to global gross domestic product (GDP). 2 The traffic jams usually take place due to small and large accidents. These accidents occur because of driving on the opposite side of regular traffic and applying sudden brakes while overtaking. 3 To reduce the daily accident rate, wastage of time, and pollution, there is a need for a communication mechanism among the vehicles. The Internet of vehicles (IOV) used wireless communication to send and receive status information (speed, acceleration, and direction) of the neighborhood vehicles to each other. 4 IOV consists of various components of the transportation network which include vehicles, humans, and hardware devices present in the environment which are connected through an IP-based infrastructure. All these components share vehicular information directly or indirectly. 2 This vehicular communication grants an opportunity to the other traffic participants to get warning messages about sudden collisions and variations in speed. These messages result in a safe, more comfortable driving environment and enhance the reaction time of drivers. The warning messages, exchanged among vehicles, can be divided into distinctive types such as lane change warning, blind spot warning, forward collision, emergency electronic brake light warning, intersection movement assistance, and do not pass by warning. 5
A shared wireless medium is a conventional approach in the vehicular ad hoc network (VANET) for data dissemination during vehicle-to-vehicle (V2V) communication. With an increasing number of automobiles, the load increases on the centralized system, which could cause a slow response or even no response. Also, the messages sent through V2V communication are subjected to multiple security threats such as Sybil attack, Wormhole attack, and Illusion attack. 6 These attacks not only affect the privacy of drivers but also can cause severe threats to their lives. The digital signature is commonly used to secure messages where each message is digitally signed with the help of some authentication protocol. 7 These digital signatures are accompanied by digital certificates that are issued through some central authority. Failure of this central authority and the inclusion of these digital signatures cause overhead in urban areas. Furthermore, it also increases the redundancy of data. 7
The goal of this research is to build a hybrid framework that can create, disseminate, and secure the warning messages communicated among vehicles through the decentralized system without the requirement of any roadside unit (RSU).
More specifically, we have asked the following research questions:
How to create a warning message effectively at the application layer for different collision scenarios?
How to disseminate emergency warning messages to vehicles effectively?
How to secure and authenticate messages exchanged among vehicles?
Introduction to blockchain technology
To provide a secured distributed network, we have considered different frameworks. We believe that the blockchain is the best-distributed solution for the given research question. In this section, we provide a brief introduction to the blockchain, so it is easier to understand the proposed solution.
To overcome the issues caused due to centralized network structure, Satoshi Nakamoto proposed a decentralized and consistent database system called “Blockchain.” 8 It consists of a distributed and open ledger which is saved and updated by each node. Each ledger consists of blocks that are chained together and store transactions. Each block consists of a list of previously made transactions and their hash keys. Each transaction has digital signatures of sender and receiver. These transactions are validated by trust-less participants “Validators” in this distributed network. These validators run a protocol called “Consensus Algorithm” that allows them to validate a transaction on the blockchain. The structure of a blockchain is shown in Figure 1.

Architecture diagram of blockchain.
The rest of the article is divided into the five sections. The “Related work” section contains a comprehensive literature review, the “Proposed solution” section describes the proposed solution, and the “Experiments” section gives the details of the experiments and reports the results. Finally, the “Discussion” section is given, and the article is concluded.
Related work
Chen and Mao 9 developed a framework for the analysis of the security of warning messages those are distributed randomly among vehicles present in a VANET. In this network, malicious vehicles were usually distributed. This work calculated the probability of receiving a message correctly by a vehicle at a particular distance. Moreover, the accuracy of the broadcast messages was improved to some extent through the fusion of all received messages. The theoretical model was validated through simulation for correct delivery of the message and did not focus toward the use of any hardware resource.
Liu et al. 10 proposed a broadcasting scheme “Receiver Consensus” (ReC) for distribution of warning messages in vehicles present in a VANET. This algorithm employed geographical information to assist the nodes to make a consensus for the choice of a forwarding node. The neighboring vehicles, based on their distance from the ideal location, were ranked and assigned priority autonomously to broadcast the message. Results of the experiments showed delays in communication due to medium access contention. Madani 11 proposed an agent-based simulation model which applied the self-pruning broadcast algorithm on the disseminated warning messages among vehicles. This algorithm employed a roadside sensor for sending warning messages. The messages were forwarded to all nearby vehicles up to a certain number of hops. Results showed that communication in VANET is affected by roadside equipment as only one roadside sensor was used that proved to be ineffective in sparsely connected vehicular networks.
To target the position accuracy and time-critical problems in the distribution of warning messages among vehicles, Tsai et al. 12 proposed a cooperative emergency braking warning system that employed a camera sensor and dedicated short-range communication (DSRC) communication protocol. The state of neighboring cars was constructed along with the method to reduce message transmission. The warning messages were only distributed in the same lane where the brakes were applied. However, this work ignored the security and authentication of the distributed messages. The possibility of a message coming from a malicious car was very high. Basheer et al. 13 proposed a two-stage decentralized model to authenticate a message sender in a VANET. The sender was authenticated by evaluating multiple environment variables along with their dependencies using a Bayesian network.
Chuang and Chen 14 proposed a density-aware emergency message extension protocol (DEEP) to deliver emergency messages to resolve the broadcast storm problem with low dissemination delay in specific areas. Villas et al. 15 proposed a data dissemination protocol for VANETs (DRIVE) to target the problem of a broadcast storm. This protocol used one-hop neighbor information and selected vehicles in a sweet spot to rebroadcast the message. An event-based reputation system was proposed by Feng et al. 16 to suppress the effect of Sybil attack within a VANET. This system generated dynamic reputation and trusted values for each event, hence ensuring the integrity of each message and the identity of each vehicle by employing a trusted RSU. This RSU was used to issue certificates to vehicles in its communication range. Tobin and Thorpe purposed an approach to mitigating black hole attacks on VANET. This solution was a multi-step process consisting of attack detection, node accusation, and malicious node blacklisting. 17 The system assigned a unique identifier to each vehicle through electronic vehicle identifier (EVI) that made each vehicle incapable of spoofing. RoselinMary et al. 18 suggested an attack packet detection algorithm (APDA) for detecting denial-of-service (DOS) attacks in a VANET. The system identified a malicious sender (vehicle) through the velocity and packet broadcasting rate. However, this algorithm was unable to identify multiple malicious vehicles those are sending multiple packets simultaneously.
A vehicular communication system was proposed by Wararkar and Dorle 19 for quick and cost-effective data distribution among vehicles. The authors used hardware resources, RF transmitters and receivers, for reporting any unusual situation around the automobiles. The position of vehicles as reported by the RF transceivers also helped to identify malicious automobiles. Mokhtar and Azab 20 briefly described the characteristics of VANET that lead to vulnerabilities. These features include network scale, volatility, heterogeneity, and wireless link use. The authors also classified the security attacks on VANET respective to each layer in the layered stack model. Countermeasures for each of these attacks were also discussed in detail.
Sedjelmaci and Senouci 21 implemented AECFV, a clustering algorithm for intrusion detection in VANET. The authors used detection and categorization techniques for detecting attacks like a black hole, wormhole, packet duplication, and Sybil attacks. A secure identity-based scheme with aggregate signatures was proposed to avoid communication and computation bottlenecks in revocation of new vehicles. 22 The simulation results showed a fast response and low latency rates. Rathi 23 suggested a counter field–based reputation technique for V2V communication. The author employed counter field to authenticate the sender, the semantics of the message, and usage frequency of same anonymity key of a sender vehicle. Mühlbauer and Kleinschmidt 24 presented a certified reputation system where reputations of vehicles were updated periodically by centralized authorities. Reputation level of a vehicle was determined through the behavior of a vehicle over the network. Jenefa and Anita proposed a secure authentication framework that generated and used pseudonyms instead of the original identification numbers of the vehicles. The technique helped to reject attacking nodes from the network. 25
In summary, inter-vehicular communication is responsible for spacing between vehicles and controlling other components such as sudden braking and message broadcasting to other vehicles. The communication between vehicles is usually wireless, which is vulnerable to be intercepted and hacked. 26 Moreover, this communication also gets unavailable or failed in case of natural disasters resulting in heavy traffic congestion. The RSUs have their limitation of processing and storing when a large number of vehicles are communicating with each other. Also, the centralized system is very much vulnerable to attack. Furthermore, the dissemination rate of these messages is limited to a specific geographical area. Table 1 presents a comparison between existing literature on the distribution and security of inter-vehicular messages.
Comparison between existing literature on the distribution and security of inter-vehicular messages and proposed work.

RSU: roadside unit.
Proposed solution
System architecture
The proposed system consists of the following layered architecture Figure 2:
The application layer is the topmost layer of our system’s architecture. This layer offers services to generate warning messages and corresponding actions.
The transport layer is responsible for node-to-node communication.
Network layer plays a vital role in the proposed system as it uses blockchain for distributing and storing the emergency warning messages among vehicles.

The layered architecture of the proposed model.
The proposed system creates emergency warning messages to disseminate among the vehicles through a distribution channel when there is a chance of collision or accident. It also provides a decentralized system for authenticating the identity of the sender (vehicle) with the backend technology of blockchain that is explained in section “Introduction to blockchain technology.” The proposed system generates different warning messages for each scenario that can result in a collision. These types of messages are discussed below.
Types of warning messages in the V2V communication
Emergency Electronic Brake Light (EEBL) Warning: This type of warning message warns a vehicle about a hard brake ahead when the line of sight is obstructed by other vehicles.
Forward Collision Warning: This warning message notifies a vehicle about the rear-end collision with an approaching car traveling ahead within the same lane and in the same direction.
Intersection Movement Assistance: The drivers of the vehicles at an intersection are warned if it is not safe to change the direction. Also, the probability of collision is higher due to the vehicles coming from the other directions of the intersection.
Lane Change/Blind Spot Warning: This type of message is distributed among vehicles if it is not safe to change the lane due to an already present or an oncoming vehicle.
System flow
The flow of the system is shown in Figure 3, where we have discussed a few scenarios that cause traffic congestion (emergency brake, lane change, forward collision, and intersection movement). On-board equipments (OBEs) are sensors fixed on the vehicles that help to find anomalies in vehicle behavior. When a vehicle finds abnormal behavior (emergency brake, lane change, forward collision, or intersection movement) exhibited by another vehicle, it forwards a transaction containing Foundation for Intelligent Physical Agents (FIPA)-compliant messages along with the respective actions to the other incoming and neighbor vehicles through DSRC technology. This transaction is logged and updated by all receiver vehicles. To check the authenticity of the message, we have used the reputation system for vehicles. In this system, each vehicle is assigned specific points on the exchange of a message, and if there exists any previous transaction from the sender (vehicle), the reputation of the sender is increased. Priority is given to high-reputation vehicles, and the reputation is higher than a threshold value. The reputation of the sender is stored in the variable “REPO_ID.” The value of the variable “REPO_ID” is also sent along with the message to assist the receiver to measure the authenticity of the message.

Overall system flow.
All the nodes (vehicles) communicate with each other through transactions containing signatures of both sender and receiver. Each vehicle is responsible for storing its identity-related information. The format of each message sent by a vehicle is mentioned below in Figure 4:
Transaction ID: it is the ID of the current transaction.
Previous Transaction ID: it represents the ID of the previous transaction that is made by the subject.
Sender ID: it is the ID of the sender.
Repo_ID: this number represents the reputation (points) of the subject vehicle.
Receiver ID: it is the ID of all receiver vehicles to whom warning or query message is to be sent.
Message Content: this layer consists of message content, that is, message text, location, and direction of the sender vehicle.
Message Type: this layer contains the information about the type of warning message, that is, intersection movement assistance warning, emergency electronic brake, light warning, and forward collision warning.
Action Requested: it is the type of action requested by sender vehicle from all receiver vehicles, that is, application of brakes or requests to lower the vehicle’s speed.

Message format.
Creation of FIPA-compliant messages
This section briefly describes the creation process of emergency warning messages. These messages are created based on the results of sensors present on a vehicle. In case, if the value of sensors is equal to the particular threshold, the system creates the specific FIPA-compliant messages.
Scenario 1: Emergency Electronic Brake Light (EEBL).
In this scenario, the vehicle that is applying emergency hard braking informs the other vehicles those are in front of it and in the same lane. However, the vehicles in the adjacent lane will not get a warning message.
Message Format:
)
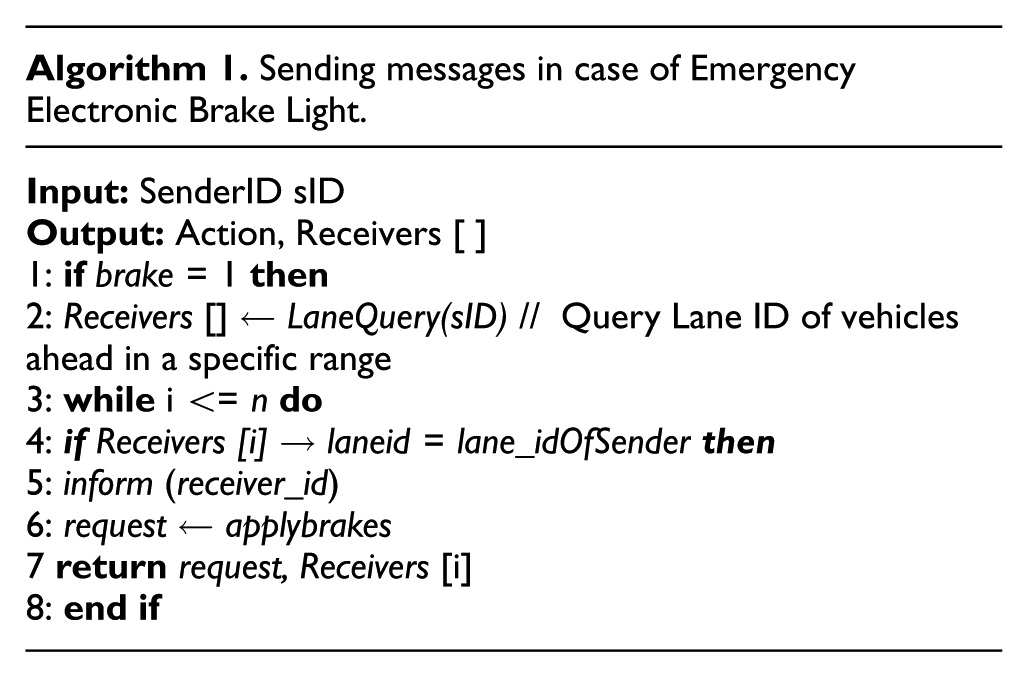
Description
If the sensors equipped on a vehicle shows an emergency brake light indicator in one of the vehicles ahead, the system queries for lane id of each vehicle in a particular range through the function LaneQuery(). The function LaneQuery() returns an array of ids of all the vehicles in the specific area. If the lane id of any of the receiver vehicle matches with that of the sender vehicle, the first one sent a message consisting of the warning and a request to apply brakes.
Scenario 2: Lane Change Warning.
In this scenario, a vehicle that changes the lane warned a collision to other vehicles those are present in the lane where the vehicle is going to shift.
Message Format:

Description
In case, if the left or right indicator of a vehicle is turned on, the vehicle asks for lane_id of each vehicle in a particular range through function LaneQuery(). The vehicles have the same lane_id, as of the sender vehicle and the lane_id in which sender vehicle will shift, are sent the location of sender vehicle and a warning message to lower their speed.
Scenario 3: Forward Collision Warning.
This type of warning is made if the sensors of a vehicle sense a quick deceleration in the vehicle moving ahead.
Message Format:

Description
If the sensors of a vehicle show that distance between two vehicles in the same lane is less than a particular range, the sender agent asks for lane_id of each vehicle in a particular range through the function LaneQuery() that returns the list of receivers. The sender vehicle then sends a warning message (including the location, speed, and acceleration) to the vehicles present in the same lane.
Scenario 4: Intersection Movement Assistance.
Message Format:
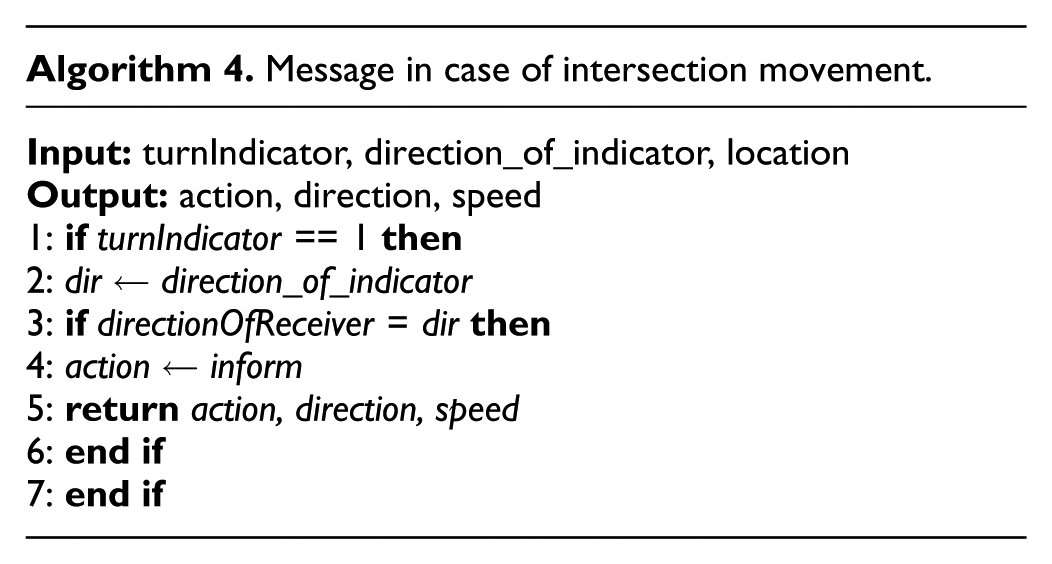
Description
In this case, if the turn indicator of a vehicle is found to be turned on, a warning message is sent to each vehicle having the same direction as that of the indicator. The warning message encapsulates the message text, direction, speed, and location of the turning vehicle.
Experiments
Simulation environment
We performed simulations of the urban traffic in specific areas using data from OpenStreetMap (OSM). 27 We have used the map of the area of Model Town and Railway Station in Lahore, Pakistan, that frequently have massive traffic Figure 5(a) and (b), respectively. Yellow dots on the roads represent the vehicles.

Simulation environment: (a) simulation environment and (b) zoomed version of simulation environment.
We used sumo 5.1.0 to simulate the traffic environment of the mentioned areas. The package (SUMO) can simulate an extensive network of roads with multiple lanes as well as various intersections at these roads. We employed OMNET++ 5.1.0, an event-based network simulator, for routing, layering, and sending messages. Simulations in OMNET++ are run interactively through graphical user interface (GUI) or by command line interface. OMNET++ and sumo can buffer multiple commands that are executed after the completion of a particular timestamp, and the messages are disseminated to the vehicles. The parameters that we have used to evaluate the performance of the proposed system during the traffic congestion are average traffic speed and average hop count of message packets. For evaluating the efficiency of the system regarding security, we used the data produced by our system showing the classification of normal and malicious vehicles. We introduced 20 new vehicles in the simulation environment with different parameters like speed, acceleration, and direction. For evaluation purpose, the vehicles were configured to drive at a maximum speed of 25 m/s.
For the detection of a collision, we employed speed, acceleration, and distance among vehicles. If the speed of a particular vehicle is 0 m/s along with the acceleration for a particular time interval (4 s) and distance less than a particular threshold, a message is created by the vehicle and is distributed to the incoming vehicles.
Experiment 1: vehicle speed and message distribution rate without blockchain
In the first experiment, the total of 25 new vehicles was introduced in the simulator. The simulation was run with different values of speed, direction, and other driving parameters. The speed of some vehicles was set to “0 m/s” for introducing a collision effect (brakes). The simulation environment consisted of a traffic mobility environment containing multiple vehicles moving at different speeds and in different directions. After the completion of simulation time, the average speed of vehicles and the number of hop counts covered by message packets are logged in Tables 2 and 3, respectively. Figure 6 shows the hop count and node information obtained in Experiment 1.
Traffic congestion warning distribution matrix.

Average hop counts covered by message packets with and without blockchain.


Hop count and node information in the simulation setup.
Experiment 2: vehicle speed and message distribution rate with blockchain
The purpose of this experiment was to estimate the elevation in average speeds of vehicles and distribution rate of the warning messages. The experimental environment was same as of the Experiment 1. The only addition in this environment was blockchain for disseminating emergency warning messages among vehicles. The average speed of all vehicles at three different time intervals is logged in Table 2. The average number of hops covered by a message packet is also logged in Table 3.
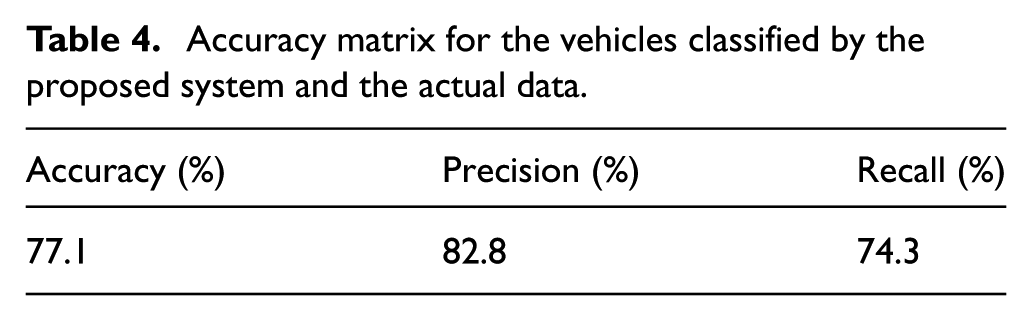
Experiment 3: message security with blockchain
This experiment was performed to calculate the efficiency of the proposed system regarding the security of the messages being exchanged. For this purpose, “n = 70” number of vehicles were simulated in the simulation environment (section “Simulation environment”). These vehicles were moving in different directions with the specific speed. The speed of 12 random vehicles was set to 0 m/s to produce collisions. Vehicles exchanged warning messages with each other in case of emergency. Messages among vehicles were distributed using blockchain. Our system classified each vehicle as “normal” (verified) and “malicious” (unverified) based on the value of its REPO_ID variable. Actual data about the authenticity of each vehicle were already present. In this experiment, only those vehicles were subjected to the classification which has a reputation greater or equal to a threshold value, threshold = 5 in our case. Results for this experiment are logged in Table 4.
Accuracy matrix for the vehicles classified by the proposed system and the actual data.
Results
For calculating the efficiency of message-passing among the vehicles to avoid collision and congestion, we have used average traffic speed, the average number of hops, and the number of vehicles classified as normal.
For this purpose, we have selected a random sample of 20 vehicles plotted in the simulator (Experiments 1 and 2). Also, we used the mean of their speed (Table 2) and the average number of hops (Table 3) covered by message packets. The observations (Table 2) were taken at three different time intervals. Figure 7 shows a comparison of average speed of vehicles in the scenarios when blockchain was employed and the other where blockchain was not used.

Comparison between average speed of vehicles in the simulator with and without employing blockchain.
Average traffic congestion was calculated by comparing the number of hops traveled by a packet without employing blockchain to those of covered after using blockchain. The results are logged in Table 3.
For calculating the efficiency of the system regarding the security, we used the data generated by our system about the classification of the vehicles. The proposed system classified vehicles as “verified” or “malicious” based on their reputation. Table 4 presents an accuracy matrix for the vehicles classified by the proposed system and the actual data about vehicles authenticity.
Significance tests
We have performed two significance tests. In the first test, we verified whether the proposed technique has significantly increased the message-passing rate. In the second test, we verified whether the proposed techniques significantly decreased the congestion rate. For significance testing, we employed one-sample right-tailed t-test that used mean of traffic speed (Table 2) to show that whether the blockchain significantly increased the average traffic speed. The formula for this test is

where n is the number of vehicles selected for the sample, and s is the standard deviation of the speeds of vehicles when they did not exchange messages. µ is the mean of the average speed of vehicles when they did not exchange messages with each other.
Comparison of distribution rate of messages with and without blockchain layered architecture
We conducted two experiments: Experiments 1 and 2. In the first experiment, the simulation was run for a fixed time interval along with the vehicles moving around at different speeds:
H 0. Distributing intravehicular messages through blockchain does not increase the average traffic speed.

H 1. Distributing intravehicular messages through blockchain increases the average traffic speed.

Confidence interval used in this testing was α = 0.05. t-value obtained from this section was 2.940 > 1.729.
Comparison of the congestion rate with and without blockchain layered architecture
In Experiments 1 and 2, the number of hops covered by a message packet assisted in determining the average congestion rate of vehicles. The simulation environment was the same as of section “Comparison of distribution rate of messages with and without blockchain layered architecture.” The significance test performed in this section was for the following observations:
H 0. Distributing messages through blockchain does not affect the traffic congestion rate.

H 1. Distributing messages through blockchain decreases traffic congestion.

Confidence interval used in this testing was α = 0.05. t-value obtained from this section was “−1.842 < 1.761.”
Discussion
In this research, we have proposed a layered architecture for intravehicular communication with blockchain. We simulated an environment for urban traffic mobility and performed three experiments (Experiments 1, 2, and 3). Results of these experiments are logged in Tables 2–4, respectively. In this research, we have effectively created warning messages those are disseminated among vehicles. These messages were FIPA-compliant and were different according to the situation that could cause a collision. The warning messages were effectively distributed among vehicles through the use of blockchain. This fact was proved through the average speed of vehicles, employing blockchain architecture for passing intravehicular warning messages, which was increased from 18.893 to 19.515 m/s (Table 2). This increase in vehicles’ average speed rejects the null hypothesis: employing blockchain for inter-vehicular communication does not affect the speed of vehicles by t-value (2.940 > 1.729). These results prove that communication through blockchain results in less congestion and smoothness in traffic flow. Also, these results prove that the distribution rate of messages increases through blockchain.
Inter-vehicular communication through blockchain also decreased traffic congestion (Experiment 2) by reducing the average number of hops covered by message packets from 7.33 to 6.00. The significance test proves the alternate hypothesis that blockchain decreases the typical traffic congestion with t-value (“−1.842 < 1.761”). For evaluating the efficiency of the system regarding security, Experiment 3 was performed. The results of this experiment proved that use of blockchain for passing inter-vehicular messages increased the security of those messages by correctly identifying the “normal” and “malicious” vehicles. In this experiment, the number of vehicles classified by the proposed system was compared to their actual label. The system showed an accuracy of 77.1%, a recall of 74.3%, and the precision of 82.8%, which proves the high-efficiency rate of securing the messages by authenticating the sender. The error rate of the proposed system is 22.8% with still space for improvement.
Conclusion
In this research, we have proposed a secure and decentralized system for vehicular communication to avoid the security risks and low distribution rates of the centralized system. This system distributes FIPA-compliant warning messages through the decentralized database (blockchain) for different scenarios to avoid a collision. Also, we have employed blockchain to authenticate the sender (vehicle) of a warning message through the reputation assigned to each vehicle. The high accuracy rate proves that the system is successfully distinguishing between malicious vehicles and regular vehicles.
Moreover, the average speed of traffic has also increased by employing blockchain. This system works only for the vehicles that possess a reputation higher or equal to a threshold value. In future, this work can be extended to authenticate the vehicles with their first transaction which is below the threshold reputation.
Footnotes
Handling Editor: Razi Iqbal
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
