Abstract
Selective forwarding attack in wireless sensor networks shows great impact on network performance and consumes limited energy resource. In previous countermeasures, it is assumed that all nodes in the communication range can detect misbehaviors of the attacker. However, as wireless devices require certain signal-to-noise ratio to receive frames correctly, and interference among nodes is inevitable in densely deployed wireless sensor networks, it is very difficult for previous approaches to detect misbehaviors accurately. In this article, a scheme named E-watchdog is proposed to improve accuracy of selective forwarding attack detection. Detection agents that are closer to the attacker are used to detect misbehaviors, which can improve the detection accuracy and reduce the false alarm rate effectively. Moreover, to prevent collaborative selective forwarding attack, E-watchdog uses reports from more than one detection agents. Fake reports from attackers are filtered out through an election algorithm. Simulation results show that the E-watchdog reduces the false detection rate by 25% and improves the detection accuracy by 10% on the premise of increasing negligible energy consumption.
Wireless sensor networks (WSNs) have broad application prospects in the fields of environmental monitoring, wildlife tracking, smart home, and healthcare monitoring. WSN consists of dozens to thousands of tiny sensor nodes that collect information from the physical environment and send it to the sink node. Sink node is gateway to external networks, data processing, and storage centers. Since nodes in WSN have limited communication range, multi-hop communication is used to send data to sink node. Nodes in WSN communicate with each other using open wireless channel. Therefore, security is an essential prerequisite for the real-world deployment of WSN. 1 The WSN is characterized by its limited storage and computation resources. Therefore, security mechanisms for traditional wired or wireless networks and the ad hoc networks cannot be adopted because of their heavy computation overheads. 2
In a selective forwarding attack (SFA), an attacker, which participates in the routing as normal node, selectively discards packets from neighboring nodes. The attacker may forward non-critical data normally, but discard important data such as a reports triggered by enemy in a military application. It will lead to serious damage to WSN because losing sensitive information in monitoring application is unacceptable. 3 Detection and isolation of SFA is an important research topic in the field of WSN security.
Many schemes are proposed to defend against SFA in WSN. Some schemes adopt multi-path forwarding, in which multiple paths are used to route data to the sink node. In the presence of SFA, more than one copy of data is forwarded to the sink node via different paths to avoid losing sensitive information. However, as compared to single-path forwarding, the average power consumption doubled if data from source node are forwarded to the sink node via two different paths. The network life cycle is reduced drastically. Therefore, multi-path schemes are not suitable for WSN due to their excessive power consumption.
Watchdog is a typical scheme that detects SFA without multi-path forwarding. In this scheme, node enters promiscuous mode after transmitting to determine whether the neighboring node forwards the data as requested. Only limited overhear time is required in watchdog to detect SFA. Therefore, this scheme is power efficient because no additional communications are required. The main problem of watchdog is that this scheme adopts a quite simple communication model. That is, nodes within the communication range can receive data from each other without error. However, due to interferences among nodes in the network, communications are much more complex in real-world wireless world. Watchdog cannot detect SFA accurately in two situations. First, a node may forward the data as requested. But the detector node cannot capture the forwarded data because of collisions at the detector node. Therefore, the node is considered to be a malicious node even if it forwards the data as requested. We call this a false alarm. Second, a node may intentionally forward the data to a node that is transmitting data to other node. Apparently, the destined node cannot receive the data successfully because it is transmitting. But from the perspective of the detector node, the node acts normally as it forwards the data as requested. This is a more subtle SFA, which is quite difficult to be detected. Watchdog scheme is not effective because SFA cannot be detected under both situations.
To effectively improve the detection accuracy of SFA in WSN, a scheme named E-watchdog is proposed in this article. A node named detection agent that is closer to the forwarding node is selected for SFA detection, which can effectively reduce the false alarm. Moreover, nodes between the receiving node and the forwarding node have priority to be selected as detection agents under E-watchdog. Since such nodes can capture both data transmitted by the forwarding node and the receiving node, it can also detect subtle SFA mentioned above. In order to prevent joint spoofing of multiple malicious nodes, more than one detection agent is selected in E-watchdog. The final decision of SFA malicious nodes is based on reports from multiple detection agents, which can further improve the detection accuracy.
Related works
In the work of Marti et al., 4 the authors analyzed the SFA against wireless routing protocol of multi-hop networks. It is the first time that the SFA is illustrated in detail. Extensive simulation results show that with the increase of misbehaving nodes, the average throughput of the network is reduced by up to 32%. The authors propose the watchdog scheme, in which the node judges whether the forwarding node forwards the data as requested via capturing. This article also declares that the main disadvantage of this scheme is that the detection accuracy for misbehaving nodes is low because of interference from other nodes. But no schemes with higher detection accuracy are proposed.
In the work of Karlof and Wagner, 5 the author first illustrated black hole attack and SFAs against WSN. In the black hole attack, the attacker misleads traffic from neighboring nodes by broadcasting the shortest path to sink node. From the perspective of misbehaving node detection, the black hole attack is a special case of SFA, which absorb traffic without any forwarding. However, as compared with SFA that forwards portion of data, the black hole attack is much easier to be detected. The authors analyzed the SFA against typical routing protocols such as Directed Diffusion and Geographic Routing in detail. A multiple-path forwarding scheme is proposed to defend against SFA. Multiple forwarding paths are established between the source node and the sink node. On having data to be transmitted to sink node, the source node sends a copy of the data through each path, ensuring that the sink node can receive at least one copy of the data. The disadvantage of this scheme is that the energy consumption is increased by several times due to multiple copies of data are sent to the sink node through different paths. For WSN with limited energy resource, such schemes will reduce the life cycle of the network drastically.
In the work of Liu et al., 3 while forwarding data to the sink node, each node along the path sends an ACK to the source node to declare that it is not an SFA node. These ACKs are routed to the source node through different paths to avoid attacks against ACKs. If a node in the path discards the data, all nodes from it to the sink node will not send ACKs to the source node. Therefore, the source node can accurately detect the malicious node in the forwarding path. The main disadvantage of this scheme lies in great power consumption. Assuming that there are 10 hops from the source node to the sink node, 10 transmissions are needed for data forwarding and 50 transmissions are needed for ACKs. The number of transmissions is six times than that of original routing. Furthermore, node in a typical WSN only records routings to the sink node. But this scheme requires node having routings to source nodes. The memory and computation overheads are increased drastically.
The work of Ren et al. 6 is the closest to our scheme. The authors argued that the interference from nodes affects the SFA detection accuracy and proposed a channel-aware reputation system. Channel quality is considered to adjust the threshold for SFA detection. For node with higher interferences, a higher threshold for data loss is used to avoid false alarm. Apparently, this scheme is more practical as compared with schemes with simple communication model. But in a real-world WSN, SFA will not introduce noticeable changes in data loss rate. Only a small portion of data are discarded by the SFA node. Therefore, this scheme cannot improve the accuracy of SFA detection.
Wireless propagation model
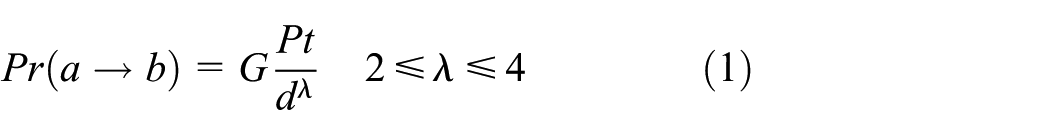
To analyze interference among nodes in the WSN, a wireless propagation model is used, which can be expressed as 7
where
The ratio of received signal strength from the transmitter and environment noise can be called SINR, which is denoted by
where N0 is the environmental noise. For expressing, we simplify
Network model
Definitions and assumptions
Definition 1 (SFA node). An SFA node is a malicious node which attempts to discard data that are requested to be forwarded by other nodes.
Definition 2 (initiator). An initiator is a node which tries to detect whether the next hop neighboring node discards its data without forwarding.
Definition 3 (target). A target is a node which is the next hop node to the initiator.
Definition 4 (agent). An agent is a node that is selected by the initiator to detect whether the target is an SFA node.
Definition 5.
It is assumed that there are many sensor nodes and one sink node in the WSN. Sensor nodes detect the physical environment via its sensors. On detecting event of interesting, the node sends data to the sink node (D in Figure 1) for reporting. The node that detects the external event is called a source node (S in Figure 1). Since the source node is far away from the sink node, data need to be forwarded by an intermediate node. During forwarding, the initiator (A in Figure 1) forwards data to node C through node B. After node A sends data to node B, it needs to detect whether the target (B in Figure 1) forwards the data to node C as requested. Therefore, node A is an initiator, node B is a target, and node C is a receiving node. In order to accurately detect whether node B forwards the data as requested, node A requests node G to detect, and node G is referred to as an agent.
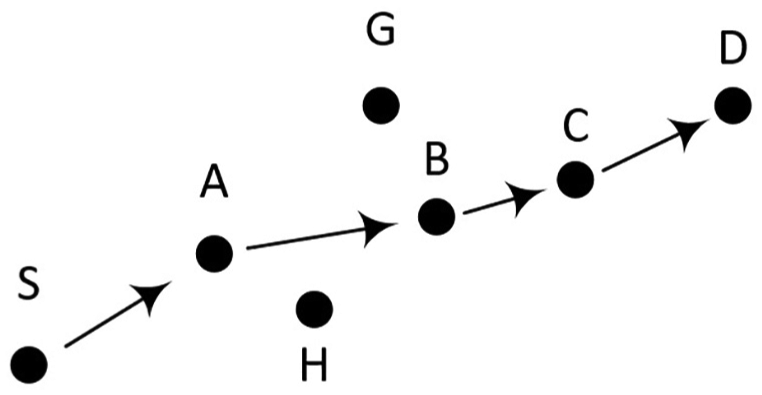
Detection agent for accurate SFA detection.
Adversary model
We assume that the SFA node in the network is a normal WSN node with the same wireless transmission range as the others in the network. The attacker may obtain some nodes through compromising. After analyzing and modifying programs within the node, the node becomes a misbehaved SFA node. The SFA node participates routing as normal nodes. However, this node may discard some important data during forwarding, in order to jeopardize the normal operation of the network. To avoid being discovered, SFA node forwards most of the data normally. We assume that the attacker is familiar with the routing protocol and the scheme proposed in this article. Therefore, multiple SFA nodes may jointly deceive to avoid being discovered.
Disadvantages of watchdog and the proposed schemes
The watchdog mechanism proposed by Marti et al. 4 is a fundamental SFA detection scheme. As illustrated in Figure 2, node S sends data to node D through intermediate nodes A, B, and C. After sending data to node B, node A captures the wireless channel to determine whether node B forwards data to node C as requested. If node A detects that node B forwards data to node C, node B is considered to be a normal node. If node A does not detect the forwarded data from node B, node A considers node B an SFA node. As watchdog monitors forwarded activities via neighboring nodes without introducing additional communications, and it overcomes the shortcomings of the end-to-end feedback schemes. 3 Watchdog assumes that the wireless channel is symmetric. That is, if node B can receive data from node A, node A can also receive data from node B. However, in the real wireless world, the wireless channel is often asymmetrical due to environmental interferences. With different interferences at node A and node C, node A may not be able to successfully receive data sent from node B even if node C can successfully receive it. 8

SFA detection in watchdog and E-watchdog.
As shown in Figure 2, node A sends data to node C through node B. Under watchdog scheme, after sending data to node B, node A monitors whether node B forwards as requested through channel capturing. As node C is closer to node B, node C may receive the data, but node A may not receive it correctly because of interferences. As node A does not receive the data correctly, node A may draw a conclusion that node B has not forwarded the data, which is apparently a false alarm. Suppose that the signal-to-noise ratio threshold of the wireless device is β. According to equation (2), node C can receive data from node B successfully, while node A cannot receive it if
By analyzing, it can be noticed that the main drawback of watchdog is that a quite communication model is used without considering signal-to-noise ratio at the initiator and the receiver. If the signal-to-noise ratio at the initiator is greater than that at the receiver, the detection accuracy is greatly improved because the false alarm is reduced. Of course, it is impossible to guarantee that the initiator is always closer to the target in a randomly deployed WSN. The enhanced watchdog (E-watchdog) proposed in this article invites one or more neighboring nodes of the initiator that are closer to the target to detect SFA, which can detect SFA node accurately.
While receiving data from node B, in the case that the signal-to-noise ratio at node A is greater than or equal to that at node C, node A can detect SFA by itself. Otherwise, in the case that the signal-to-noise ratio at node A is less than that at node C, node A invites one or more agents, whose signal-to-noise ratio is greater than or equal to that of node C. In Figure 2, node G is selected as detect agent because it has stronger signal-to-noise ratio than node C. Stronger signal-to-noise ratio means higher data reception possibility, which improves accuracy of SFA detection.
In another attack scenario, after receiving the forwarding request, node B does not discard the data directly, but adopts an approach which jeopardizes media access control schemes at data link layer. As we known, the most widely used media access control scheme is carrier-sense multiple access with collision avoidance (CSMA/CA). Under CSMA/CA, in order to avoid collisions among nodes, a node performs channel listening before transmitting. If there is a neighboring node transmitting, the transmission is postponed. In the attack scenario, when node B detects that node C is transmitting, it forwards the data to node C. As illustrated in Figure 2, it is assumed that node H is selected as the detect agent. From the perspective of the agent, node B performs forwarding requested by node A. But actually, as node C is transmitting, it cannot correctly receive the data from node B. 9 Such SFA is much more difficult to be detected. We call it a hidden SFA (HSFA).
In fact, we find that detect agent node H cannot detect the HSFA. But node G can detect it. The reason is that node G is located within the communication range of both node B and node C. Therefore, node G can detect whether the node B violates the medium access control (MAC) scheme. If node B sends data to node C while node C is transmitting, node B must be an HSFA node. As illustrated in Figure 2, all nodes in Candidate Area I can detect HSFA, which is characterized by G ∈ {
Details of E-watchdog
The E-watchdog proposed in this article is based on the real signal-to-noise ratio communication model, which can detect SFA accurately in WSN. Based on the example in Figure 2, the detailed description is as follows.

Simulation results
NS-2 (Network Simulator) is used to simulate the performance of E-watchdog as compared to that of watchdog scheme. Simulation parameters are listed in Table 1.
Simulation parameters.

BER: bit error rate.
The first simulation is to evaluate the ability of the E-Watchdog to detect SFA nodes with asymmetric communications channel for static deployed WSN. We adopt deliver rate to evaluate the performance of WSN. In this simulation, the network consists of 100 nodes, and 5 of the 100 nodes are randomly selected as the source node, and the sink node is also randomly selected; 20% of the communication links are randomly selected as asymmetric; 10%–15% of the propagation loss is added in a certain direction of these links, to form asymmetric links. Randomly selected nodes are configured to be SFA nodes, which discard 10% of the forwarded packets.
Figure 3 shows the simulation results of the impact of SFA on network performance. The watchdog scheme detects with a great deal of false alarms because of asymmetric links. As the number of SFA nodes increases, the packet delivery rate of the network decreases. As to E-watchdog, the accuracy of SFA detection keeps high even if more asymmetric links are introduced in the network. The packets delivery rate of the network is less affected by the SFA, because SFA nodes are detected and deleted from the forwarding path. We have conducted the simulations for 20 times for different random topologies. As compared to watchdog, the false alarm of the E-watchdog is reduced by 25%, and the networks throughput is increased by 10%.
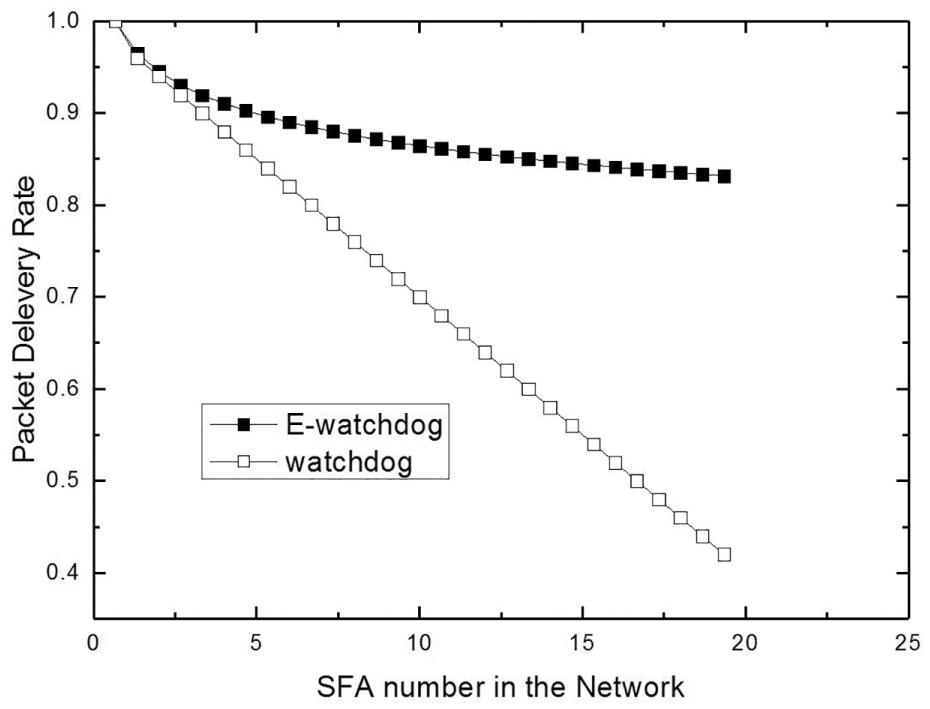
Performance of E-watchdog to detect SFA with asymmetric communication channel.
To analyze the impact of topology change on network performance, the second simulation compares network performance changes at different node movement speeds. Of course, most of WSNs are static deployed. But the topologies of static WSNs are actually changing because of node adding and removing. Mobile node is a simplified approach to evaluating the network performance of WSN with dynamic topologies. Node adding and removing make the detection of SFA becomes even complex, because removed node or disabled node in the network may be detected as SFA node; 100 nodes are deployed in the simulation. Five source nodes are randomly selected and 10 SFA nodes are deployed randomly in the network. Random Way Point motion model is used for mobility model. The mobile node randomly selects a direction and moves along that direction with a preset speed Vt for a random time. After that, another random direction and time is selected. Each node repeats this until the end of simulation.
Figure 4 shows the packet delivery rate at different movement speeds. In E-watchdog, as the initiator, agent, or the target moves, the signal-to-noise ratio is also changed. The initiator and the detect agent require communications to exchange the information about that. Therefore, as MreqI, MrepI, MresI, and MresII are used for communication, the faster node moves, and more communication is required to reflect real-time channel situations. From the simulation results, it can be found that when the moving speed of the node is less than 21 m/s, the network delivery rate of the E-watchdog is higher than that of the watchdog, but when the moving speed of the node is greater than 21 m/s, the network performance under the E-watchdog becomes lower than that of watchdog. However, in a static deployed WSN, topology changes introduced by node adding and removing are much slower. E-watchdog is more efficient than watchdog scheme.

Impact of topology changes to network performance.
To evaluate the power consumption of E-watchdog, another simulation is conducted. A total of 100 nodes are randomly deployed, and 1 sink node is configured; 5 nodes are configured as source node and 10 nodes are configured as SFA nodes. To select appropriate agents and receive reports from the agents, E-watchdog introduces additional communication overheads. For event triggered monitoring applications, all communications among nodes serve for event reporting. Therefore, we use the packets per event (PPE) as a metric to evaluate the power consumption. PPE is a reasonable metric because the final goal of all communications is to report the events to the sink node reliably and efficiently. As we know, communication consumes more than 80% battery power of a WSN node. 10 As compared to communication, power consumptions for computation and sensing are much less. Most WSNs adopt no power control schemes. Fixed transmission power is used, which means the total power consumption is in proportion to packets count. Therefore, the average PPE can be used as a metric for the overall power consumption of a specific scheme.
As illustrated in Figure 5, the simulations are conducted for 140 min. And 20 different random topologies are used for evaluation. The average PPE of watchdog and E-watchdog is shown. As we can see, the PPE of watchdog and E-watchdog are much higher at the beginning and decrease for longer simulations. The reason is that there are many initializations at different levels for WSN nodes, which require communication among nodes in WSN. For example, the initialization of protocol at network layer requires many network-wide broadcasting. After initialization, only necessary forwarding and beacon broadcasting are required. Therefore, the PPE decreased to 7.3. This means that about seven transmissions are required to forward the event packet from the source node to the sink node. As compared to that of watchdog, the PPE of E-watchdog is higher at the beginning. The reason is that E-watchdog introduces additional communication overheads to find appropriate agents and to receive reports from the agents. As the network runs for a longer time, the PPE of E-watchdog reduces to the level of watchdog.

Packets per event under E-watchdog.
Finally, we simulate the network performance in the presence of joint spoofing. The watchdog relies entirely on the initiator to detect SFA, thus there is no case of joint spoofing. But E-watchdog relies on the detect agents to detect SFA. The detect agents may generate fake reports, which is a joint spoofing. Figure 6 shows the change in the delivery rate of packets in the case of different numbers of neighboring nodes. It can be found that when the density of network nodes is large (5.5 neighboring nodes per node), joint spoofing has less impact on the network performance. This is because election algorithm can effectively filter out fake reports from normal ones.

Performance of WSN with joint spoofing.
Conclusion
The SFA in the WSN introduces decreased network performance. Effective detection and isolation of SFA is very important, and accurate and efficient SFA detection is fundamental for SFA node isolation. The E-watchdog proposed in this article is an SFA detection scheme based on real-world signal-to-noise ratio communication model, which can detect SFA accurately. Simulation results show that the proposed scheme achieves accuracy with the expense of minimal energy expense.
Footnotes
Handling Editor: Shancang Li
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work is supported by Research Foundation of the Department of Education of Shaaxi Province under Grant No. 16JK1706.