Abstract
The bit error in quantum communication is mainly caused by eavesdropping and noise. However, most quantum communication protocols only take eavesdropping into consideration and ignore the result of noise, making the inaccuracy situations in detecting the eavesdropper. To analyze the security of the quantum E91 protocol presented by Ekert in collective-rotation noise channel, an excellent model of noise analysis is proposed. The increment of the qubits error rate (ber) is used to detect eavesdropping. In our analysis, eavesdropper (Eve) can maximally get about 50% of the key from the communication when the noise level approximates to 0.5. The results show that in the collective-rotation noise environment, E91 protocol is secure and the raw key is available just as we have knew and proved. We also presented a new idea in analyzing the protocol security in noise channel.
Keywords
Introduction
Cryptography is the basis of information security; the task of cryptograph is to ensure that only the legitimate users like Alice and Bob can read the secret message in the secure communication, which the unauthorized users like Eve cannot read. In Cryptography, the secret message is generated by the key and should not be read without the key. In 1926, Vernam 1 presented the one-time pad (OTP). In 1949, Shannon 2 proved that the OTP is perfectly secure with equal length of key and plain text. But there is still a serious problem on how to distribute the key safely.3–5
Different from the classical secure communication protocol, quantum secure communication (QSC) protocol is based on the fundamental laws of quantum physics rather than the complexity of computing. So QSC has much higher performance of security. Quantum communication and quantum cryptography mainly include quantum key distribution (QKD),6–8 quantum teleportation (QT),9,10 quantum secret sharing (QSS),11,12 quantum secure direct communication (QSDC),13–15 and so on. In 1984, CH Bennett and Brassard 16 presented the first QKD protocol, which is called the BB84 protocol. The BB84 protocol uses four quantum single particle state and avoids using quantum entangled states and storing quantum particles, making it easy to operate. Later in 1991, Ekert 17 proposed that QKD be implemented using the quantum entangled states explored in the Einstein-Podolsky-Rosen (EPR) thought experiment, which is called the E91 protocol.
Compared with the BB84 protocol which Alice sends quantum particles to Bob, the E91 protocol uses an EPR pair during the communication, which divides the EPR pair and sends one particle to Alice and Bob separately. As we know, it is a difficult problem to keep EPR entangled. In other words, the E91 protocol is more difficult to application than the BB84 protocol. But there is a center source that sends one of the EPR particles to Alice and Bob, respectively, with the E91 protocol. Which is similar to the classical cryptographic protocol structure. The E91 has received lots of attention since its inception.18–22
However, those protocols and analyses almost only take the eavesdropping into consideration and ignore the result of noise which cannot be neglected in practice. For application in the real environment, we must take the noise into account.
With the model of collective-rotation noise, the effect of noise can be described as a sine
Related works
The E91 protocol
Let us give a brief introduction of the quantum E91 protocol. There are two groups of measurement basis:
The source center
Alice and Bob randomly choose
Alice and Bob know the choice of both parties. They divide the measurement result into two groups: one is the decoy qubits
The group
If the quantum channel is safe,
The E91 protocol ends successfully.
The noise in E91 protocol
An explanation should be stated that in the noisy environment, the noise and eavesdropping cannot be distinguished between each other. The qubits error rate
The
In the process of quantum communication, the bit error rate only caused by noise can be seen as
The original E91 protocol uses the decoy group
The level of collective-rotation noise
During the process of analyzing the security conveniently, an assumption can be reasonably proposed that the environmental noise is constant. Even if actually noise is variable, the maximum or average value of the noise can still be conducted. To ensure the security of the E91 protocol, we should take the maximum value into account.
The noise will produce the same effect on every particle in an ideal collective-rotation noise environment. The effect is making every particle left or right deflect
Under the effect of collective-rotation noise, the quantum states become
When there is no noise,
Once the level of noise
Our target is to find the relationship between the bit error rate
The security analysis of E91 protocol in the noise environment
The analysis without eavesdropping
In the security analysis of E91 protocol, we ignore the decoy group and only discuss the raw key group. Alice and Bob randomly receive the qubit
According the formulas (2)–(5), we can easily calculate the probability when
The result of Alice’s measurement.
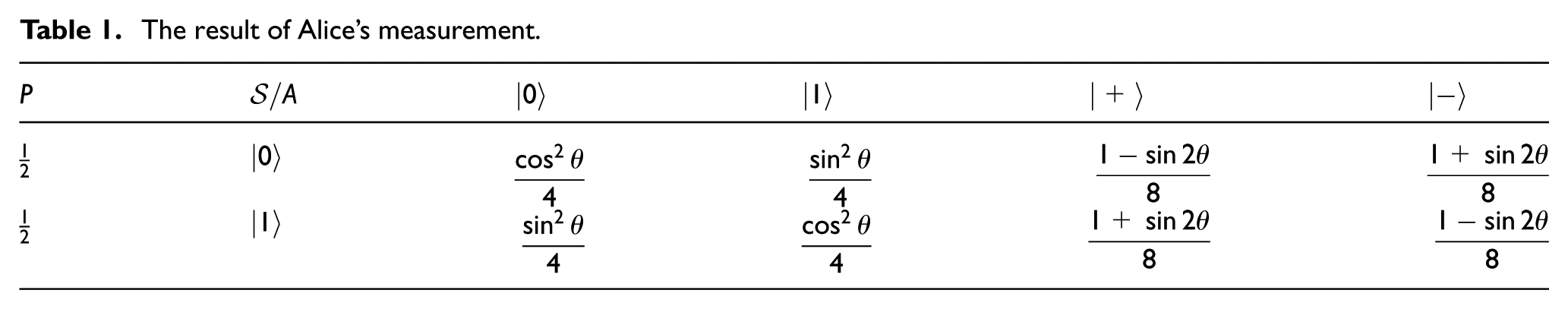
Let us analyze the situation that the source center

That is to say, when there is no eavesdropping, the bit error rate

The information that Eve can get
Before we analyze how much bit error rate is caused by eavesdropping, let us analyze how much information that Eve can get.
According to Deng et al., 28 the maximal amount of the information that Eve can eavesdrop from Alice is given

The qubit is sent randomly by Alice, so H(A) = 1 and

According to Table 1 and formulas (6), (8), and (9). To make it easy to express, let
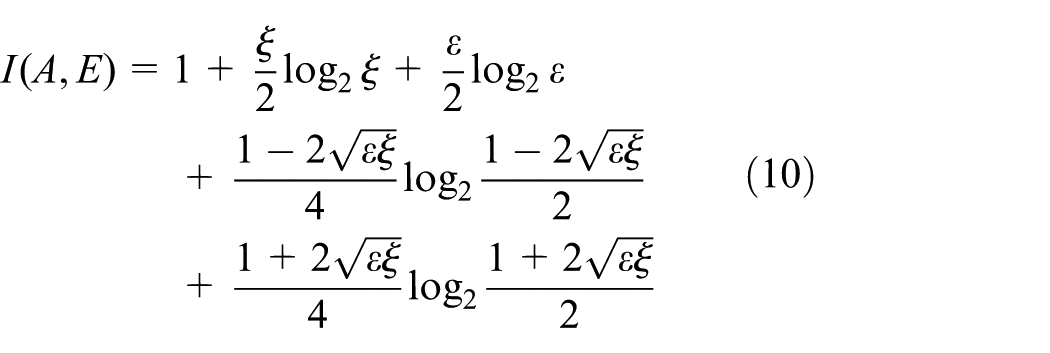
Formula 10 shows that
The analysis with eavesdropping
Just as Figure 1 shows, as we know, Eve will intercept the qubits, take a measurement, and reprepare them to Alice. The quantum state that Eve receives is one of

Eve intercepts and resends qubits.
The result of Alice’s measurement.

According to Tables 1 and 2, Alice and Bob always choose the same measurement basis; the probability that
Alice’s and Bob’s measurement result.

From Table 3, it can be seen that when Alice’s measurement is different from Bob’s measurement, there is a bit error. We only need to calculate the value of
Alice gets
Alice gets
Alice gets
Alice gets
And so is

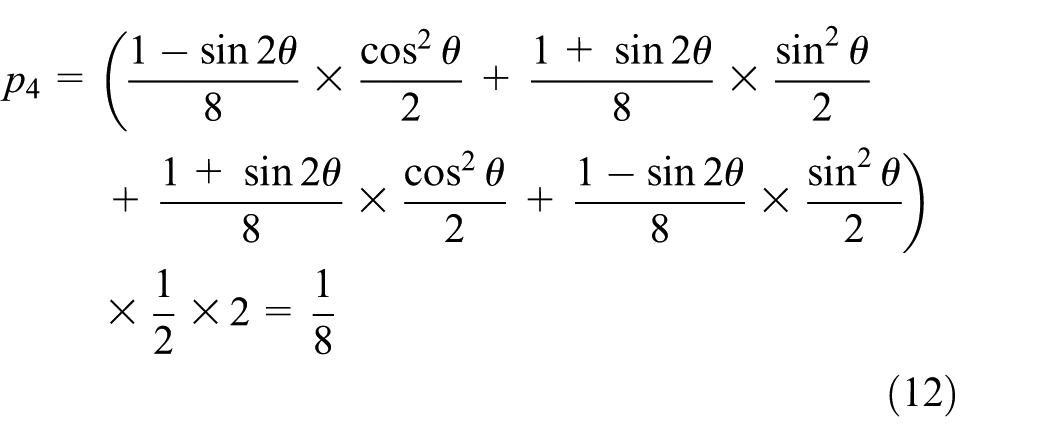
So the bit error rate caused by both eavesdropping and noise can be easily calculated

Figure 2 shows the relationship between the bit error rate caused by both eavesdropping and noise

The relationship between
From Figure 2, it can be seen that when
Let us define

It is easy to find that
Now, let us analyze how much information that Eve can get from her eavesdropping. The maximal and minimal information

The relationship between
As it shown in Figure 3, the minimum of information that Eve can get is
From Figure 3, Eve can most get only 50% information, since each qubits’ transmission is mutual independence; Eve can only get randomly 50% raw keys, but she does not know which parts she has gotten. This means that Eve cannot read the secret message with the raw keys she have obtained, and the quantum E91 protocol has been proven to be safe.
Conclusion
In this article, we have analyzed the relationship between the bit error rate
From Figure 2, it can be concluded that the quantum E91 protocol is safe when
From Figure 3, it can be concluded that the maximal information Eve can get is
In conclusion, the QKD protocol named E91’s security has been analyzed. When the level of noise
Footnotes
Handling Editor: Posco Fung Po Tso
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work is supported by the National Natural Science Foundation of China (grant nos U1636106, 61472048, and 61572053).





