Abstract
The age of Internet of things gives rise to more challenges to various secure demands when designing the protocols, such as object identification and tracking, and privacy control. In many of the current protocols, a malicious server may cheat users as if it was a legal server, making it vital to verify the legality of both users and servers with the help of a trusted third-party, such as a registration center. Li et al. proposed an authentication protocol based on dynamic identity for multi-server environment, which is still susceptible to password-guessing attack, eavesdropping attack, masquerade attack, and insider attack etc. Besides, their protocol does not provide the anonymity of users, which is an essential request to protect users’ privacy. In this article, we present an improved authentication protocol, depending on the registration center in multi-server environments to remedy these security flaws. Different from the previous protocols, registration center in our proposed protocol is one of parties in authentication phase to verify the legality of the users and the servers, thus can effectively avoid the server spoofing attack. Our protocol only uses nonce, exclusive-OR operation, and one-way hash function in its implementation. Formal analysis has been performed using the Burrows–Abadi–Needham logic to show its security.
Introduction
In the past decades, great research efforts have been made on Internet of things (IoT), and a wide range of application scenarios, such as object identification and tracking, healthcare, privacy control, and military.1–4 Along with the convenience they bring security issues of personal privacy in terms of the constant, and transparent leakage of private information may also arise. End-devices like smart cards often carry a certain level of infrastructure equivalent to a tiny computer, including the computation power, storage functionality, and communications, which make the mutual authentication and key agreement protocol possible. They can prevent unauthorized users from gaining access to sensitive resources and prevent legitimate users from accessing resources in an unauthorized manner.
Since Lamport 5 proposed the first password-based authentication protocol, great efforts have been made on the authentication to improve the security. Password-based authentication is simple, but it needs to maintain the verification table and leads to table disclosure or password compromising. Hwang and Li 6 presented a new remote user authentication protocol with the help of smart cards based on the protocol proposed by ElGamal. 7 In their schemes, the servers do not need to keep any verification table. Since then, kinds of smart card–based authentication protocols with hash function have been presented.8–12 Traditional password-based or smart card–based authentication protocols are adapted in single-server environments and are not suitable for the multi-server environments. To overcome these weaknesses, many protocols for multi-server environment have been devised.13–16 They can implement mutual authentication with one registration. However, we find that they are still susceptible to replay attack, impersonation attack, password-guessing attack, and so on. To remedy these flaws, enhance security, and reduce the computational complexity, we propose an improved dynamic identity (ID) based on authentication protocol for multi-server architecture. This protocol not only achieves user’s anonymity and resists various kinds of attacks, but also finishes the mutual authentication and session key agreement.
The rest of the article is organized as follows. In section “Related work and discussion,” we provide a brief review of related protocols and analyze their securities. Then, we present an improved authentication protocol for the multi-server environment in section “The proposed protocol.” The correctness of the proposed protocol is verified by performing formal verification with the Burrows–Abadi–Needham (BAN) logic in section “Analysis of correctness.” Section “Security analysis of the improved protocol” evaluates the security of our proposed protocol. Section “Cost and functionality analysis” analyzes the costs and functionalities among ours and other protocols. Finally, we present the conclusion in section “Conclusion.”
Related work and discussion
In the lectures, Liao and Wang 17 presented a secure user authentication protocol for multi-server architectures based on dynamic ID. However, Hsiang et al. claimed that Liao et al.’s protocol not only failed to achieve mutual authentication but also could not withstand server spoofing attack, insider attack, masquerade attack, and so on. Moreover, Lee et al. 18 proposed an improved remote user authentication scheme based on dynamic ID, but their protocol is still vulnerable to server spoofing attack and forgery attack. Hsiang et al. presented a new authentication protocol. 19 They claimed that their protocol efficiently protects the identity of the user and can resist various known attacks. Unfortunately, Sood et al. 20 stated that Hsiang et al.’s scheme cannot withstand stolen smart card attack, replay attack, and impersonation attack. Besides, the password change method of Hsiang et al.’s scheme is incorrect. In order to overcome these security weaknesses, Sood et al. presented an improved authentication protocol. 20 They declared that their proposed protocol can help the servers and the registration center validate the user’s identity successfully and can also keep the dynamic ID of users in communication channel. Sood et al. argued that their scheme can withstand various known attacks, such as impersonation attack, offline dictionary attack, and replay attack. However, Li et al. 21 found that Sood et al.’s scheme cannot withstand stolen smart card attack and leak-of-verifier attack. Furthermore, Li et al. presented an efficient and secure dynamic ID–based authentication scheme. 21 Unfortunately, Li et al.’s protocol was soon identified to be susceptible to password-guessing attack and masquerade attack by Han. 22 In addition, Xue et al. 23 claimed that Li et al.’s protocol is susceptible to insider attack, eavesdropping attack, masquerade attack, and so on. Moreover, Wang et al. 24 uncovered two other vulnerabilities: offline password-guessing attack and no provision of user’s anonymity. In recent years, many researchers also studied group data sharing via cloud storage or new preserving encryption model in cloud environments.25–27
Review of Li et al.’s protocol
In this section, we mainly review the authentication protocol presented by Li et al.
21
This protocol consists of three parties: the user
Notations.

Registration phase
Step 1:
Step 2: Upon receiving
Step 3:
Login phase
Step 1: When
Step 2: After local verification, the smart card generates a random number
Authentication and session key agreement phase
Step 1: Upon receiving the login request from the user,
Step 2: Once
Step 3:
Step 4:
Step 5: On receiving the mutual authentication message,
Step 6: Upon receiving messages from
Finally,
Password change phase
When
Cryptanalysis of Li et al.’s protocol
Li et al. stated that their protocol could resist kinds of security attacks; however, we find that their protocol is still vulnerable to many attacks, such as insider attack, smart card forgery attack, eavesdropping attack, masquerade attack, and offline password-guessing attack, which are detailed as the following.
Insider attack
If an adversary is a malicious legal user, he or she is able to extract
Smart card forgery attack
For Li et al.’s scheme is lack of
If the attacker makes use of the fabricated smart card to get services from


In Li et al.’s scheme, these messages can be verified by
Eavesdropping attack
As a malicious legal user, he or she can use his or her own smart card to attain
Masquerade attack
From the eavesdropping attack mentioned above, the adversary obtains a legal user
First, the adversary chooses a random number

Then,
Server-spoofing attack
First, a malicious attacker intercepts the messages
Unfortunately,
User’s anonymity
A malicious server
Offline password-guessing attack
If the smart card of a legal user
The proposed protocol
This proposed protocol also consists of four phases. In the protocol, the server has only one private key, which can effectively resist server spoofing attack. The mutual authentication among user, server, and registration center can achieve multiple security goals.
Registration phase
If a user wants to get services from servers, he or she shall register in
Step 1:
Step 2: Upon receiving
Step 3: Upon receiving the smart card,
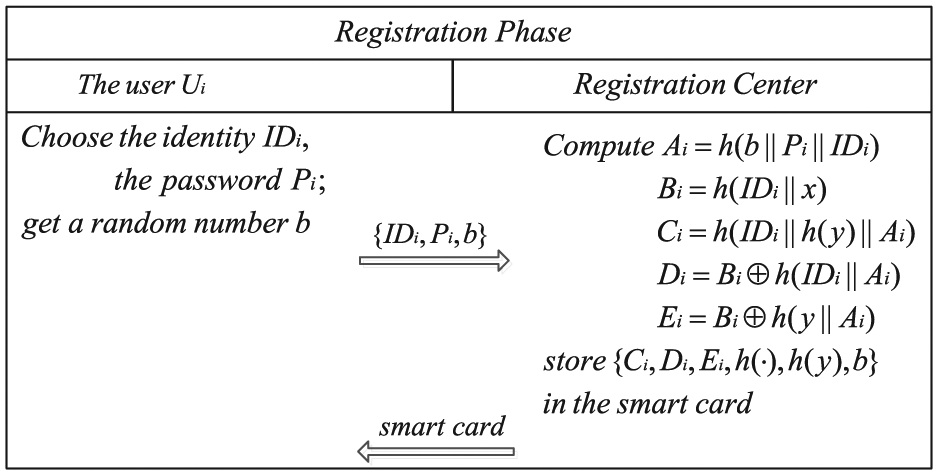
Registration phase of the improved protocol.
Login phase
In the phase,
Step 1: When
Step 2: After local verification, the smart card generates a random number
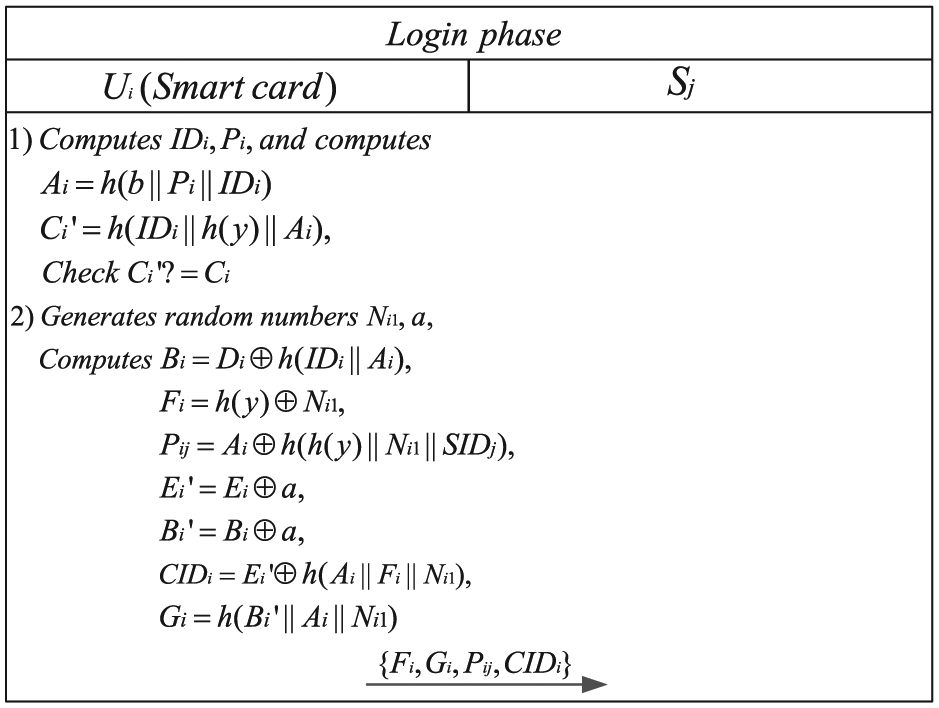
Login phase of the improved protocol.
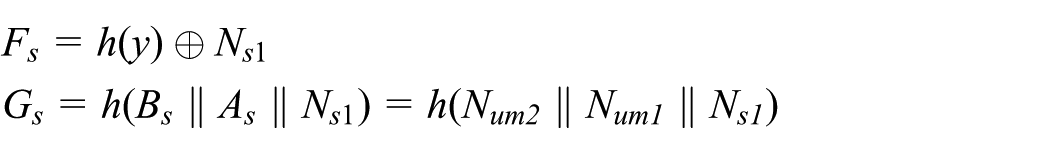
Authentication and session key generation phase
Step 1: Upon receiving the login request from the user,
Step 2: Once
Step 3:
Step 4:

Then
Step 5: Once
Step 6: Upon receiving the message from

Authentication phase of the improved protocol.
Password change phase
Analysis of correctness
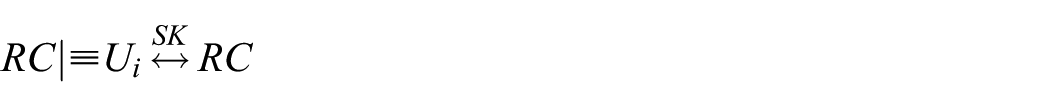
First of all, we can prove the correctness of the protocol using the BAN logic.
28
Through specific logic analysis, it can be proved that the protocol can not only achieve session key agreement among users, servers, and
BAN logic notation
The notations for BAN logic are listed as the following. 29
BAN logical postulates
To prove feasibility and correctness of the protocol, the BAN logic needs to set some special rules to complete the authentication protocol analysis and reasoning. The rules used in the article are as follows.
R1: Message-meaning rule

If
R2: Nonce-verification rule

If
R3: Jurisdiction rule

If
R4: Freshness rule

If
Logic premises
Based on the aforementioned, we can obtain the initiative premises as below
















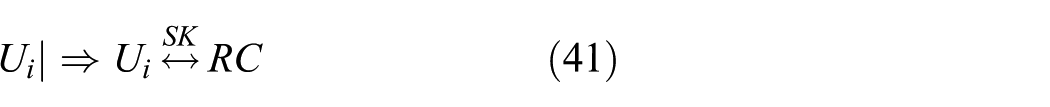
Correctness analysis using BAN logic
In this protocol, three messages are used to achieve key agreements and mutual authentications. The first one is sent to
Message1

Message2

Message3:
The basic believes are as follows.
A1.
A2.
A3.
A4.
A5.
A6.
A7.
A8.
A9.
A10.
A11.
A12.
A13.
A14.
A15.
A16.
A17.
A18.
A19.
A20.
A21.
A22.
Based on the above assumptions, the agreement can be converted to BAN logic in specific patterns. The specific logic proved as follows:

Formula 1 can be disassembled






Based on A6, equation (2), and R2, we can obtain

Based on A7, equation (9), and R2, we can obtain

Based on A6, equation (3), and R2, we can obtain

Based on A7, equation (11), and R2, we can obtain

Based on A6, equation (4), and R2, we can obtain

Based on A7, equation (13), and R2, we can obtain

Based on A6, equation (5), and R2, we can obtain

Based on A7, equation (15), and R2, we can obtain

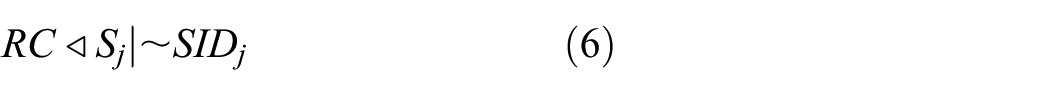
Based on A16, equation (6), and R2, we can obtain
Based on A15, equation (7), and R2, we can obtain
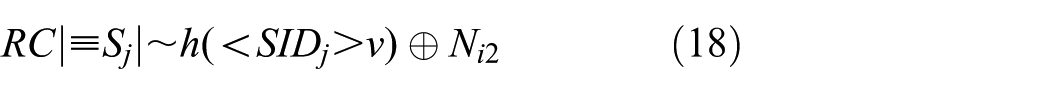
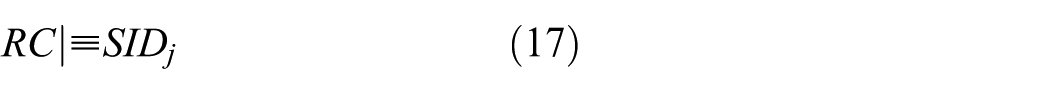
Based on A13, equation (18), and R1, we can obtain

Based on A15, equation (8), and R2, we can obtain

Based on A13, equation (20), and R1, we can obtain

Then

and they can be converted as




Based on A10, A11, equation (23), and R2, we can obtain

Based on A9, equation (27), and R1, we can obtain

Based on A9, equation (24), and R1, we can obtain
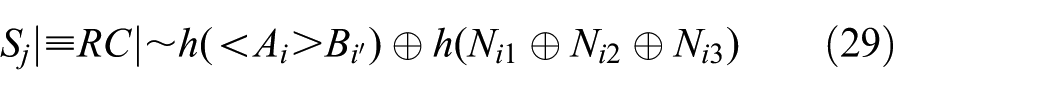
Based on A10, A11, equation (29), and R2, we can obtain
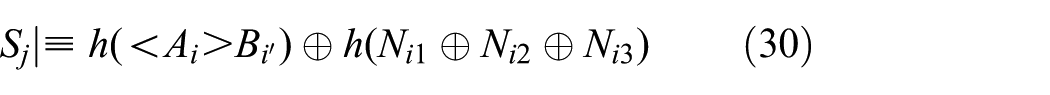
Based on A9, equation (25), and R1, we can obtain

Based on A10, A11, equation (31), and R2, we can obtain

Based on A10, A11, equation (26), and R2, we can obtain

Based on A9, equation (33), and R1, we can obtain

Finally,

Then they can be converted as


Based on A3, equation (33), and R2, we can obtain
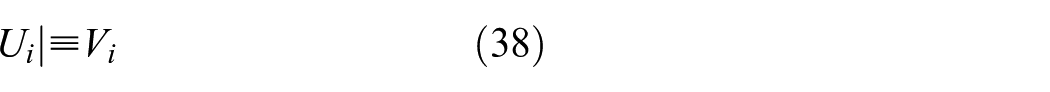
Based on A3, equation (34), and R2, we can obtain
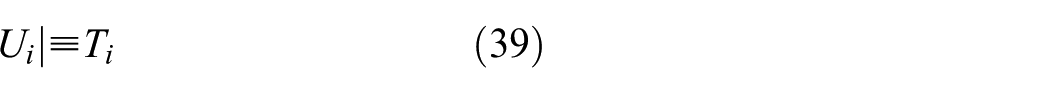
Finally, based on R2, it can be proved that
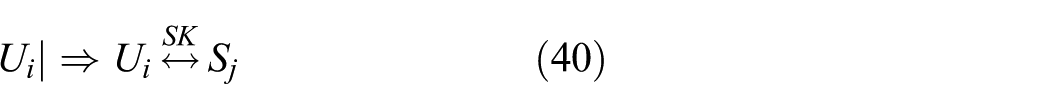


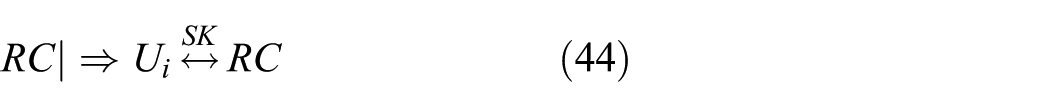
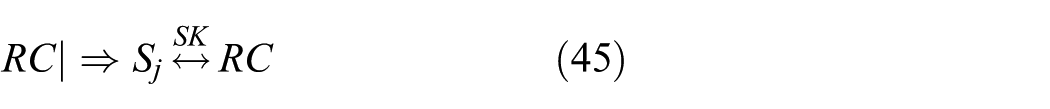
Hence, the improved protocol can achieve mutual authentication among the user, the server and
Security analysis of the improved protocol
Compared with other related protocols, our protocol can resist much more attacks illuminate as the following.
Leak of verifier attack
Different from some other protocols, registration center is involved in the authentication, and session key agreement phase. There is no verification table in both the registration center and the servers in our protocol, so it can avoid leak of verifier attack.
User’s anonymity
When
Insider attack
After registering in
Eavesdropping attack
Even if the adversary intercepts the message {
Masquerade attack
Even though a malicious user can extract
Offline password-guessing attack
When a malicious legal user intercepts the login message {
Stolen smart card attack
If a user’s smart card is lost or stolen, the adversary is able to extract the parameters stored in the smart card. Unfortunately, the adversary does not know the user’s
Cost and functionality analysis
In this section, we evaluate the computational costs and functionality of our proposed protocol and compare it with some related authentication protocols for multi-server environment. To analyze the computational complexity, let
Cost comparisons of our protocol and other related protocols.

Functionality comparisons of our protocol and other related protocols.

Conclusion
In this article, we investigate Li et al.’s dynamic ID–based authentication protocol for multi-server architecture and show that Li et al.’s protocol is susceptible to certain security issues including insider attack, stolen smart card attack, eavesdropping attack, masquerade attack, no provision of user’s anonymity, and password-guessing attack. In order to address these issues, we propose an improved authentication protocol based on dynamic ID, and it is dependent on registration center for multi-server environments. Compared with other related schemes, our protocol remedies the secure flaws existing in Li et al.’s protocol with a minor increase in computational complexity. In addition, we provide the correctness analysis by using BAN logic.
Footnotes
Handling Editor: Gary Leavens
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported in part by the Natural Science Foundation of China under grants 61472229 and 61701284, in part by project funded by the China Postdoctoral Science Foundation (2016M592216) and Qingdao Postdoctoral Research Project (2016125).
