Abstract
When monitoring the environment with wireless sensor networks, the data sensed by the nodes within event backbone regions can adequately represent the events. As a result, identifying event backbone regions is a key issue for wireless sensor networks. With this aim, we propose a distributed and morphological operation-based data collection algorithm. Inspired by the use of morphological erosion and dilation on binary images, the proposed distributed and morphological operation-based data collection algorithm calculates the structuring neighbors of each node based on the structuring element, and it produces an event-monitoring map of structuring neighbors with less cost and then determines whether to erode or not. The remaining nodes that are not eroded become the event backbone nodes and send their sensing data. Moreover, according to the event backbone regions, the sink can approximately recover the complete event regions by the dilation operation. The algorithm analysis and experimental results show that the proposed algorithm can lead to lower overhead, decrease the amount of transmitted data, prolong the network lifetime, and rapidly recover event regions.
Introduction
With the development of low-power wireless communication, microsensors, microprocessors, embedded computing, and distributed information collecting and processing, wireless sensor networks (WSNs) have been widely used in many fields. WSNs sense the environment via a large number of inexpensive and tiny wireless sensor nodes. They are characterized by limited communicating and computing resources, un- or hard-rechargeable power, and other features. Limited node energy is one of the key constraints for applications in WSNs. 1
The energy consumption in wireless sensor nodes consists of three parts: sensing, computing, and communicating. The energy spent on communication accounts for the largest expenditure and depends on the transmission of data and control messages. Thus, decreasing in-network data volumes is an effective method of conserving energy. Currently, many researchers design data compression or fusion mechanisms, mine in-network data correlation, and investigate the methods for building aggregation routing trees that facilitate data aggregation to decrease the in-network data.2–35
For in-network data transmissions, sensing data from nodes within event border regions is not sufficiently precise and fluctuate, and the sensing data from nodes within event backbone regions can determine the event information. In addition, data sensed by nodes in event backbone regions are highly correlated, whereas the sensing data from event border regions are poorly correlated. As a result, event backbone regions are more effective for aggregating data than whole event regions, and they present higher data aggregation efficiency and better data reconstruction accuracy. Although important information can be obtained from event border regions, the probability is small. Statistically, information in event backbone regions is important and well correlated. Under limited power conditions, energy should be saved as much as possible. Based on the discussion above, a method of determining the event backbone regions must be developed to facilitate decrease in data size. Although current methods associated with decreases of in-network data can save energy, they may not consider the advantages obtained from event backbone regions or provide a method of determining event backbone regions.
To address this issue, we incorporate the erosion and dilation of binary images to WSNs and propose a distributed and morphological operation-based data collection algorithm (DMOA). The major contributions of this article are threefold: (1) the DMOA can extract event backbone regions effectively to decrease in-network data transmission, and it can recover event regions quickly by simple morphological operations; (2) the DMOA provides a low overhead strategy for event information exchange; and (3) experimental analyses indicated that our proposed method can be combined with other energy saving strategies to improve energy conservation.
The remainder of this article is organized as follows: section “Related works” introduces the current energy-saving algorithms on in-network data in WSNs, section “Background and motivation” presents the background knowledge and our research motivation, section “Proposed algorithm” details the DMOA, section “Theoretical analysis and experiments” analyzes the algorithm and verifies it by simulation, and section “Conclusion” concludes the article.
Related works
The techniques for energy conservation represent essential research with regard to WSNs, and developing methods of decreasing in-network data transmission is always a hotspot problem. The volume and manner of decreasing data will directly affect the performance of the WSNs. In recent years, many experts have conducted studies on various strategies associated with decreasing data.
Routing for data aggregation, compression, and fusion is very effective to decrease in-network data transmission.2–15 In the shortest path tree (SPT), 2 each source sends its information to the sink along the shortest path between the two and overlapping paths are combined to form an aggregation tree. Energy efficient cluster-based data aggregation (ECBDA) 3 divides the monitoring region into multiple layers, forms K clusters for each layer according to the node residual energy and communication cost, fuses data in clusters, and routes data by efficient route discovery. Dynamic and scalable tree (DST) 4 and dynamic and scalable tree aware of spatial correlation (YEAST) 5 are algorithms for event-driven WSNs, and they can build routing trees with high fusion efficiency based on events. The load balanced data aggregation tree (LBDAT) can construct a load-balanced data aggregation tree based on a probability network model by solving maximum independent sets. 6 Sutagundar and Manvi 7 used multi-agent technology to construct the fishbone structure of the whole network, which can aggregate the data in parallel. Wan et al. 8 work on constructing data aggregation trees to minimize the total energy cost of data transmission for large-scale WSNs. They divide query area and build trees within each sub-query area to reduce network hot spots, which can help prolong network lifetime. Liu et al. 9 design a polynomial time algorithm to determine the optimal transmission policy and the corresponding time slot for each node to transmit the aggregation data on an arbitrary tree. Nguyen et al. 10 studied the maximum lifetime data aggregation tree scheduling (MLDATS) problem and propose a local-tree-reconstruction-based scheduling algorithm (LTRBSA), which uses the local-tree reconstruction algorithm to find more virtual data aggregation trees. A lightweight, latency-aware routing for data compression (L2DC) scheme 11 facilitates data compression by determining each node to keep packets for compression locally or to send them out to be compressed in a distributed manner, and it can eliminate auxiliary redundant packet and select relay nodes to reduce packet latency. Aly et al.12–14 proposed a series of distributed data collection algorithms for large-scale WSNs, and these algorithms do not depend on the sensor network topology, routing tables, or geographic locations of sensor nodes. Subtree merging–based data collection (SMDC) is designed for area query applications, and it can prevent unnecessary energy consumption in ancestor nodes for routing through the union of disjoint sets for different subtrees. 15
In-network data compression, fusion, and scheduling are related to data decreasing directly.16–24 Multi-level aggregation (MLA) 16 utilizes Brownian motion to remove redundancies and processes data according to the entropy and wavelet based on clusters. Liu and Jhang 17 analyze the problem of data scheduling with minimum transmission cost and proposed a distributed data scheduling algorithm based on the theory of a dominating set. The adaptive data aggregation strategy using network coding (ADANC) 18 combines network coding and traditional data aggregation to improve the efficiency in the cluster-based, random, duty-cycled WSN regions. Li and Liang 19 present a generalized predictive coding framework for unified lossless and lossy data compression and design a corresponding lossless compression algorithm to improve data compression performance for various applications in WSNs. Sheltami et al. 20 study discrete cosine transform (DCT) and discrete wavelet transform (DWT) image-compression techniques as they can be implemented on sensor nodes and find DWT outperforms DCT in terms of peak-signal-to-noise, throughput, end-to-end delay, and battery lifetime, while DCT provides better compression ratio than DWT. Chen et al. 21 discover the DCT coefficients of sorted data become more concentrated and propose a data sorting–based adaptive spatial compression scheme (DS-ASCS) which includes a zigzag scan method and an adaptive spatial compression algorithm, gaining good performance on data compression. Alsheikh et al. 22 utilize compressing neural networks to compress data with bound guarantee and propose a rate-distortion balanced data compression algorithm. Wu et al. 23 propose a novel framework with dedicated combination of data prediction, compression, and recovery to simultaneously achieve accuracy and efficiency of the data processing in clustered WSNs. Kim et al. 24 propose an m-hop averaging compression algorithm which makes each node compress a certain amount of packets according to the average energy levels of the next m nodes within m hops.
Node selection and sleeping schemes can also help decrease the volume of in-network data transmission, saving energy significantly.25–35 Chen and Wassell 25 propose an active node selection framework for compressive sleeping WSNs, where the node selection problem is framed as the design of a specialized sensing matrix and solved as an optimization problem by a constrained convex relaxation plus a rounding scheme approximately. Cheng et al. 26 use the partially ordered tuple (data coverage range, residual energy) to find an initial active node set, calculate the correlated node set with minimum set size and maximum geometric mean of residual energy of each node, and finally, remove nodes based on correlated node sets to reduce the number of active nodes. For heterogeneous WSNs, Sandhya et al. 27 select the aggregator nodes periodically based on location, taking advantage of the energy heterogeneity of the sensor nodes. For sleep/wake-up scheduling, Ye and Zhang 28 make each node decide its own operation mode (sleep, listen, or transmission) autonomously in each time slot in a decentralized manner based on the reinforcement learning technique. Sleep-awake energy efficient distributed (SEED) clustering algorithm 29 divides the network sensing field into three energy regions and let same application base sensor nodes form sub-clusters to decrease the number of transmissions toward the base station. Wang and Wang 30 propose a dynamic node selection scheme based on genetic algorithms whose objective function for collaborative target tracking is constructed by the information utility and the remaining energy of sensor nodes. The scheme can optimize the tradeoff between the accuracy of tracking and the energy cost of nodes. Jiang et al. 31 propose an energy efficient node selection algorithm for bearings-only target tracking WSNs, in which the residual energy of a node is incorporated into the objective function of node selection. Feng et al. 32 design a novel spatial-correlated node selection strategy, which selects the node according to the residual energy and the spatial correlation of the nodes located at the different positions. Shi et al. 33 propose a centralized algorithm to determine the approximate minimum set of nodes based on the calculation of node redundancy degree and the partition of the target area. Group-based energy-conserving protocol (GECP) 34 divides the network into groups and selects only one active node in each group to maintain a connected backbone and minimizes the number of transitions between sleep and active states to minimize the transition energy and the leader election frequency. Nasridinov et al. 35 seem the aggregator node selection process as a top-k query problem and solve it using a modified sort-filter-skyline algorithm.
Background and motivation
Morphological operations
For a digital image, its pixel values can be regarded as a function of the pixel coordinates,
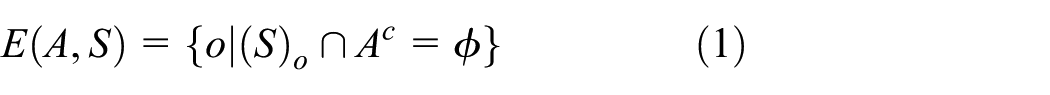
Morphological operations: (a) binary image with rectangle object (b) structuring element.
The basic concept of a mathematical morphology 36 is to measure and extract the corresponding shapes from an image using a structuring element for image analysis and recognition. The erosion and dilation operations are the basis of morphological image processing. The style of erosion and dilation on binary images and the changes in the images are controlled by structuring elements. A structuring element is a binary matrix image. For convenience, the structuring element can be displayed only by 1, and its origin must be marked as shown in Figure 1(b).
To erode and dilate binary images, the morphology defines two basic operators on binary images. Suppose that A is a binary image and S is a structuring element. The complement of A is
With the complement, reflection, and translation operators above, the erosion and dilation operators are defined as set operations based on the structuring element. The erosion of A by S, denoted as
The dilation of A by S, which is denoted as
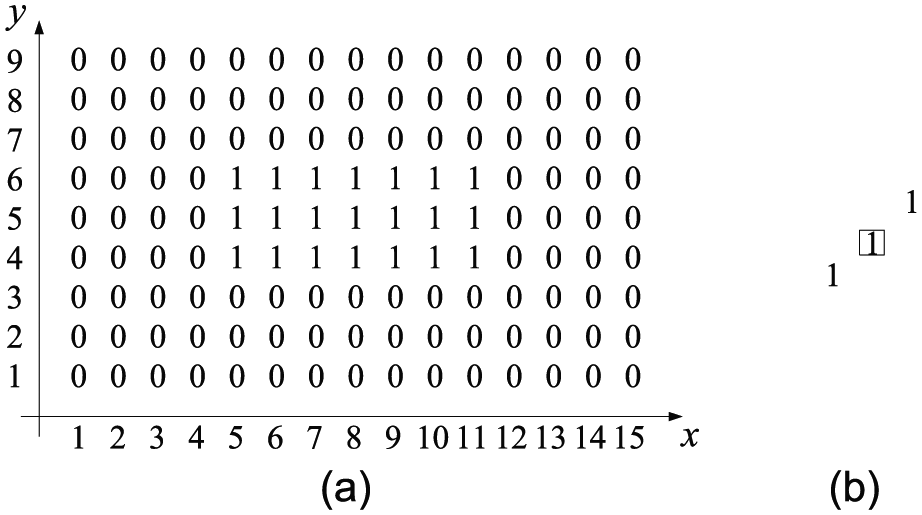
The rectangular object in Figure 1(a) is eroded and dilated using the structuring element in Figure 1(b), and the results are shown in Figure 2(a) and (b), respectively. For the object in Figure 1(a), Figure 2(a) depicts its backbone and Figure 2(b) shows the corresponding dilation. With different structuring elements, the style and level of erosion and dilation on binary images are different.
Illustrations of erosion and dilation: (a) erosion and (b) dilation.
Research motivation
Based on the above information, the erosion operation on a binary image can thin or shrink the objects within the images to obtain the backbone, and the dilation operation can thicken or expand the objects. The eroded binary image can be dilated to obtain an approximate original image.
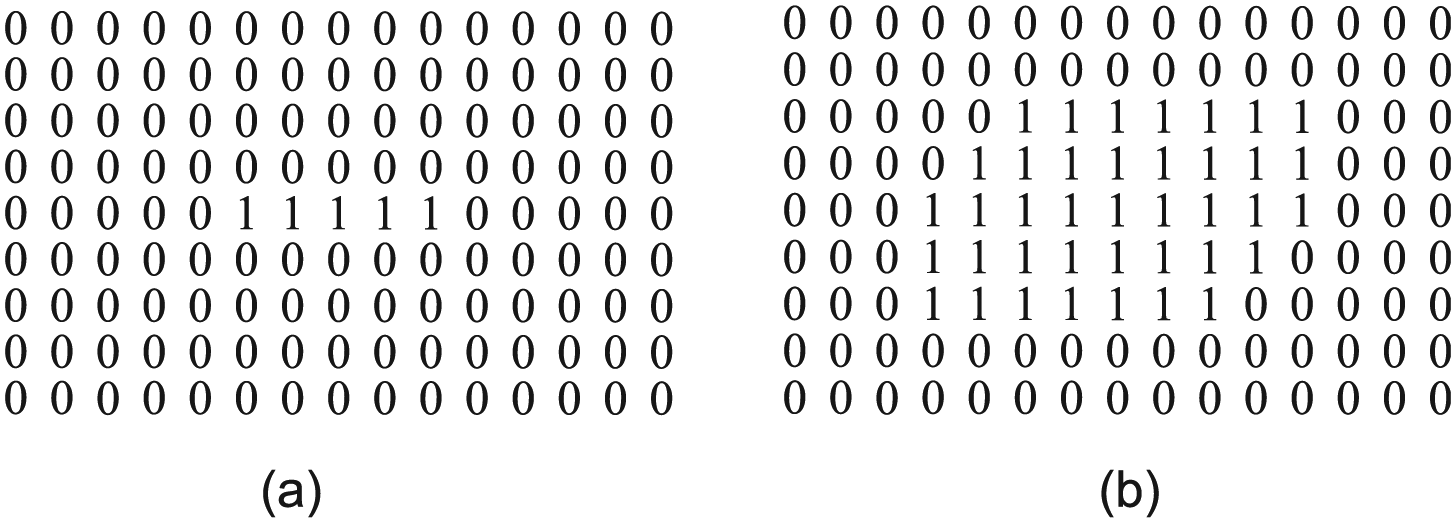
Suppose that
Demonstration of a uniform WSN: (a) WSN with nodes deployed uniformly and (b) event-monitoring status.
Therefore, we can introduce erosion and dilation operations to WSNs with nodes deployed uniformly. Event backbone regions can be extracted by the erosion operation on the nodes, and collecting data only from the nodes within the backbone regions can help reduce inaccurate data transmission and improve data aggregation. In addition, through the dilation operation on nodes, the whole event region can be approximately recovered according to its backbone. Because WSNs are limited by energy and require a quick response and scientific decision-making, a method of applying simple morphological operations to WSNs is valuable.
For WSNs with nodes deployed irregularly, a uniform network can be transformed by gridding technologies. 37 For example, we can utilize the existing technologies to partition the network into meshes, choose one active node for each grid and take the center of the grid as the node’s position, thereby producing an approximate uniform WSN. Therefore, in this article, we only discuss the strategies for uniform WSNs.
Proposed algorithm
This section details the algorithm DMOA. For uniform WSNs, the location of each node is identified by the coordinates
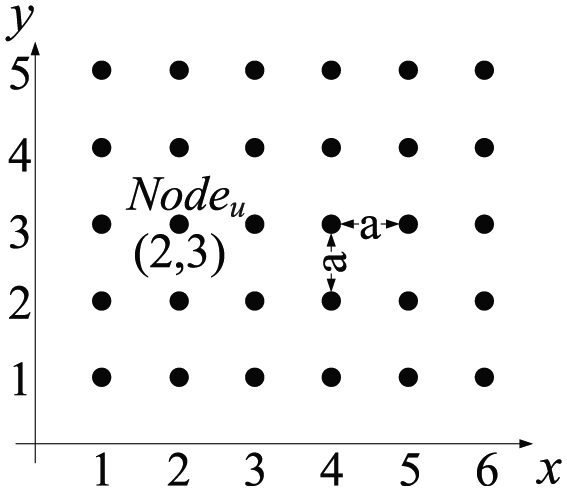
Coordinates of node.
Determination about border and backbone nodes
Suppose that the structuring element used for node erosion and dilation is S. For
If
where
Each node has a field
If
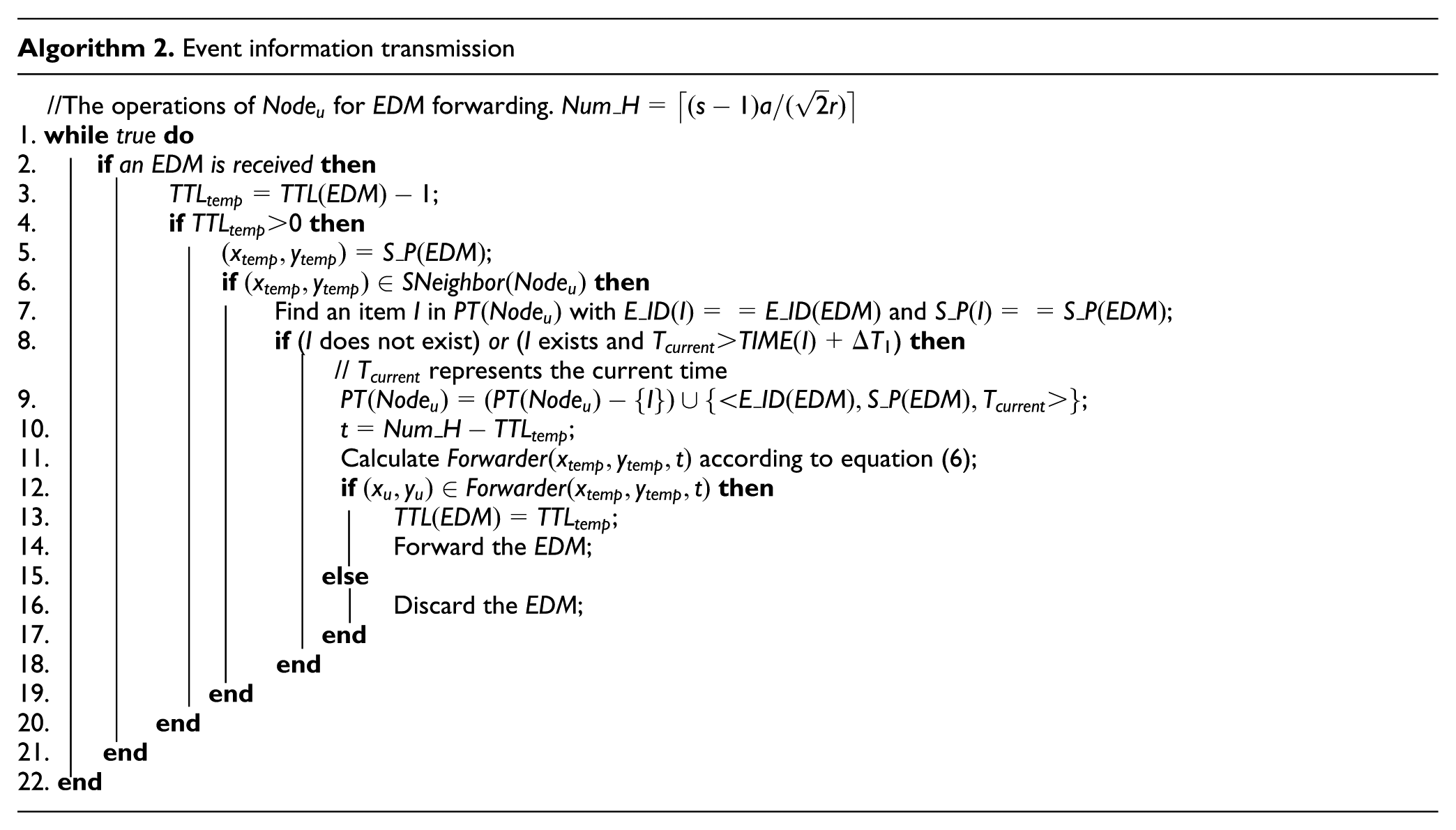
Figure 5 shows the case of structuring neighbors of four nodes, where the numbers beside the nodes are node identifiers and the white nodes are monitoring an event. We take

Structuring neighbors and event-monitoring maps of nodes.
Structuring neighbors
Considering the characteristics of WSNs, we select a square structuring element, such as

Square structuring elements.

Event information transmission
From section “Determination about border and backbone nodes,” a node requires event-monitoring information about its structuring neighbors and produces an event-monitoring map to determine whether it should be eroded. Because of the limited energy of sensor nodes, the cost for a node to acquire the event information from its structuring neighbors should be as small as possible. Thus, we design a strategy for event information transmission with a low cost.
Each node does not require its structuring neighbors to send their event-monitoring information actively. The node sends out the event-monitoring information within its structuring neighborhood when an event occurs, and then the structuring neighbors can passively obtain the event-monitoring information. Because a node only requires event information from its structuring neighbors, the transmission of event information is restricted within the structuring neighborhood determined by the structuring element.
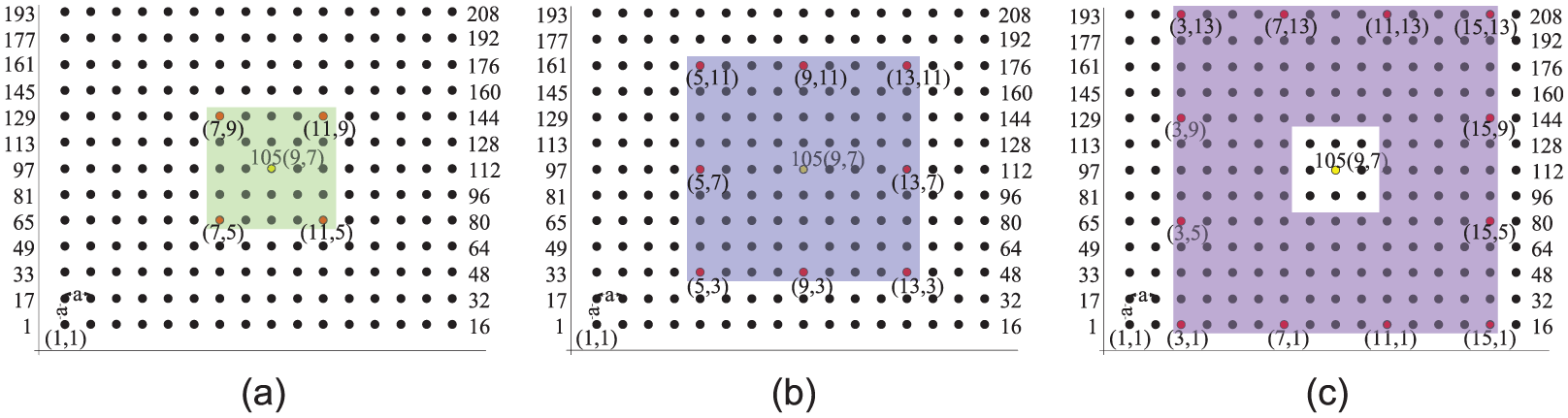
For a WSN,
The event information is enveloped in the event discovery message (EDM),
Suppose that a node

where
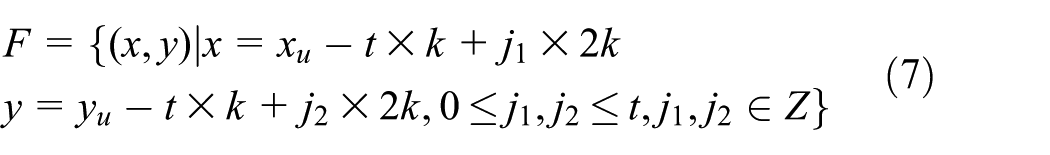

Figure 7 shows an example of EDM forwarding, and k is set to 2. In Figure 7(a), when the node
Examples of EDM forwarding: (a) t = 1, (b) t = 2, and (c) t = 3.
To restrict the EDM forwarding to the structuring neighborhood, each node holds a variable
Additionally, each node contains a processing table for EDM, and we denote the table as PT. This table can accelerate the nodes to discard the processed
Algorithm 2 introduces the transmission strategy of the event information. Suppose that a node
Event backbone node acquisition
In addition,
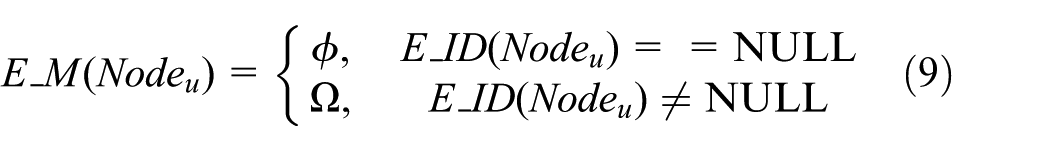
where
If

If CollectEDM expires, the event information collecting phase ends and the erosion phase begins as shown in lines 16–22 of Algorithm 3. When the
In addition,
The structuring element to be used is not fixed, and its size can be changed according to the network conditions. When the average residual energy is low, a large size is recommended to produce a small event backbone region to extend the network’s lifetime. In this case, although the data cannot represent the whole event region exactly, the data are obtained from the nodes that are more related to the event; thus, the key information remains. Naturally, extending the lifetime at this time is more important than the exact data acquisition. A small size is recommended when the average residual energy is high because it can extend the event backbone region to represent the event more exactly. In other words, because the primary task of WSNs is collecting data, our proposed DMOA can transmit data with appropriate accuracy via an adaptive structuring element size while also saving energy.
Event region recovery
Based on the structuring element and the positions of the data-transmission nodes (i.e. the positions of the event backbone nodes), the sink can recover event regions through a dilation operation. Consequently, the sink can deduce the scope of the event and direct the response or decision. Suppose that there is a WSN used to monitor the environment temperature. If the temperature of a region rises sharply at a certain moment, to facilitate rapid and precise decision making, the backbone of the abnormal region should be dilated to obtain the rough scope of the event.
If a square structuring element is
DMOA
DMOA includes two parts: event region erosion and event region recovery, and the corresponding pseudo-codes of DMOA are listed in Algorithm 5. In lines 2–3, a node

Theoretical analysis and experiments
Theoretical analysis
The feasibility and effectiveness of the DMOA are analyzed as below.
A. Based on reliable communication links, Algorithm 2 of the DMOA can transmit the
of any node to its structuring neighbors
Suppose that
Let
According to equation (6), calculate the forwarding set
Let
Because
From the above,
B. Based on reliable communication links, DMOA can ensure that the correct and complete monitoring status of the structuring neighbors is transmitted to any node that detects an event
C. DMOA has low control overhead
The control overhead of the DMOA is mainly generated via EDM forwarding. Suppose that there are
D. DMOA is effective at energy conservation
To show the effectiveness of energy conservation, we estimate the number of backbone nodes for DMOA. To simplify the analysis, the shape of an event is assumed to be a convex polygon. Suppose that there is a minimum rectangle
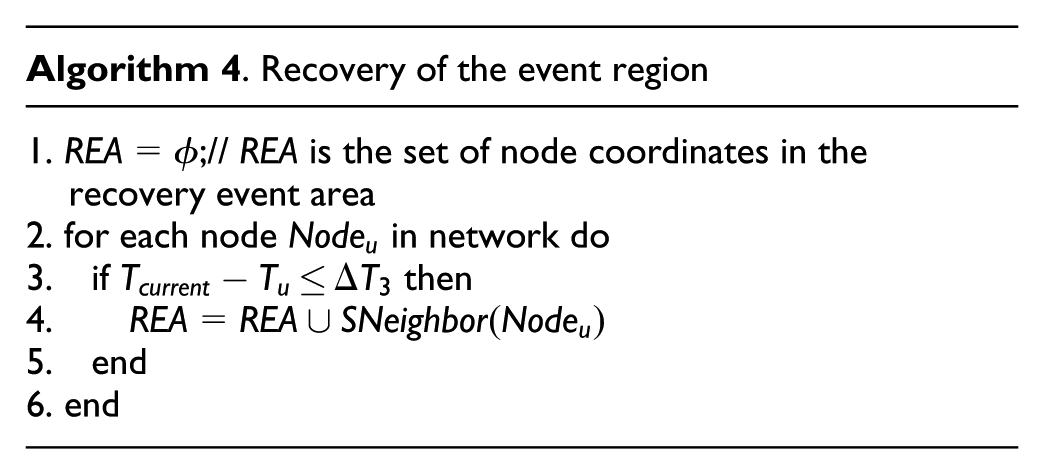
Experiments
To validate the effectiveness of the DMOA, we first perform experiments with different structuring element sizes and communication radiuses to show their influence on the control overhead of the DMOA. Then, we integrate our DMOA with three data collection algorithms, SPT, 2 MLA, 16 and YEAST, 5 and they are denoted as DMOA-SPT, DMOA-MLA, and DMOA-YEAST, respectively. We evaluate those algorithms according to the energy consumption and network lifetime with different node densities, transmission failures, time, and initial node energies. Finally, we verify the DMOA’s performance on backbone node mining and event region recovery under different structuring element sizes. We simulated the WSNs using MATLAB R2010b, and all of the experiments were executed on a PC with an Intel Xeon E3-1231 3.40 GHz CPU with 16 GB RAM.
The energy consumption model used in our experiments is the same as that in Heinzelman et al. 38 A node sends an l-bit message at a distance of d, and the energy cost is determined by equation (10)

When a node receives an l-bit message, the energy cost is calculated by equation (11)

where
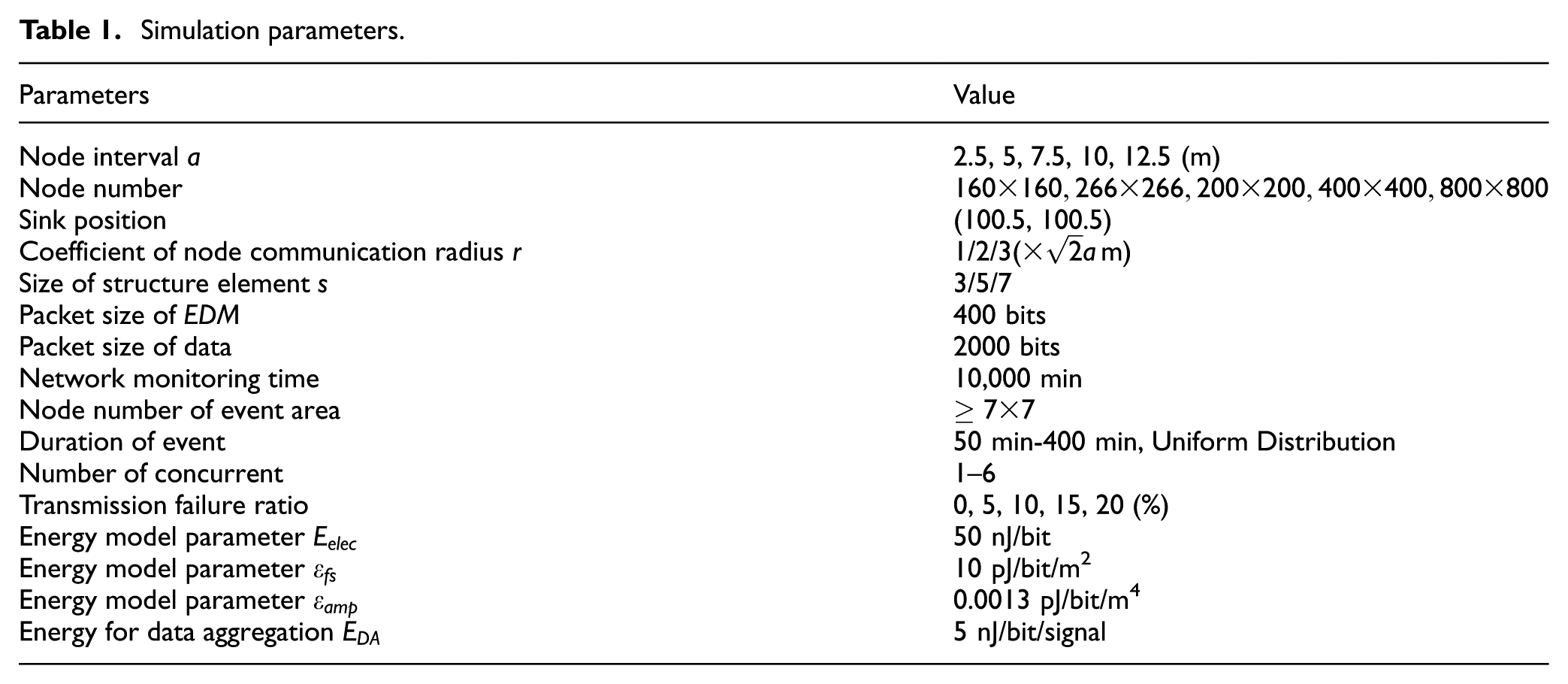
We assume that the shape of the event regions is arbitrary and that the positions and start times are random. The main simulation parameters are listed in Table 1.
Simulation parameters.
The performance assessments to be compared are listed as follows:
TEC: total energy consumption
EC-EDM: energy consumption of EDM
TN-S: total number of senders
TFDN: time of first died node
RP: recovery precision (ratio between the node number of the estimated event regions and that of the origin event regions)
Control overhead
To discuss the influence of the node communication radius r and the structuring element size s on the control overhead of the DMOA, the transmission energy consumed for the EDMs using different

Control overhead.
Network energy consumption
For DMOA-SPT, the DMOA is used first to erode nodes in event regions, and then the data sensed by the backbone nodes are transmitted and aggregated along the SPT created by the SPT algorithm. For DMOA-MLA, the backbone nodes in the event areas are mined by DMOA first, and their sensing data are processed by the method from the MLA algorithm. For DMOA-YEAST, the most correlated data are obtained by the DMOA, and they are aggregated and transmitted to the sink along the aggregation tree built by the YEAST algorithm.
Figure 9 shows a comparison of the TECs at different moments. The TEC of each algorithm increases approximately linearly over time, and the DMOA improves the performance of the other algorithms as the total energy consumption increases.

Total energy consumption at different time.
Smaller values of a correspond to a greater density of the nodes in the network. Thus, to show the influence of the node density on the energy consumption, we perform experiments with different values of a. Figure 10 shows the results of the total energy consumption with different values of a at the 2000-th minute. With a larger value of a, the number of nodes in the event regions is reduced and the energy spent on data transmission would decrease. The DMOA can erode the nodes in the event border regions, which can help decrease the energy consumption with data transmission. Thus, as shown in Figure 10, the DMOA performs well regardless of the node density.
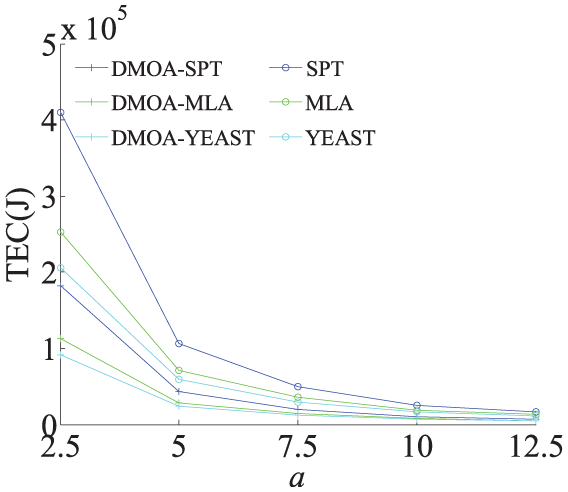
Total energy consumption with varying a.
To verify the performance of the DMOA in WSNs with unreliable communication channels, we consider transmission failures in our experiments, and the results are shown in Figure 11. In these experiments, a reliable data transmission scheme is adopted when the nodes transmit the sensed data, and the event information exchange for the node erosion does not use a reliable data transmission method. With an increasing transmission failure ratio (TFR), the energy consumption of the SPT, MLA, and YEAST algorithms increases because of data retransmission, whereas the energy consumption of the other three algorithms decreases because a transmission failure can cause more nodes to be eroded by the DMOA. As the TFR value increases, the number of event backbone nodes determined by the DMOA decreases, which leads to less data transmission in the network. Compared to data retransmission, the decrease in the number of event backbone nodes plays a leading role, which decreases the energy consumption of the DMOA-SPT, DMOA-MLA and DMOA-YEAST (as shown in Figure 11).
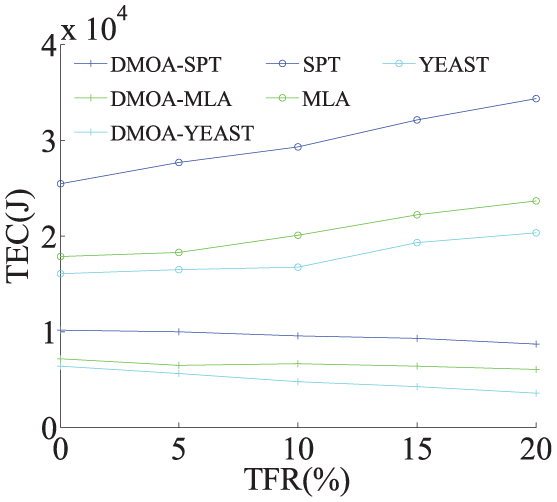
Total energy consumption with varying TFRs.
Time when the first node dies
Many parameters are used to measure the lifetime of WSNs. Because the network structure can destabilize after a node dies, we selected the time when the first node dies to measure the network lifetime.
Figure 12 shows the results about TFDN with different node initial energy. As the initial energy increases, the TFDN of those algorithms are lengthened, and especially DMOA is more significant in this point.

Time at which the first node dies, with varying initial energies.
As a changes, we investigate the time at which the first node dies, and the results are shown in Figure 13. When a increases, the number of nodes in the event regions decreases, which leads to less data transmission in the network and prolongs the TFDN. Because the DMOA can further reduce the number of nodes that send data, it can lead to a longer TFDN, and this advantage is much more obvious with a smaller node density.

Time at which the first node dies, with varying a a.
Although the communication links are unreliable, the DMOA can help the algorithms to lengthen the time at which the first node dies. In addition, with an increasing TFR, the TFDNs of the SPT, MLA, and YEAST shorten because of data retransmission, whereas the TFDNs of the DMOA-SPT, DMOA-MLA, and DMOA-YEAST lengthen because of the anabatic decrease in the event backbone nodes introduced by the DMOA as shown in Figure 14.

Time at which the first node dies, with varying TFRs.
Number of transmission nodes
To clearly demonstrate the energy conservation of the DMOA, we conduct experiments to compare the total number of senders (TN-Ss) between the SPT and DMOA-SPT with different values of s at different moments, and the results are shown in Figure 15. As the network runs, the TN-Ss all increase, although the TN-Ss of DMOA_SPTs are always smaller than that of the SPT. Greater values of s correspond to a larger difference between SPT and DMOA_SPT and greater energy conservation of the DMOAs.

Total number of senders.
Recovery accuracy
Based on the distribution of backbone nodes, the sink utilizes the dilation operation to recover the event regions. To respond more effectively for offline guiding, the approximate regions should be as close to the original regions as possible. In this subsection, the recovery accuracies at different moments of DMOAs with different values of s are presented in Figure 16. This figure shows that the recovery accuracy decreases with increase in s, although the accuracy changes are small over time. The average recovery accuracies for

Recovery accuracy.
Node erosion and event region recovery
To further show the effectiveness of the DMOA, we extract the event distributions at the 4644-th and 6132-th minutes in the experiments, and the results are shown in Figure 17(a)–(c). The three subfigures correspond to the results with the structuring elements of size

Examples of erosion and recovery for event regions: (a) s = 3, (b) s = 5, and (c) s = 7.
Conclusion
The key mission of WSNs is sensory data collection. After an event occurs, the sensor nodes within the event border region sense more fluctuating data than the nodes within the event backbone region, and this discrepancy affects the conclusions on the whole event. To decrease the amount of data transmitted from the event border regions, a novel DMOA is proposed, and it is motivated by morphological erosion and dilation in digital image processing. This algorithm can extract event backbone nodes in a distributed manner and recover event regions rapidly. The DMOA takes the event monitoring of a uniform network as a binary image, which provides the possibility of applying distributed morphological operations. Each node determines its own structuring neighbors according to the structuring element and collects event monitoring information from its neighborhood using the constrained transmission of
However, the DMOA is designed for isomorphic WSNs. Researching on how to gain event backbone regions in a distributed manner with low cost for heterogeneous WSNs is one of our future goals.
Footnotes
Acknowledgements
The authors would like to thank the anonymous reviewers for their valuable comments and suggestions.
Academic Editor: Fei Yu
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported in part by the National Natural Science Foundation of China under grant no. 61602230, in part by the Key Scientific Research Project in Colleges and Universities of Henan Province under grant no. 16A520063 and 18A120002, in part by the Henan Province Education Department Cultivation Young Key Teachers under grant no. 2016GGJS-158, in part by the Henan Province Education Department Natural Science Foundation under grant no. 17A520044, and in part by High-level Talent Startup Foundation of Luoyang Institute of Science and Technology under grant no. 2015BZ01.