Abstract
The architecture of C-RAN-based soft-defined vehicular networks can support increasing demands of various applications in the future vehicular cyber-physical systems, but lacks strong and practical security–enhancing mechanisms in the physical layer. In this article, we propose a hybrid beamforming and vehicle-selection framework for vehicle-to-infrastructure communications to broadcast high-speed confidential messages. A one-dimensional roadway scenario having multiple lanes is considered, and the concept of secure region and interference-selection region is, respectively, developed for each roadside unit. We formulate an optimization problem of maximizing secrecy sumrate with the constraint of orthogonality-based vehicle selection. The original problem is then divided into two subproblems subtly. In terms of the first subproblem, we, by exploiting the orthogonality assumption, obtain a corresponding secure beamformer for each vehicle located in the secure region to reduce the interference and confidential information leakage. Based on secure beamformers, the second subproblem is changed to be a vehicle-selection problem, which is then solved by adopting hierarchical agglomerative clustering method and implemented by two proposed novel algorithms blending vehicle selection with beamformer generation. Simulation results verify the effectiveness of the proposed algorithms in the respect of secrecy sumrate compared with the conventional zero-forcing beamforming using semi-orthogonal user selection algorithms. Furthermore, simulations show how our proposed algorithms resist against eavesdropping from collusive vehicles located in the same secure region by flexibly altering the size of secure region and interference-selection according to the traffic density.
Keywords
Introduction
Cyber-physical systems (CPS), a new generation of systems with integrated computational and physical capabilities, can achieve human’s real-time and high-efficiency interactions with advanced systems through many new modality transformations from the nano-world to large-scale wide-area systems of systems.1,2 In general, the interactions with various complex systems require co-working of control, computing, network, and physical subsystems.3–5 By integrating those different subsystems, the potential benefits of the CPS can be developed in different networks such as cellular networks, 6 cognitive ad hoc networks, 7 and in wide application areas: intervention, precision, operation in dangerous or inaccessible environments and coordination, for example, vehicle scheduling and traffic control in vehicular networks. 8
With the aid of CPS, the combination of vehicular networks and CPS comes to be possible, considered as vehicular cyber-physical systems (VCPS). 9 By fully exploiting CPS, the next generation of VCPS is enabled to construct intelligence across different subsystems to improve security, efficiency, and energy conservation in transportation and further requires more innovative approaches in terms of system architectures that enable seamless integration of control, communication, and computation. 10 However, the integration of various subsystems, while keeping VCPS functional and operational, has been time-consuming and costly. Moreover, the increasing complexity of system components and the use of more advanced technologies for sensors, wireless communication, and processors exert much more pressure on the design of next-generation VCPS during its journey of enabling reliable integration of different critical system components. 11 Traditionally, those vital components or subsystems include several specific vehicular networks with various communicating and computing abilities. It is the variety of networks and interfaces that make the joint and efficient use of resource across these different networks full of challenges. In terms of architecture designs for vehicular networks, powerful vehicular communication networks play a vital role in connecting different system components of VCPS and has been drawn great attention from both industry and academic due to its social and economic benefits expected from Intelligent Transport System (ITS). Thus, accompanying with the evolution and updating of VCPS, new innovative communication architectures of vehicular networks also need to be more integrated and compatible with future networks, which is vital and necessary to efficiently utilize vehicles and infrastructures for road services in VCPS.
Generally, in vehicular communication networks,12–14 vehicles can flexibly communicate with each other and roadside unit (RSU) via vehicle-to-vehicle (V2V) and vehicle-to-infrastructure (V2I), respectively, and achieve information delivering and exchanging for various applications. However, with the scale of dynamic network topology and various quality-of-service requirements increasing, the architecture of conventional vehicular networks has a tendency to be more heterogeneous, such as dedicated short-range communication (DSRC) based on IEEE 802.11p for V2V communications,15,16 co-existing with the fourth generation (4G) long-term evolution (LTE) exploited to support V2I communications. 17 Unfortunately, interfaces usually have been standardized between different protocols in conventional vehicular communication networks, thus constraining the resource utilization across different domains.
To achieve the resource sharing between different types of networks and interfaces, specialized developments for higher layer protocols need to be considered. Heterogeneous Vehicular NETworks (HetVNET), 18 by integrating different access networks including DSRC and LTE through a unified framework, can support a dynamic and instant composition of different networks and allow operators to utilize radio resources in an efficient and flexible way. Therefore, HetVNET is expected to be a practicable solution to meet various communication requirements for ITS services. In HetVNET, soft-defined network (SDN)-based cloud radio access network (Cloud-RAN) has been widely accepted to be a feasible solution for integrating various interfaces and other wireless resources efficiently, thus forming a Cloud-RAN-based HetVNET infrastructures. In general, in Cloud-RAN, 19 all RAN functionalities are achieved in the centralized central processor (CP) responsible for all of the baseband unit (BBU) processing tasks. BBUs are connected to remote radio heads (RRHs) via high bandwidth links on a wide geographical area. When performing large-scale and real-time dynamic resource scheduling in HetVNET, C-RAN is triggered and enabled to take advantages of technologies such as cloud computing, advanced RRH techniques, and SDN approaches with more open platform and more flexible operation.
However, though providing a rich set of available resource, the C-RAN-based HetVNET infrastructure is incurring significant security risks and threats from complex environment, including a formidable set of intentional overhearing on confidential message and malicious jamming on useful information possibly due to its heterogeneous features. 20 Those security issues undoubtedly impact both the protocol design in the upper layer and information transmission in the physical layer, which calls for new consideration on the protocol and mechanism design. It is a critical challenge because uncertainty in the environment and possible security attacks often impose significant impact on system robustness and security, thus determining how to design a practical and robust system. Exploiting the physical nature of HetVNET by leveraging location-based, channel-based, and tag-based mechanisms is a feasible way of providing security solutions, especially for wireless vehicular communication networks.21,22
In this article, we consider in a vehicular network the one-dimensional road scenario where RSUs connected by fiber are deployed as a C-RAN architecture to support confidential message transmission for V2I communications. Seen as a kind of hybrid location–based and channel-based scheme, a hybrid secure beamforming and vehicle-selection framework is proposed. First, we define a secure region restricted by accessing control and interference-selection region for each corresponding RSU, respectively, both of which is regulable and adjusted according to vehicle traffic, selection algorithms, and secrecy considerations. As a worst case, vehicles located in the secure region serve as the collusive eavesdroppers in a genie-aided way to overhear confidential messages transmitted by a target vehicle in the same secure region. By performing a novel general algorithm of vehicle selection, each RSU managing the corresponding secure region is enabled to perform secure beamforming for each vehicle located in this region with high speed of confidential message transmission. Our contributions can be summarized as follows:
The concept of secure region for C-RAN-based V2I architecture is first proposed, based on which a joint optimization problem that maximizes the secrecy sumrate with constraints of orthogonality-based vehicle selection is formulated.
By fully exploiting orthogonality between any two channels of vehicles, we transform the original optimization problem into two subproblems. The first subproblem gives a solution of how to determine optimal secure beamformers for vehicles with relative high orthogonality, and the other one describes how to conduct efficient vehicle-selection strategies to guarantee selected vehicles to have good channel orthogonality, thus improving the efficiency of proposed beamformer generation algorithms as described in subproblem 1.
In terms of the first subproblem, using generalized singular value decomposition (GSVD) method, we, for each vehicle, design a corresponding optimal beamformer, which is suboptimal for the original problem. To solve the second subproblem, we then adopt the hierarchical agglomerative clustering method and introduce two kinds of measures to determine the vehicle cluster in each process of clustering, based on which we first implement a vehicle-selection algorithm Suboptimal Algorithm for Maximum Secrecy Sumrate (SAMSS); then, when the concept of interference-selection region is defined to better tackle with the multi-user diversity and interference across different secure region with low complexity, new algorithm denoted as Suboptimal Algorithm for Maximum Secrecy Sumrate With Low Complexity (SAMSS-LC) is proposed to further implement the dynamic vehicle selection.
Simulation results prove that our proposed scheme outperforms the conventional Zero-forcing Semi-orthogonal User Selection (ZF-SUS) user selection algorithm. Interestingly, the secrecy sumrate of SAMSS-LC outperforms that of SAMSS in various scenarios. What’s more, our simulations show how our proposed algorithms are affected by the various traffic densities and then robustly demonstrate what characteristic the secrecy sumrate has in the presence of a high traffic density.
The remainder of this article is organized as follows: section “Related work” reviews the related works regarding vehicular networks in VCPS. In section “System model,” we present the system model overview. In section “Problem formulation and solution approach,” an optimization of joint maximizing secrecy sumrate and vehicle selection is proposed and solved. Simulation results are presented in section “Simulation results.” Finally, we conclude our work in section “Conclusion.”
Notation: Boldface is used for matrixes
Related work
The research in area of VCPS has formally commenced since National Science Foundation (NSF) CPS workshop held in 2006. The US project called the United States Council for Automotive Research (USCAR) is considering cyber-physical concepts for building a smart adaptive vehicle. One such autonomous vehicle concept is presented in Chen and Fraichard. 23 From the academic point, research into the architecture design of vehicular network in VCPS has been extensively conducted in recent years. The multi-layer Cloud-RAN architecture 18 is proposed for implementing the new vehicular network, where the multi-domain resources can be exploited as needed for vehicle users. Authors in Zheng et al. 24 develop a generic HetVNET framework focusing specifically on various services that can be provisioned by heterogeneous vehicular networks and flexible switch among various candidate networking techniques.
With the consideration of security and privacy, Papadimitratos et al. 22 propose a security architecture as a kind of location-based scheme that provides a comprehensive solution for securing vehicular communication in the respect of identity, credential, and key management in upper protocols. By assuming that a large number of certification authorities (CAs) are instantiated, served areas can be divided into many regions, in each of which one CA manages the identities and credentials of all vehicle nodes registered with it. Each vehicle located in a specific region managed by the corresponding CA cannot access its neighboring CA, while vehicles belonging to the same CA adopt secret-key based cryptographic encryption and decryption methods to keep pseudonymous with each other. However, secret-key distribution and management in the system is subject to dynamic and variable wireless environment, which incurs security vulnerabilities in wireless networks. Smart and harmful vehicles with powerful computation ability may be able to obtain the keys and eavesdrop confidential messages of vehicles in the same region.
As a type of channel-based mechanism and simultaneously a complement of cryptography techniques in the upper layer, physical layer techniques have been developed for further enhancing on the security of wireless systems in recent years.25,26 In Wyner, 27 a three-terminal network having a transceiver pair and an extra eavesdropper, known as the wiretap channel, was considered. To measure secrecy performance, secrecy capacity is first defined as the maximum achievable rate between the source and the destination while ensuring that no information can be inferred by the eavesdropper. It was shown that a non-zero secrecy capacity can be achieved for the source–destination pair if the desire receiver has better channel conditions than the eavesdropper(s).28,29
Rather than those security analysis from the view of information theory, many coding and signal processing techniques have been developed to support and to further enhance security especially in some specific networks. 30 Geraci et al. 31 studied the secrecy sumrate for multi-user multiple-input-multiple-output (MIMO) system with regularized channel inversion (RCI) precoding by considering a worst-case scene in which malicious users collude with each other and act as an eavesdropper to decode a certain user for obtaining its confidential message. The author obtains a deterministic approximation for the achievable secrecy sumrate with a fixed ratio of the user number to the transmit antenna number in the large-system regime. However, the method is based on the assumption that the system with a large number of antennas communicates with users simultaneously without user selection, which may be impossible in practical systems with limited transmit antenna number and the necessary user selection and scheduling mechanism for some business requirements such as the user fairness. To overcome this problem, user selection is necessary but need special design. In general, the user selection mechanism for the multi-user system has been widely studied in the past years. In MIMO systems with M transmit antennas and K ≥ M single-antenna users, the full multiplexing gain M can be achieved. Specifically, it was shown that when channel state information at the transmitter (CSIT) is known ideally, the system capacity grows like M log logK in a large-user regime K M due to multi-user diversity. 32 The scheme based on Zero-forcing Beamforming (ZFBF) or zero-forcing dirty-paper coding (ZF-DPC) has been proposed to reach this growth rate with low complexity. 33
However, the multi-user diversity may also be exploited by malicious users which jointly act as an eavesdropper and decode the confidential messages for intended users. Worst of all, for an intended user, all the other users always tend to collude with each other for obtaining its message, whether the user selection is performed or not at the transmitter. Thus, the conventional user selection such as SUS will be limited in the respect of system secrecy sumrate. In another work, 34 a joint secure beamforming and user selection (J-SBS) scheme is proposed to improve the secrecy sumrate in multi-user multiple-input-single output (MISO) broadcast channels with confidential messages (BCC). However, those mechanisms usually possibly do not apply when the topology of networks is huge and specific application scenarios are considered.
System model
In this section, we present the system model, including the C-RAN-based V2I communications architecture, scenario configuration, and confidential message transmission model. We present a more detailed framework of communications in V2I systems and propose some novel concepts accommodated to this framework. The main notations used are summarized in Table 1.
Summary of notations.

RSU: roadside unit; CSI: channel state information; SINR: signal to interference plus noise ratio.
C-RAN-based V2I communications architecture
This work considers the V2I communications in a C-RAN-based HetVNET 18 responsible for downlink confidential message providing to vehicles in one-dimensional roads, as shown in Figure 1. As a part of HetVNET, the architecture consisting of C-RAN based on specific wireless access techniques, for example, LTE, is adopted for providing more reliable and confidential messages. C-RAN-based networks have been researched extensively and also been deployed in many hotspots in cities of China for supporting high-speed communications service seamlessly. According to the work in Zheng et al., 18 using C-RAN techniques, Soft-defined HetVNET is enabled to integrate different access networks including DSRC and LTE to meet various communication requirements for ITS service. Thanks to its own Remote Cloud and Local Cloud, the C-RAN has ability to manage various applications such as confidential message transmission service through a large-scale centralized process which is beneficial for V2I communications. Furthermore, confidential data services, we assume, are solely provided through V2I communications, although they could be delivered among vehicles via V2V communications guaranteed by some specific protocols. Because many vehicles possibly act as untrusted nodes to track target vehicles for a long time and overhear the confidential messages, especially when traffic jam cause long-time waiting in the roads and provide sufficient time for eavesdropping vehicles to break down the upper protocol.

C-RAN Based V2I communication systems under lots of one-dimensional roads.
Scenario configuration
We consider a one-dimensional road with multiple lanes, which is partitioned into segments. Without loss of generality, the segments are numbered from 1 to R, increasing in the car moving direction, as shown in Figure 2. There is one RSU placed in each segment and the RSU is placed at the center of the segment. In C-RAN-based V2I networks, each of RSUs can be seen as the RRH, usually used in C-RAN networks. In this article, we assume each of RSU has the same hardware configuration as the RRH, which usually consists of antenna system, power amplifier, low noise amplifier (LNA), and A/D converter. Since all the baseband processing functions have been concentrated into the BBUs, these modules have much less energy consumption and complexity which directly lowers their price, thus inducing easy and massive deployment along the road. Based on the above settings, there are more specific details to be considered.

Secure region and interference-selection region in one-dimensional road scenario.
First, centralized control and processing in BBUs makes the centralized scheduling for large-scale vehicles possible. However, due to the limit of the antennas at RSUs, the number of selected vehicles on the same time and frequency resource is restricted. Therefore, to better provide high-speed transmission of confidential messages, vehicle selection is necessary and important for vehicle network.
Second, besides the goal of improving secrecy rate, the interference from adjacent RSUs is unavoidable during RSU’s transmitting messages to their own vehicles registered with it. Given the large-scale vehicles, how to precisely measure the interference level with low complexity is vital for high-speed message transmission. So, the measure range of interference level first needs to be defined. We assume that each service cell of RSUs can be overlapped due to the uncertainty of transmission power, channel condition, and vehicle traffic, as shown in Figure 2. This configuration also has the advantages of providing flexible multi-user diversity for vehicle selection. Now let’s introduce the details about the two types of proposed regions as follows.
Secure region
To reduce the confidential message leakage, we divide the segments served by RSUs into many small secure regions, as is shown in Figure 2. The range of secure region is predefined and each range of secure regions is identical for facilitating the modeling and analysis. Access control 35 is adopted to manage the vehicles located in secure regions and tending to access RSUs for confidential message transmission request. Especially, vehicles outside the secure region served by one RSU cannot access this RSU absolutely. Nowadays, vehicles are usually equipped with global positioning system (GPS) and the movement of vehicles is constrained by the layout of roads. Thus, each RSU can know the location of all vehicles accurately by vehicles’ periodical reporting their GPS information. Therefore, location-based accessing control is practical for the current vehicle networks. Moreover, local cloud is responsible for the confidential message transmission to each vehicle going through a corresponding secure region and manages the accessing number of vehicles in this region by controlling the range of the secure region. However, although the confidentiality across different regions can be guaranteed by above location-based accessing control, confidential messages of vehicles within secure regions can be eavesdropped and obtained by some other deliberate vehicles within the same secure region due to its vulnerability of upper protocols, especially for vehicle communications usually with high vehicle density. Usually, those messages including safety beacons that report a vehicles location, which is possibly utilized by collusive vehicles to track the target vehicles location and transactions, infer confidential information about its driver and passengers. Moreover, one secure region should disjoint with its neighboring secure region, so that systems can reserve one spare region for handover. However, dealing with handover problems is not the focus of this article.
Interference-selection region
Also to better avoid co-channel interference among selected vehicles on the same time and frequency resource block, we define the interference-selection region as such a segment with its radius larger than that of the secure region belonging to the same RSU. The range of interference-selection is predefined and each range of regions is identical. Although a large number of vehicles in the network usually generate interference among each other, we only consider the interference from vehicles located in the interference-selection region when we perform interference estimation during the vehicle selection. Obviously, the range of interference-selection determines the number of vehicles deserving being considered to calculate the interference, thus influencing the accuracy of interference calculation methods. It is worth noting that reasonable setting of the subsequent simulation has verified the effectiveness of this type of region.
Confidential message transmission model
We consider the downlink information transmission process in which each RSU i and its serving vehicles can be seen as a downlink multi-user MISO BCC system with a transmitter having

We assume perfect channel state information (CSI) is known at the transmitter, based on which each beamforming vector

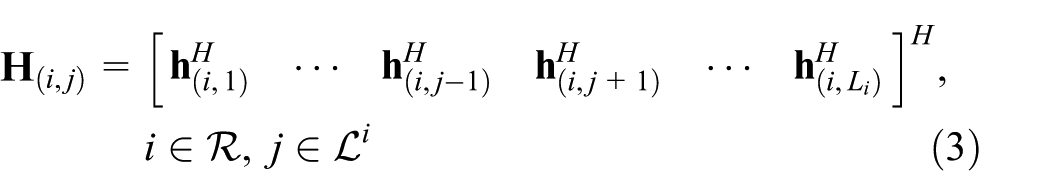
where the channel matrix
Problem formulation and solution approach
In this section, we define the achievable secrecy sumrate in C-RAN-based V2I communication systems. Based on the secrecy sumrate, we formulate the vehicle selection and secure beamforming design as a joint optimization problem. To solve the optimization problem, we propose two suboptimal algorithms with different complexities.
Achievable secrecy sumrate
As is shown in Geraci et al.,
31
if the transmitter uses independent codebooks for each user, where each codebook is a code for the scalar wiretap channel, an achievable secrecy sumrate can be derived as the sum of secrecy rate of each user. In this article, we adopt the assumption that each RSU
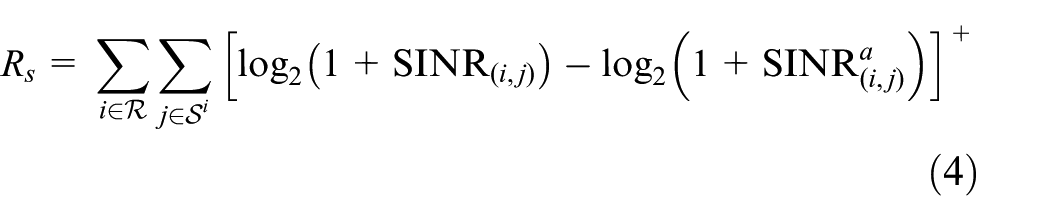
where

and
Existing ZFBF-SUS algorithm
To exploit the multi-user diversity sufficiently, the authors in Yoo and Goldsmith
36
adopt a ZFBF strategy with SUS algorithm where the system can achieve the same asymptotic sum capacity as that dirty-paper coding (DPC), as the number of users goes to infinity. Using SUS algorithm, the transmitter selects user group
Initialization:
The transmitter calculates
if
3. In this step, we update the user group as follows

4. If

where
However, when considering the scene where the eavesdropper a composed of multiple collusive vehicles decodes the confidential message
Novel optimization problem
As is shown in section “Existing ZFBF-SUS algorithm,” the vehicle selection and secure beamformer design should be considered jointly. This article considers the problem of joint secure beamforming design and vehicle selection to each RSU
The maximum number of selected vehicles for each RSU i is no more than
Each RSU has identical and fixed power budget. Among vehicles located in the secure region i, average power allocation is adopted based on the number of selected vehicles.
Each RSU only selects from the vehicles located in the secure region the desired vehicles, each of which has beamformer being orthogonal with each other. This restriction is imposed in order to reduce the interference caused by vehicles located in the same secure region.
Thus, we formulate the problem maximizing secrecy sumrate of the V2I communications as follows

Obviously, the problem is non-convex and difficult to obtain its global optimal solution, accompanying with extremely high computational complexity. However, we propose suboptimal algorithms to efficiently obtain the suboptimal solutions with low complexity. We divide the original optimization problem into two subproblems. The subproblem 1 aims to perform beamforming for each of vehicles in secure region under the assumption that each RSU always select fixed number of vehicles in secure regions but do not know which vehicle deserve being selected. Thus, subproblem 1 creates a situation that the number of alternative beamformers in each secure region is relatively large, providing much more multi-user diversity for the system. And then the next step is to design suitable algorithms able to select vehicles inducing maximum secrecy sumrate. Therefore, subproblem 2 is adopted aiming to select vehicles which satisfies orthogonal properties and brings maximum secrecy maximum sumrate. The mathematical expression of two subproblems is given as follows:
1. Subproblem 1 (Beamformer Design). Optimization of

2. Subproblem 2 (Vehicle Selection). Optimization of

Solution approach
To implement valid algorithms solving above two subproblems, we propose two corresponding methods, such as secrecy beamforming design and novel vehicle-selection algorithm. Specifically, secrecy beamforming design method can induce an optimal solution of the subproblem 1 when
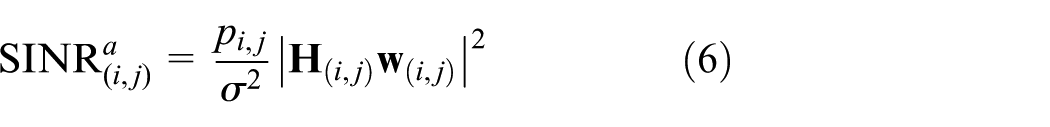
Secrecy beamforming design. In terms of the subproblem 1, the optimal beamformer is difficult to obtain. The interference to vehicle
The interference to vehicle

From the above, the optimal beamforming
Lemma 37
For a given user j served by i RSU with channel
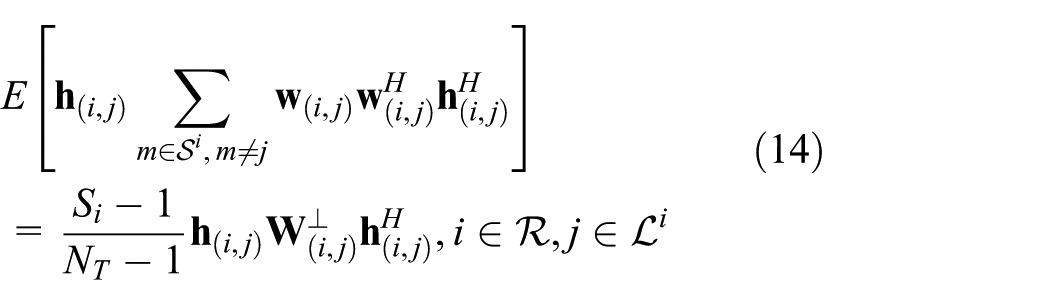
where

According to the above principle, the optimization problem (8) can be transformed into maximizing the lower bound of secrecy rate for each vehicle. Thus, the achievable secrecy rate for each vehicle can be updated as maximizing the lower bound of secrecy rate, which is shown as follows


where

and
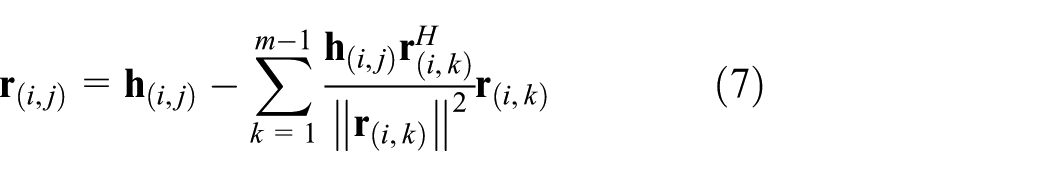
This definition of achievable secrecy rate can be seen as maximizing the lower bound of genuine secrecy rate at each vehicle, which is reasonable. To solve the above optimization, we maximize the ratio inside the logarithm by applying the GSVD method. 38
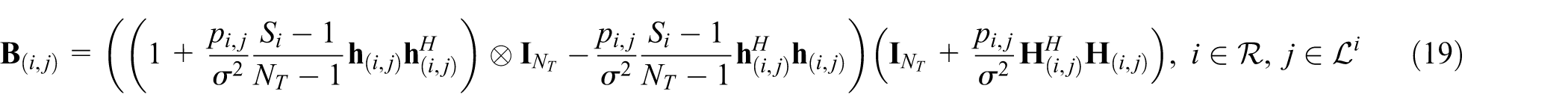
Theorem 1
Given that the selected users in group

where

where
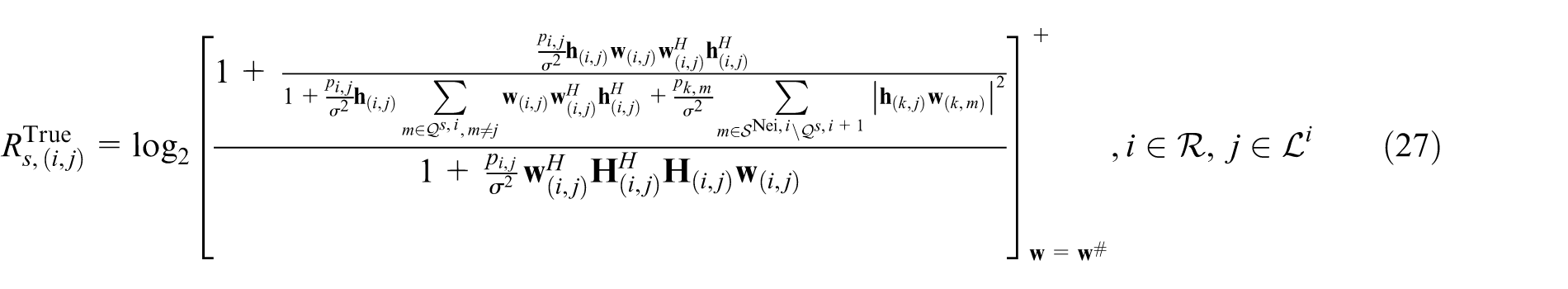
When deriving the secure beamformers above, we now calculate the true secrecy sumrate obtained by each vehicle as follows

Once the above secrecy sumrate is obtained, we can perform the following vehicle-selection algorithms based on clustering analysis to solve subproblem 2.
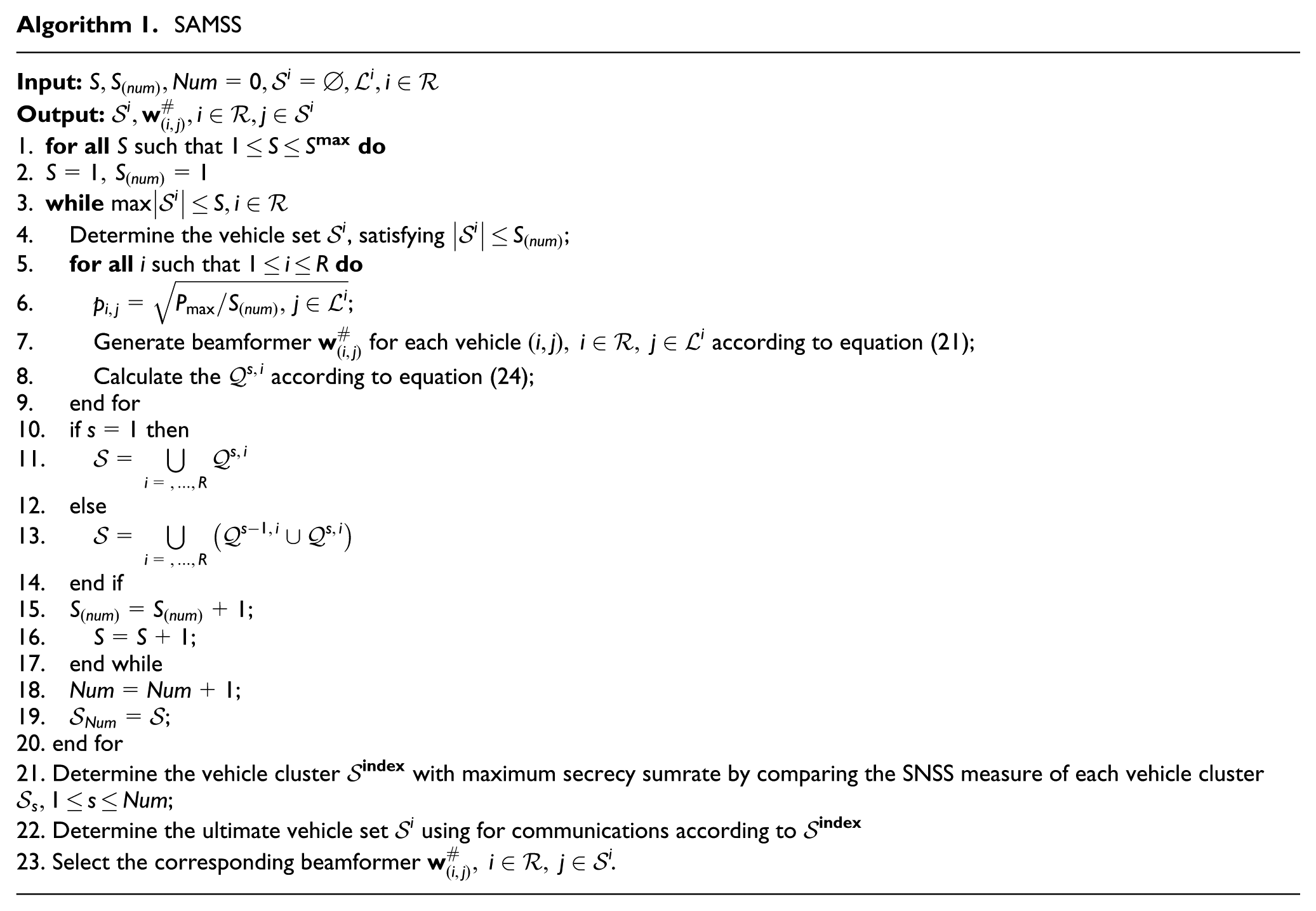
2. Novel vehicle-selection algorithms. In this subsection, we first describe the cluster analysis method, 39 based on which we propose two algorithms to select vehicles: SAMSS and SAMSS-LC, respectively.
Cluster analysis distinguishes and groups users (observations, events) based on the information found in the data describing the users or their relationships. The goal is that the users in a group will be similar to one another and different from the objects in other groups. The greater the similarity within a group, and the greater the difference between groups, the better or more distinct the clustering. How to define similarity and difference and adopt which clustering method is important for clustering analysis.
Hierarchical method: agglomerative clustering
As one technique of cluster analysis, hierarchical clustering usually starts with one large cluster and split it, which is denoted as Division. Or it starts with sub-clusters each of which containing a point or multiple points, and then merges them, which is defined as Agglomeration.
We, in this article, adopt the agglomerative clustering method as is shown in Figure 3 and start with sub-clusters each of which is obtained according to orthogonality-based vehicle pairing (OBVP) measure. Each sub-cluster has at most R vehicles. Then, we, at each step, merge or combine the closest pair of clusters according to the sum of neighboring secrecy sumrate (SNSS) measure until the decision criterion for the algorithm is broken, as is shown in Figure 3. Both of two measures will be interpreted in the following.

An illustration of the process in the hierarchical agglomerative clustering method using traditional nested set (left) and dendrogram (right).
Objective functions
Many clustering techniques are based on trying to minimize or maximize a global objective function, which, in theory, can be solved by enumerating all possible ways of dividing the points into clusters and evaluating each potential set of clusters according to the objective function. However, this approach is computationally infeasible (NP complete) and as a result, many practical techniques for optimizing a global objective function have been developed. One approach is to rely on algorithms, which find solutions that are often good, but not optimal.
Hierarchical clustering procedures proceed by making local decisions at each step of the clustering process. These “local” decisions are also based on an objective function or a specified measure, though the overall or global result is not easily interpreted in terms of a global objective function. Different from the common proximity measures such as distance measures, ordinal measures, and cosine measure, we in this article define a two-limit measure model including OBVP measure for vehicles in each secure region and SNSS measure for vehicles across different secure regions, to help systems make local decisions. Obviously, SNSS measure determines the element belonging to each sub-cluster in each step, and OBVP measure determines how to merge different sub-clusters across different steps.
OBVP
To determine each sub-cluster jointly with the design mechanism of beamformer generation, we, from each secure region, select outstanding vehicles among which the orthogonality measure should be satisfied. This measure is derived by calculating the orthogonality of channels between vehicles in the secure region

Using this measure, we obtain the vehicle set as follows

which constituting the sub-cluster s. The operational sth sub-cluster in each step s can then be defined as

As is shown above, there possibly exists many alternative sub-cluster sets. It is vital to know how to confirm which sub-cluster is optimal according to some measure method. In the following, we give the specific definition of SNSS.
SNSS
We first calculate a simplified message transmission rate
Then, we define the neighboring secrecy sumrate (NSS) as the intermediate measure which is obtained as:

where
and
Based on the two measures above, SAMSS algorithm is given as shown in Algorithm 1. However, due to the specificity of vehicle network, the number of vehicles in the road at a certain time may be very large, even though the traffic density is not high. Therefore, when we calculate the interference to a certain RSU i caused by its adjacent RSU
As a consequence, we propose SAMSS-LC algorithm, shown in Algorithm 2, to reduce the computational complexity with relatively desirable secrecy performance. Different from SAMSS algorithm, we ignore the interference to a certain vehicle

The details of SAMSS-LC are given in Table 1.
Simulation results
In this section, we evaluate the performance of our proposed joint secure beamforming and vehicle-selection strategy via simulations. The road topology is shown in Figure 2, which consists of a one-dimensional road with eight lanes. The region for each road measures 3750 m × 30 m, and the RSUs are with equal interval deployed in the middle of the road, such that they can serve vehicles on both roads. The mobility of vehicles is generated by cellular automata (CA) model,
40
in which each vehicle occupy a space measuring 7.5 m × 3.5 m.
We adopt location-based channel access control policy and the free space model for channel propagation

The common radius of transmission range for each RSU is
Simulation parameters and values.
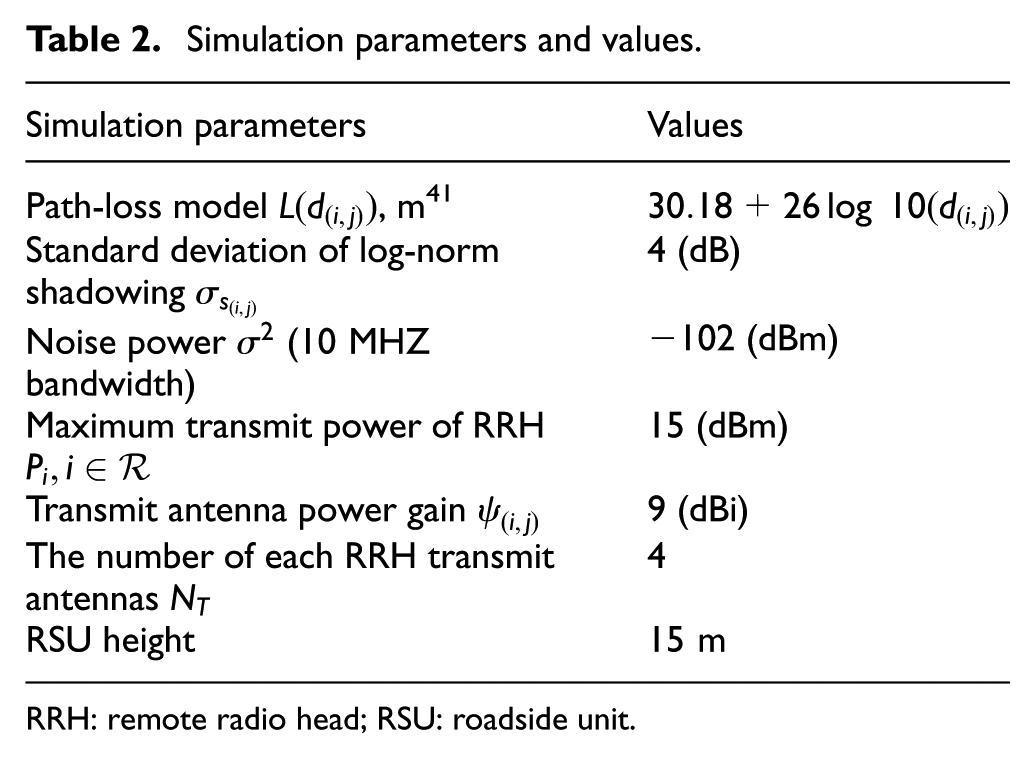
RRH: remote radio head; RSU: roadside unit.
The impact of secure region and interference-selection region
The key indicator of the performance offered by the proposed algorithms in the vehicular scenario is the secrecy sumrate in the respect of different radius of secure region and interference-selection region, respectively. In general, the radius of those two regions affects the number of vehicles to be scheduled. Due to the adopted model of vehicle mobility, the vehicle traffic in fact also imposes an impact on the scheduling conducted by RSUs.

Based on this more practical model, we fix the traffic density
Figure 4 shows that when increasing

Secrecy sumrate versus

Secrecy sumrate versus
The performance of proposed algorithms
To explore the characteristic of our proposed two algorithms, we generate several vehicle traffics such as
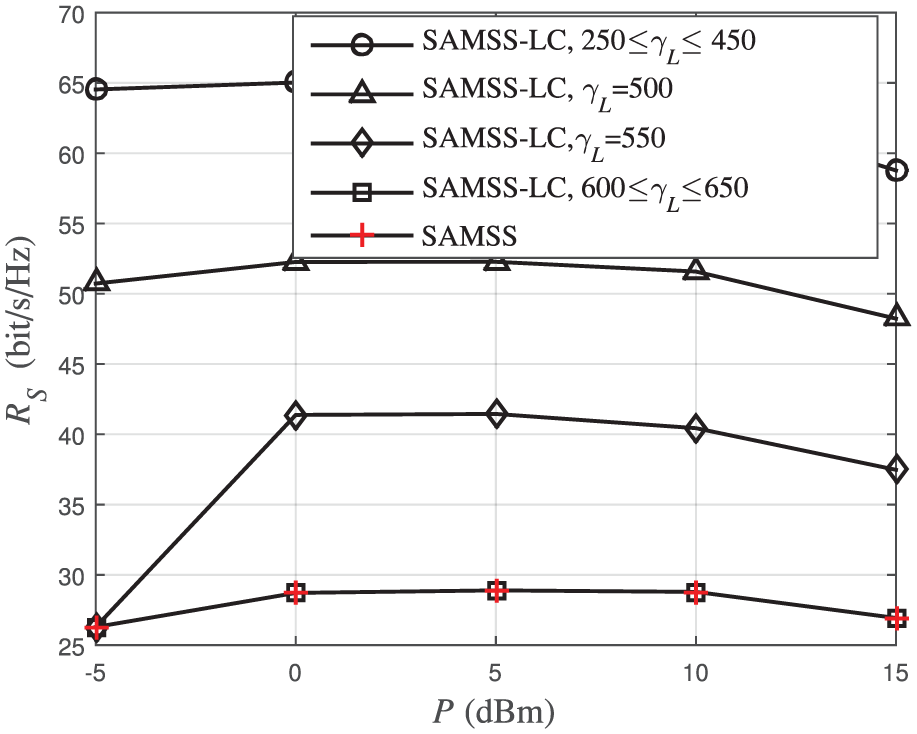
Secrecy sumrate versus different transmit power P under algorithm SAMSS and algorithm SAMSS-LC, respectively,

Secrecy sumrate versus different transmit power P under algorithm SAMSS and algorithm SAMSS-LC, respectively,
The impact of interference-selection region and transmit power
To better analyze the performance of proposed algorithm SAMSS-LC, we explore the secrecy sumrate of SAMSS-LC versus transmit power P under low traffic density and high traffic density such as

Secrecy sumrate versus different transmit power P and
Compared with Figure 8, high traffic density in Figure 9 induces several changes in secrecy sumrate, one of which is that when
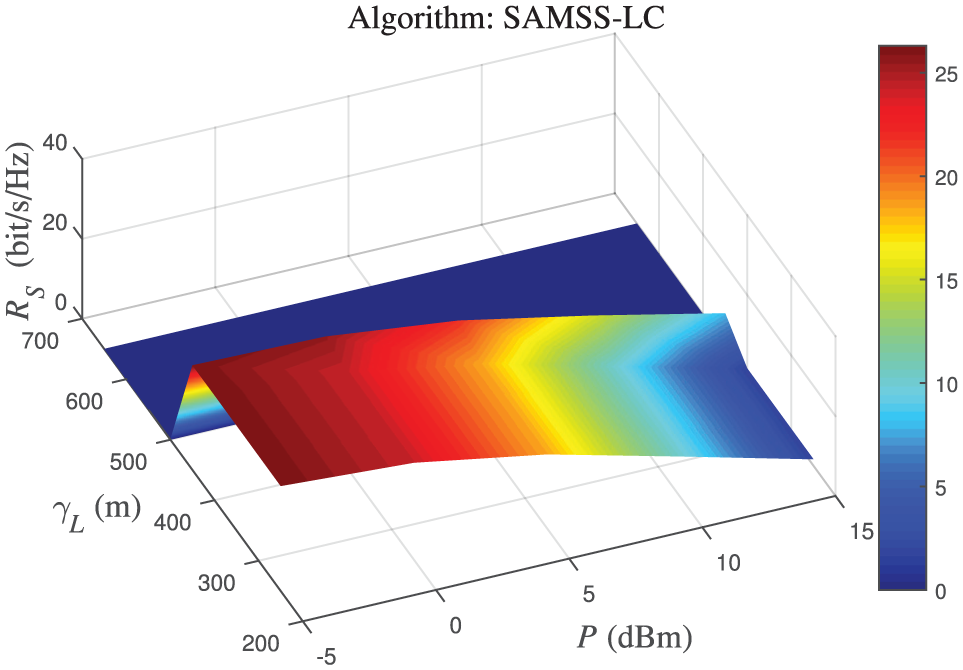
Secrecy sumrate versus different transmit power P and
The impact of secure region and transmit power
To further explore the characteristic of SAMSS-LC, we fix the radius of interference-selection region but alter the radius of the secure region, accompanying with different transmit power. In general, the radius of secure region and traffic density jointly determines the number of vehicles located in one secure region. Therefore, we illustrate three different configurations of traffic density, under which we conduct the simulation of secrecy sumrate versus transmit power. In Figure 10,

Secrecy sumrate versus different transmit power P and
However, as is shown in Figure 11, when the traffic density increases to be medium such as

Secrecy sumrate versus different transmit power P and

Secrecy sumrate versus different transmit power P with
As the traffic density get to
Conclusion
In this article, we have studied the hybrid secure beamforming and vehicle selection for a C-RAN-based V2I communications in VCPS. We propose the concept of secure region and interference-selection region, based on which a secure beamforming strategy is generated, together with two vehicle-selection algorithms, denoted as SAMSS and SAMSS-LC, to further improve the secrecy sumrate of the whole network. Specifically, we verify that SAMSS-LC algorithm has the lower complexity and better performance than SAMSS. SAMSS-LC outperforms the ZF-SUS algorithm in the respect of secrecy sumrate and has wider secure region and interference-selection region in which non-zero secrecy sumrate can be achieved. Furthermore, different size of secure region and interference-selection region determines what the secrecy sumrate can reach. When the radius of the secure region is relatively small, high secrecy sumrate can be reached if we control the interference-selection region to be a suitable extent. Otherwise, unsuitable configurations of secure region and interference-selection region can induce undesirable secrecy sumrate. What’s more, we show that the transmit power, respectively, together with the secure region and interference-selection region can impact the secrecy sumrate jointly. In the end, we found that the region of non-zero secrecy sumrate can change with different traffic densities. Therefore, reasonable configurations of transmit power, secure region, interference region, and traffic density jointly are necessary procedure for desirable secrecy sumrate, which will be our next work in the future.
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: The research work reported in this paper was supported by the National Natural Science Foundation of China (NSFC) under Grant No. 61431011, the Specialized Research Fund for the Doctoral Program of Higher Education under Grant No. 20120201110066, and the Fundamental Research Funds for the Central Universities.
