Abstract
Wireless sensor networks (WSNs) are ad-hoc networks composed primarily of a large number of sensor nodes with limited power, computation, storage and communication capabilities. The issue of securing and authenticating communications in such a network is problematic, and thus an adversary has an opportunity to capture a sensor node directly from the target field and extract all the information from its memory. In 2013, Yoon and Kim proposed an advanced biometric-based user authentication scheme for WSNs. Choi et al. analyzed Yoon and Kim’s scheme and performed a security cryptanalysis in 2016. They demonstrated that Yoon and Kim’s scheme had several security problems, and proposed instead an improved biometric-based user authentication scheme using fuzzy extraction. However, we cryptanalyze Choi et al.’s scheme and demonstrate that their scheme is vulnerable to insider attack and has a problem with smart card revocation/reissue. To overcome these drawbacks, we propose a secure biometric-based authentication scheme in WSNs that is secure against inside adversaries and provides secure and efficient smart card revocation/reissue.
Introduction
Wireless sensor networks (WSNs) are ad-hoc networks composed of a large number of sensor nodes with limited power, computation, storage and communication capabilities.
1
They are used for monitoring purposes, providing information about an area of interest to the rest of the system. The sensor nodes can communicate with each other via short-range radio wireless communications. The base station, also known as the gateway node
User authentication schemes have been designed and developed to address these security issues and to facilitate authorized access.7,8 User authentication is a common approach to verifying the legitimacy of a potential user, and has become an indispensable component of service access. By employing a user authentication scheme, the GW can first authenticate users before connecting them to the sensor nodes. If the sensor nodes and users are able to authenticate each other, they can communicate securely using a session key. Otherwise, the GW or a sensor node will reject the unauthorized entity, whose aim is potentially to damage the network security.
In traditional authentication schemes for WSNs, versions based on smart cards were initially introduced to resolve such security issues.9–12 Recently, a large amount of research on password-based authentication schemes using smart cards has been presented.13,14 However, password-based authentication schemes are vulnerable to identity or password-based guessing attacks, and suffer from inefficient password-change policies.15,16 To resolve single-password authentication problems, several biometric-based user authentication schemes have been proposed.17–19 In contrast with passwords, biometric information, such as faces, irises, fingerprints and palmprints, is considered a unique identifier of a user and is difficult to forge. Therefore, biometric-based user authentication is inherently more secure and reliable than conventional authentication schemes.20–22
In 2010, Yuan et al. 18 proposed the first biometric-based user authentication scheme for WSNs. Their scheme was very efficient because it used only the hash function. However, Yoon and Yoo 23 pointed out that this scheme 18 was vulnerable to insider attack, user impersonation attack, GW-impersonation attack and sensor-node-impersonate attack. To improve security, in 2011, Yoon and Yoo 23 proposed an improved scheme and claimed their scheme could withstand various attacks. In 2012, He et al. 24 proposed a robust biometric-based user authentication scheme for WSNs. However, Yoon and Kim 25 demonstrated that this scheme 24 had security breaches. Yoon and Kim then proposed an improved and advanced biometric-based user authentication scheme in 2013. They demonstrated that their scheme for WSNs was more effective and had stronger security than other related schemes. In 2016, Choi et al. 26 analyzed this scheme 25 and performed a security cryptanalysis. They demonstrated that Yoon and Kim’s scheme had several security problems: error with biometric recognition, problem with user verification, a lack of anonymity and perfect forward secrecy, exposure of the session key by the gateway node, a vulnerability to denial of service attack and a problem with revocation. To solve these problems, Choi et al. 26 proposed a biometric-based user authentication scheme using fuzzy extraction, which overcame the security weaknesses of Yoon and Kim’s scheme. 25
This paper discusses the security vulnerabilities of Choi et al.’s scheme 26 and proposes an enhanced biometric authentication scheme for WSNs with has improved security functionalities. 26 We provide an analysis of our scheme in terms of its security and efficiency. The major contributions of this study are summarized as follows.
Cryptanalysis of Choi et al.’s scheme. We cryptanalyze Choi et al.’s scheme and demonstrate that it is insecure against anonymity, user impersonation attack and illegal smart card revocation/reissue. Furthermore, we show that its revocation/reissue phase may cause high computational loads for both users and the GW. We illustrate that an inside adversary can obtain the identity of – and impersonate – an authenticated user.
Improvement of Choi et al.’s scheme. We propose an enhanced biometric authentication scheme for WSNs to overcome the security weaknesses of Choi et al.’s scheme. Our scheme is secure against inside adversaries and provides secure smart card revocation/reissue.
Security analysis against various attacks. We analyze the proposed scheme in security and efficiency. Our scheme supports better security functionalities than those of Choi et al.’s scheme. Our scheme is secure against insider attack and user impersonation attack. In addition, ours provides user anonymity, mutual authentication, session key agreement, efficient smart card revocation/reissue and forward secrecy.
The remainder of this paper is organized as follows. First, we present our preliminary details, before reviewing Choi et al.’s scheme. Next, we cryptanalyze Choi et al.’s scheme, before presenting our proposed scheme. After this, we analyze our proposed scheme and finally, we list our findings.
Preliminaries
In this section, we define the cryptographic system and primitives that are used as the building blocks in our scheme. Notation is defined in the appendix.
Capability of adversary
We assume that the capabilities of an adversary
Elliptic curves cryptography
Let p,q be two large primes, and
We assume that the elliptic curve decisional Diffie–Hellman problem is intractable, which may guarantee that there is no probabilistic polynomial time algorithm to solve these three problems with non-negligible probability.
Fuzzy extraction
We briefly describe the extraction process of key data from the given biometric information of a user using a fuzzy extractor. The output of a conventional hash function is sensitive; the hash function may also return completely different outputs even if there is a little variation in inputs. Note that the biometric is prone to various noises during data acquisition, and that reproduction of the actual biometric is hard in common practice. To avoid such problems, a fuzzy extractor method33,34 is preferred, which can extract a uniformly random string and public information from the biometric template with a given error tolerance. In the reproduction process, the fuzzy extractor recovers the original biometric key data for a noisy biometric using a helper string. The fuzzy extractor consists of Gen (generate) and Rep (reproduce).
Review of Choi et al.’s authentication scheme
In this section, we review Choi et al.’s authentication scheme.
26
The GW generates two master keys, x and y, and provides a long-term secret key
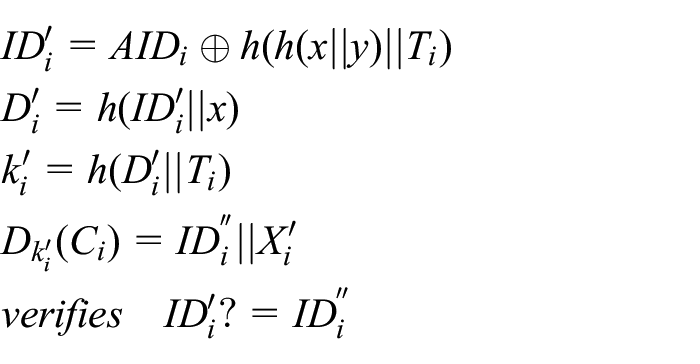
Registration phase
A user
On receiving
GW stores
Login and authentication phase
In this phase, the smart card
Then
On receiving
GW computes
GW picks up
Then GW sends the authentication message
On receiving
Then
On receiving
Only the legitimate
Revocation/reissue phase
Revocation/reissue phase is as follows:
GW checks whether
GW stores
Cryptanalysis of Choi et al.’s authentication scheme
In this section, we analyze the security problems of Choi et al.’s scheme. Choi et al. cryptanalyzed a scheme of Yoon and Kim 25 and improved it to support better security functionality. However, we found that Choi et al.’s scheme 26 also has security vulnerabilities.
Anonymity
We assumed that an authenticated user of the system could try to acquire the information of other users27,30,31. This legitimate user would then be a powerful adversary
If a legitimate user
After that,
Finally,
User impersonation attack
Choi et al. analyzed the security of their authentication scheme and claimed that it is secure against user impersonation attack, because
If it is true,
Then
The following steps are the same as those of Choi et al.’s login/authentication phase from their step (4). 26
The GW cannot distinguish whether
Illegal smart card revocation/reissue attack
A revocation/reissue phase should be provided to protect a user’s information from loss of the smart card or other security risks. However, revocation and reissue are troublesome and require additional communication with the user, so an indiscriminate revocation/reissue phase might give rise to high computational loads for both the user and the GW.
In Choi et al.’s revocation/reissue phase,
26
GW compares the new identity
(a) (b) GW checks whether
(c) GW sends (d) Using the computed
Any authenticated/unauthenticated user or adversary can revoke the smart card of an authenticated user who does not wish the said smart card to be revoked without permission because GW has no proper process for checking the legitimacy of the user on the previous identity
The proposed scheme
We propose a WSN biometric-based authentication scheme that is secure against an inside adversary. We overcome the security problems of Choi et al.’s scheme. In our scheme, we modify some secret values to support anonymity and resist insider attack. We assume that the GW generates two master keys, x and y, and provides a long-term secret key
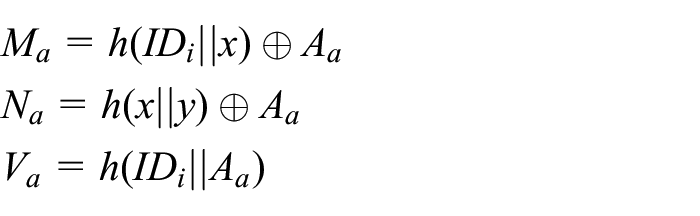
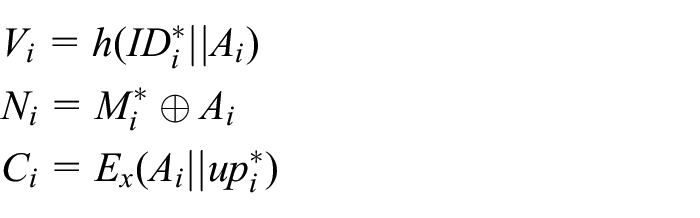
Registration phase
In this phase, a user
On receiving
GW stores
Figure 1 illustrates the registration phase of our proposed scheme.
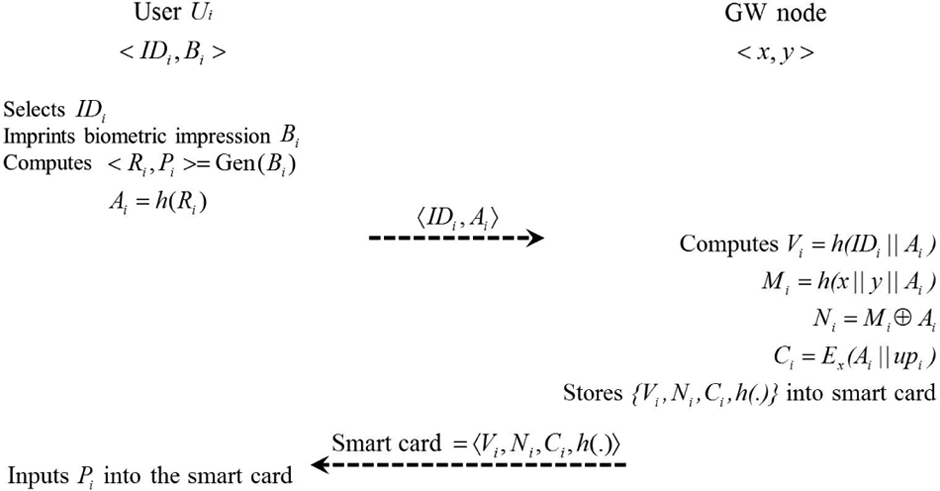
Registration phase of proposed scheme.
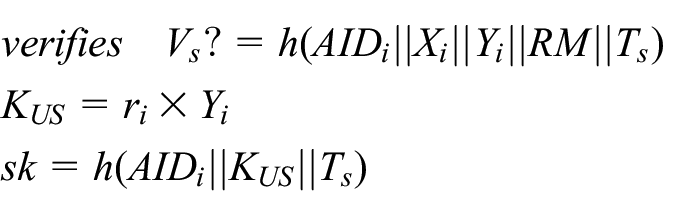
Login and authentication phase
To log in to GW and
Then
On receiving
If this is true, GW verifies the legitimacy of
GW picks up
Then GW sends the authentication message
On receiving
Then
On receiving
Only the legitimate
Figure 2 illustrates the login and authentication phase of our proposed scheme.

Login and authentication phase of the proposed scheme.
Revocation or reissue phase
To make up for smart card loss or long-term key disclosure, the smart card should be revoked and reissued in cycles.
GW computes
If this is true, GW revokes
GW stores
Figure 3 illustrates the revocation/reissue phase of our proposed scheme.

Revocation or reissue phase of the proposed scheme.
Analysis
In this section, we describe an analysis of our proposed authentication scheme with respect to security and performance. Table 1 compares the functionality features provided by our scheme with those of other existing schemes.
Comparison of functionality features.

°: scheme provides the property; ×: scheme does not provide the property;
N/A: scheme does not consider the property.
Security
User anonymity against insider/outsider. We use a dynamic pseudo identity
Perfect forward secrecy. The session key between
Mutual authentication. In our scheme,
Message confidentiality. Messages
User impersonation attack.
Gateway or sensor node impersonation attack. To masquerade as the gateway node GW or a sensor node
Illegal smart card revocation/reissue attack.
Session key exposure by GW.
GW can get both
Vulnerability of denial of service attacks. Our scheme is comparatively robust against denial of service attacks, because
User verification problem. By using fuzzy extraction,
Stolen verifier attack.
Replay attack.
Performance
We compare the functionality features and the computational cost of the proposed scheme with those of other existing schemes. In Table 2, we compare the computational cost. In the comparisons, XOR operations are not considered because these can be ignored. We use mostly hash functions; these are acceptable, compared with traditional authentication schemes in WSNs. Compared with Choi et al.’s scheme, 26 we reduce one hash function and one encryption. Therefore our authentication is reasonable for adaptation in WSNs.
Comparison of computation costs

Conclusions
In this paper, we demonstrated the security vulnerabilities of Choi et al.’s scheme and its security weakness in the revocation/reissue phase. We noted that this scheme is vulnerable to insider attack, and can cause unnecessary computational loads for a user and the gateway node, owing to faulty design of the revocation/reissue phase. In addition, we proposed a secure biometric-based authentication scheme with better security functionalities than those of Choi et al. Our scheme provides a secure and efficient smart card revocation/reissue and resists insider attack and user impersonation attack. Our scheme satisfies all the desirable security attributes, as demonstrated in our security analysis.
Footnotes
Appendix 1
Declaration of conflicting interests
This research received no specific grant from any funding agency in the public, commercial or not-for-profit sectors.