Abstract
A sparse wireless sensor network for forest fire detection is considered. It is assumed that two types of malicious nodes can exist in this network. The malicious behaviors are assumed to be concealed through some statistical behavior. A lightweight centralized trust-based model is proposed to detect malicious or misbehaving nodes. We assume that all nodes contribute to this process through the gathering of statistical data related to communication with their neighbors. These data are periodically sent to a base station, where all trust functions are executed. A simulation model is built to evaluate system performance, and the results show that the proposed model is efficient in detecting all types of considered malicious nodes.
Keywords
Introduction
The widespread popularity of the Internet has engendered a new form of communication in which all smart objects can be connected together to form what has become known as the Internet of Things (IoT). 1 The IoT has initiated a vibrant research field that combines computer networks and electronics technology. Its most common manifestation is as a Wireless Sensor Network (WSN), which consists of sensor nodes with very limited resources.2,3 This has made the IoT category vulnerable to malicious attacks and very hard to protect. 4
A typical application of the IoT can be found in the early detection of forest fires,5,6 which is important in preserving forests. A forest fire is precipitated by weather conditions or human negligence, 7 and can quickly become unmanageable and out of control, spreading quickly and causing serious damage. Early detection may aid in environmental protection and minimize damage. 8 WSNs, which consist of tiny, cheap, and low-power sensor devices, may have the ability to detect fires early through the use of spatially separated sensor nodes that collaboratively collect, process, and disseminate environmental data through a wireless broadcast medium. The immediate notification of a fire occurrence, which is the most critical issue in a forest fire detection system, can be provided through a WSN that will detect any signs of fire in real time with a high degree of accuracy. 3
Forest fire detection systems consist of nodes deployed randomly in a forest area. These nodes collect information, such as atmospheric humidity, air temperature, wind speed and direction, smoke, atmospheric pressure, and other fire monitoring parameters. When a significant change in sensor data is detected by some sensor nodes, they broadcast packets that contain their measurements. These packets are received by the nodes that are in the broadcast region of the sender and relay them until they reach the node that acts as the base station. 5 A typical scenario is shown in Figure 1.

Typical forest fire detection system.
Detecting and predicting a forest fire promptly and accurately can help minimize the loss of forests, wild animals, and human life. Therefore, any malicious behavior that blocks this information from reaching the base station could cause substantial damage. 3 In most cases, WSNs usually exist in hostile environments and are vulnerable to both external and internal malicious attacks. The most common attacks include eavesdropping, fabrication or modification of packets, and clones of nodes. Consequently, to ensure the proper operation of such networks, issues such as privacy, availability, data authentication, and integrity need to be addressed.
These nodes need to be deployed for long periods of time and need to be left operating unattended with a self-powered battery, which requires them to have low processing and communication power. However, these characteristics lead to a favorable environment for easily compromising these nodes. Thus, some means of protection, or at least detection, needs to be devised to isolate any malicious or misbehaving nodes. However, it is unpractical and even unfeasible to equip these sensor nodes with strong and computation-intensive security means. Only lightweight means will be efficient in such situations, 9 with trust-based means being among the most prominent.
The WSN can be considered as the sensor layer in the IoT three-layer model. 10 The two other layers are the edge (or sink or gateway) layer and the Cloud (or application or end-user) layer. In the current study, emphasis is placed on the sensor layer. Nevertheless, it is assumed that all sensor nodes feed some information to a base station located at the edge layer.
In this paper, we propose a lightweight trust-based model that effectively detects concealed malicious nodes. We consider two types of malicious attacks: jamming and selfishness. The model maintains one level of trust in which each node monitors its one-hop neighbor’s behavior and gathers some pertinent information, which is ultimately gathered by the base station and evaluated using some trust measures. The trust measures are based on current and past trust values to detect a concealed malicious node that is trying to change its behavior after a long period and act as a normal node. The aim of the solution is to propose an efficient trust model that is able to detect concealed malicious nodes with little memory and minimal computational power required. Along with a high detection rate of malicious nodes, there needs to be a low rate of erroneously flagging non-malicious nodes as malicious.
The rest of this paper is organized as follows: Section 2 presents recent related work. In Section 3, we propose a mathematical model for the considered system. In Section 4, the proposed trust model is presented. Finally, performance evaluation, including results and a comparison, are presented in Section 5.
Related work
The broad concept of trust-based security models designed for pervasive computing environments was introduced in Boukerche and Ren 11 through a model known as the Trust Computation and Management System (TOMS). The model was set to be applicable for dynamic and agile environments, such as Mobile Ad hoc Networks (MANETs) and WSNs. Each mobile node equipped with TOMS assesses its neighboring nodes according to their activities and contributions, and selects the most trustworthy path in its communication.
Various models have been suggested to evaluate the trust measures in WSNs. The first reputation- and trust-based model that was designed exclusively for sensor networks was presented and developed in Ganeriwal et al. 12 It was a Bayesian-based formulation for the representation of a node reputation and trust evolution. This was achieved through a watchdog mechanism that monitors the behavior of neighboring nodes in terms of data forwarding and raw sensing data consistency. A similar formulation in Liqin and Chuang 13 provided a mechanism that uses the node’s past trust to predict its future trust. A Bayesian model was proposed by Momani et al.14,15 that combines the communication components to be used in our model and some data components as well. The method also uses well-known probability density functions to both evaluate the trust values and classify the sensor nodes. Comparatively, our model is both lighter in weight and has a better performance (as will be shown in the comparison section).
A behavioral-based model was proposed in Huang et al. 16 The trust was formulated as a combination of the direct trust value to the target node and was evaluated independently by the trust issuer, based on previous interactions and network traffic monitoring metrics. In the indirect case, the trust value was derived from the recommendations of neighboring nodes. These computations were run in the middleware of every node, in a completely distributed manner. Implementing such a technique is very challenging given the small and stringent node resources. A central repository for storing the reputation of every entity in the system can be suggested to resolve such limitations, as we show in our current proposed model.
A Group-Based Trust-Management Scheme (GTMS) for clustered WSNs was proposed in Shaikh et al. 17 Its aim was to detect and prevent selfish, faulty and malicious nodes. However, it did not take into account the dynamic aspects of trust and pre-deployment knowledge of sensor nodes. Moreover, a GTMS has significant communication overhead in terms of calculations needed to determine a node’s trust value. A remedy was followed in Zhang et al. 18 where the proposed trust-management architecture was hierarchical, and aimed at improving the trust evaluation process by taking into account the dynamic aspects of trust.
A combined trust model that effectively discovers trustworthy devices and eliminates malicious ones was proposed in Denko et al. 19 The model uses both direct experience with other nodes and recommendations related to its services. A probabilistic approach using Bayesian inference was used in the decision-making process. A very similar model that uses both direct and indirect trust computations was presented in Duan et al. 20 The differences are in the industrial environment where it is applied and in the centralized computation and decisions executed by the network manager.
A trust-management protocol was proposed in Bao et al. 21 that is characterized by a hierarchical structure that maintains two levels of trust: sensor node-level trust and Cluster Head (CH)-level trust. Its implementation is based on using periodic peer-to-peer trust evaluations between two sensor nodes and two CHs. The trust metric is composed of social and Quality of Service (QoS) trusts to take into account the effect of both aspects. Social trust in the context of wireless sensors may include intimacy, honesty, privacy, centrality, and connectivity, while QoS trust may include competence, cooperativeness, reliability, and task completion capability.
A design algorithm was presented in Ukil. 22 It optimizes both reliability and communication efficiencies at the cost of the possibility of not sending data through the shortest route. The algorithm uses a combination of trust- and reputation-based collaborating computing models, which gives reliability preference over efficiency.
A trust-based access control scheme was proposed in Mahalle et al. 23 The approach uses the notion of trust levels for identity management. A fuzzy approach framework is defined, then the computed fuzzy trust values are mapped to a set of permissions and access credentials. The established trust management was shown to be both scalable and energy efficient.
In a mobile environment, a distributed model was presented in Meghanathan. 24 Data aggregation is utilized, taking into account the dynamically changing topology. The beacon data gathered in the neighborhood are used by each sensor node to maintain an estimate of the trust score of each of its neighbors.
In an underwater environment, which is characterized by unreliable communication channel and mobile network environments, the authors in Han et al. 25 proposed a trust model that ought to achieve accurate and energy-efficient evaluation. The proposed model is based on multidimensional trust metrics (ARTMMs). ARTMMs mainly consist of three types of trust metrics: link trust, data trust, and node trust.
System model
Considered network
The considered network consists of N static wireless sensor nodes randomly deployed in a sparse manner over a large area of an open forest where the sensors record data pertinent to fire detection. The collected data can include information such as air humidity, ambient temperature, wind speed and direction, smoke level, and atmospheric pressure. These data are sent to the base station through the formed mesh network. The data are then analyzed, and a decision is made as to whether there are any signs of a fire.26,27
In the event of a fire, the closest neighboring nodes detecting a sign of the fire through one or more of their sensors send an alarm packet to the base station. As time progresses, the fire and its signs may expand to a certain area, where all nodes sense it and send alarm packets to the base station.
Following this operation mode, the network can be modeled by fire events occurring at random locations followed by alarm packets sent by nodes within a certain fixed area. The complexity of such a model will be significant due to the requirements for determining the nodes that exist within a fixed area but with random coordinates. Instead, the network can be approximated by a set of contiguous fixed rectangular zones. The occurrence of a fire within any zone will trigger an alarm that will be sent to the base station by all nodes existing within the boundaries of that zone. As the size of these zones decreases, the approximation may improve, but with an increase in complexity.
It is assumed that events may happen randomly in all zones. Alarm packets are sent by sensor nodes (depending on their energy level) to the base station through the use of a multihop routing protocol. The collected information about the node’s neighbors is assumed to be sent by all nodes on a separate communication channel to the base station. The interactions among sensors are bridged via ZigBee connections.
Normal nodes
A normal node may transmit two types of packet: generated packets by the node itself to send alarms, or relayed packets to be transmitted to the next-hop, and which include all packets arriving from other nodes, using the considered node as a relay node.
Generated packets
Given the sending threshold

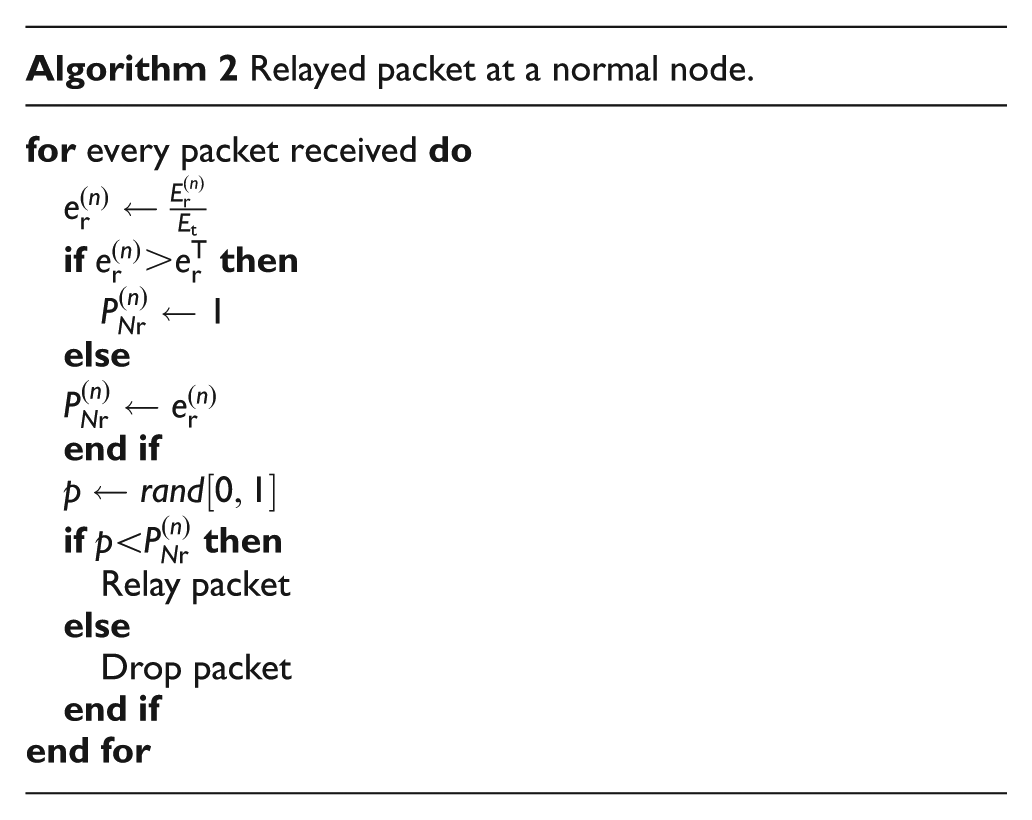
Relayed packets
Given an energy threshold
Malicious nodes
One of the fundamental principles of WSNs is that they are based on the concept of multihop. Multihop means that the sensor node receiving the message will forward the received message to the next node in line. Multihop networks, such as sensor networks, rely on the fact that neighboring nodes will faithfully forward their messages to the base station. However, unfortunately, this is not the case in selective forwarding attacks. 28
In selective forwarding attacks, malicious nodes act in a selfish manner by stopping the forwarding of selected packets. Malicious nodes have a condition on the packets that are dropped; not all packets are dropped, and this makes detection of these malicious nodes difficult. This attack can isolate some nodes in the network from connection to the base station, and that will affect data accuracy. 28
A selective forwarding attack is considered a kind of black hole attack known as a gray hole attack. This causes the node to selectively drop some received packets. However, a black hole attack drops all received packets. In all previous attacks, an attacker has to include itself in the path to be able to start dropping packets instead of forwarding them. 29
Jamming node
A denial of service attack is an explicit attempt to obstruct the legitimate user of a service or data. It is a form of jamming malicious behavior. The common method of attack involves overloading the target node with requests to try to make it unavailable. 29 This will affect network performance and increase traffic. This attack will also consume sensor node resources, such as battery, processor, and memory.
The operation of the considered jamming node is based on sending a large number of packets to hinder the accessibility of its next-hop node to other preceding nodes. It follows the steps described in Algorithm 3. To conceal its malicious behavior, when a jamming node detects a fire in its zone, it either transmits with probability

As will be described in the next sections, to combat such malicious operations, each node needs to record the number of packets it receives from its preceding neighbor node j during the time interval n.
Selfish nodes
In Misra et al. 30 a non-cooperative node model was presented where a mobile Worldwide Interoperability for Microwave Access (WiMAX) network with misbehaving nodes was considered. The behavior of the nodes was modeled with a binomial case of Bernoulli’s trials. The behavior of a mobile node u in the network was described through a random variable X, which follows a Bernoulli distribution given by

The probability that a node cooperates, i.e.
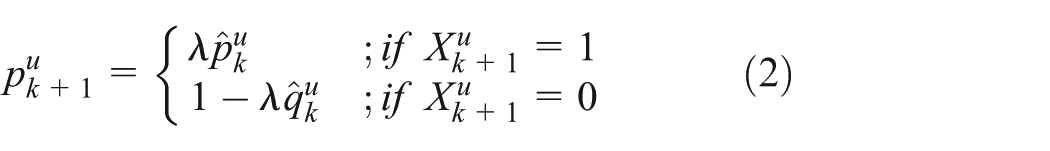
where
In our current model, a selfish node may act in a selfish manner by not relaying the received packets. Therefore, all precedent nodes to a given node j need to record the number of packets that they have sent to node j during the time interval n.
The considered selfish node will operate according to the steps in Algorithm 4. To conceal its behavior, it will not drop all received packets but a random number

The operation of our considered selfish node is equivalent to the model described in Misra et al.
30
with
Sensor node operation
The operation of a sensor node is assumed to follow a sequence of four transition states during its normal operation, as shown in Figure 2. The four states are as follows:
when there is no event, the sensor node stays in the idle/control mode (also known as listening mode) awaiting an event to occur in its zone;
when an event occurs, the node switches to transmission mode and sends an alarm packet to the base station, then returns to the listening mode;
the node may also be awakened by one of its preceding neighbors to forward its packets. The node switches to receiving mode, receives the packets, sends them to its next-hop node, and returns to the idle/control mode;
to save battery energy, if no activity is sensed for a long period, the node switches to sleep mode.

Sensor node operation model.
Proposed trust model
In our framework, the base station is where all the trust calculations are executed. Our trust-management protocol maintains one level of trust. The trust component values are obtained through direct observations of the considered node j and its next one-hop neighbors defined through our routing algorithm, as shown in Figure 3. Any node j in the network may have at most one next-hop node k and may be the next-hop of many precedent nodes i, with

General one-hop routing model.
a jamming node will affect only the next-hop node; thus, the jamming node j will affect only node k;
a selfish node will affect all its precedent neighboring nodes; thus, the selfish node j will affect all its preceding neighboring nodes from 1 to
Malicious behavior measures
After receiving the required data from all nodes, the base station evaluates the possible malicious behaviors for each node. For this, it computes the two measures described below.
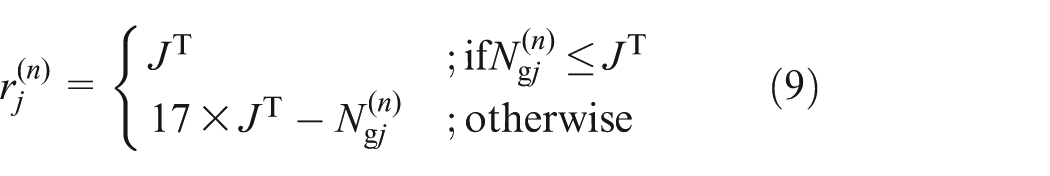
Current jamming measure
This measure is used to evaluate how far the node operation is from the jamming behavior. In our current application, a normal node may at most send one packet per event occurrence. Consequently, it will send at most the number of event occurrences during the period over which the data update is sent to the base station. The corresponding average will be denoted by
The measure to be used here is an improvement of the one used in Alnasser and Rikli. 33 For each node j, the current jamming measure is computed by
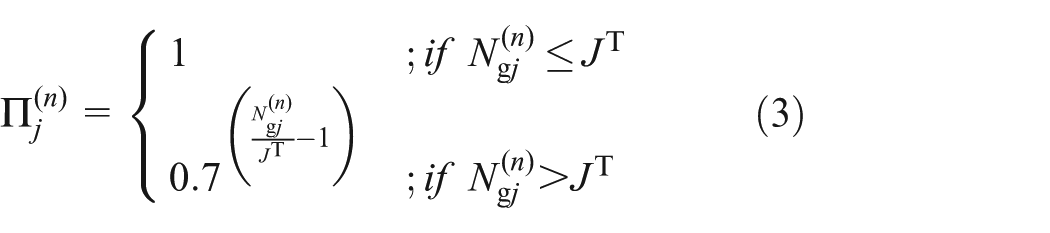
where
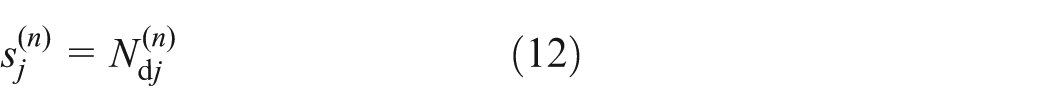
Current selfish measure
This measure is used to evaluate the level of cooperation of nodes with the forwarding process. Every node located in the routing path of another node should forward the received packets toward the base station. As a node misbehaves, by dropping instead of forwarding received packets, a measure should be defined to carry such information to the base station.
For each node j, the base station computes the current selfish measure using the following equations

where

where
Trust parameters
Based on the information gathered from all nodes, the base station calculates two parameters for each node and makes its decisions based on their values. These parameters are as follows:
Jamming parameter
The base station decision on a node should not be based only on its current behavior but should include its past as well. This is necessary because on one hand a malicious node tries to hide its malicious behavior by running its attacks in some intervals and behaving normally in others and on the other hand a non-malicious node may temporarily act in a seemingly abnormal manner. For that reason, this measure is computed as the weighted sum of the current jamming measure
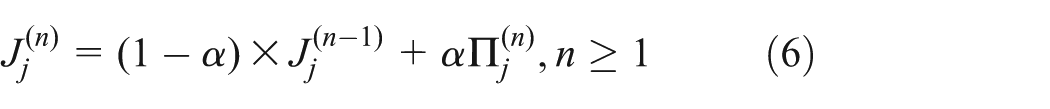
where
Selfishness parameter
For the same reasons as the jamming parameter, the selfishness parameter is computed as the weighted sum of the current selfish measure

where
Trust decision
The trust decision used here is also an improvement over the one used in Alnasser and Rikli.
33
The information gathered by the base station from all nodes is used to calculate a different trust threshold for each parameter, i.e.
if
if
if
if

Trust decision mapping.
The decision reached by the base station at this point represents the final result of this phase, which is the goal of our study. To complete the solution, the base station needs to take action against nodes detected as malicious nodes, which will be addressed in future studies. This would probably affect the operation and performance of the complete IoT system. So, an optimal solution, through the selection of appropriate weights and thresholds, should be sought through either simulation or analysis.
Performance evaluation
Network specifications
In our simulation model, we consider a WSN with nine sensor nodes with parameters as shown in Table 1. The nodes were randomly distributed over an area of
Simulation parameters.


Considered network topology.
The considered area is split into M contiguous zones. The system operates on an event basis, such that each node continuously monitors a predetermined event in its zone, and may send an alarm only when the event occurs.
Practically speaking, a fire can occur anywhere in a forest. The existing sensors surrounding this fire, as time progresses and depending on the climate conditions (wind, terrain, etc.), will initiate alarms to the base station. The zoning principle would be an approximation that simplifies the operation of the simulation model. Furthermore, contiguous zones with rectangular shapes may be the easiest non-overlapping shapes. As the size of the zones decreases, the approximation improves while the model complexity may increase.
All nodes are assumed to have the same power characteristics, as shown in Table 2. The sensor node starts with maximum energy
Energy parameters.

To measure the performance of our model, we selected five nodes representing the five types that exist in our network.
The node types and locations were chosen to study specific common situations and are supposed to be representative of all topology settings of interest. All common scenarios that could happen in such networks were covered in this proposed topology. For instance, Node 8 may receive a large number of packets, which will deplete its battery and cause packets to be dropped so that the node can save some of its energy. A second example is Node 4, which is a selfish node but will probably drop only a few packets since it will relay packets only from an edge node.
Network operation statistics
As was described in the previous sections, the various measures need some thresholds to be set. In a real system, experiments need to be run to gather the various operational statistics for both malicious and non-malicious nodes. In our current situation, simulation experiments will be used for this aim.
Energy consumption
The energy consumption for all considered nodes is basically the same, and is shown in Figure 6. After each time interval, the node’s energy decreases by 10% so that after the 5th interval it will be less than 50% of its original energy.

The variation in the percentage of the remaining energy in the considered nodes (relay node shown here).
Packets dropped
The number of packets dropped by each one of the considered nodes is shown in Figure 7. As can be noticed, in the first five intervals only the selfish node and the mixed node (due to its selfish trait) drop packets. The normal node will start dropping relayed packets when its energy level goes below a certain threshold, as is the case for Node 8.

The number of packets dropped by the considered nodes.
It can also be noticed after the energy threshold is past the 5th time interval, the number of dropped packets by the selfish and mixed nodes decreases. This is due to the decrease in the number of received packets coming from the previous nodes.
Packets generated
The number of packets generated by each of the considered nodes, along with the average number of packets generated by all nodes, is shown in Figure 8. The normal nodes (2 and 8) operate in conformance with Algorithm 1, where they generate, on average, 250 packets before the 5th time interval and then their generation rate drops. The selfish node operates similarly but keeps the same generation rate even after its energy level goes below the threshold, i.e. the 5th time interval.

The number of generated packets by the considered nodes.
The jamming node and the mixed node (due to its jamming trait) will generate many more packets than the normal or selfish nodes and keep the same generation rate irrespective of their energy level.
Packets transmitted
The number of transmitted packets by each one of the considered nodes, along with the average of all nodes, is shown in Figure 9. The number of transmitted packets consists of generated packets by the node itself and relayed packets received from the previous nodes. Therefore, each node behaves differently as follows.
Normal node (2): as it is an edge node, it has a steady number of transmitted packets up to the 5th time interval and starts decreasing afterwards.
Selfish node (4): behaves similarly to a normal node but keeps the same rate even after the 5th time interval.
Jamming node (13): transmits more packets due to its jamming behavior.
Mixed node (6): carries the jamming trait and operates similarly to a jamming node.
Relay node (8): transmits its generated packets in addition to the relayed packets received from previous nodes up to the 5th time interval. After that, it starts the dropping of received packets and generates fewer packets due to its decreased energy level.
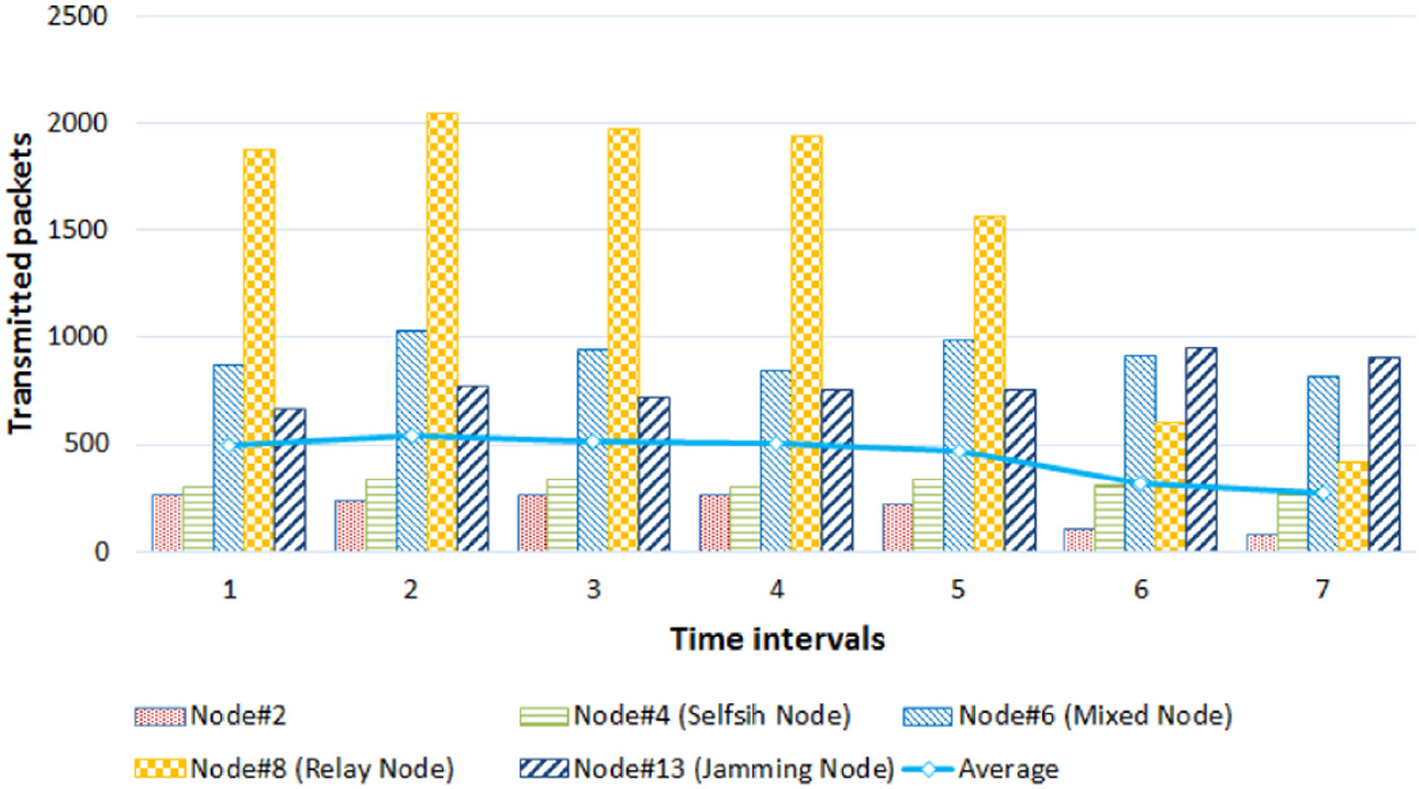
Number of transmitted packets by the considered nodes.
Results
In this section, we study the various parameters on the total trust measure and relate these to the false-negative or false-positive alarms for malicious and non-malicious nodes, respectively.
Effects of the jamming threshold
The corresponding results for a jamming node are shown in Figure 10.
as can be expected, the jamming value decreases when
for a jamming threshold equal to 0.1, the jamming node will be detected wrongly as a normal node if the trust threshold is less than 0.7;
with all jamming threshold values, the jamming behavior will be detected correctly when the trust threshold is greater than 0.77;
only for
the selfish value improves with time and is the same for all

Effects of
Figure 11 shows the corresponding results for a mixed node, which basically follows the same trends as a jamming node except for the selfish measure where it is also detected as a selfish node.

Effects of
Effects of the jamming measure threshold
In this case, the simulation experiments were run with all parameters unchanged except
(1) Normal Node
The corresponding results are shown in Figure 12. The following remarks can be made:
all jamming values are unaffected by
in all cases, the jamming value improves as time progresses;
a normal node will always be detected correctly when the trust threshold is greater than or equal to 0.7;

Effects of
(2) Selfish Node
The corresponding results are shown in Figure 13. The results are generally very similar to that of a normal node, in particular the following remarks can be made:
for
when
where this node is a selfish node, the selfish value will decrease with time.

Effects of
(3) Jamming Node
The corresponding results are shown in Figure 14. The following remarks can be made:
when
the selfish value increases with time and is not affected by changes to the jamming measure threshold.

Effects of
(4) Mixed Node
The corresponding results are shown in Figure 15. It is quite clear that the mixed node follows the same trends as the jamming node when

Effects of
Effects of the selfish measure parameter (
)
The selfish measure parameter
(1) Relay Node
The variations of
before the 5th time interval where the remaining energy is above the dropping threshold
after the 5th time interval, the selfish value continues with the same improvement trend for

Effects of
Therefore,
(2) Selfish Node
To ensure that the new measure did not affect the detection of selfish nodes, the variations of

Effects of
Effects of the relaying threshold (
)
Since the relaying threshold is the value above which a received packet will be relayed to the next-hop node, as can be expected, the effects of this parameter are mainly restricted to normal nodes that are in the routing path of other neighboring nodes. Its effects on the average false-negative of malicious nodes, as the simulation results confirmed, were minimal. Hence, only results related to the relay node shown in Figure 18 are presented and analyzed. The following remarks can be made:
when the relaying threshold is 0.9, the relay node will be detected all the time as a malicious node at a trust threshold less than 0.35;
when the relaying threshold is 0.7, the selfish value will increase and then start to decrease after the 3rd interval where the remaining energy goes below 70% of total energy; then the node will start dropping packets. The node will be detected as malicious all the time when the trust threshold is less than 0.87;
when the relaying threshold is less than 0.7, the selfish value will steadily increase with time, and the node becomes more trusted as time progresses;
the jamming value also increases with time and is not affected by changes to the relaying threshold where it is a normal node.

Effects of
Comparison with the Bayesian model
We use the Bayesian model 35 as a benchmark to evaluate the performance of the proposed model.
Measures definition
The Bayesian model uses the expected value of beta PDF defined by

where the parameters
The Bayesian parameters
Jamming measure
and

Selfishness measure

and
where
Performance
The two models were run with typical network conditions and model parameters, and the corresponding results displayed in Figure 19 for three typical nodes: relaying, selfish, and jamming.
From these results we can draw the following conclusions:
the selfish node will be detected more easily in our model than in the Bayesian model. In our model, the selfish measure starts at around 0.4 and decreases to 0.02 by the 7th time interval, while in the Bayesian model it stays almost unchanged at 0.75;
the jamming measures in both the proposed model and the Bayesian model stay almost unchanged as time progresses but with a net advantage of around 0.4 for our model;
in the case of the relay node, the Bayesian model starts with an advantage due to the fact that the proposed model starts with an initial jamming measure of 0.6. As time progresses, the proposed model catches up with the Bayesian model and surpasses it after the 5th interval when the relaying starts dropping packets.

Comparison of the proposed model with the Bayesian model for typical nodes and network conditions.
Conclusion
In this paper, we have presented some new statistical representations for the operation of concealed malicious nodes and non-malicious nodes and have devised a new trust model to detect malicious nodes of jamming and selfish types. Although the general concept is not new, there are novelties in its application to an IoT system in the proposed nodes algorithmic operations (non-malicious, jamming, and selfish) and in the designed measures for the classification and detection of nodes.
Furthermore, the proposed model is lightweight in various aspects. First, the information used in the decision is basic communication statistical data. Second, the formula used in the decision is based on simple recursive algorithmic operations that require little memory and need few computations. Third, the nodes are relieved from the computations and decision process, which is completely delegated to the base station. The results showed the adaptation of the models to the changing nodes operations, the high detection rate of malicious nodes, and the low detection errors of non-malicious nodes.
A thorough parameter sensitivity study was conducted to evaluate the performance of the model for various parameter combinations. Some general rules have been drawn up to balance between the two important performance measures, i.e. false-positive and false-negative alarms. A comparison of the proposed model with the Bayesian model showed its superiority and adaptation of detection with almost all types of nodes.
In setting the model components, the limited available energy, the low memory capacity, and the limited computational power of the sensor nodes were carefully considered. In future work, the model should be tested in other network scenarios and with different malicious behaviors.
Footnotes
Declaration of conflicting interests
The authors declare that there is no conflict of interest.
Funding
This research received no specific grant from any funding agency in the public, commercial, or not-for-profit sectors.
