Abstract
Smart meters are one of the key components of intelligent power grids. Wireless mesh networks based on smart meters could provide customer-oriented information on electricity use to the operational control systems, which monitor power grid status and estimate electric power demand. Using this information, an operational control system could regulate devices within the smart grid in order to provide electricity in a cost-efficient manner. Ensuring the availability of the smart meter mesh network is therefore a critical factor in securing the soundness of an intelligent power system. Wormhole attacks can be one of the most difficult-to-address threats to the availability of mesh networks, and although many methods to nullify wormhole attacks have been tried, these have been limited by high computational resource requirements and unnecessary overhead, as well as by the lack of ability of such methods to respond to attacks. In this paper, an effective defense mechanism that both detects and responds to wormhole attacks is proposed. In the proposed system, each device maintains information on its neighbors, allowing each node to identify replayed packets. The effectiveness and efficiency of the proposed method is analyzed in light of additional computational message and memory complexities.
Keywords
1. Introduction
Smart meters are one of the key building blocks of smart power grid systems. In such systems, each smart meter measures and transmits fine-grained electric power usage information and information on the quality of electricity to the utility, which can use this information for generating customer bills and also for automatically controlling the consumption of electricity through the delivery of load control messages to the smart meters. In many cases, smart meters form wireless ad hoc mesh networks for data delivery, and the failure of such networks could lead to improper power grid operation.
A wireless ad hoc network consists of wireless nodes, which can communicate with each other without the use of communications infrastructure. Each network communication is facilitated by the stepwise transference of a message through a series of nodes, based on the ability of each of these wireless nodes to relay to any other communications node. As such, wireless ad hoc networks can easily be constructed within relatively short periods of time and in many locations. In mobile ad hoc networks, each node can freely join and leave the network. Because of such characteristics, ad hoc systems have come into the spotlight as valuable means for building networks in ubiquitous computing environments.
As ad hoc networks are being merged into various ubiquitous and pervasive computing environments, security becomes one of the more important concerns, and much research into the development of methods for enhancing security has been conducted. In particular, secure routing protocols are now being actively developed and implemented. However, since these efforts focus specifically only on cyber-attacks launched by a single attacker, they have not considered collusion attacks, in which multiple attackers cooperate with each other in order to compromise target nodes or intercept critical information.
Wormhole attacks are one of the most dangerous threats to ad hoc networks. In a wormhole attack, a pair of attackers forms a tunnel to deliver received packets to distant points in the network by using a direct, low-latency communications link called a wormhole link. This can be done through a variety of means, including use of an Ethernet cable, long-range wireless transmission, or an optical link. Upon the establishment of the wormhole link, one attacker replays the packets forwarded from the source attacker, nullifying the efficiency of the network's wireless protocol through the use of hostile delivery activities. Many methods have been tested for detection of such attacks, including Packet leash [1], DelPhi [2], LiteWorp [3], and MobiWorp [4]. However, such methods are limited in their efficacy owing to high computational resource requirements and communication overheads.
In this paper, we propose an effective defense technique to properly detect and respond to wormhole attacks. This technique employs a cooperative approach among distributed nodes, in which each node maintains information on its neighbors. With this information, each node can identify whether or not communication routing paths have been compromised by a wormhole attack. Using this approach helps to remove some of the impractical assumptions behind existing detection methods. Moreover, the response method in the proposed approach effectively isolates malicious nodes, enhancing network security.
This paper is organized as follows: Section 2 of this paper describes existing approaches for detecting wormhole attacks. In Section 3, a proposed detection and response method is introduced. Section 4 analyzes this proposed method, and Section 5 summarizes the experimental results. Section 6 concludes the paper.
2. Background and Existing Wormhole Defense Mechanisms
2.1 Wormhole Attacks
A wormhole attack is a special type of collusion attack on ad hoc networks in which two colluding malicious nodes use wormhole links to capture and replay communicated messages in order to disrupt wireless network protocols. A malicious node snatches packets, routing them via a constructed wormhole link to another malicious node, which subsequently replays them to a distant node from which they are finally replayed back into the network. As these are legitimate network packets, other nodes will process them normally. By exploiting these wormhole-replayed packets, an attacker could launch a flooding attack or attempt unauthorized access to network services. Most seriously, since most of the packets passed through a wormhole link will not be delivered to proper designated destinations, the presence of a wormhole constitutes one of the more serious threats to network efficiency.
Figure 1 illustrates a typical wormhole attack in a wireless ad hoc network. If the network employs a dynamic source routing (DSR) protocol to establish routing paths, source S will broadcast a route request packet, and each intermediate node receiving the request packet will add its identity to the request list prior to rebroadcasting it. The destination node D generates a route reply packet for each received route request packet, and it sends the packet to source S. From the replies, source S will then select the most efficient path for routing, with the selection based either on which path has the smallest hop count or which path delivered a reply packet first. However, if two colluding attacker nodes—shown in Figure 1 as m1 and m2—deceive destination D into judging that the route containing m1 and m2 is the best path, not only will the routing protocol to establish a legitimate communications path between source S and destination D be disrupted but the routing tables in other nodes will also be compromised. In the case shown in Figure 1, when an attacker m1 receives a route request packet, it transmits the packet to the other attacker m2 through the wormhole link. The malicious node m2 then rebroadcasts this packet to its neighbors. In order to prevent the network from being filled with route request packets, each node generally drops all route requests except for the first one received; therefore, neighbors of node m2 will discard any further requests that may arrive later through legitimate hops or paths. This causes packets sent between node S and node D to always follow the link between nodes m1 and m2.
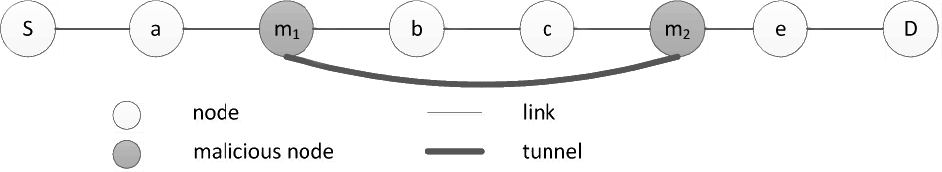
An example of a wormhole attack
Once the wormhole attack has taken place, all packets coming from nodes within the transmission range of the attackers in the networks will be delivered through the wormhole link. Consequently, attackers gain the ability to snatch and modify as many packets as they want. Thus, they can launch an attack such as a denial of service (DoS) by dropping all packets needed to be properly delivered from the sender to the destination. Furthermore, attackers can obtain statistical information on message traffic by analyzing packets passing through the wormhole.
A wormhole link between two colluding parties can be created either through a tunneling technique or an out-of-band channel. Briefly, these techniques involve the following:
Tunneling: In a tunneling attack, two malicious nodes m1 and m2 connect via a wormhole tunnel in order to launch attacks. Node m1 encapsulates the received route request packets in order to tunnel these messages to m2. Node m2 then rebroadcasts the request packets after removing additional packet headers that had been attached to the original packet prior to entering the tunnel. Thus, even though there are one or more nodes between the two malicious nodes, other victim nodes should believe that there are no intermediate nodes between them. The neighbor nodes of m2 thus believe that the distance between m1 and m2 is one hop.
Out-of-band channel: In an out-of-band channel attack, two malicious nodes m1 and m2 construct an out-of-band channel via a direct wired link or a long range wireless link in order to carry out wormhole attack. Node m1 forwards the received route request packets to m2 via the wired link. Hence, the source and the destination believe that node m1 is one hop away from node m2.
When malicious nodes form a wormhole link, they can either reveal or hide themselves in the routing path. The former condition is called an exposed or open wormhole attack, while the latter is a hidden or closed one. Under a closed attack, destination D in Figure 1 would believe that a packet from source S was transferred through nodes a and e, whereas, under an open wormhole attack, it would believe that the packet is delivered via nodes a, m1, m2, and e.
2.2 Previous Wormhole Attack Detection Methods
As wormhole attacks abuses the cost-effectiveness of algorithms underlying routing protocols, malicious nodes cause other wireless devices to misunderstand network topologies. Thus, much research had been conducted thus far in order to protect against such attacks by using temporal and geographic countermeasures.
Hu et al. introduce the concept of wormhole attacks and the concept of geographical and temporal packet leashes in order to detect them [1]. For geographical leashes, their method requires that each node has accurate location information and loose clock synchronization. When a node receives packets, it calculates the distance between previous nodes and itself by using a send/receive timestamp to derive the velocity between nodes. If the calculated distance falls above an upper bound, the node decides that a wormhole attack has taken place. For temporal leashes, each node should be accurately synchronized in time, and each packet should be delivered to the next node within the computed lifetime of the packet; otherwise, the next node should regard the path as a wormhole link. The packet leashes method does not isolate malicious nodes in response to an attack.
Wang et al. suggest another type of temporal leash [5]. In their method, each packet is equipped with data on geographic location, timestamps of receipt and delivery, and the migration authorization code (MAC) of the sending packet. The destination node then computes the propagation delay for each hop on the entire route, and each delay should be smaller than the maximum delay. The cost of detection for this solution is too high to justify adapting it for use with low-computational wireless resources on ad hoc networks.
Song et al. have analyzed the characteristic frequencies of links on network routes [6], finding that the frequencies of wormhole links tend to be much higher than those of normal links. If a wormhole attack is detected with the investigation, the scheme sends a data packet, and waits for an acknowledgement (ACK). However, the scheme has only been evaluated for routing protocols similar to split multipath routing (SMR) [7].
Chiu et al. introduce a simple delay analysis approach, DelPHI [2], which calculates the mean value of the delay per hop for every possible route, based on sender initiation of detection packets, such as route requests (RREQ) and response by the receiver to every received detection packet. After collecting all responses, the sender computes the mean value of the delay per hop for each packet, with the assumption that a wormhole would have more hops than its hop count would indicate. The scheme then analyzes computed delays to determine if there is a large difference between any two of the values. As this scheme does not employ any confidentiality or authentication service, an attacker can easily deceive the sender.
Evans et al. employed directional antennas in order to prevent wormhole attacks [8]. In their study, each node was equipped with a directional antenna; a sender broadcasted a HELLO message bearing its identity, and receivers sent back a response containing the direction from which the received HELLO message had come, allowing the sender to verify whether the response came from the same direction as the HELLO had been sent. The method is expensive, as each node needs to be equipped with a directional antenna.
Pirzada et al. proposed a trust-based wormhole detection scheme [9] in which nodes quantify trust values for their neighbors by checking whether the sent packets are retransmitted within a specified time interval. If a forwarded packet is the same as the original, the trust value of the neighbor is increased; otherwise, the neighbor's trust value is decreased. This method requires that each node set its wireless interface to a promiscuous mode; additionally, it can only be applied to networks using a DSR routing protocol.
Awerbuch et al. have designed a new secure routing protocol, (ODSBR), in order to mitigate attacks that exploit Byzantine fault tolerance limits [10]. To detect such wormholes, the protocol requires that the destination return an acknowledgement to the source for each data packet. If there is a fault in acknowledgement, the source will increase the weight of the link involved. Subsequently, links with higher weights will not be used to build routes. The disadvantage of this protocol is that nodes will be comparatively burdened and network traffic will be filled with enormous amount of acknowledgements.
Wang et al. have developed a method for observing the occurrence of a wormhole in a static sensor network [11]. Their approach employs multi-dimensional scaling to reconstruct the network, detecting an attack by observing wormhole links. Based on signal strength, each node estimates the distances to its immediate neighbors and sends this information to a centralized controller. By modeling a virtual position map of the sensors, the controller computes a wormhole indicator for each node.
Khalil et al. have suggested two wormhole detection and response methods: LiteWorp for static ad hoc networks [3] and MobiWorp for mobile ad hoc networks [4]. In these methods, information is gathered on neighbors within two hops of a node. As each node can overhear both the adjacent forwarder and its next-hop neighbor, it monitors two sets of packets forwarded, ensuring that both of these are the same. In using this approach, several monitors should be activated for links and equipped with buffers to store information on each packet delivered. The MobiWorp method requires a certified authority to verify exact location information on each node, and also requires that, whenever it moves, each node acquire authentication messages in order to transmit messages.
3. Proposed Wormhole Attack Defense Mechanism
The defense mechanism proposed here consists of two components: a method for detecting wormhole attacks and a method for responding to the detected attack. To detect wormhole attacks, information on the neighborhood of each node is used; as each packet carries a proof of its forwarding node's identity, intermediate nodes forwarding a message can detect a wormhole in the route by verifying whether or not these proofs contain only the identities associated with their neighbor nodes.
The detection mechanism is built upon the fact that each node contains a list of all paths connecting it to its neighbors. In deploying a network, each node should build such a list, and when a new node joins the network, it should also construct a corresponding neighbor list, while its new neighbors should update their own lists. When a node transmits or forwards a packet to a neighbor, it should insert a proof of its identity into the packet so that the next-hop node can verify the proof of identity in the packet by checking that the proof is associated with the previous node.
For this mechanism to work, each node uses a secret key, held only by that node, to generate a temporal key (TK). During the building of a neighbors list, TK serves as an authentication key. In addition to its neighbors list, each node maintains a key list consisting of a pair-wise listing of secure keys shared between the node and its neighbors. Based on this verification method, each node can detect a wormhole attack, and a response involving dropping packets forwarded by attackers or delivered through a wormhole to isolate such attackers from the network can be adopted.
3.1 Detection of Wormholes
3.1.1 Indication of Wormhole Attack
The detection of wormhole attacks through the recognition of various attack symptoms has been addressed in previous studies. These symptoms include the following:
Longer propagation delay than expected by the source node: When a tunneling wormhole attack is launched by malicious nodes, the number of hops indicated in an information packet will be less than that in the real routing path, as colluding malicious nodes remove hops between them. Figure 1 illustrates this, contrasting seven real hops between source S and destination D with only five hops indicated to the source node under the shown wormhole attack. A disparity between the actual propagation delay time and that suggested by the number of hops indicated in the information packet, then, might be an indication of a wormhole attack.
Longer delay per hop: Total propagation delay divided by total number of hops on the route is the average delay per hop. If the source selects the route through a wormhole as a message delivery path, the average delay per hop calculated by the sender will have a high probability of being longer than that of any other regular path. Accordingly, if each node knows the average delay per hop on a wormhole-free route, the source will have evidence of a possible wormhole in the path.
Larger transmission power than that for a normal node: Two malicious nodes can employ high power antennas to establish a wormhole connection with a propagation range large enough for the nodes to communicate directly. In such a case, a normal neighbor node might notice an unusual amount of transmission power in the region, indicating a wormhole attack.
Two consecutive nodes in a routing path are not neighbor of each other: Generally, two successive nodes in a routing path should connect with each other by a single-hop communications link. However, if a source node selects a routing path containing a wormhole, at least one pair of consecutive nodes in the resulting path will not be one-hop neighbors, nor will these nodes be aware of the fact.
In developing the method described in this paper, the last test for detection listed above has been focused upon, since either accurate time synchronization or monitoring burden should be needed to employ a detection method using any other symptoms. As monitoring systems should observe each transmitted packet, wormhole attack detection methods using the first three methods would be less effective, in terms of synchronization and monitoring load, in monitoring an ad hoc network as compared to a method involving examination of packets for signs of false one-hop neighbors. Those two assumptions are too impractical to apply the wormhole attack detection method, which investigates one of first three evidences. Thus, the detection method that uses the last indication is more effective one for ad hoc network than the others.
An easy way to test for indications that adjacent path nodes are not one-hop neighbors would involve each node checking whether a node forwarding a packet is actually in the receiving node's neighborhood. A pair of attackers building a wormhole would deceive a receiver node into believing that no intermediate node exists between a forwarder and a receiver. This is illustrated in Figure 1, where m1 and m2 link to each other with a wormhole. Node m1 will deceive node e into believing that node m1 is a one-hop neighbor of node m2. To defeat this wormhole attack, then, m1 and m2 must be prevented from deceiving their neighbors in this way, and if a node can search the neighbors list of a forwarder, it can easily decide whether a packet came through a wormhole or not. Turning again to Figure 1, it is assumed that node e maintains a list including all of its neighbors. If a hidden wormhole attack is launched by malicious nodes m1 and m2, node e can check whether node a is in its neighbor list or not if it receives a packet from node a: if so, node e can then transmit the packet to the destination node d; otherwise, it can regard the route as a wormhole.
Another possibility must be considered, however, in which a node does not detect an exposed wormhole with direct neighbor information because one of the attackers is actually a neighbor of the node. If it is supposed that an exposed attack is being launched by nodes m1 and m2 in Figure 1, then node e's neighbor list will confirm m2 as the previous node on route. Thus the node e may not be able to detect the wormhole. However if e is able to perceive m1 as not being a neighbor of m2, it can still identify the wormhole. Therefore, in order to detect neighboring malicious nodes, each node must gather information on two-hop neighbors as well as one-hop neighbors.
3.1.2 Building a Neighbor List
In order to build a neighbor list containing information on each path to one-hop and two-hop neighbors, all nodes newly joining a network will broadcast an announcement message-called a two-hop broadcast—which is valid until it has been sent over two hops. A node receiving this announcement forwards the packet to its neighbors only if, after decrementing by 1, the time to live (TTL) value is 1. Each node receiving the announcement should return an ACK to the new node, and when the new node receives this ACK, it registers the responder as a neighbor only if the ACK is valid. In the process, the new node and its neighbors will set up a new session key for further data communication. The detailed process of building such a neighbor list, illustrated in Figures 2 and 3, is as follows:

Detail of the process of adding a 1-hop neighbor to a neighbor list, showing newly joining node C and its 1-hop neighbor A

Detail of the process of adding neighbor information to a neighbor list, showing newly joining node C and its 2-hop neighbor B
A newly joining node C broadcasts an announcement message saying that a new node has just joined the network. This packet includes the identity of the node IDC, and an authenticator HMACTK(C)(IDC). In order to generate this authenticator, the node employs a keyed hash function such as a keyed-hash message authentication code (HMAC). The identity of the node and the TK generated by the secret key are provided as inputs to this HMAC function, and the result of the HMAC is used as the authenticator. The TTL value of the announcement is set to 2 for a two-hop broadcast.
When a node receives an announcement message, it first checks the TTL value. According to the value, each node notices what kind of neighbor it is. If the TTL is 2, then the receiving node is a one-hop neighbor of the new node; if the value is 1, then the node is a two-hop neighbor. Based on this determination, each node will perform one of the following:
One-hop Neighbor: As shown in Figure 2, after receiving the announcement message, node A decreases the TTL value by 1 and relays the packet by broadcasting it. After this, it stores the source's identity, IDC and, the authenticator HMACTK(C)(IDC) then sends back to the new node an ACK including its identity IDA, parameters for a Diffie-Hellman key exchange algorithm, PK(A), and its authenticator HMACTK(A)(IDA).
Two-hop Neighbor: If the TTL value is 1, then the node is a two-hop neighbor of the new node C. As shown in Figure 3, after node B receives an announcement message, it stores the new node C's identity, IDC, HMACTK(C)(IDC), and the previous node's identity (in this example, IDA). After this, it sends an ACK message to the new node C just as the one-hop neighbor has done; if node B already has sent an ACK to the new node C, the ACK message will not contain PK(B), because its parameters are needed for a session key exchange and only one shared-session key is required between the new node C and the two-hop neighbor, node B.
When the announcer (that is, the new node C) receives an ACK message from any neighbor, the node keeps the identity and the authenticator in the packet. If the ACK comes from a two-hop neighbor, the announcer also saves the identity of the node previous to the two-hop neighbor, which relays the ACK came from the two-hop neighbor. The announcer then generates a session key by using the PK(X) included in the packet for the Diffie-Hellman key exchange algorithm. This session key will be shared between node C and the sender of the ACK. If at this moment the packet does not have parameters, node C checks whether there is an entry having the same identity in the neighbor list, and if one is listed as a two-hop neighbor, it registers the identities of the two-hop neighbor and of the forwarder (i.e., IDB and IDA, respectively, in this example) as neighbors having a different route. Otherwise, the packet is discarded. If C generates a new session key in this step, it responds to the ACK by sending a reply message that includes parameter PK(C) for the Diffie-Hellman algorithm, its temporal key TK(C), and a random nonce N. The temporal key and the nonce are encrypted with the new session key (in this example, SK(A,C) for node A, or SK(B,C) for node B).
Once a node receives a reply message, it generates its own session key: node A, for instance, will generate SK(A,C) while node B will generate SK(B,C). Using this key, the node obtains the sender's temporal key TK(C) and nonce N, and by using the temporal key, it verifies whether or not authenticator HMACTK(C)(IDC) stored in step 2 came from node C. If this verification succeeds, the neighbor sends the announcer a commitment message, which should be encrypted with the session key, including N+1 and its temporal key (TK(A) or TK(B) in this example). Otherwise, it terminates the list-building process. After sending the commitment message, the neighbor then updates its neighbors list with the announcer's identity.
When the announcer receives the commitment message, it obtains the temporal key of the sender and the incremented nonce N+1. It then checks these against the sender's nonce and authenticator, which were saved in step 3, and if this check succeeds, it registers the sender as a neighbor. Each entry in the neighbors list is a pair of neighbors' identities, such as (ID1, ID2). For listing a one-hop neighbor, the second object of the pair ID2 is filled with a null value. For a two-hop neighbor, a pair consisting of the identities of the forwarder (as ID1) and the sender (as ID2) is constructed. For example, if an announcer C receives a commitment message from a one-hop neighbor A, it adds (IDA, null) to its neighbor list. The announcer also adds a pair including the neighbor's identity and session key to its key list; for example, for neighbor A the announcer will insert (IDA, SK(A,C)) into its key list.
Figure 4 shows an example of a successfully built neighbor list. As illustrated in the Figure, node C and node D can be both one-hop and two-hop neighbors at the same time. Additionally, node E is both a one-hop neighbor of node B and a one-hop neighbor of node C. All of this information is encoded in A's neighbor list, shown in Figure 4. It should be noted that since node G is not a neighbor of node A, there is no information on G in the neighbor list.

An example of a completed neighbor list
In sending the messages detailed in steps 1 to 4 above, each node waits for the responses of its neighbors over expected time intervals that can be calculated with the following equations:
ti,n is the time interval between the new node and its neighbors, with n being one (for one-hop neighbors of the new node) or two (for two-hop neighbors). dp is the propagation delay in the air calculated by Equation (2), where c is the velocity of light in the medium of transmission in meters per second, and r is the maximum transmission range in meters. dt,n is the transmission delay of each node, with S being the number of bits in the message and R the rate of transmission in bits per second. The three possible values of n from 0 to 2 indicate a new node, a one-hop neighbor, or a two-hop neighbor, respectively. δn is the processing time for one-hop and two-hop neighbors.
If a one-hop neighbor and a two-hop neighbor form a wormhole, the journey time of a message between them will be longer than that for any other hop. Therefore, each node, which participates in the process of building a list, should discard any response (or acknowledgement) that arrives after the interval calculated above.
3.1.3 Detecting a Wormhole
After it has joined the network, each node will have a neighbor list and a key table, and in transmitting a packet, the node will attach two sets of data pair to the packet. A data pair includes two sorts of data — one indicating the identity of the node, and one indicating proof of the identity of the node. The first set of data pair is for the one-hop neighbor of the node, which is transmitting a packet, and the second one is for the two-hop neighbor of the node. Thus, the proofs computed by means of a session key shared between the transmitter and the corresponding neighbor node by a keyed hash function such as HMAC. By using this method, a wormhole can be detected by the next node of the transmitter in the route. In order to limit packet data use, information is maintained only from the two previous hops taken by the message; in other words, when a node receives a packet for forwarding to its neighbor, if there are already four pairs attached to the packet, the node removes the first two pairs before attaching its own pair. This method is illustrated in Figure 5.

A breakdown packet information pairs: identities and MACs
A node, n3, receiving a packet from its neighbor, n2, will perform one-hop and two-hop neighbor correctness tests on the packet. To test one-hop correctness, n3 searches its neighbor list for the identity of n2, and if an entry (n2, null) exists, n3 verifies its proof of identity for n2 against n2's forwarded proof of identity. If these are identical, n3 will believe that n2 is not a wormhole node; otherwise, it will drop the packet and distrust n2. If there is more than one set of identity and proof of identity in the received packet, a test for two-hop correctness is carried out, and n3 checks whether or not node n1 is a two-hop neighbor. If the entry (n2, n1) exists and n1 is proven to be valid, the node n3 trusts that n1 is a two-hop neighbor; otherwise it drops the packet and distrust n1. If n3 and n5, as shown in Figure 5, are wormhole nodes, then the second entry of the last set of information pair cannot be generated by n3, as it n3 does not have the session key
3.2 Responding to a Wormhole
The failure of either of the two correctness tests described above would indicate that the route hosts a wormhole and also that a node related to the failed test might be malicious. If a malicious node that replays packets from a wormhole's entry node is detected, this node can be isolated from the network by dropping packets sent from it. In the method proposed here, if a node decides that another node is malicious based on the tests described above, it will then send a notification message to its neighboring nodes—encrypted with each node's session key—and every node so notified will drop any packets originating from the malicious node.
Every possible result of the test is shown in Table 1. Depending on table outputs observed, it will not necessarily be possible to perfectly identify attackers. It is easy to identify the replaying node at the end of a wormhole in two of the four attack cases described (i.e., in the first and the second rows): in these scenarios, the one-hop neighbor node of the tester will be an attacker. It is possible to identify an attacker by looking at MAC address in the received packet. If the MAC address of the previous node does not match that in the MAC header of the received packet, then the owner of the address in the header will be a malicious node.
Results of the neighbor correctness test.

However, in the other two cases (i.e., the third and the fourth row) it will be difficult to ascertain whether the previous node is malicious or not, as in these cases the last entry of the example route could either be a normal node or an attacker. To locate attackers with precision, a node, which detects wormhole, can employ a reverse test. Based on such a reverse tests it is possible to easily identify all two-hacker configurations aside from hidden wormholes. In a reverse test, a node X, which detects wormhole attack, sends a test message to the original sender of a packet replayed via a detected wormhole attack, using the same route through which the replayed packet came. If, in the transmission of the test message back to the sender, another normal node Y, is also able to detect a wormhole attack, then node Y will send a reply message to the sender of the test message (node X). The reply message includes the results of the neighbor correctness test and the identity of the test message forwarder. According to the results of correctness test and the changes of the last two nodes en route, node X can identify attackers as follows:
If the result of the correctness test is (Yes, No) and a change has not been occurred, an exposed wormhole attack has been launched by two nodes attaching authentication information to the packet.
If the result of the correctness test is (Yes, No) and a change has been occurred, a known exit wormhole attack has been launched by two nodes, where one attacker is the node that inserted the last two authenticator pairs into the original packet, and the other attacker is the node that added the last two authenticator pairs to the reverse test message.
If the result of the correctness test is (No, No) and a change has been occurred, known entrance wormhole attack has been launched by two nodes, where one attacker is the node that inserted the last two authenticator pairs into the original packet, and the other is the node that added the last two authenticator pairs to the reverse test message.
If the result of the correctness test is (No, No) and a change has not been occurred, a hidden wormhole attack has been launched by two nodes. In this case, it is not possible to exactly identify the attackers.
4. Analysis of the Proposed Protocol
4.1 Security Analysis
Since the proposed method detects wormholes based on information about neighbors' identities, it can detect any kind of wormhole:
In exposed wormholes, each packet arriving at a next node of the wormhole's exit includes identities and authentication codes for the wormhole ends. Thus, this node (the next node of the wormhole) would be able to detect wormhole-replayed packets since it would not be able to find the identity of the wormhole entrance node in its neighbor list. Even if a malicious node were to fabricate its identity, the next node would notice this since the malicious node wouldn't be able to generate a session key for the spoofed identity and it wouldn't be able to compute the HMAC for its identity.
In the case of a known-exit or -entrance wormhole, the method proposed would be able to properly detect the wormhole and prevent a wormhole attack from acquiring benefits of replaying the packet.
In the case of a hidden wormhole, the proposed approach would be able to inhibit malicious nodes from profiting from packet replaying; however, it would not be able to identify the malicious nodes in a hidden wormhole attack.
Several potential attacks against the method developed in this paper are envisioned. Below, they are described and methods for properly handling them are detailed:
False two-hop neighbor registration: In the process of building a neighbor list, a node may be deceived by other malicious nodes into believing that they are neighbors. This can be done, for instance, if a malicious one-hop neighbor sends a node's announcement to another malicious node via a wormhole. Such false registration can be thwarted by requiring that each packet exchanged between a new node and a neighbor be delivered before the expiration of the time interval. As the journey time through the wormhole exceeds the time interval, the attempt would be detected.
Denial of Service (DoS) or flooding attack: As a new node builds its neighbor list, it will transmit many messages over local areas of the network. By using this characteristic, a DoS attack can exploit transmission activity by flooding the network with a continuous series of announcements and acknowledgements. However, such an attack could also be stopped by use of time interval restrictions on exchanged messages discussed above; additionally, such an attack could be detected by screening for nodes which engage in the abnormal activity of continuously gathering neighbors' information.
Misconceived malicious node: An attacker may try to make a normal node malicious by launching a hidden wormhole. However, as such an attack would not identify the entrance of the wormhole, an attempted attack could be properly neutralized.
Man-in-the-middle attack: The Diffie-Hellman key exchange algorithm is vulnerable to a man-in-the-middle attack, in which an attacker between a new node and a normal node intercepts packets originating from each of them and masquerades both as a new node (in order to fool the normal one) and as a normal one (in order to deceive the new node). As a result of it, each node shares a different session key with the attacker. However, in the proposed method, two parties should exchange their identity encrypted with the secret key, and the only node who knows the secret key is the owner of the secret key. Moreover, they can trust that they share a session key without the attacker. They give their secret key to each other at the final step of building neighbors list. Since the secret key is encrypted the session key, if they have different session key, they cannot achieve a secret key of each other. Thus, they should then be confident that the proper session key will not be shared with any possible attackers, and the procedure will not be done properly.
4.2 Performance Analysis
To analyze its performance, the effectiveness of the proposed method, in terms of number of messages exchanged during the building of a neighbors list and in terms of memory usage, have been modeled.
In building a neighbors list, a new node exchanges many messages with its neighbors: for each neighbor, four messages should be exchanged. Thus, if the new node has n one-hop neighbors and m two-hop neighbors, 4(n+m) messages should be delivered; if there are n neighbors for each node in a network, then the number of messages transferred will be 4(n+n2). However, as discussed in section 3, some node neighbors are both one-hop and two-hop neighbors, and a node can neighbor several others. Using this formulation, the number of messages transferred will then be 4(1-ρ)n2 where ϱ is the probability that each node is a neighbor of two other nodes. Figure 6 plots the number of messages transferred against the number of one-hop neighbors for several values of this probability.
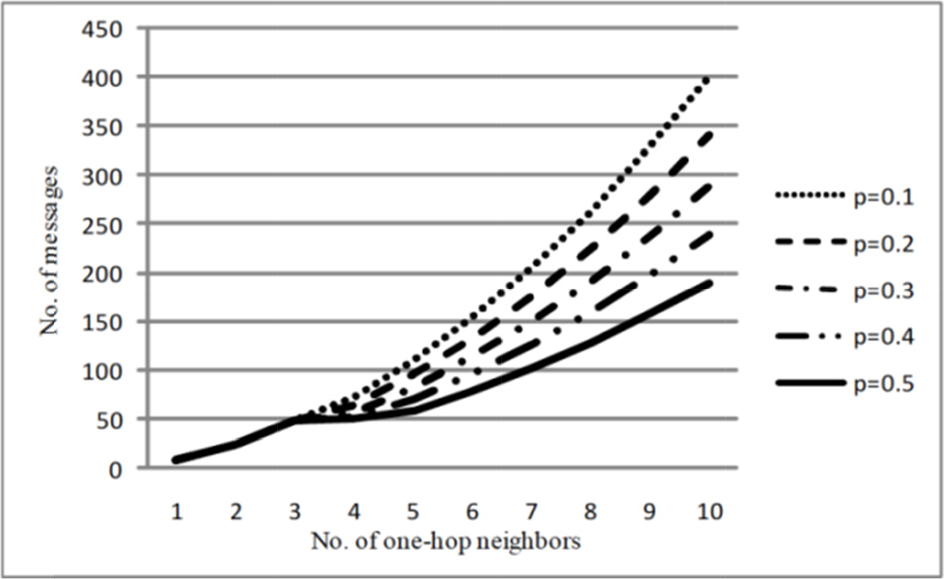
Number of messages transferred during the building procedure.
In the proposed method, a list of neighbors is built, with each list entry containing two 4-byte identities. The memory used for the list would then be n(1+(1+ρ)n) bytes, where n is the number of neighbors for each node in the network. For example, if there are 6 neighbors for each node and the probability is 0.4, the amount of memory used would be approximately 226 bytes. For n less than 13, the amount of used memory would be less than 1 kilobyte (KB) - a reasonable amount of memory for even a sensor node.
5. Simulation Results
The ns-2 simulation environment was used to simulate data exchange scenarios in wireless ad hoc networks, both under a base case assuming no protection and a case employing the proposed mechanism. In the simulation, 100 nodes were distributed randomly over a 180m×180m square-shaped field, implying a density of nodes of 0.3%. Since the number of malicious nodes varied from 0 to 6, the corresponding number of wormholes varied from 0 to 3. The simulation used a dynamic source routing (DSR) protocol that floods route requests and unicasts route replies in a reverse direction. When a malicious node received a packet, it directed the packet to the other end of its wormhole using packet encapsulation; for packet encapsulation, it was assumed that the colluding nodes always have a route between them. All nodes except for malicious ones acted as data sources, generating messages using an exponential random variable with an inter-arrival rate 0.2. Message destination was chosen at random and is altered by use of an exponential random distribution with rate 0.02.
Figure 7 plots the number of packets dropped as a function of the simulation time for sets of two and four colluding nodes – both in the baseline case lacking a defense mechanism and assuming a proposed defense mechanism – for an attack started 50 seconds after the beginning of the simulation. In the baseline case, the cumulative number of packets dropped continued to increase constantly with time; after employing the proposed defense mechanism, however, the cumulative number of dropped packets stabilizes, although this cumulative number does continue to grow for some time after the wormhole is isolated from the network, since under the DSR protocol the cached routes including the wormhole will continue to be used for a predefined time. The differential in cumulative dropped packets can be attributed to the fact that, under the defense mechanism wormhole attacks are identified during message routing and permanently isolated.

Cumulative number of packets dropped by an attacker
Figure 8 plots the average latency of the network against the number of malicious nodes, both in the baseline case and with a defense mechanism. With the defense mechanism installed in the network, the average latency is increased by as much as 50%, which would be expected if each hop involved in relaying the message verified authentication performed in previous hops. However, the absolute value (0.02 seconds) of this improvement is not significant enough to justify employment of the proposed mechanism in wireless ad hoc networks. Figure 9 shows that the packet loss ratio with the proposed defense mechanism was below 3%.

Average latency over simulation time

Packet loss ratio, both with and without defense mechanism
6. Conclusion Remarks
We propose a wormhole attack defense mechanism that detects and responds to attacks on a smart meter mesh network underlying an intelligent power grid system. This detection methodology is based on the collection by each newly joining node of information on its one-hop and two-hop neighbors. Based on this collected information, the joining node builds a neighbors list and shares a session key with each of its neighbors. In forwarding packets, each node attaches an identity and a self-generated authenticator, and based on this attached information, the next node checks whether or not the previous node is a neighbor. In response to a wormhole attack, the proposed method drops packets replayed from the wormhole and advertises the exit node of the wormhole to the network. Since the proposed mechanism can detect a wormhole attack upon delivery of a packet, it can mitigate such an attack as soon as it is launched. The proposed mechanism can detect any kind of wormhole attack and is capable of overcoming most conceivable vulnerabilities to these. From analysis of simulation results, we have concluded that use of the proposed wormhole attack defense mechanism would involve relatively modest computational and communications overhead, and that the proposed approach is effective as described in the analysis. The proposed approach to wormhole defense described here has the potential to help wireless ad hoc networks improve security.
Footnotes
7. Acknowledgments
This work was supported by the Power Generation & Electricity Delivery of the Korea Institute of Energy Technology Evaluation and Planning (KETEP) grant funded by the Korea government Ministry of Knowledge Economy (No.2010101040046A and No. 2011101050001A)



