Abstract
Lightweight ciphers are often used as the underlying encryption algorithm in resource-constrained devices. Their cryptographic security is a mandatory goal for ensuring the security of data transmission. Differential cryptanalysis is one of the most fundamental methods applicable primarily to block ciphers, and the resistance against this type of cryptanalysis is a necessary design criterion. ANU-II is an ultra-lightweight block cipher proposed in 2017, whose design offers many advantages such as the use of fewer hardware resources (logic gates), low power consumption and fast encryption for Internet of Things devices. The designers of ANU-II claimed its resistance against differential cryptanalysis and postulated that the design is safe enough for Internet of Things devices. However, as addressed in this article, the security claims made by designers appear not to be well grounded. Using mixed-integer linear programming–like techniques, we identify one-round differential characteristic that holds with probability 1, which is then efficiently employed in mounting the key recovery attack on full-round ANU-II with only 22 chosen plaintexts and 262.4 full-round encryptions. The result shows that the designers’ security evaluation of ANU-II against differential cryptanalysis is incorrect and the design rationale is flawed. To remedy this weakness, we provide an improved variant of ANU-II, which has much better resistance to differential cryptanalysis without affecting the hardware and/or software implementation cost.
Introduction
With a rapid development of 5G technology and networks, the demand for Internet of Things (IoT) devices is constantly increasing in daily life. The information exchange between IoT devices is commonly performed through embedded encryption algorithms for the reasons of providing secure data transmission, device authentication and other sensitive services. A majority of the IoT devices (especially sensors and microcontrollers) implement as encryption algorithm a class of lightweight block ciphers that are designed to operate under certain power, memory and/or computation constraints. 1 In general, this family of ciphers is characterized by a low hardware implementation cost and low power consumption, while at the same time providing sufficient security margins in sensitive applications. On the other hand, for applications without the mentioned limitations, traditionally designed encryption algorithms (e.g. advanced encryption standard (AES)) generally have lower computing efficiency due to their robust design rationales.
Being more suitable for use in restrained environments, lightweight block ciphers have attracted much attention of cryptographic society. To date, there are numerous lightweight block ciphers that have emerged during the last decade, including PRESENT 2 that uses a substation permutation network (SPN), the LBlock 3 cipher implementing the Feistel network, Simon and Speck 4 having highly efficient (fast) software and hardware implementation, and RECTANGLE 5 using the so-called bit-slice technology.
Differential cryptanalysis 6 is one of the earliest generic cryptanalytic tools (along with linear cryptanalysis) applicable to block ciphers. This technique is currently well understood and for testing the resistance of ciphers against differential cryptanalysis the following approach is commonly applied. First, lower bounds on the number of active substitution boxes (S-boxes) is estimated and then a propagating differential characteristic with as high probability as possible needs to be specified. However, the computational complexity of specifying optimal differential paths (involving a few active S-boxes and holding with a high probability) grows exponentially with the number of rounds, which leads to efficient use of different algorithms that may identify optimal solutions.
The use of mixed-integer linear programming (MILP) techniques for this purpose has been quite a common method during the last decade. In 2011, lower bounds of the number of active S-boxes for Enocoro128v2 and AES were obtained by Mouha et al. 7 using MILP-based models. This approach is, however, only applicable to byte-oriented block ciphers. To fill this gap, Sun et al. 8 extended the byte-oriented MILP model to bit-oriented block ciphers for the purpose of searching for lower bounds on active S-boxes and good (having a high probability) differential characteristics. Also, in the work of Sun et al., 8 a heuristic search algorithm for finding the best differential characteristic was proposed. Later, automated MILP-based search algorithms have been widely used to evaluate the security of block ciphers with quite outstanding results. Fu et al. 9 applied MILP-based techniques to ARX ciphers, where also a search for good differential characteristics and a linear approximation of the SPECK block cipher were addressed. Abdelkhalek et al. 10 further developed the MILP modelling for (large) S-boxes to optimize the probability of differential characteristics. In addition, Sadeghi et al. 11 presented zero-correlation linear approximations and the related-tweakey impossible differential characteristics for the block cipher SKINNY. Zhou et al. 12 greatly improved the efficiency of MILP-based search algorithms by embedding the divide-and-conquer idea into the MILP model. In Crypto2020, 13 a novel MILP model with the possibility of handling simultaneously the propagation of differentials and their values was developed. In FSE2021, 14 a suitable MILP model for finding more efficient distinguishers that cover more encryption rounds was introduced.
ANU is an ultra-lightweight block cipher proposed by Bansod et al.
15
However, the full-round ANU cipher was broken by Sasaki
16
using the related-key boomerang attack. ANU-II is an improved version of ANU and was proposed by Dahiphale et al.,
17
which is superior to ANU in terms of memory, latency, throughput and power consumption. However, in 2020, Wang et al.
18
conducted an eight-round integral attack on ANU-II (designed for 25 encryption rounds) and mounted a key recovery attack using
Our contributions
We investigate the security of ANU-II and the main contributions are summarized as follows:
First, we construct an accurate MILP model for specifying exact lower bounds on the number of active S-boxes for ANU-II. Most notably and quite surprisingly, this model identifies an interesting property that the lower bounds of the minimum number of active S-boxes of any round always equal zero.
Then, by observing the input and output of each round, we unexpectedly (disproving the claims made by the designers) find a one-round iterative differential characteristic with probability 1.
Consequently, using repeatedly found one-round differential characteristic, we could mount a key recovery attack on the full-round ANU-II (consisting of 25 encryption rounds), which shows that the design has severe security flaws.
Finally, we propose an improved variant of ANU-II with the same hardware or software implementation expenses as the original cipher. Compared to the actual design, this variant is much more robust against differential cryptanalysis.
The summary of our main results and the previous works is shown in Table 1.
Existing attacks on ANU-II.

Organization
The article is arranged as follows. In the ‘Preliminaries’ section, we introduce some basic notations and give a description of the ultra-lightweight block cipher ANU-II. A MILP-based differential search model for a minimal number of active S-boxes is given in the ‘Bit-oriented MILP model for differential analysis’ section. In the ‘Differential cryptanalysis of ANU-II’ section, a one-round iterative differential characteristic with probability 1 for ANU-II is specified, along with its application to the full-round key recovery attack. In the ‘An efficient modification of ANU-II’ section, we propose a new modified variant of ANU-II and estimate its resistance against differential cryptanalysis. Some concluding remarks are given in the ‘Conclusion’ section.
Preliminaries
Notations
The following notations are used throughout the article:
⊕: XOR;
∥: concatenation;
The description of ANU-II
ANU-II is an ultra-lightweight block cipher with a 64-bit block size and an 80/128-bit key size. ANU-II belongs to the family of Feistel networks and uses iteratively 25 encryption rounds. We mainly focus on the variant of ANU-II that uses a 128-bit master key. Let the left- and right-branch inputs of the rth round be denoted as

The round function of ANU-II.
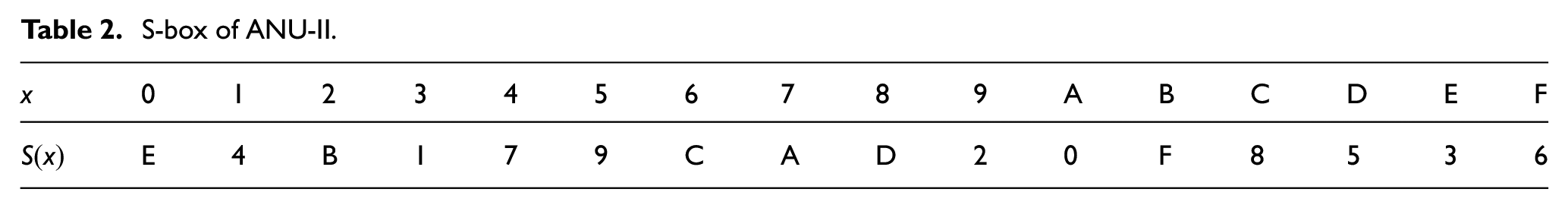
There are four operations used in the round function: SubBox, AddRoundKey, Rotation and XOR. Among these, the operation SubBox is the only non-linear component and it employs eight S-boxes of size
Key schedule
When the master key is of length 128 bits, the key schedule extracts 64-bit key and XOR these with the intermediate encryption state. The first-round subkey is equal to the master key, and the update process for deriving round subkeys is as follows





Rotation to the left by 13 bits

Applying S-box operation


Applying S-box and XOR with a round constant
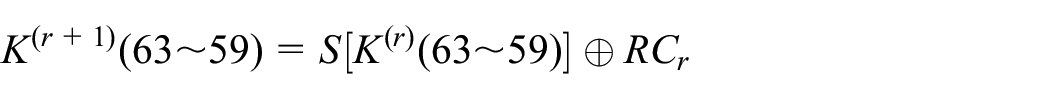
Note that the S-box in the above key schedule still uses the description in Table 2, and the value of
S-box of ANU-II.
Bit-oriented MILP model for differential analysis
MILP is a type of integer linear programming, especially suitable for solving optimization problems. Its goal is to minimize or maximize the value of the objective function under certain linear constraints. At the moment, commercial software such as in Sun et al. 19 is usually used to solve such optimization problems. In this section, we introduce a bit-oriented MILP model for searching the exact lower bounds of active S-boxes with respect to propagation of differentials and the best differential characteristics in the single-key model.
Searching for the exact lower boundsof active S-boxes
To identify which S-boxes are active when specific differentials pass through the intermediate states of a given block cipher, we recall the following notation.
Definition 1
Let

Definition 2
Let

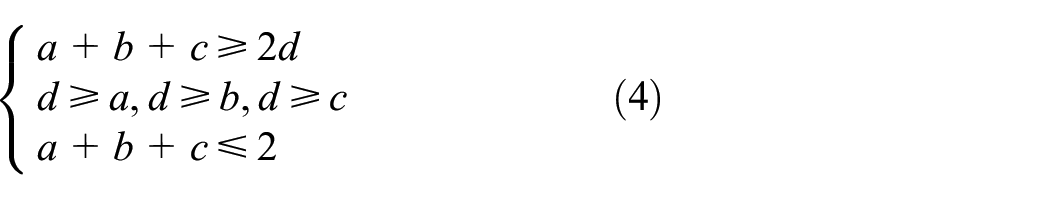
Next, we explain how to model diverse operations, such as: SubBox, XOR, and linear layer operation.
SubBox
Assume that

In addition, we need to consider the propagation of differential values through an (active) S-box. Using the

where
For instance, let

Getting
Similarly, we can convert all possible differential propagation patterns into inequalities in accordance to the differential distribution table (DDT) given in Appendix 1 for the S-box of ANU-II. SageMath is generally used to transform possible differential patterns into a large number of linear inequalities.
When this phase is completed, some redundant inequalities need to be excluded. To achieve this, commonly two methods are used: the greedy algorithm by Sun et al. 19 whose removal of redundant inequalities is not optimal and the MILP-reduced algorithm introduced by Sasaki and Todo. 21 The latter algorithm is preferred in this article since it appears to be more efficient in removing redundant inequalities than the greedy algorithm.
XOR
Let
where
Linear operation
For ciphers that employ the Feistel network, the rotation and branch swapping are both included when modelling the linear layer operation. These operations can be efficiently described by linear equalities. To clarify this, we consider the right (cyclic) rotation of ANU-II as an example. Suppose the input is

An initial constraint
The inequality
The objective function
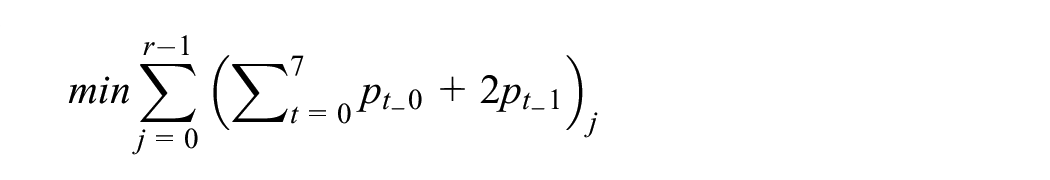
The r-round objective function, minimizing the number of active S-boxes, is set as (

where
Searching for the best differential characteristic
To find the best differential characteristic, we encode the probability information for possible differential patterns of an S-box. Except for the non-linear SubBox operation, the constraints induced by the XOR and Rotation operations are same as described in the ‘Searching for the exact lower bounds of active S-boxes’ section.
SubBox
We consider the 4-bit S-boxes of ANU-II block cipher. There are three non-zero differential probabilities according to the DDT of S-box: 16/16 = 20, 4/16 = 2−2 and

For instance, the possible differential pattern (0000 → 0000) can be expanded from the eight-dimensional tuple (0,0,0,0,0,0,0,0) to the 10-dimensional tuple (0,0,0,0,0,0,0,0,0,0). Similarly, using the DDT, the differential pattern (0001 → 0101) with probability
The MILP-reduced algorithm is then applied to remove redundant inequalities.
The objective function
Since equation (7) only describes the probabilities of differentials of a single S-box, we need to introduce additional notation to refer to different S-boxes used. Using

where the integer representation 0, 2 and 3 of the binary tuple

An initial constraint
We need to add the inequality
Differential cryptanalysis of ANU-II
In this section, we first establish an MILP model that specifically searches for lower bounds on the number of active S-boxes for ANU-II. Then, again using our MILP model, we specify a single round differential characteristic that holds with probability one. Finally, we mount a key recovery attack on the full-round ANU-II that only requires
The exact lower bounds of the number of differential active S-boxes of ANU-II
In the single-key setting, the linear constraints discussed previously include SubBox, XOR, rotation and the initial constraint. Assume that 64-bit input difference is
SubBox
ANU-II employs the Feistel network and uses eight S-boxes of size
Essentially, equation (10) indicates whether the first S-box is active, whereas equation (11) specifies the propagation of differentials through the first S-box. Similarly, one can specify the constraints for the remaining seven S-boxes of ANU-II


Linear operation
We consider one of the cyclic rotation of ANU-II as an example. Suppose that

XOR
We only consider the constraints for the first XOR operation. (Similarly, the constraints for the second operation can also be attained.) Let

An initial constraint

The objective function
Set the r-round objective function as

At this point, all inequality constraints are specified and a search for the best lower bound on the number of active S-boxes can be performed. We utilize the commercial software Gurobi 22 for this purpose. The experimental results are shown in Table 3, and most notably, the lower bound on the number of active S-boxes equals 0. This observation is very interesting and it essentially indicates that ANU-II might have some serious design flaws.
Lower bounds on the number of active S-boxes for ANU-II.
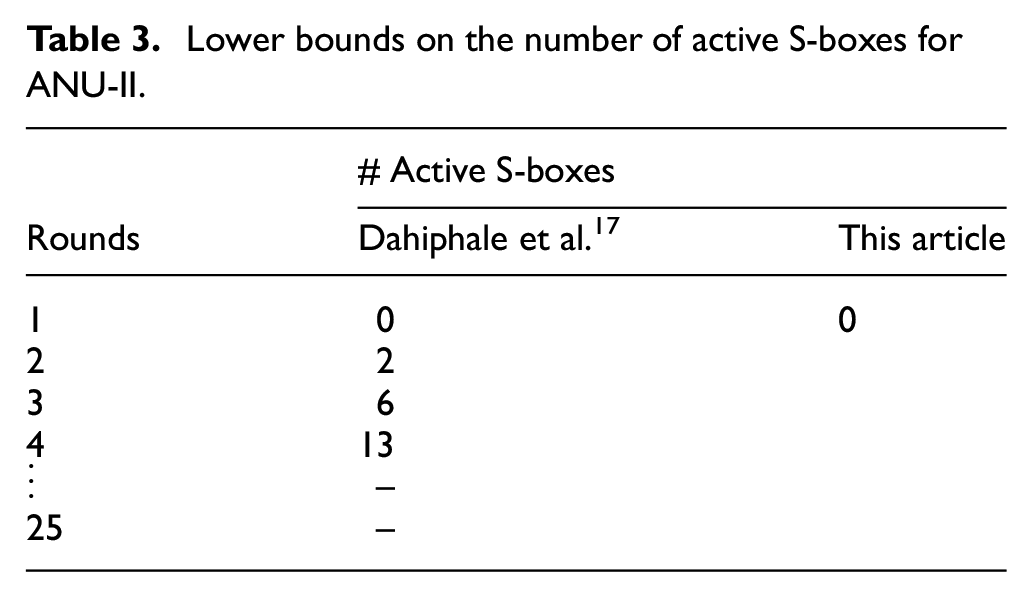
Iterated differential characteristic
The above result related to the lower bound on the number of active S-boxed (being 0), initiated a careful investigation of the design rationales of ANU-II, which then resulted in the identification of an iterative differential characteristic that holds with probability 1, as shown in Figure 3. Apparently, this differential characteristic holds with probability 1, because active bits only appear on the right-hand side (in total 32 bits) and the corresponding S-boxes are not active.
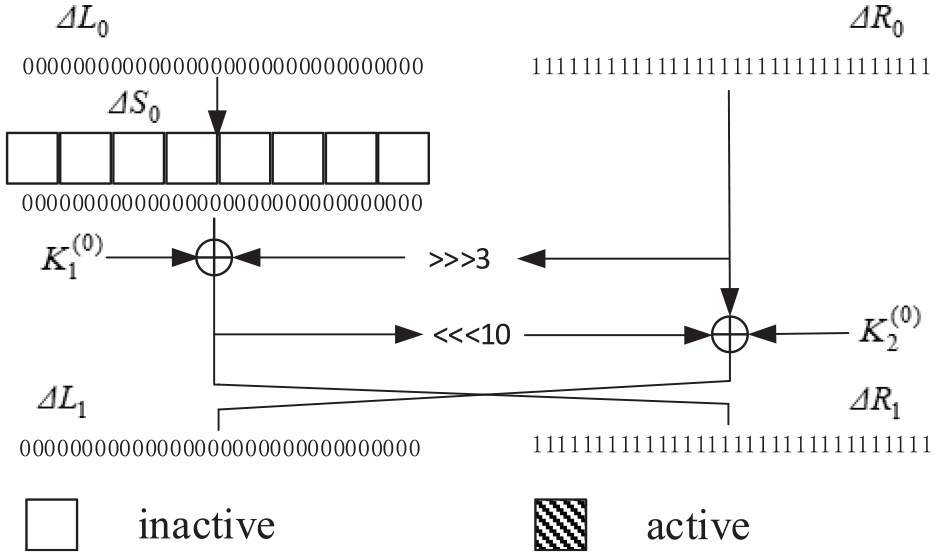
One-round iterated differential characteristic of ANU-II.
Key recovery attack on full-round ANU-II
Employing the iterative differential characteristic of a single round found in the ‘Iterated differential characteristic’ section, one can construct a full-round differential characteristic by iterating the single round differential 25 times, as described in Figure 4. We use ‘1’ and ‘0’ to denote active and inactive bits, respectively. Let now the subkeys of 25 rounds of ANU-II be denoted as

Differential attack on full-round ANU-II.
Property 1
The subkeys of two consecutive encryption rounds are heavily related, due to the key schedule of ANU-II. For our purpose, the relation between the subkey bits of the 24th and 25th rounds (96 bits in total) is of interest

where
The attack consists of the following four steps:
1. Select
2. Since the 25-round differential characteristic holds with probability with 1, having the input difference
3. We now consider the totality of 96 key bits relevant to our attack, more precisely 64 bits of the subkey (
(a) For every guessed value of the 64-bit subkey
(b) For every guessed value of the 32-bit subkey
4. Output the 96-bit subkey guessed
Data complexity
We utilize the signal-to-noise ratio
Time complexity
The time complexity of the attack is clearly dominated by Step 3(a) that is executed first. In particular, Step 3(a) requires about
An efficient modification of ANU-II
The experimental results confirm that the designers’ security evaluation of ANU-II against differential cryptanalysis is incorrect and the design is essentially flawed. The main reason for this is that suitable differences cancel out each other in the right branch (consequently, there is a differential characteristic that holds with probability 1). Therefore, we provide an improved variant of ANU-II given in Figure 5, which avoids this problem (modifying slightly the internal structure) and additionally has the best resistance to differential cryptanalysis without changing hardware and software implementation cost. The minimum number of active S-boxes of the proposed variant of ANU-II is listed in Table 4.

Our modified variant of ANU-II.
Lower bounds on the number of active S-boxes of our modified variant of ANU-II.

The best differential characteristic of our modified variant
We have also performed experiments towards finding the best differential characteristic of our modified version of ANU-II. For this purpose, we have built an MILP model, as described previously in the ‘Searching for the best differential characteristic’ section

SubBox
Our modified variant of ANU-II also uses eight 4-bit S-boxes. For each 4-bit S-box, there are 97 possible differential patterns that essentially give 97 possible 10-dimensional points when the probability information is embedded. SageMath is used to transform 97 points into 1033 inequalities. After applying the MILP-reduced algorithm, only 18 inequalities then remain. We again assume that
XOR and linear operation
Similar to the method described in the ‘Searching for the exact lower bounds of active S-boxes’ section.
An initial constraint

Objective function
At this point, all inequality constraints have been specified and our MILP model can search for the best differential characteristics. The experimental results are shown in Table 5, where clearly the situation is now quite different compared to the original design.
The six-round best differential characteristic of our variant of ANU-II.

Conclusion
In this article, we have successfully applied the standard differential cryptanalysis to the full-round ANU-II block cipher. Due to the design flaw, a differential characteristic that holds with probability 1 could be identified for the entire cipher, which then leads to an efficient attack that uses a few plaintext pairs and
Footnotes
Appendix 1
DDT of ANU-II S-box, as shown in Table 6.
Handling Editor: Yanjiao Chen
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship and/or publication of this article: The work was supported in part by the National Natural Science Foundation of China (61872103), in part by the National Natural Science Foundation of China (62162016), in part by the Guangxi Natural Science Foundation (2019GXNSFGA245004), in part by the Scientific Research Project of Young Innovative Talent of Guangxi (Guike AD20238082) and the Guangxi Natural Science Foundation (2020GXNSFBA297076).
