Abstract
Insurgency conflicts pose significant challenges to societies globally. The increase of insurgency conflicts creates a need to understand how insurgencies arise, and to identify societal drivers of insurgencies or effective strategies to counter them. In this paper, we analyze the contributions of computational modeling methods for the analysis of insurgent conflicts. We formalize a specific literature-based analysis framework using the identified key factors and drivers, which enables the evaluation of specific models in this domain. Through a systematic literature search, we identify 64 computational models to apply our framework. We highlight the development and contributions of various methodologies through an in-depth analysis of 13 high-quality models. The evaluation of these computational models revealed promising directions and future topics to design specific simulation models for all identified factors. In addition, our analysis revealed specific pitfalls concerning validity issues for each of the modeling methods.
1. Introduction
One out of four people in this world live in countries that deal with violent conflicts. 1 Since 1975, intrastate wars have been the predominant form of political violence around the world. 2 In fact, intrastate wars account for roughly four times more deaths and injuries than conflicts between nations. 3 While the number of armed conflicts between nations has declined, the number of insurgent conflicts has risen. Well-known examples of these insurgent conflicts exist across the globe, such as the Fuerzas Armadas Revolucionarias de Colombia (FARC), the Irish Republican Army (IRA), the Euskadi Ta Askatasuna (ETA), the Taliban or more recently the Islamic State of Iraq and the Levant (ISIL), and Boko Haram.
Preventing the emergence of insurgent conflicts is highly complex and requires a deep understanding and capability to perform analyses of counterinsurgency (COIN) strategies in different scenarios. In the last two decades, computational modeling has paved the way for a deeper understanding of the emergence and escalation of conflicts. An advantage of the application of computational models is the ability to analyze the effects of military strategies ex-ante, and hence before they are used in practice. 4 For example, Chaturvedi et al. 5 demonstrated the capability of agent-based modeling (ABM) to analyze the interactions of government, firms, and adversaries in (potential) information warfare scenarios. While an increased amount of available data promised a quick development of predictive models for emerging insurgent conflicts, machine learning techniques have been unable to fulfill the promise to deliver early-warning systems. 6 Instead, simulation models have been developed to gain insights into this emergent phenomenon using a top-down or bottom-up approach.
The introduction of simulation models has provided various means to evaluate the impact of military policies, strategies, and tactics in conflict environments. The PSOM model 7 is an interesting application of ABM to better understand the effects of military and political interventions in peace support operation. With semi-agent-based modeling, the Peace Support Operations Model (PSOM) wargame bridges a gap between fundamental computational modeling and analysis of strategy and policy, in a complex operational environment. Recently, Davis et al. 8 described the challenges of social behavior modeling and explained how the incorporation of computational models in the analysis of such complex environments provides the flexibility to conduct “what if” scenarios and analyze behavior in different circumstances, especially the capability to combine theory-interpretable and data-driven models. 9 While wargaming and simulations have proven to be useful for addition for the analysis of COIN operations, direct application of simulations in mission environments is limited due to lack of data, and the complexity of this environment. 10 More importantly, various applications of ABM and system dynamics modeling have demonstrated their potential to analyze the strategic and adaptive behavior of emerging insurgency threats. 11 However, these methodologies have important caveats in terms of data availability and conceptual challenges. 12 In this paper, we analyze these promises and pitfalls of various computational modeling methods for the military domain by analyzing models identified in the literature.
This paper contributes to the analysis of insurgency conflicts along four steps. First, we construct a literature-based analysis framework that allows for the evaluation of computational models along factors that focus on the complexity of insurgency. Second, an overview of high-quality computational models on insurgent conflicts in the literature is provided and discussed. Third, we evaluate the contributions of various prominent examples along the analysis framework. Finally, we identify potential advantages and shortcomings for various computational modeling methods.
The paper consists of four parts. First, the base of the analysis framework is proposed based on a characterization of the complexity of insurgency conflicts in sections 2 and 3. Second, the analysis of computational models along their fundamental aspects is summarized in section 4. Third, section 5 provides an overview and discussion of existing computational models of insurgency conflicts. A selection of analytical models, system dynamics models, and agent-based models are discussed using our analysis framework. Finally, we discuss the promises and pitfalls of computational models for this field in section 6.
2. Insurgency conflicts
The onset of insurgent conflicts involves a revolt against a civil authority or an established government. These conflicts consist of at least one non-state (armed) actor that is the perpetrator and/or the target of acts of politicalviolence. 13 The Additional Protocol II of the Geneva Convention 14 defines non-state armed groups as “dissident armed forces or other organised armed groups, who fight regular armed forces or against each other on the territory of one or several States.” While analysts struggle to distinguish insurgent groups and terrorist organizations, 15 the local population struggles from the safety, health, and economic deprivation in both cases. For this reason, the emergence of an insurgent conflict is often linked to the state’s failure to cope with political, economic, social, or environmental stress within a society. 16 In these societies, population segments are built around a shared identity based on ethnicity, religion, political, or other cultural similarities. Individuals with rebellious behavior can emerge from these segments as they can espouse a shared sense of being separated or subordinated by elites 17 or as they notice opportunities to gain political power. 18 In some cases, insurgency movements evolve into insurgent organizations. These groups aim to recruit from the local population and deploy tactics beyond the aggressive actions attributed to terrorist groups; they aim to reduce the legitimacy, power, and authority of a state. 15 In some cases, insurgent organizations even take over governmental services to the population. 19 In modern irregular conflicts, insurgent groups and the local government compete for the support of the civilian population by providing information and resources. 20
Governments try to prevent the onset of insurgent conflicts using COIN policies, strategies, and tactics. 21 The Counterinsurgency Field Manual describes these efforts as counters against all protracted struggles of political and violent means aimed to weaken the control and legitimacy of an established government. 22 A COIN strategy is formalized based on security, political, and economic dimensions to counter insurgency threats and address the root causes of the insurgent conflict. 23 Over the years, COIN efforts have yielded mixed results. 24 Evidence demonstrates that large COIN interventions yield more failures than success stories; 25 these failings have been attributed to the enemy-centric focus of COIN. Paul et al. 26 demonstrated that the “crush them” tactic against insurgencies was ineffective 23 out of 33 times. In their analysis of 71 insurgencies, they assess 24 concepts of COIN. An alternative population-centric approach was designed to focus on understanding and aiding the local population. 15 However, Kaplan 24 argued that commanders that designed COIN interventions to perfection beforehand were unable to anticipate changes in the local environment. This has urged COIN operations to focus on an information-centric approach that aims to optimize the flow of information from the civilians, to improve the ability of the COIN forces to make effective decisions. 3
The deficiencies and failures of various policies and COIN strategies demonstrate the complexity involved in phases of social, political, and economic stress. Societies are complex, dynamic systems; we might perceive an insurgent organization as a rather small collective when compared to the total population. However, these organizations are intertwined with the population in many ways. Therefore, the organization’s ideology and identity might be shared by a large proportion of the population. As policies and interventions interact with societies in various ways which are not well-understood, they often yield unpredictable and oscillating effects. 27 Moreover, insurgent organizations are able to change rather quickly over time, react to COIN interventions, and select the most effective tactics themselves. 28 These three characteristics are distinctive features of complex adaptive systems, 27 and are the adaptive and evolutionary responses leading to the resilience of insurgent organizations to COIN strategies.
3. A characterization of the dynamics in insurgency conflicts
In this section, we introduce a framework to assess the contributions by computational modeling efforts. The framework is constructed along three clusters of key factors that characterize the dynamics of insurgent conflicts and numerous dynamics at specific scales. The first cluster describes the complexity of insurgent conflicts, the second cluster characterizes dynamic behavior of insurgent organizations in terms of emergence and resilience, and the third cluster concerns the COIN efforts. The goal of this framework is to describe the dynamics of an insurgent conflict at large.
3.1. Complexity of insurgency
Insurgency conflicts are complex and defy any linear type of thinking. 29 The literature tends to focus mostly on either the effects at a societal level or dynamics at an individual level. 30 However, understanding insurgent conflicts requires assessment and policy action at a micro-, meso-, and macro-level. 31 At an individual level (micro), individuals and households are subject to social and economic pressures that may lead to a radicalization process in which extremist beliefs, feelings, and attitudes develop. At the societal level (macro), processes such as elections, justice and security reforms, and economic developments influence the stability of the state. In between these levels (meso), we can identify specific group-level processes that connect the processes of individuals at a communal level. An abundance of studies exist for describing factors to analyze insurgency. Davis et al. 32 provided an in-depth literature survey and mapping of underlying causal factors that contribute to the root causes of terrorism and insurgency, the willingness to engage in terrorism or insurgency, and the development of public support for terrorism. In order to sort through the complexity, we identify seven key factors which influence the emergence of insurgent conflicts. While the complexity of insurgent conflicts might not be limited to these seven factors, they provide a starting point to assess the focus and contribution of computational models in general, using a characterization insurgency at the micro-, macro-, and meso-level.
3.1.1. Grievances
The central factor within the root causes of conflicts is the population grievances.32,33 These grievances are mixed feelings of inequality, perceived hardship, and injustice which form legitimate grounds for complaint. The emergence of grievances is a product of a group’s perceived deprivation of social, economic, and political opportunities. 32 Traditionally, the development of grievances has been linked to the emergence of rebellious and violent groups. The psychological processes of radicalization, which change an individual’s beliefs, feelings, and attitudes, lead to the support of these groups and the use of violence. 34
3.1.2. Social identity
Groups of people share and support each other’s morals, ambitions, and grievances; they build a social identity as they share these cultural values within their communities. Families and peers within deprived communities can develop a shared belief of victimization, which stimulates the radicalization process.34,35 Eventually, this can build to an “us versus them” feeling, in which people develop a readiness or willingness to conduct violence to protect the group, which forms the basis for the emergence of insurgent movements. Some political propaganda efforts aim to politicize conflicts and amplify this dynamic by emphasizing cultural or religious symbols.
3.1.3. Governmental legitimacy
Governmental legitimacy is the first of three factors attributed to the resilience of a state. The consent of people to be governed by a central authority was described as political legitimacy by social philosopher John Locke. Political and economic science relates governmental legitimacy to the ability of a government to provide state stability and resilience. State resilience is defined as the capability and capacity of a state to deploy means to recover from strains within a society. 29 These strains are the result of economic hardship, safety issues, or long-term cultural developments. Intensified strains can develop or trigger existing grievances in a society, which increases the probability of insurgent conflict emergence. While COIN operations can be aimed at these strains, successful governance requires a deep social and cultural understanding. 36
3.1.4. Deterrence
Deterrence aims to suppress the emergence of insurgent movements with the presence and effectiveness of military and police operations. Freedom and protection can be endangered by the emergence of insurgent conflict, which urges the government to suppress this movement. This might be done by implementing effective law and order measures or establishing a visible presence of military and police operations. 37 However, it is difficult to balance humanitarian and suppression activities as governments can damage their legitimacy with violent repressive measures that legitimize the grievances of the insurgent groups. These developments can stimulate recruitment and create a negative spiral for the government.
3.1.5. Contextual setting
Environment is comprised of specific contextual factors that increase or decrease the probability of the emergence of insurgency conflicts. Once contextual factors begin to influence the behavior of insurgencies, “in-situ” analysis becomes more important in order to understand this phenomenon in particular cases. 38 For example, the demographic distribution of groups in a population is one of the most prevalent factors, as young males are especially prone to radicalization processes. 39 In addition, mobilization of insurgency movements requires a legacy of networks and organization that can accommodate the required resources. 40 Daly explains why the FARC was able to grow and recruit in particular groups in the population and geographical sections of Colombia; meanwhile, other sections of the country did not experience an emergence of insurgency, although they suffered equally from inequality and economic depression. Finally, the physical domain tends to favor insurgency movements on some occasions as mountains provide insurgent organizations the ability to shelter and areas with high population densities tend to more difficult to govern and control.
3.1.6. Cohesion
The social-institutional theory of cohesion explains how emerging insurgent movements develop into insurgent organizations. 41 Through interactions and pre-existing ties to family and friends, insurgent movements are able to create unity. This unity fosters cohesion and is built by trust, discipline, and mutual agreement upon strategy. Cohesion among individual members creates a mandate for the leaders of the insurgent movements to coordinate activities. 42 A lack of cohesion can split insurgent groups and ultimately lead to fragmentation. This may be triggered by internal rivalries or disputes about strategy.
3.1.7. Popular support
Similar to governmental institutions, insurgent organizations need to obtain legitimacy for their operations. Whereas cohesion refers to the internal state of insurgent organizations, popular support deals with how the environment perceives the attitude and actions of the group. Organizations can obtain popular support through their accomplishments and patronage or through the charisma of their leaders. Leaders of insurgent groups therefore continuously spend effort justifying and explaining their actions, since a strong level of popular support can, among other things, mobilize the recruitment of new insurgents. However, the use of violence against civilians can damage popular support and even create new rivalries within population segments.
3.2. Dynamic behavior of insurgent organizations
The following cluster of factors deals with the dynamic behavior of insurgent organizations, and focuses on the emergence and resilience of these organizations. Insurgent organizations emerge from pre-existing social ties in insurgency movements, and are therefore characterized as networks.28,35 These networks enable various forms of motives, strategies, and cooperation to emerge. While many differences between organizations exist, all organizations encounter similar challenges that influence their behavior. In particular, organizations have to politicize activities, decide on the use of violent means, avoid internal disputes, and mitigate the risk of detection. 43 As these challenges threaten the aforementioned popular support and cohesion of the organization, they are purposefully targeted by COIN efforts. The capability to deal with these internal and external threats determines the resilience of insurgent organizations. 44 We distinguish four forms of adaptive mechanisms that enable insurgent organizations to deal with these challenges: functional adaptations, Social capital, resource flows, and structural adaptations.
3.2.1. Functional adaptations
Organizations formalize mutual goals, and have to develop and agree upon organizational strategy and activities. Organizations are adaptive as they are able to change their functional character or deploy hybrid strategies. 19 Hybrid strategies have various aims and can challenge the authority through non-violent, violent, or political efforts. Next to activities to extend power and control in a certain area, some insurgent organizations invest a significant proportion of their resources in non-military activities, such as political and governmental tasks to help and control local populations. 19 This shows the breadth of strategies that insurgent organizations can adopt. Hezbollah, for example, after fighting in the Lebanese Civil War in the 1980s, developed a complex social network engaging in charity, development, and governance-related work. These efforts enabled them to develop new resource supply chains, foster popular support, and expand through recruitment. While these strategies provide obvious benefits, they can be expensive, attract international pressure, or undercut the repression of the local population. In addition, diverging strategies can increase the probability of preference divergence, which can yield internal conflicts due to a conflict of interests at various levels of the insurgent organization. 43
3.2.2. Managing social capital
Insurgent organizations vary in terms of size and discipline. New recruits provide organizations with human capital as they offer new skills, manpower, and extend the foundation of the organization. Recruitment does not come without challenges. It can be costly in terms of financial support to members and their families. In addition, new recruits can harm the group cohesion as they can differ in terms of their belief about the strategy. Therefore, recruitment is depicted as an attempt to grow without fragmentation. 41 While organizations can strive for a high degree of loyalty, punishment can damage the popular support of the group and a lack of recruitment can limit the ability of organizations to recover from interventions or exploit new activities.
3.2.3. Resource flows
The structure of the organization facilitates the supply structure for required resources. Material and financial resource availability is essential for the functioning of insurgent organizations. Availability of resources or technological development enables insurgent organizations to deploy new strategies or fall back on previous ones. Through recruitment, organizations can obtain new resources and develop new strategies in a decentralized manner, for example, from allied governments or insurgent groups.
3.2.4. Structural adaptations
Similar to ordinary business companies, effective insurgent organizations require structure for coordination and cooperation. The structural dimension of insurgent organization deals with hierarchy, chain of command, and division of labor. 45 Due to the asymmetric nature of insurgent conflict, insurgent organizations require secrecy to hide their members and their operations from infiltration and surveillance COIN efforts. While a cell-based structure enables decentralized decision-making with minimal communication, it can hinder communication and limit the capability of collective action. Therefore, these organizations are continuously challenged by a trade-off between secrecy and efficiency. 43
3.3. COIN efforts
The last cluster of factors concerns COIN efforts to contain the growth of an insurgency movement, prevent development of insurgent organizations, or disrupt the effectiveness of their operations. 20 A distinction can be made between military efforts and humanitarian or political non-military efforts. 46 Military efforts are all kinetic and non-kinetic operations by military services, which might include violent countermeasures or intelligence efforts. Humanitarian and political efforts include all other efforts to respectively aid populations or contain an insurgency movement. The contribution of these combined military, social, and political efforts should be assessed in terms of their effect on the emergence and resilience of insurgent movements and organizations.21,46 The materialization of both efforts can be analyzed in three layers, namely, strategic, operational, and tactical. 47 First, is the formulation of strategic goals that should be achieved long-term. Kilcullen 23 describes these goals along three pillars of security, political, and economic goals in order to bring the system to “normality.” While these goals can be general, strategic goals should specify the conditions of how to obtain these goals, such as minimal use of violent force. 21 Second, on an operational level, all campaigns and operations that are planned and coordinated should contribute to accomplishing the strategic goals. 47 These operations naturally extend to a regional level and, for example, determine the number of armed forces deployed in a certain area. Third, all battle, political, and social interventions are coordinated and executed at the tactical level. 48 While clustering COIN efforts along these three layers depicts the top-down direction from strategy to practice of military doctrine, the development of COIN strategies is much more complex.
3.4. Characteristics of insurgency conflicts
This characterization of insurgency conflicts demonstrates that various factors at micro-, macro-, and meso-level are required to capture all dynamics involved. Moreover, understanding the complexity of insurgency conflicts requires focus on the dynamics of insurgent organizations and their interaction with COIN efforts aimed to disrupt their emergence. In our analysis framework, we denote whether computational models address these factors in order to assess the depth and completeness of the analysis provided by the models.
4. An analysis framework for computational modeling
In this section, we provide an analysis framework to assess the contributions of computational models on insurgency conflicts. The characterization factors form the base of our analysis framework. Comparison of the models requires description of model assumptions and mechanisms, as not all the papers address the described phenomena and characterizations with similar vocabulary. An application of our evaluation framework is presented for a selection of models, see Figure 1. These models are part of the models identified in our literature search and will be discussed in detail in section 5. Additional to the characteristics of insurgency, we include a set of factors to analyze the implementation and robustness quality of various prototypical computational modeling approaches in terms of calibration, validation, and sensitivity analysis. These factors are explained briefly in this section. We distinguish these factors for analytical models and three types of simulation-based modeling methods: systems of differential equations in system dynamics modeling (SDM), modeling autonomous behavior and interactions in ABM, or a combination of SDM and ABM in hybrid modeling (HM).
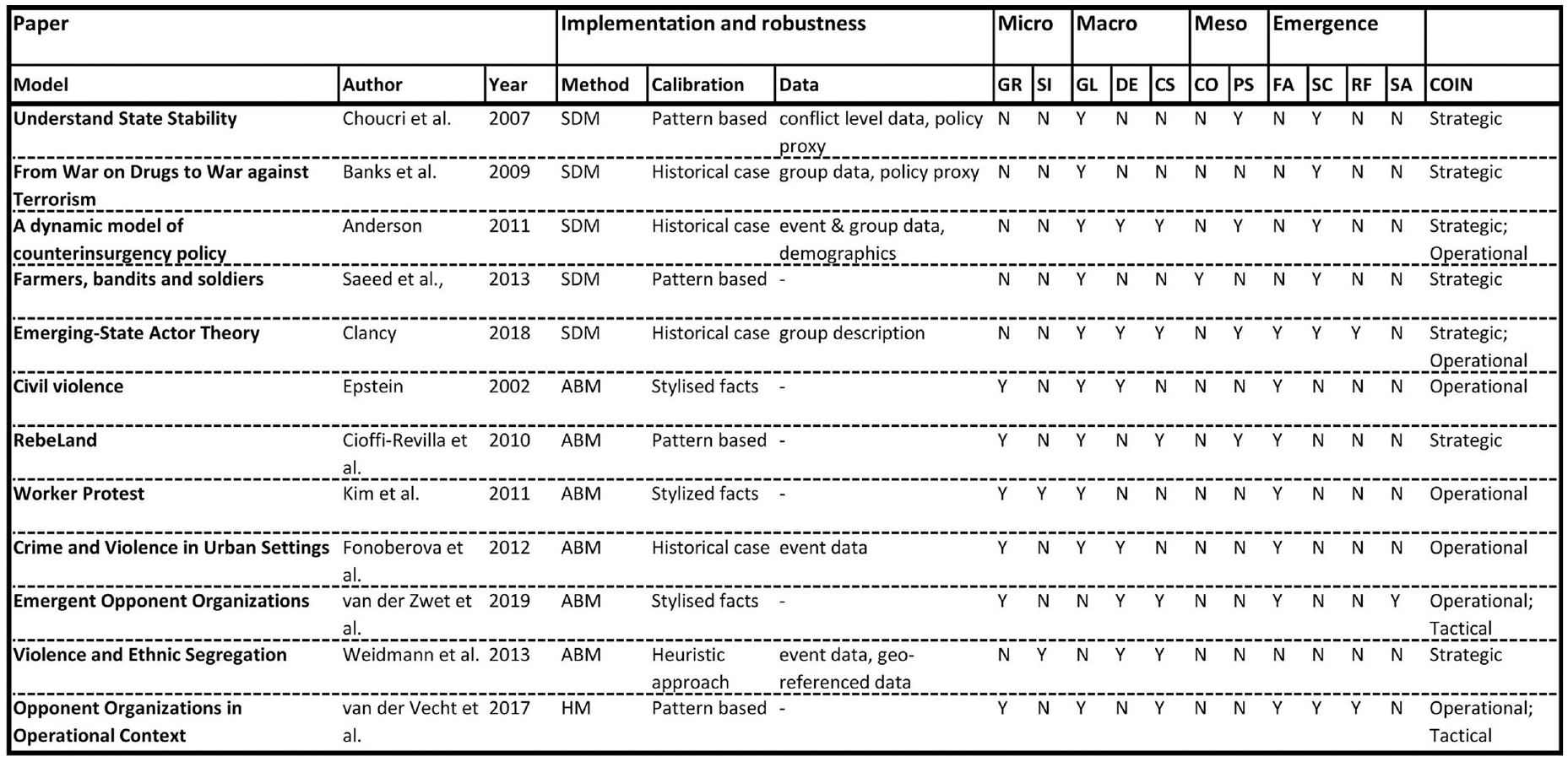
Analysis framework for computational models on insurgency. Models are scored on whether they address each of the identified characterizing factors of insurgency.
4.1. Analytical models
In this section, we introduce analytical models that form the foundation and inspiration for simulation-based models. 49 Over the last few decades, analytical sociology has emerged as a quantitatively oriented field aimed at the analysis of collective social dynamics through theory-grounded explanation and modeling. The development of large volumes of fine-grained data has opened the possibility to analyze other phenomena such as network structures, inequalities and violence, migration, or segregation patterns. 50
4.2. Simulation-based modeling
SDM and ABM emerge as the most dominant methods for analyzing the complexities of insurgent conflicts. Both these techniques hinge on the simulation-based science paradigm, which is placed between strict empirical research and theoretical research. The aim is to analyze the behavior of a system by constructing a model that reproduces this behavior and accounts for uncertainty. In this section, we will discuss the merits, requirements, and differences between SDM, ABM, and HM.
4.2.1. SDM
SDM was created by Forrester and was aimed to help researchers understand the behavior that emerges from a system. 51 In SDM, research focus on the underlying complex interactions of feedback loops and non-linear behavior of variables in social systems. Therefore, SDMs are characterized as top-down information feedback methods, which do not specify local interactions. By assuming causal relationships between model variables, dynamic behavior can be expressed with differential equations. Validated SDMs aim to enable researchers to simulate and evaluate the probable effects of intervention strategies through “what if” scenarios.
4.2.2. ABM
ABM offers a method for conducting empirical research to study the connectionist phenomena in social science. 52 These models utilize basic ontological units and heterogeneous agents that follow simple rules and incorporate uncertainty and bounded rationality. 53 The merit of ABM is the ability to formalize explicit model individual behavior and interactions between individuals and carry out experiments to observe emergence. 54 This method is, therefore, the bottom-up counterpart of SDM.
4.2.3. HM
More recently, a hybrid combination of ABM and SDM is suggested for the analysis of social-ecological interactions. 55 Linking the emergent patterns of ecological systems to individual-level human decisions—such as reinforcing feedback mechanisms—forms a major challenge when analyzing complex systems. Through a combination of ABM and SDM, HM simulations enable the analysis of such complex systems and their dynamic feedback interactions, that encapsulate both emergent properties and downward causation.
4.3. Implementation and robustness of computational models
The quality of computational models lies in their implementation and robustness. The description of the model implementation should document the modeling process in terms of model purpose, overview, and scheduling among others things. 56 The model robustness depends on the quality of the data, validation, calibration, and sensitivity tests.
4.3.1. Data
Intelligence data for computational models vary on scope and accuracy. 57 The scope of the data can be disaggregated based on resolution, agents, and strategy and tactics. 58 First, the resolution of the data determines the amount of information available about the conflict events at a specific scale. Current databases provide event data, that describe the lower-level dynamics of conflicts, such as violent incidents that enable to study temporal sequences or spatial characteristics. 59 Quite recently, the development of databases that include non-violent interactions in insurgent conflicts enables analysis in more detail. 60 This rapid development of new databases provides new possibilities for computational research. However, a critical note has been placed on the accuracy of these databases in terms of selection bias, under-reporting, and consistency. 61 Also, event data are disaggregated for the actors involved in the conflict. 58 The dynamics of insurgent conflicts can be mapped by describing these groups in terms of size, ideology, and their dyadic relationships with each other. 62 The third dimension of aggregation concerns strategies and tactics. These data describe the characteristics of actors and how they behave within the conflict in terms of strategies and tactics. 63 Finally, Gleditsch et al. 58 point to the importance of non-violent strategies and tactics within insurgent conflicts, that are severely under-reported within conflict databases.
4.3.2. Validation and calibration
Model validation is an important step in model development as it improves the accuracy, and the acceptability and applicability of the model at hand. The US Department of Defense (DoD) defines validation as the degree to which a model or simulation and its associated data are an accurate representation of the real world from the perspective of the intended uses of the model. 64 For this purpose, a distinction can be made between conceptual validation and operational validation. 64 The conceptual validity concerns that causal relationships in the model are retraceable and underpinnings exist in the literature. Models with a high degree of conceptual validity include the relevant aspects to model the capture the behavior of a specific phenomenon. The operational validity is determined by the accuracy of the model to generate useful predictions and usability for the intended purpose. The degree of operational validity is therefore related both to its ability to replicate stylized facts 53 or ability to match with real-world patterns 65 and its actual applicability in practice to describe or predict behavior of specific systems. These distinctions are particularly important when considering applications of simulation of social systems like insurgency. Models without proper explanation of the intended meaning and appropriate usance of validation methods pave the way for unacceptable risks. 66 In this way, the application of simulation methodologies might become controversial. 67
Calibration methods are applied for parameterization of the model using available data. 68 The granularity and quality of the data determine which calibration method is best applicable. For computational models of insurgent conflicts, the calibration approach is typically focused on pattern-oriented, historically based, and stylized facts. The basic idea of pattern-oriented modeling is to find parameter values that reproduce patterns observed in data sufficiently well. 56 The historically based approach uses a specific historic case to calibrate a model. Finally, due to the unavailability of accurate data, in their efforts to construct realistic models, modelers may aim to reproduce stylized facts. This enables modelers to implement dynamics in a plausible fashion and test a combination of theories. Sensitivity analysis is performed to test the effect of small changes in the parameter settings of the model to learn about their relative importance. 68
5. Computational models in the literature: promises and pitfalls
This section provides an overview and analysis of computational models in the literature, and discusses prominent models and their ability to analyze the dynamics of insurgent conflicts. The goal of our literature search is to establish an overview of high-quality papers including an insurgency model to assess and compare the contributions of different modeling approaches. A systematic review or meta-analysis is structured along the steps identification, screening, eligibility, and finally, a list of included studies. 69 For our search process, we formalized steps for identifying, reviewing, and selecting papers. Our identification process consists of a combination of forward and backward searching. 70 With a process of forward searching, we identified papers in the libraries CataloguePlus and Scopus using title, abstract, and keywords for matches with our search criteria. Along the described modeling approaches, we selected the following combinations of words for our search criteria: “computational OR agent-based OR system dynamics AND conflict OR insurgent OR insurgency OR civil violence OR civil war OR terrorism OR terrorist.” This provided a data set of 906 articles. In addition, we conducted a backward search from four canonical highly cited papers: Cederman, 71 Epstein, 72 Coyle, 73 and Richardson. 74 Papers referencing to these papers were added to the data set of papers only if they had more than 30 citations, in order to maintain a manageable set for the reviewing phase. In the reviewing phase, we read all titles and abstracts of the identified papers. Articles that did not address dynamics of insurgent conflicts or did not provide a computational model were filtered from the list. After reading the title and abstract, we filtered a list of 64 papers that included a computational modeling effort. This list is available on request from the authors.
To explore whether a underlying structure between the papers exists content-wise, a network structure for the selected papers was created with VOSViewer, 75 see Figure 2. This software applies an algorithm to construct a network of keywords based on co-occurrences of keywords in a bibliographic database containing the title, keywords, and abstract of articles and books. The algorithm includes various steps of natural language processing to improve the quality of the identified keywords (e.g., through removal of copyright statements and by noun phrase detection). The threshold for the minimum number of co-occurrences of keywords was set to 3. The network is a graph in which links are weighted by the number of co-occurrences. For the community detection, the tool applies a modularity-based clustering algorithm based on these weights. Three of the identified clusters (green, yellow, and purple) emphasize the selected modeling approaches specifically and are linked to the topics mostly addressed by those approaches. First, the green cluster focuses primarily on ABM and analytical methods, which is linked to analysis of social (blue cluster) and human (red cluster) behavior. Second, the yellow cluster focuses on systems dynamics and theory, which are specifically linked with modeling of population dynamics and public policy. Third, the purple cluster focuses on analytical spatial and geographic information system (GIS) analysis, which is related to decision-making and migration applications. The visualization by the VOSViewer provides a preliminary overview of links between topics and methodologies. These three clusters underline the structure for reviewing computational modeling efforts applying analytical methods, or SDM and ABM techniques.
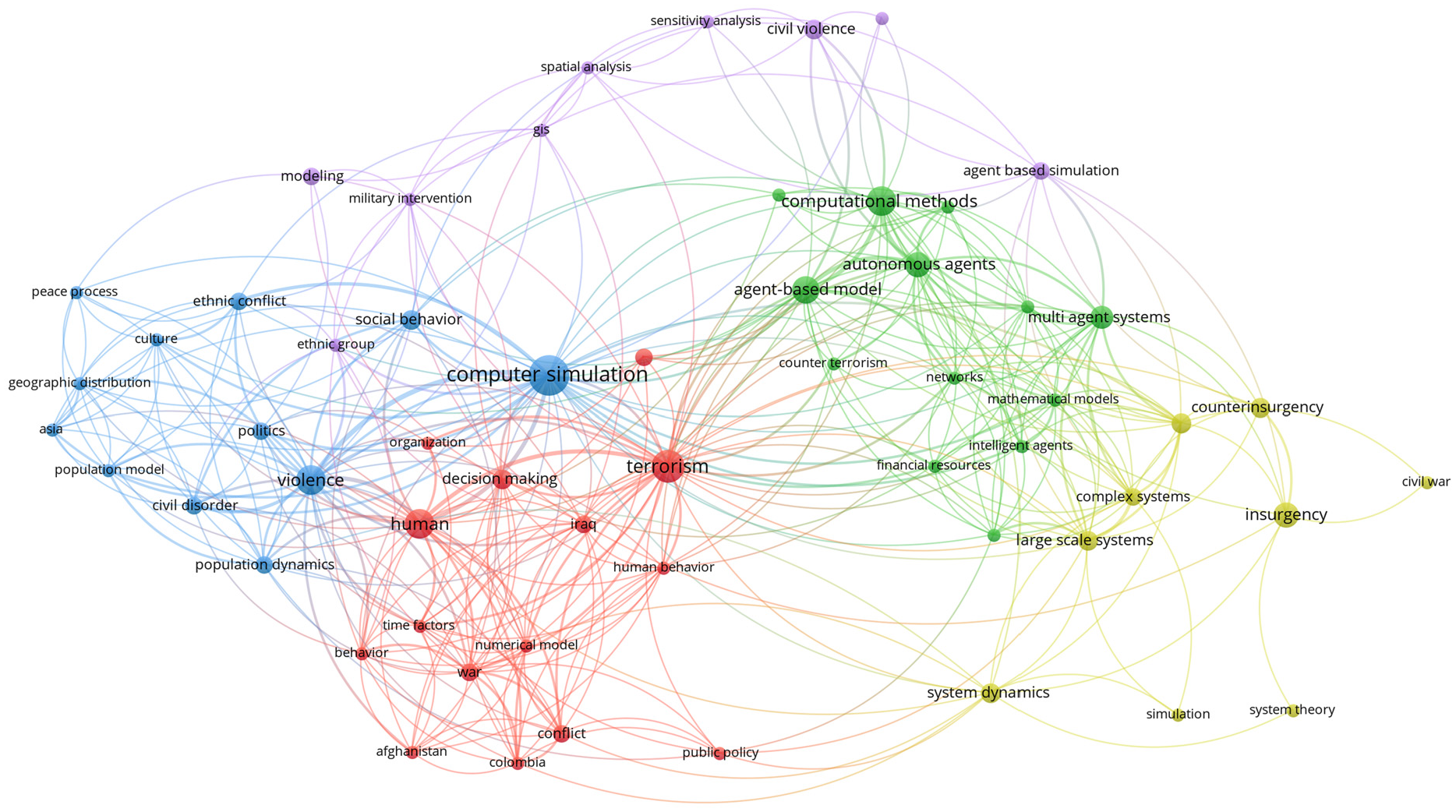
Resulting clusters based on co-occurrences of papers’ keywords. The next sections contain an in-depth analysis of highly cited or high-quality papers. The analysis also contains papers that provide models that built upon these findings in order to track their conceptual and operational development.
5.1. Analytical models
In this section, we discuss three main types of analytical modeling approaches for analyzing the behavior of insurgent conflicts: mathematical, statistical, and network-based analytical models. The work of Richardson 74 on “deadly quarrels” and their severity inspired Johnson et al. 76 and Clauset et al. 77 to statistically analyze incidents within insurgent conflicts in terms of severity and frequency, for which they detect a similar power-law scaling that points to a scale-invariance property. This suggests that insurgent conflicts might not differ fundamentally from each other. Various mathematical explanations for self-organizing group behavior exist that support the property of scale-invariance. 78 Bohorquez et al. 79 provide an analytical particle model of a dynamic evolving insurgent population. The model assumes that the evolution of insurgent groups relies on group dynamics of fragmentation and coalescence that protect them against state army repercussions. It also assumes a distribution of the insurgent movement strength according to the size of the various groups. This suggests that COIN operations should not focus on detecting the most lethal insurgent groups, but instead focus on breaking the insurgent movement into as many small groups as possible. Contrarily, Clauset and Gleditsch 80 suggest that larger and more experienced insurgent organizations are able to conduct terrorist attacks more frequently, and thus produce deadly attacks more often. They provide a mathematical model of insurgent organizations that describes feedback mechanisms between attacks, recruitment, and experience. This model suggests that policies aiming to limit the growth of insurgent groups are most effective in the early phase of a conflict.
These analytical models demonstrate the potential of data-driven insurgent conflict analysis. Most importantly, the estimation of the power-law distribution in the frequency of severe events suggests that conflicts share underlying social, political, and physical mechanisms. In practice, however, these mathematical behavior models provide few links to grasp the actual impact of COIN efforts upon the behavior of insurgent groups. Due to the limited scope of the data, it is practically impossible to analytically evaluate how COIN efforts actually effect the internal behavior of insurgent groups, and examination of the long-term effects of COIN efforts is an issue as well. The operational validity of such models is therefore limited to extracting characterizing trends in their behavior. More importantly, the contributions of these efforts are that they provide similar empirical correlates as Paul et al. 26 and stylized facts that enable to test behavior of computational models against real-world behavior.
Spatial-temporal analysis of insurgent conflicts specifically addresses decisions by insurgent groups on their tactics in terms of target location and timing, and the effect of COIN operations on these tactical decisions. Braithwaite and Johnson 81 have identified that attacks with improvised explosive devices are clustered in time and space, but also contested that COIN actions provoke these attacks as some theories suggest. Rather they suggest that other dynamics—such as competition between insurgent groups for popular support—steer this attack behavior. More specifically, LaFree et al. 82 and Tench et al. 83 combine spatial-temporal attack data with assumed insights on the tactics of particular insurgent groups during a specific phase of the conflict. The application of geo-referenced (GIS) and temporal data, combined with analytical analysis, demonstrate the ability to understand the behavior of insurgent groups in terms of strategy, tactics, targeting, and movement. The development of mobility data provides promising signs to analyze these dynamics more precisely. While these methods enable the analysis of specific insurgent tactics and strategies in a specific context, they are quite limited to analyze the actual adaptive reactions. More specifically, these approaches solely focus on the patterns of attack tactics, which limits the capability to grasp the entire dynamic of insurgent groups. In addition, due to the limited number of terrorist attacks compared to regular events, statistical approaches struggle to identify independent variables.
Network analysis in conflict studies focuses on particular insurgent groups to grasp the structural properties of organizations and their internal dynamics. 84 Dynamic network models can analyze structural dependencies within insurgent groups with the aim to unravel internal dynamics and identify COIN tactics to disrupt and destabilize these groups. 84 Dynamic network analysis in criminology has demonstrated the importance of analyzing the effects of law enforcement interventions on illicit networks structures. 85 Ilachinski 86 and Li et al. 87 provide dynamic network analysis models for insurgent networks that adapt to COIN efforts or change in contextual settings. However, they were unable to calibrate or test their models using actual data, which limits the operational validation of their models.
5.2. SDMs
In this section, we describe three different modeling approaches using SDM. While all models analyze the dynamics of insurgent conflicts, they consider different emergent patterns of insurgent behavior and various containments or counter strategies.
5.2.1. State stability modeling
With the state stability model (SSM), Choucri et al. 16 provide one of the first SDMs to help the researchers understand the emergent patterns of insurgent conflicts. The model provides a system-level exploration of the emergence of insurgent movements, the emergence of regime resilience, and the dynamic relationship between them. This interplay between insurgent pressures (load) and regime capabilities (resilience) forms the basis of the model. Choucri et al. 16 attempt to identify and understand different pathways that lead to either escalation or containment of insurgent conflicts. First, they aim to understand how the emergence of insurgency movements might override the regime resilience and lead to escalation of the conflict. Second, they aim to isolate conditions under which small changes in anti-regime activities might trigger major disruptions. Third, they seek to identify appropriate actionable mitigation factors to reduce the probability of this undesirable effect.
The causal relationships are built around the factors that describe dynamics in regime resilience and the number of insurgents. These dynamics contribute to understanding the relationship between government legitimacy and management of social capital by insurgent organizations. The SSM describes a reinforcing causal relationship from the insurgent tactics of protest and violence to the propensity of the population to be recruited to the insurgency movement as dissidents.
In terms of mitigating factors and strategies, the SSM is focused on the regime resilience and COIN efforts that either remove insurgents from the movement or lower the effectiveness of anti-regime messaging. The regime resilience factor within the SSM is based on generalized factors that described the economic, political, legitimacy, and social dynamics over time. These dynamics were operationalized using the gross domestic product, the employment rate, the polity type, the literacy rate index, and the civil liberties index. This enabled cross-national comparison in terms of long-term dynamics of state resilience in terms of economic and social dynamics, and the short-term triggers of that influence this resilience, such as regime-type change. While the value of SDM has been demonstrated to be useful in helping to understand the emergent patterns of insurgency conflicts, the model remains quite limited in its ability to explain the complexity of containment of emerging insurgent threats. The prominent contribution of the SSM model is that it describes a first attempt of systematically retrieving the causal effects underlying the emergence of insurgency movements—from the literature and expert interviews—and modeling them quantitatively. However, while these efforts aim to foster the conceptual validity of the model, the ability of the SSM to incorporate all the facets and dynamics of insurgent conflicts is limited as it neglects both micro- and group-level dynamics such as grievances, social cohesion, and functional adaptations.
5.2.2. Counterinsurgency policy model
Anderson 88 proposed an SDM counterinsurgency policy model (CPM) to analyze more specifically the effects of various COIN efforts. The CPM basic structure shares many similarities with the model of Choucri et al. 16 , as the emergent phenomena of an insurgency movement within the model are measured by the number of insurgents, and a decline of the governmental legitimacy has a positive causal effect on the insurgent recruitment process.
The model is mostly based on the Field Manual of Counterinsurgency 22 and as such incorporates various feedback mechanisms driven by kinetic and intelligence COIN patrols. Whereas kinetic patrols aim to detain or eliminate insurgents, intelligence patrols gather information from the population about insurgent operations. With this distinction, Anderson 88 analyzes how the number of COIN patrols and the ratio between kinetic and intelligence patrols yield feedback loops that effect the emergence of insurgency movements. The model shows that kinetic patrols yield both a suppression loop that has an instant effect on the number of active insurgents and an additional “blowback” loop that reduces the legitimacy of the government. Intelligence patrols improve the combat efficacy as they enable more precise kinetic patrols, which enables the government to decrease the number of insurgents without lowering the legitimacy of the government. However, insurgent incidents and government kinetic patrols hinder the information retrieval. The CPM model used data from the Anglo-Irish conflict of 1919–1921 for the calibration of model parameters. This included data on population, death rates, emigration, insurgent incidents, active and detained insurgents, and the number of COIN troops. A set of sensitivity analysis tests were conducted with the calibrated model for studying the relationships within the model. From an internal perspective, the model is highly sensitive to the blowback and intimidation loop. Without the blowback effect, kinetic patrols would be a very effective measure to suppress an insurgency. However, the model demonstrates that the intimidating effect of the insurgency upon the population and the harmful effects of kinetic patrols require an advanced policy analysis to balance the ratio and timing of kinetic and intelligence operations. However, a strategy that emphasizes kinetic patrols will have a long trajectory and cause many casualties. A balanced effort between intelligence and kinetic operations would yield the best results, and as the intelligence gathering has a delayed effect, the best scenario to suppress the insurgency occurs when the kinetic patrols increase in a later stage. In addition, a gradual decrease in the number of COIN patrols would minimize the effect of the blowback loop.
With the CPM model, Anderson 88 achieved creating a detailed insight into the effects of various COIN policies. Compared to the SDM model of Choucri et al., 16 Anderson 88 provides a detailed model that enables data-driven analyses of COIN at both the strategic and operational levels. The ratio between kinetic and intelligence patrols integrated the deterrence effect, especially the delayed effect of the intelligence efforts advocates for revision of the findings in the FM 3-24. 22 In addition, Anderson 88 provided a model to analyze the contextual setting of the insurgency for specific country characteristics. First, the implementation of age cohorts enables the analysis of country-specific demographic configurations that differ in terms of density and age structure. Second, the base level of government legitimacy could indicate the effectiveness of intelligence efforts.
However, the CPM model has some limitations as a generalizable model for real-world insurgencies as it specifically models the Anglo-Irish conflict. First, the model overemphasizes the effect of insurgent incidents and kinetic patrols on the legitimacy of the government and is unable to address the adaptivity of insurgent movements to deploy other strategies. In addition, Anderson 88 neglected the economic, social, and political grievances factors that influence the governmental legitimacy. Therefore, the model should be communicated as a proof-of-concept for SDM of evaluating COIN policy at a strategic level.
The “hairball” model by Pierson et al. 89 is an early and extensive analysis of governmental legitimacy using SDM. This model expresses legitimacy as function of governance effectiveness, perceived security, economic development, essential services, and the presence of security forces. However, the exact implementation and results of this model are classified and not available for further comparison. While providing a much more basic SDM, Banks and Sokolowski 90 demonstrated the influence of a change in government strategy on the growth of an insurgency movement. As the strategy switched from the war on drugs to the war against terror, the government was able to restore some legitimacy as it relieved some burden on the economic hardship of the population. The model of Saeed et al. 91 used the metaphor of a farmers, bandits, and soldiers ratio within populations to model the dynamics of conflicts. They argue and demonstrate that a pathway from conflict to peace should include the timely provision of liberty and economic aid.
5.2.3. Emerging-state actor model
By analyzing emerging insurgent conflicts from the perspective of an insurgent movement, Clancy 92 modeled an SDM to understand both the COIN efforts and the insurgent and social responses to them. With the emerging-state actor model (E-SAM), Clancy 92 addresses the adaptive functioning which yields dynamic organizational behavior by the insurgent movement.
The model reveals the urgency to obtain a better understanding of the underlying processes of insurgent organizations. Rather than envisioning the insurgent movement as a “black box,” these types of models could reveal new possibilities for effective COIN intervention operations and tactics. Clancy 92 explains that as insurgent organizations grow and control more people and resources, they require more combatants and insurgent incidents to prevent uprisings against their rebel governance. Ultimately, this will lead to fragmentation processes as described analytically by Johnson et al. 76
5.3. ABMs
In this section, we describe the use of ABM for analyzing the behavior of insurgent conflicts. In contrast to SDM models, each of the ABMs discussed model insurgency movements as bottom-up phenomena. As the literature of ABM on insurgent behavior is vast and diverse, we describe the most cited models and those with interesting applications in this area.
5.3.1. Civil violence model
With the civil violence model (CVM), Epstein 72 introduced ABM as a method to analyze the emergence of insurgency movements. Epstein provides a model of “decentralized rebellion” and a central authority that seeks to suppress the emergence of this behavior. The model describes a grid cell environment in which two types of agents interact and move. The “population agents” can be either “quiescent” or active in terms of rebellion. The “cop agents” suppress this rebellion and can detain rebelling agents.
Epstein provides a simple rule-based model to describe the behavior of the agents. The population agents determine whether to rebel or not based on their local parameter states “hardship” and “risk aversion.” The hardship parameter mimics the perceived physical and economic deprivation and is heterogeneous for all population agents. The model provides a global parameter of governmental legitimacy. Epstein then determines that the level of grievance of an agent is the difference between the government legitimacy and individual hardship. The legitimacy thus provides a threshold value. Once the hardship exceeds the legitimacy, the population agent will perceive a positive level of grievances and will tend to rebel against the central authority. However, Epstein argues that individuals are risk-averse, and thus are more likely to rebel if surrounded by other rebelling agents and less likely to rebel when surrounded by “cop agents.” The population agents, therefore, inherit a risk aversion parameter that affects their tendency to rebel.
In addition, for the rebelling agents, the probability of being detained at each time step is computed by calculating the number of cops and rebellious agents in their line of sight, knowing that each cop can only detain one rebellious agent. With the CVM, Epstein provides a simple but elegant model with a minimal set of dynamics to describe the emergence of an insurgency movement.
Various simulation runs were conducted to analyze the model behavior. Epstein reveals two patterns typical for complex systems. First, outbursts of decentralized rebellion follow a punctuated equilibrium. Long periods of relative stability are punctuated by outbursts in which many agents exert rebellious behavior. Second, a macroscopic regularity arises as a waiting time distribution between these rebellious outbursts. In addition, Epstein tests how the model reacts to a reduction in the number of cop agents and a decline of governance legitimacy. While a gradual decline of governance legitimacy causes a gradual increase in the number of rebellious outbursts, a gradual reduction of the number of cops causes sudden escalation of rebellion at a certain point.
Even in its preliminary state, the CVM enables simulation of some emergent behavior patterns, which were also identified by the SDMs. This emergent behavior of the system depends on interactions of grievances, governance legitimacy, deterrence, and functional adaptations. The bottom-up approach specifically analyzes in which way individual grievances cause decentralized outbreaks of collective rebellious behavior. While Epstein explicitly avoids calibration to a historic case, other researchers were inspired to use the model to analyze the emergence of civil violence in US cities. In addition, the operational validity of Epstein’s model to reproduce characteristic behavior of historic events has been tested by linking the model to several other models. 64
Due to its simplicity, the CVM is significantly limited in its ability to obtain a thorough analysis of actual insurgent conflicts, mostly because many of the feedback mechanisms described in previous models are not included. Most importantly, as both government legitimacy and deterrence are included, the model can be criticized for the fact that the number of cops does not affect the governmental legitimacy. Moreover, the model only weakly enables testing COIN at an operational level by allowing a variation in the number of cop patrols. Second, the agents do not interact with the government, and thus rebelling agents do not affect the functioning of the government. Third, the model does not incorporate any contextual factors that enable analysis of conflict-specific characteristics. Finally, while the agents interact indirectly through observing each other, the model does not model any organizational interaction between the agents. Thus, the model does not account for any of the group-level dynamics, and therefore, the emergent patterns do not account for an evolution of the insurgent movement from a decentralized phase to an organized phase.
5.3.2. Extensions on the CVM
The CVM inspired many others to search for improvements or enable calibration, validation, or sensitivity tests. As the foundation of these models is quite similar to the CVM, only the main improvements or contributing extensions will be discussed here.
With the ABM RebeLand, Cioffi-Revilla and Rouleau 93 analyze how agents yield emergent insurgent behavior that potentially leads to state instability. To enable this analysis, a “political decision component” is modeled. This component describes a rule-based decision model that governs various incoming economic, security, and environmental policy issues. In this manner, Cioffi-Revilla and Rouleau 93 attempt to increase the model realism, which enables analysis of the contextual setting. This model is able to also show, when altering these contextual parameters, the emergence of a drifting pattern of insurgent behavior before a sudden collapse of the state stability.
The Worker Protest model by Kim and Hanneman 94 proposed two adjustments to the model of Epstein. First, the relative deprivation theory by Gurr 33 was implemented to model the emergence of individual grievances in a more realistic manner. This theory from social psychology states that individuals (workers) develop grievances through relative (wage) inequality. As to be expected, model simulations with a higher parameter value for wage inequality yield insurgent outbursts more frequently. In addition, the model demonstrated low sensitivity to the social identity parameter. This can be explained by the fact that the model does not incorporate any form of organization between agents in the same group. As such, it does not enable analysis of the impact of social identity and cohesion with regard to the effectiveness of organizational functioning and stability.
Fonoberova et al. 95 provided a first attempt to validate the CVM, using FBI data of crime and violence in US cities. They find that a uniform distribution of the risk aversion among the population does not allow model calibration with actual data. Rather a sigmoidal function enables better calibration with the FBI data. This indicates to irrational behavior, in which individuals actually underestimate or overestimate the amount of risk. However, as the model does not incorporate the feedback mechanism between deterrence and government legitimacy, these recommendations can be questioned. This highlights the importance of comparing the outcome of ABM efforts with that of SDM models or analytical approaches in order to validate the conceptual and operational validity of such models.
The model for Emergent Opponent Organizations extended the CVM to analyze organizational behavior among insurgent agents. 96 Similar to the CVM, the hardship of the agents could trigger rebel behavior. The effectiveness of insurgent activities increases as active rebelling agents establish a connection with other rebelling agents within their vision. Rebelling agents deliberately add or deduct connections, as they increase the likelihood of being detected by patrolling cop agents. The model enables the testing of two COIN tactics. The cop agents can either detain a rebel once detected or infiltrate and attempt to disrupt the network. A game-theoretic model is suggested to enable the rebelling agents to adapt to these tactics. The model demonstrates a specific tipping-point in which an increase of COIN efforts triggers a shift in the insurgents’ organizational behavior.
5.3.3. Violence and ethnic segregation
Weidmann and Salehyan 97 provided the violence and ethnic segregation model (VES). In contrast with previous approaches, this modeling effort specifically considered a real-world conflict. This model aims to understand the dynamics of violence, migration, and segregation in conflicts. The VES shows analyses the ethnic conflict in Baghdad at various stages of the invasion between 2003 and 2009. In that period, Baghdad was troubled by violent attacks by two ethno-religious groups. In 2007, the American army increased the number of troops, hoping to contain the level of violence through security presence. In addition, COIN efforts placed greater emphasis on institution-building by training Iraqi police officers. While these changes preceded a decline in violence, it is debatable whether the deterrence effect, migration, or segregation caused this decline.
For the calibration of the model, Weidmann and Salehyan opt to use high-resolution geo-referenced data of 85 Baghdad neighborhoods. For the violent incidents, event-level data were used from the Significant Activities (SIGACTs) database, which has location data. The VES uses a heuristic calibration approach, for which many simulations are run to identify the combinations of parameter settings, which can be a time-consuming process or lead to suboptimal results. The model simulations yield various interesting insights. First, violence is most likely to occur in a given place when small but significant minorities are located in the area. Second, the fear for these violent actions is enough to trigger migration patterns. These migration patterns cannot be explained by the desire of agents to live in a neighborhood which is dominated by their ethnic group, as this would imply too much migration. Finally, the model was not able to link the increase in the number of troops with the decline of violence, as the migration process is mainly responsible for the violent patterns. The model outcomes emphasize the importance of timing, as a considerable initial troop force would be able to limit the migration process.
The main contribution of the VES model is the explicit context modeling, and in particular the integration of geo-reference data. However, the interaction between population agents and government is limited, which oversimplifies many of the complexities within Baghdad. For example, the model agents only target each other and do not conduct violence against the central suppressor. In addition, contrary to the CPM model, the CVM model does not account for any “blowback” mechanisms that would be triggered by the increase in the number of troops.
5.4. HM
The hybrid approach of ABM and SDM can be applied to explore the relationship between socio-culturally driven cognition and the emergent patterns of violent conflicts. 98 Van der Vecht et al. 99 focus more specifically on dynamics of insurgent conflicts by modeling these dynamics within their operational context. Their effort attempts to understand how insurgent organizations grow and increase their activities. The insurgent organizations are modeled using a combination of ABM and SDM.
The ABM consists of agents that can be trained to conduct different tasks, which are financial, fighter, recruiter, or leader. Depending on the predetermined strategy, the insurgent organization will recruit and train insurgents for a specific task. Through attack activities, the fighter agents can influence the popular support for the insurgent group, the recruiting agents can attract new agents to the organization, and finally, the financial expert agents can obtain resources to finance the insurgent activities and wages for insurgents. The SDM model is inspired by CPM and describes the contextual context for the insurgent organization. The model is able to test the resilience of insurgent organizations against various COIN tactics that target specific roles from the insurgent organization. Simulations of the model demonstrate that tactics that target financial roles are able to contain the long-term growth of the insurgent movement. This simulation effort demonstrates the analysis of downward causation on the behavior of insurgent movements.
In comparison with the SDM models such as SSM and E-SAM, these hybrid models are better capable to explicitly model the micro-dynamics such as grievances, and emergent dynamics such as functional change. In comparison to ABM models such as the emergent opponent organizations model, these hybrid models enable similar analysis of COIN policies on a tactical level while providing a better framework for “in-situ” analysis. However—while the combination of various methodologies is promising—the unavailability of data for the exact role distribution of insurgent organizations prohibits validation. Furthermore, operational validation of HM is fundamentally challenging, as the ABM and SDM components should be tested in combination against real-world data, on top of the challenges of validating beliefs about causal relationships in SDM models and micro-interactions in ABM. 100
6. Promises and pitfalls
Our literature review identified 64 computational models from which three clusters emerge. While our selection of reviewed computational models addresses the described key factors for insurgencies like grievances, legitimacy, and cohesion, currently none of the models is able to provide a complete holistic model incorporating all specific aspects of insurgency conflicts. In general, modeling efforts are limited in their ability to account for the role of social identity or cohesion of insurgency movements. While qualitative research points to the importance of these factors for the growth and endurance of insurgent organizations, computational models tend to avoid this matter due to lack of available data. Therefore, analysis of emergent patterns of structural adaptation in terms of fragmentation and coalescence remains quite theoretical and inapplicable to evaluate COIN measures in practice.
In recent years, open-source data have been disaggregated for microscopic violent events in insurgency conflicts. These databases enable the study of temporal sequences and spatial characteristics. Foremost, the development of databases that include non-violent events and interactions would enable the study of the resilience of insurgent organizations through functional adaptations. As insurgent organizations evolve and develop non-violent tactics, they are able to influence and change the landscape of conflicts. Ultimately, understanding these developments might enable computational modelers to contribute to promising pathways toward peaceful resolutions. Furthermore, the ability to integrate geo-referenced data, event data, and proxy data could steer the development of models by integrating contextual factors such as socioeconomic data or demographics for specific regions.
In general, computational modeling methods are able to address specific research questions for the identified factors and dynamics of insurgency conflicts. SDMs mainly focus upon understanding the causal effects that yield the emergence of insurgency movements. The COIN policy model demonstrates the ability to calibrate these models using aggregated conflict data and proxy data. Due to their high-level abstraction, SDMs are unable to unravel the underlying complexity of emerging insurgent threats in terms of functional and structural adaptation, which hinders the ability to extend this method for the analysis of various tactical interventions. ABM efforts dominantly address social and human behavior, which are linked to grievances and functional adaptations. Most ABM models provide a proof-of-concept to analyze the bottom-up emergence of insurgency movements. These models use stylized facts to design models that mimic specific behaviors of insurgency conflicts. More specifically, they focus on emergent patterns of violence which might be related to specific tipping points. The fine-grained character of ABM would enable unraveling the consequences of tactical interventions and test the long-term effects of new policies. ABM models can be criticized on their operational validity, as they purposefully avoid calibration to historical cases due to a lack of appropriate data. The model of crime and violence in urban settings, however, demonstrates the value of validation using a combination of intervention and event data. More importantly, we identified conceptual validity issues for ABMs as each of the models is unable to test specific essential feedback mechanisms. Most notably, the actions of the insurgent movement or COIN interventions do not affect the legitimacy of the government in these ABM models. The model on VES demonstrates the ability to both integrate geo-referenced and temporal event data in ABM. Such ABM models could identify restraining factors in the development of insurgent organizations or catalysts for functional adaptations. Finally, studies in criminology demonstrate the importance of analyzing the effect of interventions on structural adaptations by illicit networks. Unraveling the network characteristics using ABM could reveal resilience issues in insurgent organizations and possible disruption strategies at a COIN tactical level. Finally, hybrid models are quite new for insurgency conflicts and social science in general. Development of this field might enable analyzing the effect of interventions in a dynamic context. The models discussed provide a proof-of-concept to analyze the interplay between macro-societal dynamics and micro-tactical interventions upon the growth of insurgent organizations over time. The possibility of this approach to incorporate both contextual factors and explicitly model emergent patterns enables to model insurgent behavior “in-situ.” However, as the validation of these hybrid models is currently only pattern-based, they are not usable in an operational setting.
7. Discussion
Unraveling the emergence and resilience of insurgency movements and organizations requires a deeply understanding of the intertwined effects of microscopic dynamics such as grievances and social identity, with the emergent patterns of cohesion, popular support, and government legitimacy. To facilitate this analysis, we have been able to construct a detailed and founded evaluation framework based on characterizing factors. The value of this framework has been evaluated through an assessment of the contributions of some computational modeling efforts for the analysis of insurgency conflicts. We have been able to classify the contributions of various computational approaches and identify their promises and pitfalls in terms of their design, implementation, and findings.
While our literature review and analysis revealed the potential of computational modeling, a number of factors potentially impact the completeness of our analysis. The characterization of insurgency and insurgent organizations is limited to 11 wide-ranging factors. The impact of this broad selection of both micro-, macro-, and meso-level dynamics could be that the scope of the analysis is too large and results a more general analysis of the field. In addition, the characterization is possibly prone to selection bias. Furthermore, our overview of computational models could have excluded high-quality papers due to missing articles in our selected databases or a selection bias in our selection of search terms. A replication of our research using another scope or more detailed characterization of insurgency could test the robustness of our analysis. Although, we belief our holistic analysis upon models on contemporary insurgency conflicts provides interesting linkages between different modeling approaches. Therefore, with the lingering impact of insurgencies upon the global society, many interesting opportunities are present for computational model development and validation.
Footnotes
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
