Abstract
In this systematic review, we provide a summary of the current knowledge and understanding of escalation crossover offenders who transition from online to subsequent contact child sexual offenses. A systematic search of 14 databases was conducted to identify literature relevant to escalation crossover offenders. Thirty-two studies met the inclusion criteria. Findings reveal different profiles of escalation crossover from child sexual exploitation material (CSEM) offending, online solicitation (OS) offending, and commercial offending. Risk factors and characteristics of CSEM escalation crossover offenders included age, prior criminal history, sexual inclination toward children, cognitive distortions, severity, extremity, and frequency of CSEM engagement, communicating or attempting to communicate with children, and networking with other CSEM offenders. Risk factors and characteristics of OS escalation crossover offenders included race, age, marital/relationship status, employment status, education level, sexual inclination toward children, cognitive distortions, psychiatric disorders, and prior criminal history. Risk factors and characteristics of commercial escalation crossover offenders included race, age, employment status, marital/relationship status, and denying a history of contact offending. Behavioral themes were also identified for OS and commercial escalation crossover offenders. Findings and future directions are discussed in relation to practical, policy, and research implications.
Keywords
The anonymity, accessibility, and affordability of the internet (Cooper, 1998) and its associated freedom from social rules, restrictions, and regulations have enabled an environment where users can engage in criminality and deviancy. Online child sexual exploitation is defined as the use of technology or the internet to facilitate the sexual victimization of a child, including the production, dissemination and possession of child sexual exploitation material (CSEM); online grooming for sexual purposes (“sexting”); sexual extortion (“sextortion”), commercial sexual exploitation, such as livestreaming of child sexual abuse (Quayle, 2016). The diversity of online child sexual exploitation has been divided into consumers of CSEM, who use the internet to access, view and trade CSEM; sexual solicitors of children, who use the internet to contact victims and engage in inappropriate conversations to secure and manipulate them; and mixed sexual offenders, who are not limited to the internet, and commit contact child sexual offenses (Paquette et al., 2020). A less studied form of offending is the commercial sexual exploitation of children, including the sexual exploitation or abuse of a child resulting in financial benefit (Barnert et al., 2018).
Online child sexual exploitation (WeProtect Global Alliance, 2018) is marked by its increasing prevalence and significant challenges associated with estimating the true scale of this often-hidden offending. In 2021, the Australian Centre to Counter Child Exploitation (ACCCE) received over 33,000 reports (ACCCE, 2022). In the 2022–2023 fiscal year, the ACCCE received 40,232 reports being a further 22% increase from 2021 (ACCCE, 2022). On a global scale, 54% of 18-year-olds report having experienced online sexual harm during childhood (WeProtect Global Alliance, 2023). These figures are suggested to underestimate the level of online child sexual exploitation due to underreporting, despite the anonymity and complexities of the digital environment leading to increasing rates (Maxwell et al., 2024).
Online offending is inherently harmful and dangerous, and as the prevalence of online child sexual exploitation increases, questions are raised about the dangerousness posed by these offenders to the community (McCarthy, 2010), and the link between online and contact offenses. Quayle and Taylor (2003) note there is limited empirical support for a direct causal link between online offending, namely CSEM offenses, and subsequent contact offending, although Long et al. (2013) suggest that the quantity and consumption of stored CSEM collections are closely related to contact offending behaviors. These gaps in knowledge highlight the need for a holistic and nuanced exploration of the factors that facilitate the crossover from online to contact offending.
Crossover offending is defined as offenders who progress from online offending, such as CSEM, to contact child sexual offending (Babchishin et al., 2015; Merdian et al., 2018). However, crossover has also been used to describe sexual offenses where victims are different ages, gender, and relationship categories (Bourke & Hernandez, 2009; Eke & Seto, 2023; Owens et al., 2016), or where offenders are engaging in multiple offending categories without regard for the temporal order of offending, such as possession and production of CSEM, and traveling with intent to sexually abuse a child (Owens et al., 2016; Woodhams et al., 2021). This results in a combination of terms including “dual offenders,” “mixed offenders,” and “crossover offenders,” obscuring the understanding of the pathways from online to contact offending. Most empirical research has focused on dual or mixed offenders who engage in both online and contact offending, regardless of the temporal sequence. This cohort includes offenders who may have started their offending trajectory with contact offending and expanded to online offending. Crossover offenders are an under-researched, smaller subset of offenders with a distinct pathway from online to contact offending, and where our understanding of this developmental journey is limited. Another potential limitation is that online offenders are often classified as CSEM-only offenders. This may overlook a broader spectrum of online behaviors, such as commercial sexual exploitation (Babchishin et al., 2015; Lim et al., 2021; Paquette et al., 2020).
The Current Study
The order of offenses within the mixed/dual offending category is an area requiring further examination (Babchishin et al., 2022). Specifically, further research is required on crossover offenders. In this review, we collated and systematically analyzed all studies that have addressed crossover offending, including those directly focusing on this offending group within their scope or providing any related findings. In this review, we present our current understanding of the nature of crossover offending, including risk factors arising from online offending that potentially precipitate contact offending.
Method
This review was conducted in accordance with the Preferred Reporting Items for Systematic reviews and Meta-Analyses statement (Page et al., 2021).
Search Strategy
An extensive search of EBSCOhost, Scopus, ProQuest Central, including the Criminal Justice Database, Nursing and Allied Health Database, Psychology Database, Science Database, Social Science Database, and Sociology Database, was conducted between March to April 2024 to identify peer-reviewed articles that presented a typology or subtype of CSE offenders. Using the EBSCOHost platform, the following databases were searched: American Psychological Association (APA) PsychArticles, APA PsycInfo, Cumulative Index to Nursing and Allied Health Literature (CINAHL), MEDLINE, and Psychology and Behavioral Sciences Collection. The full search commands are available in Supplemental Material Appendix A. A search of research databases and gray literature was also performed on Google Scholar and MedNar with the following generalized search terms: “online child sexual abuse and exploitation offenders.” Searches were refined to exclude articles published in languages other than English.
To ensure the review was current, in April 2025, we: (a) reconducted the search with original and new search terms published between April 2024 to April 2025 in the same above databases; (b) conducted a new search with only new search terms (no timeframe restriction) in the same databases.
Eligibility Criteria
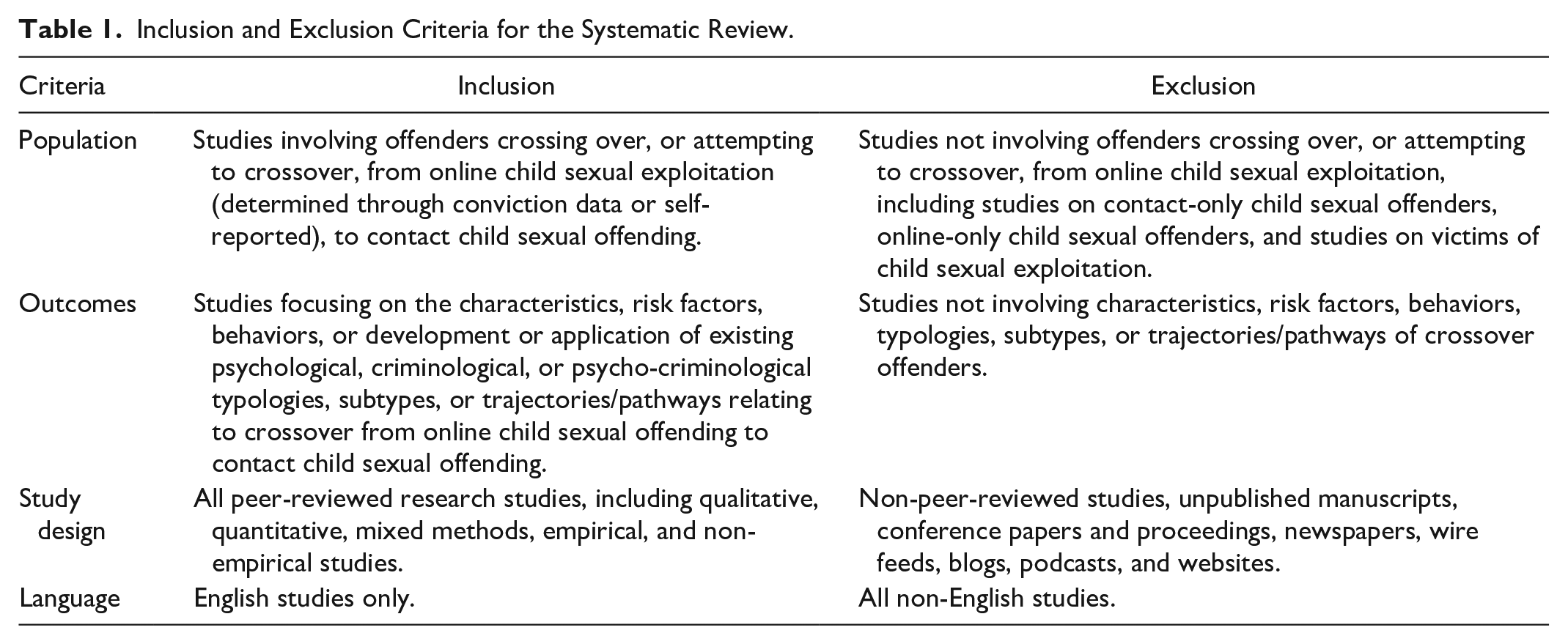
The studies found in the citation searches were assessed for eligibility in accordance with the inclusion and exclusion criteria in Table 1.
Inclusion and Exclusion Criteria for the Systematic Review.
Study Selection and Outcomes
Two independent reviewers carried out initial screening of titles and abstracts against the eligibility criteria (see Table 1) using Covidence. Eligible articles were independently assessed during full-text review by the same two reviewers to further assess eligibility. Differences of opinion between reviewed studies were resolved through discussion between authors. Data were extracted from each eligible study regarding study type, offending groups considered, data analysis, and results. For a detailed progression of each study through title and abstract screening and full-text screening, see Figure 1.
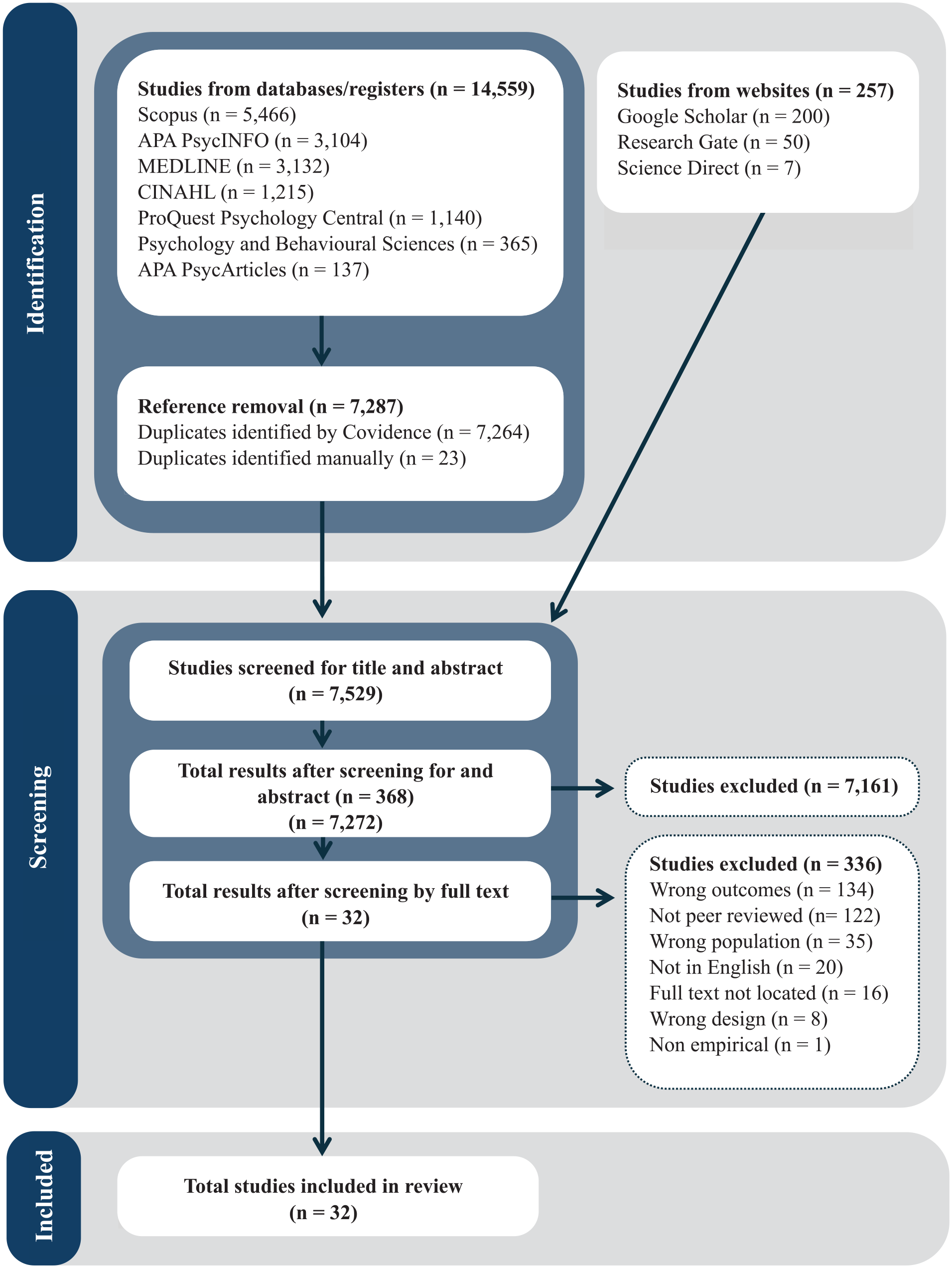
PRISMA flowchart.
Analysis
The results of this systematic review were analyzed qualitatively after combining the design, quality, and results of each study to produce a summary for all studies that considered crossover offending. A quantitative synthesis of findings was not possible due to the variety of study designs and samples.
Study Design
A total of 13,101 studies were imported for screening into Covidence in 2024, and a further 1,458 were imported in 2025. After removal of duplicates and screening against the eligibility criteria, a total of 32 studies were eligible for this review (see Figure 1), with a diversity of methodologies including qualitative, quantitative descriptive, quantitative nonrandomized, and mixed methods. An overview of the authors, study design, sampling, and offender groups is presented in Table 2.
Study Characteristics.
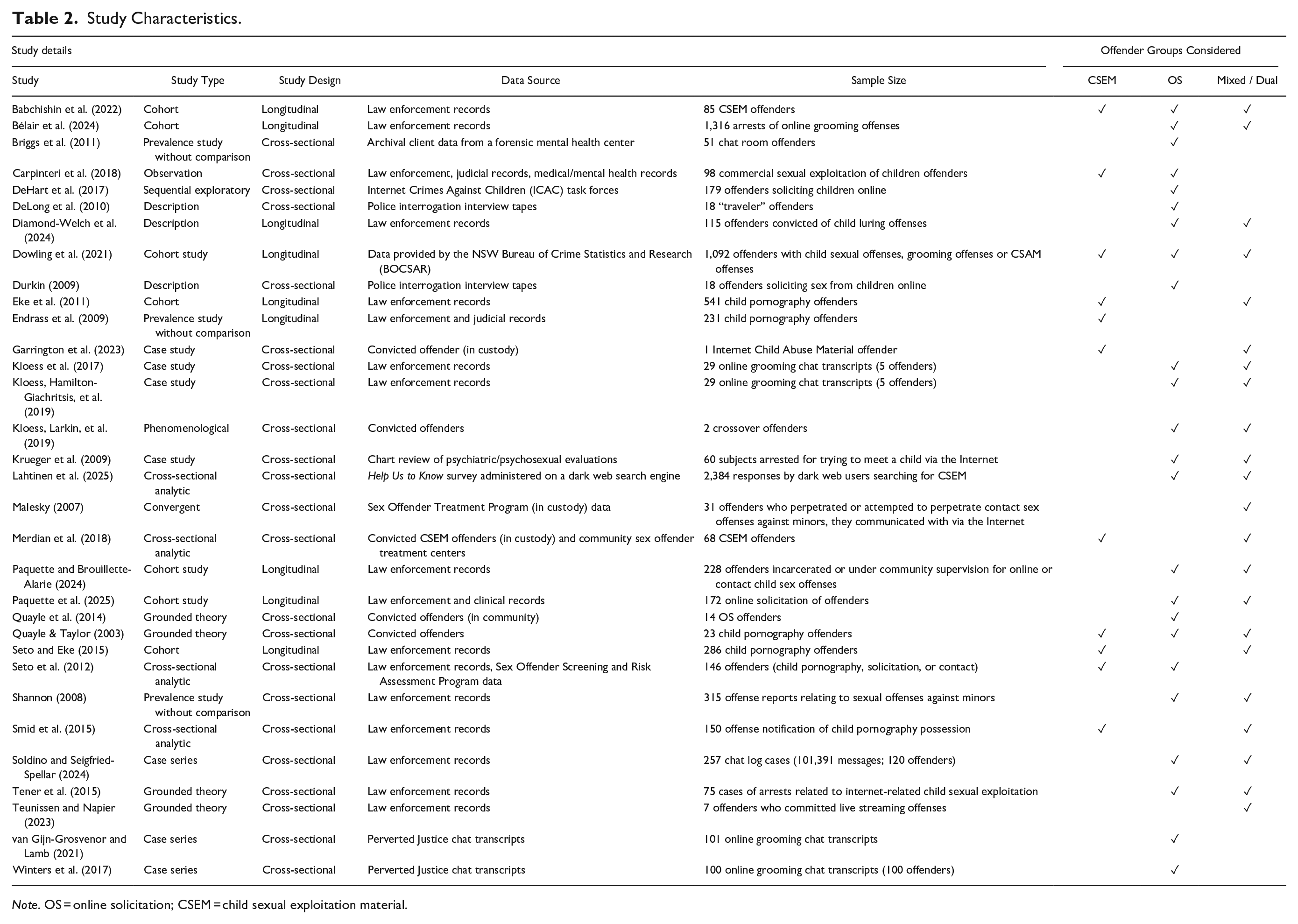
Note. OS = online solicitation; CSEM = child sexual exploitation material.
Quality and Risk of Bias Assessment
The Mixed-Method Appraisal Tool (MMAT; Hong et al., 2018) was employed to assess the quality of each study included in this systematic review. The methodological quality was high for 25 of the studies, medium for 5 studies, and low for 2 studies. The high-quality studies had clear research questions, demonstrated robust methodology, and linkages between data and findings. Most of the medium quality studies were more vague in their approaches or provided less robust and unclear methodology, and for the low quality studies, it was unclear how the chosen measurements were appropriate or allowed the researcher/s to answer the research questions.
All studies passed the initial screening questions, indicating that the tool could assess their methodological quality. Each study was assessed using the appropriate subscales depending on the study methodology. The results of the 32 studies included demonstrate preliminary evidence for a progression pattern from online to contact offending, suggesting the internet may be used as a precursor to more serious offending. Of the 32 studies, 10 contributed to our understanding of crossover from CSEM offending (Babchishin et al., 2022; Dowling et al., 2021; Eke et al., 2011; Endrass et al., 2009; Garrington et al., 2023; Lahtinen et al., 2025; Merdian et al., 2018; Quayle & Taylor, 2003; Seto & Eke, 2015; Smid et al., 2015), 21 from OS offending (Bélair et al., 2024; Briggs et al., 2011; DeHart et al., 2017; DeLong et al., 2010; Diamond-Welch et al., 2024; Dowling et al., 2021; Durkin, 2009; Kloess et al., 2017; Kloess, Hamilton-Giachritsis, et al., 2019; Kloess, Larkin, et al. (2019); Krueger et al., 2009; Malesky, 2007; Paquette & Brouilette-Alarie, 2024; Paquette et al., 2025; Quayle et al., 2014; Seto et al., 2012; Shannon, 2008; Soldino & Seigfried-Spellar, 2024; Tener et al., 2015; van Gijn-Grosvenor & Lamb, 2021; Winters et al., 2017), and 3 from commercial offending (Carpinteri et al., 2018; DeHart et al., 2017; Teunissen & Napier, 2023). Refer to Supplemental Material Appendix B for a full overview of the quality and risk bias assessment completed.
Longitudinal Versus Cross-Sectional Studies: Examination into Direct and Indirect Crossover
We define crossover offenders as those who display a particular trajectory of the contact offense being, or attempting to be, committed after the online offense (s). It is important here to differentiate between longitudinal studies that undertake a direct examination of crossover and cross-sectional studies that undertake an indirect examination of crossover. Longitudinal studies track individuals over time to observe the temporal sequence of events, for instance, if offenders have subsequent contact with child sexual offenses, and cross-sectional studies are only able to examine behaviors at a single point in time. As such, nine studies (Babchishin et al., 2022; Bélair et al., 2024; Diamond-Welch et al., 2024; Dowling et al., 2021; Eke et al., 2011; Endrass et al., 2009; Paquette & Brouillette-Alarie, 2024; Paquette et al., 2025; Seto & Eke, 2015) being longitudinal in design, directly examine crossover from CSEM or OS to subsequent contact child sexual offences. Notably, Paquette and Brouillette-Alarie (2024) directly examined crossover; however, they do not differentiate between CSEM and OS in the online offending group. Garrington et al. (2023), Kloess et al. (2017), and Kloess, Larkin, et al. (2019), through cross-sectional studies, have also directly examined crossover by identifying the risk factors for crossover from online to contact offenses.
The remaining 20 studies were cross-sectional in design and provided indirect findings related to crossover. Two of these (Merdian et al., 2018; Quayle & Taylor, 2003) had a broader focus on mixed groups that do not consider the transition from online and contact offending, and Smid et al. (2015) studied the link between CSEM to broader direct victimization, including contact offending, grooming, online offending, or CSEM production. The study by Lahtinen et al. (2025), although it did not distinguish between the mixed and crossover groups, used regression analyses to identify predictive variables increasing the likelihood of online contact offenses. All OS studies measured offenders who attempted and/or perpetrated contact offending against minors initiated over the internet. All three commercial offending studies researched offenders who initiated their offending online and progressed, or attempted to progress, to contact offending. The findings of each study will be discussed according to the types of offending.
Results and Discussion
Crossover Prevalence
Eighteen studies assessed the prevalence of crossover offending, with five directly assessing crossover from CSEM offending (Babchishin et al., 2022; Dowling et al., 2021; Eke et al., 2011; Endrass et al., 2009; Seto & Eke, 2015), 11 considering crossover from OS offending (Bélair et al., 2024; Briggs et al., 2011; DeHart et al., 2017; Diamond-Welch et al., 2024; Dowling et al., 2021; Kloess et al., 2017; Kloess, Hamilton-Giachritsis, et al., 2019; Malesky, 2007; Paquette & Brouillette-Alarie, 2024; Paquette et al., 2025; Quayle et al., 2014; Seto et al., 2012; Shannon, 2008; Soldino & Seigfried-Spellar, 2024; van Gijn-Grosvenor & Lamb, 2021; Winters et al., 2017), and three from commercial offending (Carpinteri et al., 2018; DeHart et al., 2017; Teunissen & Napier, 2023).
Prevalence of crossover from commercial offending varied, ranging from 13% to 57%. Prevalence rates were low for CSEM (range: 0.8%–12%), consistent with studies reporting low recidivism baseline rates for CSEM offenders committing future contact offenses (Babchishin et al., 2018; Henshaw et al., 2018; Merdian et al., 2020; Seto & Eke, 2015). There was variability in prevalence rates for OS offenders crossing over, or attempting crossover, to contact offending, ranging from 15% to 96%, suggesting OS offenders who crossover may use the internet as a means to access victims. This is supported by research assessing the use of the internet by online offenders, suggesting online interactions serve as an antecedent to more serious abuse occurring offline, which is driven by intentions for victim selection and/or recruitment (Hornor et al., 2022; Paquette & Cortoni, 2022), further reinforcing the original typology proposed by Briggs et al. (2011) differentiating contact-driven and fantasy-driven offenders. Different OS studies found varying prevalence rates for attempted crossover (for example, scheduling a meeting) when compared to completed crossover (for example, attempting to meet the victim at the agreed location). Briggs et al. (2011) found that 93.3% of contact-driven offenders scheduled a face-to-face meeting; Kloess, et al. (2017) found that out of the total five cases, the offending motivation of two online groomers could be linked to arranging a meeting which led to contact sexual offenses; Kloess, Hamilton-Giachritsis, et al. (2019) found that out of the total five cases, offenders often introduced a physical meeting, however, only one offender arranged the physical meeting (though this did not take place); Malesky (2007) found that 45% attempted to set up in-person meetings; Quayle et al. (2014) found that 36% arranged to meet their victim; Winters et al. (2017) found that in 96% of cases, the offender attempted to arrange an in-person meeting with the decoy victim; DeHart et al. (2017) found that prevalence of setting up meetings ranged from 13% to 35% depending on the type of offender; and van Gijn-Grosvenor and Lamb (2021) found that 23% of offenders invested a lot of time and effort in arranging offline sexual encounters. In contrast, Briggs et al. (2011) found that 80% of contact-driven offenders made an actual attempt to meet their victim at the agreed location; Diamond-Welch et al. (2024) reported that following an index OS offense, 41.38% went on to commit another OS offense where they intentionally took a step toward physical meeting; and Shannon (2008) found that in 22% of cases, the offender and victim transitioned to an in-person meeting where the offender subsequently committed a contact sexual offense. While not differentiating between scheduling and attempts to meet the victim, Bélair et al. (2024) reported that 28.6% of online groomers were contact oriented and therefore more likely to lead to contact offending, and an additional 17.1% of online groomers aimed to meet their victims offline, given that they generally engaged in predatory offenses. Similarly, Paquette et al. (2025) found that 43.9% of OS offenders indicated that they either attempted or completed an offline meeting, whether with a real victim or an undercover officer. Dowling et al. (2021) reported that no OS offenders moved on to commit contact offenses; rather, most of those who reoffended did so with CSEM offenses (9%), noting that this study was limited to data that came to the attention of law enforcement. Diamond-Welch et al. (2024) found that 17.7% of offenders with an index offense of OS escalated to a commercial child sexual exploitation conviction. Diamond-Welch et al. (2024) report that many OS offenders continue to escalate to other serious offenses, such as commercial offending and child sex trafficking, supporting DeHart et al.’s (2017) inference that OS offenders may be involved in a range of other child exploitation offenses.
Crossover from CSEM: Demographics and Characteristics
Several risk factors were identified across the studies considering crossover from CSEM. Many studies identified age as a critical risk factor (Babchishin et al., 2022; Eke et al., 2011; Garrington et al., 2023; Seto & Eke, 2015), with the range of 25 to 39 years at the highest risk of crossover and an average age of 32 years (Babchishin et al., 2022). Findings also suggested that having a sexual inclination toward children, or pedophilia (Eke et al., 2011; Garrington et al., 2023; Quayle & Taylor, 2003; Seto & Eke, 2015), is an important motivation for facilitating the use of the internet as a medium for meeting their victims, and for acting on one’s sexual contact with children. Cognitive distortions were noted as playing a key role in the escalation of behavior from online to contact offending (Merdian et al., 2018; Quayle & Taylor, 2003), particularly as they support the legitimacy of sexual inclination toward children and allow the offender to normalize the behavior. Prior criminal history was identified as a risk factor (Eke et al., 2011; Merdian et al., 2018; Seto & Eke, 2015; Smid et al., 2015), where prior police contacts, charges, and convictions including noncontact sexual offending (i.e., CSEM possession, exhibitionism; Smid et al., 2015) increased the risk of crossover. Other risk factors included higher levels of substance abuse (Babchishin et al., 2022), being unemployed, communicating (or attempting to communicate) with children (Garrington et al., 2023; Lahtinen et al., 2025), and seeking physical contact with children (Lahtinen et al., 2025). Crossover offenders were also less likely to be married or in a committed relationship (Babchishin et al., 2022; Garrington et al., 2023).
Crossover from CSEM: Online Offending Behaviors
Several behavioral risk factors were identified across the studies considering crossover from CSEM. Studies identified the nature of CSEM content (Garrington et al., 2023; Lahtinen et al., 2025; Smid et al., 2015) being relevant to their risk of crossover, with watching videos (instead of viewing photos-only) and engaging with extreme material, such as penetrative sexual activity between adults and children, sadism or bestiality involving children, or content with victims below 5 years old, the highest risk category. Regularity of viewing and classifying CSEM was also identified as associated with risk contribution to further offending (Garrington et al., 2023). In contrast, Merdian et al. (2018) found that higher frequency and intensity of extreme CSEM use were associated with fantasy-driven CSEM users as opposed to contact-driven. Communication with other offenders, which can enable learning tips and tricks of the trade, was also found to be another risk factor (Garrington et al., 2023).
Crossover from OS: Demographics and Characteristics
Like CSEM offenders, age was identified as a risk factor for online grooming offenders at risk of crossover, with Briggs et al. (2011) reporting an average age of 30 years, Winters et al. (2017) reporting 32 years, Krueger et al. (2009) reporting 39 years, Shannon (2008) a range of 25 to 34 years, and Bélair et al. (2024) reporting a range of 29 and 30 years. Most crossover offenders had never been married, were single or divorced, or had relationship problems (Seto et al., 2012), and were unemployed (Briggs et al., 2011; DeLong et al., 2010; Durkin, 2009). Findings were inconsistent for education level, with one reporting crossover offenders having less formal education (Briggs et al., 2011), another reporting higher levels of education (Seto et al., 2012). Sexual inclination toward children (DeHart et al., 2017), including specific hebephiliac sexual interests (Seto et al., 2012), was identified as a characteristic for these offenders as reported or indicated in the grooming conversations. Further, cognitive distortions, including justification, minimization, and refutation (DeLong et al., 2010), and disavowal strategies, including denial of pedophilia/perversion, attribution to poor judgment, and denial of sexual intent, were found (Durkin, 2009; Kloess, Larkin, et al. (2019)). Psychiatric findings included compulsive pornography use as well as DSM-IV-TR Axis I diagnoses (Briggs et al., 2011), notably, hypersexual disorder characterized by cyber sexual dependence (Krueger et al., 2009). Most crossover offenders were also noted to be Caucasian (DeHart et al., 2017; DeLong et al., 2010; Malesky, 2007). Additionally, one study (Kloess, Larkin, et al. (2019)) noted personal life problems as a potential risk factor, as findings suggested that offenders sought the internet and engaged in offending as a coping mechanism and sexual outlet. One study (Bélair et al., 2024) also noted that the majority of crossover offenders perpetrated another sexual crime other than online grooming.
Crossover from Online Solicitation: Behavioral Themes
Victim Selection Behaviors
Selection of victims is the first step in initiating the online grooming process. This included targeting chat rooms geared toward minors and utilizing online profiles, bulletin boards, and username age identifiers to screen for victims (Malesky, 2007; Kloess, Hamilton-Giachritsis, et al., 2019), and preferences for age and gender (Tener et al., 2015). Victim selection was first based on minors mentioning sex in any form online, second, on appearing “needy,” “submissive,” or lonely children looking for attention, and third, having their age apparent in their usernames (Malesky, 2007). Offenders spent a significant amount of time, across multiple platforms, and a variety of techniques in attracting victims, sometimes collaborating with other offenders to help access victims (Malesky, 2007; Tener et al., 2015). Soldino and Seigfried-Spellar (2024) found that contact-driven offenders were more likely to have some degree of pre-existing relationships with victims before the grooming process commenced.
Rapport-Building Conversational Behaviors
Offenders were likely to employ rapport strategies by spending time in lengthy conversations with victims, including transitioning between different online platforms (Briggs et al., 2011; Soldino & Seigfried-Spellar, 2024; Tener et al., 2015; van Gijn-Grosvenor & Lamb, 2021). In contrast, Tener et al. (2015) identified attention-focused offenders who were characterized by genuine feelings of affection for victims, a relationship without coercion or manipulation. The relationship developed by attention-focused offenders was usually of a close romantic relationship, where both offenders and victims were interested in meeting face-to-face to pursue a long-term relationship. This is similar to Shannon’s (2008) findings, where the largest group of offline offense reports related to cases where the offenders developed a friendship or romantic relationship with the victim online, and in some of these cases, the victim had fallen in love with the offender. Tener et al. (2015) also identified a group of sex-focused offenders, where both the offender and victim were interested in pursuing offline sexual encounters and almost immediately engaged in doing so. Notably, sex-focused offenders did not exclusively target minors. Similarly, Kloess et al. (2017) found that offenders did not engage in a friendship or relationship-forming process with their victims, nor did they believe they were in a romantic relationship with them. Instead, offenders almost immediately introduced sexual topics to initiate online sexual activity. Kloess, Hamilton-Giachritsis, et al. (2019) also found mixed results regarding relationship-building behaviors, with some offenders spending time to get to know the victim and engaging in aspects of relationship building, whereas others employed a direct and blunt approach to introduce sexual content almost immediately. The authors noted that not all online solicitation interactions necessarily involve online grooming.
Sex-Related Preparatory Behaviors
Winters et al. (2017) found that in most cases (68%), sexual content was introduced within the first 30 minutes of the conversations and within the first day. In contrast, Soldino and Seigfried-Spellar (2024) found that contact-driven offenders gradually introduced sexual content into prolonged and frequent conversations. Once introduced, contact-driven offenders were likely to send unprompted sexually explicit images of themselves to victims. In 48% of cases, the victims willingly or under manipulation sent sexually explicit images of themselves back to the offender. Dehart et al. (2017) reported that 48% of cybersex/schedulers and 14% of schedulers exposed themselves through camera or video; 48% of cybersex/schedulers and 23% of schedulers sought sexually explicit photos from the victim. Cybersex/schedulers were also noted to discuss the victim’s sexual features, such as their breast size or pubic hair, often attempting to coach the victim in masturbation. These offenders also discussed details of sexual behavior and plans that would be carried out when they met. Kloess et al. (2017) found that offenders used many strategies, directive and suggestive, to initiate online sexual activity. This included exposing themselves through webcam, masturbating, and directing female victims to carry out digital penetration themselves. Offenders also displayed a pattern of pursuing sexual information from the victim, including their sexual likings, body parts, and previous sexual experiences. In contrast, schedulers appear more opportunistic, seeking quick sexual “hook-ups,” where the offender may or may not discuss victims’ sexual experiences before scheduling a meeting. Consistent with the above, van Gijn-Grosvenor and Lamb (2021) found that sending or requesting sexually explicit photos, discussing intended sexual activities, or offering to teach victims about sexual matters was a way to desensitize victims, normalize sexual matters, and prevent disclosure. Kloess, Hamilton-Giachritsis, et al. (2019) also found that in interactions that featured online grooming, offenders used a range of strategies, including compliments and flattery, to sexualize the conversation and make the victim feel “special.” There were differences, however, in whether they employed a direct or indirect approach; offenders employing a direct approach utilized blackmail/threats, insults, and peer pressure to incite the victims in sexual activity, whereas offenders employing an indirect approach presented themselves as desperate or in need of sexual stimulation. Malesky (2007) found that 52% of offenders reported sending CSEM to their victims and 97% engaged in sexually explicit conversations with them; in contrast, however, Briggs et al. (2011) found that contact-driven offenders were less likely than online-focused offenders to exchange CSEM with victims. Briggs et al. (2011) also found that contact-driven offenders engaged in relatively short relationships prior to attempt meeting, where sexually explicit conversations were a means to identify a sexually active victim, determine their willingness to engage in sex with an adult, willingness to keep it a secret, and describe the intended sexual behaviors in which they would engage.
Scheduling Behaviors
A distinction was identified between suggesting an in-person meeting and having an intention to proceed with the meeting. Soldino and Seigfried-Spellar (2024) found that 66.5% of cases referred to in-person meetings but only 13.6% observed specific scheduling. Briggs et al. (2011) found that 93.3% of contact-driven offenders scheduled an in-person meeting, out of which 80% attempted to meet the victim. Similarly, DeHart et al. (2017) found that cybersex/schedulers were the most likely to cancel or be a no-show at meetings, which could be attributed to offenders pretending to be interested in meeting to extend online interaction, or that discussions of meetings alone may lead to sexual gratification. Kloess et al. (2017) also found that while all five offenders discussed elaborate fantasies of a physical meeting and the sexual activities it would entail, the motivations of only two offenders could be linked to arranging a physical meeting. Similarly, Kloess, Hamilton-Giachritsis, et al. (2019) found that despite most offenders introducing a physical meeting, only one offender attempted to arrange the meeting. These findings support the fantasy-driven offender proposed by Briggs et al. (2011), who are solely motivated to engage in cybersex with minors for both sexual arousal and gratification without intentions of meeting offline. Malesky (2007) also identified that 45% of offenders attempted to arrange in-person meetings; however, they noted this may not capture the true extent of crossover offenders, as other offenders also intended to schedule meetings but were intercepted by law enforcement before they could do so. Winters et al. (2017) found that offenders typically moved quickly to attempt offline contact after only 3 days. These findings contrast with findings by Shannon (2008), who reported that the length of the online contacts varied depending on the type of method utilized by the offenders, including for over 6 months before the contact offense in one-third of cases. Three different methods were identified that offenders used to coerce victims into agreeing to an offline meeting: promising work as a model, offering payment for sexual services, and developing a friendship or romantic relationship. The second method is consistent with Soldino and Seigfried-Spellar (2024), who found that contact-driven suspects were more likely to offer incentives, such as money or drugs, to victims to negotiate in-person encounters.
Crossover from Commercial Offending: Demographics and Characteristics
Demographics
Only one study (Carpinteri et al., 2018) focused on analyzing characteristics to differentiate types of commercial offenders and found that being younger (under the age of 35), unemployed, single, and denying a history of contact offending were predictive variables of offenders engaging in traveling/enticement of their victims. Also, DeHart et al. (2017) noted that most buyers were Caucasian.
Crossover from Commercial Offending: Behavioral Themes
Transactional Versus Intimate Relationships
Most commercial offender/victim relationships appeared transactional, where scheduling and negotiation of terms was often the focus, including what sex acts would be allowed and any costs (DeHart et al., 2017; Teunissen & Napier, 2023). Teunissen and Napier (2023) found that some offenders believed they were in an intimate relationship with both the victims and/or facilitators. Romantic language used by offenders and victims was observed toward each other in their communication. The authors argue that this romantic and familial relationship building between offenders and facilitators/victims was a key factor in increasing the risk of contact offending, as it allowed offenders greater access and an increased desire to sexually abuse the victims in person.
Exchange of Sexually Explicit Material and Engagement with CSEM
An interrelationship between CSEM and crossover was found in the commercial offending studies. DeHart et al. (2017) found that although buyers were less frequently exposed themselves through camera or video (17%), a third sought sexually explicit photos from the victim to prove they were “real.” Teunissen and Napier (2023) also found that it was common for live streaming offenders to request images and/or videos of the victims from the live streaming sessions. Further, out of the four offenders who traveled to offend, three did so after viewing their victims in live streaming sessions.
Financial Exchange
Financial exchange was found to occur throughout the relationship, where offenders paid for photos and videos (Teunissen & Napier, 2023), particularly for the final transition to contact offending. Teunissen and Napier (2023) provided further insights on this, arguing that a second key factor in increasing the risk of crossover is the vulnerability of the victims, where they are likely to comply with the offender’s requests for monetary benefit.
Limitations and Future Directions
Inconsistent Nomenclature
As stated above, there is an overall lack of consistent nomenclature regarding the term “crossover.” Not only has the term been used to describe distinct types of offenders, but it is also not consistently used to refer to the type of offending being considered. We recommend that future research referring to this offending group use the terminology of “escalation crossover offenders,” consistent with the “escalation pattern” group in Babchishin et al. (2022), to distinguish this group from other types of crossover offenders in the literature. Future research is needed to standardize the terminology used for distinct types of offenders, including crossover offenders, to ensure that policymakers, researchers, and practitioners can search for relevant studies more effectively.
Not a Linear Process
While many of the themes presented in this paper may seem to be part of a linear process, for example, OS groomers progressing from victim selection to rapport building, to sex-related preparation, to scheduling, it cannot be concluded that these stages occur linearly and follow such a static trajectory. Kloess, Hamilton-Giachritsis, et al. (2019) also noted that their results indicated that the process of OS is a varied and nonlinear process, as offenders did not move through a particular notion of stages. This is consistent with research suggesting that not all offenders follow a linear path (Fortin et al., 2018), and that certain stages of the online grooming process, such as the conclusion or scheduling stage, occur throughout the conversation and not just at the end (Gupta et al., 2012).
In this review, the focus was on linkages between online and subsequent contact offending; however, it should be noted that not all offenders will follow a linear path from online offending categories (CSEM, OS, commercial) to contact offending. Research has noted that some offenders adopt a parallel strategy (Fortin et al., 2018) where they may be offending in multiple categories at the same time. This may also include the types of online offending before the crossover to contact offending. A recent study (Insoll et al., 2022) found a link between CSEM and OS offending, suggesting that the frequency of CSEM use was a key factor in increasing the likelihood of CSEM offenders engaging in OS offending. Briggs et al. (2011) also found that almost half of the fantasy-driven offenders had engaged in online contact with a minor, suggesting a link between CSEM and OS offending. Diamond-Welch et al. (2024) and DeHart et al. (2017) suggested a potential trajectory from OS to commercial offending. While crossover offenders may be at higher risk of committing contact offenses, there may be a higher risk of online-only offenders, such as fantasy offenders, extending their online crimes by contacting children online and potentially coercing them to produce CSEM.
Lack of Direct Research into Escalation Crossover
As evident from the findings of this review, there is a lack of direct research into crossover offending, particularly in undertaking a longitudinal design to analyze the progression from online to subsequent contact offending. A distinction between longitudinal and cross-sectional is crucial for the interpretation of findings, as noted in this review, and particularly when investigating escalation crossover offenders. This is because longitudinal studies directly examine the escalation of offending by considering its temporal element, allowing for conclusions about the developmental pathway from online to contact offenses. In contrast, cross-sectional studies can only provide an indirect examination of escalation crossover offending by analyzing offenders at a single point in time. This has significant implications for practitioners, as longitudinal data can provide insight into the predictive variables of escalation and inform risk assessment responses through the temporal sequencing of events. In this review, we only found nine studies that undertook a longitudinal design, and so there is a need for future research on longitudinal studies to examine the temporal relationships between online and contact offending further.
In this review, we synthesized a number of risk factors that can contribute to escalation crossover, and in doing so, we note the limitations of existing risk assessment tools. At present, there are only a handful of risk assessment tools relating to online child sexual exploitation (Reichel et al., 2024), including the Child Pornography Offender Risk Tool (CPORT; Seto & Eke, 2015), the Kent Internet Risk Assessment Tool-Version 2 (KIRAT-2; Long et al., 2016), and the Estimated Risk for Internet Child Sexual Offending (ERICSO; Garrington et al., 2022). Notably, some risk factors from CPORT and KIRAT-2 have also been identified in this review, such as age, prior criminal history, sexual inclination toward children, and communicating or attempting to communicate with children. Both the CPORT and KIRAT-2 have limitations in assessing escalation crossover as they were designed to consider risk from CSEM behaviors and therefore do not consider the diversity of other online offending behaviors and their respective profiles. Although the KIRAT-2 has been approved for use by law enforcement in the United Kingdom (Reichel et al., 2024), it is not a predictive tool, further highlighting the need for distinction between cross-section and longitudinal methodologies. Similarly, the ERICSO has not been evaluated as a predictive tool and at present, can only be used as a framework for data collection (Reichel et al., 2024). Consequently, we suggest that future studies prioritize longitudinal methodologies to consider temporal elements of offending and develop tools with predictive validity. Noting the limitation of current risk assessment tools, our findings also indicate a need for research to contribute to the integration and refinement of existing tools or the development of a new tool to specifically address escalation crossover offending. This development should focus on two key areas as identified by this review: first, consideration of the diversity of offending, including CSEM, OS, and commercial; and second, integrating the temporal sequence of events in the assessment of risk. This tool should also differentiate between attempted and completed crossover for OS offenders to inform accurate risk assessment responses.
Conclusion
The aim of this review was to synthesize current understanding of crossover offenders escalating from online to contact, with a focus on CSEM, OS, and commercial offenders. We found prevalence rates of escalation crossover were low for CSEM offenders, high for OS offenders, and inconclusive for commercial offenders. Risk factors for CSEM escalation crossover offending included age, prior criminal history, sexual inclination toward children, cognitive distortions, severity, extremity, and frequency of CSEM engagement, communicating or attempting to communicate with children, and networking with other CSEM offenders. Risk factors for OS escalation crossover offending included race, age, marital/relationship status, employment status, education level, sexual inclination toward children, cognitive distortions, psychiatric disorders, and prior criminal history. Risk factors for commercial escalation crossover offending included race, age, employment status, marital/relationship status, and denying a history of contact offending. Behavioral themes of online groomers crossing over included victim selection methods, rapport-building behaviors, and sex-related preparatory and scheduling behaviors. Behavioral themes of commercial offenders included developing transactional and/or intimate relationships with victims and facilitators, the exchange of sexually explicit material, and financial exchange. A summary of our critical findings can be seen in Table 3 below.
Summary of Critical Findings.
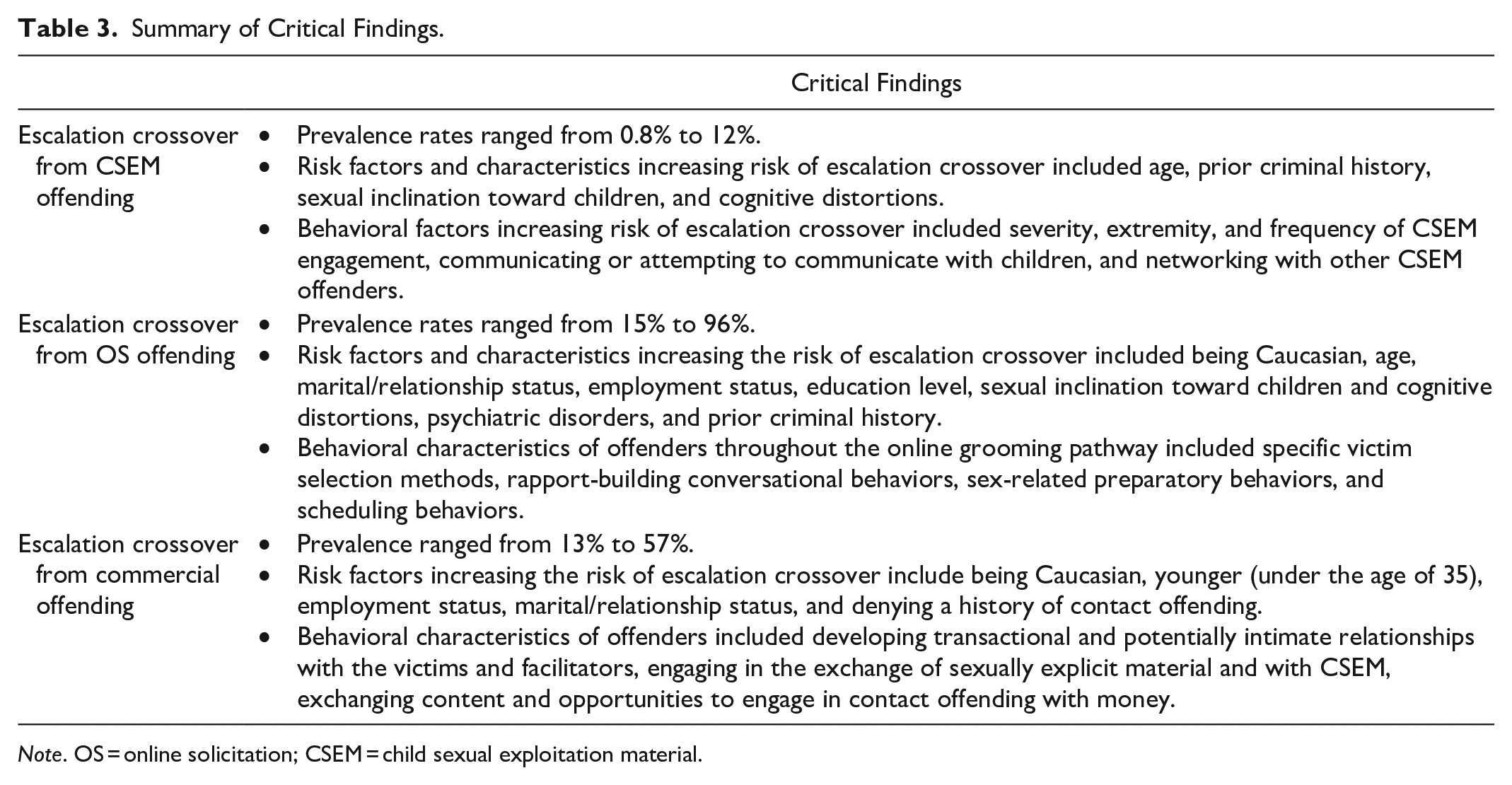
Note. OS = online solicitation; CSEM = child sexual exploitation material.
Furthering our knowledge of escalation crossover offenders is important regarding implications for law enforcement, practitioners, and policy. Law enforcement could benefit from a robust evidence base on escalation crossover offenders, informing risk assessment and early detection. Practitioners and clinicians could benefit from empirical evidence to guide offender profiles and to underpin rehabilitation programs and strategies. Policymakers could benefit from the standardization of terminology describing escalation crossover offenders and the risk posed by this offending. Our findings emphasize the importance of moving toward a robust understanding of the pathway and trajectories from online to contact offending. A summary of the implications of this review for policy, practice, and research can be seen in Table 4.
Summary of Implications for Practice, Policy, and Research.
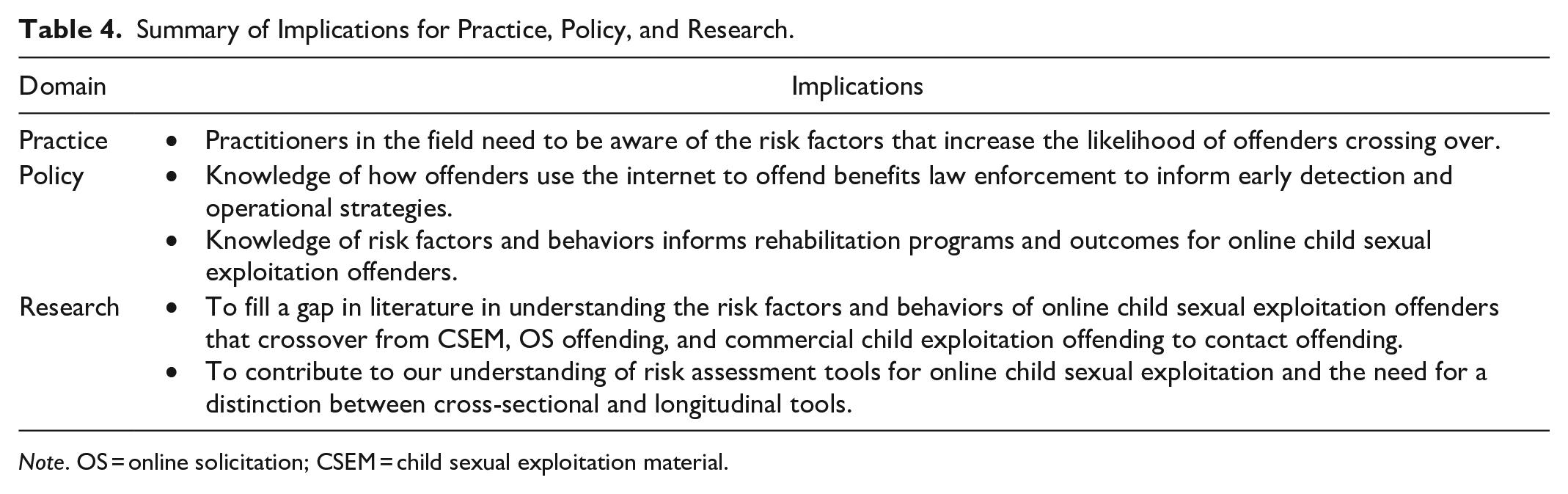
Note. OS = online solicitation; CSEM = child sexual exploitation material.
Supplemental Material
sj-docx-1-tva-10.1177_15248380251361065 – Supplemental material for Crossing the Line: A Critical Systematic Review of Escalation Crossover Offending in Online Child Sexual Exploitation
Supplemental material, sj-docx-1-tva-10.1177_15248380251361065 for Crossing the Line: A Critical Systematic Review of Escalation Crossover Offending in Online Child Sexual Exploitation by Naushaan Ahmad, Sally F. Kelty, Phillip S. Kavanagh and Thomas Tran in Trauma, Violence, & Abuse
Footnotes
Acknowledgements
We would like to acknowledge and thank Mr. Murray Turner, Research Associate and Senior Librarian at the University of Canberra, for their expertise and guidance on the methodology used in this review. We extend our thanks to our peer reviewers who provided valuable comments on our manuscript and whose insights allowed us to enhance our work.
Author Contributions
Data Availability Statement
The datasets generated and analyzed during the current study are available from the corresponding author on reasonable request.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
This research did not receive any specific grant from funding agencies in the public, commercial, or not-for-profit sectors. However, the corresponding author received Australian Commonwealth Government funding under the Postgraduate PhD Research Training Program (RTP).
Ethical Approval and Informed Consent Statements
Not required.
Consent for Publication
Not applicable for this systematic review.
Generative AI
Large Language Models (LLMs, e.g., ChatGPT) were not used in our research or in this paper.
Supplemental Material
Supplemental material for this article is available online.
Author Biographies
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
