Abstract
Over recent years, there has been a notable increase in online sexual grooming and technology-assisted child sexual abuse. However, to date, a comprehensive overview of the manipulative strategies used by individuals with a history thereof to approach, identify, and engage children and young people in these contexts, with a focus on real-world, naturally-occurring data, is absent from the existing literature. The systematic literature review presented here therefore intends to fill this gap. A mixed-methods systematic literature search was conducted in September 2023 across six databases, in addition to a gray literature search, using relevant terms. A total of 12 articles were included in the review, and a thematic synthesis approach was used to integrate the qualitative and quantitative data. Eight themes and 37 subthemes were identified. The findings highlight that individuals use a number of different strategies which are of a highly manipulative, adaptive, and individualized nature in order to identify, approach, and engage victims in online sexual grooming, and technology-assisted child sexual abuse respectively. Our findings are discussed with a view to informing directions for future research and practical implications.
Keywords
Introduction
The exponential growth of the Internet since the 1980s, alongside the continuous evolvement of social media platforms, has increased opportunities for individuals with a sexual interest in children to identify, contact, and groom them online (Borj et al., 2023; Lykousas & Patsakis, 2021). According to the National Society for the Prevention of Cruelty to Children (NSPCC), recorded offenses of online sexual grooming (OSG) have risen by 82% from 2017 to 2018 (NSPCC, 2022b). Despite this, this figure likely only represents the tip of the iceberg, given the issue of under-reporting around child sexual abuse more generally, and in relation to OSG specifically. The manipulative nature of OSG, alongside self-blame and shame, means that children and young people 1 may often not realize or disclose that they are being or have been groomed (Greene-Colozzi et al., 2021). As such, the true prevalence of OSG is widely believed to be much higher than documented cases, with a substantial proportion of events thought to remain hidden within the dark figure of crime.
A number of studies over the past two decades have examined OSG, yet misperceptions remain regarding the definition of “grooming” and what it represents. Craven et al. (2006) describe “grooming” as a deliberate process used to prepare a child, their surroundings, and influential adults for abuse. The main aims of this process are to gain access to the child, ensure their compliance, and secure their silence to prevent disclosure. This process also reinforces the individual’s abusive behavior by helping them rationalize or deny their actions. While developed in the context of offline abuse, this definition still very much applies to the online environment – that is, “grooming” is the process whereby a child is prepared for abuse, irrespective of whether the abuse takes place via Internet technologies or in the physical world (Kloess et al., 2014, 2017, 2019).
More specifically, technology-assisted child sexual abuse (TA-CSA) refers to child sexual abuse that involves the use of digital or online technologies (Hamilton-Giachritsis et al., 2021). This term is preferred to “online sexual abuse” as it more accurately captures how such abuse often spans both digital and offline interactions. Nevertheless, the term “grooming” is still frequently used in the academic literature to describe TA-CSA, which risks trivializing these acts and failing to reflect that they constitute abuse (Kloess et al., 2017; Whittle et al., 2014). Another common misperception is that “grooming” only occurs as a precursor to meetings in the physical world, rather than a preparatory process to elicit sexualized conversation, sharing of sexual images, sexual activities via webcam, or other sexual exchanges without necessarily attempting offline contact (Kloess et al., 2017, 2019). In fact, research indicates that many cases of a sexually exploitative and abusive nature, where contact is first initiated online, never progress to offline meetings (Briggs et al., 2011; Gottschalk, 2011; Kloess et al., 2017, 2019; Whittle et al., 2013), suggesting the existence of a subgroup of individuals whose sole motivation appears to be to engage in cybersexual interactions.
Although grooming and abuse can be conceptually distinguished, they frequently overlap in practice. It can be challenging to determine where grooming ends and sexual abuse begins, as individuals may alternate between grooming behaviors and overtly abusive acts. Some sexually abusive behaviors, such as the exchange of explicit material, may also serve ongoing grooming purposes, further complicating efforts to separate these processes both conceptually and in research (Mooney & Ost, 2013; Winters & Jeglic, 2017). This fluidity underscores the need for a more nuanced understanding of OSG and TA-CSA as interlinked processes.
Theoretical frameworks have been applied to explain both the motivation for and facilitation of sexual offending online, and provide an important foundation for understanding the strategic behaviors observed in OSG and TA-CSA. Finkelhor’s Precondition Model (1984) outlines four preconditions that must be met for sexual offending to occur: (a) motivation to sexually offend, (b) overcoming internal inhibitors, (c) overcoming external inhibitors, and (d) overcoming the child’s resistance. For example, motivation may be reflected in behaviors such as frequenting platforms popular among children (Briggs et al., 2011; Malesky, 2007), while overcoming internal inhibitors can be facilitated by the psychological distance of online communication (Alexy et al., 2005; Quayle & Taylor, 2001). Cooper’s (1998) Triple A Engine further explains the specific aspects of the Internet that facilitate these processes – that is, anonymity reduces the perceived risk of detection and weakens external barriers to offending, accessibility increases opportunities to contact children in the absence of guardians, and affordability (in terms of time and effort) enables sustained interactions (Cooper & Griffin-Shelley, 2002).
Similarly, the Routine Activity Approach (Cohen & Felson, 1979) offers a situational explanation for how OSG opportunities emerge, emphasizing the convergence of a motivated offender, a suitable target, and the absence of capable guardians. The relevance of this theory in the context of OSG has been empirically supported by Wachs et al. (2020) who found that (a) unsupervised Internet use increased the risk of victimization among young people, and (b) parental supervision and monitoring of Internet use served as a protective factor against victimization, and reduced risk thereof. Together, these theoretical perspectives highlight that online environments create conditions in which grooming can thrive, and where individuals may more easily initiate the grooming process, employing tactics to reduce a child’s resistance, secure compliance, and maintain secrecy to prevent disclosure (Craven et al., 2006).
O’Connell (2003) employed a participant observation methodology, which involved posing as a minor in chat rooms for more than 50 hr over a five-year period, to report on the detailed analysis of sexualized conversations/interactions as initiated and engaged in by adults. It led to the development of a typology and identification of six stages: (a) friendship-forming stage, (b) relationship-forming stage, (c) risk assessment stage, (d) exclusivity stage, (e) sexual stage, and (f) the concluding stage in the form of damage limitation and the hit-and-run tactic (where individuals who engaged in OSG presented with no apparent interest in damage limitation or continued contact). The research found that those who engaged in OSG varied in terms of the types and order of stages through which they progressed. Some individuals invested considerable time in relationship-building, while others progressed rapidly to sexual interactions.
Elliott’s (2017) Self-Regulation Model further builds on these behavioral descriptions, integrating self-regulation approaches and control theory to outline two phases: (a) an initial potentiality phase involving strategies such as rapport-building, incentivization, disinhibition, and security management; and (b) a subsequent disclosure phase during which the four potentiality strategies continue to operate and adjust based on received feedback from victims. While this model arguably offers a more dynamic framework for understanding OSG, it has been criticized for its complexity, limiting its application to real-world scenarios and research (Winters et al., 2020). Taken together, these conceptualizations illustrate that the process of grooming is not linear; rather, it is an adaptive process shaped by offender goals, victim responses, and situational factors – a finding very much observed and emphasized by Kloess et al. (2017) and Whittle et al. (2014), based on their analysis of naturally-occurring, real-world data.
The existing literature consistently describes individuals who engage in OSG, and TA-CSA more broadly, as a heterogenous group, using a wide range of strategies from flattery, gifts, and praise, to threats, intimidation, and blackmail (Campbell, 2009; Kloess et al., 2019; Sullivan & Quayle, 2012). Methods of engagement may include introducing sexual topics, making sexual innuendos, showing sexually explicit material, and using manipulation and peer pressure. In a study by Kloess et al. (2019), those who had a history of OSG offenses adopted either an indirect approach, namely building trust before introducing sexual content, or a direct approach, namely initiating sexual interactions from the outset (Kloess et al., 2019). This is further supported by other studies that found that some of those who engaged in OSG behaviors promptly sexualized interactions with victims, while others spent time developing trusting relationships with them through affection and praise, introducing sexualization more gradually (Chiu & Quayle, 2022; Henshaw et al., 2020; Winters & Jeglic, 2017). Overall, these methods of engagement and manipulative strategies serve many functions, including desensitizing children, lowering inhibitions, stimulating sexual curiosity, and normalizing sexual relationships between adults and children (Berson, 2003; Kloess et al., 2017, 2019; O’Connell, 2003; Olson et al., 2007; Singer et al., 1992).
More recently, two systematic reviews synthesized the strategies used by individuals with cybergrooming offense histories (Moosburner et al., 2025), and those specifically adopted as part of the grooming process pre- and post Internet (Ringenberg et al., 2022). Both reviews identified a number of strategies commonly adopted by individuals as part of sexually exploitative and abusive interactions, with Moosburner et al. (2025) organizing them into (a) identity manipulation, (b) rapport-building, (c) risk assessment, (d) enticement, (e) relationship-building, (f) aggression and explicit control, and (g) sexualization and sexual contact. The individuals across the included studies further appeared to be either primarily interested in an intimate relationship with the victim (i.e., intimacy-seeking), or primarily interested in a quick satisfaction of their sexual needs (i.e., sexually preoccupied). While Ringenberg et al. (2022) compared grooming strategies across online and offline contexts, they identified a substantial overlap in the use of trust-building, secrecy, and sexualization, although they noted that certain strategies, such as the use of media for the purpose of deception to facilitate engagement, were more prevalent online.
These reviews offer valuable insights in terms of providing a comprehensive overview of the most commonly used strategies by individuals as part of sexually exploitative and abusive interactions. However, it is important to note that the reviews’ findings are limited by (a) their use of decoy data, and (b) not clearly distinguishing between strategies used in online and offline contexts. More specifically, 10 out of 22 studies included in the review by Moosburner et al. (2025) had used Perverted Justice data (i.e., representing interactions between an adult and a decoy posing as a child). Given that existing research has shown that decoys tend to respond more favorably to sexual solicitation and exhibit greater compliance than real victims (Briggs et al., 2011; Joleby et al., 2021; Seymour-Smith & Kloess, 2021), and that real victims demonstrate resistance to a larger degree than decoys, resulting in the use of more coercive strategies among offenders (Chiang & Grant, 2017, 2019; Schneevogt et al., 2018), findings derived from such data therefore need to be interpreted with caution. It further suggests that those who volunteer to pose as children on behalf of Perverted Justice may be highly motivated and driven to “catch predators,” and thereby engage in language and behavior that is more akin to entrapment.
While using decoy data to explore the use of strategies more generally is of interest from a theoretical perspective, it limits our ability to apply such findings in practice. Decoy data do not capture the intrinsic nuances and unique dynamics of naturally-occurring 1:1 interactions that take place in the real world, and therefore lack the complexity of human behavior at play. In fact, it is the inter-relationship between “offender” and “victim” that often sheds light on the factors that may contribute to the progression or escalation of a particular interaction – an important insight that is key to any risk assessment. Recognizing these limitations, Moosburner et al. (2025) recommend that future research analyze the interaction patterns between offenders and victims. While this was partly addressed by the research undertaken by Kloess et al. (2017, 2019) and Seymour-Smith and Kloess (2021), the former was limited by the absence of victim contributions in its presentation due to confidentiality.
The Present Review
The present article addresses this critical gap in the literature by conducting a mixed-methods systematic literature review focusing exclusively on strategies identified in naturally-occurring, real-world interactions of a sexually exploitative and abusive nature. While existing reviews have examined strategies used in OSG, they have all relied, at least in part, on studies using data derived from decoys, and spanning the online-offline divide. Furthermore, key aspects of grooming tactics, such as individuals’ responses to victim resistance, remain underexplored. By synthesizing both qualitative and quantitative findings, this review aims to provide a more accurate and comprehensive understanding of how such interactions unfold. This is crucial for improving early detection, preventing escalation to TA-CSA and sexual abuse in the physical world, and informing targeted intervention strategies. The systematic literature review presented here therefore seeks to answer the following research question: “What strategies do adults use to identify, approach, and engage children in conversations and interactions of a sexually exploitative and abusive nature online, particularly in relation to OSG, and TA-CSA overall?”
Methods
Protocol and Registration
This mixed-methods systematic literature review followed the recommendations of the Preferred Reporting Items for Systematic Reviews and Meta-Analyses (PRISMA; Moher et al., 2009) to enhance reproducibility and transparency. The protocol was prospectively registered on PROSPERO (registration number CRD42023423596).
Search Strategy
The search strategy followed the Cochrane Qualitative and Implementation Methods Group’s “7S” principles of literature searching (e.g., using preferred sources for searching and supplementary strategies such as reference checking; Harris et al., 2018). A set of preliminary search terms was developed collaboratively by the first and second authors in consultation with the University’s subject librarian (see Supplemental Table A1). A total of six electronic databases were searched to identify studies that met the pre-determined eligibility criteria, namely (a) MEDLINE, (b) ASSIA, (c) CINAHL, (d) Web of Science, (e) EMBASE, and (f) PsychINFO. A gray literature search was undertaken via ProQuest Dissertations and Theses Global, mitigating the effects of publication bias (Paez, 2017). Web searches were conducted on Google Scholar using the previously outlined search strategy. Reference lists of included studies were screened to ensure that no relevant articles were missed. The final search was undertaken on September 16, 2023.
Eligibility Criteria
Studies were eligible for inclusion in the literature review, if (a) samples of individuals with a history of OSG and TA-CSA were aged 18 years or over at the time of the offense; (b) samples of victims were aged under 16 years at the time of the offense; (c) the study reported on analyses using naturally-occurring and/or real-world data; (d) the study’s focus was on strategies used as part of OSG; and (e) the research was published after 2000, as this marks the period when research into the potential misuse of the Internet began to gain academic attention. Studies were not eligible for inclusion in the literature review, if (a) the article was published in a language other than English; and (b) the study employed a non-empirical research design (e.g., of a theoretical, opinion-based, narrative, or review nature).
Study Selection
The present article follows a PRISMA flow diagram for study selection (Page et al., 2021). References and abstracts were exported to Covidence using EndNote20 referencing software. Duplicate articles were removed within Covidence. Titles and abstracts were first screened against the pre-determined eligibility criteria, and those articles that met the criteria underwent full-text screening. To minimize bias and ensure consistency in the application of the eligibility criteria across the two stages (McDonagh et al., 2013), this was carried out independently by the first and second authors. The inter-rater agreement for the combined screening process was 83%, indicating strong agreement between the two authors (McHugh, 2012). Disagreements regarding the eligibility of studies for inclusion in the literature review arose from differences in applying the eligibility criteria. These were resolved through discussion until a consensus was reached. The process of study selection, and reasons for exclusion of any articles, were recorded using the PRISMA diagram for transparency (Moher et al., 2009).
Data Extraction
A data extraction form was created using Microsoft Excel and piloted on four articles. Based on use during the pilot, the form was revised by adding extra columns to ensure that the researchers collected complete data from the articles. This piloting process aligns with PRISMA guidelines (Moher et al., 2009). The first and second authors independently extracted data from each article, and combined it thereafter for the purpose of the present review. Supplemental Table A2 provides an overview of the study characteristics for each of the included articles. The authors extracted key findings relating to OSG strategies or tactics from included articles into the data extraction form. Two articles only partially met the eligibility criteria: (a) K. Thomas et al. (2023) used data pertaining to individuals who were below the age of 18 years at the time the offense took place – as such, only data pertaining to adult individuals were extracted and used; (b) Chiang (2018) encompassed multiple investigations within a single publication, of which only two were relevant – as such, only data from these two were extracted and used, with the remainder excluded from further analysis.
Quality Appraisal
The Critical Appraisal Skills Programme (CASP) qualitative checklist (2018) was used to appraise the articles that had adopted a qualitative design, and the National Institute of Health (NIH) Quality Assessment Tool for Observational Cohort and Cross-Sectional Studies (2014) was used to appraise the articles that had adopted a quantitative design. The first and second authors completed this process independently for all included articles, and assigned an overall quality rating of “good,” “moderate,” or “poor.” Key criteria that formed part of the quality appraisal centered around (a) research aims and questions being clearly stated, (b) choice of research design and recruitment strategy being appropriate and clearly outlined, (c) data being relevant, (d) ethical issues being considered, (e) data analysis being sufficiently rigorous, and (f) findings being clearly described and communicated. The inter-rater agreement between the two authors was 85% (McHugh, 2012), with the inter-rater reliability score (Cohen’s kappa = .70; Bland & Altman, 1999, based on Landis & Koch, 1977) indicating a good to substantial level of agreement. Disagreements arose from individual differences in how the researchers interpreted the appraisal tools, and were resolved through discussion until consensus was reached. No article was excluded on the basis of its quality rating. Supplemental Tables A3 and A4 provide an overview of the quality appraisal and ratings for each of the included articles.
Data Synthesis
A thematic synthesis approach was used and adapted to synthesize both qualitative and quantitative findings from the included articles. This approach followed the recommendations by J. Thomas and Harden (2008) for qualitative data synthesis, and incorporated guidance from the Joanna Briggs Institute (Stern et al., 2020) to obtain seamless integration of quantitative data. The included articles were imported into NVivo, a qualitative data analysis software program that facilitates qualitative data analysis. The synthesis followed a three-step process. The first step involved a bottom-up approach that comprised line-by-line coding of findings to identify any data, both narrative and quote, relating to strategies and tactics of OSG. For quantitative articles, data were manually converted into narrative descriptions of statistical analysis and coded in the same manner. The second step entailed the development of descriptive theme labels developed on the basis of the extracted data. These themes moved beyond the description of the data in the original articles. The third step involved an iterative process of review and refinement. The first and second authors repeatedly reviewed the themes and the extracted data they represented (Noyes & Lewin, 2011).
Results
Characteristics and Quality of Included Articles
Despite utilizing the same sample/dataset, Chiang (2018) and Chiang and Grant (2019) were considered separately due to variations in research questions, analyses, and outcomes. The same approach was applied to Kloess et al. (2017) and Kloess et al. (2019). Of the 12 articles included in the present review (see Supplemental Figure A1), nine studies employed a qualitative methodology, two employed a quantitative methodology, and one employed a mixed-methods design. Of the latter, only the qualitative data were deemed to be relevant, and met the inclusion criteria, and were therefore assessed using the CASP qualitative checklist (2018).
The nature of the datasets varied, namely transcripts of chat logs between individuals with a history of OSG/TA-CSA offenses and underage children (n = 6), semi-structured interviews with victims or individuals with a history of OSG/TA-CSA offenses (n = 3), cross-sectional surveys completed by victims (n = 2), and police reports of OSG/TA-CSA cases (n = 1). The majority of studies were conducted in the UK (n = 8), alongside Spain (n = 2), Sweden (n = 1), and Australia (n = 1). The timeframe within which the studies were completed was between 2008 and 2023. Together, the studies included a total of 382 individuals with a history of OSG/TA-CSA offenses, and a total of 2,393 victims. The methodological quality of the 12 articles varied – six were rated as being of “good” quality, five were rated as being of “moderate” quality, and one was rated as being of “poor” quality (see Supplemental Material for an overview of the quality assessment ratings).
Synthesis of Results
The following findings provide an overview of and outline the range of strategies that individuals with a history of OSG/TA-CSA offenses employed to identify, approach, and engage children in sexually exploitative and abusive interactions online. 2 While the identified themes are presented according to escalating severity, based on the perceived forcefulness of the strategies therein, this is not intended to represent a linear process (see Figure 1 for an overview of the identified themes, alongside their subthemes).
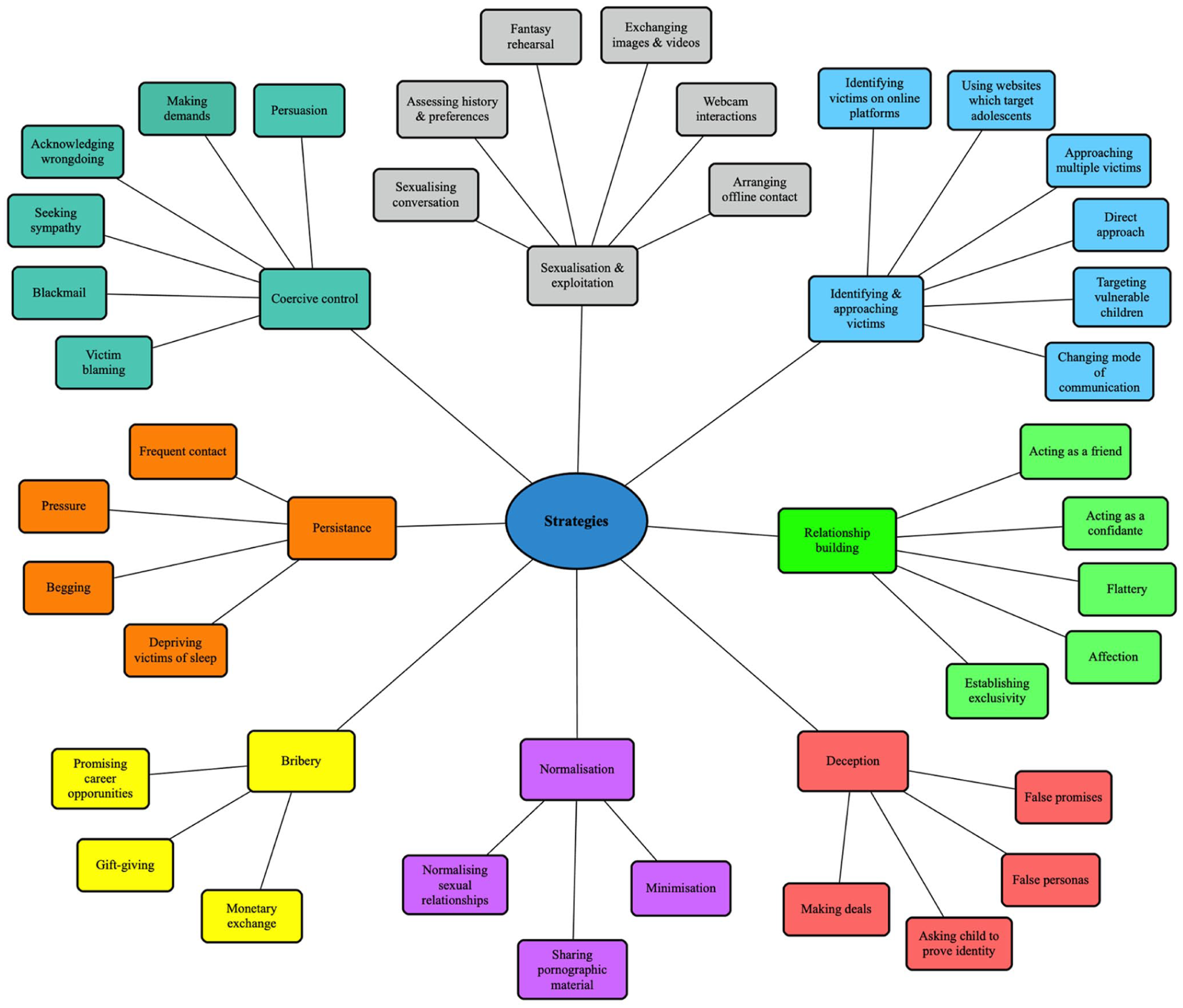
Thematic map of key strategies identified across included articles.
Theme 1: Identifying and Approaching Possible Victims
Identifying Possible Victims on Online Platforms
Across three articles, individuals used various websites to identify potential victims (De Santisteban et al., 2018; Kloess et al., 2017, 2019). Initial contact was often made through public chat rooms, social networking sites, or dating sites. Some individuals described intentionally utilizing websites designed for and popular among children and young people, such as public chat rooms of a particular topic (area), to identify and approach potential victims (Kloess et al., 2019). Others reported a preference for targeting victims on websites which offered a video chat function due to the opportunities this presents for facilitating sexual interactions (De Santisteban et al., 2018; Kloess et al., 2019). While some individuals reported selecting victims based on the age displayed on their profile (De Santisteban et al., 2018), others were thought to select victims based on their profile pictures (Kloess et al., 2019).
Approaching Multiple Victims
Three articles described individuals initiating contact with multiple victims simultaneously (De Santisteban et al., 2018; Kloess et al., 2019; Shannon, 2008) or sequentially (Kloess et al., 2019). Some individuals with a history of OSG offenses contacted hundreds of potential victims (De Santisteban et al., 2018; Kloess et al., 2019), attempting to increase their chances of successfully identifying, approaching, and engaging with a victim: “I had prepared phrases, I opened 100 windows and cut and paste.” (De Santisteban et al., 2018, p. 210). This multiplicity is further reflected in two additional articles, namely Chiang (2018) and Chiang and Grant (2019), who reported that one individual befriended a large number of victims before coercing them to engage in sexualized interactions online.
Direct Approach
One article noted that having made initial contact, some individuals swiftly transitioned from basic introductions to attempting to engage the child in sexual acts/activities (Kloess et al., 2017, 2019). In one instance, within just 9 minutes of the initial introduction, the individual asked whether the victim wanted to see their genitals, and made several requests for the victim to expose themselves via webcam (Kloess et al., 2017).
Targeting Vulnerable Children
It was evident across five of the included articles that some individuals deliberately selected vulnerable children as victims. Once engaged in conversation, individuals displayed an avid interest in the child’s environment, and actively sought out vulnerabilities within their microsystem, such as poverty, abuse, and bullying (De Santisteban et al., 2018; Gámez-Guadix et al., 2021; Shannon, 2008). The individual would subsequently offer to meet these through financial and/or emotional support, and thereby attempt to maintain engagement. This strategy has been suggested to help an individual establish their role in the child’s life as a confidante by building trust, increasing contact, and using learnt knowledge to tailor their methods of engagement (Chiang, 2018; De Santisteban et al., 2018; Whittle et al., 2015). Gámez-Guadix et al. (2021) reported that individuals demonstrated an interest in a child’s environment in nearly 20% of cases in their sample.
Changing Mode of Communication
Four of the included articles described that, after initiating contact and engaging a victim in conversation, individuals frequently sought to migrate the interaction to a different messaging platform. Individuals typically fulfilled this desire by requesting the child’s contact information, including their telephone number (De Santisteban et al., 2018; Kloess et al., 2019; Shannon, 2008), instant messaging account details (Kloess et al., 2017, 2019; Shannon, 2008), and, less commonly, their email address (Kloess et al., 2017). Multiple articles noted that individuals may do so to further establish their role in the victim’s lives: “This (phone contact) can also be seen as a form of escalation, as the offender becomes a part of the victim’s personal life offline.” (Kloess et al., 2019, p. 85).
Theme 2: Relationship-Building
Acting as a Friend
Across six articles (Chiang, 2018; Chiang & Grant, 2019; De Santisteban et al., 2018; Kloess et al., 2019; Shannon, 2008; Whittle et al., 2015), many individuals with a history of OSG and TA-CSA offenses portrayed themselves as a friend to victims. More specifically, they presented as curious about the child’s interests, and asked about and shared personal information relating to hobbies, relationships, and daily life (Shannon, 2008). Some individuals assisted victims with their homework (De Santisteban et al., 2018), seemingly hoping to enhance their connection with the child to ensure continued engagement.
Acting as a Confidante
Four of the included articles described how individuals often presented themselves as a trustworthy confidante as a method of building a deeper, emotional connection with the victim, and sustaining engagement (De Santisteban et al., 2018; Kloess et al., 2019; Powell et al., 2021; Whittle et al., 2015). Some individuals used empathy to build trust (Powell et al., 2021), demonstrated through actions such as engaging in prolonged telephone conversations, providing a space for children to feel listened to and validated, and offering advice (De Santisteban et al., 2018; Kloess et al., 2019). One victim expressed this as follows: “I felt like I could tell him anything, really trusted him.” (Whittle et al., 2015, p. 17).
Flattery
Across 10 articles, individuals with a history of OSG and TA-CSA offenses frequently complimented and flattered their victims (Chiang, 2018; Chiang & Grant, 2019; Kloess et al., 2017, 2019; Powell et al., 2021; Seymour-Smith & Kloess, 2021; Shannon, 2008; Whittle et al., 2015). Compliments encompassed positive comments about victims’ appearance or personality, and statements about what they “deserved,” such as being cared for, admired, or treated in a uniquely special way. This strategy created a sense of an intimate and special bond, allowing the individual to establish themselves as a kind and loving figure in victims’ lives: “It was mainly like everything a girl would like to hear, like you’re beautiful, um you deserve good things and I can do all that for you.” (Whittle et al., 2015, p. 14). Flattery also often directly preceded a sexual request (Kloess et al., 2019; Powell et al., 2021; Seymour-Smith & Kloess, 2021). This strategic placement of flattery may mitigate the intensity of the subsequent request, priming the victim to gain compliance (Seymour-Smith & Kloess, 2021).
Affection
Expressions of love, care, and affection for the victim were identified as a recurring tactic across eight articles (De Santisteban et al., 2018; Gámez-Guadix et al., 2018; Kloess et al., 2017, 2019; Powell et al., 2021; Seymour-Smith & Kloess, 2021; K. Thomas et al., 2023; Whittle et al., 2015). These were commonly used in conjunction with flattery, and were often directly followed by sexual requests (Kloess et al., 2017; Seymour-Smith & Kloess, 2021). Again, this deliberate placement of affection appears to serve the purpose of creating an emotional attachment with the victim in order to initiate and/or maintain their engagement (Kloess et al., 2017).
Establishing Exclusivity
In four of the included articles, individuals were seen to establish an exclusive relationship with the victim in order to maintain their engagement (De Santisteban et al., 2018; Kloess et al., 2017, 2019; Whittle et al., 2015). This led to some victims referring to the individual as their boyfriend (Whittle et al., 2015), and conversations featuring plans for the future, such as having children (De Santisteban et al., 2018) and moving in together (Kloess et al., 2017), which were often followed by sexualized interactions: “When we [decided] that we were going to be engaged, we would send [each other] sexual photos.” (De Santisteban et al., 2018, p. 210).
Theme 3: Deception
False Personas
Individuals with a history of OSG and TA-CSA offenses were observed to make use of false online personas in 10 articles (Chiang, 2018; Chiang & Grant, 2019; De Santisteban et al., 2018; Gámez-Guadix et al., 2018, 2021; Kloess et al., 2019; Seymour-Smith & Kloess, 2021; Shannon, 2008; K. Thomas et al., 2023; Whittle et al., 2015). In order to maintain victims’ engagement, and ensure continuous interactions, individuals often altered aspects of their online identity/persona: “I don’t think there’s one thing that he said back then that I know now, that was actually the truth.” (Whittle et al., 2015, p. 17). In the study by Gámez-Guadix et al. (2018), the use of deception was most commonly related to an individual presenting as (a) younger and closer to the victim’s age, (b) sharing similar hobbies/interests, and (c) pretending to be someone else (for the purpose of persuasion or blackmail).
More specifically, while some individuals portrayed themselves to be around the same age as their victims (Kloess et al., 2019; Seymour-Smith & Kloess, 2021; K. Thomas et al., 2023), others slightly reduced their age while still presenting themselves as much older than the child (De Santisteban et al., 2018; Shannon, 2008). In some cases, individuals used other children’s identities/personas in order to present as more realistic and relatable: “The photos that I sent were from another webpage of a boy.” (De Santisteban et al., 2018, p. 209). Furthermore, individuals were also reported to (a) misrepresent their gender, particularly when interacting with male victims (Seymour-Smith & Kloess, 2021; K. Thomas et al., 2023); and (b) fabricate their profession/career in line with victims’ interests, again to pique their curiosity and maintain engagement (De Santisteban et al., 2018; Shannon, 2008). Three articles specifically discussed how individuals made use of this strategy and adapted their personas/identities to match their victim’s preferences in terms of age, gender, and sexual orientation (Chiang, 2018; Chiang & Grant, 2019; De Santisteban et al., 2018). In fact, Chiang (2018) highlights the high-level manipulation adopted by individuals using identity performance, and how the ultimate goal of this strategy is victim compliance: These adopted personas enabled him to play with various aspects of identity such as gender when engaging with victims, and he would cycle through them throughout interactions in an apparent attempt to find those most likely to achieve victim compliance in various forms (e.g., he might switch to a bisexual female persona after an unsuccessful attempt to engage female victims (. . .) using a straight male persona). (Chiang, 2018, p. 115)
False Promises
In three articles, individuals were further reported to make “false” promises to victims as a way of maintaining ongoing engagement (Powell et al., 2021; Seymour-Smith & Kloess, 2021; Whittle et al., 2015), for example, of a typical romantic relationship: “We could date as boyfriend and girlfriend.” (Powell et al., 2021), swiftly followed by requests for secrecy. “I will. . ., if you. . .” formulations were observed to be used throughout interactions by individuals in order to elicit compliance or overcome resistance to sexualized requests (Seymour-Smith & Kloess, 2021). These “deals” were typically of a sexual nature, and framed as conditional exchanges, implying a benefit for the victim that is contingent on compliance. However, once victims fulfilled their part of the “agreement,” individuals were often seen not to deliver on their promises.
Asking Child to Prove Their Identity
Only one article reported that some individuals claimed not to believe the child’s identity, and therefore requested proof thereof. This was suggested to serve the purpose of “luring” the victim to initiate engagement via webcam (Kloess et al., 2017).
Theme 4: Normalization
Minimization
Individuals in four articles were observed to diminish the significance of sexualized requests by adopting playful and light-hearted language (Chiang, 2018; Chiang & Grant, 2019; Kloess et al., 2017; K. Thomas et al., 2023). For example, some individuals made use of adolescent-like expressions, such as “lol” and “hehe,” to increase the likelihood of compliance (Chiang, 2018), while minimizing the risk of disclosure (Kloess et al., 2017): “lol its only girly fun” (Chiang, 2018, p. 128). In order to overcome resistance in victims, some individuals used similar language to present their requests as merely jokes, and downplay their sexual motivation (Chiang, 2018; Chiang & Grant, 2019; K. Thomas et al., 2023).
Sharing Pornographic Material
Across three articles (Kloess et al., 2017, 2019; Powell et al., 2021), individuals were found to share pornographic material with victims, which appeared to serve the purpose of desensitizing them to explicit content, and familiarizing them with it. This ultimately functioned to increase victims’ compliance with subsequent sexualized requests (Kloess et al., 2017; Powell et al., 2021).
Normalizing Sexual Relationships
It was evident across three articles that some individuals attempted to normalize sexual relationships between adults and children in order to reduce victims’ inhibitions and minimize risk of disclosure (Kloess et al., 2017, 2019; Powell et al., 2021). This involved individuals sharing details of their past sexual experiences with other victims, including emphasizing the child’s level of enjoyment and their own level of experience (Kloess et al., 2017; Powell et al., 2021), and thereby presenting themselves as an appropriate sexual partner: “ive taken a few virginities before. . . .” (Kloess et al., 2019, p. 83). This strategy often preceded sexual interactions, and ultimately functioned to increase victims’ compliance (Kloess et al., 2019).
Theme 5: Bribery
Promising Career Opportunities
In two articles, individuals were reported to bribe victims into engaging in sexual acts/activities by promising them job opportunities. In Shannon’s (2008) study, individuals lured victims to meetings in the physical world under the guise of modeling work, and in De Santisteban et al.’s (2018) study, individuals persuaded victims to send explicit pictures or undress via webcam under the pretense of securing acting or modeling work. Compared with other strategies, such as deception and sexualization, this strategy was reported to be used less frequently (Gámez-Guadix et al., 2021).
Gift-Giving
Four articles reported the use of material gifts (De Santisteban et al., 2018; Gámez-Guadix et al., 2021; Kloess et al., 2019). This strategy was more prevalent in cases involving female victims (Gámez-Guadix et al., 2021). More specifically, individuals provided victims with a variety of gifts, including concert tickets, phones, clothes, and sex toys, with the intention of creating a sense of obligation within the victim to reciprocate in some way, and thereby ultimately achieving compliance and engagement (De Santisteban et al., 2018; Kloess et al., 2019).
Monetary Exchange
The most prevalent form of bribery described across eight articles was monetary exchange (Chiang, 2018; Chiang & Grant, 2019; De Santisteban et al., 2018; Gámez-Guadix et al., 2018; Kloess et al., 2019; Powell et al., 2021; Shannon, 2008; Whittle et al., 2015). Sometimes used in conjunction with gift-giving (Kloess et al., 2019), and in order to achieve victims’ compliance, individuals were seen to incite them to engage in specified sexual acts/activities in exchange for financial payment: “£20 to let me stare at ur tits for 5 mins.” (Chiang, 2018, p. 99). More specifically, Gámez-Guadix et al. (2018) found that 45% of victims in their sample had been the target of bribery, and that this was associated with higher rates of experiencing sexual solicitation, and sexually exploitative and abusive interactions respectively.
Theme 6: Persistence
Frequency and Intensity of Contact
The nature and level of contact between individuals and their victims were described in six articles (Chiang, 2018; De Santisteban et al., 2018; Kloess et al., 2019; Shannon, 2008; K. Thomas et al., 2023; Whittle et al., 2015), with some contact as frequent as daily and of an intense nature (De Santisteban et al., 2018; Kloess et al., 2019): “I couldn’t like hardly ever have any time to myself.” (Whittle et al., 2015, p. 15). This quote illustrates that the purpose of such frequent and intense contact appeared to be to isolate the victim, and thereby create dependence on the individual and further establish their place and presence in the victim’s life. In the K. Thomas et al. (2023) study, some individuals were reported to engage victims in conversations into the early hours of the morning, suggesting that this strategic use of late-night conversations was aimed at depriving victims of sleep, thereby reducing their cognitive capacity, and leaving them more vulnerable to persistent requests.
Pressure
The use of pressure in order to overcome victims’ resistance was observed across five articles (Kloess et al., 2017, 2019; Powell et al., 2021; Seymour-Smith & Kloess, 2021; K. Thomas et al., 2023). Following resistance to their initial requests, individuals persistently attempted to elicit the desired response from the victim by repeating them, often becoming increasingly direct and aggressive, and thereby increasing pressure on the victim to cooperate: “You just have to tell me. Are we having sex when we meet? Yes or no.” (Powell et al., 2021, p. 5).
Begging
Individuals in two articles were reported to resort to begging in response to victims’ non-compliance (Kloess et al., 2017, 2019) through presenting as desperate and in need, and using repeated pleas to overcome victims’ resistance and achieve engagement in sexualized interactions: “Offenders could be seen to be persistent by repeating questions and statements, as well as using question marks (‘??’), to elicit responses by victims.” (Kloess et al., 2017, p. 574).
Theme 7: Coercive Control
Persuasion
The use of explicit persuasion strategies in order to overcome victims’ resistance and achieve the goal of continued engagement in sexual interactions was observed across four articles (Chiang & Grant, 2019; Seymour-Smith & Kloess, 2021; Shannon, 2008; K. Thomas et al., 2023): “Overt persuasion accounts for the more obvious instances of where he attempts to push victims into some sort of compliance” (Chiang & Grant, 2019, p. 684); “O: I know u can but u don’t want; V: I don’t want my friend here; O: why? You don’t have to do nothing dirty; V: I know; O: please; V: no; O: why you scared; [. . .]” (Seymour-Smith & Kloess, 2021, p. 1000). Such efforts commonly involved the strategic use of affection, flattery, minimization of the sexual nature of requests, and assurances of exclusivity – all to persuade victims to comply with sexual requests. While these tactics often initially served to build emotional connection, they were later repurposed as persuasive tools to overcome resistance and achieve compliance.
Making Demands
In the context of victims presenting as non-compliant, seven articles described how individuals’ sexual requests escalated into demands (Chiang, 2018; Chiang & Grant, 2019; Kloess et al., 2017, 2019; Powell et al., 2021; Seymour-Smith & Kloess, 2021; K. Thomas et al., 2023), and became increasingly aggressive, as they attempted to coerce victims into engaging in specific sexual acts/activities (Powell et al., 2021).
Acknowledging Wrongdoing
Across six articles, individuals were reported to acknowledge the age differences between themselves and victims (Chiang, 2018; Chiang & Grant, 2019; Kloess et al., 2017, 2019; Powell et al., 2021; Whittle et al., 2015). However, through repeatedly emphasizing the illegality and societal disapproval around their contact/interaction/relationship, individuals created fear in victims that disclosing it would be negatively perceived by others, and ultimately manipulated them into secrecy. In fact, some individuals initiated contact with victims, and sexually exploitative and abusive interactions respectively, by conceding that their demands were improper. This, in turn, induced feelings of guilt in victims, and worked to achieve their compliance to engage in sexual acts/activities, while simultaneously minimizing the risk of disclosure (Powell et al., 2021).
Seeking Sympathy
Five articles reported on findings that individuals sought sympathy when met with resistance to their directive requests (Chiang, 2018; Chiang & Grant, 2019; Kloess et al., 2017, 2019; Whittle et al., 2015). The more subtle version of this approach involved conveying disappointment and sadness at victims’ refusal to engage (Kloess et al., 2017, 2019). In more extreme cases, individuals exploited the emotional connection they had established with victims in order to pursue meeting their needs: “‘If you loved me you wouldn’t say that, you wouldn’t do that’ I think I said. . ., and she bent over backwards to make sure she was there.” (Whittle et al., 2015, p. 19).
Blackmail
The use of blackmail by individuals to incite victims into participating in sexual acts/activities was reported across 10 articles (Chiang, 2018; Chiang & Grant, 2019; De Santisteban et al., 2018; Gámez-Guadix et al., 2021; Kloess et al., 2017, 2019; Powell et al., 2021; Seymour-Smith & Kloess, 2021; Shannon, 2008; K. Thomas et al., 2023). In addition, persuasion and bribery were used to facilitate the exchange of images and/or videos, which were subsequently used to coerce victims into continued compliance. When victims resisted escalating demands, threats to expose them and their explicit material became commonplace: “he’d threaten me – ‘If you don’t do this, the footage that I do have, I’m going to post all over Facebook and everything and I’m going to show it to your friends’” (K. Thomas et al., 2023, p. 5). While such threats were the least commonly reported form of blackmail in the article by Gàmez-Guadix et al. (2021), others (Chiang, 2018; Chiang & Grant, 2019; Kloess et al., 2017, 2019; Powell et al., 2021) reported that individuals exploited victims’ emotional attachment to them by resorting to threats of ending the contact/interaction/relationship: “get ur cam workin. . . or im goin.” (Chiang & Grant, 2019, p. 684).
Victim Blaming
Three articles described how individuals skillfully shifted responsibility and blame onto victims (Chiang & Grant, 2019, Kloess et al., 2017; K. Thomas et al., 2023). By periodically reminding victims of their apparent wrongdoing, and emphasizing potential consequences for them, they elicited feelings of fear and guilt in them: “I don’t want you to get caught. . .that would be a huge problem.” (Kloess et al., 2017, p. 29). This strategy served the purpose of reducing the risk of victims disclosing, and ultimately being detected by authorities.
Theme 8: Sexualization and Exploitation
Sexualizing Conversations
Seven articles described how individuals sexualized conversations in order to incite victims to engage in, and initiate, sexual acts/activities (Chiang, 2018; Gámez-Guadix et al., 2021; Kloess et al., 2017, 2019; Seymour-Smith & Kloess, 2021; Powell et al., 2021; Shannon, 2008). According to Gámez-Guadix et al. (2021), sexualizing conversations and interactions is a central feature of OSG. However, the manner in which this was done varied across articles. Some individuals used a direct and highly explicit approach (Chiang, 2018; Kloess et al., 2019; Powell et al., 2021), while others opted for a more gradual and suggestive approach (Gámez-Guadix et al., 2021; Kloess et al., 2017, 2019; Seymour-Smith & Kloess, 2021; Shannon, 2008). For example: “Offenders used both suggestive and directive styles of interaction (. . .) to initiate online sexual activity” (Kloess et al., 2017, p. 570). Nevertheless, there was consensus across the articles with regard to the lack and absence of “preparation” engaged in by individuals: “One of the most striking features of these interactions generally is the speed at which sexual topics are introduced by the offender” (Chiang, 2018, p. 133).
Exploration of History and Preferences
Six articles reported that individuals enquired about victims’ sexual experiences, including past sexual encounters, their sexual orientation, and preferences, as well as genitalia (Chiang, 2018; Chiang & Grant, 2019; Gámez-Guadix et al., 2021; Kloess et al., 2017, 2019; Powell et al., 2021). It is suggested that this not only serves the purpose of sexualizing the conversation/interaction, but also determining the likelihood of victims engaging in sexual acts/activities, and whether they meet individuals’ (sexual) interests and likes (Chiang, 2018).
Fantasy Rehearsal
Two articles reported on individuals’ approaches to sexualizing conversations and interactions by rehearsing hypothetical scenarios with victims in the physical world (Kloess et al., 2017, 2019). While this may have started off in a seemingly affectionate and light-hearted tone, it often escalated into more aggressive statements, driven by individuals’ desire to fulfill their sexual needs: “i wud push as much of my dick in ur mouth as possible.” (Kloess et al., 2017, p. 24).
Exchanging Sexual Images and Videos
The exchange of and request for explicit material was a strategy commonly used by individuals as part of their interactions with victims. It was reported across eight articles (Chiang, 2018; Chiang & Grant, 2019; De Santisteban et al., 2018; Kloess et al., 2017, 2019; Seymour-Smith & Kloess, 2021; K. Thomas et al., 2023; Whittle et al., 2015). Most victims were pressured or coerced into sending sexual images or videos by individuals, with the latter sometimes initiating the exchange by sending an explicit photograph in order to incite them to reciprocate.
Webcam Interactions
The use of webcams to facilitate sexually exploitative and abusive interactions was described across eight articles. More specifically, individuals were reported to direct victims to undress and expose certain body parts, including genitalia, via webcam (Chiang, 2018; Chiang & Grant, 2019; De Santisteban et al., 2018; Seymour-Smith & Kloess, 2021), and perform masturbatory sexual acts (Kloess et al., 2017; Whittle et al., 2015). In an attempt to incite victims, individuals also exposed themselves and engaged in masturbation (Kloess et al., 2019; Shannon, 2008; Whittle et al., 2015).
Arranging Offline Contact
Six articles described how individuals initiated discussions and/or arrangements surrounding a meeting in the physical world. While in some instances this clearly served the purpose of engaging in sexual acts/activities in the physical world (Chiang, 2018; Powell et al., 2021; Shannon, 2008; Whittle et al., 2015), it appeared to be more of a strategy to maintain victims’ online engagement in others, without any intention of transitioning to a physical meeting (Kloess et al., 2017, 2019).
Discussion
This systematic literature review aimed to provide a comprehensive overview of the strategies used to identify, approach, and engage children and young people in OSG, and TA-CSA respectively, including both quantitative and qualitative studies using naturally-occurring, real-world data only. 12 articles met the inclusion criteria, and were included in the final set for review – nine adopted a qualitative design, two adopted a quantitative design, and one adopted a mixed-methods design. A thematic synthesis approach was used to integrate the studies’ findings of the qualitative and quantitative data (Stern et al., 2020; J. Thomas & Harden, 2008).
Summary of Findings
The findings highlight that individuals with a history of OSG and/or TA-CSA offenses use a number of different strategies to identify, approach, and engage children in sexually exploitative and abusive interactions online. Across the included articles, identified strategies appeared to serve multiple functions, namely to (a) overcome victim resistance, (b) secure victim compliance, and (c) maintain victim engagement. However, it also became apparent that strategies varied across individuals. For example, some individuals used a direct approach, making sexual requests shortly after initial contact, while others spent a considerable amount of time developing a relationship before sexualizing the conversation/interaction. This is in line with previous research that reports that while strategies vary, they do appear to fall into two categories, namely taking a more direct versus indirect approach to approaching and engaging victims (Chiu & Quayle, 2022; Henshaw et al., 2020; Kloess et al., 2017, 2019; Winters & Jeglic, 2017).
It is possible that the differing use of strategies, or type of approach, may be explained by offender motivation (Briggs et al., 2011; Gottschalk, 2011; Winters et al., 2017). An exploratory study of transcripts of chat logs reported significant differences in the strategies used by individuals who were motivated to arrange a meeting in the physical world, compared to those who were merely interested in pursuing sexualized conversations/interactions online (Taylor, 2017). However, our findings also suggest that individuals with a history of OSG and/or TA-CSA offenses adapt or even tailor their strategies according to the responses of individual victims. Again, this is in line with previous research that suggests that such adaptations serve to maximize chances of initiating and maintaining conversations/interactions/relationships with victims, and achieving their compliance and engagement (De Santisteban et al., 2018; Lorenzo-Dus & Izura, 2017).
Such adaptability was particularly apparent when individuals were met with resistance by victims following the introduction of sexual demands or requests. Here, individuals used various strategies, such as minimization, seeking sympathy, pressure, and blackmail, to overcome this while avoiding the risk of disclosure and detection. According to Control Theory (Carver & Scheier, 1982), behavior is continuously regulated in order to achieve a desired outcome, which further supports Elliott’s (2017) Self-Regulation Model, and suggests that strategies identified as part of the potentiality stage are unlikely to be universal. It further highlights that “grooming” strategies are not typically employed in a linear sequence, contrary to O’Connell’s (2003) typology of cybersexploitation, but rather in a more dynamic and multi-faceted way to prevent disclosure, evade detection, minimize resistance, and achieve compliance. An exploration of some of the nuances that underpinned the sexually exploitative and abusive interactions across the included articles was not possible due to the often limited presentation of contextual information. For example, as described in the study by Kloess et al. (2017), the question arises as to what factors may contribute to a conversation/interaction/relationship escalating, whereby an individual who engages with hundreds of children and young people online over a significant period of time “suddenly” progresses and commits a sexual offense against a child in the physical world. Current knowledge and understanding of this is still limited, and it is not clear what may facilitate progression and escalation in terms of the nature of offending behaviors engaged in online, as well as crossing over into the physical world.
These findings are echoed by Joleby et al. (2021), who employed an explorative mixed-methods approach using naturally-occurring data to examine strategies used by adults to engage children in online sexual activity. Although their study did not meet the inclusion criteria of the present review, due to the age range of participants, their findings are nevertheless relevant – the authors identified the frequent use of coercive strategies, such as bribes and threats, alongside manipulative tactics, including flattery, expressions of love, and acting as a friend. Of particular note was the use of alternating pressure and affection to gain compliance, a pattern similarly observed in our synthesis. The overlap with our findings further reinforces the idea that strategies used by individuals with an interest in or motivation to engage children and young people in sexually exploitative and abusive interactions are both purposeful and adaptive, tailored to maximize control and minimize victim resistance.
In terms of how such individuals identify and approach potential victims, some do so on the basis of profile pictures, and information displayed thereon, in particular age. Others deliberately use websites geared toward children and young people (Malesky, 2007; Wurtele & Kenny, 2016). The strategy of targeting vulnerable victims provides important insights into individuals’ modus operandi in terms of how they seek to exploit their vulnerabilities. According to Maslow’s Hierarchy of Needs (1943), human beings strive to fulfill their most basic needs – in the present context, it could be argued that individuals who engage in OSG and TA-CSA offenses strive to fulfill their need for emotional connectedness. By targeting vulnerable children and young people online, who may have experienced or are experiencing difficult life circumstances and events (e.g., abuse, broken home, bullying), they further exploit their basic needs for belonging, connection, love and safety by acting as a friend or confidante, giving them gifts, offering them money, and/or promising them job opportunities, with the aim of creating a certain dependence on them.
Overall, our findings demonstrate the purposeful nature of efforts by individuals in terms of identifying, approaching, and engaging children and young people in inappropriate conversations and sexually exploitative and abusive interactions online, and their use of a wide range of manipulative strategies as part thereof. While many of the identified strategies have previously been reported in the literature (Moosburner et al., 2025; Ringenberg et al., 2022), and our review therefore lends additional support to existing findings, it further presents a more in-depth and nuanced perspective of the nature of sexually exploitative and abusive interactions by considering the unique dynamics inherent therein. More specifically, the findings illustrate how quickly such interactions can progress and escalate, and how direct and explicit of an approach some individuals adopt. The question therefore arises as to whether the types of strategies used as part of OSG, and TA-CSA more broadly, are better considered along a spectrum of “mere” manipulative strategies human beings draw on when engaging in a process through which they aim to achieve a particular goal. The nature of the particular goal may vary, but the process in order to achieve it will undoubtedly share similarities across different contexts, and reflect common human behavior. This would challenge the use of typologies which does not allow for a consideration of context or unique dynamics often present as part of sexually exploitative and abuse interactions.
In order to derive such more nuanced understanding, researchers would require access to more complete conversational data and contextual information. Most studies were limited in terms of their data merely capturing a snapshot of conversations/interactions – transitioning from public spaces to more private ones is a common strategy, especially once initial contact has been established. As such, data are often not available for the earlier stages of the conversation/interaction, or where the use of certain platforms means that data are not retained/accessible (e.g., Snapchat, a picture messaging app popular among children and young people, where an image “disappears” after the recipient views it). Furthermore, according to UK police reports, OSG is increasingly becoming a cross-platform issue, with “sexual communication with a child” offenses (Section 15/15(A); Sexual Offences Act, 2003) having been recorded as taking place across 70 different apps, gaming sites, and websites between 2021 and 2022 alone, with Snapchat identified as the most commonly used platform (NSPCC, 2022a).
Strengths, Limitations, and Directions for Future Research
The mixed-methods design of the present systematic literature review allowed for the triangulation and synthesis of findings that represent strategies used as part of OSG and TA-CSA offenses, and were reported across studies, irrespective of their choice of methodological approach (Gibson, 2017). Throughout, a rigorous process of article screening and review was employed, with the first and second authors completing the processes around study selection, data extraction, quality appraisal, and thematic synthesis independently. The inclusion of gray literature mitigated against publication bias (Paez, 2017). It is worth noting that the included articles were assessed to be of variable study quality (i.e., 50% = good, 42% = moderate, 8% = poor), with one rated as “poor” for failing to adequately address ethical issues, undertaking a rigorous data analysis process, and providing a clear and conclusive statement of findings.
Although many instances of OSG never lead to conviction (Greene-Colozzi et al., 2021), all except three articles (Gámez-Guadix et al., 2018, 2021; K. Thomas et al., 2023) analyzed data from individuals convicted of TA-CSA offenses. As such, our findings exclude insights from individuals who have not been apprehended by authorities, and whose modus operandi may differ from that of apprehended individuals. They are further limited by the small sample sizes across the included articles – 50% used a sample size of n = 5 or less, and the one with the largest sample size (n = 315) received a quality rating of “poor.” In addition, studies were limited in terms of (a) samples primarily involving males who engaged in OSG and/or TA-CSA offenses; (b) samples primarily involving female victims; and (c) datasets primarily involving transcripts of chat logs. While such limitations are somewhat unavoidable due to the significant challenges in getting access to data of this nature, they are important to bear in mind when considering the findings of the present review, and designing future research.
More specifically, future research would benefit from addressing any of these limitations, including making use of larger samples of males and females with offending histories, and those of male and female victims, as well as more varied datasets overall. In addition, in line with suggestions in the existing literature (Moosburner et al., 2025; Ringenberg et al., 2022), future research would also benefit from undertaking further in-depth comparisons between findings derived from naturally-occurring data and those derived from decoy data in order to shed light on their commonalities and differences, in terms of modus operandi, offender motivation, and offending process, as well as the applicability of the latter to real-world scenarios.
Diversity Statement
A total of 2,393 victims and 382 individuals with a history of OSG and/or TA-CSA offenses participated in the 12 articles included in this review. Among the victim participants, 59.52% were female and 40.48% were male. Of the eight articles that reported the gender of participants with a history of offending, 98.07% were male and 1.93% were female, indicating an over-representation of males in the literature. The age of victim participants ranged from 11 to 15 years across the 10 articles that reported age. In contrast, the age of individuals with an offending history ranged from 18 to 65 years across the six articles that reported age. Of the 10 articles that included participants with an offending history, 98.17% involved convicted individuals, while 1.83% involved non-convicted individuals, indicating an over-representation of individuals with convictions in the literature.
The included studies were primarily conducted in Western countries. Nevertheless, the strategies used by adults to identify, approach, and engage children and young people in inappropriate conversations and sexually exploitative and abusive interactions online likely vary depending on a range of demographic factors, including gender, age, and ethnicity. This review highlights the need for future research to adopt a more targeted approach to exploring strategies used by individuals who engage in OSG and/or TA-CSA offenses across different demographic profiles. Specifically, there is a significant gap in terms of examining this type of offending behavior in females, and against male victims.
Conclusion
Individuals who engage in OSG and TA-CSA make use of a number of different manipulative strategies to identify, approach, and engage children and young people in inappropriate conversations and sexually exploitative and abusive interactions online. Our findings demonstrate that individuals adapt and individualize their strategies to victims’ unique vulnerabilities, presentations, and perceived preferences, as well as their own motivation, and the function their behavior intends to serve. An overview of how these findings may be used to inform policy, practice, and research implications is presented in the summary table below.
Summary of Critical Findings
Implications for Practice, Policy, and Research
Note. OSG = online sexual grooming; TA-CSA = technology-assisted child sexual abuse.
Supplemental Material
sj-docx-1-tva-10.1177_15248380251411261 – Supplemental material for Unraveling the Complexities of Offender Strategies as Part of Online Sexual Grooming and Technology-Assisted Child Sexual Abuse: A Systematic Review
Supplemental material, sj-docx-1-tva-10.1177_15248380251411261 for Unraveling the Complexities of Offender Strategies as Part of Online Sexual Grooming and Technology-Assisted Child Sexual Abuse: A Systematic Review by Carly Porcelli, Flora Anderson and Juliane A. Kloess in Trauma, Violence, & Abuse
Footnotes
Authors’ Note
Juliane A. Kloess is now at the School of Health & Wellbeing, University of Glasgow.
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
Declaration of Conflicting Interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Supplemental Material
Supplemental Material for this article is available online.
Notes
Author Biographies
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
