Abstract
The existing body of research on cyberstalking has identified the prevalent nature of this behavior, and the detrimental impact that cyberstalking has on victims and society. This systematic review aims to summarize literature on the perpetration of cyberstalking with two research questions: (a) Who are the perpetrators of cyberstalking? and (b) What are the methods of cyberstalking? Two literature databases (SCOPUS and Web of Science) were searched for empirical research or literature reviews examining cyberstalking perpetration and/or methods. Following screening, 80 articles were identified and rated as highly relevant based on their applicability to the research questions. Perpetrators of cyberstalking were found to lack social skills, have low self-control, have experienced physical abuse victimization, endorsed stalking-related attitudes, and have higher rates of Internet use. Perpetrators were motivated by trying to reconcile a relationship, exact revenge, seek a relationship, or establish control over the victim. The most commonly reported methods of cyberstalking were unwanted and repeated online contact through email, social media, or text message. Other methods of cyberstalking include accessing the victim’s accounts, tracking their GPS location, posing as the victim online, or contacting friends/family of the victim. The findings of this review highlight precursors to, and patterns of, cyberstalking perpetration, and future research is required to explore how existing “offline” stalking risk assessments and typologies can be applied to cases of cyberstalking, which would allow authorities to develop effective case management strategies.
Keywords
The undeniable and exponential growth of the Internet and social media has streamlined communication between individuals across the globe (Paullet & Chawdhry, 2020). However, researchers have noted that social media can facilitate high-risk online behaviors such as sending sexually explicit messages (sexting), image-based sexual abuse, distribution of malware, trolling, and cyberstalking (Akram & Kumar, 2018; Cookingham & Ryan, 2015; Howard et al., 2019; Marcum et al., 2017; Powell et al., 2020). Cyberstalking is the subject of an increasing body of research, however, there remains a need to better our knowledge of cyberstalking perpetrators and their methods of cyberstalking to help inform our understanding of, and ability to predict, patterns within cyberstalking perpetration (Kaur et al., 2021; Wilson et al., 2023). Thus, the aim of this systematic literature review is to summarize the existing research on cyberstalking perpetrators and their methods.
Although definitions of “offline” stalking and cyberstalking vary across research, policy, and practice (Wilson et al., 2022), stalking is generally defined as repeated, unwanted behavior that causes a victim distress or fear, and cyberstalking is when this behavior is conducted solely online. Cyberstalking, therefore, generally includes repeated monitoring, contacting, or pursuit of an individual exclusively using technology and/or the Internet (Becker et al., 2020; Marcum et al., 2017; Nobles et al., 2014; Wilson et al., 2022). Whether cyberstalking should be considered a method of stalking, or that it is a fundamentally distinct form of behavior, has been debated and a consensus has not yet been reached (Sheridan & Grant, 2007; Nobles et al., 2014; Wilson et al., 2022). Ultimately, most stalking cases include a mixture of offline and online behaviors during the course of conduct (Wilson et al., 2022; Woodlock, 2017), and there remains a need to elucidate whether there is a meaningful distinction between stalking and cyberstalking.
The academic understanding of cyberstalking is improving with an increase in research over recent years (Kaur et al., 2021). However, a literature review by Wilson et al. (2022), examining how cyberstalking is measured in research, highlighted inconsistencies among definitions and operationalizations of cyberstalking. All 33 studies included in the review adopted definitions of cyberstalking which stated that the behaviors were unwanted by the victim, but definitions differed in their requirements of cyberstalking duration and timeframe, perpetrator intent, and victim fear. Of the included studies, 45% provided a minimum number of incidents required for the behavior to be considered cyberstalking. Of these, 21% defined repetition as the behavior being experienced 1 or more times (e.g., Maran & Begotti, 2019), 21% required 2 or more times (e.g., Dardis & Gidycz, 2017), and 3% required 10 or more occurrences (e.g., Sheridan & Grant, 2007). The remaining 55% of studies did not specify a minimum number of behaviors, and instead only implied that the behaviors must have been repeated (Wilson et al., 2022). Further, only 30% of studies asked the victim to identify if the behavior caused them to feel fear for their safety (e.g., Fissel & Reyns, 2019). Thus, the operationalization of cyberstalking in research is inconsistent and there is a need for a universal definition and criteria for cyberstalking to support consistent future research. Suggestions forwarded in the research literature include requiring a minimum number of cyberstalking behaviors or a minimum duration of the cyberstalking pursuit, but further research is needed to specify what these minimums would be (Purcell et al., 2011; Wilson et al., 2022).
Logan and Walker (2017) have proposed a multidimensional framework that provides a basis for a consistent stalking definition and encourages a systematic approach to assessing a course of conduct. Namely, stalking is an intentional course of conduct including tactics of surveillance, life invasion, intimidation, and interference that is unwanted by the victim and causes the victim to feel reasonable fear. The authors highlight that stalking is a dynamic act that differs in duration, intensity, and frequency. The framework applies to both stalking and cyberstalking with the only distinction being the modality of perpetration, that is, stalking occurs “offline” and cyberstalking occurs online. The framework aligns with many legal definitions of cyberstalking, including statutes in the United States (Branscum et al., 2021; Hazelwood & Koon-Magnin, 2013) and the Protection from Harassment Act (1997) and Protection of Freedoms Act (2012) in the United Kingdom, which generally define cyberstalking as any unwanted, repeated online behavior that causes the victim reasonable alarm, distress, or fear. The adoption of such a framework would therefore allow a standardized approach to defining and operationalizing cyberstalking with relevance to existing legal definitions.
The lack of a universal definition of cyberstalking in research has contributed to varying estimates of the prevalence of cyberstalking perpetration and victimization. In both general population and university samples, self-reported cyberstalking victimization rates have varied from 3.4% to 40.8% and self-reported rates of cyberstalking perpetration have varied from 4.9% to 50.9% (Berry & Bainbridge, 2017; DeKeseredy et al., 2019; Dressing et al., 2014; Fissel et al., 2021; Kraft & Wang, 2010; Lee & O’Sullivan, 2014; Lyndon et al., 2011; Navarro et al., 2016; Reyns et al., 2012, 2018). Researchers have also noted that victims may be unable to self-identify as victims, despite experiencing “offline” stalking and cyberstalking according to definitional criteria. For instance, McNamara and Marsil (2012) identified that 75% of stalking victims did not label their experience as stalking, and Brady et al. (2023) identified that 50% of cyberstalking victims did not consider the perpetrator to be cyberstalking them. Relatedly, Montero-Fernández et al. (2023) examined the perceived acceptability of various cyberstalking methods in the context of intimate relationships. A striking majority, 70% of females and 56% of males, agreed that reading a partner’s private online conversations was acceptable behavior. Many methods of cyberstalking may therefore be minimized or justified by perpetrators, mirroring findings in domestic abuse research, whereby perpetrators are known to often justify their actions (Giezek et al., 2023). Overall, victims and perpetrators of cyberstalking may under-recognize and under-report methods of cyberstalking, having implications for ongoing research into prevalence rates.
Nonetheless, research has highlighted the detrimental and extensive impact of cyberstalking on victims (Worsley et al., 2017). Victims of cyberstalking are likely to experience anxiety, depression, helplessness, sleep disturbance, physical health deterioration, and social withdrawal (Dressing et al., 2005, 2014; Worsley et al., 2017). Victims of cyberstalking report various coping responses and impacts on their daily life, such as having to reduce their attendance or change their place of school/work, and reduce or cease use of social media (Dressing et al., 2005; Worsley et al., 2017).
Despite reviews by Kaur et al. (2021) and Wilson et al. (2023) having explored cyberstalking perpetration, there remains scope for the current systematic review, especially in light of the ever-changing technological landscape which enables perpetrators to quickly develop novel methods of cyberstalking. Wilson et al. (2023) highlighted key factors relating to perpetration, including deviant peer association, low self-control, previous victimization, and personality traits. Kaur et al. (2021) identified the major thematic areas within cyberstalking research to date, namely, predictors of perpetration and victimization as well as the role of stakeholders. These reviews provide a succinct summary of much cyberstalking research, however, neither review fully explored methods of cyberstalking. The existing body of cyberstalking research is oriented toward victimization (i.e., predictors of victimization; victim experiences, and impact on victims), and while the importance of this research should not be understated, a more comprehensive understanding of cyberstalking perpetration and methods is required (Kaur et al., 2021).
Policing cyberstalking evokes a variety of challenges. For instance, many police officers have a limited working knowledge of the fast-evolving technology used by cyberstalking perpetrators or the risks that perpetrators pose to victims (O’Shea et al., 2019). With an enhanced understanding of cyberstalking perpetration set out by this systematic review, future research should investigate whether existing stalking typologies, risk factors, and risk assessment tools can be considered effective in the policing and management of cyberstalking cases. In addition, a summary of the methods used by cyberstalking perpetrators provided by this systematic review can inform authorities of what behaviors to expect in cases of cyberstalking, and consequently, which restrictions are required in legal injunctions or court orders put in place to protect victims. The current systematic literature review identifies empirical research into perpetrators and methods of cyberstalking, aiming to answer two research questions: (a) Who are the perpetrators of cyberstalking?, and (b) What are the methods of cyberstalking?
Method
This systematic literature review followed PRISMA-P guidelines (Moher et al., 2015) to ensure transparency of method and was pre-registered on PROSPERO (ID: CRD42021288986).
Terminology Parameters
Previous reviews have identified that existing literature uses a range of terminology to describe cyberstalking behavior (Wilson et al., 2022, 2023). The search process, therefore, began with a preliminary search of the literature to identify keywords for use in the database search. This was performed on Google Scholar using the keyword “cyberstalking.” The first 50 results ordered by relevance, where a full text paper was available, were consulted, and the variant keywords “online stalking,” “internet stalking,” “cyber-stalking,” and “cyber obsessional pursuit” were identified for inclusion in the search criteria. These search terms were combined to create searches on SCOPUS and Web of Science, Figure 1 demonstrates the database search process. To adopt an inclusive approach and address the issue of definitional variations, a specific definition of cyberstalking was not considered as part of the search process.
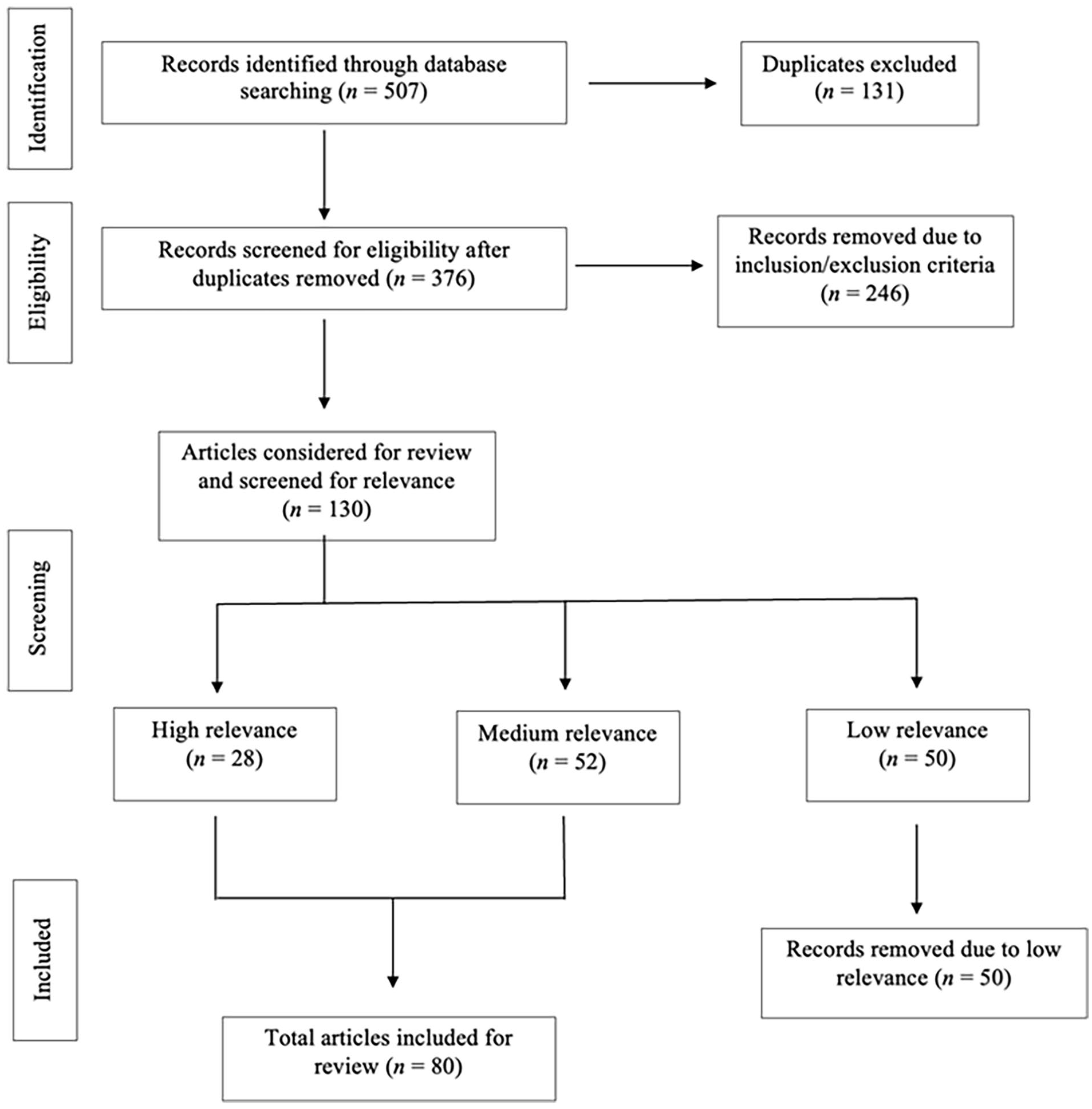
Search process.
Inclusion and Exclusion Criteria
To reflect the modern-day usage of communication technologies such as social media and smartphone devices, and the perpetration of cyberstalking on these platforms, the date range of 2009 to 2024 was chosen for study inclusion. Prior to 2009, research on cyberstalking generally focused on the use of email, telephone, chatrooms, and instant messages (D’Ovidio & Doyle, 2003). The availability and use of social media platforms and smartphones has grown exponentially since 2009, and it is widely understood that cyberstalking now commonly occurs through social media and smartphones (Dressing et al., 2014; Lyndon et al., 2011).
The search identified 507 articles from the 2 databases. Duplicates were removed (n = 131), leaving 376 articles to be screened for eligibility by the first author. Eligibility screening was conducted through title and abstract reading against the following inclusion criteria: the term “cyberstalking” or an alternative term (i.e., “online stalking,” “internet stalking,” “cyber-stalking,” “cyber obsessional pursuit”) was included in title, keywords, or abstract; the paper was an empirical study, literature review, or meta-analysis; the paper focused on perpetration and/or methods of cyberstalking; the paper was published in a peer-reviewed journal from 2009 to 2024; and the full text was available in English. Empirical papers that included only participants under 18 were excluded, since research into children’s online behaviors generally focuses on cyberbullying, defined as repeated, intentional, harmful, often anonymous online contact toward another child or adolescent, often perpetrated within school contexts and involving multiple perpetrators and victims (Aboujaoude et al., 2015; Chandrashekhar et al., 2016) and is generally considered distinct to cyberstalking (Kircaburun et al., 2018). Gray literature was excluded from the review due to the absence of peer review and issues with quality, credibility, and reproducibility. Articles were removed based on the inclusion and exclusion criteria (n = 246), leaving 130 articles to be assessed for relevance and quality. The reliability of inclusion/exclusion ratings was examined using Cohen’s kappa value on a random sample of 10 articles coded independently by the first and second authors. The Cohen’s kappa value was 1.0, indicating perfect agreement (Landis & Koch, 1977).
Relevance Screening
The first author categorized the 130 articles as high, medium, or low relevance based on their relevance to the research questions. Articles were rated as high relevance if they could be used to directly answer both research questions. Articles were rated as medium relevance if they could be used to answer one research question. Articles were rated as low relevance if they could not directly answer either research question. Reliability of the relevance ratings was examined using Cohen’s kappa value on a sample of 10 articles, coded independently by the first and third authors. The Cohen’s kappa value was .688, indicating substantial agreement (Landis & Koch, 1977). Articles rated as high relevance (n = 28) or medium relevance (n = 52) totaled 80 articles to be included in the systematic review. Articles rated as low relevance (n = 50) were not included in the results of the systematic review.
Results
Who Are the Perpetrators of Cyberstalking?
Perpetrator Gender
Ten studies identified differences in the gender balance of cyberstalking perpetrators. Out of these, three studies found that being female significantly predicted cyberstalking perpetration (March et al., 2020; Resett et al., 2023; Silva Santos et al., 2021). Specifically, two further studies found that women were more likely than men to perpetrate intimate partner cyberstalking (i.e., targeting a person of romantic interest to obtain or maintain a romantic connection; Rodríguez-Castro et al., 2021; Smoker & March, 2017). Three studies found a higher prevalence of male perpetrators (Cavezza & McEwan, 2014; Fernández-Cruz et al., 2021; Reyns, 2019). Only 1 of the 10 studies found no gender difference in cyberstalking perpetration (Fissel, 2021). Overall, there was no consensus on the gender balance of cyberstalking perpetration, and gender alone was not identified as a reliable predictor (Wilson et al., 2023).
Research by Dardis and Gidycz (2019) explored how cyberstalking perpetration differs by gender. The authors defined “minor cyber unwanted pursuit” behaviors as excessive contact or seeking information about the victim, motivated by the desire to reconcile a relationship, and “severe cyber unwanted pursuit” behaviors as sending explicit threats or using GPS to monitor a victim’s location, motivated by coercive control. Results showed that women were more likely to perpetrate “minor cyber unwanted pursuit” behaviors, whereas men were more likely to engage in “severe cyber unwanted pursuit” behaviors. Studies by Begotti et al. (2020) and Nuttman-Shwartz et al. (2023) highlighted that male cyberstalking perpetrators engaged in a greater number of cyberstalking behaviors, including unwanted online sexual advances and online threats of violence. Three studies posited that women may be more likely to engage in covert cyberstalking behaviors due to the relative anonymity afforded by these online acts, and this may be motivated by insecurity or rejection sensitivity (March et al., 2020; Miller, 2012). Men, however, may be thrill-seeking through their overt, more severe cyberstalking behaviors (March et al., 2020; Smoker & March, 2017).
Personality and Psychological Traits
Regarding personality and psychological predictors of cyberstalking perpetration among women, high borderline traits, low self-control, childhood physical abuse, preoccupied attachment style, physical abuse, sexual abuse, and “offline” stalking victimization have all been found to predict cyberstalking perpetration (Duffy et al., 2023; Holmes et al., 2022; Ménard & Pincus, 2012; Reyns, 2019). Conversely, sending explicit messages, experience of childhood sexual abuse, and narcissistic vulnerability (poor self- and emotion-regulation in response to self-enhancement failures) have been found to predict cyberstalking perpetration among men (Ménard & Pincus, 2012; Reyns, 2019).
Many studies also explored psychological traits and disorders as predictors of cyberstalking perpetration, without regard to gender. A meta-analysis by Kim (2023) examining self-report studies on cyberstalking perpetration and victimization, as well as systematic literature reviews by Kaur et al. (2021) and Moor and Anderson (2019), highlighted that anxiety, depression, PTSD, sadism, psychopathy, and Machiavellianism were most strongly correlated with cyberstalking perpetration when compared to other risk domains such as sociodemographics, relationship status, and community support. Considering the dark tetrad traits (Machiavellianism, narcissism, sadism, and psychopathy), further self-report studies by Branković et al. (2023) and Smoker and March (2017) identified that all dark tetrad traits were positively correlated with cyberstalking perpetration. However, Kircaburun et al. (2018) identified that only sadism, Machiavellianism, and narcissism were directly associated with cyberstalking, but not psychopathy.
Social Skills, Attachment, and Self-Control
Jenaro et al. (2018) identified that cyberstalking perpetrators were more likely than non-perpetrators to be impulsive and lack social skills. Cyberstalking perpetration was also correlated with increased levels of attachment anxiety (i.e., worries about the availability of a partner, desire for closeness, and fear of rejection). The authors hypothesized that an individual may engage in intimate partner cyberstalking if they perceive a threat to their relationship and fear abandonment (Reiss et al., 2022a). Research into self-control and its relationship with intimate partner cyberstalking perpetration identified that low self-control significantly predicted perpetration, including infiltrating the victim’s personal accounts and tracking their location, as well as the belief that cyberstalking would not have a negative impact on the victim (Marcum et al., 2017, 2018).
Attitudes and Emotional Characteristics
Chan et al. (2021) highlighted correlations between emotional characteristics, endorsement of stalking-related attitudes, and cyberstalking perpetration. Specifically, emotion dysregulation (i.e., a lack of emotional awareness/understanding, poor impulse control, and poor coping mechanisms) was directly associated with cyberstalking perpetration. The authors also measured stalking-related attitudes pertaining to the minimization of stalking (i.e., the belief that stalking is not serious), flattery (i.e., stalking is romantic), and victim blaming. A higher endorsement of these stalking-supportive attitudes was positively associated with cyberstalking perpetration, and the authors stated that this association may exist because it enables perpetrators to justify and minimize the nature of their cyberstalking (Chan et al., 2021).
Childhood and Adulthood Experiences
Research has also highlighted how childhood and adulthood experiences correlate with cyberstalking perpetration. Cano-Gonzalez et al. (2022) identified that participants with exposure to parental violence in childhood were more likely to perpetrate cyberstalking in adulthood than those with no exposure. A replication study, including 1,113 young adults, also found that individuals with experiences of childhood maltreatment and parental violence were more likely to perpetrate intimate partner cyberstalking (Cano-Gonzalez et al., 2023). Considering violent experiences in adulthood, one study identified that physical abuse victimization from a partner predicted intimate partner cyberstalking perpetration (Curry & Zavala, 2020).
Extent and Nature of Internet Use
Six studies explored the relationship between cyberstalking perpetration and the extent of Internet use, including the frequency and nature of use, risky online behaviors, social media engagement, and Internet addiction. Reviews by Jenaro et al. (2018) and Marcum and Higgins (2021) highlighted that high levels of access to technology, high rates of Internet use, and greater time spent online predicted cyberstalking perpetration. Reyns (2019) identified that cyberstalking perpetration was predicted by sexting (receiving explicit images) in both men and women. Silva Santos et al. (2021) identified a positive correlation between cyberstalking perpetration and social media engagement, demonstrating that perpetrators tend to use social media sites more frequently. Internet addiction, that is, an individual’s problematic use of the Internet when this is detrimental to their day-to-day functioning and social relationships (Chakraborty et al., 2010) has also been shown to predict cyberstalking perpetration (Navarro et al., 2016).
Perpetrator-Victim Relationship
Three studies aimed to identify the most common relationship between cyberstalking perpetrators and victims. Reyns et al. (2012) asked participants to indicate their relationship to the cyberstalking perpetrator, out of three categories: current or ex-intimate partner, friend/acquaintance, or stranger. Cases of cyberstalking were almost evenly split between known and unknown perpetrators, with 56% of cases involving either an (ex)intimate perpetrator (17.4%) or a friend/acquaintance (38.6%), and 44% of cases involving a stranger. Another study found that cyberstalking perpetrators and victims were most likely to be known to each other, and only 11% of cases involved an unknown (i.e., stranger) perpetrator (Fernández-Cruz et al., 2021). In a comparison of “offline” stalking to cyberstalking in a forensic sample, perpetrators of cyberstalking were significantly more likely to be an ex-intimate partner of the victim, represented in 75% of cyberstalking cases compared to 47% of “offline” stalking cases (Cavezza & McEwan, 2014).
Perpetrator Motivation
Seven studies explored the motivations of cyberstalking perpetration. Cavezza and McEwan (2014) aimed to do this by grouping cyberstalking perpetrators into five types: Rejected, Intimacy Seeking, Incompetent Suitor, Resentful, and Predatory, based on Mullen et al.’s (1999) stalking typology. The most commonly identified category, Rejected perpetrators who engage in stalking for reconciliation or revenge following the breakdown of a relationship with the victim, represented 75% of cyberstalking cases. This was followed by 14% of cases who fit the Resentful category, perpetrators who feel they have been humiliated by the victim and desire revenge. Only 5% of cases involved Intimacy Seeking perpetrators, who have a fantasy of love and aim to establish an intimate relationship with the victim, generally a stranger or acquaintance, and 3% Incompetent Suitor perpetrators who aim to initiate contact with the victim and feel entitled to a relationship with them. Predatory perpetrators who have deviant sexual beliefs and conduct stalking in preparation for an attack, represented 3% of cases (Cavezza & McEwan, 2014). Additional research by March et al. (2023) suggested that Intimacy Seeking cyberstalking perpetrators may be motivated by mate-seeking behavior to gather information on a potential mate and may use the cyberstalking behavior as a strategy to maximize successful dating.
The remaining studies on motivations of cyberstalking perpetrators highlighted that cyberstalking is motivated by the desire to reconcile or that cyberstalking is motivated by power and control. In ex-intimate partner cyberstalking cases, perpetrators’ behavior has been explained by relational goal pursuit theory (Cupach & Spitzberg, 2000), whereby cyberstalking perpetrators are motivated by the desire to reconcile a romantic relationship, particularly if they were surprised or distressed by the break-up (Belu et al., 2016; Dardis & Gidycz, 2019). Alternatively, other research suggests that cyberstalking perpetration is explained by coercive control theory (Stark, 2007), whereby cyberstalking perpetrators are motivated to engage in intimidation of the victim to retaliate or (re-)establish control (Dardis & Gidycz, 2019; Frampton & Fox, 2021). Victims of cyberstalking targeted by a friend, classmate, colleague, or acquaintance perceived the behavior to be a form of control and believed the perpetrator was motivated to gain power over the victim (Fissel, 2021; Melander, 2010). Overall, motivations of cyberstalking perpetrators appear to mirror Mullen et al.’s (1999) typology of stalking, and perpetrators engage in cyberstalking in an effort to reconcile with or control the victim.
What Are the Methods of Cyberstalking?
Categorizing Methods of Cyberstalking
Four studies attempted to categorize cyberstalking methods. Categories of cyberstalking methods were identified through principal axis factor analysis (De Fazio et al., 2020), thematic analysis (Reiss et al., 2022b), confirmatory factor analysis (Ybarra et al., 2017), and exploratory factor analysis (March et al., 2022). The authors also identified specific methods of cyberstalking within each category (see Table 1). As can be seen in Table 1, each study’s results produced a different categorization and not all categories were distinct, as many overlap in the cyberstalking methods included. For this reason, the methods of cyberstalking reported in this literature review will not be categorized in one of the four existing classification systems. Instead, the overall prevalence of different cyberstalking methods in the literature will be discussed, as well as the specific platforms and technologies used to engage in the methods of cyberstalking perpetration.
Categories of Cyberstalking Methods.
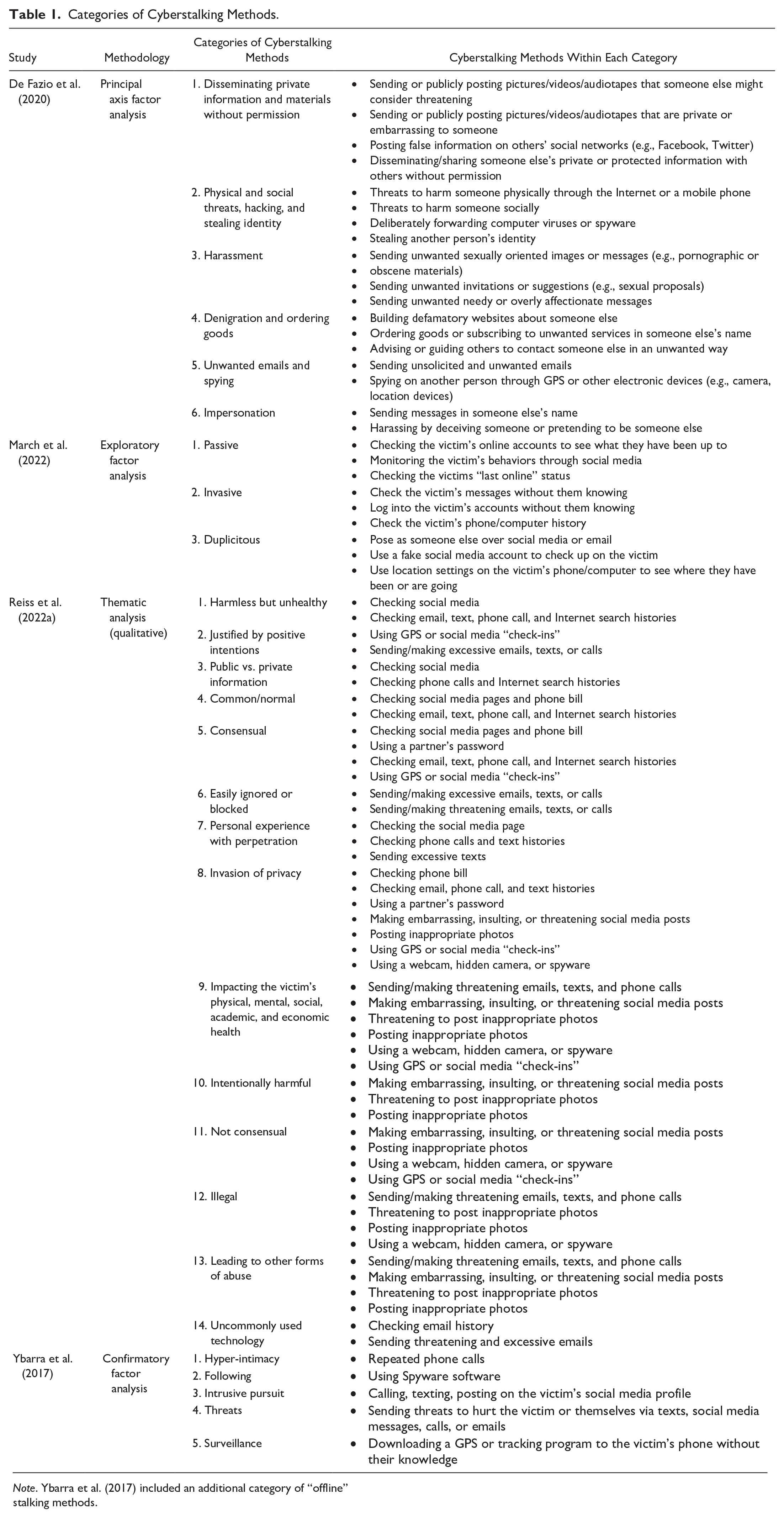
Note. Ybarra et al. (2017) included an additional category of “offline” stalking methods.
Prevalence of Cyberstalking Methods
Many articles reported unwanted and/or inappropriate contact as the most common method of cyberstalking, which can be conducted via repeated phone calls, text messages, social media messages, friend requests, and on dating apps (Centelles et al., 2021; DeMatteo et al., 2017; Dimond et al., 2011; Dressing et al., 2014; Every-Palmer et al., 2015; Olson et al., 2024; Romanosky & Schirmer, 2023; Sambasivan et al., 2019; Tokunaga & Aune, 2017). Begotti and Maran (2019) further explored the nature of unwanted online contact and reported that 20.2% of their participants experienced unwanted sexual advances online, and 11.8% experienced online threats of violence. Lee and O’Sullivan (2014) also identified that 22% of participants had sent their ex-partner unwanted messages of affection, and 9% had sent their ex-partner unwanted sexual messages.
There may be an unexplored minority of cyberstalking cases, however, whereby the perpetrator uses primarily covert methods to monitor or track their victim. Two articles highlighted that cyberstalking victims are less likely to report methods that do not involve direct contact (i.e., accessing the victim’s devices or online accounts, downloading data from the victim’s device, accessing the victim’s online banking, or posing as the victim online) compared to direct repeated, unwanted contact from a perpetrator (Begotti & Maran, 2019; Dressing et al., 2014).
Platforms Used to Perpetrate Cyberstalking
An early literature review found that sending repeated, unwanted emails was the most common cyberstalking method (Miller, 2012). However, three subsequent reviews have highlighted an increase in cyberstalking on social media including through monitoring a victim’s social media posts, sending repeated, unwanted messages, or posting on the victim’s social media profile (Henry & Powell, 2018; Henry et al., 2020; Kaur et al., 2021). Through an analysis of cases of cyberstalking, Al-Mutawa et al. (2016) also identified that cyberstalking perpetrators used social media sites such as Facebook and Twitter to post embarrassing, hateful, or threatening comments about their victims.
Early research by Lyndon et al. (2011) explored specific methods of cyberstalking perpetrated on Facebook. From a sample of 411 university students, 58% had created a Facebook post targeting their ex-partner, 20% had written on their ex-partner’s Facebook wall, 8% had asked their ex-partner to unblock them, 7.6% posted a nasty or spiteful comment on a photo of their ex-partner, 4% had posted embarrassing photos of their ex-partner, 3.6% had created a fake Facebook profile, impersonating their ex-partner, and 3.6% had used Facebook to spread vexatious rumors about their ex-partner. More recent research highlights how newer social media platforms and dating apps have created further opportunities for perpetration of cyberstalking. Perpetrators who utilize Snapchat, for example, can also send repeated, unwanted messages, photos, or videos to a victim but these messages disappear after being viewed, and the sender is notified if the victim takes a screenshot of the messages. In addition, Snapchat enables geolocation tracking of a victim in real-time (Brady et al., 2023). The use of dating apps within cases of cyberstalking, such as Tinder, has also been noted in research. Among a sample of dating app users, Centelles et al. (2021) identified a cyberstalking victimization rate of 64.8% (n = 210), operationalized by receiving repeated, unwanted messages.
One study coined the term “social media stalking” (Dhir et al., 2021, p. 1380) to describe cyberstalking through the surreptitious monitoring of a victim’s social media, such as frequently checking the victim’s profile to see what they are up to, and this method of cyberstalking has been frequently reported by victims (Ferdous & Huda, 2023). Dhir et al. (2021) hypothesized that the tendency to monitor others through social media may have become “normalized” and further research has demonstrated that methods of cyberstalking perpetrated through social media may not be labeled as cyberstalking, by victims or perpetrators. Brady et al. (2023) explored victim perception of cyberstalking on Snapchat. From their sample of cyberstalking victims (n = 194), 32% reported experiencing unwanted repeated contact or threats on Snapchat. However, 50% of these victims did not consider the perpetrator’s use of Snapchat to be cyberstalking. Montero-Fernández et al. (2023) also identified that, in a sample of university students (n = 303), 27% reported monitoring their partner’s social media accounts, and 70.1% of female participants and 55.7% of male participants agreed that reading a partner’s private conversations on social media was acceptable behavior within a relationship.
Technologies Used to Perpetrate Cyberstalking
Four studies detailed specific technologies that enable the perpetration of cyberstalking and how these technologies relate to particular cyberstalking methods. Horsman and Conniss (2015) investigated the use of anonymous messaging resources in cyberstalking perpetration. The authors identified a number of services that allow a perpetrator to send a victim a text message without leaving any trace of their identity. Attempts to identify the perpetrator through analysis of mobile operator logs can also be prevented by these services, thus allowing for repeated, unwanted, anonymous contact.
Eterovic-Soric et al. (2017) further identified how specific technology and software can enable cyberstalking through location tracking. Specialized GPS tracking devices allow a perpetrator to easily trace a victim’s location and movements, but concerningly, location-based apps on a victim’s mobile phone can also provide this information to a perpetrator without the need to plant an additional device. The authors describe the concerning development of “stalker apps” which can be disguised and downloaded onto a victim’s phone to share their location with a perpetrator. In addition, spyware installed on a victim’s computer or device without their knowledge can provide a perpetrator with information on the victim’s computer usage, email accounts, and passwords. Webcams and microphones can also be compromised by cyberstalking perpetrators to monitor and gather personal images, videos, or conversations of the victim (Eterovic-Soric et al., 2017). Victims of cyberstalking who experienced online monitoring (e.g., the perpetrator tracked the victim with GPS software, monitored the victim’s online activity, or accessed the victim’s online accounts) were more likely to report that the cyberstalking had resulted in more life interference including having to change their Internet use, or having to change or move jobs, and also resulted in higher levels of fear when compared to cyberstalking victims who had only experienced unwanted online contact (Logan, 2023). Research therefore suggests that these covert cyberstalking methods, facilitated through accessible and widespread technology such as smartphones and apps, can result in significant negative impacts on victims.
Sovacool et al. (2021) highlighted methods of cyberstalking perpetrated using smart home technology. Findings from their national U.K. sample (n = 1,032) and a review of the existing literature indicated that certain technologies in the home, such as smart surveillance systems, doorbell cameras, and smart home energy monitoring systems, can facilitate surveillance of a victim. A cyberstalking perpetrator can use smart surveillance systems or doorbell cameras to monitor the victim’s whereabouts and visitors to the home, and smart home energy monitoring systems to monitor the victim’s routines. The authors clarify that the perpetration of cyberstalking through smart home technology does not require face-to-face encounters and can be perpetrated regardless of the time or location of the perpetrator or victim, thus facilitating constant control over the victim (Sovacool et al., 2021). Overall, research highlights a concerning trend of increasing opportunities for cyberstalking perpetrators to instill fear in their victims. Novel technology can enable anonymous unwanted contact, location tracking, infiltration of online accounts, monitoring of online activity and home routines, negatively impacting the lives of victims greatly.
Discussion
This systematic literature review presented existing research examining who cyberstalking perpetrators are, and the methods through which they perpetrate cyberstalking. When considering the implications and wider context of the findings of this review, it is also important to consider how they relate to “offline” stalking research, given that “offline” stalking has been far more extensively studied. Nobles et al. (2014) posit that cyberstalking victims represent a subset of stalking victims, in that all victims experience unwanted, repeated communication but cyberstalking victims experience this exclusively via online avenues. Related arguments have also been presented by Cavezza and McEwan (2014), that perpetrators of “offline” stalking and cyberstalking do not differ significantly in their motivations or demographic and clinical characteristics, and by Sheridan and Grant (2007), that the impact on victims does not differ significantly between “offline” stalking and cyberstalking victimization. Thus, research suggests that “offline” stalking and cyberstalking perpetration and victimization yield more similarities than differences. It is also worth noting that the majority of stalking cases contain both online and “offline” methods employed by the perpetrator (Wilson et al., 2023). Therefore, the findings of this systematic review will be considered in light of existing research into “offline” stalking and cyberstalking.
Perpetrators of Cyberstalking
Research discussed in this review indicates that both men and women perpetrate cyberstalking, but male perpetrators were more likely to perpetrate severe, intrusive cyberstalking behaviors such as sexual harassment and tracking a victim’s location (Begotti et al., 2020; Dardis & Gidycz, 2017). Victims of cyberstalking who experience sexual harassment and location monitoring report high levels of fear and life interference (Logan, 2023), suggesting that victims targeted by male perpetrators may be more likely to experience significant negative impacts. The finding that male perpetrators of cyberstalking are more likely than female perpetrators to engage in severe, intrusive methods (Begotti et al., 2020; Dardis & Gidycz, 2017) is mirrored in “offline” stalking research which has identified that male perpetrators pose a greater risk of harm to victims (Lyndon et al., 2012). Future research should aim to test hypotheses explaining why these gender differences exist, including whether male perpetrators may be thrill-seeking through overt cyberstalking perpetration compared to female perpetrators who may appreciate the anonymity afforded by covert cyberstalking perpetration (March et al., 2020; Miller, 2012; Smoker & March, 2017).
The research reviewed stipulates that perpetrators of cyberstalking were likely to have high levels of impulsivity and attachment anxiety, as well as childhood experience of parental violence, physical abuse victimization in adulthood, and low self-control (Cano-Gonzalez et al., 2023; Curry & Zavala, 2020; Jenaro et al., 2018; Marcum et al., 2018; Reiss et al., 2022a). Chan et al. (2021) further identified that perpetration of both cyberstalking and “offline” stalking was predicted by emotional dysregulation and stalking-supportive attitudes. Regarding dark tetrad personality traits, research identified positive correlations between cyberstalking perpetration and sadism, Machiavellianism, and narcissism (Branković et al., 2023; Smoker & March, 2017). Considering the remaining dark tetrad trait psychopathy, however, one study identified that psychopathy did not have a direct correlation to cyberstalking perpetration (Kircaburun et al., 2018) and previous research of “offline” stalking has also identified that psychopathy is not prevalent in stalking perpetrators (Storey et al., 2009).
Thus, research to date indicates similarities between predictors and correlates of cyberstalking and “offline” stalking perpetration; however, there remains a lack of comparative research that examines precursors of both “offline” stalking and cyberstalking perpetration concurrently. Understanding how personality and psychological characteristics predict “offline” stalking perpetration has led to the successful development and implementation of stalking risk assessment tools, for instance, the Guidelines for Stalking Assessment and Management (SAM; Kropp et al., 2008) and the Stalking Risk Profile (SRP; MacKenzie et al., 2009) which consider psychological and social characteristics of the perpetrator (Weekes & Storey, 2024). It is likely, considering the similarities in precursors to offending, that these existing “offline” stalking risk assessment tools have utility in the prediction of risk in cases of cyberstalking. Further research should consider using mixed samples of “offline” stalking and cyberstalking cases to identify the extent to which the SAM and SRP can successfully predict the risk of harm to victims. In addition, correlates specific to cyberstalking perpetration but not “offline” stalking perpetration require further investigation for potential inclusion in risk assessment tools. For instance, it is hypothesized that increased time spent online and Internet addiction may disrupt an individual’s ability to maintain “in-person” relationships and increase the risk of cyberstalking perpetration, but the causal direction of this relationship has not yet been determined (Navarro et al., 2016).
Cyberstalking perpetrators were most often found to be an ex-intimate partner of the victim; however, findings did vary (e.g., Cavezza & McEwan, 2014; Reyns et al., 2012). Cyberstalking perpetrators were most likely to be rejected perpetrators (Mullen et al., 1999) who engage in cyberstalking for reconciliation or revenge following the breakdown of a relationship (Cavezza & McEwan, 2014). The “offline” stalking literature has identified ex-intimate partner as the most common relationship between victim and perpetrator, and that stalking victims targeted by an ex-partner are at a higher risk of violence (L. Sheridan & Davies, 2001; McEwan et al., 2017). However, the dearth of cyberstalking research in this area highlighted herein means that a similar conclusion has not been reached. Victims of cyberstalking targeted by an ex-partner may endure more invasive, severe, or persistent forms of cyberstalking, but further exploration should aim to identify whether this presents a greater risk of harm to the victim and precedes physical violence.
One study reviewed most cyberstalking perpetrators as Rejected in line with Mullen et al.’s (1999) typology (Cavezza & McEwan, 2014). However, this finding was identified in a small forensic sample of perpetrators and the question remains whether Mullen et al.’s (1999) existing typology is sufficient to categorize perpetrators of cyberstalking. Future research should include a broad sample of cyberstalking cases to identify whether the existing categories within Mullen et al.’s (1999) typology are sufficient to categorize cyberstalking perpetrators, and in turn, whether these perpetrators differ fundamentally from perpetrators of “offline” stalking. Overall, there remains a lack of understanding regarding how to effectively predict, manage, and reduce cyberstalking perpetration, and although existing stalking literature can and should inform these approaches, further comparative research would aid in the categorization of perpetrators and assessment of risk.
Methods of Cyberstalking
Results of this systematic review identified that repeated and unwanted contact was the most commonly reported method of cyberstalking which occurs through phone calls, text messages, and social media (Al-Mutawa et al., 2016; Centelles et al., 2021; Dressing et al., 2014; Lee & O’Sullivan, 2014; Sambasivan et al., 2019). Certain methods of cyberstalking that do not involve direct contact with the victim, such as impersonating the victim, accessing the victim’s online accounts, downloading data from the victim’s devices, or tracking the victim’s location, were less often noticed and/or reported by victims (Begotti & Maran, 2019). This could mean that true prevalence rates of these methods have not been identified, especially if they were perpetrated as part of a course of conduct of cyberstalking, but without the victim’s knowledge. Moreover, cyberstalking that is perpetrated through social media, for instance, checking someone’s private conversations, may not be recognized as cyberstalking by victims and considered as normal practice in intimate relationships (Brady et al., 2023; Montero-Fernández et al., 2023). Overall, victims may not always recognize the behavior they are experiencing as cyberstalking or be aware that the perpetrator is using covert methods. Future research must carefully consider the operationalization of cyberstalking to ensure it is accurately reported by victims, and where possible, use victim reports alongside information from perpetrators when drawing conclusions about the prevalence and nature of cyberstalking.
As well as the use of social media, perpetrators of cyberstalking used specific technologies such as anonymous text messaging services, location-based apps, and smart home technology to target their victims (Eterovic-Soric et al., 2017; Horsman & Conniss, 2015; Sovacool et al., 2021). The use of social media apps that share a person’s live location, such as Snapchat or dating apps, can increase an individual’s risk of cyberstalking victimization (Centelles et al., 2021). However, the detection and identification of perpetrators using these apps to conduct cyberstalking is hindered by perpetrators’ inclination to use false or anonymous accounts, and even if their accounts are frozen or removed, there are few effective measures in place to prevent perpetrators from creating new accounts. The fast-developing nature of technology and its ubiquitous presence in cases of cyberstalking means perpetrators’ use of specific technology is subject to continuous change and future research must not only maintain an up-to-date operationalization of cyberstalking to include these methods but also recognize how new technologies allow the negative effects of cyberstalking to permeate victims’ lives.
Limitations
The current study was limited by certain methodological choices. The terminology included in the database searches was identified through a preliminary search and examination of language used in published research, which was a method previously utilized by Kaur et al. (2021), however, some relevant terminology may not have been identified. Another potential limitation of the review is the exclusion of gray literature. While some gray literature could have provided relevant insight, this was not included due to the lack of peer review and consequent reliability. This approach is in line with PRISMA-P guidelines, which dictate that it is at the discretion of the authors whether to include gray literature in a systematic review. During the literature search, only one author conducted the main screening of studies; however, good inter-rater reliability of the screening was established on a sample of studies by two authors. Regarding the results of the literature review, some demographic factors such as age, socio-economic backgrounds, education, and professions of cyberstalking perpetrators were not discussed. These factors may provide relevant insight into who perpetrators of cyberstalking are and warrant further exploration.
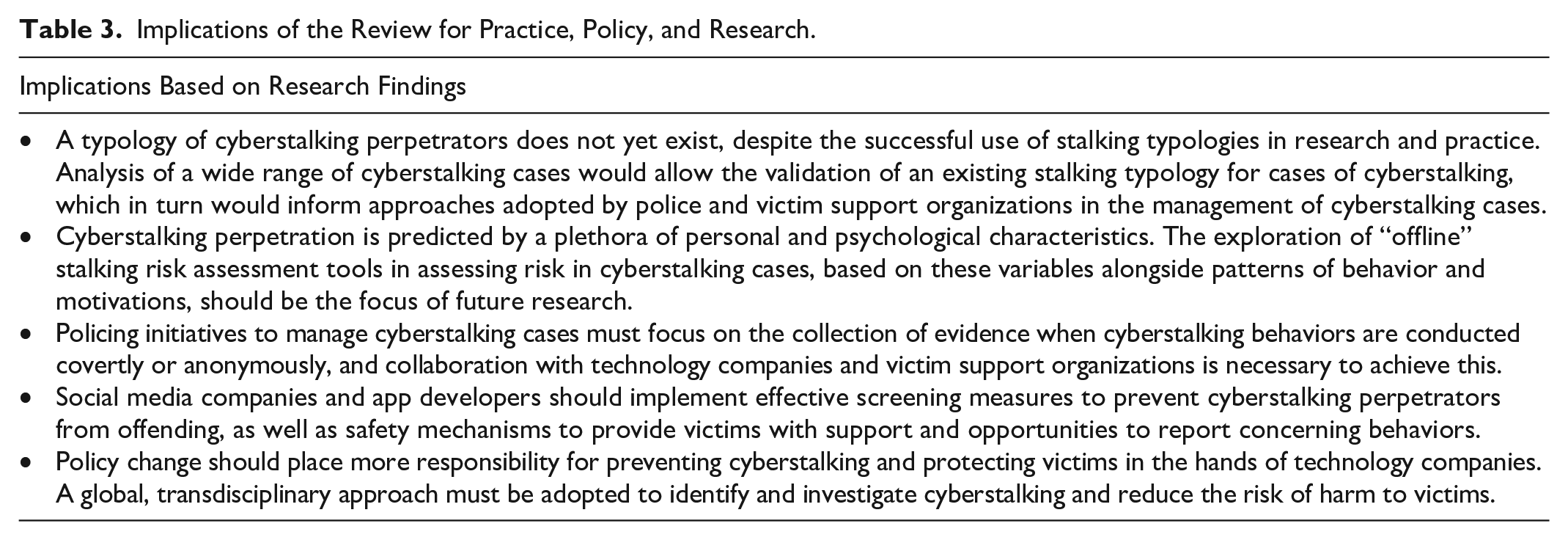
Implications for Policy and Practice
Police often fail to sufficiently identify cyberstalking behaviors, pursue arrests or charges, and protect victims (O’Shea et al., 2019). The further exploration of existing “offline” stalking risk assessment tools for use in cyberstalking cases, and the validation of a stalking typology for cyberstalking would allow authorities and professionals to identify risks posed to victims of cyberstalking and categorize perpetrators. Based on the similarities between findings from the literature highlighted in this review and the plethora of “offline” stalking research, it is unlikely that approaches to managing cases of cyberstalking would differ significantly to existing approaches to the management of “offline” stalking cases. A comprehensive understanding of the risk of stalking persistence, escalation, and continuation has allowed stakeholders to develop effective interventions to prevent further offending, including legal protective orders, supervision requirements, and victim safety plans, and the same could be achieved for cases of cyberstalking.
Notwithstanding, there are areas of policing and managing cyberstalking where further knowledge development could improve practice within the criminal justice system. For instance, this review also highlighted that perpetrators are known to post a victim’s information online, monitor their online activity, access their online accounts, and track their location, and much of this can be done covertly or anonymously. These findings are vital to consider for improving the identification and collection of evidence when behavior is conducted covertly or anonymously. For more effective evidence collection, a holistic approach to case management should be adopted by police alongside victim support organizations and technology enterprises (e.g., social media companies, app developers) to improve detection of concerning behaviors, encourage detailed record keeping of incidents by victims, enable the identification of a perpetrator’s online accounts and activity, and increase safety measures to protect victims from future harm. A transdisciplinary approach is necessary as cyberstalking is a crime that transcends physical limits and thus can have an international dimension, either due to the location of the perpetrator in relation to the victim or when requiring the cooperation of global social media companies. As such, the cooperation of technology companies must be mandated by policy change. For instance, the U.K. Online Safety Act (2023) holds online platforms accountable for removing illegal content, and age-inappropriate content for children. Similar policies which require technology enterprises to actively reduce cyberstalking on their platforms and assist authorities with investigations of cyberstalking should be informed by research and implemented.
Conclusion
This systematic literature review identified existing research into cyberstalking perpetrators and their methods of perpetration. Future research should continue to compare “offline” stalking and cyberstalking perpetration and victimization, thus identifying the utility of “offline” stalking risk assessment tools and typologies for cyberstalking cases. Additional potential risk factors, such as a perpetrator’s time spent online and technological ability, require consideration in the ongoing assessment and management of cyberstalking cases. The ongoing development of technology accompanied by the emergence of new methods of cyberstalking is inevitable, and researchers must endeavor to “keep up” with these new technologies. Collaboration, therefore, between researchers, stakeholders from the criminal justice system, victim support organizations, and technology companies is necessary to improve detection of cyberstalking perpetration and management of cases, and this must be mandated by policy change (Tables 2 and 3).
Summary of Critical Findings.

Implications of the Review for Practice, Policy, and Research.
Footnotes
Data Transparency
This review was planned and conducted in adherence to the PRISMA (preferred reporting items for systematic reviews and meta-analyses) standards of quality for reporting systematic reviews.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: The author received a graduate teaching studentship from the University of Kent.
