Abstract
In this study, we investigated the relation between the different stages of women trafficking (i.e. recruitment, entrance, accommodation, labor, and finance) and the structure of five criminal networks involved in women trafficking in the Netherlands (Ns ranging from 6 to 15). On the one hand, it could be argued that for efficiency and avoidance of being detected by law enforcement agencies, the network structure might align with the different stages, resulting in a cell-structured network with collaboration between actors within rather than across stages. On the other hand, criminal actors might prefer to collaborate and rely on a few others, whom they trust in order to circumvent the lack of formal opportunities to enforce collaboration and agreements, resulting in a core-periphery network with actors also collaborating across stages. Results indicate that three of the five networks were characterized by a core-periphery structure, whereas the two other networks exhibit a mixture of both a cell-structured and core-periphery network. Furthermore, using an Exponential Random Graph Model (ERGM), we found that actors were likely to form ties with each other in the stages of recruitment, accommodation, and exploitation, but not in the stages of transport and finance.
Keywords
Introduction
In the Netherlands, every year, around 5000 women of both Dutch and foreign origin fall victim to illegal trafficking. Approximately, 75% of these women end up being exploited involuntarily in the prostitution business, like sex clubs, window prostitution, or escort services (Nationaal Rapporteur, 2018). The trafficking of women for sexual exploitation purposes is one of the most widely known forms of human trafficking in Europe (Campana, 2016; Mancuso, 2014). In the Netherlands, two changes in legislation have indirectly facilitated women trafficking. First, the brothel ban was lifted in 2000, legalizing voluntary prostitution, which also extends to employing women who voluntarily work as prostitutes. As prostitution is in principal not prohibited, this opened up opportunities for the exploitation of women as prostitutes on a seemingly voluntary basis. Second, the adopted Schengen agreement, with most countries included from 2007 onward, allows members of the European Union to freely cross internal European borders. This has unintendedly facilitated women trafficking from the less prosperous countries, such as Bulgaria and Romania, to more prosperous countries, including the Netherlands.
There are two key aspects of women trafficking. First, women trafficking is mostly not an endeavor of a single individual, but consists of cooperation among a number of involved actors (cf. Aronowitz, 2009). This cooperation gives rise to a network among those responsible for women trafficking through which they achieve their goals. Social network analysis (SNA) provides a way to empirically map this collaboration by capturing individuals involved in criminal activities and their connections and relationships (Bichler and Malm, 2015; Diviák, 2020; Morselli, 2009, 2014). A social network approach makes it possible to describe and model the emergence of the structure of collaboration among a group of offenders from their interactions. This in turn allows to test various theories about criminal collaboration and organization.
Second, similar to smuggling and trading illicit commodities, such as drugs and arms, women trafficking can be captured by decomposing the underlying process into different successive stages, also called crime scripts or acts (Aronowitz, 2009; Brayley et al., 2011; Campana, 2016; Salt and Stein, 1997). Each stage represents a step in the chain along which women end up in the prostitution business. Some of the conceptualizations divide women trafficking into three main stages: (1) recruitment, (2) transportation, and (3) exploitation (Campana, 2016; Salt and Stein, 1997). Recruitment refers to the acquisition of control over the victim, transportation refers to the movement of a victim from a source location to a destination, and labor denotes the stage in which the victims are exploited in prostitution. A more refined distinction of stages (Jansen and Velting, 2014) also involves (4) accommodation of women in the host country (see also Mancuso, 2014) and (5) dealing with finances, such as laundering of earnings (see also Aronowitz, 2009). This latter approach aligns with the barrier-model used by the Dutch police, which aims to identify potential hurdles and obstacles to hinder and disrupt the process of women trafficking by creating barriers (Bottenberg et al., 2012). We use the barrier-model as a basis for a crime script analysis (Cornish, 1994; Dehghanniri and Borrion, 2019). Crime script analysis aims at mapping the steps necessary to commission the given criminal event. We combine both SNA and crime script analysis to investigate the intersections between scripts and networks, as the two approaches are complementary (Bellotti et al., 2018). This way, we can assess whether the resulting structure of women trafficking aligns more with the network or crime script perspective.
This study investigates the relation between the different stages of women trafficking (i.e. recruitment, transportation, accommodation, exploitation, and finance) and the structure of the social network of those involved in five cases of women trafficking networks in the Netherlands (Ns ranging from 6 to 15). Specifically, we are interested in the extent to which the different stages of the crime process are reflected in the structure of the criminal network. Doing so, our study addresses one of the issues in the studies of women trafficking, namely, the paucity of quantitative studies (Cockbain and Kleemans, 2019).
The remainder of this study is organized as follows. We first review extant research on women trafficking networks and formulate two competing perspectives on its structure; one argues that the structure reflects the stages of the criminal process and thus aligns with the crime script of the barrier-model, whereas the other one emphasizes the role of more general mechanisms in these networks. Subsequently, we describe our data and methodology. We, in turn, examine the two perspectives by analyzing both the structure of the five Dutch networks as well as the underlying mechanisms operating in them using statistical models for network data. We discuss the contribution and limitations of our findings afterward. Our study contributes to the research on human trafficking by empirically testing to what extent the criminal process perspective corresponds with the criminal network perspective.
Theory
Actors involved in criminal networks collaborate in order to achieve their collective goal, which in case of women trafficking, is generating profit from the exploitation of their victims. However, their collaboration is constrained by the fact that actors in criminal networks also try to avoid detection from law enforcement (cf. Diviák, 2019; Morselli, 2009). The fact that criminal actors need to restrict their actions modifies the way they act and interact with others, which is in turn reflected in the structure of the network. In this section, we formulate two competing theoretical perspectives on how actors involved in human trafficking might collaborate and how this affects the network structure. Although these two perspectives are competing because of the different emphasized theoretical assumptions, they are not necessarily contradictory. Despite quantitative evidence being rather scant in this area (Cockbain and Kleemans, 2019), we briefly situate each perspective in previous research.
Cell-structured network
The first perspective emphasizes that criminal actors aim to remain concealed and avoid detection by law enforcement agencies. In this view, criminal actors should aim for minimizing contact among each other and avoid the existence of redundant ties, as this increases visibility, and therefore, the risk of detection. In doing so, criminal actors would be motivated to restrict their collaboration to the task they are responsible for, leading to a clear task division into the successive stages of the crime script (Cornish, 1994; Dehghanniri and Borrion, 2019). Therefore, this perspective closely aligns with the crime script approach to women trafficking. The division and specialization of tasks are seen as critical for successful women trafficking operations (Salt and Stein, 1997). In network terms, actors would have tendencies towards homophily (cf. Grund and Densley, 2012, 2014) on the stages of the crime process, that is, they would be expected to work with others involved in the same stage more often than with actors involved in other stages. Note that the stages are not equally intensive in terms of resources such as time, effort, labor, or money. For instance, in the phase of transportation, the monitoring costs are lower as the time horizon is shorter, and less people need to be involved. This has been referred to as a process of scaling down (Campana, 2016). By contrast, in the phase of recruitment and exploitation, more criminal actors need to be involved to monitor women, thus increasing the amount of resources that need to be mobilized, referred to as scaling up (Campana, 2016). Therefore, actors in the stages where scaling up takes place may be more active and collaborative than in the scaling down stages.
These tendencies towards same-stage collaboration at the individual level would translate into a network structure that would align with the different stages of women trafficking. The predominant focus of collaboration between actors within the same stage would generate interconnected groups or clusters of actors corresponding to each stage. In the study of criminal networks, this is sometimes referred to as a cell-structure or a modular structure (DellaPosta, 2017; Newman and Girvan, 2004). In a cell-structure, collaboration between actors would be stronger within than across stages, hinting at task division and specialization (Campana, 2016) and also limiting redundant ties. This also implies the absence of disproportionately central actors responsible for keeping the network together, which reduces the risk of detection.
Some studies support the idea that women trafficking networks are cell-structured. Bruinsma and Bernasco (2002) found that women trafficking networks were characterized as a chain by small clusters of actors each responsible for a specific stage and linked to each other with a few instrumental relationships, resulting in a rather sparse network without many redundant relations. According to a study by Europol (2018), multiple human trafficking networks were organized or divided into operative cells. This finding is based on Nigerian, Vietnamese, Albanian trafficking networks, and criminal networks originating from the Czech Republic, Hungary, and Romania. Moreover, the Europol study documents a case of an Albanian network in which certain cells were in charge of specific phases in the criminal process. The criminal process perspective is also in line with previous research that uses crime script analysis. An example of such studies is a study of child sex trafficking and abuse (Brayley et al., 2011), which identified three stages (find, groom, abuse), and a study of two Italian human trafficking cases (Savona et al., 2014), which identified four stages (namely: recruitment, transportation, exploitation, aftermath).
Hence, the first perspective assumes that actors are able to organize themselves and develop a division of tasks in the foresight of the whole criminal process, optimizing the structure of their collaboration in order to avoid detection.
Core-periphery structure
By contrast, the second perspective argues that criminal actors, like humans in general, are hindered in their decision-making by a lack of information, time restrictions, and limited cognitive capacities (Simon, 1956; Snijders, 2013). This is exacerbated by the context of crime in which criminal actors have to deal with and collaborate in situations that involve high uncertainty and risks (Campana and Varese, 2013; von Lampe and Ole Johansen, 2004). Consequently, the rationality of criminal actors may be rather bounded often resulting in ad hoc and opportunistic decision making.
Trust may compensate for the absence of formal regulations and institutions to enforce cooperation in criminal settings. Therefore, criminal actors may prefer to collaborate and rely on a few others, whom they trust in order to circumvent the lack of formal control. As a consequence, many criminal collaborations are built upon their embeddedness within broader social settings (van de Bunt et al., 2014). In terms of actor-level tendencies, two network mechanisms may enhance as much trust as possible. The first mechanism is tie accumulation (de Solla Price, 1976; Diviák et al., 2019), which denotes the tendency of certain actors in the network to accumulate a high number of ties. The high amount of connections allows such actors to directly oversee and control their collaborators. The second network mechanism potentially enhancing trust is triadic closure (Coleman, 1988; Diviák et al., 2019; Grund and Densley, 2014). Triadic closure refers to the tendency of actors who share a common collaborator to also collaborate directly. In other words, it is a tendency to collaborate with collaborators of one’s own collaborators. Triadic closure implies that actors in a closed triad can oversee, control, and support each other, reducing the risk of defection and free riding.
The operating underlying mechanisms of triadic closure would result in close collaboration among a group of highly interconnected and central actors in the network who have a few ties with actors at the periphery of the network, forming a core-periphery network (Borgatti and Everett, 1999). The members of the core are densely interconnected with each other, frequently in closed triads. Furthermore, they are also relatively central. The core-periphery structure allows core actors to support and control each other, while they may only occasionally involve peripheral actors in order to carry out a task at hand (Diviák et al., 2018).
There is some evidence from prior research on human trafficking networks that supports the core-periphery perspective. In the case of a major trafficking ring between Nigeria and Europe studied by Campana (2016), a core-periphery structure was present with a large group of actors at the periphery of the network linked to a small group of actors forming the core of the network. The findings from Mancuso’s (2014) study also indicate a possible presence of a core-periphery structure, as the analysis reveals a considerable centralization around a group of highly central actors in a network of a Nigerian sex trafficking ring. Cockbain and colleagues (2011) studied two cases of child sex trafficking networks and found one of them to be heavily centralized around a few ringleaders.
To conclude, according to the first perspective, actors in human trafficking networks should display strong tendencies towards collaboration within the stages of the process, which should translate into a cell-structure at the network level. According to the second perspective, actors should display tendencies towards collaborating in such a way that enhances trust (via tie accumulation and closure), generating a core-periphery structure in human trafficking networks.
Data
In this study, we used data from five cases of women trafficking, which were all subject to police investigations. These cases concerned organized forms of human trafficking, which took place in the northern regions of the Netherlands in 2013 and 2014. Information about actors and their network was derived from transcripts of wiretaps, observational information, statements and interrogation of suspects, victims and witnesses, official reports, and charges by the police. Furthermore, information about characteristics and the network of suspects was complemented from the police database BlueView.
As the involvement of actors in different stages of women trafficking was the focus of our study, we only included actors with information about their involvement in any of the stages we had information. Although 25 actors were identified via BlueView as being connected to the persons who were initially part of the police investigation, it was not possible to ascertain their exact involvement in any of the stages or their exact ties to others. Thus, these actors could not be linked to any of the five stages. For these reasons, we decided to exclude these 25 actors from the analysis.
For each case, relations among actors were coded as either being present (1) or absent (0). The ties in our study represent whether the two actors were reported in the data sources as being seen together, mentioned as collaborating together, or in contact with each other. As all these activities are by definition mutual, the networks are symmetric consisting only of undirected ties.
We were also able to extract individual information about actors involved in our networks that we used as attributes in our analysis. We distinguished the roles of actors in the network and in which stage actors were involved. Roles were divided into two categories: pimps and facilitators (Valk, Kuipers and Weerd, 2012). Pimps were those actors who received and controlled (a substantial part of) the earnings of women and frequently exploited them. Facilitators were actors who helped and supported the pimps in the process of trafficking and exploiting the women. Finally, when the role of actors in the criminal network was unclear or ambiguous, we coded them as unknown. We coded for each actor their involvement in one or more of the different stages of women trafficking, following the stages from the barrier model used by the Dutch police (Bottenberg et al., 2012); recruitment, transportation, accommodation, exploitation, and finance. Based on this distinction, we are able to examine to what extent actors are involved in either one or multiple different stages. Finally, we also coded information about the sex, age, and nationality of actors. Nationality was coded into four categories: Dutch, Eastern European, Southern European, and others. This latter category was used as some nationalities were rare, which potentially could harm the anonymity of actors.
Cases
We first give a brief description of each case. Case A (N = 6) is a police investigation that focused on a woman who exploited an illegal escort service and recruited women from her country of origin with the help of five other active individuals. The exploited women worked as escorts and earned a minimum of money. Case B (N = 13) is centered around two brothers of whom one is in charge of an escort service, whereas the other was doing chores for him. During the investigation, several suspects from Eastern Europe were detected by the police, when they were recruiting women in their country and intending to traffic them to the Netherlands for prostitution. Case C (N = 15) received attention from the police after suspicious financial transactions that seemed to point at human trafficking. All money transactions ended up at the same person in Eastern Europe. The police suspected that this person recruited women for prostitution in the Netherlands. He received money from three contacts in the Netherlands. One of these contacts was the owner of six sex clubs in the Netherlands for whom women from different countries worked. Once the women entered the sex clubs, the owner took their passports and exploited them in forced prostitution. Case D (N = 15) started after a victim reported to the police. She declared that she had been a victim of a criminal organization involved in human trafficking which also forced women to assist with burglaries. The final case E (N = 9) is about an Eastern European family and friendship group, who take their girlfriends to work in the prostitution business in the Netherlands. Frequently, these women were forced in combination with physical violence to hand over their earnings. For each case, we depicted a network of the collaboration ties among actors and a separate network of the actors being linked to the different stages in which they were involved (see Appendix, Figures A1–A5).
Methods
Descriptive measures
We calculated four network-level measures. Two so-called cohesion measures were used for descriptive purposes: density and centralization (see e.g. Borgatti et al., 2013; Wasserman and Faust, 1994). Density denotes the ratio of observed ties to all the possible ties (the number of all pairs of actors). Density ranges from 0 (no ties present in the network) to 1 (all the possible ties are present). Centralization indicates to what extent the network is centered around a specific actor or a set of actors, who have a high number of connections. Centralization also ranges from 0 (equal distribution of ties in the network) to 1 (one actor has all the ties to everyone else).
The other two network measures indicate whether the networks in our study resemble cell-structures or core-periphery structures. With these measures, we can formally test the structure of the overall network for each case. Cell-structure was measured by first using the Louvain algorithm (Blondel et al., 2008) to detect subgroups and subsequently using modularity score (Newman, 2006), to measure to what extent the ties in the network are located within these subgroups. Higher scores of modularity indicate the existence of different subgroups in the network with a high number of ties within the groups and a minimum of ties between the groups. A value of 0.3 is usually taken as a thumb rule for indicating a clear modular or cell-structure (DellaPosta, 2017). Core-periphery fit was calculated using the categorical core-periphery routine in UCINET (Borgatti et al., 2002) to examine to what extent the network is characterized by a core of highly interconnected actors with relations outside the core, who themselves are not connected with each other (Borgatti and Everett, 1999). In the core-periphery routine, the observed network is iteratively rearranged until it reaches the best possible core-periphery structure, which is subsequently correlated with an ideal core-periphery structured network of the same size. Therefore, high values of the correlation indicate a strong core-periphery resemblance.
We also provide frequencies of the individual attributes in each network together with the average degree of each actors, which indicates the average amount of ties per actor in the network. In order to visualize the involvement of actors in different stages as well as their involvement in multiple stages, we used the so-called upset plot (Lex et al., 2014), which utilizes well-known bar plots in a way that allows to depict multiple overlapping categories. The depiction of frequencies within single stages and their various combination allows us to assess how labor-intensive each stage in the crime script is and what is the involvement of actors in them. Doing so, we leverage the quantitative information to describe to what extent the stages align with the crime script.
Statistical models
To understand which underlying mechanisms brought about the structure of our observed network, we tested the effects of individual-level tendencies of actors to form ties using an exponential random graph model (ERGM; Lusher et al., 2013). ERGMs represent a class of statistical models specifically suited for network data. ERGMs rely on simulations in order to disentangle the effects of theoretically specified mechanisms on the formation of ties in the network. Specifically, we utilized a multi-group estimation procedure by combining all five networks in one larger network with structural zeros separating them (Kalish and Luria, 2013). Structural zeros make the ties across different networks impossible during the simulations that are used for the estimation. This allows for the estimation of a model for multiple independent networks that would otherwise be too small to be amenable to an ERGM analysis on their own. We conducted the analysis using the MPNet software package (Wang et al., 2009).
In ERGM, the mechanisms of interest are operationalized by configurations. Specifically, we examine four endogenous network effects, the effect of background characteristics of actors, and involvement in the different stages of human trafficking. For the endogenous network effects, we included the edge effect, which indicates the presence of ties. This effect is analogous to an intercept in standard logistic regression. We also included the so-called alternating star (AS), alternating triangle (AT), and alternating two-path (A2P) configurations. AS models the accumulation of ties mechanism. AT captures the mechanism of triadic closure (three fully interconnected actors). A2P is used as a lower-order control effect for triadic closure, as it models the presence of open triadic structures. In order to control for different sizes of our networks, we also included a specific edge effect for each network to capture the influence of larger networks in our sample on the estimation.
For both the individual background characteristics (i.e. sex, role, and nationality) and stages (i.e. recruitment, transportation, accommodation, exploitation, and finance), we included two types of effects: activity and interaction. The activity effect indicates to what extent actors with a certain characteristic or involvement in a stage are likely to have more ties. The interaction effect models whether actors with similar characteristics or involvement in the same stage are likely to form a tie with others with whom they share the characteristic or involvement in a stage.
Finally, we assessed the goodness of fit of our model by simulating a sample of networks from our model and comparing it with the observed networks. The model is deemed adequately fitting if it captures the properties of the data reasonably well.
Results
Descriptive statistics
First, we discuss the descriptive statistics for each network (see Table 1). The density of the networks is partially related to the size of the networks, ranging from .47 in the smallest network (case A) and .10 in one of the larger networks (case D). In this latter, network centralization is also the lowest (.11), pointing at a rather sparse network with few connections between actors. The other networks show higher levels of centralization varying from .33 (case A) to .63 (case B), suggesting that ties in these networks are more concentrated around particular actors. The average number of ties per actor varies from 0.89 (case E) to 2.67 (case C).
Descriptive statistics for each case.
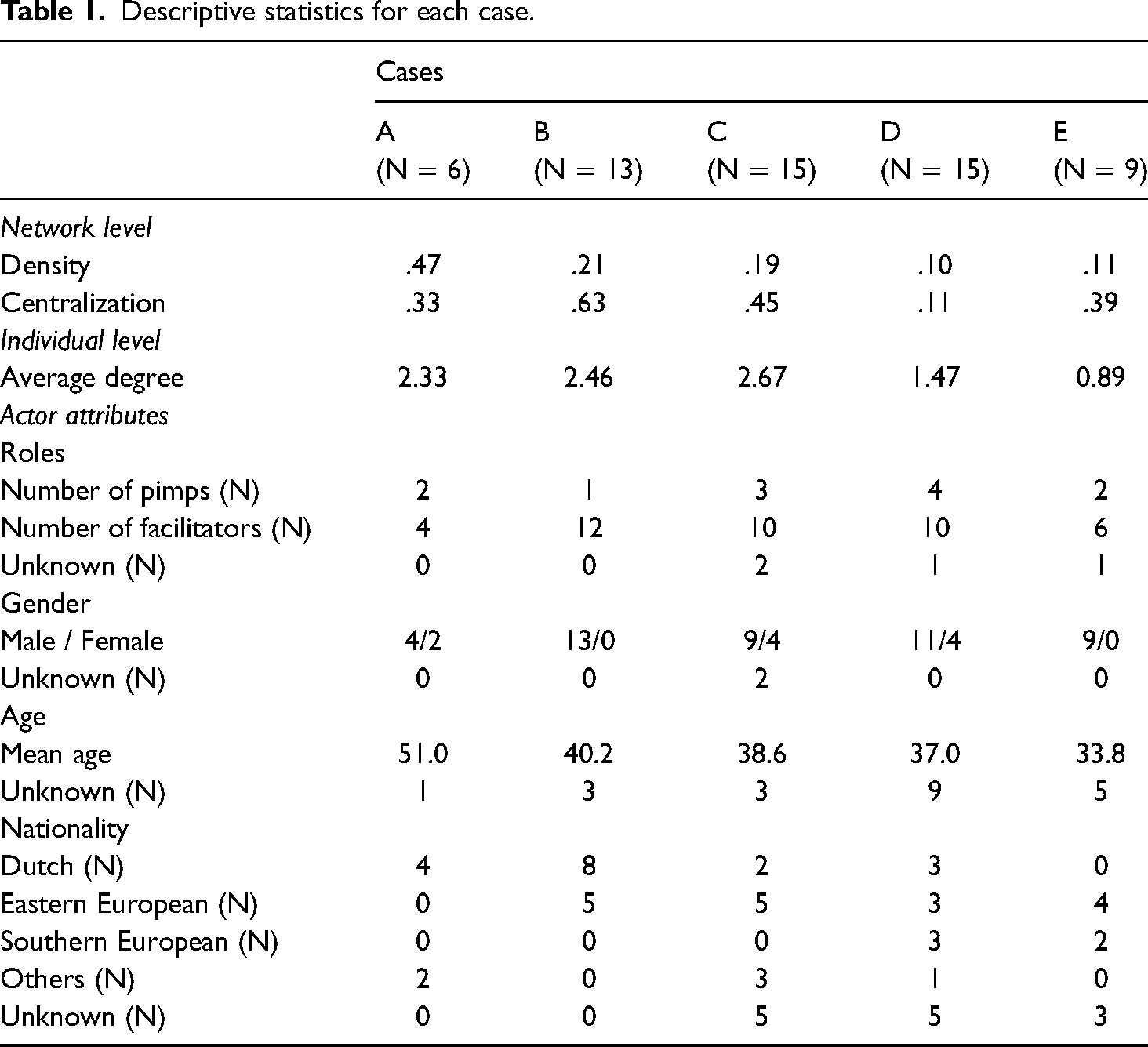
We also distinguished between pimps and facilitators in the network, revealing that in each network the number of facilitators exceeds the number of pimps. Although women form a minority in these networks, they do participate in three of the five networks (cases A, C, and D). Yet, the descriptive data for age should be treated with some caution in view of missing data. The ‘youngest’ network is case E (average age = 33.8) and the ‘oldest’ network is case A (average age = 51). Finally, all networks are composed of actors from at least two different nationalities, hinting at the international character of women trafficking.
In Table 2, we describe the information about actors’ involvement across different stages of women trafficking as well as the network-level measures for cell-structure (modularity) and core-periphery. Starting with the different stages, it appears that on average actors are involved in one and a half stages, with case A as an exception with actors involved in 2.5 stages on average. Furthermore, the range of the number of stages indicates that involvement in multiple stages varies from one to five across all five networks.
Descriptive statistics for stages and network characteristics.
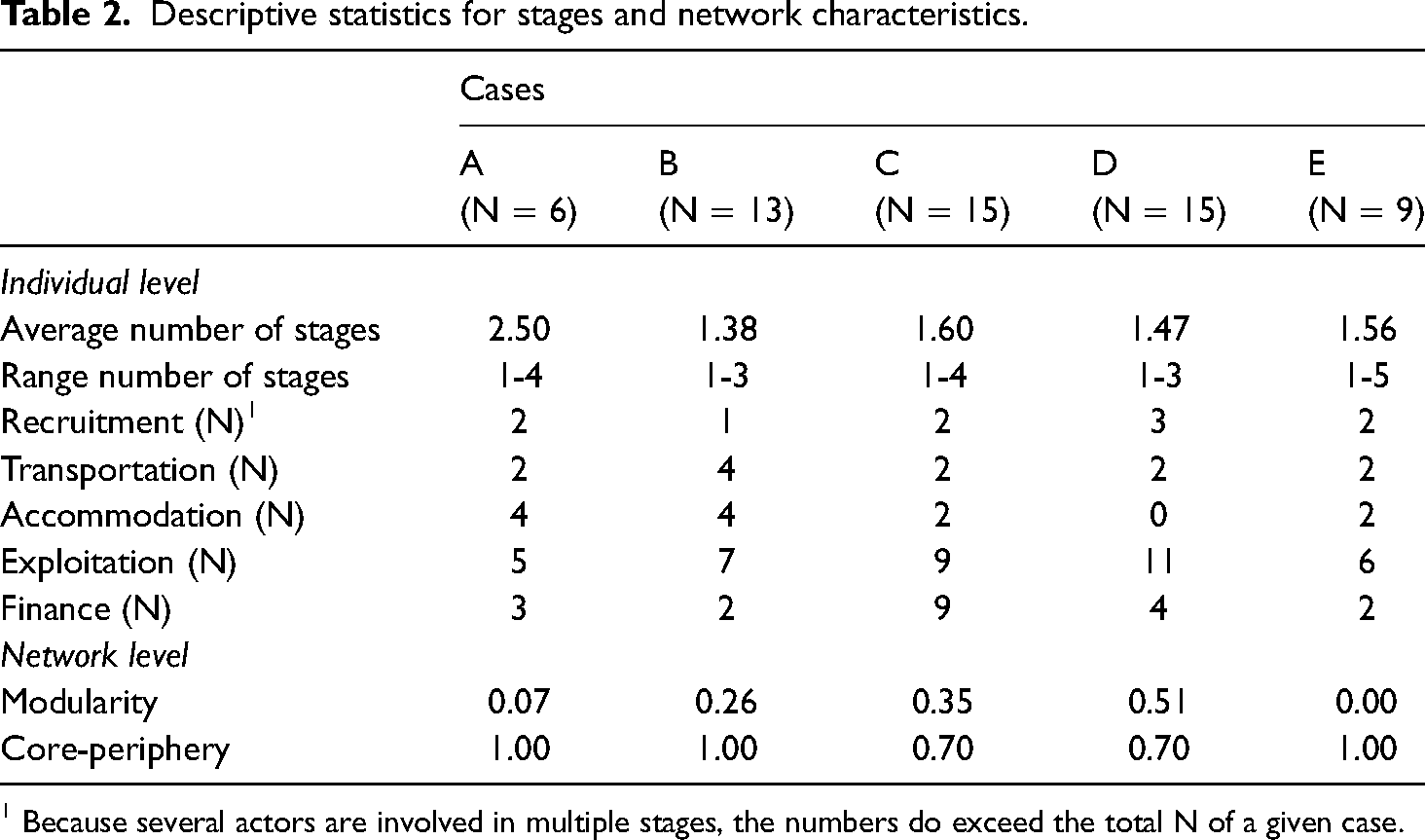
Because several actors are involved in multiple stages, the numbers do exceed the total N of a given case.
In order to analyze the crime script of the whole criminal process, we depicted the number of actors involved in each stage and the distribution of actors across involvement in different combinations of stages using the upset plot (Figure 1). The horizontal bars for each stage represent how many actors in total are involved in the given stage. As it can be seen, the lowest number of actors participated in the recruitment stage and the highest number in the exploitation stage. The vertical bars in the upset plot represent how many actors are involved in the given intersection of stages (indicated below each bar). Most actors were involved in only one stage, particularly in the exploitation stage (18 actors). The most frequent combination of the two stages is the combination of exploitation and finance with seven actors in this intersection. In the case of three stages, the intersection of exploitation, finance, and accommodation with three participating actors is the most frequent combination. Only four actors in total were involved in four stages and only a single actor was involved in all the five stages. Overall, the upset plot indicates that a substantial portion of actors follows the crime script of the barrier-model. However, it is by far not universal, as there are actors and activities that cut across different and non-successive stages of the criminal process.
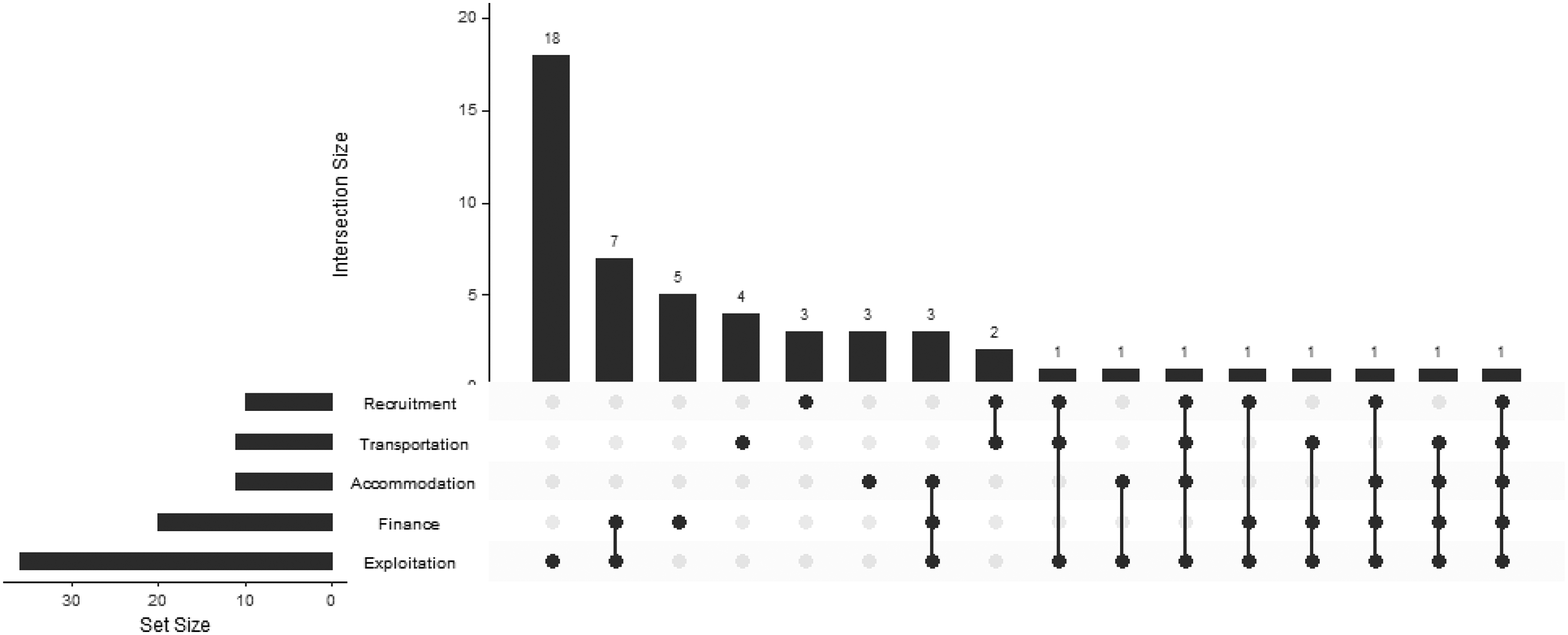
Upset plot of frequencies of different stages and their intersections.
To examine the network structure, we looked at whether the networks could be characterized either as a cell-structure or as a core-periphery structure (Table 2). Three of the networks were identified as having a clear core-periphery structure (case A, B, and E, core-periphery fit = 1.0), but not as a cell-structure, whereas case B exhibits elements of both a cell-structure and core-periphery. The networks in cases C and D also appear to be characterized by a core-periphery structure (both .7), but at the same time, exhibit features of a cell-structures as evidenced by modularity scores of .35 and .51, respectively. This indicates that the two largest networks exhibit a mixture of both core-periphery and cell-structure. Visual inspection of the networks confirms this (see Appendix, Figures A1–A5).
Exponential random graph model results
Table 3 reports the results of the ERGM that we applied to test the underlying mechanisms accounting for the structure of the five women trafficking networks. Looking at the network effects, the edge effect is negative with a high standard error indicating a non-significant effect. Of the remaining network effects, only the A2P was statistically significant. The A2P effect has primarily been included as a lower-order control for the effect of triadic closure (AT), but its positive sign together with the non-significant AT effect indicates that actors in the networks tend to create open two-paths (and thus to share some collaborators), but do not close them into full triangles. The insignificant AS effect suggests no evidence for certain actors to have the tendency to accumulate ties. Therefore, we found no evidence for the network mechanisms facilitating trust by means of triadic closure or tie accumulation. Regarding the actor background characteristics, no statistically significant effects were found for neither the activity nor interaction effect for gender, the role of actors, or nationality on the formation of ties within the networks.
Results of the exponential random graph model for all five cases.
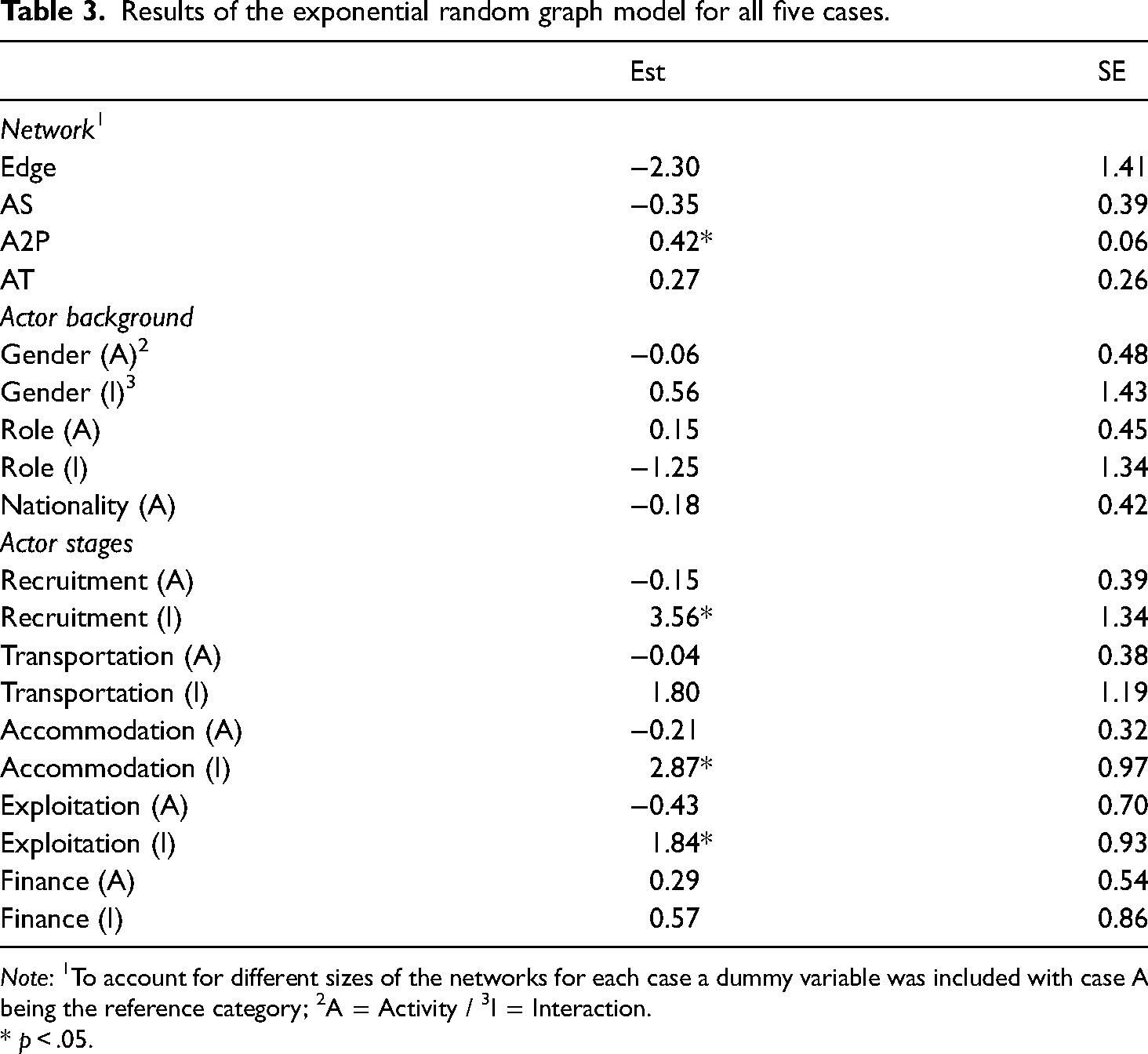
Note: 1To account for different sizes of the networks for each case a dummy variable was included with case A being the reference category; 2A = Activity / 3I = Interaction.
* p < .05.
Finally, we tested the activity and interaction effects for each of the five stages of the women trafficking criminal process. None of the activity effects turned out statistically significant, suggesting that there is no stage in which the actors would be more or less likely to create ties than in others. As for the interaction effects, we found statistically significant effects for the stages of recruitment, accommodation, and exploitation. All these effects are relatively strong and positive. This means that actors involved in these stages were much more likely to collaborate with others involved within the same stages, all else being equal in the model, hinting at a higher need for collaboration and coordination in these stages.
None of the dummy variables (not shown in Table 3, available upon request) controlling different activities of actors in different networks turned out to be statistically significant, suggesting that none of the networks is significantly different from others with regard to the presented model. Finally, we also conducted a goodness of fit assessment by simulating a sample of 10,000 networks from the model and comparing the properties of this distribution to our data on 128 effects available in MPNet. None of these effects display a significant deviation of the simulated distribution from our data, indicating an adequate fit of the model (results available upon request).
Discussion
We formulated two competing perspectives on women trafficking networks. The first perspective argues that the network structure aligning with the crime script decomposed into five different stages, resulting in a cell-structured network with more ties among actors within than across stages. The second perspective argues that criminal actors are hindered by limited knowledge and information, resulting in actors who prefer to collaborate with a small group of trustworthy persons as reflected by a core-periphery network. We investigated both views by comparing network-level indicators of cell-structures and core-periphery structures and by formally testing the mechanisms that enhance criminal collaboration using an exponential random graph model. Results indicate that three of the five networks display a core-periphery structure, whereas two other, somewhat larger, networks exhibit a mixture of both cell-structure and core-periphery structure.
Furthermore, using statistical models for network data, we found that actors within the stages of recruitment, accommodation, and exploitation tend to form ties with others involved in the same stage. This was not found for the stages of transportation and finance. As for the endogenous network mechanisms, we found no mechanism, but the tendency to share common collaborators to significantly shape the structure of the network. Therefore, our results are mixed providing partial support for both perspectives. At the level of individual actors, they support the perspective suggesting that the network aligns with different stages. At the level of the network, our results are more in favor of the perspective emphasizing core-periphery structures.
Networks involved in women trafficking may contain elements of both cell-structure and core-periphery structure, which also partially varies by stages. This nuanced finding aligns with Campana (2016) who studied the involvement of different actors in three stages of women trafficking (i.e. recruitment, transportation, and exploitation) and decomposed involvement of actors depending on the number of victims involved. In line with the processes of scaling down and scaling up, Campana found actors involved in the scaling up stages (e.g. recruitment) to be more active than actors involved in scaling down stages (e.g. transportation).
We defined the five stages of the women trafficking process based on the barrier-model used by the Dutch National police (cf. Bottenberg et al., 2012). We used this definition for script analysis, and subsequently, combined it with the network perspective, which allowed us to investigate in which stages and how (i.e. within a stage or in between two stages) are the actors cooperating. Our findings gained from the upset plot and the ERGM analysis indicate that while some portion of the collaboration was happening within specific stages or between successive stages, there is also a lot of evidence for collaboration unfolding outside of the script (i.e. across non-successive stages).
In the context of our study, it appears that in the stages of recruitment, accommodation, and exploitation, actors tend to collaborate with others involved in the same stage. This can be explained by the scaling up process, as these stages require more monitoring of the exploited women and are more intense in terms of the logistics and thus they require the involved actors to collaborate more closely. In this regard, our findings align with those by Mancuso (2014) in showing networks that are relatively centralized around a group of key actors.
One reason for the differences between networks could be related to their size. The networks with a combination of both cell-structure and core-periphery structure were the largest. Salt and Stein (1997) argued that the larger the organization of human trafficking, the more likely it is that centralization will occur with a few actors managing the network (Campana, 2016: 69–70). Once the network has grown, tasks can be differentiated, more different roles can be identified with more specialization (Aronowitz, 2009). When networks are smaller, members tend to participate in several or all steps of and to fulfill a number of roles in the operation (Hesseling, et al., 2001). Analogously, some of the differences between our networks may be because of the different kinds of businesses they engaged in to exploit their victims. The differences between more visible forms of prostitution (e.g. sex clubs) and less visible forms of prostitution (e.g. escort service) maybe also because the latter forms are more difficult to detect. More research is needed to establish whether there are genuine differences between the types of businesses or between networks of different sizes.
Limitations and future research
One obvious limitation of our data was the small size of the networks. Related is the distinction made by Aronowitz (2009), who made a typology of organizations involved in human trafficking with individual traffickers, small groups of criminal actors, and large trafficking organizations. Our data fit within the second category of a small group of criminal actors. At the same time, it does not exclude the possibility that these networks were part of larger trafficking organizations, which were, however, not subject to a police investigation. This also relates to a limitation of data based on police records. These type of data are always limited in the sense that it reflects what police and law enforcement agencies know. Our finding that most actors were involved in the stage of exploitation can partly be attributed to the fact that the exploitation stage is the most visible stage as well as the usual starting point for investigations by law enforcement agencies.
We were not able to further dive into the different roles of criminal actors within these women trafficking networks because of a lack of specific information. However, further research could benefit from a closer inspection of the relations prostitutes might have with pimps (Morselli and Savoice-Gargiso, 2014) as well as a more detailed description of all types of roles in these networks (Aronowitz, 2009). Similarly, we found that women were actively involved in three of our cases, which raises the question of the specific roles women may fulfil in women trafficking networks (Diviák et al., 2020). Previous research suggests that the roles of women may be categorized into three different categories (Siegel and de Blank, 2010; Wijkman and Kleemans, 2019; Mancuso, 2014): supporters, partners-in-crime, and madams. ‘Supporters’ are women whose activities are limited to recruiting, guarding, controlling, or instructing other women (prostitutes). ‘Partners-in-crime’ are women who voluntarily take up women trafficking together with their partner(s), such as their spouse, boyfriend, or business partner. ‘Madams’ are women who lead the criminal organization and plan the phases and activities. How these roles of women translate into the network structure is a question for future research, such as the study of Mancuso (2014) that demonstrates that some madams in a Nigerian sex trafficking network hold the positions of brokers. Brokerage roles may also be crucial in terms of disrupting these networks (cf. Morselli and Roy, 2008), as removing brokers bridging between different stages could potentially break down the network as a whole.
Conclusion
Women trafficking is in many cases a group endeavor with cooperation between actors, resulting in a criminal collaboration network. Women trafficking can also be understood as composed of different stages that together constitute a crime process. We examined the relation between the structure of five criminal networks involved in women trafficking and its different stages. We formulated two competing perspectives on the structure of these networks – the first perspective emphasizing the alignment of the network structure with the stages and the other emphasizing the effect of more general network mechanisms on the network structure. For three of the analyzed networks, the results are more in line with the latter perspective, whereas the two remaining networks present mixed evidence. The fact that the networks exhibit core-periphery structures and that actors are more active in the stages of recruitment, accommodation, and exploitation can also be used in designing interventions and policies against women trafficking networks.
There are multiple available intervention designs that may be derived from our results. Removing brokers between successive stages only incapacitates the network as it relies on the brokers to be connected. However, this is not always the case. As our findings indicate, some networks may exhibit strong core-periphery structures. For such networks, targeting the core actors with monitoring and subsequent arrests may be a more efficient strategy for law enforcement. It is important to note that in a core-periphery structure, actors in the core are structurally equivalent and so removing only a part of the core may not be enough to dismantle the network as the remaining core actors have structural positions that allow them to quickly substitute for the removed actors.
The structure of the network represents an endpoint of the criminal process, which further complicates the situation for the law enforcement agencies. During an undergoing investigation, law enforcement may not have the entire picture of a network to point out its core. In this regard, we may utilize our finding that the stages of recruitment, accommodation, and exploitation are the stages within which statistically significantly more interactions take place. Since the amount of activity within these stages is a strong driver of the network formation and it also increases the visibility of the network in these stages, law enforcement agencies may leverage the information about the network from these stages as an approximation of the network structure. However, both the findings about core-periphery structure and the most visible stages are subject to further research and should in no way be taken for granted in other cases of human trafficking networks. Every attempt of intervention or policy aiming at these networks should first assess their structure and tailor the intervention to it, while weighing in potential negative unintended consequence interventions and policies may trigger, especially with regard to the victims of human trafficking.
To conclude, our study demonstrates that the social network perspective can be fruitfully combined with the crime script perspective to shed more light on human trafficking networks. Despite the limitations of the data, our findings may help to uncover these networks and provide law enforcement agencies with evidence-based suggestions for interventions.
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
