Abstract
This article reports findings from the first study to investigate smartphone sharing in intimate relationships in Australia. Efforts to strengthen cybersecurity have been hindered by a lack of knowledge about the prevalence and dynamics of smartphone sharing, resulting in blind spots in cybersecurity design and policy. Based on a survey of 967 Australian adults who use smartphones and have been in an intimate relationship, we found that 70% share access to their mobile phones with their intimate partners. This high rate of shared access indicates that one-user, one-device threat models are inadequate for promoting cybersecurity in realistic use conditions. Such models are particularly ill-suited to intimate relationship contexts where the parties are more likely to share devices than not. Our findings provide previously unavailable baseline information about mainstream smartphone-sharing practices. This evidence can be used to improve privacy protections for telecommunications users in Australia and elsewhere.
Introduction
This article reports findings from the first study of Australian couples’ everyday smartphone-sharing practices. Our interest in this matter is underpinned by the recognition that a substantial amount of cybercrime is committed by people known to the victim, using mainstream communication devices and services. Following feminist accounts of trust as accepted vulnerability, routine device sharing within intimate relationships may feel unremarkable at the time, yet still create conditions for misuse (Hardley et al., 2021). Consensual smartphone sharing may enable technology-facilitated abuse of current and former intimate partners, encompassing intrusive behaviours like contacting survivors’ social networks; surveillance activities such as monitoring and stalking, or image-based sexual abuse (Dragiewicz et al., 2018b, 2019, 2021, 2023; Powell and Henry, 2017; Singh, 2022; Woodlock, 2017); and identity crimes including impersonation, identity theft and fraud (Dragiewicz et al., 2019; Koops et al., 2009).
We used a survey of 967 Australian adults to examine smartphone and credential sharing, smartphone cybersecurity and privacy practices, and the factors influencing individuals’ decisions to allow or restrict partner access to these devices. These practices are situated within a broader technological landscape shaped by the rapid global adoption of mobile phones. Mobile phones are the fastest-spreading communication technology in history (Castells et al., 2006). They surpassed the number of landlines on Earth in 2002, and by mid-2022, there were more mobile phone subscriptions than people globally (Donner, 2008). By 2023, 69% of the global population, approximately 6.7 out of 7.4 billion people, owned a smartphone (Lariccia, 2023). Australia has one of the highest smartphone use rates per capita. A total of 87% of Australians aged 16–64 years own a smartphone. Comparatively, only 75% own a laptop or desktop computer, and 46% own a tablet (Hughes, 2023). Notably, more than 10% of Australians are mobile-only users, meaning they have a mobile phone with a data allowance but no access to a fixed broadband connection. The percentage of mobile-only users is increasing in Australia, with people living in very remote areas (32.6%), First Nations people (21.3%) and people in the lowest income brackets (20.7%) overrepresented among mobile-only users (Thomas et al., 2023: 6).
Secure access to smartphones is more critical than ever due to the ubiquity of mobile-centric services. In Australia, essential private sector and government services are increasingly delivered via mobile interfaces. For example, almost half of Australians aged 16–64 years use a banking or other financial mobile app each month, while around one-third use a mobile payment service monthly. Although Australians spend an average of almost 3.5 hours using smartphones daily (WeAreSocial and Meltwater, 2024), previous research has not investigated whether any of this use is via shared devices in the general population.
In Australia, the Australian Cyber Security Centre (ACSC) leads government efforts to improve cybersecurity. Cybersecurity threat models are used to ‘analyse technology systems and services to better understand how that system or service might be attacked or otherwise fail, and the measures or controls needed to manage the risk posed by such attacks or failings’ (National Cyber Security Centre, n.d.). The ACSC (2024b) threat model is based on skilled, distant, ‘malicious cyber actors who continue to target Australia’s networks’ (p. 1) including government and industry. For example, the ACSC (2024b) website says, State-sponsored cyber actors persistently target Australian governments, critical infrastructure and businesses using evolving tradecraft. These actors conduct cyber operations in pursuit of state goals, including for espionage, in exerting malign influence, interference and coercion, and in seeking to pre-position on networks for disruptive cyber attacks. (p. 12)
This focus is consistent with dominant cybersecurity models globally. However, a growing body of research has called for a more holistic approach to cybersecurity that takes the full range of threats into account (Doerfler, 2019; PenzeyMoog, 2021; Slupska and Tanczer, 2021; Wu et al., 2022). This study builds on calls for a comprehensive approach that includes greater attention to cybersecurity threats from people we know, including partners, friends and family.
In Australia, the eSafety Commissioner has advocated for technology companies to shift towards Safety by Design. Safety by Design focuses on minimising potential harms from technology by anticipating and mitigating them before they occur, rather than reacting to misuse after the fact. The eSafety Commissioner argues that ‘the burden of safety should never fall solely upon the user’ (eSafety Commissioner and Australian Government, 2019). Instead, potential harms from technology should be understood, assessed and addressed during the design phase. A key component of safety by design is identifying and anticipating potential interpersonal threats to technology users from people they know. Everyday practices like device sharing can later become mechanisms of control or surveillance, making proactive design essential. As PenzeyMoog (2021) put it,
Literature review
The research relevant to mobile phone sharing is cross-disciplinary. Researchers from Human–Computer Interaction (HCI), User Centred Design (UCD), computer science, criminology, sociology, law, communication and digital media studies approach this topic from a range of orientations. Prior feminist work situates gender-technology-trust relations in the quotidian use of mobile media, underscoring the value of baseline data on ordinary sharing practices (Hardley et al., 2021). Building on this, Cumiskey’s research on mobile media and gendered safety demonstrates how smartphones are imagined as protective tools, fostering trust while introducing new vulnerabilities through practices such as geolocation sharing (Cumiskey, 2010; Cumiskey and Brewster, 2012; Hardley et al., 2021). Hardley, McGrane, and Richardson (2021) extend this discussion by examining how mobile and social media practices shape gendered experiences of trust and risk, emphasising the ambivalence of technologies that simultaneously enable intimacy and surveillance. Similarly, Powell and Henry’s (2017) work on technology-facilitated abuse situates these dynamics within broader patterns of coercive control and gendered violence. Together, this scholarship highlights the paradox of intimacy and risk in everyday mobile practices and underscores the need for cybersecurity frameworks that account for interpersonal misuse. This interdisciplinary literature review focuses on two central areas of research pertinent to this study: credential and device sharing and cybercrime.
Credential and device sharing
Dominant cybersecurity paradigms employ a one-user, one-device model. Most devices, from mobile phones to computers, provide default access to all content on a device once a user is logged in (Jacobs et al., 2016). Where individual applications require authentication, this can often be achieved via credentials saved on the device. The cybersecurity advice accompanying this reality is not to share passwords. Nonetheless, many people do share credentials and devices. More than two decades of research have found that credential and device sharing is prevalent among people who know one another.
Password and device sharing is common in workplaces, families and couples (Baker and Carreño, 2016; Doerfler et al., 2024; Ferreira et al., 2011; Jacobs et al., 2016; Lin et al., 2020, 2021; Matthews et al., 2016; Park et al., 2018; Sambasivan et al., 2018; Singh et al., 2007; Vogels and Anderson, 2020). Most research to date focuses on password sharing and consistently indicates that this practice is widespread. For example, the Pew Research Center reported that 75% of American adults share their mobile phone passwords with their intimate partners. More specifically, a high percentage of Americans who are married (79%), cohabiting (74%) or in a committed relationship (58%) report having given their spouse or partner the password for their cell phone (Vogels and Anderson, 2020: 13). People share passwords and devices for various reasons. Some do so for convenience (Ferreira et al., 2011; Singh et al., 2007), while others do so to show trust in or demonstrate fidelity to partners (Baker and Carreño, 2016; Doerfler et al., 2024).
Kaye (2011) found that one-third of 122 survey respondents from multiple countries had shared their email passwords with others, and one-quarter had shared their Facebook password, mostly with partners and friends. Kaye identified couples as a key context for understanding credential sharing, finding that people with partners were significantly more likely to share than those without. Kaye’s respondents indicated that partners often share bank account details and PINs. Others suggested that their partners could likely figure out their passwords if they wanted to, based on knowledge gleaned from close relationships. Kaye observed that people gave thoughtful accounts of their reasoning behind password sharing, noting intimacy in close relationships and increasingly onerous password requirements as contributing factors.
These findings highlight how personal and relational dynamics shape credential-sharing practices – often in ways that diverge from idealised cybersecurity norms. Cybersecurity can be compromised when policies and recommended practices are not well-suited to real-life conditions. This finding is reinforced by research on the social functions of sharing. For example, in an early study investigating the social uses of mobile phones, Weilenmann and Larsson (2001) used an ethnographic approach involving public observations of mobile phone use by teenagers in Sweden to understand ‘the everyday, actual use of this technology’ (p. 92). They concluded that, contrary to the dominant understanding of mobile phones as individual devices used for communication with distant interlocutors, mobile phones were frequently shared among friends. They noted that sharing could be minimal, involving sharing content without sharing the phone itself, or hands-on, wherein multiple people handle the phone. Ultimately, Weilenmann and Larsson concluded that the mobile phone was a collaborative rather than an individual resource.
Australian scholars have also investigated the social aspects of mobile phone and credential sharing. Singh et al. (2007) used a qualitative study of 108 Australians to investigate how married and de facto couples, Aboriginal users and people with disability share online banking passwords. They found that the frequent violation of prohibitions on password sharing is due to ‘the lack of fit between security design and social and cultural practice, rather than a lack of security awareness’ (p. 476). Accordingly, they argued that individual-user-centred approaches to cybersecurity are inadequate. Technology design needs to shift to centre social and cultural norms and practices in order to accommodate the ways in which people actually use applications and services (Singh et al., 2007). Similarly, Rennie et al. (2018) found that device and credential sharing are common in remote Aboriginal communities. They reported widespread circulation of mobile devices and credit, with 80% of participants primarily using their own devices and 57% also using others’. In addition, 72% reported allowing others to use their devices, typically on a voluntary basis. As the authors observed, ‘the tools and platform features for managing online privacy do not necessarily accord with the relatedness that characterises social life in Aboriginal communities’ (p. 6).
Cybercrime
Despite Australia’s focus on threats to national infrastructure, government and companies, the financial cost of cybercrimes against individuals is increasing faster than that for businesses (ACSC, 2024b). The most common types of cybercrime affecting individuals were identity fraud (26%), online shopping fraud (15%) and online banking fraud (12%) (ACSC, 2024b: 12). While these types of cybercrime are particularly vulnerable to intimate threats and have been identified in research on technology-facilitated domestic violence (Slupska and Tanczer, 2021), the ACSC’s
Technology-facilitated abuse is a key component of cybercrime that is often a secondary focus of cybersecurity policy and practice compared with stranger danger. Technology-facilitated abuse by current and former intimate partners is a ubiquitous part of coercive control. As Singh (2022) put it, ‘The technologies that are generally seen as ways of connecting, become technology-facilitated abuse in family violence’ (p. 8). A survey of Australian domestic violence services found that 99% of professionals reported having clients who had experienced technology-facilitated stalking and abuse (Woodlock et al., 2020). Technology-facilitated domestic violence, stalking, identity crimes, image-based sexual abuse and financial fraud are frequently committed by current and former intimate partners (Dragiewicz et al., 2019, 2020, 2021, 2022; Powell and Henry, 2017; Singh, 2022; Woodlock, 2017; Woodlock et al., 2020). These types of abuse may be enabled by shared smartphone access, with consequences often remaining latent during the relationship and only becoming apparent after trust has been betrayed (Hardley et al., 2021).
Our study extends the evidence base on mobile phone use practices by providing population-level prevalence data on smartphone sharing in intimate relationships. Whereas prior research centres power dynamics and harms of digital abuse (Dragiewicz et al., 2019, 2020, 2021, 2022; Powell and Henry, 2017; Singh, 2022; Woodlock, 2017; Woodlock et al., 2020), our findings identify commonplace sharing practices that can function as preconditions for smartphone misuse. While consensual sharing may be unremarkable during the relationship, risks may be present all along or when the nature of the relationship changes. Baseline phone-sharing information is critical for understanding how normative behaviours intersect with technology-facilitated abuse and other forms of cybercrime. Everyday phone-sharing and privacy behaviours are essential knowledge for informing Safety-by-Design and interpersonal threat modelling.
Hand et al. (2009) reviewed the use of technology in post-separation abuse, noting how abusers use access to their partners’ mobile phones and accounts to engage in surveillance and coercive control. Hand et al. (2009) described how abusers may access their targets’ mobile phones and accounts surreptitiously or demand access to review text messages, calls, voicemails, emails, movements and online activity. Woodlock (2017) surveyed 152 domestic violence advocates and 46 victims, finding that commonplace technologies were used more frequently in intimate partner stalking than specialised tracking tools such as spyware. Woodlock (2017: 591) found that 56% of survivors reported abusers using technology to check their location, 47% said their partner checked their text messages without permission, 17% had demanded their passwords and 14% had impersonated them via emails, text messages or social media.
Singh’s (2022) work on financial abuse highlights the interconnected nature of coercive control, financial abuse and technology-facilitated abuse. As Singh notes, ‘control over the mobile phone, computers, the Internet and the car increasingly [becomes] part of the way a man isolates, monitors and abuses a woman’ (p. 8). The financial abuse to which Singh refers is defined as ‘a deliberate pattern of behaviours in which an individual seeks to control, exploit or sabotage their partner’s ability to acquire, use and maintain financial resources’ (Deloitte Access Economics, 2022: 7), and is a common feature of coercive control dynamics. Building on this, Littwin (2012) coined the term
These findings underscore the limitations of conventional cybersecurity approaches, particularly in interpersonal contexts. Research on cybercrime in such settings highlights the need for expanded threat modelling that accounts for misuse as well as intended use (Fernandez et al., 2009). Threat modelling is ‘a process used to investigate potential cybersecurity attacks, to shift the conventional technical focus from the risks to systems toward risks to people’ (Slupska and Tanczer, 2021).
In response to these challenges, Dragiewicz et al. (2019, 2020) proposed an Intimate Threat Model (ITM) for cybersecurity, which encompasses risks arising from intentional credential sharing, intimate knowledge that can facilitate password or security question guessing, and physical access to passwords, networks and devices, factors that frequently emerge in the context of intimate relationships.
Australian researchers have emphasised the need to pay attention to the context, meaning, motives and impact of technology-facilitated behaviours rather than focusing solely on specific technologies or affordances. Identical technologies and behaviours can be used to document, escape, or survive abuse or exert coercive control (Douglas et al., 2019; Dragiewicz, 2023; Dragiewicz et al., 2019; Hand et al., 2009; Woodlock, 2017). This perspective informed our decision to examine the full spectrum of smartphone-sharing practices in this study, regardless of whether they appeared benign or potentially harmful.
Empirical foundations for theoretical advancement
The scale of smartphone adoption has outpaced research on how these devices are used in everyday life. Although there is growing attention to cybersecurity threats in domestic contexts (Bellini et al., 2021; Doerfler, 2019; Slupska and Tanczer, 2021), little is known about the prevalence, context and implications of mobile phone sharing in Australia. We argue that before theory and security practice can be meaningfully advanced or refined, it is essential to establish a baseline understanding of everyday sharing practices and the cultural values and attitudes that shape them. Without this foundational knowledge, theoretical models risk being misaligned with lived realities and are likely to overlook or misunderstand nuanced intimate relationship dynamics. This project helps fill this empirical gap and provides foundational knowledge to support future theoretical elaboration in cybersecurity research and to inform necessary changes in cybersecurity practice that reflect the realities of intimate device sharing.
Methods
We conducted a computer-assisted online survey to explore smartphone-sharing practices among Australians in the context of intimate relationships. 1 The study aimed to understand how individuals navigate access, privacy and control of mobile devices. The survey consisted primarily of closed-ended questions supplemented by open-ended items. The open-ended items were designed to address potential ambiguities in fixed-choice items that permitted participants to elaborate on their responses. 2 Given space constraints, qualitative data from this study are analysed in other publications.
The choice of survey questions was informed by our prior research on technology-facilitated abuse (Dragiewicz et al., 2018a, 2018b, 2019, 2020, 2021, 2022) and the literature on interpersonal cybersecurity and mobile phone sharing. We conducted pilot testing to refine question wording, ensure accessibility and manage survey length. We used contingency questions to ensure a logical flow of information. For example, participants who did not lock their phones were not asked about partner access to locked devices.
Recruitment took place from May to September 2024, primarily through paid advertisements on Meta, chosen for its wide reach. Additional recruitment included outreach via a local community organisation and our professional networks. Recruitment materials featured a brief study description and QR code or URL embedded with unique query strings, enabling us to track the source of participants and assess whether key outcomes varied across recruitment channels. We deliberately chose this approach over ‘representative’ samples from commercial survey companies, which typically rely on pre-existing panels of individuals who opt in for financial incentives. This model can introduce systematic bias, as ‘professional survey takers’ may differ from the general population in ways that affect responses. For instance, commercial panel participants may be more focused on efficiency than reflection, or more inclined to provide socially desirable responses to remain eligible for future opportunities. These tendencies could distort findings related to sensitive behaviours like smartphone sharing in intimate relationships.
While all recruitment methods involve some degree of self-selection bias, we reasoned that social media advertising could reach a broader, more dynamic audience, including individuals less likely to participate in panels, potentially improving representativeness on variables relevant to our study. In the context of mobile phone sharing, we reasoned that representativeness should reflect behavioural patterns rather than demographic quotas. For example, detecting sex differences in sharing does not require equal numbers of women and men, but rather a sample whose behaviours align with those observed in the broader population. Our analysis of sharing behaviours across recruitment methods and examination of demographic variations revealed no meaningful differences (see Table 3) that would suggest that a commercial panel would have offered any advantage over our recruitment strategy. Importantly, we found no significant variation in sharing behaviours across demographic groups such as sex, age, education, First Nations status or country of birth, nor across the different recruitment streams. This consistency supports our contention that the sample is likely to be broadly behaviourally representative of the broader population of Australian adults who use smartphones and are currently or recently involved in a romantic relationship, even if not demographically proportional in all respects.
To enhance sample diversity, we partnered with the Multicultural Families Organisation (MFO), a nonprofit community-based organisation serving Culturally and Linguistically Diverse communities. 3 MFO staff provided feedback on item wording and promoted the study through their newsletter, in-office signage and social media channels. MFO recommended the inclusion of recent ex-partners, aligning with best practices in domestic violence research, where it is widely recognised that people with abusive partners may be reluctant to participate due to safety concerns (Ackerman and Field, 2011; Johnson, 2014). Additional recruitment occurred through our professional and personal networks (e.g. email, and individual Twitter/X and Facebook accounts). As an incentive, those who completed the survey could enter a draw to win one of five US$50 gift cards or one US$250 gift card.
Participant eligibility
Participants were required to be 18 years or older, reside in Australia, use a mobile phone and have current or recent involvement in a romantic relationship. Eligibility was determined via screening questions. Ineligible volunteers were thanked and exited from the survey.
Relationship status was the most complex demographic criterion and was evaluated through a series of contingency-based questions. Participants were first asked about their marital status. Those not currently married, in a de facto relationship (common-law marriage) or engaged were asked if they were currently dating, in a serious relationship or had an intimate or sexual partner. If none of these applied, never-married individuals were asked whether such relationships had occurred in the past.
Divorced, separated and never-married individuals who reported previous partnerships were asked when their most recent relationship ended. Those who had exited a relationship within the past 3 years were considered eligible, along with participants in current relationships. Divorced or separated individuals, including those formerly in de facto relationships who had a new partner, were asked about the new relationship; otherwise, they were asked about the previous partner from whom they had separated. Never-married individuals without a current relationship but who terminated a past relationship within 3 years were also asked about their previous partner.
Of the individuals who proceeded beyond the survey information page, 1049 met our eligibility criteria. Usable responses numbered 988, defined as completing the survey through the section on mobile phone locking. Following a quality check, 21 responses were removed due to duplication (likely unintentional based upon the time gaps between entries), inattentiveness (e.g. identical responses across selected critical items) or implausible answer patterns (e.g. never using the phone to make phone calls). One widowed person was excluded because they were the only person in this relationship category. This resulted in a final analytic sample that contained 967 participants. For analyses focused on partner access to individual devices, we excluded six participants who reported sharing a single phone with their partner. This resulted in a sub-sample of 961 participants for many of our analyses.
Participant characteristics
Participants ranged in age from 18 to 82 years (
In terms of education, 34.4% completed an undergraduate degree, and 35.4% held a postgraduate qualification. About 30% had completed secondary school (29.7%), and fewer than 0.5% reported primary school as their highest level of education. Annual income ranged from US$0 to over US$200,000, with a mean of US$72,164.
Regarding sexuality, 75.3% identified as heterosexual. In addition, 14.7% identified as bisexual and 4.5% as gay or lesbian. The remaining 5.5% selected another category, preferred not to answer, or were unsure.
Nearly half of participants were married (44.6%), followed by those in de facto relationships (28.9%), never married (15.5%), engaged (6.1%) or divorced (2.7%). Relationship durations ranged from 1 month to 64 years, with an average of 12 years. Most participants (76.1%) lived with the partner they reported on, while 23.9% did not cohabit.
Our analyses recognise the nuanced interpretations of the term sharing. We distinguish among three key forms:
(a) Sharing a single mobile phone;
(b) Sharing credentials that allow a partner to access one’s phone;
(c) Granting access to one’s phone either by sharing credentials or by intentionally leaving a phone unlocked for a partner.
Importantly, scenarios (b) and (c) are rendered moot when couples share a single device, as in (a). In addition, (b) constitutes a specific case within the broader category defined in (c). For consistency with the prior literature, which typically does not differentiate among these forms, we use the term mobile phone sharing unless a more specific distinction is warranted. These distinctions, combined with the fact that some analyses apply only to participants who engage in mobile phone sharing, result in varying sample sizes across several tables.
Findings
Participants primarily used either an iPhone (51.2%) or an Android device (48.4%). Fewer than 1% reported using another type or were unsure of their device type (data not shown in table).
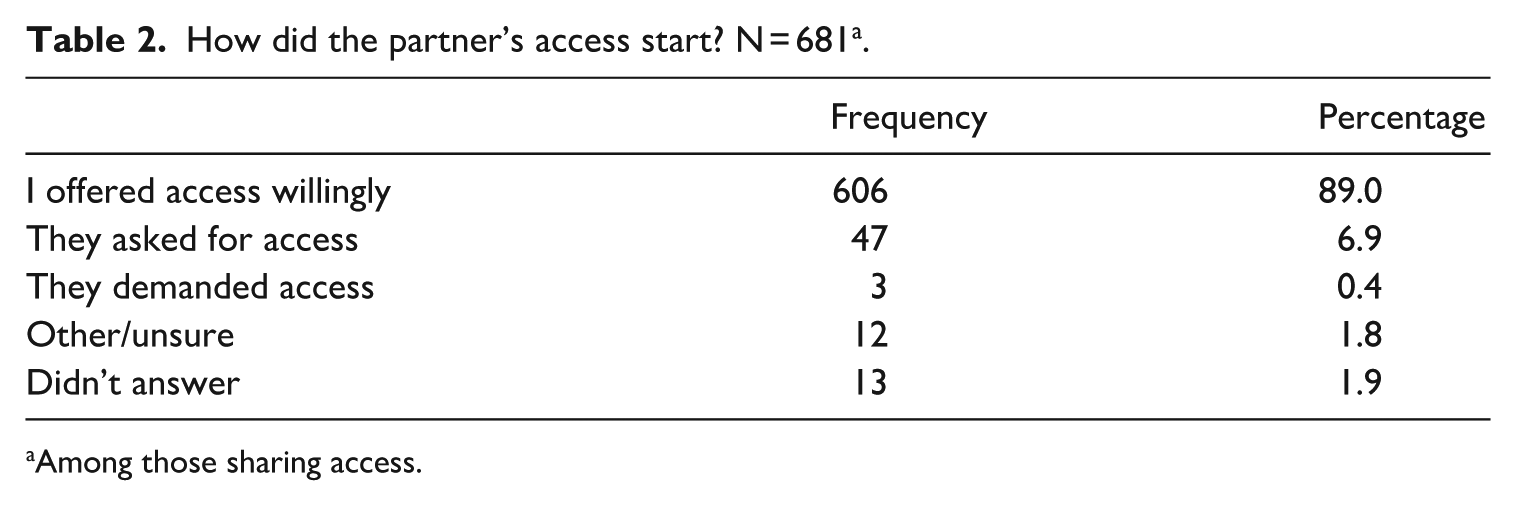
As shown in Table 1, only six participants shared a single mobile phone with their partner, fewer than 1% of the sample, indicating that nearly all participants used a separate device. The vast majority (94.8%) used a lock screen. Although not shown in the table, participants reported using a range of authentication methods, often in combination. The most common method was a PIN (61%), followed by facial recognition (47%), fingerprint scanning (30%), swipe pattern (9%) and password entry (4%).
Partner access variables.
Phone unlocked so ‘partner can use it’ or ‘partner doesn’t want me to lock it’.
Among those who do not share a single phone.
Among those who do not use a lockscreen.
Among those who used a lock screen.
Those who left unlocked for partner or partner has access credentials.
Of the 50 who did not use a lock screen (5.2%), 8 participants (16.0%) said that they did not use a lock screen so that their ‘partner can use it’ or that their ‘partner doesn’t want me to lock it’. We counted these eight among those we classified as ‘sharing access’. Sharing unlock credentials was a more common way to share access, however. Among the 912 who used a lock screen, 673 (73.4%) reported that their partner could unlock their phone.
Even when access sharing was not more routinised through purposely leaving the phone unlocked for the partner or providing access credentials to the partner, an additional number of participants, 815 (84.8% in all), reported that their partners had used their phones in the last year. Although we did not inquire how the partners gained this access, we reasoned that it was likely due to the participant unlocking the phone for the partner’s use.
When combining cases where partners had access through shared credentials with those where phones were left unlocked for the partner, 681 (70.9%) of participants were classified as sharing access with their partner (see the last row of Table 1).
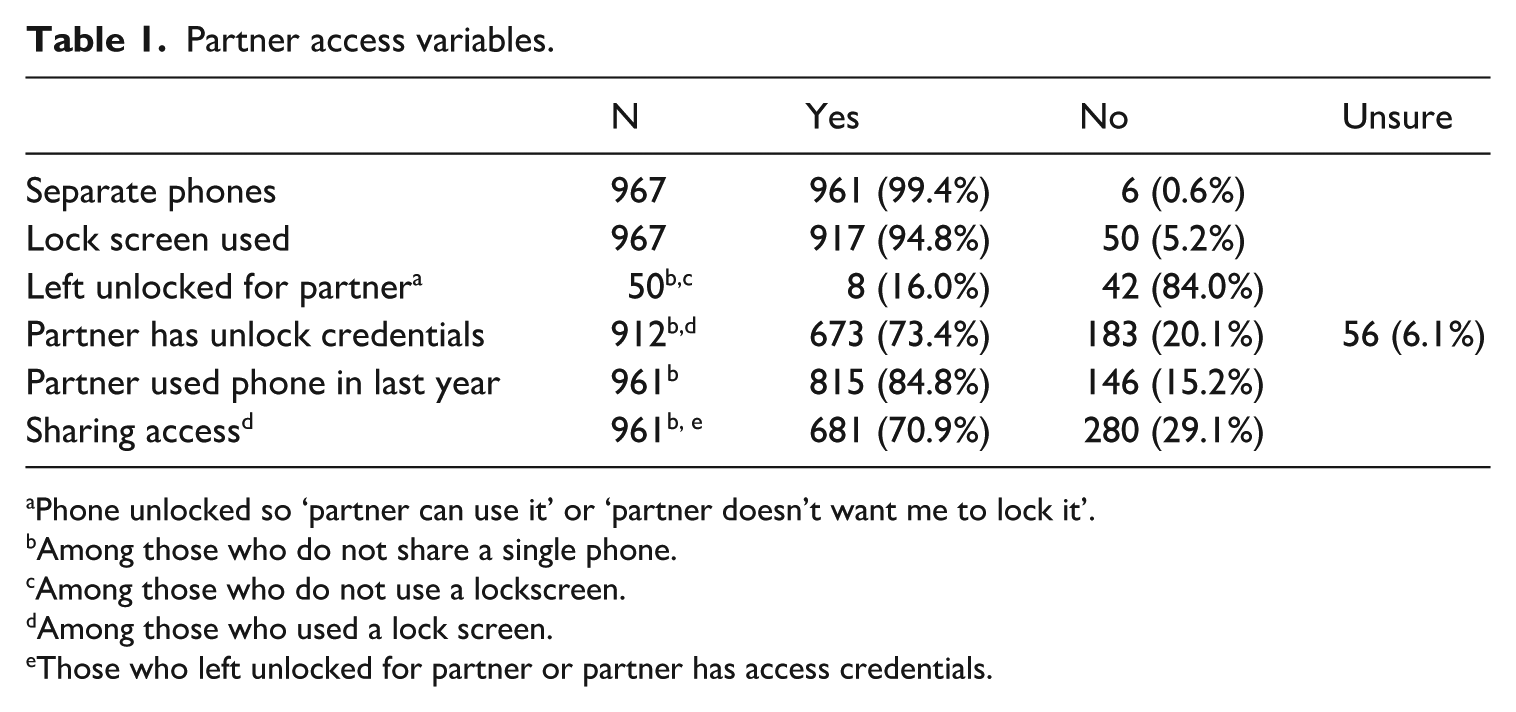
How mobile phone access sharing begins is a critical consideration, as it may indicate whether the practice reflects mutual agreement or potentially suggests an unhealthy relationship dynamic. In some instances, access may be shaped by force, coercion, surveillance or the absence of genuine consent, factors commonly associated with controlling or abusive behaviour.
As shown in Table 2, only a small proportion of the 681 participants who reported sharing phone access (the ‘yes’ responses in the final row of Table 1) described circumstances suggestive of such concerns. Among those who shared access, 90% reported voluntarily offering it. An additional 7% indicated that their partner had requested access. Fewer than 0.5% stated that their partner had demanded access, while under 2% were unsure, did not respond, or selected another option.
As shown in Table 3, mobile phone access sharing rates were relatively consistent across demographic groups, with no statistically significant differences by sex, age or education level. Approximately 70% of participants reported sharing access, with women (71.1%) and men (69.8%) reporting nearly identical rates (
Sharing access by demographic characteristics N = 961.
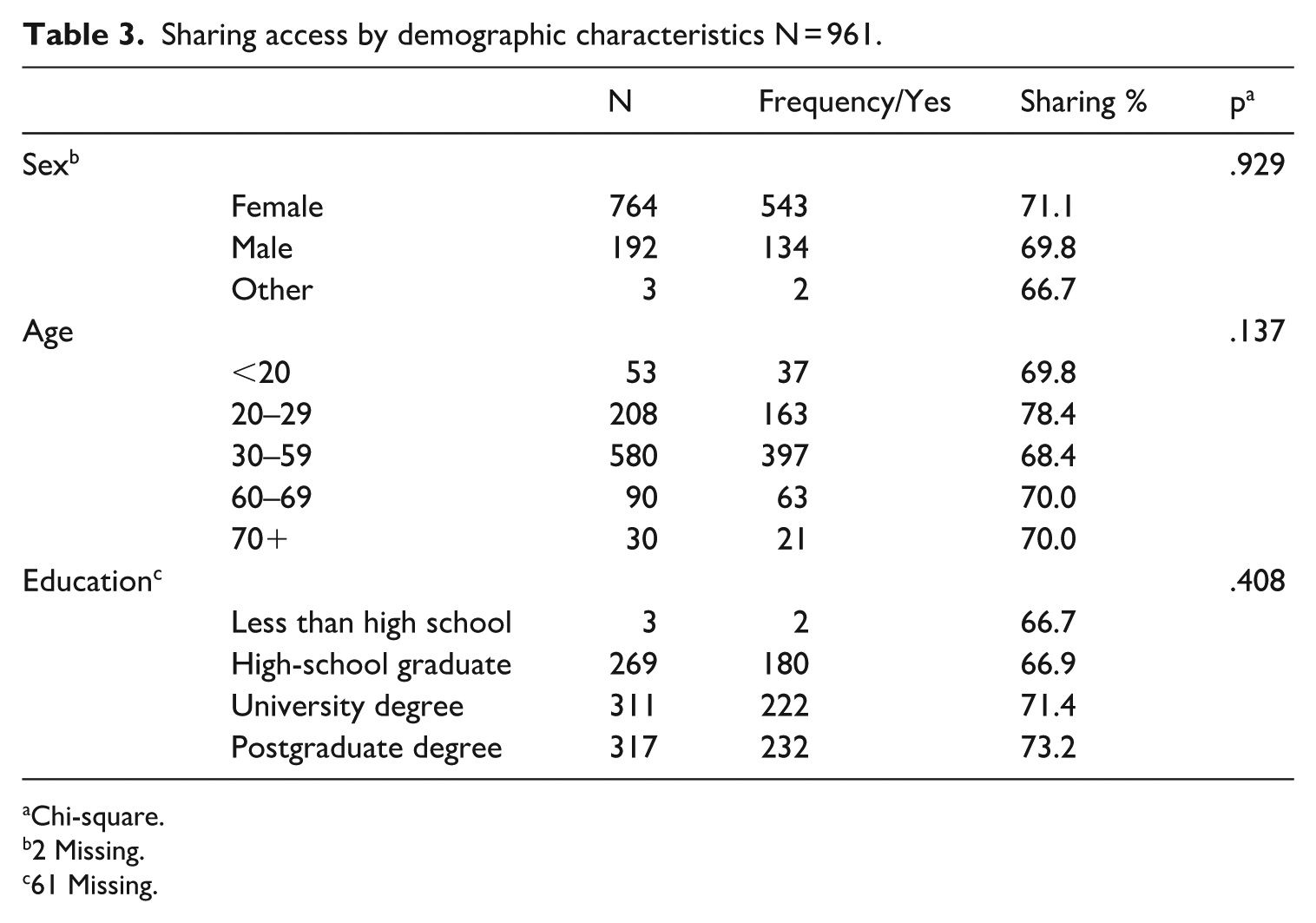
Chi-square.
2 Missing.
61 Missing.
First Nations status and nativity were also not significantly associated with sharing behaviour (
These findings support the recruitment strategy outlined earlier. The absence of statistically significant demographic variation in sharing behaviour suggests that the sample likely succeeded in capturing the key behaviours relevant to our aims in a reasonably unbiased way. In other words, our use of social media advertising, rather than commercial survey panels, appears to have yielded a diverse sample without introducing detectable demographic bias in relation to the core construct of phone sharing. This outcome aligns with our conceptualisation of representativeness as behaviourally, rather than demographically, grounded.
As illustrated in Figure 1, participants reported frequent engagement with a wide range of mobile phone functions. The most used features were text messaging and information lookup, each reported by 97% of participants at least once per week, followed closely by social media use (96%) and making phone calls (90%). Entertainment-related functions such as playing music (82%) and watching TV (39%) were also widely used, though to varying degrees.
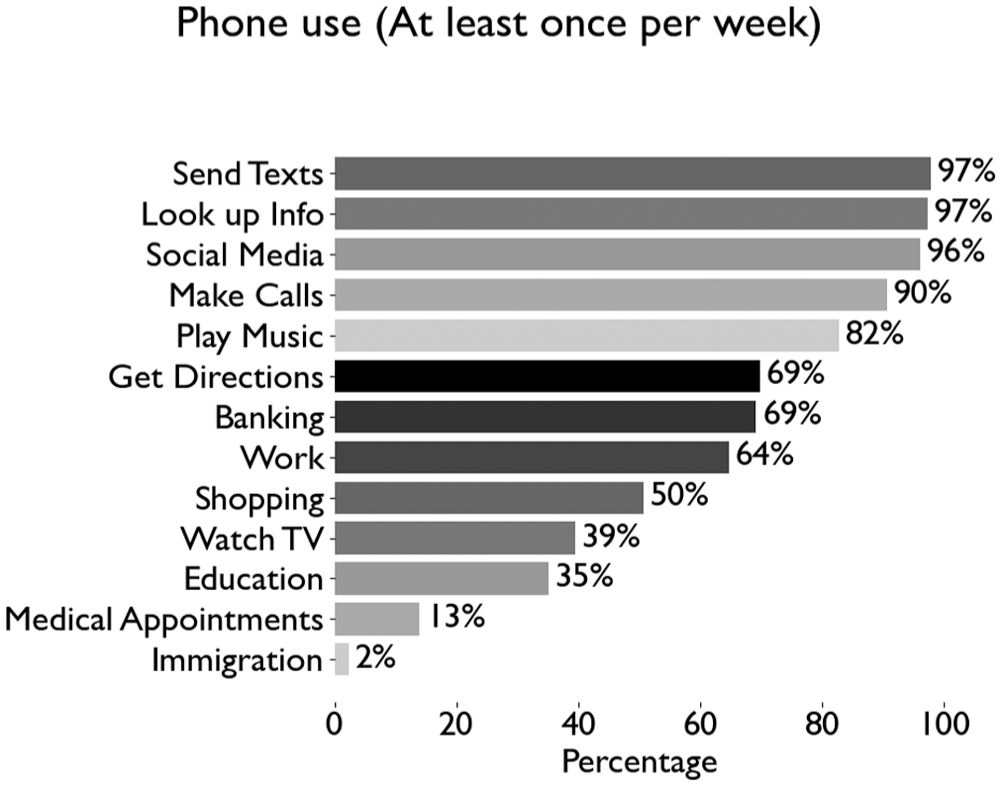
Phone use (At least once per week).
Functional activities such as getting directions and mobile banking were each reported by 69% of participants, indicating that mobile phones serve both logistical and financial purposes in everyday life. Work-related use was reported by 64%, while 50% used their phone for shopping and 35% for educational purposes. Less common uses included scheduling or attending medical appointments (13%) and accessing immigration-related services (2%), suggesting that while mobile phones play a significant role in communication, social interaction and daily logistics, they are less commonly used for more specialised interactions. While immigration and visa matters affect a relatively small percentage of the population, two-factor mobile phone authentication is required for accessing these services in Australia.
These findings underscore the centrality of mobile phones in daily life and highlight the breadth of contexts in which access and sharing could become relevant or sensitive. The frequency of both personal and functional uses reinforces the importance of understanding mobile phone sharing not only as a symbolic gesture of intimacy but also as a practical consideration in navigating everyday life. While some functions, such as immigration, affect only a small percentage of the population, the implications of sharing in these cases can be profound.
As shown in Figure 2, participants reported sharing mobile phone access with a range of non-romantic contacts over the past year. The most common recipients were children (34%), followed by friends (31%), other family members (18%) and parents or in-laws (17%). Sharing with a roommate or housemate was comparatively rare, reported by only 3% of participants.
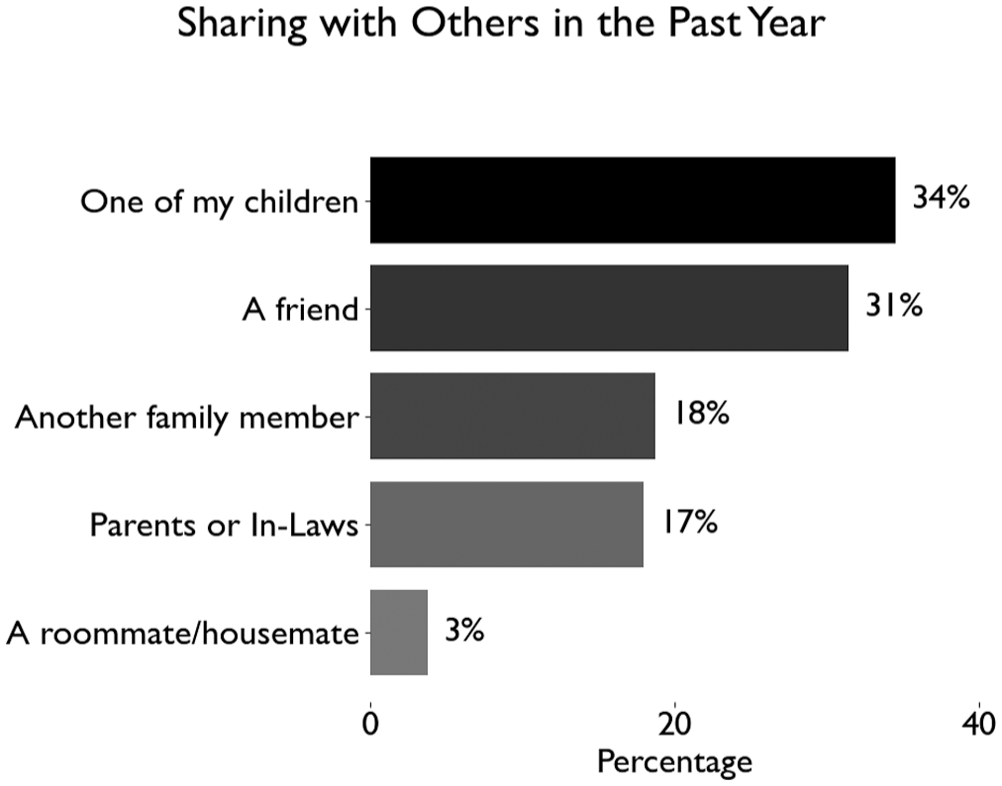
Sharing with others in the past year.
These patterns suggest that mobile phone sharing extends beyond romantic relationships and occurs within broader social and familial networks, albeit at lower rates. The relatively high levels of sharing with children and friends may reflect practical caregiving responsibilities, trust-based exchanges or shared digital tasks. By contrast, the lower prevalence of sharing with housemates and extended family members may reflect weaker relational ties or privacy concerns.
This broader context reinforces the notion that mobile phone sharing is embedded in everyday relational practices, shaped by interpersonal trust, dependency and household dynamics. While romantic partners remain a primary context for sharing, the data highlight that sharing is not limited to romantic or cohabiting relationships, suggesting a need for research and policy frameworks that account for these diverse relationship settings.
Figure 3 presents the reasons participants shared their mobile phone access with partners. The most frequently endorsed reason was ‘I have nothing to hide’ (53%), followed closely by ‘It’s convenient’ (50%) and ‘In case they need backup’ (33%). These responses suggest that many participants view sharing as a pragmatic or low-stakes act, often framed in terms of transparency, ease or mutual support. Less common, though still notable, were responses reflecting resource availability (‘I have resources’, 26%) or a belief that sharing benefits the relationship (21%). Together, these rationales suggest a mix of instrumental and relational motivations behind access sharing.
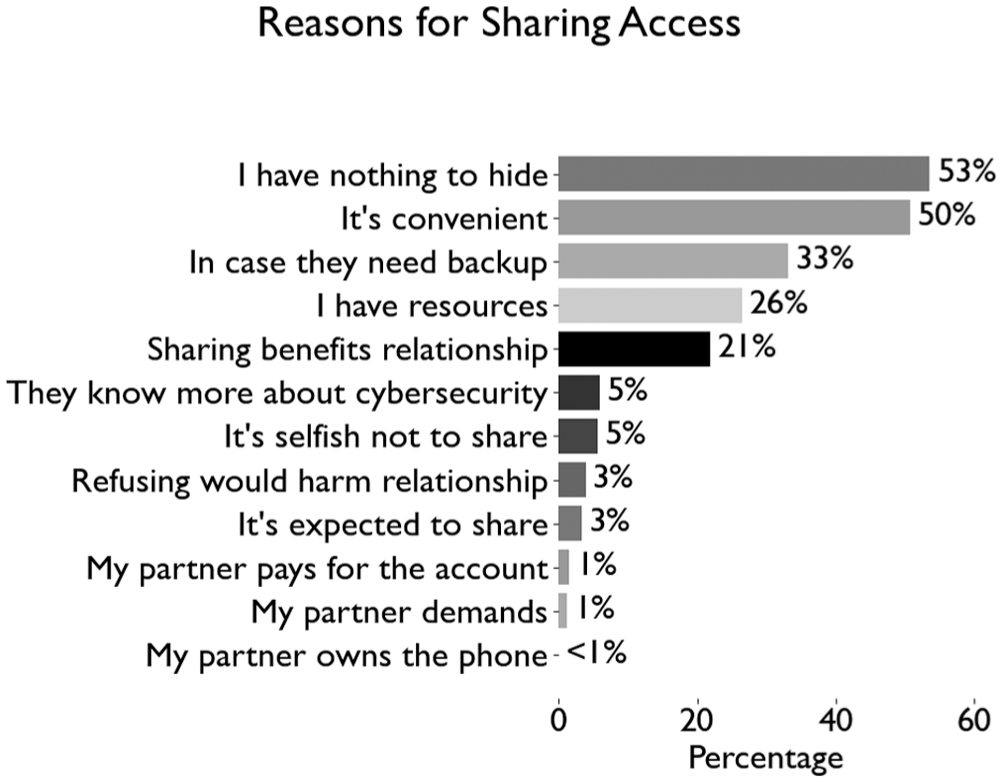
Reasons for sharing access.
A smaller proportion of participants (5% or less) endorsed reasons that may suggest external pressure or obligation, such as believing that refusal would harm the relationship (3%), feeling it’s expected (3%) or citing partner control (e.g. ‘My partner demands it’, 1%; ‘My partner owns the phone’, <1%). These lower frequencies suggest that, for most participants, access sharing is not driven by coercion or relationship power imbalances, though such cases do exist and merit close attention.
Overall, the data highlight the everyday rationales that underpin access sharing, often rooted in convenience, trust and care, while also underscoring that a small subset of respondents may engage in sharing under relational or structural constraints.
Figure 4 illustrates the privacy-related behaviours participants engaged in to conceal information from partners. The most frequently reported actions involved deleting (40%) or hiding (36%) content so a partner would not see it, indicating that a substantial proportion of participants actively managed information visibility on their phones. In the open-ended item, which provided a space for more information, some participants noted that concealment and deletion were for benevolent reasons.
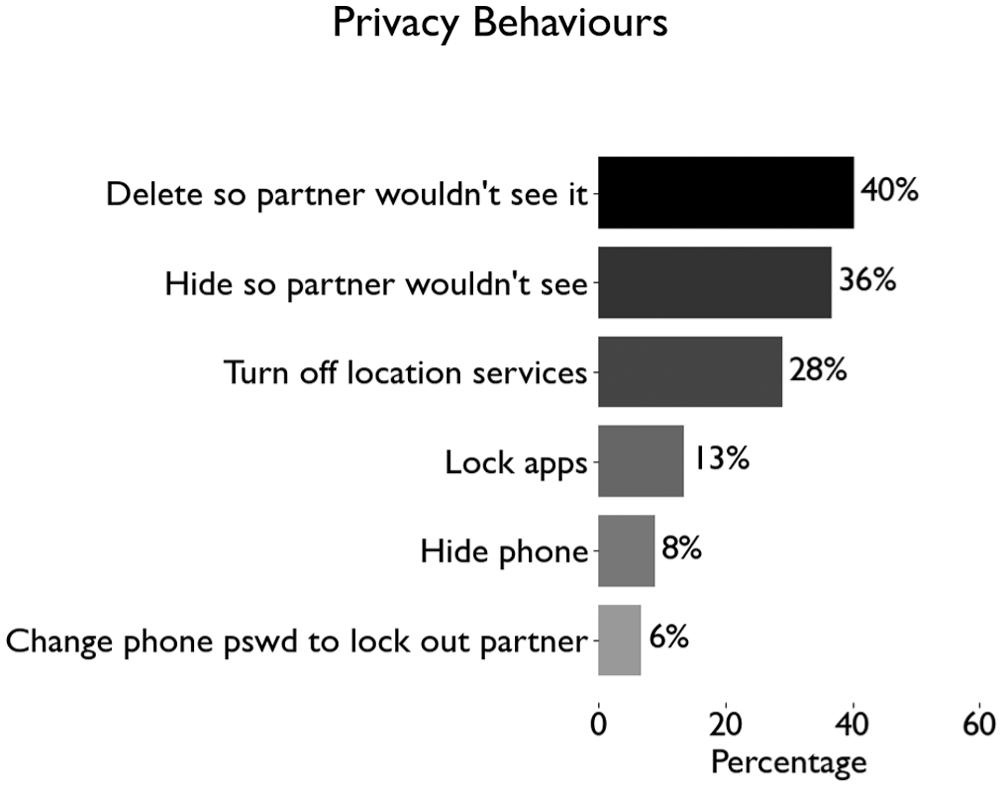
Privacy behaviours.
In addition, nearly one-third (28%) reported turning off location services, which may reflect efforts to maintain spatial privacy. However, as we did not include questions about participants’ motivations for disabling these services, it remains unclear whether this behaviour was explicitly intended to prevent a partner from tracking their location or general privacy concerns. Less common behaviours included locking specific apps (13%), hiding the phone (8%) or changing the password to prevent partner access (6%).
These findings highlight a tension between access sharing and privacy maintenance. While many participants reported voluntarily sharing access, a significant minority engaged in digital boundary-setting practices. This suggests that sharing access does not preclude the presence of privacy concerns. Moreover, these behaviours may reflect a spectrum of motivations, from benign boundary-setting to responses to surveillance or coercion. As such, they underscore the complexity of access-sharing and suggest the importance of contextualising sharing within relationships and technological ecosystems.
Finally, we examined whether participants discussed any rules or expectations regarding phone sharing with their partners. Among the 632 participants for whom this question was applicable, only 72 (11.4%) reported having had such discussions, while 551 (87.2%) reported no discussions. Nine (1.4%) were unsure if they had discussed expectations for sharing. 4
Discussion
Sharing smartphone access with partners effectively involves device and credential sharing. Our findings on smartphone sharing in Australia build on prior research on mobile phone and password sharing. Similar to previous research, we found that credential sharing is common. Prior research in the United States found similar rates of password sharing with partners (75% on average), with higher rates of sharing associated with relationship seriousness (Kaye, 2011; Vogels and Anderson, 2020). Our research confirms earlier research showing that many people share passwords and devices for multiple innocuous purposes, including convenience (Ferreira et al., 2011; Sing et al., 2007), because they trust their partner, or to demonstrate their trustworthiness to a partner (Baker and Carreño, 2016; Doerfler et al., 2024). However, few participants (less than 12%) had discussed expectations for sharing. The lack of communication about how phones are to be shared could lead to problems where the partners’ expectations differ or boundaries are inadvertently crossed. This is a missed opportunity for both parties to consider and articulate how sharing should function.
Our findings build on the earlier research on the social nature of mobile phone use, showing that mobile phones function as shared and relational tools in intimate contexts, not merely as devices for individual telephone conversations. Like Weilenmann and Larsson (2001), Rennie et al. (2018) and Wu et al. (2022), we found that mobile phones are communal rather than individual resources. While sharing devices and credentials is often presumed to be problematic, the meaning of sharing is highly context dependent. The nature of technology-related behaviours cannot be determined based on their presence or absence alone.
Our findings indicate that mobile phone and credential sharing are usually innocuous. Responses to questions about why participants shared access indicate that 5% or fewer endorsed reasons that may suggest external pressures or social obligations to share. This supports prior research documenting the positive uses of sharing in couples (Lin et al., 2021). On a related note, the majority of participants reported that sharing began when they voluntarily offered their partners access or the partner requested it. While less than 1% of our sample indicated that their partner had demanded access to their phone, we reiterate that those experiencing abuse are less likely to participate in survey research (Ackerman and Field, 2011; Johnson, 2014). As the majority of our participants reported on current partners and what appear to be non-coercive relationships, future analyses from this study will investigate differences based on relationship status and characteristics.
Although most sharing is not driven by coercion, such cases do exist and merit attention to understand the cybersecurity needs and priorities of those exposed to potentially problematic sharing dynamics. As discussed above, privacy and interpersonal cybercrime are legitimate concerns with serious implications. Our research points to the cultural influences that shape phone sharing in relationships in Australia, supporting earlier calls for what Wu et al. (2022) call ‘social cybersecurity’. Social cybersecurity is concerned with the ways in which ‘human social dynamics push against and complicate the use of technical tools intended to support [security and privacy] practices’ (Wu et al., 2022: 1863). While sharing is a concept that may be decreasing in importance for social networking platforms (John, 2024), sharing smartphones is a commonplace occurrence for the majority of Australian couples. Our study confirms that sharing mobile phones is frequently a form of intimate communication based on trust in couples. Although our survey is descriptive, prior research highlights a hierarchy of technology risks, suggesting that shared access may have uneven consequences across different groups depending on gender, social context and vulnerability (Hardley et al., 2021; Powell and Henry, 2017; Rennie et al., 2018). Future analyses of data from this project will examine these differential risks now that baseline prevalence has been established.
Furthermore, as Messing et al. (2020) observed, the meaning of technology behaviours is entirely contingent upon the context in which they occur, including factors such as frequency, duration, history of abuse in the relationship and their effects. Our study affirms their conclusion that the subjective and ambiguous nature of technology behaviours necessitates careful attention. The mere presence or absence of behaviours on a list cannot tell us if they constitute technology-facilitated abuse. As Messing et al. note, survivors themselves may not have a clear understanding of the threshold at which monitoring behaviours cross the line into abuse. Accordingly, we concur that researchers should use care when defining and measuring technology behaviours that may or may not be abusive depending on the context. Taken together, these findings underscore that cybersecurity policies and advice focused on not sharing devices and credentials are inadequate for understanding and mitigating interpersonal threats because they fail to account for Australians’ everyday practices and the varied vulnerabilities that accompany them.
Limitations
Like any study, this one has limitations. First, although the sample was not demographically representative in the conventional sense, our recruitment strategy was designed to capture behaviourally relevant insights and whether sharing behaviours vary across major demographic variables rather than providing precise estimates of population prevalence. As noted earlier, we found no significant variation in sharing behaviours across demographic groups or recruitment streams. Second, although we provided definitions for key terms, participants may have interpreted them in slightly different ways. In particular, ‘sharing’ can encompass a range of practices, including providing credentials, leaving a phone unlocked, or jointly using a single device. Third, the reliance on self-report data introduces the possibility of recall bias. However, given the relatively non-stigmatised nature of the behaviours under study and the high rate of admitted access-sharing, even when access sharing contradicts recommended privacy practices, social desirability effects are likely minimal. Participants appeared willing to disclose behaviours that are discouraged in cybersecurity advice but are socially normative in the context of trust-based relationships. In summary, while the study has limitations common to behavioural research, it was strengthened by a large and diverse sample, as well as a rigorous survey design. Where present, we feel that the limitations we identified are likely to lead to the underreporting of potentially problematic behaviours, leading to conservative estimates of their prevalence.
Conclusion
The goal of this study was to build a new knowledge base on how Australian couples share their smartphones in everyday life. Based on our findings that most Australian couples share access to their smartphones and few people have had explicit discussions about sharing with their partners, we encourage couples to consider and engage in conversations about their preferences and the potential implications of smartphone sharing. While this project was not focused on technology-facilitated abuse, our findings show that widespread device and credential sharing may introduce Intimate Threats to cybersecurity for many Australians, risks that could be heightened in the event of relationship breakdown. As relationships evolve, technology misuse by one partner may go unnoticed by the other. In many cases, technology-facilitated abuse may only come to light following separation. These complexities underscore the need to move beyond one-user/one-device cybersecurity models, which make it more difficult to navigate the balance between the positive social uses of sharing and its potential risks.
Another aim of this research was to share knowledge about smartphone sharing with telecommunications companies, government cybersecurity bodies such as eSafety, the Australian Cyber Security Centre, and the Australian Communications and Media Authority. Our findings can be used to ensure policy approaches are adequate to address real-world risks from everyday sharing in relationships. Safety by design requires affordances and applications that are appropriate for how people actually use them. It is essential that the Intimate Threat Model for cybersecurity is integrated into cybersecurity frameworks. The social uses of mobile phones and their culturally informed meanings are an important part of the cybersecurity landscape.
Future research
While this article reports on a study of mobile phone sharing among couples, further research on sharing within families, particularly with children and older adults, is needed. These populations have unique interests in sharing smartphones safely and consensually. Older adults have concerns about their ability to keep up with technological changes while protecting access and security. Children are subject to unprecedented levels of surveillance by their parents, with unclear implications for their attitudes towards privacy and cybersecurity later in life.
Our findings also highlight the need for further research on the social and cultural aspects of smartphone sharing in affluent Western countries, as well as in emerging economies. Our findings show that cultural norms shape phone sharing in ‘mainstream’ Australian culture. While Culturally and Linguistically Diverse Australians are more likely than others to rely on a single interconnected device in the household (Good Things Foundation Australia, 2021: 22), our findings show that social values around relationships shape smartphone sharing for the majority of Australians. While quantitative research is necessary to understand the scale of device and credential sharing, qualitative research will be required to understand the nuances of these interactions and their implications for individuals, relationships and communities.
Interpersonal cybersecurity lapses are often attributed to telecommunications consumers’ skill deficits. However, consumers cannot be held responsible for corporations’ failure to design devices, applications and interfaces that are appropriate for the majority of Australians’ actual lived experience. Our findings suggest that interpersonal dynamics such as widespread device and credential sharing should be considered in future cybersecurity policy development. Incorporating the Intimate Threat Model could help align government policy and education campaigns with the broader spectrum of real-life conditions in which cybersecurity vulnerabilities may arise.
Footnotes
Acknowledgements
The authors express their appreciation to everyone who took part in the study. Sharing your knowledge and experiences has provided an opportunity for telecommunications companies, platforms, services, justice systems, government and academics to better understand the nature and dynamics of mobile phone sharing. They also thank Rana Al-Mekarry from Multicultural Families Organisation (MFO), which served as their community partner for this study. They thank Angie Signorini, Belinda Watanabe and Irene Dullaway from Griffith University. They thank the Australian Communications Consumer Action Network, which made this study possible via their independent research grants scheme. From ACCAN, they thank Samuel Kininmonth, David Hack, Tanya Karliychuk and Laetitia Kwan.
Author contributions
Consent to participate
Respondents were required to tick a box indicating their consent on the online survey information and cover sheet before accessing the survey questions.
Consent for publication
Respondents provided consent for publication of their anonymised data as a condition of consent to participate.
Data availability statement
Data from this study are not publicly available.
Declaration of conflicting interests
The authors declared no potential conflicts of interest with respect to the research, authorship and/or publication of this article.
Ethics approval
Ethical approval for this research was provided by the Griffith University Human Research Ethics Committee (GUHREC), GU Ref No: 2023/651.
Funding
The authors disclosed receipt of the following financial support for the research, authorship and/or publication of this article: This research was made possible by the grant Smartphone sharing with intimate partners: Implications for telecommunications consumer cybersecurity, funded by the Australian Communications Consumer Action Network (ACCAN). ACCAN is Australia’s peak communications consumer organisation representing individuals, small businesses and not-for-profit groups as consumers of communications products and services. It focuses on goods and services encompassed by the converged areas of telecommunications, broadcasting, the Internet and online services, including both current and emerging technologies.