Abstract
Privacy scholars have posited that institutional privacy threats arouse more uncertainty than social privacy threats, though research examining different types of privacy threats side-by-side is limited. This research uses the repeal of federal protection for abortion in the United States as a case study to explore reactions to these different threats. Moreover, by separately considering corporations and the state, we inductively examine beliefs about the flows of information and resulting power dynamics between individuals (horizontal) and multiple institutions (vertical). Data from interviews with 45 young women in California and Indiana revealed that privacy threats from institutions—especially the state—were perceived as more uncertain, and that these various threats were seen as intertwined. We present the construct of cooperative privacy threats to highlight the lack of boundaries between privacy threats, which often amplifies the risks they pose. Our findings elaborate on online privacy theory and may inform future privacy-preserving policy and technology design.
In 2022, the Supreme Court radically changed the nature of abortion access in the United States (Dobbs v. Jackson Women’s Health Organization, 597 US 215), creating new opportunities for digital surveillance from the state and tech companies, sometimes with grave consequences. Yet little is known about how everyday citizens, particularly women, are responding to these new risks. Digital privacy scholarship in communication identifying risks from different types of institutional threats has been limited to date (for the exception, see Zhang et al., 2024), and the perceived overlap between these threats is rarer still.
The term privacy risk describes the belief in the potential for loss or negative consequences from disclosing personal information (Xu et al., 2011). As new digital privacy risks from the state continue to make headlines (Horsley and Manuel, 2025), greater theoretical elaboration is needed to understand how people interpret and respond to state versus corporate institutional privacy threats, and how they differ from social privacy threats. Using the context of abortion to approach these questions, we interview 45 women of childbearing age from both California and Indiana, two states with dramatically different abortion laws, to inductively explore how they respond to the uncertainty of online privacy threats from different sources. In particular, we elaborate on previous privacy scholarship by studying interpersonal, corporate, and state threats within the context of abortion to better understand how those threats are perceived as distinct and overlapping. Elaborating on previous privacy scholarship (Crain, 2018; Dencik and Cable, 2017), we propose a new concept of cooperative privacy threats to reflect the often fuzzy boundaries between different vertical and horizontal threats. In doing so, we extend theoretical privacy constructs and underscore the need for more work on the navigation of interpersonal, corporate, and state privacy threats, ultimately allowing for future deductive tests of the effects of perceptions of cooperative threats on Internet use and psychological outcomes for different groups.
The state of online privacy
Privacy involves “selective control of access to the self” (Altman, 1975: 24), and enables us to act autonomously, explore who we are, process our emotions, and build or maintain relationships (Westin, 1967). According to Nissenbaum’s contextual integrity framework, people’s normative privacy beliefs about how certain outside actors should handle their information will vary depending on the context and the type of information involved (Nissenbaum, 2010). Although people historically tend to consider some types of information more private than others (e.g. our sex lives, illnesses), the nature of what we as a society consider private tends to evolve over time (Solove, 2002). Given the contextual nature of privacy, it is thus necessary to reconsider people’s privacy beliefs and attitudes as technology, legal policy, and culture evolve. We are particularly interested in inductively exploring relationships between different forms of horizontal and vertical privacy threats, which have historically been underexplored in privacy literature (for an exception, see Zhang et al., 2024), and which may yield serious personal and social consequences.
The networked nature of the Internet and the persistence of our digital data complicate our ability to control the flow of our personal information (Bazarova and Masur, 2020). Challenges arise with respect to managing both horizontal or social privacy, which denotes privacy from other individuals, and vertical or institutional privacy, which describes privacy from institutions, including corporations and the government (Bazarova and Masur, 2020; Quinn and Epstein, 2023; Raynes-Goldie, 2010). Due to the lack of transparency from institutions regarding their data practices, a number of privacy scholars have surmised that people are more uncertain about vertical privacy risks than horizontal ones (Acquisti et al., 2015; Masur, 2018; Quinn and Epstein, 2023), yet there is limited data to support this, and scholars have called for more work in this area (Quinn and Epstein, 2023). In the tradition of privacy sensemaking, a construct used to describe how women navigate fertility-related privacy online in a post-Dobbs world (Song et al., 2024), we use qualitative analyses to reveal tensions between perceptions of horizontal and vertical threats. In doing so, we elaborate privacy phenomena as they pertain to women’s health specifically and fill gaps in privacy scholarship generally by newly articulating the interconnectedness between vertical and horizontal threats. We discuss the ways that boundary fuzziness between threats may contribute to uncertainty or even privacy cynicism, the feeling that a desired level of online privacy is impossible (Hoffmann et al., 2016).
Identifying horizontal and vertical privacy threats
Managing our horizontal privacy boundaries with members of our online social networks can be challenging. The interconnected nature of online communication increases personal privacy risks, such as when people share photos without consent. The consolidation of our many distinct social groups on social networking sites—known as context collapse—can exacerbate these risks (Shi et al., 2013; Vitak, 2012). Furthermore, people may experience severe privacy violations at times, such as doxxing or hacking of their social media accounts. Thus, people must carefully, often creatively, negotiate online privacy boundaries to avoid horizontal privacy violations (Chou and Chou, 2023; Marwick and boyd, 2014).
Although vertical privacy encompasses privacy from both corporations and the government, the literature on corporate and state surveillance remains mostly separate. And although both areas of research explore the asymmetrical distribution of information and power between people and institutions (Lightfoot and Wisniewski, 2014; Zhang et al., 2024), the structures and procedures that shape these institutions differ. Nevertheless, the limited research discussing corporate and state surveillance has primarily focused on their similarities (Marwick and Hargittai, 2019; Zhang et al., 2024). Part of our goal for this piece is to better disentangle these threats.
Corporate surveillance
A system of surveillance capitalism currently exists in which corporations are incentivized to accumulate as much consumer information as possible (Zuboff, 2019), and online service providers (OSPs) employ an arsenal of tactics to do so (Acquisti et al., 2015; Draper and Turow, 2019). They use these data to improve user experience while also sharing our personal information with third parties such as data brokers or government agencies (Draper and Turow, 2019; Huq and Wexler, 2022; Zuboff, 2019). Notably, whereas the European Union has the General Data Protection Regulation (GDPR), at the time of writing, the United States has yet to pass comprehensive federal privacy legislation (Bakare et al., 2024), making American Internet users particularly vulnerable.
Given these practices, it is not surprising that many people express mistrust toward OSPs (Hoffmann et al., 2016)—four in five American adults are concerned about how companies use their personal data (McClain et al., 2023). However, compared to negotiating privacy with other individuals online, there are few mechanisms people can use to protect their privacy from corporations, and the efficacy of these methods is inscrutable (Bazarova and Masur, 2020; Masur, 2018; Quinn and Epstein, 2023). As a result, most people do little to protect their privacy from corporations and frequently cede control of their personal information to gain access to valuable online services: a privacy paradox (Acquisti and Gross, 2006; Norberg et al., 2007).
State surveillance
In 2013, whistleblower Edward Snowden revealed that the US National Security Agency (NSA) had been working with popular OSPs to access user data en masse as a means of protecting public safety following the 9/11 terrorist attacks (Lyon, 2014). Many Americans were shocked by this revelation, whereas others, such as members of marginalized communities, had long been subject to state surveillance as a mechanism of control (Franks, 2017). Since then, Americans have openly debated the ethics of broad surveillance by government agencies (Lyon, 2014; Ping Yu, 2021). In 2025, as the Department of Government Efficiency acquired sensitive data from tens of millions of Americans, the legality of which was in question (Horsley and Manuel, 2025), the privacy threat posed by the government once again sparked concern.
A growing body of research examines how people conceptualize privacy threats from the government. Many of these studies document a general feeling of being watched, often tempered with the attitude that one has nothing to hide (Marwick and Hargittai, 2019; Zhang et al., 2024). Research has also found that awareness of state surveillance stifles political expression and deters both legal and illegal activities online (Dinev et al., 2008; Oz and Yanik, 2022; Ping Yu, 2021; Stoycheff, 2016; Stoycheff et al., 2019). A few studies have focused on the specific legal consequences of revealing personal information online for undocumented immigrants or gang members in the United States (Guberek et al., 2018; Lane et al., 2018), but work on vulnerable subgroups is rare. Across the board, while some people actively resist, facilitate, or passively cope with state surveillance, many believe that it is inescapable (Albrecht et al., 2021; Fuchs and Trottier, 2017; Guberek et al., 2018; Oz and Yanik, 2022; Zhang et al., 2024).
Abortion and online privacy
Information about women’s reproductive health is among the few types of information that is of interest to a range of parties, including family members and friends, employers, healthcare providers, advertisers, law enforcement, and policymakers. Women may reveal reproductive health information to these various parties offline or, in many cases, online. In particular, women considering abortion may scour health information websites, order abortion pills online, or discuss it with others electronically (Upadhyay et al., 2022; Wilson-Lowe et al., 2024). Each of these activities leaves behind a trail of digital footprints that could be tracked by institutions or other people, thereby exposing women to privacy risks.
Even when abortion was still federally legal across the United States, records of pregnant women’s online activities were used as evidence to prosecute them for feticide (Conti-Cook, 2020). These cases almost exclusively involved low-income people of color, who have historically been more vulnerable to privacy risks (McDonald and Forte, 2022). In the post-Dobbs era, when the risk of revealing abortion information online is even greater, people who could become pregnant are understandably concerned about the privacy of their reproductive health information, but many feel powerless to protect their privacy (Cao et al., 2024; Dewan et al., 2024; McDonald and Andalibi, 2023; Song et al., 2024). Indeed, the lack of legal and corporate privacy protections for reproductive health information leaves women vulnerable to privacy threats.
Gaps in legal and corporate privacy policies
The extent to which women are aware of data privacy law and factor it into their reproductive privacy decision-making remains unknown. The Health Insurance Portability and Accountability Act (HIPAA) protects the privacy of the information Americans share with healthcare providers and insurers (US Department of Health and Human Services, n.d.), but it does not cover most information shared with OSPs (e.g. web searches, electronic messages, location data, and app usage). Because federal data privacy legislation is absent, and many states lack data privacy laws (Bakare et al., 2024), individuals, corporations, and the state can legally obtain sensitive information about people’s reproductive health. Like previous scholars who have considered privacy sensemaking regarding fertility tracking (Song et al., 2024), here we explore awareness of data privacy law as a lens through which to better understand how Internet users are distinguishing between the shape and consequences of different privacy threats.
Meanwhile, OSPs do little to fill in the gaps in privacy law and safeguard their users’ reproductive health data, though the extent to which women consider this is also unclear. For example, Google announced that it would proactively delete the location data of people visiting abortion clinics, yet investigators found that the company had continued to sell this data (Fowler, 2023). A number of online pharmacies that sell abortion pills were also sharing people’s sensitive data with third parties (Gollan, 2023). Moreover, Meta supplied law enforcement in Nebraska with the private Facebook messages of a mother and her teenage daughter as part of an investigation of an illegal abortion (Kaste, 2022). Thus, women cannot rely on institutions to protect the privacy of the reproductive health information they share online.
Horizontal and vertical privacy threats
Women are incredibly vulnerable to threats to the horizontal and vertical privacy of their reproductive health information. The boundaries between various horizontal and vertical privacy threats are especially blurred in the context of abortion post-Dobbs, as legal reach varies by state and over time, and tech companies such as Google and Meta have been reluctant to clearly outline their policies when it comes to aiding investigations into abortion law violations (Huq and Wexler, 2022). Previous scholars have acknowledged the ambiguity in how horizontal and vertical privacy threats are enacted and perceived (Crain, 2018; Dencik and Cable, 2017), but have not focused on a specific event. In focusing on abortion, we can begin to build a typology of how threat actors are perceived to work together across types in a context of high uncertainty and great consequence:
RQ. How do women assess and manage horizontal and vertical privacy threats, and the flow of information between them, in the context of seeking information about abortion online?
Methodology
Participants
Participants were recruited from the University of California, Santa Barbara (UCSB) and Indiana University, Bloomington (IU) to partake in a study on people’s use of the Internet in the context of nationwide abortion restrictions. The study was advertised via flyers, social media posts, and campus-wide email newsletters. A screener survey was used to verify whether interested students were at least 18 years of age, had a nonzero chance of becoming pregnant, and believed that abortion should be accessible in at least some circumstances.
A total of 45 cisgender women 1 participated in the interviews (24 from UCSB, and 21 from IU). The women ranged in age from 18 to 27 (median = 20). Most participants (82.2%) were sexually active, and the majority (71.1%) identified as heterosexual. Nearly half of the sample (48.9%) were in relationships, although none of them had children, were currently pregnant, or were trying to conceive. The racial and ethnic composition of the sample was fairly diverse: 48.9% identified as White/Caucasian, 44.4% Asian/Asian American, 11.1% Hispanic/Latina, 6.7% Black/African American, 6.7% Middle Eastern, and 2.2% Native American (15.6% selected more than one category). Although we do not have additional information on socioeconomic status, we note that all data represent college students, suggesting a minimal degree of class privilege in this sample.
Data collection
Interviews lasted between 30 and 60 minutes, and participants received a $20 gift card. All interviews were conducted and recorded via Zoom and transcribed using Temi, an artificial intelligence (AI) transcription software. Interview transcripts were reviewed by the research team to ensure that they were free of errors.
During the interview, participants were asked to rank the government, corporations, and other people in terms of the threat they pose to their privacy in general and explain their rationale. Later, participants were asked to imagine they found out they were pregnant and were considering having an abortion, for whatever reason that might be. Interviewers probed how they would go about finding more information about how to do that. Afterwards, participants were separately asked to imagine the negative outcomes of other people, companies, and the state, knowing that they were searching for abortion information online, and rate the severity and likelihood of each possible outcome. They were also asked if they were aware of any strategies to prevent each entity from having access to or sharing information about their reproductive health, and they rated the effectiveness and their ability to use each strategy.
Interviews took place between October 2022 and March 2023. During this period, California was one of the states offering the greatest protection of abortion rights. Meanwhile, in Indiana, state legislators had passed a near-total ban on abortion in August of 2022. A couple of lawsuits halted the policy from taking effect shortly before we began data collection, however. The future of abortion in Indiana remained uncertain over the course of this study, although abortion access in the state was nonetheless limited. Ultimately, in June of 2023, the Indiana Supreme Court ruled to uphold the abortion ban.
Data analysis
To answer the research question outlined above, the first and second authors conducted a reflexive thematic analysis (RTA; Braun and Clarke, 2019), which recognizes the active role of the researcher in knowledge production and combines inductive and deductive approaches to theory building. We followed the analytical procedure outlined by Braun and Clarke (2006), which involves (1) familiarizing oneself with the data, (2) generating initial codes, (3) generating initial themes, (4) reviewing themes, (5) defining and naming themes, and (6) producing the report. The RTA approach conceptualizes themes as “stories about particular patterns of shared meaning across the dataset” (Braun and Clarke, 2019: 592) and includes both semantic and latent themes. Examples of semantic themes in this study included mentions of specific horizontal and vertical privacy risks (e.g. targeted ads) and coping strategies (e.g. using a virtual private network [VPN]). Meanwhile, latent themes involved making inferences about participants’ feelings or emotions, such as their uncertainty about institutional surveillance.
Results
Our research question explores how young women assess and manage horizontal and vertical privacy threats and the flow of information between them when searching for abortion information online. Participants were aware that these threats vary depending on the level of abortion access in the state where one is located, underscoring the contextual dependence of privacy beliefs. Participants expressed more uncertainty about vertical privacy risks than horizontal ones and felt less able to cope with the former. They were also somewhat uncertain about the flow of information between institutions, and in general, they perceived the boundaries between various horizontal and vertical sources of privacy threats as rather blurry. Indeed, women’s responses illustrate how individuals and institutions frequently operate cooperatively and elusively to compromise privacy.
Contextualizing privacy risk
Whether considering other individuals or corporations as potential privacy threats, participants repeatedly demonstrated an awareness that privacy risks are contextually dependent. That is, participants acknowledged that the risks of searching for abortion information online, their likelihood, and their severity could vary over time as federal and state abortion policies shift. The indefinite nature of privacy risks over time was evident in the following response from a woman in California: “As of right now I would be okay, but like, I don’t know in the very near future . . . You never really know. It’s not like, ‘oh, it’s a given that we’re protected’” (P6, UCSB). That is, regardless of the location of residence, participants observed that state or federal abortion laws could evolve to complicate women’s ability to make decisions about sharing reproductive health information.
Despite this across-the-board observation of potential future privacy risks, women also observed that these risks currently varied depending on the level of abortion access in their state of residence. For example, the majority of participants from UCSB did not perceive any personal risk associated with the state knowing that they were searching for abortion information online, yet only one participant from IU shared this sentiment. Accordingly, UCSB students recognized their privilege of living in a state where abortion is largely protected: Not in my area specifically, but in other states I can definitely see the risk of um, especially arresting people who need this like medical care or medical attention. I can see it happening in other states but um, personal concern in California is not right now. (P13, UCSB)
In contrast to the general consensus regarding the legality of abortion among participants from UCSB, beliefs about the legality of abortion varied considerably among participants from IU. Nearly a third of the IU participants mentioned the legal uncertainty of Indiana’s state abortion law, and many were unsure about their degree of legal risk: That’s kind of a gray area right now because I saw something where, like, a judge had kind of overruled the overruling of, you know, of like Roe v. Wade and um, the fact that like, it was supposed to be illegal in Indiana. But I don’t know what the current laws are . . . I know that [if] necessary, somebody in the state of Indiana could travel over state lines and receive an abortion, but yeah, I really don’t know what the guidelines are right now. (P18, IU)
As this participant illustrates, the ambiguity surrounding the legality of abortion in Indiana at the time of this study made it difficult for women to precisely weigh the risks and benefits of searching for reproductive health information online.
Social privacy threats
Participants from both states, when asked about the negative consequences of other people finding out that they were searching for abortion information online, discussed experiencing conflict in their relationships, receiving unwanted input, being the subject of gossip, and facing social disapproval. Perceptions of risk likelihood and severity varied considerably depending on who they envisioned having access to their reproductive health information. For example, women believed that healthcare providers posed minimal risk, whereas participants who came from religious families or communities felt that other personal relationships could pose severe privacy risks. Women at IU were especially likely to discuss social repercussions and tended to perceive them as more severe and likely than women at UCSB.
As with online privacy management in general, participants felt that the negative consequences of other people learning about abortion information seeking were largely preventable, though risk prevention strategies were not without cost. The most cited strategy was self-censorship: “I feel like I would just be quiet about it. That’s the easiest thing. And that’s kind of sad too, because like, if I’m worried about it, I wanna get help with it” (P40, IU). Despite expressing some degree of efficacy to minimize social privacy risks, women often felt they would need to disclose their desire for an abortion in order to obtain medical care.
Institutional privacy threats
Women were more uncertain about the likelihood of negative outcomes resulting from state or corporate surveillance than they were of the likelihood of negative outcomes from interpersonal surveillance. We explore each type of institutional privacy threat, followed by a discussion of the relationship between threats.
Corporate surveillance
Many participants were able to articulate the specific risks of corporate surveillance, such as organizations that supported or opposed abortion using targeted ads to influence their reproductive decision-making. Or, in the case that they had already gotten an abortion, women worried that exposure to ads for maternity or baby products would be upsetting for them. As one woman explained, “I’d obviously be triggered by seeing that on my phone, and it would cause potentially a lot of negative emotions for me” (P38, IU). Most participants mentioned strategies that they could use to minimize these risks, including adjusting one’s privacy settings or using a private web browser or VPN. About a third were not aware of any effective strategies, and a few believed that it was impossible. Of those who offered privacy protection strategies, most felt that these strategies were effective, but a few exhibited privacy cynicism, noting that they were only effective up to a point and that corporations might not respect these preferences.
State surveillance
Participants noted various legal outcomes associated with abortion information seeking (e.g. fines, arrest, or incarceration), yet they were often rather uncertain about the likelihood of these threats or how to protect against them. Specific concerns included fear of legal risks involving bodily autonomy, such as states restricting travel for pregnant people or forcing them to carry pregnancies to term. Another repeated concern was monitoring by state agencies, though this risk was only discussed by women at IU: I could absolutely see a scenario in which your name is added to a list of people that are searching for it. Um, and you’re kinda on like the higher watch, like what they’ve done with potential terrorists or threats to security, putting people on watch lists based on what information they’re searching or what information they’re texting about. I could absolutely see [this] being a possibility. (P37, IU)
Another participant articulated how this surveillance could evolve into the state preventing people from accessing abortion information, stating, “I feel like . . . you would be pinged for searching up that information, and then you might even be tracked or followed” (P38, IU). Hence, the negative outcomes of state surveillance are not always tangible; at times, they can include feelings of discomfort or inhibition from engaging in a certain behavior.
Despite awareness of reproductive privacy risks from the state, women expressed a high degree of uncertainty about state surveillance practices, the likelihood of these resulting in privacy risks, and strategies for preventing risks. As one IU student noted, I don’t know a lot about what goes on with the government and, um, for me, I’m very scared of the unknown. Um, it’s a kind of a giant question mark for me. So I would rather that . . . as little identifying information and valuable information, only the information that is necessary should be able to be accessible. It’s just a little scary, just I guess a little like power imbalance, me being just a regular civilian. (P1, IU)
This quote illustrates how the lack of transparency into state surveillance practices creates a sense of powerlessness, a key element of privacy cynicism (Hoffmann et al., 2016). Thus, the concept of privacy cynicism applies to the state in addition to OSPs. Moreover, few participants provided strategies to protect their privacy from the state—nearly half said that they were not aware of any, and several more believed that it was impossible to circumvent state surveillance. Those who did mention state privacy protection strategies discussed using a VPN, going offline for abortion information, or engaging in collective action to fight for expanded privacy rights.
In sum, women felt that they had more agency when it came to protecting their privacy from corporations compared to the state, and they demonstrated greater privacy cynicism about state threats. The contrast between women’s beliefs about corporate versus state privacy threats in the context of abortion underscores the importance of differentiating between these sources of institutional surveillance.
Cooperative privacy threats
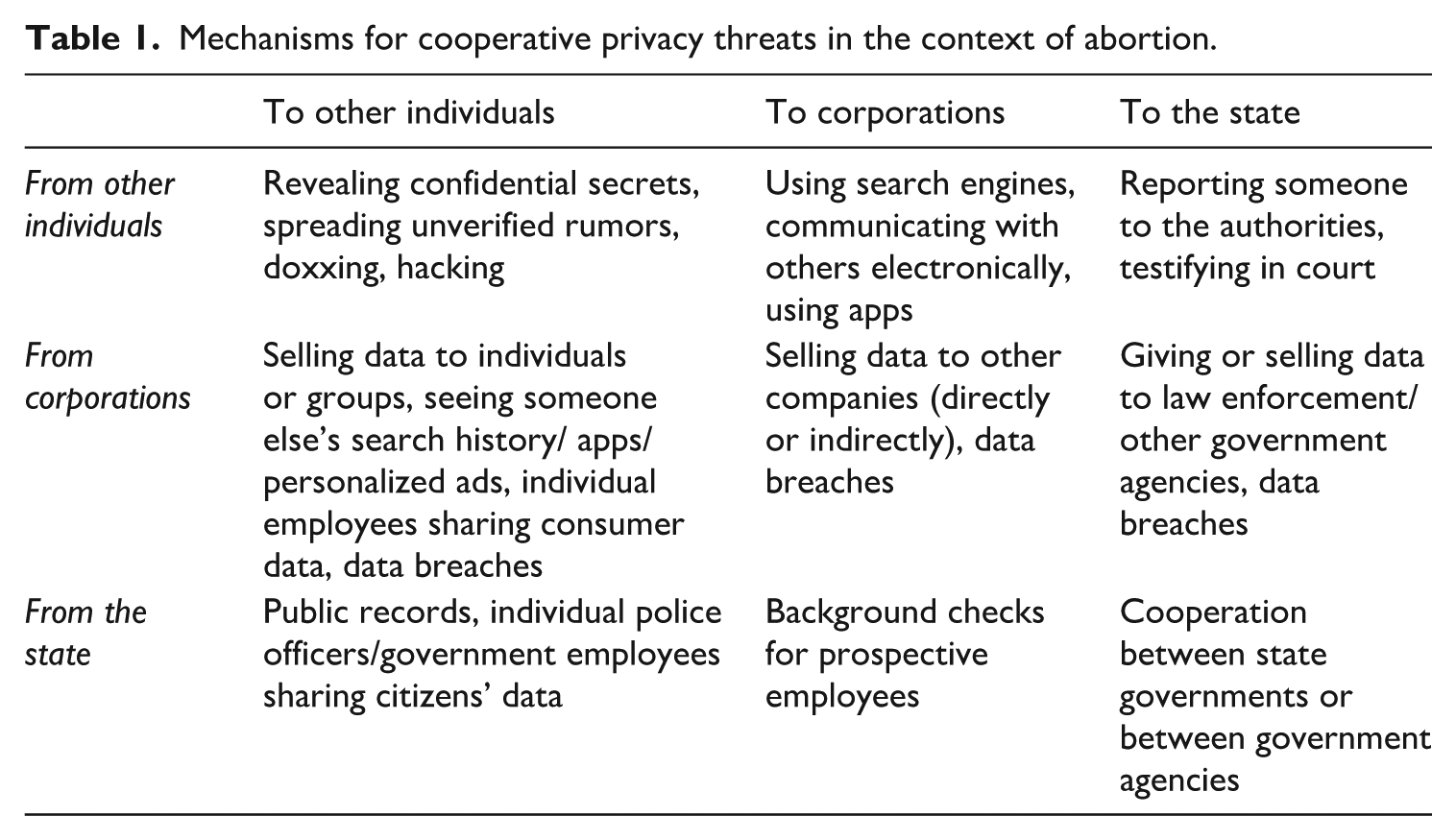
We argue that the boundaries between these threat actors are perhaps more fuzzy than previous works have delineated. Many of the women in our sample observed that cooperation between corporations, the state, and individuals amplifies privacy risks in the context of abortion. Their interconnectedness via numerous pathways enables information to flow between them, compounding the potential for risk (see Table 1). These cooperative privacy threats emerge as individuals and institutions operate jointly, with or without a concerted effort, to complicate the process of searching for abortion information online. As a result of fuzziness in the boundaries between threats, it may be harder for women to protect against a given threat, and it may become easier for any single actor within these information-sharing networks to skirt responsibility when women are harmed. We expand on a few illuminating examples of cooperative privacy threats and their mechanisms below.
Mechanisms for cooperative privacy threats in the context of abortion.
Other people pose legal risks
As an example of cooperative privacy threats between vertical and horizontal sources, several participants mentioned indirect legal consequences of other people knowing that they were searching for abortion information online. For instance, some noted that other people could report them to the authorities or testify against them in court. A few participants were also concerned about implicating loved ones or benevolent strangers online if they were to share that they were seeking an abortion or enlist their help. Participants observed that this fuzziness between the privacy threats posed by other people and the state could have a chilling effect on people offering help to abortion seekers online: I think people would be less likely to offer help to those in need . . . When Roe v. Wade was overturned, people in Illinois were reaching out and saying, “Oh, my home is open. If you wanna get an abortion and come to Illinois, you need a place to stay.” And a lot of people were, yeah, being very helpful, and they’re like, if you need money, resources, et cetera. I think people would stop doing that if they had, if they knew that the law had access to their info or private conversations. (P10, IU)
This response reflects the indirect consequences of cooperative privacy threats from individuals and the state, such as a disinclination to help one another and an erosion of trust in other people.
Furthermore, when participants considered the possibility of the government knowing that they were searching for abortion information, a few participants discussed how the severity of legal outcomes depended on the personal beliefs of the officers involved: I definitely think that, especially in Indiana . . . small town law enforcement, um, they don’t get their stereotype all the time from nothing. So, I think having that information in their hands would lead to, um, definitely some kind, I don’t wanna say retaliation, but definitely a more watchful eye than is ever appropriate. (P36, IU)
The response above points out how institutions such as government agencies and corporations are ultimately composed of individuals with an assortment of ideologies. This and the fact that the state may work with private citizens to enforce the law further underscore the lack of clear distinctions between vertical and horizontal privacy risks.
Uncertainty about cooperation between institutions
Because studies examining online privacy rarely explore people’s beliefs about various sources of institutional surveillance simultaneously, little is known about how people conceptualize the flow of information between institutions. Yet in our study, several participants explicitly discussed the relationship between corporations and the government. For a couple of them, the two were indistinguishable: “I almost kinda wanna put government and corporations together cause I just feel like they both just have such close ties” (P46, IU). Participants understood that the government was dependent upon corporate infrastructure to access people’s information, though it was unclear how the government obtained that information. Some believed that corporations sold their data to the government, some believed they supplied it freely, and others did not specify or expressed uncertainty about how this process works: [Corporations] collect your data and then, um, you know, somehow the government gets it, whether it’s sold to the government or given to the government or whatever agreement there is there . . . the corporations are the ones collecting it and deciding how it can be distributed to the government. (P18, IU)
As this first half of this quote illustrates, the mechanisms by which corporations supply consumer data to the state are ambiguous. In the second half of this quote, P18 recognizes that since corporations are the ones collecting people’s information, they ultimately have the power to control the flow of information to the state. Thus, the outcome (i.e. the cooperative privacy threat) is perhaps more important than the process by which institutions exchange information.
Furthermore, participants saw corporations as pseudo-political actors, with the power to help or hinder state investigations: In America especially, big corporations do have ties to the political realm and they do have lobbyists . . . and I think that they do have more of my information than the government does. So that could potentially lead to bad situations if they decide to take a stand. I don’t know of any companies, any big companies who have taken stands like that as of yet, but based on how much information they have, I think it is a risky situation. I think if they were forced by the law to hand over that kind of information, that could be really bad . . . they have a lot of power, but – and they are above the law in some cases – but also like on paper, they’re not above the law. (P10, IU)
This response poses the possibility that corporations might embrace anti-choice policies and work with states to exacerbate privacy risks for pregnant people, though the respondent appears uncertain about the likelihood of that possibility. Other participants believed that corporations would find it in their best interest financially to comply with the state, resulting in a cooperative privacy threat: “I don’t trust companies a lot with data privacy. I think that because so much of it is regulated by the government, um, if the government said, hey, we need access to this, they would have to do it” (P37, IU). In contrast, another participant recalled: There’s a precedent of private companies in the US kind of refusing to infringe on users, you know, like personal data and their rights. You know, [disclose their information] to the government. I remember . . . someone was suspected of being a terrorist, and the police wanted Apple to unlock their iPhone, but Apple refused. (P5, IU)
This participant, though appreciating the possibility of cooperative privacy threats, believes that corporations might resist pressure to comply with the state when investigations of abortion ban violations are underway. Greater awareness of examples such as these could potentially reduce privacy cynicism.
Vertical privacy is bidirectional
Finally, vertical privacy is typically characterized as a one-way flow of personal information from individuals to platform providers and, eventually, third-party institutions such as data brokerage firms, advertising partners, or law enforcement agencies (Bazarova and Masur, 2020). Our data demonstrate how one’s information can flow back “down” from these institutions into the hands of individuals or groups. For example, one participant mentioned the possibility that other people could accidentally oversee abortion-related advertisements on her personal device. More alarmingly, another participant imagined that if corporations such as social media platforms or search engines knew that she was searching for abortion information, “They could easily sell it to a religious group, and then they would know all your information . . . There’s so many different avenues that could go down, or they could even tell the government” (P45, IU). This participant, like several others, demonstrated a high degree of privacy literacy through her awareness of data brokers and their practices. Specifically, P45 recognized that by legally accessing women’s personal information through the data marketplace, abortion opponents could identify abortion seekers and possibly use that information to cause them harm.
Just as reproductive health information collected by platforms can flow to individuals, so too can information collected by the state. Should a pregnant woman who miscarries or seeks an abortion find herself in court following an investigation by law enforcement, this information would become available in public records. Individuals ranging from nosey neighbors to reporters to potential employers could then access this information, posing a variety of negative outcomes. “Sometimes workplaces do background checks for that type of information to see if you had like, a history with like, the police, and that would also impact their employability in the future,” explained a participant (P22, UCSB). This was a rare instance in which a participant discussed a financial privacy risk, underscoring the compounded, wide-ranging risks that can occur as a result of cooperative privacy threats. In sum, public records of court cases revealing details about women’s reproductive health further illustrate the complex interrelationships that emerge as information flows between individuals and institutions.
Discussion
These data elaborate on privacy scholarship on horizontal and vertical privacy threats through the lens of abortion in a post-Dobbs era. Because abortion is both highly personal and highly politicized, and because the legal status of abortion is now in flux in many states across the United States, it is a particularly potent lens through which to explore how people grapple with the uncertainty of privacy threats from different sources, both interpersonal and institutional (see Bazarova and Masur, 2020; Raynes-Goldie, 2010). In particular, we use an inductive analysis to explore how women distinguish and respond to personal, corporate, and government threats to privacy related to abortion, and how those responses may differ depending on the variability in the legal status of abortion in their state of residence. In doing so, we provide a new conceptual device, cooperative privacy threats, to capture the often indistinguishable relationship between vertical and horizontal privacy threats of different forms. The hope is that by foregrounding the interdependence between threat types, we move both theory and intervention design forward.
To start, we found that women in both locations expressed uncertainty about their abortion rights, though this uncertainty was heightened for women living in Indiana, where abortion policy was in flux at the time of data collection. We then turned to assessing discrete reactions to interpersonal, corporate, and government privacy threats in relation to abortion. Perceptions of social privacy risks varied in likelihood and severity, and women suggested self-censorship as an effective though flawed coping strategy. There was greater uncertainty about how to negotiate institutional privacy threats, which included pregnancy- or abortion-related ads from corporations and increased surveillance or penalties from law enforcement. Women also felt less equipped to prevent privacy risks from institutions compared to those from other people. These findings thus respond to previous calls for evidence that people feel more helpless when it comes to managing their vertical privacy compared to their horizontal privacy (Quinn and Epstein, 2023), and they derive from one of only a few studies to compare institutional threats side by side.
Perhaps most striking, however, was the consistent awareness that privacy threat actors work together, heightening the ambiguity in who is responsible for privacy risks and how to protect against them. These cooperative privacy threats can include cooperation between social and institutional actors or, in other cases, corporate and state institutions. For example, participants noted how individuals could cooperate with law enforcement to inflict legal penalties on abortion seekers, as Texas encourages with their abortion law (Johnson, 2021). Women were also cognizant of the possibility of cooperation between OSPs and the state when it comes to investigating abortion law violations. Finally, participants discussed ways in which information could flow from institutions to individuals, demonstrating the overlooked bidirectional nature of vertical privacy.
The concept of cooperative privacy threats extends previous scholarship on the ambiguity and interconnectedness of privacy threats stemming from corporate dataveillance (Crain, 2018) and government use of that data (Dencik and Cable, 2017), as well as work on privacy sensemaking (Song et al., 2024), which has investigated how women interpret the risks associated with fertility tracking apps. These scholars have all observed perceptions of fuzzy boundaries between actors in the data economy to varying degrees. However, to our knowledge, most of that work has emphasized fuzziness between the government and corporations. Moreover, this is the first time that partnerships between individual, state, and corporate threat actors have been presented as a typology (Table 1). Although this typology was crafted in response to abortion-related privacy concerns specifically, these threats are likely to generalize to other contexts. Indeed, similar cooperative threats have been used to prosecute young men of color for urban violence (e.g. Lane et al., 2018). By providing a construct label for this type of cooperation and creating a typology of specific forms of cooperation, scholars may more effectively theorize and test other specific threat-response relationships, which can be used to improve theory as well as design effective interventions. As one example, previous scholars have theorized the self-censorship effects of dataveillance (Büchi et al., 2022), which our findings also supported. However, by focusing on a high-stakes context such as abortion, these data point to tensions that arise when self-censorship must be balanced with urgent healthcare needs that depend on personal and institutional communication.
The unstable abortion landscape across the country in recent years has posed a rare and understudied test case for exploring how people cope with privacy threat uncertainty in a highly dynamic context. But our findings may extend to other domains in which people consider sharing sensitive information online in a changing legal landscape, as for example, many states have introduced age verification laws restricting access to Internet pornography (Age Verification Providers Association [AVPA], 2025). Theoretical appreciation of this dynamism will likely continue to be relevant in years to come as the role of government in protecting and threatening consumer privacy continues to evolve.
In sum, we propose that this construct of cooperative privacy threat may be particularly timely. The interconnectedness of OSPs and state institutions has risen to the fore in recent months in the case of the new Department of Government Efficiency that was built in part by the owner of a tech company (Horsley and Manuel, 2025) or as witnessed by the use of public mortgage data to single out political figures (Lieber and Bernard, 2025). By highlighting the integrated nature of threats between state, corporate, and individual social actors, scholars can and should continue to identify systematic patterns of collaboration, systematic patterns of response by individual citizens, and, perhaps as a result, ways to educate Internet users on those threats. And although policy protections against online privacy threats have long been absent in the United States, the increased visibility of cooperative privacy threats may give rise to new innovation in this arena by policymakers, privacy advocates, and consumers.
Limitations and conclusion
Although these data are not generalizable given nonrandom sampling procedures, they serve an inductive role in theory building. Qualitative data are useful in identifying phenomena that are not categorically defined; translating these ideas into quantitative tests will be necessary, but challenging. By highlighting nuances in how individuals—in this case, women of childbearing age—respond to a dynamic online privacy threat related to abortion, these findings offer new ways of thinking about online privacy that elaborate existing theory and suggest ways for future empirical tests. Certainly, given the rapidly changing abortion legal landscape, the time frame in which these data were collected likely influenced the data to some degree, particularly in Indiana, as the laws there were still being challenged in court. Subsequent research should test whether people are more uncertain about protecting themselves from state privacy versus corporate privacy threats in other contexts, making these theoretical claims more robust, and helping to identify appropriate real-world interventions. Future scholars should also continue to test and refine the idea of cooperative privacy threat to determine whether systematic modes of cooperation are identifiable between actors, and whether cooperative threats are indeed perceived as more threatening than independent ones, as these data suggest.
Footnotes
Acknowledgements
We would like to thank our research assistants Samiksha Boranna, Zachary Dietz, Sydney Fung, Chloe Osborn, and Serena Patel for their invaluable contributions to this research. We would also like to thank Dr. Nicole Martins at Indiana University Bloomington for her assistance with participant recruitment.
Data availability statement
Due to the sensitive nature of the topics discussed in this research, participants were assured that the information they provided in their interviews would be kept confidential among the authors of this study. Therefore, we are unable to share these data without violating their terms of consent.
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
Ethical approval
This research was reviewed and approved by the Institutional Review Board of the University of California, Santa Barbara (Protocol # 19-22-0532) on 19 August 2022.
Informed consent
Respondents provided their informed consent before starting interviews.
