Abstract
Drawing from protection motivation theory (PMT), this study explored subgroups of Internet users based on their patterns of privacy threat and coping appraisals (i.e. perceived severity, perceived vulnerability, perceived benefits, self-efficacy, response efficacy, and response cost) in the context of targeted advertising. A latent profile analysis using a nationally-representative sample of US adults revealed three meaningful subgroups: Privacy-Optimistic, Privacy-Cautious, and Privacy-Balanced. These profiles differed in privacy protection intention, with Privacy-Cautious individuals reporting the highest intention, followed by Privacy-Balanced and Privacy-Optimistic individuals. In addition, higher perceived surveillance was associated with higher odds of being in the Privacy-Cautious and Privacy-Balanced (vs Privacy-Optimistic) profiles. Higher privacy powerlessness was also associated with higher odds of being in the Privacy-Cautious (vs Privacy-Optimistic) profile. Findings theoretically extend PMT and previous privacy research by highlighting the heterogeneity in users’ online privacy appraisals, and practically inform more tailored intervention and message designs.
Keywords
Dataveillance refers to “the systematic use of personal data systems in the investigation or monitoring of the actions or communications of one or more persons” (Clarke, 1988: 499). Contemporary dataveillance has expanded into mass forms of data acquisition and exploitation that sustain surveillance capitalism (Zuboff, 2019) and cultivate the digital surveillance economy (Clarke, 2019). One key manifestation of the digital surveillance economy is behaviorally-targeted advertising, in which machine-learning algorithms enable automated and continuous tracking, analysis, and profiling of user data to personalize content and optimize ad relevance based on individual characteristics and interests (Büchi et al., 2022; Strycharz and Segijn, 2022). Despite potential benefits of targeted advertising (e.g. financial gain and convenience), dataveillance practices pose various threats to privacy and democracy (Clarke, 2019; Zuboff, 2019). At the individual level, people report heightened privacy concerns, feelings of cynicism and powerlessness, discomfort with algorithmic profiling, distrust toward social media executives, and loss of autonomy (Büchi et al., 2022; Hoffmann et al., 2016; Lutz et al., 2020; Segijn and Van Ooijen, 2022; Strycharz and Segijn, 2022). And at the societal level, dataveillance creates challenges for existing privacy-regulatory frameworks and broader threats to democracy (Clarke, 2019; Zuboff, 2019).
Critical and sociological frameworks within surveillance studies have laid a solid theoretical foundation for studying the societal implications of dataveillance, particularly in relation to power dynamics, governance structures, historical underpinnings, and the political economy (Clarke, 2019; Couldry and Mejias, 2019; Thatcher et al., 2016; Zuboff, 2019). However, to understand factors that motivate or discourage users’ online privacy protection vis-à-vis targeted advertising at the psychological level, we turn to protection motivation theory (PMT) (Rogers, 1975, 1983), which focuses exclusively on the cognitive processes underlying human decision-making. PMT posits that individuals appraise the threat of a risk and their coping potential to guide the extent to which they engage in protection behaviors. Although PMT is informative in explaining online privacy phenomena, the predictive power of its appraisal factors has received inconsistent support (see Boss et al., 2015; Haag et al., 2021; Mou et al., 2017, 2022). For example, while van Ooijen et al. (2024) found response efficacy (i.e. perceived effectiveness of protection mechanisms) to be a negative predictor of privacy protection behaviors, Boerman et al. (2021) found it instead to be a positive predictor.
The first goal of this study is therefore to provide insights into such empirical inconsistencies. To do so we adopt a novel person-centered approach by conducting a latent profile analysis (LPA), which allows us to uncover meaningful subgroups of Internet users based on their privacy appraisal patterns and to understand how these latent profiles differ in privacy protection intention. In addition, we examine perceived surveillance and privacy powerlessness – two recently-conceptualized constructs vis-à-vis institutional privacy threats – as covariates of users’ latent profile membership. Findings can shed light on how these novel psychological mechanisms correspond to users’ threat and coping appraisals of targeted advertising. Theoretically, this study extends PMT and privacy research by highlighting the heterogeneity in users’ online privacy appraisals. Practically, findings can inform more tailored privacy protection intervention designs to target subgroups of Internet users.
Protection motivation theory
PMT (Rogers, 1975, 1983) was developed to understand how people respond to fear appeals in persuasion contexts. Rogers (1975) proposed that a fear appeal message describing the magnitude of issue noxiousness, probability of occurrence, and efficacy of recommended response should trigger audiences’ cognitive processes involving (1) perceived severity (i.e. how harmful the outcome is perceived to be), (2) perceived vulnerability (i.e. how likely the harmful outcome is to occur to self), and (3) response efficacy (i.e. how effective a recommended behavior is in removing the threat), which then impact protection motivation. Rogers (1983) later refined the theory by including (4) intrinsic and extrinsic rewards of engaging in a maladaptive response, (5) self-efficacy of engaging in an adaptive behavior (i.e. how confident one feels about their own ability to engage in a behavior), and (6) response cost of adopting a recommended behavior. Therefore, the full PMT nomology includes two sets of cognitive appraisals: threat appraisals (i.e. perceived severity, perceived vulnerability, and perceived benefits of engaging in a maladaptive response) and coping appraisals (i.e. response efficacy, self-efficacy, and response cost).
Empirical inconsistencies in online privacy
Applications of PMT to studying online privacy phenomena generally lend support to its predictions (e.g. Boerman et al., 2021, 2024; van Ooijen et al., 2024); however, empirical inconsistencies have been identified (see Boss et al., 2015; Haag et al., 2021; Mou et al., 2017, 2022). For example, van Ooijen et al. (2024) found that perceived severity and privacy self-efficacy vis-à-vis general Internet privacy positively, and response efficacy negatively, predicted protection behaviors, whereas perceived vulnerability, perceived benefits, and response cost did not. Conversely, Boerman et al. (2021) found that privacy self-efficacy did not, but response efficacy did, positively predict privacy protective behaviors. Conceptualizing privacy behavior as self-disclosure and self-withdrawal, Meier et al. (2020) found that perceived severity and response efficacy positively predicted Facebook users’ self-withdrawal, and perceived benefits and privacy self-efficacy positively predicted their self-disclosure.
Scholars attributed these empirical inconsistencies to various theoretical and analytical decisions. For example, incorporating the full (vs part of) PMT nomology, including a fear appeal manipulation (vs not), integrating other theoretical constructs (thus introducing additional covariates), and choosing general (vs specific) measures of PMT constructs might all influence the relationships found (Boss et al., 2015; Haag et al., 2021; Mou et al., 2022). Other factors that might shape how people evaluate and respond to online privacy risks include individual differences in privacy cynicism, culture (e.g. Eastern vs Western), context (e.g. organizational vs individual information security), and sample characteristics (e.g. students vs adults) (Mou et al., 2017; van Ooijen et al., 2024).
Nonetheless, in the online privacy context, evidence is sufficient to reject Rogers’ (1975) initial assumption that all PMT appraisals are equally potent in predicting behavioral change; rather, the predictive power of each appraisal remains inconsistent, and in some cases contradictory, in understanding privacy behavioral outcomes.
A latent profile approach to testing PMT
Along the lines of focusing on individual characteristics, LPA provides a promising yet underutilized approach to reconciling these empirical inconsistencies (Krawietz and Pett, 2023; Nylund-Gibson and Choi, 2018). With LPA, we can uncover profiles or subgroups of online privacy appraisals based on unobserved similarities in people’s response patterns and thus test the relationships between PMT appraisals and privacy behaviors with a person-centered perspective in mind. An LPA approach thus extends PMT and past research by providing a novel lens of theorizing online privacy protection.
Indeed, PMT was developed to understand the relationship between each appraisal factor and protection motivation, and assumes that the population is homogeneous and thus responds to privacy threats similarly (Rogers, 1983). As a result, PMT does not highlight the heterogeneity of privacy appraisals among different subgroups that may shape their privacy behavior differently. Our study aims to fill this gap in the PMT and privacy literature by exploring latent profiles of PMT appraisals and testing how they differ in privacy protection intention, which allows us to directly speak to the empirical inconsistencies.
Latent profiles of privacy protection appraisals
Despite communication scholars’ increasing interest in adopting a latent variable mixture modeling approach (see Krawietz and Pett, 2023), applications of LPA to study online privacy phenomena are rare. Of note, Lin (2019) studied latent classes of Facebook users’ online social interactions (e.g. emotional self-disclosure, commenting) and their implications for social capital building and well-being. However, the class indicators of this study are different types of social interaction behaviors, which do not shed light on the cognitive appraisals underlying privacy protection. Two other studies have adopted a cluster analysis approach to similarly understand subgroups in various privacy contexts. For example, Kang and Jung (2021) revealed three clusters of smart watch users – ambivalent, benefit-oriented, and neutral – based on their privacy concerns, perceived hedonic and utilitarian benefits. Voorveld et al. (2024) identified four clusters of social media ad consumers – the Control Paradox, Fatigued, Uninformed but Critical, and Skilled and Critical – based on their algorithmic awareness, perceived appropriateness of algorithmic persuasion, and coping ability. Nonetheless, we are aware of no existing studies that adopt an LPA approach to studying PMT’s cognitive appraisals, despite the various methodological advantages LPA offers over cluster analysis (see the online supplementary material [OSM], Section 1, for a discussion of these benefits).
In targeted advertising, various latent PMT appraisal profiles may be uncovered. For example, one profile might report particularly high perceived severity and vulnerability, but low response and self-efficacy. This is because individual users may develop the belief that they do not have control over what data is being collected by advertisers, despite high privacy concerns (Hoffmann et al., 2016). Another profile may report low perceived severity and vulnerability but high perceived benefits of self-disclosure and self-efficacy. This can be explained by the extended privacy calculus model that says individuals weigh the benefits of self-disclosure, privacy risks, and privacy self-efficacy to determine the extent to which they may engage in protective behaviors (Dienlin and Metzger, 2016). Individuals in this profile may prioritize the benefits of targeted advertising over risks, as they feel confident about their privacy protection ability. However, given that LPA is exploratory in nature (Masyn, 2013, see OSM Section 2 for a discussion), we pose the following:
RQ1: What types of privacy protection appraisal profiles can be identified based on perceived severity, perceived vulnerability, perceived benefits, privacy self-efficacy, response efficacy, and response cost?
Profile differences in privacy protection intention
Once latent privacy appraisal profiles are identified, our central goal is to test how they differ in shaping privacy protection behaviors to help shed light on the empirical inconsistencies discussed earlier. We argue that previous research tends to consider the isolated effect of each PMT appraisal on privacy behavior, although extant theory and research suggest that these appraisals should operate in tandem. For example, building upon PMT, the extended parallel process model (EPPM, Witte, 1994) predicts that people engage in danger control (e.g. proactive privacy protection) in high threat and high efficacy conditions, whereas they engage in fear control (e.g. defensive avoidance) in high threat but low efficacy conditions. Similarly, Meier et al. (2023) showed that perceived risks and benefits interacted to impact people’s adoption of the COVID-19 contact-tracing app; those who reported higher benefits but lower risks used the app the most frequently, showing that these appraisals intricately interact to impact privacy behaviors.
A latent profile approach allows us to consider the full set of PMT appraisal factors in tandem and to understand how different subgroups may respond to privacy risks differently, which previous research fails to account for. As one example, according to EPPM, people in a profile with higher response and self-efficacy than perceived severity and perceived vulnerability may be especially proactive in privacy protection, whereas those with high threat but low efficacy perceptions may indicate a lower privacy protection intention. Therefore, we ask:
RQ2: How do privacy protection appraisal profiles differ in privacy protection intention?
Covariates of latent profiles of privacy protection appraisals
In addition to uncovering latent privacy appraisal profiles, LPA also allows us to understand how certain factors (as covariates) might be more or less meaningful to different profiles. The second goal of this study is thus to examine the covariates of privacy appraisal profiles. We specifically focus on two recently-theorized constructs – perceived surveillance (Strycharz and Segijn, 2022) and privacy powerlessness (Lutz et al., 2020)—that reflect unique psychological responses people develop vis-à-vis institutional privacy threats in targeted advertising. Findings theoretically contribute to PMT by shedding light on the psychological antecedents of threat and coping appraisals and to research on perceived surveillance and privacy powerlessness by elaborating on their impact on subsequent user cognitive responses.
Perceived surveillance
Perceived surveillance refers to the feeling of being monitored, listened to, or that personal information is being collected by institutional actors (Segijn et al., 2022). The dataveillance effects in advertising landscape (DEAL) framework (Strycharz and Segijn, 2022) theorizes perceived surveillance as a central mechanism that explains people’s responses to targeted advertising. The theoretical rationale of the DEAL framework is as such: (1) people develop surveillance beliefs based on their lived experiences or through literacy training; (2) such beliefs are activated via exposures to observable instances of dataveillance (e.g. getting an ad immediately after searching for a similar product) that (3) trigger perceived surveillance, which then (4) impacts users’ subsequent cognitive, affective, and behavioral surveillance responses (Strycharz and Segijn, 2022).
Particularly relevant to the current study are different types of cognitive responses to perceived surveillance. Strycharz and Segijn (2022) proposed that cognitive responses include privacy risks and perceived benefits associated with targeted advertising, which conceptually overlap with PMT’s threat appraisals. Indeed, those who feel constantly surveilled may report high perceived severity and vulnerability because the threat feels particularly unrelenting and omnipresent; greater perceived surveillance may also reduce benefit perceptions via the cost-benefit calculus. Wang et al. (2025) demonstrated these relationships by finding that perceived surveillance is positively associated with perceived risks of personalized advertising and negatively associated with perceived benefits. Still, more research is needed to examine how perceived surveillance relates to other cognitive surveillance responses (see Strycharz and Segijn, 2022).
We thus extend the DEAL framework by proposing that perceived surveillance should relate to PMT coping appraisals as well (i.e. response efficacy, privacy self-efficacy, and response costs). That is, feeling that dataveillance is relentless and that data collection is intrusive likely highlights the limitations of existing mechanisms and individual capacity for privacy protection, as well as the costs of engaging in protective steps. Though these relationships have yet to be empirically tested, Wang et al. (2025) found that perceived surveillance is positively associated with users’ interest in ad transparency information and desire for privacy regulation, suggesting that perceived surveillance prompts a greater desire for additional privacy-regulatory efforts, likely due to people’s lowered efficacy perceptions. Understanding how perceived surveillance relates to PMT appraisals also extends PMT because individuals’ threat and coping perceptions likely change as a result of perceived scope or normalization of dataveillance.
Privacy powerlessness
A major harm of dataveillance is the undermined individual agency and control over privacy. Recent research shows that institutional dataveillance practices often render users’ control mechanisms ineffective, and exposures to relentless and uncontrollable privacy risks over time cultivate feelings of mistrust, uncertainty, and powerlessness vis-à-vis privacy (Hoffmann et al., 2016; Lutz et al., 2020). In response, people may choose to resign from rather than engage in privacy protection (Choi et al., 2018). Privacy powerlessness encompasses users’ perceived incapacity to protect themselves from privacy threats online, and has been demonstrated to be the most central subdimension of privacy cynicism (Lutz et al., 2020).
While the negative impact of privacy powerlessness (and related constructs) on privacy behaviors has been demonstrated (Cho, 2022; Choi et al., 2018), less is known about the psychological outcomes of privacy powerlessness. One exception is Khan et al. (2023), who found that privacy cynicism negatively predicted social media satisfaction but did not predict trust in social media companies. However, research suggests that privacy powerlessness may also impact people’s subsequent threat and coping appraisals. Lutz et al. (2020) claimed that privacy cynicism allows users to “overcome or ignore privacy concerns and engage in online transactions, without ramping up privacy protection efforts” (p. 1173). This implies that privacy cynicism as a coping mechanism may lower or even discount people’s threat perceptions. In our study, then, privacy-powerless individuals may report lower perceived severity and vulnerability because doing so allows them to reconcile the discrepancy between their high privacy concern and a lack of privacy protective behavior. Privacy powerlessness may also lead people to reason that the benefits of personalized advertising outweigh the privacy risks, since nothing can be done to protect privacy anyway.
In addition, scholars argue that, in response to privacy risks, people who experience high privacy cynicism, helplessness, and fatigue tend to expend minimal cognitive resources, ignore privacy protection options, and resign themselves to the most effortless solution (Cho, 2022; Choi et al., 2018), which suggests that privacy-powerless individuals likely also lower their coping perceptions. For instance, privacy powerlessness may lower response and self-efficacy because people may believe that no actions will effectively mitigate the threat, and that they have no control over privacy. Privacy powerlessness may also elevate response costs, as individuals may conclude that investing time and energy in privacy protection is not worthwhile. Studying privacy powerlessness as an antecedent of PMT appraisals thus advances PMT by showing how people’s threat and coping appraisals evolve when the assumption of individual agency is challenged. Despite these speculations, there is no previous research upon which to base clear predictions. Therefore, we ask:
RQ3: How are a) perceived surveillance and b) privacy powerlessness associated with privacy protection appraisal profiles?
A conceptual model of our research is shown in Figure 1.
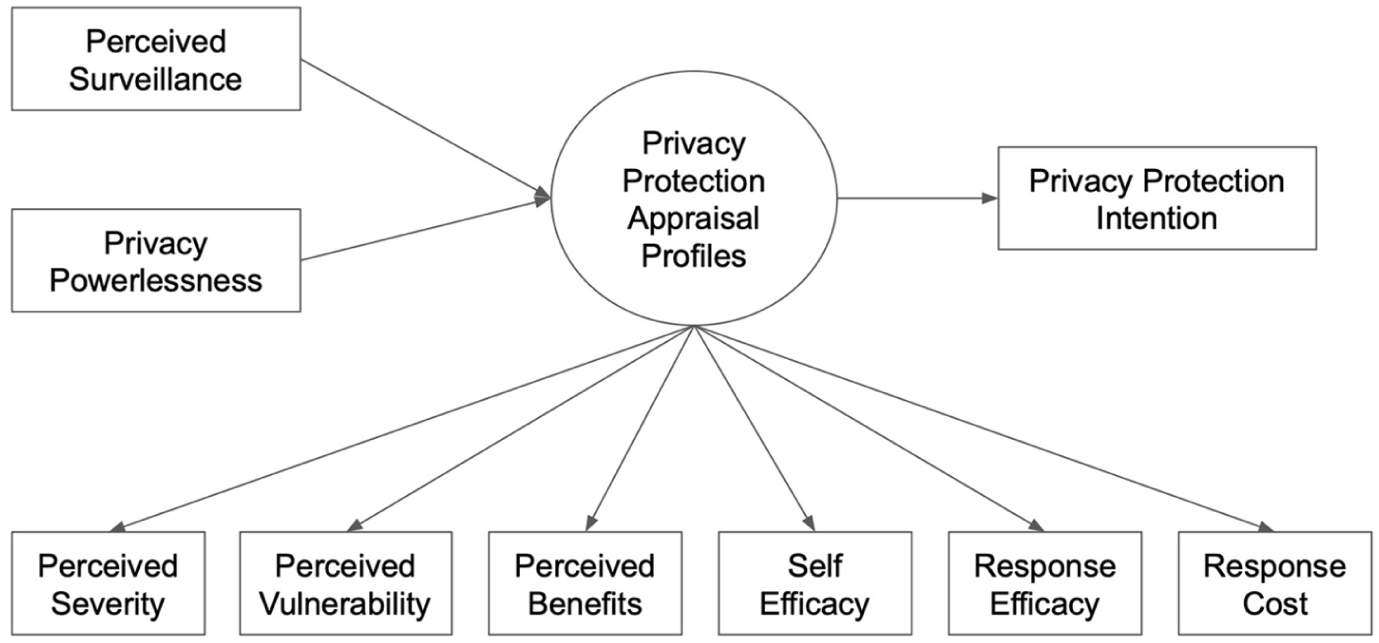
Conceptual model.
Method
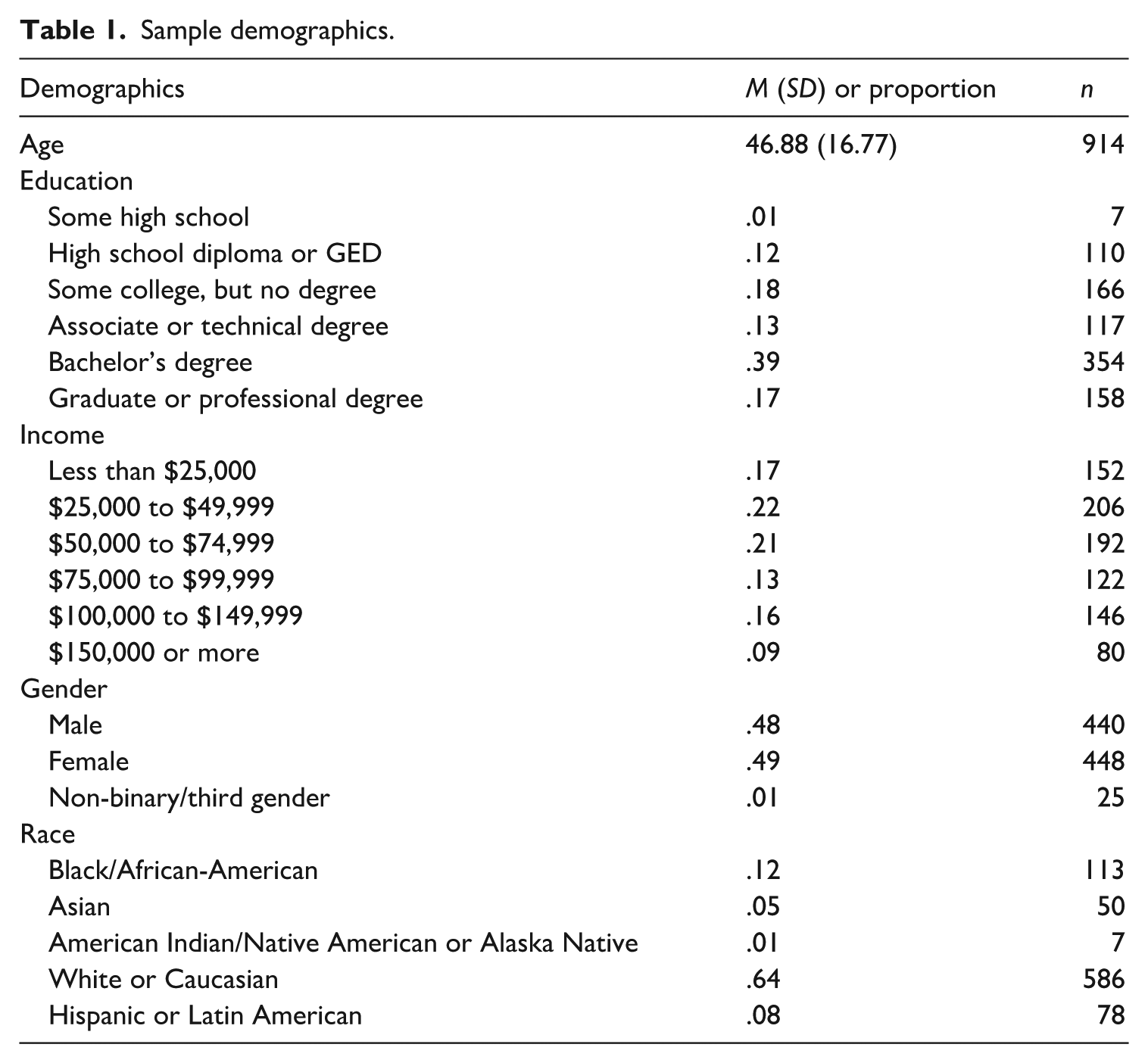
Upon IRB approval, an online survey was conducted on Prolific in March 2024. A nationally-representative sample of US adults (N = 1033) was recruited. Participants were informed of the study’s focus on targeted advertising. To ensure data quality, data cleaning was performed following methodological guidelines (McPhee et al., 2022) to eliminate the data of those who did not complete the survey (n = 23), finished the survey in less than 1/3 of the median complete time (n = 4), and failed either one of the two attention check questions (n = 87), resulting in a final sample of 918 participants (see Table 1 for sample demographics).
Sample demographics.
Measures
All measures were adapted from previously-validated scales in the targeted advertising context and measured on a 7-point scale. See OSM for a complete list of survey items.
Latent profile indicators
Perceived severity was measured using three items adapted from Boerman et al. (2021) that asked the extent to which participants felt targeted advertising was a severe problem for them, such as “Having companies collect my personal information for targeted advertising is a problem for me” (α = .94). Perceived vulnerability was measured by adapting seven items from previous research (e.g. Segijn and Van Ooijen, 2022; Van Ooijen et al., 2024) that asked the extent to which participants felt they could personally be harmed by personalized ads (α = .85). Perceived benefits were measured with seven items that asked participants how much they agreed that they personally benefited from personalized ads for various reasons, such as “make me aware of products, services, or ideas that might benefit me” (α = .93) (see Segijn and Van Ooijen, 2022; Van Ooijen et al., 2024). Adapted from Boerman et al. (2024), three privacy self-efficacy items measured the extent to which participants felt confident in their ability to protect privacy from targeted advertising (α = .94), such as “I feel confident that I can secure my privacy from targeted advertising.” Response efficacy was measured by asking participants how effective five existing mechanisms are in privacy protection, such as “Turning off ad personalization” (α = .82) (Boerman et al., 2024). Three response cost items measured the extent to which participants felt protecting privacy was too costly and effortful (α = .79) (Van Ooijen et al., 2024), such as “It takes too much time to know what data websites and apps are collecting on my mobile device.”
Distal outcome
Privacy protection intention was measured by asking participants their likelihood of engaging in seven privacy protection strategies, such as “Protect my personal information with anti-tracking tools” and “Use ad blockers to be protected from targeted ads” (α = .90) (Boerman et al., 2021).
Profile covariates
Four items adopted from Segijn et al. (2022) measured perceived surveillance by asking participants how much they felt advertisers were surveilling them on the Internet or social media, such as by “Looking over your shoulder” (α = .93). Five items adopted from Lutz et al. (2020) measured privacy powerlessness by asking the extent to which participants felt powerless about privacy protection (α = .91), such as “Even if I try to protect my data, I can’t prevent online advertisers from accessing them.”
Analytic plan
Analyses were conducted using R, the MplusAutomation R package, and Mplus version 8.8 (Muthén and Muthén, 1998–2022). LPA was performed on six PMT appraisal variables to identify distinct latent profiles that capture the heterogeneity in privacy protection appraisals. Starting with a one-profile model, profiles were incrementally increased until model non-identification or no further improvement in model fit was observed. Because LPA uses continuous indicators, models were estimated following recommended approaches, considering profile-invariant and profile-varying diagonal models (Masyn, 2013; Nylund-Gibson and Choi, 2018; Nylund-Gibson and Masyn, 2016). Specifically, we considered four LPA models: (1) the restrictive profile-invariant, diagonal model with equal variances across the latent profiles and covariances between the indicators fixed to zero with the profiles, (2) the profile-varying, diagonal model with freely estimated variances and covariances fixed to zero, (3) the profile-invariant, unrestricted model equal variances and covariances, and (4) the profile-varying, unrestricted model with free variances and equal covariances. All models were estimated using robust maximum likelihood estimation (MLR), which handles missing data via full information maximum likelihood (FIML). Multiple random starts ensured that the solution converged on a global rather than a local solution (Asparouhov and Muthén, 2014).
Based on current recommendations, we utilized multiple sources of information to guide the selection of the optimal number of profiles (e.g. Masyn, 2013; Nylund-Gibson and Choi, 2018). Model evaluation included consistent Akaike’s Information Criterion (CAIC), Bayesian Information Criterion (BIC), adjusted Bayesian Information Criterion (aBIC), Approximate Weight of Evidence Criterion (AWE), Vuong-Lo-Mendel-Rubin (VLMR), and Bootstrapped Likelihood Ratio Test (BLRT). Information criteria (CAIC, BIC, aBIC, and AWE) with the lowest value indicate the most optimal fit (Burnham et al., 2011). Likelihood ratio tests (BLRT and VLMR) test the significance of adding extra profiles. In addition, the Bayes Factor (BF) and the approximate correct model probability (cmP) were utilized for model comparisons (Masyn, 2013; Nylund-Gibson and Choi, 2018). BF assesses the relative fit between two models (Model K and Model K + 1), with a value greater than ten considered strong evidence for Model K. The cmP allows relative comparisons of each estimated model and determines the probability of each model’s correctness, with the model having the highest cmP being selected. Finally, we considered each solution’s theoretical and conceptual meaning and examined percentages within each profile solution to determine the best-fitting model (Nylund-Gibson and Choi, 2018).
After determining the best latent profile solution, we used the maximum likelihood (ML) manual three-step approach (Asparouhov and Muthén, 2014; Vermunt, 2010) to examine the association between the covariates (perceived surveillance and privacy powerlessness) of the latent profiles and their outcome (privacy protection intention), controlling for demographics (i.e. age, gender/sex identity, race/ethnicity, education, and household income). Because the latent profile variable is categorical, a multinomial logistic regression assessed the relationships between the covariates and the latent profiles. Estimated logit coefficients, odds ratios, and 95% confidence intervals were evaluated. For the distal outcome, we estimated conditional means for each latent profile. An omnibus Wald chi-square test was used for the distal outcome (i.e. privacy protection intention) to see if there was evidence of a significant relationship between profiles and the distal outcome. If the Wald test is significant, then the pairwise comparison of the profiles was carried out.
Results
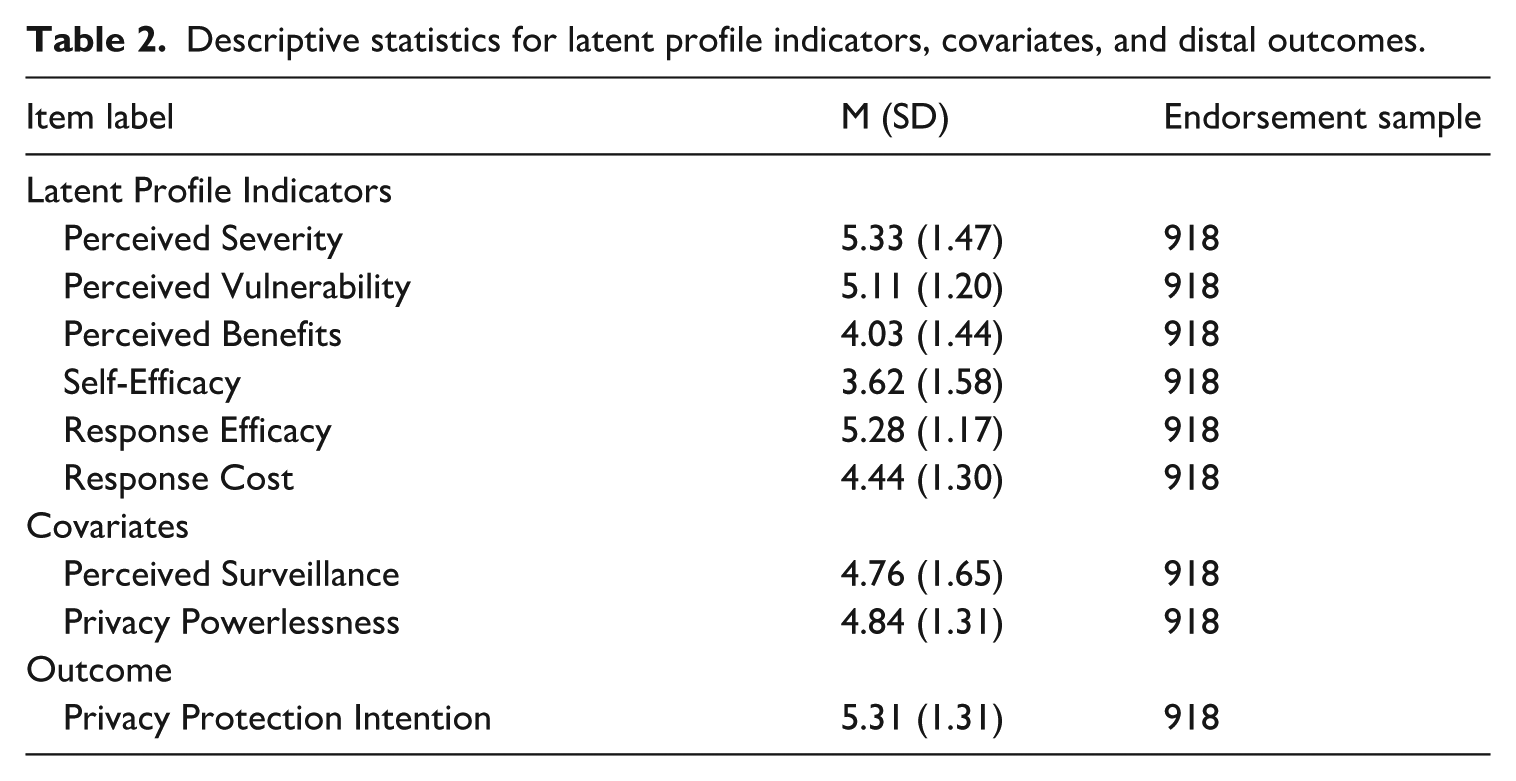
Table 2 presents the means and standard deviations for the six latent profile indicators and the proportions, means, and standard deviations for the predictors and outcome.
Descriptive statistics for latent profile indicators, covariates, and distal outcomes.
Privacy protection profile enumeration
Table 3 presents the fit indices comparing the LPA models with one through six latent profiles for each variance-covariance model specification. The fit indices and likelihood ratio tests did not indicate a single optimal model across variance-covariance specifications, as most fit information criteria did not reach an absolute minimum, and most likelihood ratio tests were significant. To further evaluate the models, we included a ΔBIC column in Table 3, representing the BIC difference between neighboring models. Analyzing the ΔBIC helps identify where improvements in fit begin to slow down or stabilize. In addition, we plotted the fit indices across each profile for each model specification to visualize the fit values and identify the “elbow” (see Figure 2). This information criteria plot compares the BIC, aBIC, CAIC, and AWE values across four variance-covariance specifications in the LPA.
Fit statistics for profile enumeration for privacy protection indicators.
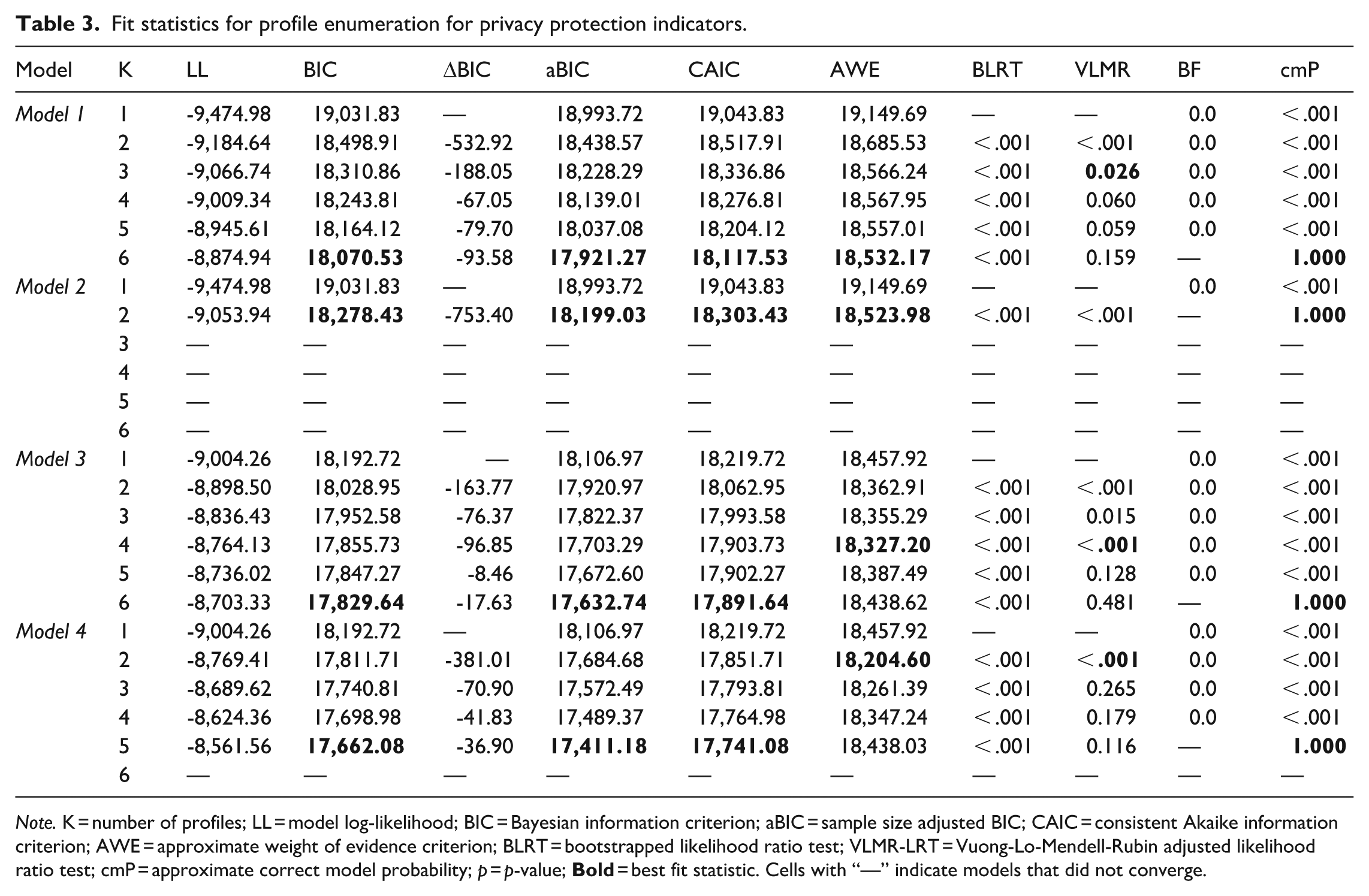
Note. K = number of profiles; LL = model log-likelihood; BIC = Bayesian information criterion; aBIC = sample size adjusted BIC; CAIC = consistent Akaike information criterion; AWE = approximate weight of evidence criterion; BLRT = bootstrapped likelihood ratio test; VLMR-LRT = Vuong-Lo-Mendell-Rubin adjusted likelihood ratio test; cmP = approximate correct model probability; p = p-value;
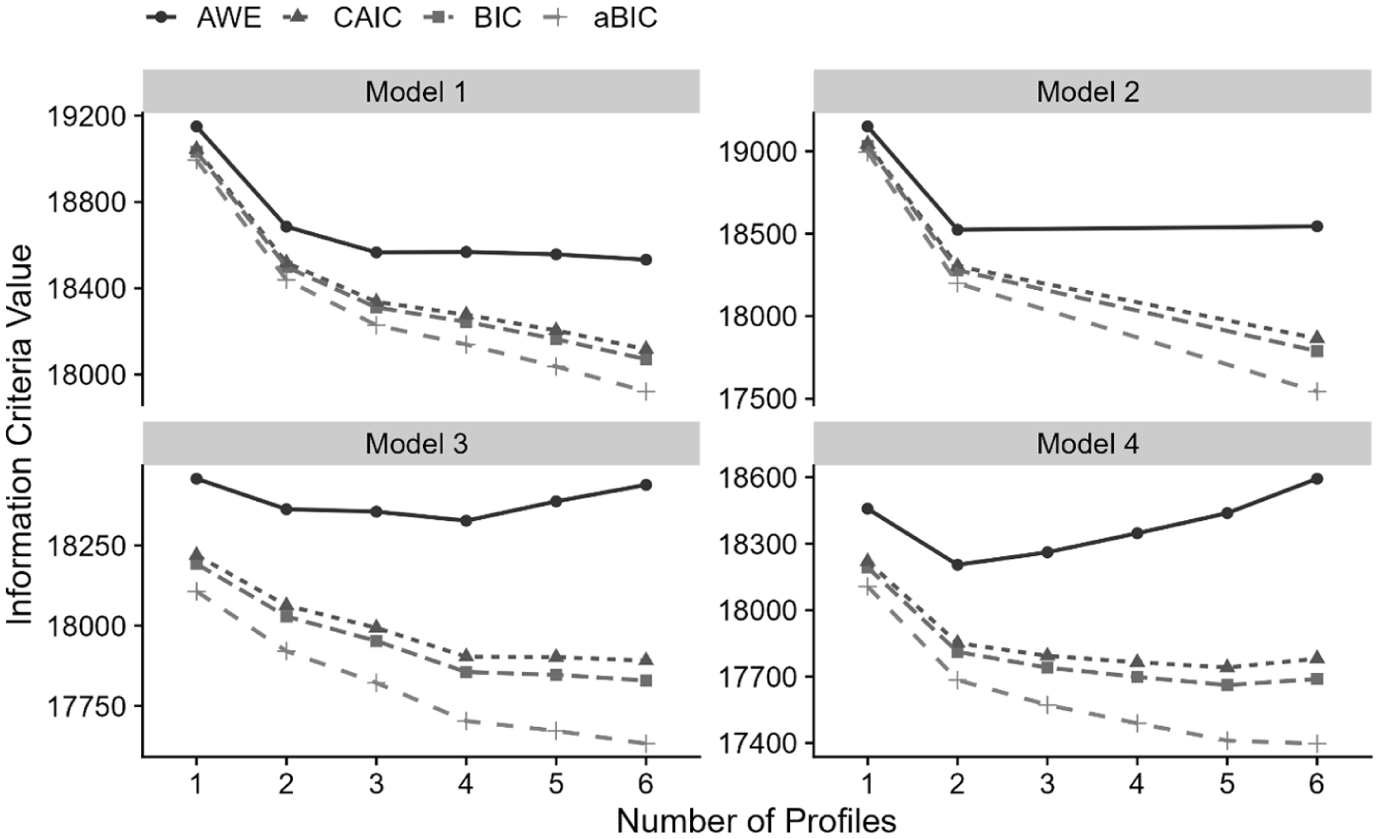
Fit information criteria comparison across variance-covariance specifications in the latent profile analysis.
For Model 1 (i.e. the restrictive profile-invariant model), the information criteria (i.e. BIC, aBIC, CAIC, and AWE) did not reach a minimum. However, the VLMR test and information criteria plot supported a three-profile solution. In addition, the reduction in BIC from two to three profiles was substantial, with diminishing improvement beyond three profiles (e.g. ΔBIC = −67.05 from three to four), further supporting the three-profile model. For Model 2, three- through six-profile solutions did not converge and this model was excluded. For Model 3, AWE (which reached a minimum value) and VLMR indicated a four-profile model. Finally, for Model 4, AWE and VLMR suggested a two-profile model. There was a substantial reduction in BIC from the one-profile to the two-profile model (ΔBIC = −381.01), with diminishing improvement beyond two profiles (e.g. ΔBIC = −70.90 from two to three profiles).
The three candidate models were considered further by evaluating the latent profile plots, which display the mean values for each indicator across profiles and profile sizes. Model 3’s four-profile model was no longer considered as it contained very small profile sizes of 1.59% and 2.85%; a profile size of over 5% is recommended (Nylund-Gibson and Choi, 2018). Model 4’s two-profile models did not make substantive theoretical sense with only two profiles. Model 1 Profile 3 model was retained as the profile model for privacy protection appraisals.
RQ1: identifying latent profiles of privacy protection appraisals
After choosing the Model 1 three-profile model, the final mean profile plot was created to interpret and label the three emergent latent profiles (see Figure 3). Based on the mean value for each indicator on a 7-point scale across profiles, the first profile was labeled “Privacy-Optimistic” (n = 129, 14.16%) and included those who reported the lowest perceived severity and perceived vulnerability, moderate self-efficacy, and relatively high perceived benefits, response efficacy, and response cost. The second profile was labeled “Privacy-Cautious” (n = 391, 42.08%) and included those who reported the highest perceived severity and perceived vulnerability, the lowest perceived benefits and self-efficacy, and high response efficacy and relatively high response cost. Finally, the third profile was labeled “Privacy-Balanced” (n = 398, 43.76%); this profile included those who reported consistently moderate to high levels of all appraisal factors (mean scores ranged from 4 to 6).
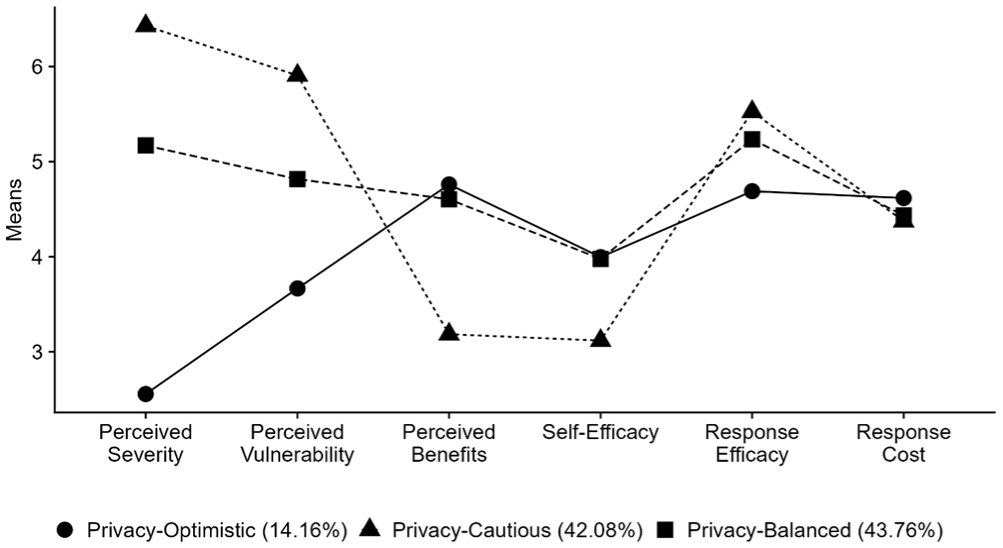
Mean profile plots for the three-profile privacy protection appraisals LPA model.
RQ2: profile mean differences in privacy protection intention
An overall omnibus test indicated significant differences in privacy protection intention across the three profiles, χ²(2) = 432.027, p < .001 (see Figure 4). Post hoc comparisons revealed that all three profiles significantly differed at p < .001, with Privacy-Cautious individuals reporting the highest intention, followed by Privacy-Balanced and Privacy-Optimistic individuals.
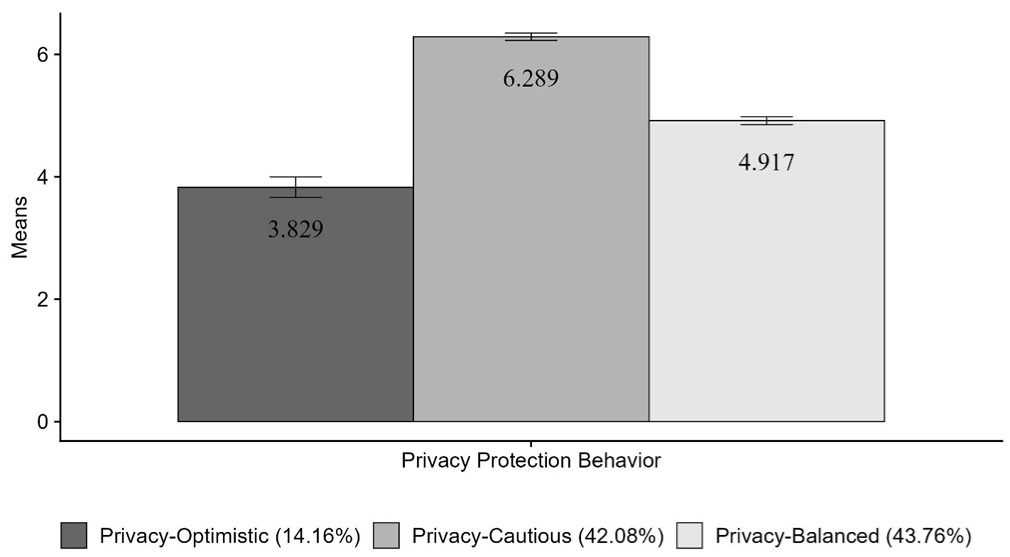
Mean scores of the distal outcome of privacy protection intention across latent profiles.
RQ3: perceived surveillance and privacy powerlessness as profiles covariates
The associations between perceived surveillance and privacy powerlessness covariates and latent profile membership were examined using multinomial logistic regression (via the ML three-step method), with the Privacy-Optimistic profile as the reference category. Results indicated that compared to being in the Privacy-Optimistic profile, higher perceived surveillance was associated with higher odds of being in the Privacy-Cautious profile (odds ratio [OR] = 2.160, confidence interval [CI] = [1.765, 2.643], p < .001) as well as higher odds of being in the Privacy-Balanced profile (OR = 1.429, CI = [1.220, 1.673], p < .001). In addition, higher privacy powerlessness was associated with higher odds of being in the Privacy-Cautious profile than the Privacy-Optimistic profile (OR = 1.311, CI = [1.050, 1.636], p = .017), but not for the Privacy-Balanced profile, p > .05.
Discussion
Empirical inconsistencies have been documented in privacy research that applies PMT (Mou et al., 2022). In response, this study adopts an LPA to uncover how subgroups of PMT appraisals differ in their subsequent privacy protection intention. In addition, we extend PMT and privacy research by testing perceived surveillance and privacy powerlessness as profile covariates to understand how threat and coping appraisals evolve vis-à-vis new privacy challenges posed by the expansion and normalization of dataveillance. Theoretically, this study highlights the heterogeneity of appraisal patterns underlying privacy decision-making, provides novel insights into the appraisal-behavior relationship to account for empirical inconsistencies, and advances PMT and privacy research by incorporating recently-proposed psychological antecedents.
Latent profiles of privacy protection appraisals
Previous studies have attempted to explore population heterogeneity in online privacy by utilizing latent class analysis or cluster analysis; however, they either focus on behaviors as class indicators (Lin, 2019) or only study a limited set of cognitive factors (e.g. Kang and Jung, 2021; Voorveld et al., 2024). Our study represents the first attempt to uncover latent profiles of privacy appraisals based on the full PMT nomology. Using a nationally-representative sample of US adults, we found three distinct profiles. These findings complement previous research but also offer new insights. The Privacy-Balanced group was the largest and comprised 43.76% the participants. This means that a great number of US Internet users have a balanced appraisal pattern vis-à-vis online privacy, such that they have the necessary privacy awareness, well-understand the potential risks and benefits associated with targeted advertising, and feel moderately efficacious about privacy protection. The threat appraisal pattern of this group resembles that of Kang and Jung’s (2021) Ambivalent cluster (i.e. high benefits and risk perceptions), though Kang and Jung did not account for coping appraisals. This pattern is also similar to that of Voorveld et al.’s (2024) Control Paradox group, who reported high algorithmic awareness and moderate coping ability.
The Privacy-Cautious group (42.08%) identified in our study reported extremely high levels of perceived severity and vulnerability, low self-efficacy, and perceived benefits, yet the highest response efficacy. While individuals in this group feel especially heightened privacy threats and lowered confidence in individual protection capacity, they believe in the effectiveness of existing mechanisms. This pattern is similar to that of Voorveld et al.’s Fatigued group, who reported the highest algorithmic awareness but low coping ability and perceived appropriateness. In sharp contrast, the third profile we identified, the Privacy-Optimistic group (14.16%), reported the lowest perceived severity and vulnerability, but high benefits, response and self-efficacy, which resembles that of the Benefit-Oriented cluster of smart watch users in Kang and Jung’s (2021) study.
Interestingly, response cost did not vary much across the three profiles and remained consistent at the scale midpoint. This suggests that while participants understand the costs of privacy protection in terms of time and inconvenience, their cost perceptions did not reach too high of a level to discourage privacy protection. And such cost perceptions did not co-vary with other threat and coping appraisals. Overall, these patterns echo findings of previous research but add to it by investigating other understudied cognitive appraisals (e.g. response efficacy). The findings also reveal the heterogeneity of privacy appraisals that traditional PMT research fails to account for.
Privacy protection intention as outcomes
PMT outlines six cognitive appraisal factors that individuals consider, yet it does not theorize how these appraisals operate in tandem to inform privacy behavior; consequently, previous research tends to study the effect of PMT appraisals in isolation from each other. There are important exceptions, such as Meier et al. (2023) who tested the interaction effects of perceived risks and perceived benefits on subsequent privacy outcomes. And although meta-analyses provide helpful insights (Mou et al., 2017; Mou et al., 2022), such as the finding that coping appraisals were overall more powerful predictors of protection motivation than threat appraisals, the population homogeneity assumption of this approach still does not allow for an understanding of how subgroups of privacy appraisals respond to privacy risks differently. Our study thus moves one step further by accounting for how individuals process the full range of PMT appraisals simultaneously, which resembles reality more closely.
Results showed that all three profiles differed in their privacy protection intention, with Privacy-Cautious individuals reporting the highest intention, followed by Privacy-Balanced and Privacy-Optimistic individuals. These findings demonstrate how LPA helps explain inconsistencies in the literature and suggest that PMT appraisal factors should be viewed in light of others. As one example, past studies have found inconsistent results regarding the relationship between self-efficacy and protection behaviors (e.g. Boerman et al., 2021; van Ooijen et al., 2024). Our data indicate that this could be because the various appraisals function simultaneously in complex and different ways for people in each profile. Specifically, among all profiles, Privacy-Cautious individuals reported the lowest levels of self-efficacy, which according to PMT and EPPM, should predict lower protection intention (i.e. defensive avoidance, fear control). However, Privacy-Cautious individuals also reported extremely high perceived severity, vulnerability, and the lowest perceived benefits, which likely motivated privacy protection to a greater extent than the other two groups. This finding thus challenges EPPM’s assertion, at least in the privacy context, that efficacy perceptions must outweigh threat perceptions to trigger danger control; rather, having an adequate level of efficacy is sufficient to prompt protection intention. Similarly, although Privacy-Optimistic individuals reported relatively high levels of response and self-efficacy, which should lead to the highest protection intention, their low perceived severity and vulnerability, coupled with high perceived benefits, likely counteracted the effects of efficacy. The appraisal patterns of Privacy-Optimistic individuals thus make them the most vulnerable to potential privacy risks. These findings offer important insights into empirical inconsistencies and advance PMT by demonstrating how threat and coping appraisals may augment and/or suppress the effects of each other in more complex and nuanced ways that were undertheorized.
Perceived surveillance and privacy powerlessness as covariates
As a novel theoretical contribution, we found that both perceived surveillance and privacy powerlessness were associated with latent profiles of privacy appraisals. In particular, people who reported higher perceived surveillance were more likely to be identified as Privacy-Cautious or Privacy-Balanced (vs Privacy-Optimistic). Notably, individuals in these two profiles reported higher perceived severity, perceived vulnerability, and response efficacy than those in the Privacy-Optimistic profile. That is, people who feel that they are being surveilled by advertisers are well-aware of the risks, but at the same time, still believe that existing protection mechanisms are effective, to a greater extent than those in the Privacy-Optimistic profile. Individuals in the Privacy-Cautious or Privacy-Balanced profiles likely have higher privacy literacy, which might have contributed to their perceptions of severity, vulnerability, and response efficacy. The finding that perceived surveillance is more salient to Privacy-Cautious (vs Privacy-Optimistic) individuals who report lower perceived benefits and self-efficacy also provides evidence for our speculation that feeling constantly surveilled likely lowers perceived benefits and highlights limited privacy protection capacity especially among individuals in this profile group. While previous research (e.g. Wang et al., 2025) tested the relationships between perceived surveillance and perceived risks and benefits, our findings extend the DEAL framework by demonstrating that perceived surveillance relates to other threat and coping appraisals. Taken together, findings suggest that the way people assess privacy threats and their coping capacity is contingent upon the extent to which they feel surveilled in targeted advertising, thus extending PMT by integrating perceived surveillance as a psychological antecedent.
Privacy powerlessness was associated with a higher likelihood of being identified as Privacy-Cautious than Privacy-Optimistic. Scholars suggest that privacy-powerless individuals likely lower their risk perceptions and minimize cognitive coping efforts (e.g. Choi et al., 2018; Lutz et al., 2020). Previous research has identified individuals who were highly aware of algorithmic persuasion yet found it less appropriate and felt less able to cope with it, which serves as evidence for privacy fatigue (e.g. Voorveld et al., 2024). Our study further shows that privacy-powerless individuals are more likely to be identified in the Privacy-Cautious group (i.e. high threat perceptions and low self-efficacy). This finding challenges previous research by suggesting that privacy powerlessness does not necessarily lead individuals to discount the potential risks. On the other hand, privacy powerlessness was not associated with the likelihood of being identified as Privacy-Balanced (vs Privacy-Optimistic). This makes sense given that Privacy-Balanced individuals’ moderate self-efficacy and high response efficacy likely fostered adequate control, despite relatively high threat perceptions. Nonetheless, these findings advance PMT by shedding light on how the way individuals evaluate privacy threats and coping potential likely depends on how powerless they feel.
As both perceived surveillance and privacy powerlessness represent unique psychological responses individuals develop vis-à-vis institutional dataveillance, these findings also contribute to the broader framework of data colonialism (Couldry and Mejias, 2019; Thatcher et al., 2016), which describes how contemporary dataveillance systems normalize the exploitation of human data. Thatcher et al. (2016) conceptualize this process as a form of capitalist “accumulation by dispossession,” wherein users’ everyday digital practices are commodified, and users are dispossessed of ownership and control over the data they produce. At its core, data colonialism points to structural privacy threats and power differentials that constrain individual agency. Our findings provide evidence on how perceived surveillance and privacy powerlessness, as products of data colonialism, can have further individual-level psychological consequences by shaping the way individuals appraise online privacy.
Practical implications
The appraisal patterns of subgroups also have meaningful real-world implications as they can inform more tailored interventions and message designs. For example, given that Privacy-Optimistic individuals already feel quite confident about privacy protection, to target this group, skills training on how to protect online privacy is likely less effective; rather, fear appeal messages that highlight the severity and salience of privacy threats may be more valuable. For Privacy-Cautious individuals who lack self-efficacy, efficacy appeals that boost feelings of control and evoke hope may be more effective at uplifting their privacy protection motivation. Educational programs that emphasize both the benefits and risks of Internet use may also be beneficial, as heightened threat appraisals in this group could undermine their ability to recognize and take advantage of the benefits of Internet use.
Limitations and future research
One main challenge of our cross-sectional survey is making causal inferences or suggesting change over time. That is, our findings do not support the claim that perceived surveillance and privacy powerlessness led to differences in PMT appraisals, or that the mixtures of these appraisals caused changes in privacy protection. Future research should conduct experiments or longitudinal surveys to make more confident causal conclusions. In any case, our decision to consider perceived surveillance and privacy powerlessness as PMT profile covariates, and privacy protection intention as the outcome, was driven by theory and previous research (e.g. Choi et al., 2018; Strycharz and Segijn, 2022; van Ooijen et al., 2024).
While we were interested in privacy decision-making in the broad targeted advertising context, future research should also study people’s surveillance responses on specific platforms, as their privacy experiences likely differ based on the affordances, disclosure norms, and regulation policies of different platforms. Future research should also attempt to uncover the heterogeneity of people’s privacy behavioral responses, which have been conceptualized as multidimensional and may include resistance, avoidance, and countersurveillance (Zuboff, 2019). In addition, while our study set out to exclusively focus on individual-level psychological factors underlying users’ privacy decision-making, future research should investigate the role of macro-level factors, such as power relations, economic interests, and political dynamics, in shaping users’ privacy responses (Thatcher et al., 2016). Indeed, macro-level surveillance infrastructure likely contributes to users’ psychological responses, including heightened feelings of perceived surveillance and privacy powerlessness (Büchi et al., 2022). Here, critical and sociological theoretical perspectives within the frameworks of surveillance studies, coupled with qualitative and/or mixed-methods approaches, will be instrumental in addressing the multilayered nature of dataveillance.
Conclusion
Institutional dataveillance presents unprecedented challenges to individual privacy. Targeted advertising is just one example of how dataveillance has become woven into the fabric of everyday digital life and is shaping how people navigate privacy in ways both visible and invisible. By uncovering latent profiles of privacy appraisals and their relationships with privacy psychological and behavioral responses, our study is among the very few attempts at understanding the within-population heterogeneity in people’s online privacy experiences. And to our knowledge, it is the first study to apply an LPA approach to test PMT’s predictions. The nationally-representative sample also renders the findings generalizable to the broad US population, which should be replicated in other cultures. Findings suggest that future theorizing must acknowledge how the privacy experience of subgroups shapes their privacy behavior in different but meaningful ways. Likewise, by reframing privacy decision-making as a heterogeneous process, our hope is that findings can inspire meaningful interventions that recognize and appreciate the differentiated privacy needs and ultimately cultivate individual autonomy and resilience in an era of pervasive digital surveillance.
Supplemental Material
sj-docx-1-nms-10.1177_14614448251393913 – Supplemental material for Not the average user: A latent profile analysis of privacy protection appraisals in targeted advertising
Supplemental material, sj-docx-1-nms-10.1177_14614448251393913 for Not the average user: A latent profile analysis of privacy protection appraisals in targeted advertising by Laurent H Wang, Dina Naji Arch and Miriam J Metzger in New Media & Society
Footnotes
Data availability
The data underlying this article will be shared on reasonable request to the corresponding author.
Funding
The authors disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the National Science Foundation under Grant No. 2151340.
Supplemental material
Supplemental material for this article is available online.
Author biographies
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
