Abstract
Internet privacy has been proposed as a new dimension of the digital divide. Although Internet privacy relates to all segments of the population, older Internet users are particularly vulnerable because they generally have lower Internet skills. Coupled with their high level of privacy concerns, this can dissuade them from fully engaging in a variety of Internet uses. As older adults overcome their limited Internet skills by asking others to perform online activities on their behalf, a practice known as use-by-proxy, it is likely that this is also a strategy for dealing with Internet privacy concerns. Therefore, we examine how Internet skills, along with Internet privacy concerns and perceived privacy control, influence their Internet uses and use-by-proxy. To this end, we develop an integrative conceptual model and test it with structural equation modelling using data collected in November 2021 from a nationwide sample of 460 Internet users aged 65+ in Slovenia.
Keywords
Introduction
Internet privacy has been proposed as a new dimension of the digital divide (Büchi et al., 2021; Park, 2013, 2021b). On the one hand, those lacking privacy protection skills are more exposed to potential threats (Park, 2013), while on the other hand, perceptions of potential misuse of personal information can dissuade people from using online services (Baruh et al., 2017; Frik et al., 2019). In this context, it is important to focus on older adults because ‘low-use and low-skilled older Internet users represent a social group particularly vulnerable to experiencing negative internet outcomes’ (Büchi et al., 2021: 305). As older adults generally have lower Internet skills and confidence in protecting personal data online (Ofcom, 2021), a bleak scenario emerges in which the digital inequality they suffer from only worsens as they are unable to reap the benefits of their Internet uses (Park, 2013, 2021b).
Internet uses are an important concept in digital divide research, referring to different types of self-reliant activities that individuals can perform online, which can be categorised into economic, cultural, social and personal uses (Helsper, 2012). They do not vary only in terms of the amount (intensity) of user engagement but also according to the breadth of uses which is defined as the range of different online activities performed by a user (van Deursen and Helsper, 2015). However, few studies have examined how older adults’ perceptions of information privacy influence their Internet uses. The limited existing research has underlined the importance of Internet privacy concerns (IPCs) and perceived privacy control (PPC) (Elueze and Quan-Haase, 2018; Frik et al., 2019). IPCs refer to concerns about the possible loss of privacy as a result of providing information to websites (Dinev and Hart, 2005), and PPC is defined as the individual’s perception of being able to control access to and use of their information (Xu et al., 2008). IPCs are an important intervening variable between individual characteristics and behavioural responses (Smith et al., 2011). However, its antecedents have been studied in a somewhat disjointed manner (Smith et al., 2011) and predominantly on populations with higher levels of Internet proficiency (Hong et al., 2021). PPC can act as a mitigator of IPCs (Li, 2012), but past research has rarely focused on PPC or its relationship with IPCs (Brough and Martin, 2020). Moreover, while some studies link digital inequalities with Internet privacy research, they focus on factors influencing individuals’ use of privacy-protective measures rather than on how IPCs and PPC affect Internet uses (Büchi et al., 2017, 2021; Park, 2013, 2021b). This raises two questions: first, what factors influence older adults’ IPCs and PPC; and second, how do IPCs and PPC together with Internet skills affect older adults’ Internet uses?
In examining the antecedents of IPCs, the multidimensional developmental theory provides a valuable framework by explaining when and why a particular situation is perceived as privacy intrusive (Laufer and Wolfe, 1977). According to this theory, three dimensions of key factors influence individuals’ perceptions of privacy: self-ego, environmental and interpersonal (see also the Internet privacy concerns section). In addition, the multidimensional developmental theory provides theoretical grounds for understanding the antecedents of PPC. It proposes that individuals’ perceptions of possible control over access to their information are based on ‘the evolving sense of self in interaction with the environment’ (Laufer and Wolfe, 1977: 37).
Understanding the outcomes of IPCs is equally important, as IPCs can influence the use of online services (Baruh et al., 2017). According to the protection motivation theory (Rogers, 1983), individuals’ behavioural responses to a threat are highly dependent on their perceived ability to cope with the threat. The impact of IPCs on behaviour should be considered alongside PPC for this reason (Brough and Martin, 2020). In the case of older Internet users, the low confidence they have in their ability to protect their personal information often leads them to ignore the threat of privacy breaches or limit their Internet uses rather than use privacy protection solutions (e.g. anti-spyware software) (Frik et al., 2019). Consequently, IPCs coupled with low PPC may lead to the further digital exclusion of older adults (Büchi et al., 2017, 2021; Park, 2013).
Nevertheless, Internet uses should no longer be considered solely as self-reliant online activities. Many low-skilled Internet users access online services indirectly by asking other users to perform activities on their behalf (Hunsaker et al., 2019; Quan-Haase et al., 2018; Selwyn et al., 2016). The use of such a practice, known as use-by-proxy (Petrovčič et al., 2022), is often initiated for Internet uses that are deemed ‘important’ but ‘risky’ (Selwyn et al., 2016). Studies show that use-by-proxy is usually activated for activities demanding the disclosure of personal information, such as e-government services, healthcare support and online banking (Petrovčič et al., 2022; Reisdorf et al., 2021; Selwyn et al., 2016). In particular, older adults often rely on others to help them protect their privacy online (Frik et al., 2019; Murthy et al., 2021). Consequently, following the propositions of the protection motivation theory, use-by-proxy seems to be a strategy for Internet users with high IPCs and low PPC to access Internet services that they consider potentially harmful to their privacy.
However, direct and indirect forms of Internet uses are also determined by Internet skills, as they represent an individual’s capacity to successfully navigate the online environment (Petrovčič et al., 2022). According to the model of compound and sequential digital exclusion, different types of Internet skills positively influence different types of direct Internet uses (van Deursen et al., 2017) and negatively affect indirect Internet uses, such as use-by-proxy (Petrovčič et al., 2022). Moreover, Internet skills play an important role in terms of Internet privacy, as individuals with higher Internet skill levels have higher PPC (Bandyopadhyay, 2012).
Against this backdrop, the present study aims to extend the current understanding of the role of Internet privacy in older adults’ direct and indirect forms of Internet engagement and thus link the fields of Internet privacy and digital divide. Specifically, by developing an integrated conceptual model based on the three theoretical frameworks described above, this study aims to outline the antecedents of IPCs among older Internet users and examine the extent to which IPCs and PPC, in combination with Internet skills, affect their breadth of Internet uses and engagement with use-by-proxy. To empirically validate the proposed model (Figure 1), 14 theoretically grounded hypotheses are developed and tested with structural equation modelling (SEM) using data collected through a telephone survey on a representative sample of older Internet users (65+) in Slovenia. Slovenia is a European Union (EU) member state where the percentage of older adults (65–74 years) who used the Internet in the last 3 months is slightly lower than the EU average (Slovenia: 62%; EU: 65%), whereas the percentage of older Internet users with at least basic digital skills is considerably lower than the EU average (31% vs 39%; Eurostat, 2022).
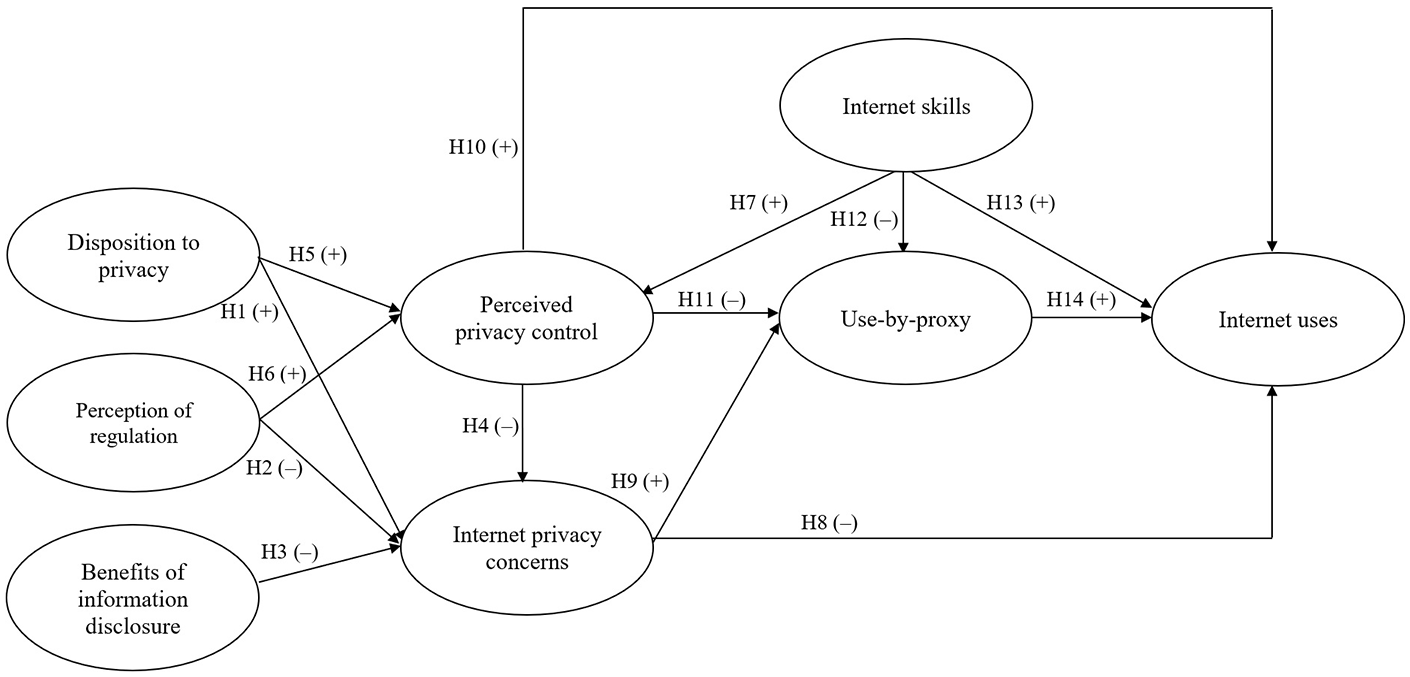
Proposed conceptual model of the role of Internet privacy perceptions on direct and indirect Internet uses.
Background
Internet privacy concerns
The three dimensions of multidimensional developmental theory provide a comprehensive framework for examining the antecedents of IPCs (Hong et al., 2021). The self-ego dimension refers to ‘a developmental process that, in our [Western] society, focuses on individuation (autonomy) and, by implication, personal dignity’ (Laufer and Wolfe, 1977: 26). This developmental process determines future perceptions and desires about privacy (Laufer and Wolfe, 1977). Hence, an individual’s disposition to value privacy, developed over the course of a lifetime, greatly influences their desired level of privacy and perceptions of privacy violations. Indeed, studies have shown that individuals’ disposition to value privacy plays a key role in the formation of IPCs (Xu et al., 2008, 2011). Accordingly, we hypothesise the following:
H1. Disposition to privacy positively influences Internet privacy concerns.
The environmental dimension refers to the elements that ‘act as boundaries of meaning and experience’ (Laufer and Wolfe, 1977: 28). It includes the interaction between social and physical (or technological) environments, life cycle stage and culture. The multidimensional developmental theory argues that these aspects shape individuals’ expectations and perceptions of privacy and provide normative guidelines for privacy management (Laufer and Wolfe, 1977). Particularly important are culture-related privacy elements as these ‘constitute boundaries of consciousness about privacy’ (Laufer and Wolfe, 1977: 28), thereby determining privacy values as well as formal and informal norms. An important type of formal norms are laws and policies, as these provide mechanisms by which individuals can claim their right to privacy (Nissenbaum, 2010). In the Internet context, where the balance of power regarding the collection and use of information is highly asymmetrical in favour of institutions, the role of policy is fundamental in balancing the powers between individuals and private and public institutions (Acquisti et al., 2015; Park, 2021a). Accordingly, we can assume that individuals who believe that policy adequately regulates the collection and use of their personal information and thus protects their privacy are also less concerned about potential privacy intrusions. Indeed, previous studies found that perceptions of regulation related to privacy influence perceptions of privacy in online environments (Lwin et al., 2007; Škrinjarić et al., 2019). Thus, we propose the following:
H2. Perceptions that legal regulations protect Internet privacy negatively affect Internet privacy concerns.
The multidimensional developmental theory also suggests that the interpersonal dimension represents the core of privacy as it relates to an individual’s ability to manage their private information in interactions with others across different social contexts. For instance, when the ability to control interaction is lost, the capability to control information is usually lost as well. However, Laufer and Wolfe (1977) point out an important distinction between the two concepts. Whereas the management of interactions relates primarily to the ability to control access to oneself, the management of information relates primarily to the mental processes individuals engage in when deciding how much information to disclose. The multidimensional developmental theory proposes that situations in which individuals perceive the disclosure of information as beneficial are less likely to be judged as privacy violations (Laufer and Wolfe, 1977). Prior studies on privacy in online environments also showed that PPC (Bandyopadhyay, 2012; Xu et al., 2008) and the perceived benefits of disclosing information (Hong et al., 2021) decrease the level of IPCs. Based on these considerations, we propose the following:
H3. Perceived benefits of disclosure negatively affect Internet privacy concerns.
H4. Perceived privacy control negatively affects Internet privacy concerns.
Perceived privacy control
The multidimensional developmental theory proposes that individuals’ perceptions of control over their privacy depend on several factors, including privacy consciousness, the environment and social structure, as well as experience and knowledge (Laufer and Wolfe, 1977). Given that the multidimensional developmental theory suggests that individuals who are more conscious of privacy also perceive more opportunities for control, it seems reasonable to expect that an individual’s disposition to value privacy increases PPC:
H5. Disposition to privacy positively influences perceived privacy control.
Furthermore, as PPC is shaped by the normative environment (Laufer and Wolfe, 1977), we expect that more stringent privacy norms could also influence PPC. If individuals believe that norms enable them to formally sanction a subject who has mishandled their personal information, then their PPC would likely increase. Studies confirm that the more individuals perceive privacy regulation as adequate, the higher their level of PPC (Xu et al., 2011). Hence, we propose the following:
H6. Perceptions that legal regulations protect Internet privacy positively affect perceived privacy control.
Laufer and Wolfe (1977) claim that technological advancements can alter the perceived ability to control access to information because they create new environments which demand new knowledge and skills for successful privacy management. Thus, it is also important to consider Internet skill level, as high-skilled users might perceive more control over access to their information on the Internet than low-skilled users. Indeed, Büchi et al. (2017) argue that high-skilled users are better able to mitigate online privacy risks. Since other studies have also shown that individuals with higher Internet skill levels have higher PPC (Bandyopadhyay, 2012), we hypothesise the following:
H7. Internet skills have a positive effect on perceived privacy control.
Direct and indirect Internet uses
As mentioned in the ‘Introduction’ section, the protection motivation theory argues that individuals’ behavioural responses to a threat depend on their perceived magnitude of the threat and their perceived ability to cope with the threat (Rogers, 1983). Li (2012) extended this reasoning to Internet privacy, claiming that when perceived privacy threats are high, only individuals who have confidence in their ability to protect themselves from privacy threats would engage in online transactions. Conversely, individuals with limited confidence would be unwilling to engage in such behaviour without guidance. According to this reasoning, users who are concerned about their privacy and believe they cannot adequately protect it may resort to indirect Internet uses. Notably, studies have shown that older adults turn to their family members and peers to help them protect their Internet privacy (Frik et al., 2019; Hunsaker et al., 2019; Murthy et al., 2021).
Based on these propositions, we first consider the relationships between IPCs and direct and indirect Internet uses. IPCs are an important factor that negatively affects a variety of online behaviours (Bandyopadhyay, 2012; Baruh et al., 2017; Dinev and Hart, 2005) and also decreases the uptake of Internet services among older adults (Bixter et al., 2019). Moreover, it is reasonable to assume that older adults who feel their privacy is threatened online are also more likely to ask others for help (Frik et al., 2019; Murthy et al., 2021). In fact, they believe that helpers are more likely to take appropriate actions to prevent potential privacy violations. Accordingly, we propose the following:
H8. Internet privacy concerns have a negative effect on Internet uses.
H9. Internet privacy concerns have a positive effect on use-by-proxy.
Since Li (2012) suggested that lack of confidence in the ability to protect oneself from privacy breaches decreases digital engagement, it is reasonable to expect that PPC affects Internet uses and use-by-proxy. Studies have shown that individuals are more willing to disclose information or conduct online transactions when they believe they have greater control over the submitted information (Bandyopadhyay, 2012; Lwin et al., 2007). While virtually no study has empirically tested the mechanism through which PPC determines use-by-proxy, there is some evidence supporting the general proposition of the protection motivation theory on how the severity of the threat appeal and lack of coping response resonate in various levels of digital disengagement. For instance, scholars have found IPCs and the lack of privacy protection skills to be motivations for disconnection from specific Internet services (e.g. social media) (Frik et al., 2019; Nguyen et al., 2021). However, ‘disconnection (. . .) comes with various informational and social challenges, making it difficult and undesirable for people to opt out of the digital world completely’ (Nguyen et al., 2021: 300). Indeed, instead of opting out, many older adults who are less confident in their ability to control access to their information in online environments turn to others to help them carry out online activities that might cause risks to their data privacy (Frik et al., 2019; Murthy et al., 2021). Accordingly, we hypothesise the following:
H10. Perceived privacy control has a positive effect on Internet uses.
H11. Perceived privacy control has a negative effect on use-by-proxy.
In addition, van Deursen et al. (2017) suggested that older adults’ Internet uses can be explained by the sequential aspect of the model of compound and sequential digital exclusion that postulates that one type of digital exclusion (e.g. lack of Internet uses) depends on another type of exclusion (e.g. lack of Internet skills). Converging evidence shows that Internet users with better self-evaluated Internet skills engage in a broader range of Internet uses (Hargittai et al., 2019; Petrovčič et al., 2022; van Deursen et al., 2017). Recently, Petrovčič et al. (2022) presented an extension of the original model of compound and sequential digital exclusion in which use-by-proxy mediates the effects of Internet skills on Internet uses. Tellingly, the authors proposed that when high-skilled users are faced with the challenge of mastering new Internet uses, they are more likely to engage in self-reliant learning than turn to others for help. Conversely, low-skilled users are more likely to lean on others to complete online activities on their behalf (Petrovčič et al., 2022). This also seems to be a reasonable assumption when explaining use-by-proxy among older Internet users, as several studies suggest they ask others for help precisely because they lack the necessary skills to perform (more) advanced and/or risky online activities (Grošelj et al., 2019; Hänninen et al., 2021; Petrovčič et al., 2022). Considering these arguments, we propose the following:
H12. Internet skills have a negative effect on use-by-proxy.
H13. Internet skills have a positive effect on Internet uses.
However, the extended model of compound and sequential digital exclusion also propounds that use-by-proxy can stimulate the acquisition of new experiences with Internet uses (Petrovčič et al., 2022). Use-by-proxy is often accompanied by learning effects (Galperin and Arcidiacono, 2019; Grošelj et al., 2019), whereby users-by-proxy, when assisted by more proficient users, recognise their own limitations and learn new competency acquisition methods. However, use-by-proxy can also lead to leaning effects where users-by-proxy prefer to rely on others instead of acquiring the needed skills (Galperin and Arcidiacono, 2019; Marler and Hargittai, 2022). While studies indicate that learning effects are more pronounced, particularly in peer-based and intra-generational use-by-proxy (Hänninen et al., 2021; Hunsaker et al., 2019), the assumption that older Internet users who benefit from indirect Internet uses as users-by-proxy also engage with the Internet more by themselves needs to be further tested. Thus, we assume:
H14. Use-by-proxy has a positive effect on Internet uses.
Methods
Procedures and data
Data for this study were collected in a population-based telephone survey (i.e. CATI) conducted in Slovenia in 2021. The target population consisted of Slovenian residents aged 65 + . The decision to conduct a telephone survey was a consequence of the COVID-19 pandemic, which prevented face-to-face fieldwork in 2021. The sample was obtained by first stratifying all landline and mobile telephone numbers in Slovenia according to the 12 statistical regions and then systematically sampling from each stratum. We obtained a total of 701 completed responses, corresponding to a response rate of 6.6% according to AAPOR’s (2016) standard Response Rate 3 (RR3) definition. Data were weighted to match the combined gender and age groups as well as region breakdown using a raking method to obtain a nationally representative sample structure of older adults aged 65+. Sociodemographic characteristics of the weighted sample are shown in Table 1. In the current study, we focused on a subsample of respondents who used the Internet in the last 3 months (N = 460; 65.6%). The dataset and codebook are available at https://doi.org/10.23668/psycharchives.5384.
Sample characteristics (weighted data).
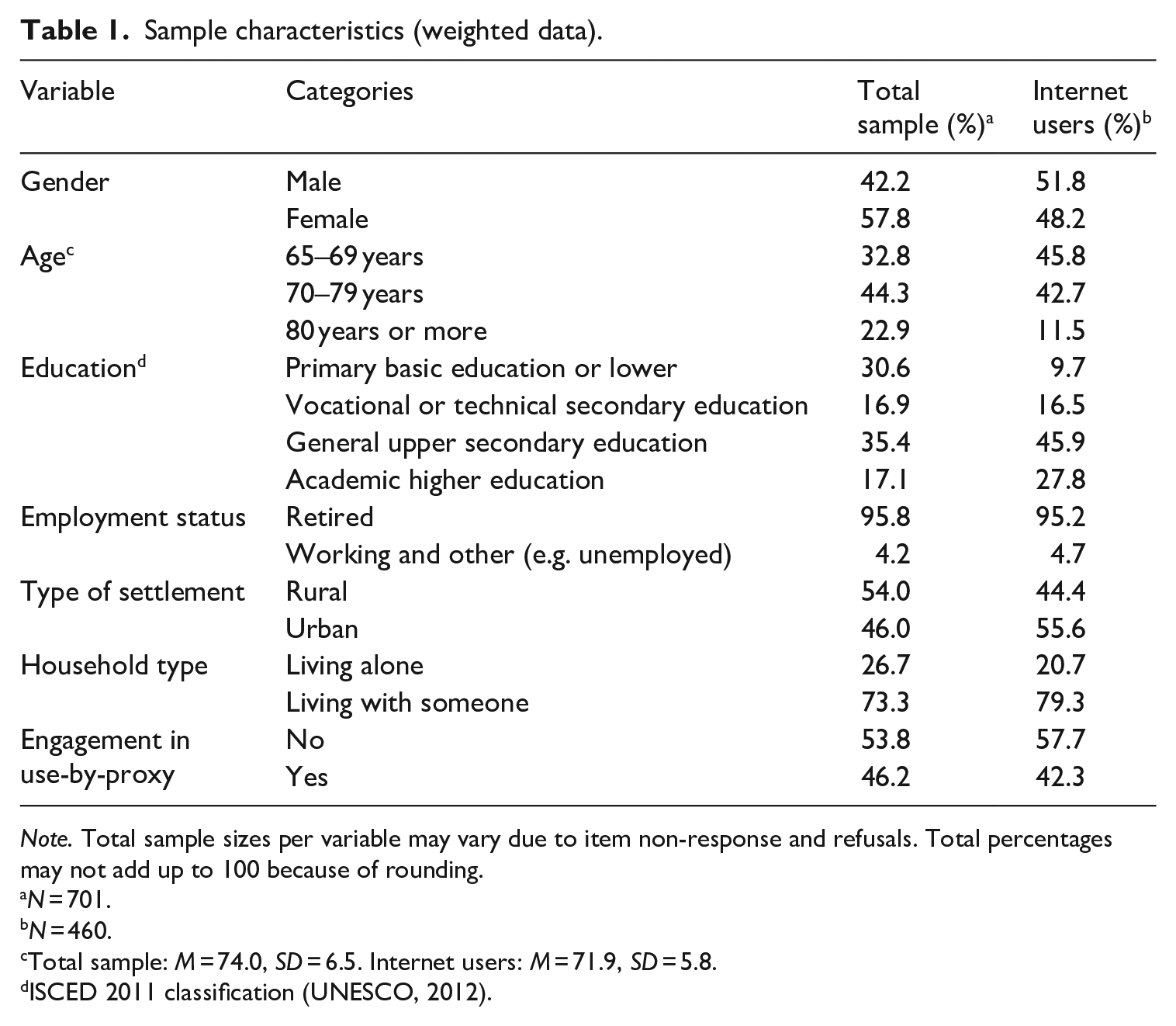
Note. Total sample sizes per variable may vary due to item non-response and refusals. Total percentages may not add up to 100 because of rounding.
N = 701.
N = 460.
Total sample: M = 74.0, SD = 6.5. Internet users: M = 71.9, SD = 5.8.
ISCED 2011 classification (UNESCO, 2012).
Measures
All measures were taken from prior literature and translated to Slovenian using the TRAPD (Translation, Review, Adjudication, Pretesting and Documentation) procedure (Harkness, 2003) (see Online supplement A). IPCs were measured using a four-item inventory that assesses individuals’ concerns about opportunistic behaviour related to their personal information disclosed online (Dinev and Hart, 2006). The results of confirmatory factor analysis (CFA) indicated that the scale has excellent internal consistency (Table 2 presents the internal consistency and convergent and discriminant validity of all reflective measurement scales). The scale for benefits of information disclosure was adapted from Dinev et al. (2013). The four items assessed individuals’ beliefs about the extent of benefits they receive from disclosing information on the Internet and showed good internal consistency. PPC was assessed using a four-item scale that measures perceived control over the disclosure and use of personal information (Xu et al., 2008). The scale exhibited adequate internal consistency. Disposition to privacy was measured with an adapted inventory based on Xu et al.’s (2011) scale consisting of four items assessing individuals’ general tendency towards ensuring their information privacy, which showed adequate reliability. Perception of regulation was assessed with an adapted scale from Lwin et al. (2007) that measures ‘the perception of legal and regulatory policy in the online privacy context’ (Lwin et al., 2007: 576). The four items exhibited adequate internal consistency. All privacy-related measures had a response scale from 1 = ‘completely disagree’ to 5 = ‘completely agree’.
Reliability and convergent and discriminant validity of measurement scales.
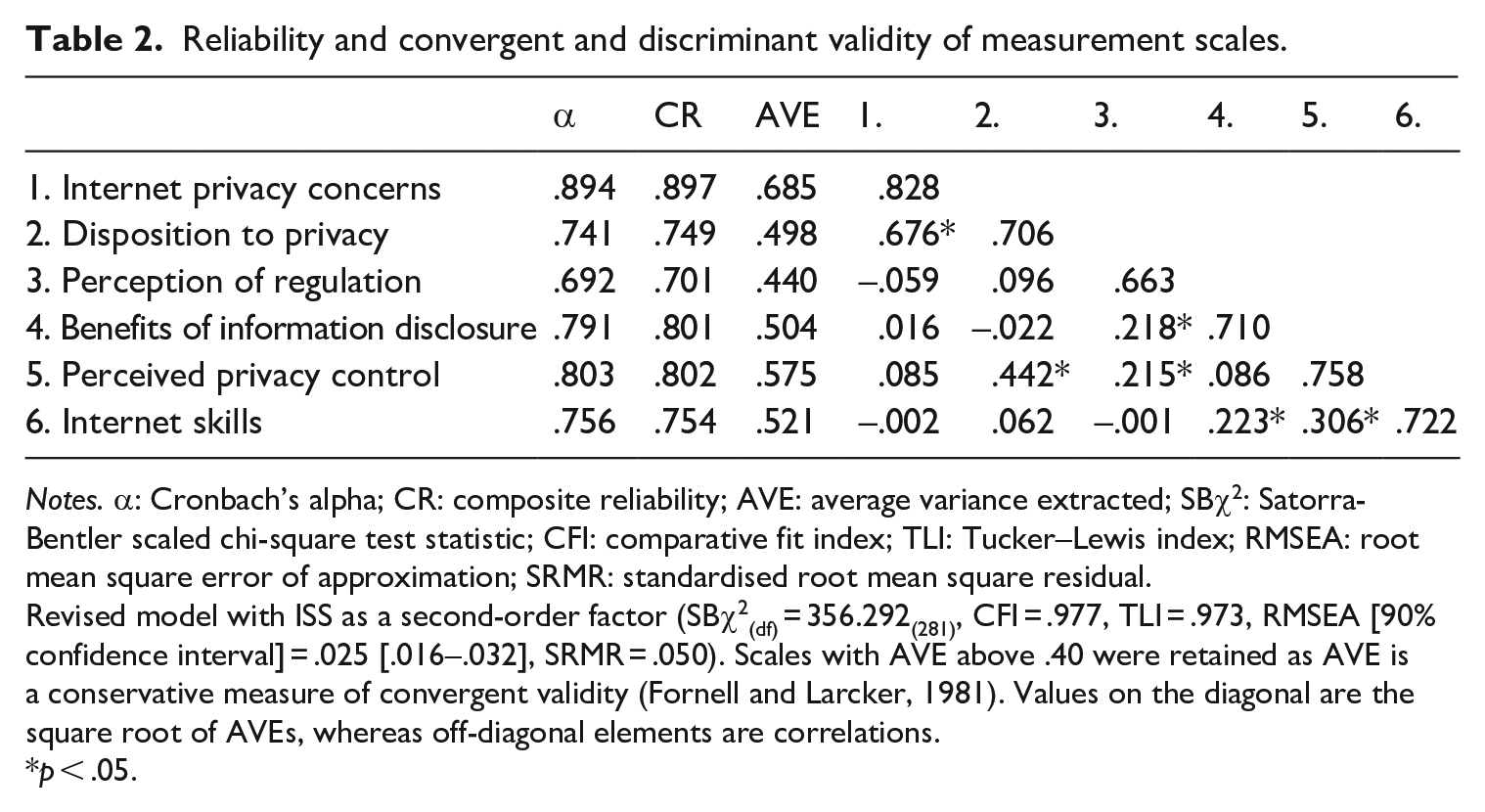
Notes. α: Cronbach’s alpha; CR: composite reliability; AVE: average variance extracted; SBχ2: Satorra-Bentler scaled chi-square test statistic; CFI: comparative fit index; TLI: Tucker–Lewis index; RMSEA: root mean square error of approximation; SRMR: standardised root mean square residual.
Revised model with ISS as a second-order factor (SBχ2(df) = 356.292(281), CFI = .977, TLI = .973, RMSEA [90% confidence interval] = .025 [.016–.032], SRMR = .050). Scales with AVE above .40 were retained as AVE is a conservative measure of convergent validity (Fornell and Larcker, 1981). Values on the diagonal are the square root of AVEs, whereas off-diagonal elements are correlations.
p < .05.
Internet skills were asserted with 13 items taken from the Slovenian version of the short Internet Skills Scale (ISS) (Grošelj et al., 2021). To reduce the response burden, we did not use the whole scale. The ISS measures operational, information navigation, social and creative skills, which together provide an overall assessment of Internet skills. Respondents answered on a scale from 1 = ‘not at all true of me’ to 5 = ‘very true of me’, with the option ‘I do not understand what you mean by that’ also included. The theorised second-order factor structure of the ISS with four first-order factors had acceptable fit, but the information navigation factor had poor reliability and convergent validity. After the removal of the items measuring the information navigation skills, the initially assumed second-order factor structure fit the data well, showing good internal consistency and convergent and discriminant validity (Table 2).
Because Internet uses and use-by-proxy are considered as formative constructs, we did not assess them in CFA due to identification issues (Kline, 2015). Internet uses were operationalised as the breadth of (different) Internet uses to capture the heterogeneity of online activities. They were assessed using a 13-item inventory adapted from Reisdorf et al. (2021). Cultural, social and personal uses were each assessed with 3 items, whereas 4 items measured economic uses (see Online supplement A). For each item, respondents indicated whether or not (0 = ‘no’, 1 = ‘yes’) they had engaged in the corresponding activity in the past 12 months. The score for (breadth of) Internet uses was calculated by first averaging across the items for each type of use and then across the four indices obtained for each type of use. Thus, a single composite variable was obtained where users with higher scores engaged in a broader range of online activities. We used a single composite variable for Internet uses because we evaluated general, rather than context-specific, perceptions of privacy (Li, 2011).
Use-by-proxy was measured with an inventory developed by Petrovčič et al. (2022), composed of a screening question and a nine-item scale that assessed the variety of online activities for which respondents relied on others. The screening question first asked respondents whether or not they engaged in use-by-proxy. Respondents who did not engage in use-by-proxy were assigned a value of 0 = ‘no use-by-proxy’. Those who responded affirmatively were presented with nine items asking them whether or not they (0 = ‘no’, 1 = ‘yes’) had turned to someone else to do any of the listed activities on their behalf in the past 12 months (see Online Supplement A). The overall use-by-proxy score was obtained by summing the nine items.
Analytical strategy
The proposed model (Figure 1) was tested using SEM in R (R Core Team, 2020) with the lavaan package (Rosseel, 2012). We screened the data for missing values and variable distributions before running SEM. From the total sample of 460 Internet users, we first excluded three respondents because they dropped out before answering the items on Internet privacy. Screening the remaining 457 respondents on the variables of interest, we found that only 4% of the answers were missing. However, the list-wise deletion of the units with missing values would reduce the sample to 230 units. 1 To avoid the loss of statistical power and the bias arising from dropping units, we used the full information maximum likelihood (FIML) procedure implemented in lavaan (Kline, 2015).
Next, because the distributions of some variables deviated from normality (see Online supplement A), we chose robust maximum likelihood estimation (MLR) (Kline, 2015). The fit of the model to the data was assessed using the Satorra-Bentler scaled chi-square test statistic (SBχ2), comparative fit index (CFI), Tucker-Lewis index (TLI), root mean square error of approximation (RMSEA) and standardised root mean square residual (SRMR). The fit was evaluated based on the guidelines by Hair et al. (2018: 642).
We then estimated the measurement model, which included only items for reflective constructs that were modelled as latent variables (Table 2). After confirming the measurement model, we estimated the structural model. The structural model included latent variables with manifest indicators for the reflective constructs, while the calculated composite variables were modelled as single-item indicators for the formative constructs (Internet uses and use-by-proxy). Weights were not used in SEM analyses as using total sample weights on subsamples can lead to bias (Levy and Lemeshow, 2008).
Results
The proposed model exhibited a good fit (SBχ2(df) = 428.131(329), CFI = .972, TLI = .968, RMSEA [90% confidence interval] = .026 [.019–.033], SRMR = .050). Estimation of structural relationships showed that disposition to value privacy had a strong and positive effect on IPCs (β = .800, p < .001), whereas PPC had a moderate negative effect (β = –.254, p < .001) (Figure 2). Moreover, PPC increased with higher levels of disposition to privacy (β = .395, p < .001), perception of appropriate privacy regulation (β = .179, p = .014) and Internet skills (β = .230, p = .002). IPCs increased the engagement in use-by-proxy (β = .108, p = .023), but were also a positive predictor of Internet uses (β = .145, p = .001). In relation to PPC, we could not confirm its effects on either use-by-proxy or Internet uses. Internet skills were a weak negative predictor of use-by-proxy (β = –.168, p = .007) but a very strong positive predictor of (breadth of) Internet uses (β = .758, p < .001). Engagement in use-by-proxy also increased Internet uses (β = .144, p < .001). The analysis confirmed 9 of 14 hypotheses at the p < .05 level (Table 3).
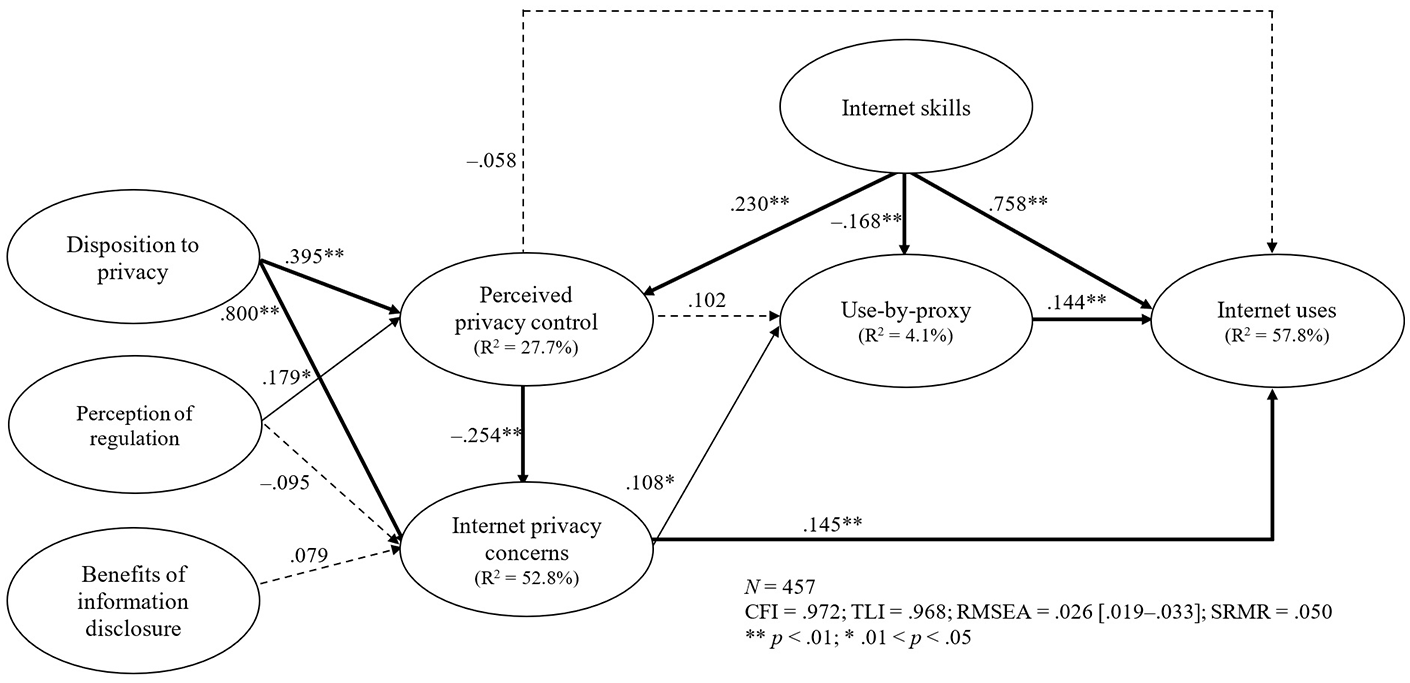
Results of the structural equation model.
Results of hypothesis testing.
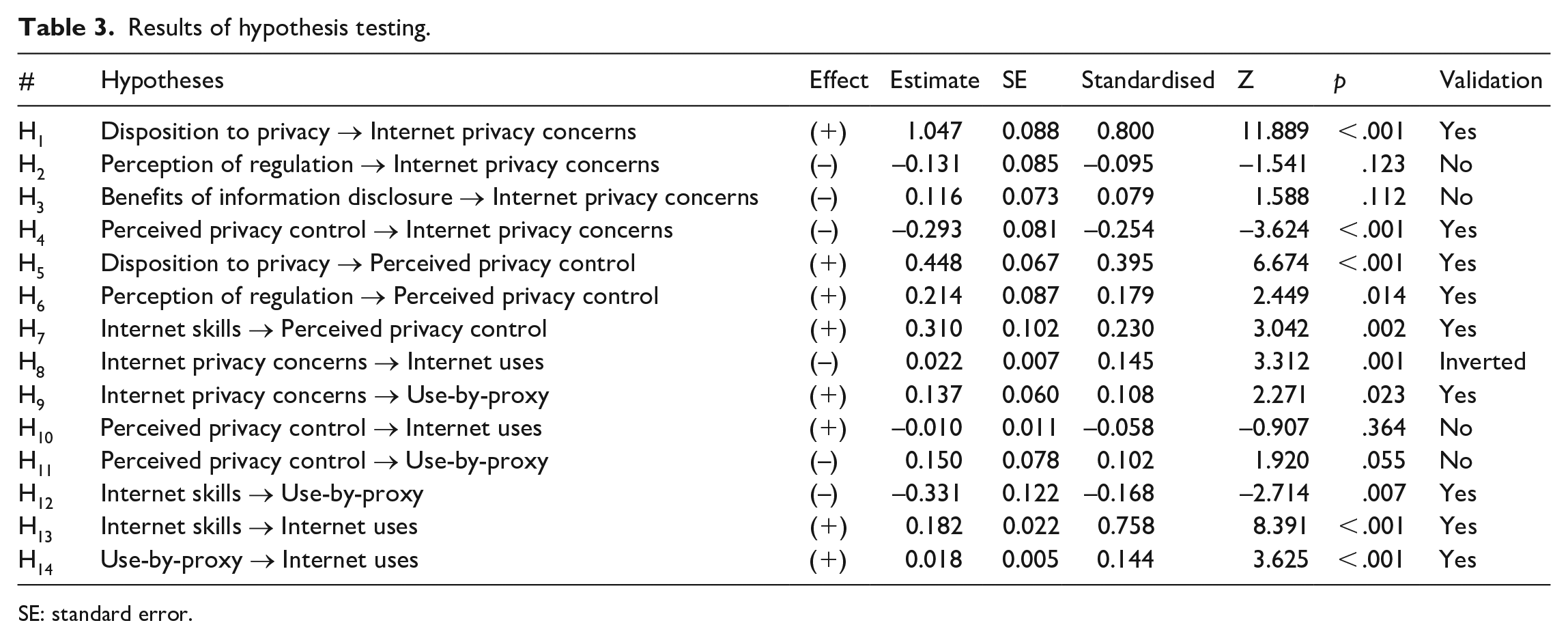
SE: standard error.
Discussion
In the present study, we aimed to integrate three theoretical frameworks (i.e. multidimensional developmental theory, protection motivation theory and the model of compound and sequential digital exclusion) to examine the antecedents of IPCs and PPC and their effects, alongside Internet skills, on direct and indirect Internet uses among Internet users aged 65 + . We found partial support for the proposed model, as older Internet users who were more concerned about their Internet privacy were more likely to engage in use-by-proxy. However, the positive impact of IPCs on Internet uses and the nonsignificant effect of PPC on direct and indirect Internet uses necessitate further attention. Below, we discuss the results and their conceptual implications, and suggest potential avenues for future research.
Looking at the antecedents of IPCs and PPC, we found that the value older users place on information privacy strongly influences their perceptions of Internet privacy, which is in line with the multidimensional developmental theory (Laufer and Wolfe, 1977). Namely, the disposition to value privacy increased both IPCs (H1) and PPC (H5). We also found that perceptions of appropriate privacy regulation increased PPC (H6) but did not directly decrease IPCs (H2). Moreover, increased levels of PPC resulted in lower IPCs (H4). However, contrary to the propositions of multidimensional developmental theory and previous research on the general population (Hong et al., 2021; Schomakers et al., 2021), we did not find that potential benefits of information disclosure lowered IPCs (H3). This might be because older Internet users are more attentive in their disclosure decisions than younger users, who often rely on privacy management heuristics (Anaraky et al., 2021). Accordingly, although older Internet users value such potential benefits, they will not change their views about Internet privacy simply due to receiving them.
Further, our data revealed supportive evidence for the extended model of the compound and sequential digital exclusion (Petrovčič et al., 2022; van Deursen et al., 2017) and its substantial integration with multidimensional developmental theory (Laufer and Wolfe, 1977). Internet skills were a strong predictor of direct (H13) and indirect (H12) Internet uses, while use-by-proxy had a significant positive effect on Internet uses (H14). Moreover, Internet skills also increased users’ PPC (H7). These results show that low-skilled users not only have less varied Internet uses but also face more constraints in protecting their privacy, suggesting that the sequential aspect of the extended model of compound and sequential digital exclusion also applies to issues associated with Internet privacy. This finding confirms the propositions by Park (2013) who suggested that lack of control over Internet privacy is a new dimension of digital exclusion. However, we were unable to confirm the hypothesised effect of PPC on use-by-proxy (H11) or Internet uses (H10). Perhaps these effects are non-significant because of the inclusion of Internet skills and our focus on the breadth of direct and indirect Internet uses. 2 In other words, the general ability to respond to challenges posed by the Internet is more important in determining the variety of Internet uses than individuals’ beliefs about control over their privacy. Drawing on the theory of contextual integrity (Nissenbaum, 2010), we could expect that in some specific domains, such as social network site use (Chen, 2018) or when sharing information with marketers (Mothersbaugh et al., 2012), PPC may play a more important role.
We confirmed the positive effect of IPCs on use-by-proxy (H9), suggesting that older users who are more concerned about their Internet privacy ask other users to perform more online activities on their behalf. Interestingly, although IPCs and Internet skills are statistically significant predictors of use-by-proxy, they explain a small proportion of the total variance of use-by-proxy (R2 = 4.1%). While scholars have mostly examined contextual and demographic antecedents for engagement in use-by-proxy among Internet non-users (Dolničar et al., 2018; Grošelj et al., 2019) or considered the lack of Internet skills as a driver of use-by-proxy among Internet users (Petrovčič et al., 2022), it seems that other motivational drivers of use-by-proxy besides IPCs (e.g. previous negative experiences with privacy breaches) should be examined further. In addition, this and previous studies addressed use-by-proxy in relation to general Internet use, and not to specific actions related to privacy protection on the Internet. As there is evidence of older Internet users’ reliance on others to manage their privacy settings and protective software (Frik et al., 2019; Murthy et al., 2021), more specific types of use-by-proxy and its antecedents and consequences should be studied in the future.
Relatedly, we also found that the theoretical link between IPCs and Internet uses needs further conceptual elaboration. Although our data revealed a significant effect of IPCs on Internet uses, the association was positive and not negative (H8). There are several possible explanations for this finding. One is related to Rogers’ (1983) suggestion that individuals may simply ignore a certain threat if they feel unable to cope with it. This seems a feasible explanation given that our data were collected during the COVID-19 pandemic, when older Internet users – many of whom are low-skilled users – were impelled to adjust their Internet uses by engaging in new online activities if they wanted to access health services and social resources remotely. The second explanation draws on the multidimensional developmental theory, which states that assessment of potential privacy threats usually occurs after the activity has been performed (Laufer and Wolfe, 1977). Accordingly, older users who engage in a broader range of Internet activities might evaluate their uses as threatening their privacy only retrospectively, giving the impression that higher IPCs lead to a broader range of Internet activities. This explanation is likely because respondents in the current study were asked about activities they had performed ‘in the past 12 months’, whereas for IPCs, they indicated their current perceptions. The third possible explanation is that older Internet users also rely on other privacy protection strategies (besides use-by-proxy). Importantly, the use of privacy protection strategies can mitigate the effect of IPCs on online behaviour (Chen, 2018). Hence, including predictors related to other privacy protection strategies (e.g. providing false information or using privacy protection software) into the model might result in the diminished direct positive effect of IPCs on Internet uses.
Such an extension of the model could also help us to more comprehensively and critically evaluate the implications that use-by-proxy, as a privacy protection strategy, has for digital and social inequalities in later life. Older adults differ in their views of privacy and privacy literacy (Elueze and Quan-Haase, 2018), and use-by-proxy might allow access to online resources to many who lack the necessary confidence to expand their Internet uses. However, use-by-proxy can also perpetuate some of the existing digital and social inequalities that affect them (Büchi et al., 2021). For instance, although older users-by-proxy may rely on others to mitigate their IPCs, this does not mean that their (online) privacy is in fact protected. Murthy et al. (2021) found that family members helping with privacy protection might themselves have only limited knowledge of protection. This can be quite critical in countries with overall lower Internet skills such as Slovenia (Eurostat, 2022) where older users-by-proxy cannot easily find a sufficiently skilful person to help them – especially if they usually turn to their spouses and/or peers (Marler and Hargittai, 2022). Next, relying on use-by-proxy might hinder the development of privacy protection skills among older Internet users (Frik et al., 2019; Murthy et al., 2021), making them even more vulnerable and preventing them from becoming self-reliant users. Moreover, while use-by-proxy can help older adults achieve the desired outcome on the Internet, it can have undesired social consequences such as feelings of dependency among users-by-proxy or increased burden among proxy providers (Hunsaker et al., 2019; Murthy et al., 2021). In this sense, although use-by-proxy enhances the online privacy of older adults it might dissolve the social tissue that is supporting their digital inclusion. Therefore, as Park (2021b) recently suggested, an integration of positivistic and normative approaches in addressing the problem of online privacy seems to be needed also in the context of use-by-proxy research to better detangle its implications for the relationship between digital and social inequalities.
Limitations and future work
This study has some noteworthy limitations. First, the proposed model focuses only on one potential privacy protection strategy (i.e. use-by-proxy). Examining a broader range of privacy protection strategies would provide a more comprehensive overview of how older Internet users manage their IPCs online. Such an extension of the model could also provide evidence on whether increasing levels of IPCs lead to and/or are mediated by these strategies.
Second, the proposed model focuses on general privacy concerns and the overall breadth of direct and indirect Internet uses rather than dealing with these notions in a specific online context. The results of our supplementary analyses (see Online supplement B) showed that there were no substantial differences between the proposed model and a model with Internet uses separated into different types, suggesting that the conceptual propositions in the proposed model can be generalised to different online domains. Nonetheless, given that perceptions of privacy are context-dependent (Nissenbaum, 2010), future research could investigate how domain-specific IPCs and PPC are related to engagement in use-by-proxy in specific online contexts.
Third, the results of a multigroup analysis (Online supplement C) showed that the tested model is robust against gender, age and educational differences among older Internet users. However, following the model of compound and sequential digital exclusion, future studies could investigate how sociodemographic characteristics affect the variables in the proposed model.
Fourth, although response rates of around 6% are typical for telephone surveys and unlikely to deteriorate the accuracy of survey estimates (Kennedy and Hartig, 2019), a higher response rate would increase the generalisability of the results (Dutwin and Lavrakas, 2016).
Finally, our findings are based on a cross-sectional survey design, which limits the analysis of causal relationships among variables. As discussed, the evaluations of privacy often happen retrospectively (Laufer and Wolfe, 1977). Hence, a longitudinal study that investigates how perceptions of privacy evolve and shape the direct and indirect Internet uses of older adults could provide a more comprehensive assessment of causal influences.
Conclusion
While older adults represent a heterogeneous group of Internet users, for many of them IPCs can represent a real barrier to online participation and expansion of their digital engagement. Consequently, they often engage in privacy protection strategies such as use-by-proxy to minimise privacy breaches or mitigate their IPCs. In the present study, we proposed a conceptual model by integrating three theoretical frameworks to explain what factors affect IPCs and PPCs and how they, along with Internet skills, predict direct and indirect Internet uses in later life. While we confirmed that use-by-proxy is used by older Internet users to mitigate their IPCs, future work should extend the research on variables related to other privacy protection strategies among older adults to more comprehensively explain the conceptual mechanisms that determine the effects of PPC and IPCs on Internet uses. Such an investigation would be especially timely in the post-pandemic world, as governments and other organisations have initiated programs aimed at developing diverse online health and social platforms that require Internet users not only to have general Internet skills but also to have adequate levels of online privacy literacy and privacy protection management. We believe that expanding the research on digital inequalities among older adults with aspects related to privacy perceptions and protection strategies is paramount to developing a more comprehensive understanding of older adults’ digital (dis)engagement. Such understanding is also necessary to foster their long-term digital inclusion and address the age-related challenges of social inequalities in an increasingly digitalised society.
Supplemental Material
sj-docx-1-nms-10.1177_14614448221122734 – Supplemental material for The roles of perceived privacy control, Internet privacy concerns and Internet skills in the direct and indirect Internet uses of older adults: Conceptual integration and empirical testing of a theoretical model
Supplemental material, sj-docx-1-nms-10.1177_14614448221122734 for The roles of perceived privacy control, Internet privacy concerns and Internet skills in the direct and indirect Internet uses of older adults: Conceptual integration and empirical testing of a theoretical model by Jošt Bartol, Katja Prevodnik, Vasja Vehovar and Andraž Petrovčič in New Media & Society
Supplemental Material
sj-docx-2-nms-10.1177_14614448221122734 – Supplemental material for The roles of perceived privacy control, Internet privacy concerns and Internet skills in the direct and indirect Internet uses of older adults: Conceptual integration and empirical testing of a theoretical model
Supplemental material, sj-docx-2-nms-10.1177_14614448221122734 for The roles of perceived privacy control, Internet privacy concerns and Internet skills in the direct and indirect Internet uses of older adults: Conceptual integration and empirical testing of a theoretical model by Jošt Bartol, Katja Prevodnik, Vasja Vehovar and Andraž Petrovčič in New Media & Society
Supplemental Material
sj-docx-3-nms-10.1177_14614448221122734 – Supplemental material for The roles of perceived privacy control, Internet privacy concerns and Internet skills in the direct and indirect Internet uses of older adults: Conceptual integration and empirical testing of a theoretical model
Supplemental material, sj-docx-3-nms-10.1177_14614448221122734 for The roles of perceived privacy control, Internet privacy concerns and Internet skills in the direct and indirect Internet uses of older adults: Conceptual integration and empirical testing of a theoretical model by Jošt Bartol, Katja Prevodnik, Vasja Vehovar and Andraž Petrovčič in New Media & Society
Footnotes
Acknowledgements
We thank Jerneja Laznik and Darja Grošelj, PhD, for their support in conducting the survey. We also thank all anonymous reviewers for their valuable comments and constructive suggestions.
Data availability statement
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship and/or publication of this article: The study was conducted as part of the first author’s Young Researcher fellowship, financed from the national budget by a contract between the Slovenian Research Agency and the Faculty of Social Sciences, University of Ljubljana. This research has also been co-funded by the Slovenian Research Agency (Grant nos. J5-2558 and P5-0399).
Supplemental material
Supplemental material for this article is available online.
Notes
Author biographies
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
