Abstract
Hacktivists oftentimes challenge or subvert existing power relations or structures and attempt to promote reform. How the public perceives occurrences of hacktivism can influence the direction and impact of operations, including their potential success. Public support can encompass person power, computational ability, resources and solidarity, among other things. This study examines socio-legal contexts in which an individual is embedded and personal perceptions as predictors for support for hacktivism. Using representative survey data from 23 countries (n = 23,140), the study finds that more effective civic participation mechanisms and more positive views toward alternative actors and hacktivists’ utilitarianism motives were associated with heightened support. In contrast, greater trust in legal and state authorities promoted opposition. Effective justice was not associated with more support but was with less opposition for hacktivism. Implications for campaigns, social movements, and desistance of activity are discussed.
Introduction
Known hacktivist activity is reportedly subsiding. Hacktivism is often defined as the use of legal and/or illegal methods to achieve social and/or political objectives within a collective action setting (Banks, 2017; George and Leidner, 2019; PytlikZillig et al., 2015; Sorell, 2015; Steinmetz, 2016; Webber and Yip, 2018). According to the 2019 Insikt Group Cyber Threat Analysis, mentions of hacktivism in mainstream media, underground forums, and technical blogs have decreased since 2016. Active hacktivist groups publicly conducting cyber campaigns have also declined during this period (Insikt Group, 2019). However, despite these reductions in activity, efforts by hacktivists persist with new waves of activity emerging from the ebb and flow of political events (Menn, 2021). In 2018, Anonymous, for instance, shut down 260 Sudanese governmental websites in retaliation for violent actions taken by Khartoum against protesters (Africa Times, 2018). In 2020, they also claimed responsibility for a series of campaigns against local police departments in the United States in protest against police misconduct (Molloy and Tidy, 2020).
In some circumstances, hacktivist groups can play an important social role as a final check against corporate and governmental abuses. The success of such operations can be contingent on public support, with some hacktivists even asking outright for public assistance. Although some types of involvement in hacktivist campaigns can require a high degree of technical sophistication, the public can assist with operations or campaigns with limited technical skills (Denning, 2011; Jordan and Taylor, 2004). They can volunteer their computers for use in distributed denial of service (DDoS) attacks, participate by clicking a link or visiting a site, or can provide tools/tutorials for others (Denning, 2011; George and Leidner, 2019; Holt and Kilger, 2012; Majchrzak et al., 2013; PytlikZillig et al., 2015; Solomon, 2017). The public can also raise the profile of campaigns by engaging in clicktivism (i.e. upvoting or following) or metavoicing (i.e. sharing, commenting or retweeting) (George and Leidner, 2019; Majchrzak et al., 2013). A 2015 Anonymous operation called #OpParis, for instance, which involved DDoS efforts against CloudFlare, gained supporters through social media and created a huge wave of attention.
Public support for campaigns can be a valuable resource for hacktivists and is an important external factor for the success and effectiveness of many different types of social movements (Jardine, 2014). Public support can be both active and passive, with both being essential for successful campaigns. Active support encompasses resources, person power, or computational ability, whereas passive support, for example, could involve members of the public refraining from disclosing the identity of hacktivists. Social movements can become successful if activists mobilize enough support—including labor, resources, and solidarity (McCarthy and Zald, 1977). Alongside pressing powerholders for demands, hacktivist campaigns also sensitize the public to their cause (Coleman, 2013a). Legislators often pay attention to public opinion and, with enough public support and action, campaigns have the potential to spread into large-scale structural change and/or policy reform (Coleman, 2013a; Kubitschko, 2015). AnonyOps and VoxAnon (along with many others), for instance, helped raise awareness of two US proposed bills, Stop Online Piracy Act (SOPA) and the PROTECT IP Act (PIPA), and publicized protesting efforts such as blackout day. The two bills lost critical political support and were ultimately defeated (Coleman, 2013a; Fuchs, 2014).
Despite the potential for the public to influence the course and success of operations, an understanding of the correlates of support for and opposition to hacktivism is largely lacking and could reveal the conditions under which campaigns are more likely to have public support, and, therefore, are potentially more likely to be successful. Continued efforts aim to understand the motivations and effects of actual hacktivists and ideologically driven hackers (e.g. Bodford and Kwan, 2018; Holt et al., 2017a; Tanczer, 2017; Webber and Yip, 2018). These works can provide a foundation for an understanding about more passive and widespread public support for hacktivism. Based on a search of the literature, only one study appears to directly investigate public support for hacktivism (PytlikZillig et al., 2015). This work focused primarily on psychological factors that might be associated with support and resistance among STEM (science, technology, engineering, and mathematics) students in the United States.
Given the extent to which public support could possibly influence the occurrence and direction of hacktivist campaigns, the purpose of this study is to further explore what factors—both individual and country level—relate to public perceptions toward hacktivism. Using representative survey data from 23 countries, the current article presents and tests hypotheses about the public’s support for hacktivism. Although the data are historical (2015/2016), the article expands our empirical focus of public support to the global context and introduces contextual socio-legal mechanisms as a source of opposition to and support for hacktivist groups.
The article finds that the effectiveness of civic participation mechanisms and trust in legal/state authorities are associated with decreased support for hacktivism. Individual perceptions that hacktivism has utilitarian functions and trust in alternative actors are also associated with decreased support for hacktivism. The opposite is found for increased opposition; however, although effectiveness of judicial measures was not significantly associated with support, decreases in the effectiveness of judicial measures correlate with decreased opposition to hacktivism.
Predictors of support of hacktivism
Cyberspace readily allows hackers with political and/or ideological beliefs to target businesses, institutions, individuals, and governments. Hacktivist activities can involve denial of service and DDoS attacks, data breaches, site redirects, theft of information, automated email bombs, and defacing webpages and malware/viruses (Banks, 2017; Denning, 2011; Solomon, 2017; Sorell, 2015; Steinmetz, 2016). The consequences of these actions can be detrimental. In 2013, for instance, Anonymous hacked into a website operated by the South African Police Service and released approximately 16,000 records about victims and whistleblowers (Van Niekerk, 2017). Despite these concerns, the efforts of hacktivists can also result in desired changes and/or public awareness about perceived public issues. Anonymous’ #OpISIS, for instance, is attributed to dismantling 149 Islamic-State associated websites and flagging about 101,000 Twitter accounts (Brooking, 2015).
The public can react in different ways to occurrences of hacktivism, and their support or opposition can have the potential to influence the direction of campaigns. In social movements, more generally, the boundaries between participants and the public are often blurred (McAdam et al., 2003; Tarrow, 2011; Tilly and Wood, 2020). The implication of these fuzzy boundaries is that hacktivists originate from within the public but perform distinct social roles from the public at large. Hacktivists are members of the public engaging in cyber activities to achieve social or political objectives (Banks, 2017; George and Leidner, 2019; PytlikZillig et al., 2015; Sorell, 2015; Steinmetz, 2016; Webber and Yip, 2018). Hacktivists may also be a subset of the overall population which are highly skilled. However, examples such as the Low Orbit Ion Cannon, an open-sourced plug and play application for network stress testing and DDoS attacks, demonstrate how individuals with low technical skills are not barred from participation. Their origin from within the public, as is the case with social movements more generally, can be advantageous, particularly as it may legitimate politically motivated actions (McAdam et al., 2003; Tarrow, 2011; Tilly and Wood, 2020). In many cases, hacktivists may act against seemingly corrupt or biased governments, corporations, and/or organizations, nominally at least on behalf of the public’s interest in transparency, accountability, good governance, and so forth. The distinction between hacktivists and the public, then, is a partial one that is often bounded in space and time. It can be best understood as one wherein (1) hacktivists drawn from the public actively participate in politically and/or ideologically motivated cyber actions in a particular place and time, and (2) the public are those that are not directly participating in a particular hacktivist event but might still hold views toward the activity. Despite its lack of active participation, the public’s ability to confer legitimacy on groups that are broadly supported can either fuel or hinder hacktivists’ efforts, such as through mechanisms like metavoicing (George and Leidner, 2019; Majchrzak et al., 2013).
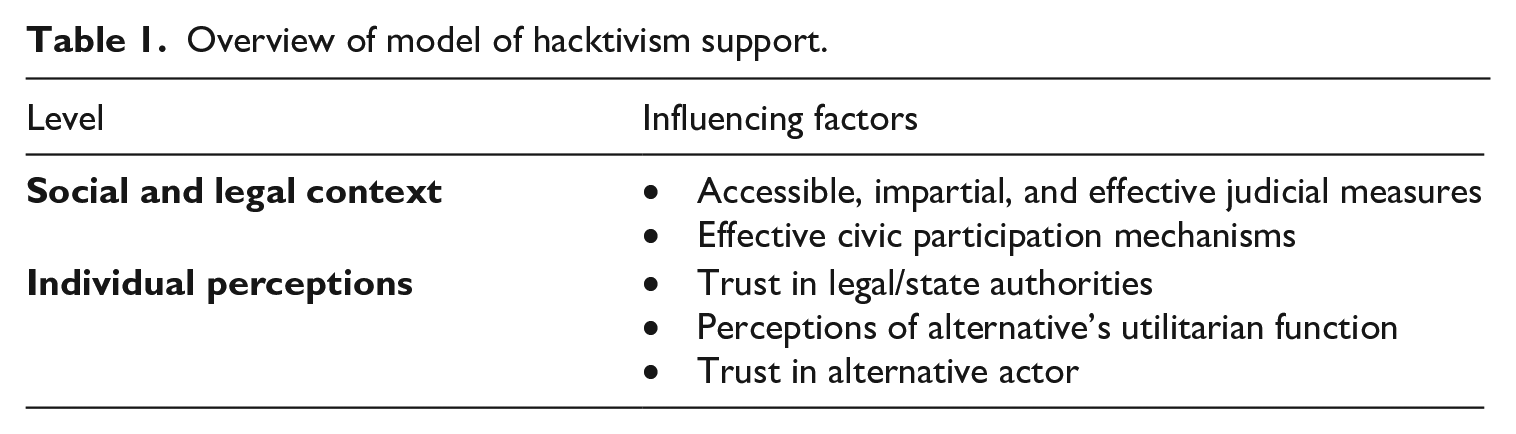
To better understand support for hacktivism, this section draws on existing literature about hacktivism to propose socio-legal and individual factors that could correlate with support for and opposition to hacktivism (see Table 1 for an overview). The influencing factors apply to hacktivist activities that are highly publicized. Hacktivism is multifaceted and can refer to categories such as cyberterrorists, civic hackers, and hackers or vigilantism, whistleblowing, guerrilla communication, and electronic humanitarianism (George and Leidner, 2019; Klein, 2015; Kubitschko, 2015; Loveluck, 2019; O’Malley, 2013; Smallridge et al., 2016). The public, however, often receives a truncated account of hacktivist activity. Some acts may remain under the radar of the public or media for a variety of reasons, such as fear of repercussion or hostility from nation-states (Kubitschko, 2015; Milan and Hintz, 2013). Some hacktivists may also use “insider strategies” such as cooperation with authorities through advocacy and lobbying (Milan and Hintz, 2013). Publicized acts, in contrast, often use more traditional protest disruption tactics, or “outsider strategies” that question the legitimacy of powerholders and usually pressure for change (Milan and Hintz, 2013). It is from these overt resistance tactics and collectives—highly visible and readily recognized—that the public draws their framing of hacktivism and on which this article focuses.
Overview of model of hacktivism support.
Accessible and effective judicial measures
Hacktivism can be a form of resistance and a way to intentionally challenge or subvert existing power relations or structures (Beck, 2016; Coleman, 2013a; Tanczer, 2017). Resistance implies “actions involving consciousness, collective action, and direct challenges to structures of power” (Rubin, 1996: 245). It is a way to refuse conformity, prompt system accommodation, and punish institutions for non-compliance.
Some forms of resistance are indirect and covert; however, publicized resistance is typically direct and overt, where the populace can collectively mobilize (Coleman, 2013a; Milan and Hintz, 2013). Anonymous, for instance, released information about employees of the Cincinnati Police Department following the shooting of Paul Gaston by Cincinnati officers (Carrero, 2016). As another example, in 2021, Myanmar Hackers disrupted governmental websites in protest against a military coup (Aljazeera, 2021). Coleman (CIGI) refers to these acts of resistance as “weapons of the geek.” The hacktivists or “geeks” are often visible and privileged actors that call attention to themselves and their issues through technology-enabled political acts (Madarie, 2017; Tanczer, 2017; Yar and Steinmetz, 2019).
In these publicized acts, there is typically a directive for reform or an attempt to change the objectionable state of affairs. Anonymous campaigns, for example, often are accompanied by filmed demands pressuring and/or holding institutions accountable for their inaction. For example, in a video threatening the city of Sacramento about their no camping ordinances and its effect on the homeless, Anonymous asked for a 60-day moratorium (Eidam, 2016). As another example, in response to perceived corporate malfeasance, the Impact Team threatened the release of Ashley Madison’s customer and company data unless their services were shut down (Tuttle, 2015).
A sense that change is possible underpins these attempts at reform. Activists need to believe that institutions of concern can be responsive to their demands. According to efficacy theory, people engage in protest because they believe changes to the existing conditions are possible through political actions (Gamson, 1992). Those involved need to believe, to some extent, that political actions can influence wider structures of power before engaging in personally costly activity (Van Stekelenburg and Klandermans, 2013). Institutions may be unresponsive to the public via a number of pathways, including, among others, unfair restrictions of legal services, a lack of judicial impartiality, limited legal rights for victims and the accused, and slow and drawn-out criminal adjudications.
While efficacy theory speaks mainly to direct participation in political events, the existence of potential institutional (un)responsiveness could also matter for public support. Although perceptions of group efficacy take into account multiple factors, the public also needs to believe positive change could happen to some degree, and such a belief may be less likely to occur in a hostile, ineffective, or impartial state. Indeed, the public may even face punitive responses from challenged institutions if hacktivists are to launch a campaign. Hacktivists typically live outside the region of conflict, creating a sense of detachment from their efforts and local movements, and their identities often stay unknown (Hai-Jew, 2013). Those involved are then more impervious to punitive responses than the general public and so the public can be left bearing the cost. The public may not want to suffer the heightened backlash when the system is perceived as unresponsive to change and so choose to not express support (active or passive) for hacktivist groups.
This discussion would lead us to expect that greater support for hacktivism in the public would be present in countries where effective, impartial, and accessible judicial measures are most developed. Specifically, people in countries with ineffective enforcement of regulations as well as an inaccessible and corrupt criminal and civil justice might be less optimistic of alternative methods that need a system responsive to change to address problematic conditions. This discussion leads to the first hypothesis:
Effective civic participation
Cyberspace is increasingly a place to express political and ideological beliefs. Hacktivism, as resistance, is a form of cyber protest that provides a form of civic participation (Banks, 2017; Fitri, 2011; Solomon, 2017; Yar and Steinmetz, 2019). It is a type of collective action or set of behaviors attempting to improve a perceived disadvantaged state (Wright et al., 1990). As mentioned, hacktivists often act in defense of civil rights and often fight against perceived oppression (Hampson and Jardine, 2017; Milan, 2012). As stated by Coleman (2013b), geeks are “the new guardians of our civil liberties.” Like traditional forms of protest, hacktivism allows the citizenry to voice their dissent and exercise a freedom of expression and assembly (Klang, 2016; Tanczer, 2017; Yar and Steinmetz, 2019).
The cyber component to hacktivism can provide an alternative to traditional forms of civic participation. In an experiment, for instance, the best predictor of a willingness to engage in cyberattacks against a home country among students was the willingness to engage in offline protests (Holt and Kilger, 2012). Resistance is culturally, socially, and historically dependent (Tilly, 1977). The socio-technical network of the Internet provides additional opportunities and benefits for people (transnationally) to become involve in campaigns (Sorell, 2015). Compared to offline actions, hacktivism efforts are often less costly, require fewer resources, and no physical and public presence to execute (Solomon, 2017; Sorell, 2015). The Internet has become a digital place of resistance, where the “geek” wields their weapon (Coleman, 2013a; Milan, 2012; Wong and Brown, 2013).
The public could see hacktivism as a more attractive course of action when opportunities for free assembly and expression of opposition toward the government are blocked. Citizens of democracies may engage in on- and off-line protests against their government (Huddy and Khatib, 2007); however, activists from more repressive regimes might have a greater need for the added protections afforded to them by protesting online (Sorell, 2015; Webber and Yip, 2018; Yar and Steinmetz, 2019). When undertaking online protests, participants can employ various anonymity-granting tools that can protect people from the dangers of assembly, such as arbitrary arrest or surveillance by officials (Jardine, 2015, 2018a, 2018b).
As an example, in 2012, Anonymous had grievances with the Government of Uganda and its anti-homosexuality policies (Solomon, 2017). Advocacy for LGBTIQ rights in Uganda is hampered by homophobia and anti-gay laws (Solomon, 2017). Traditional forms of protest would be nearly impossible without police targeting the gathering. Previous offline anti-homophobia campaign attempts had indeed ended in violence and loss of life (Gettleman, 2011). Hacktivism instead provides people with a safe alternative (e.g. distance and anonymity) to voice grievances to government officials. The Anonymous operation included hacking and vandalizing the webpage of Prime Minister Amama Mbabazi and additional cyberattacks against the Ugandan government.
Alongside risks of traditional protesting, suppression of civic participation could also make hacktivism an attractive alternative. Online civic participation mechanisms may be suppressed or blocked by countries. Internet censorship has increased in many countries considered both politically not free or free (Sundara Raman et al., 2020). Some censorship pertains to events, such as the government of Sri Lanka blocking Facebook, WhatsApp, and other social media platforms after the 2019 bomb blasts that targeted churches and hotels. In other cases, non-event content is increasingly being blocked by governments, such as news censorship, media sharing, and blogging platforms (Sundara Raman et al., 2020). Such censorship suppresses mechanisms of civic participation that could encourage support for alternative forms of expression.
This discussion leads to the second hypothesis that hacktivism will be more supported in countries where the option of civic participation is less available:
Legal/state actors and trust
A connection exists between an individual’s trust in legal authorities and the display of lawful behaviors. Trust is a judgment that one makes about someone else in terms of their expected actions under uncertain conditions, such as the expected behavior of law enforcement officers to fulfill their functions (Jackson and Gau, 2016). Trust is separate from institutional responsiveness. The more trust people have in the justice system, the more they are willing to undertake cooperative and lawful steps that assist police, such as identifying offenders and reporting crimes (e.g. Jackson et al., 2013; Sunshine and Tyler, 2003; Tankebe, 2009; Tyler and Jackson, 2014; Tyler and Sevier, 2013).
An implication of declining trust in legal authorities and the judicial system is that alternative extra-judicial actions become more palatable. A system, and its actors, considered untrustworthy is more likely to be circumvented when grievances arise (e.g. Apel and Burrow, 2011; de Haan and Nijboer, 2005; Ireland, 2020; Nivette, 2016; Tankebe, 2009; Wilkinson et al., 2009). The perceived inability of legal authorities to fulfill their duties (a lack of trust or confidence) influences how someone judges the system’s justice capability. This distrust can then push people into supporting or engaging in actions that resist or can undermine the state institution (Ireland, 2020; Nivette, 2016; Tankebe, 2009; Tyler and Jackson, 2014; Tyler and Sevier, 2013). Lower confidence in the criminal justice system, for instance, is associated with less moral outrage at and more empathy toward offline vigilantism (Haas et al., 2014).
Expanding this research to the cyber realm, distrust in victims of hacktivism has been associated with support for hacktivism. In an experimental study, STEM students rated whether the target of hacktivism attacks had good intentions, were competent, had integrity, or shared values with the students. In the presented scenarios, the targets were climate scientists, football players, a university and publishing house (i.e. MIT and JSTOR), and credit card companies. Trust in these targets resulted in a greater resistance to hacktivism from the students (PytlikZillig et al., 2015). Trust in legal authorities, however, was not examined, but the same logic might apply considering legal/state authorities are often the victims of hacktivism and trust plays a significant role in public–state interactions more generally (e.g. Jackson et al., 2013; Sunshine and Tyler, 2003; Tankebe, 2009; Tyler and Jackson, 2014; Tyler and Sevier, 2013).
The perception that legal and state authorities fulfill their duties and can be trusted is likely associated with opposition to hacktivism. Conversely, if legal actors are distrusted, it then stands to reason that people would be more supportive of an alternative method to address perceived grievances. In these circumstances, people might have greater expectations of hacktivism making a change within society. This leads to the third hypothesis:
Hacktivists as extrajudicial actors
Alongside trust in state and legal actors, perceptions about members of the public as alternative actors in resolving and bringing forth social and political issues may also matter. In their political or ideologically motivated behaviors, hacktivists often attempt to keep traditional authorities accountable for their actions in some manner (Gorham, 2015; Slobbe and Verberkt, 2012; Webber and Yip, 2018). In interviews, for instance, hackers and hacktivists have interpreted their own position as alternatives within the Internet security ecosystem that fix and highlight problems; they often consider their behaviors as acts of civil disobedience undertaken for the common good (Tanczer, 2017).
The perception that hacktivism is useful in governing and/or maintaining accountability is likely key to public support for the activity of these groups. In vigilantism research, perceptions that extrajudicial actors are effective at addressing perceived concerns have predicted satisfaction with such groups (Badiora, 2019). In the cyber realm, students from the United States who thought that people who break into computers are helping society reported a greater willingness to engage in the defacements of personal webpages of domestic government officials (Holt et al., 2017b). Somewhat similarly, and most closely related to the current study, STEM students who thought hacking has utilitarian functions were more supportive of hacktivist actions. Utilitarian functions included providing information to the public, serving the greater good and arriving at the truth (PytlikZillig et al., 2015). This discussion leads to the fourth hypothesis:
Intertwined with perceptions of hacktivist functions is trust in the public to take on the role of amplifying or redressing issues within a society. For the public to support non-state actors in their cyber protest actions, there needs to be some level of trust that these people will fulfill their duties properly. In particular scenarios of hacktivism, trust (e.g. perceived good intentions and competence) in specific actors (i.e. poster of information, Aaron Swartz who downloaded information from JSTOR, and Anonymous) was associated with greater support for hacktivists (PytlikZillig et al., 2015). Offline, people reported greater satisfaction with vigilantism when they believed the vigilantes respected citizens’ rights, treated them well, and did not give preferential treatment to particular social and political groups (Badiora, 2019). If the public does not trust its own members to be involved in political or social decisions, support for actions by hacktivists will be limited. This discussion leads to the final hypothesis:
Data and methods
The article uses secondary data from three sources. All individual-level survey data came from the 2016 CIGI-Ipsos Global Survey on Internet Security and Trust. The data were collected between 20 November 2015 and 4 December 2015. It included information from between 1000 and 1067 respondents from 23 countries (n = 23,140): Australia, Brazil, Canada, China, Egypt, France, Germany, Great Britain, India, Indonesia, Italy, Japan, Kenya, Mexico, Nigeria, Pakistan, Poland, South Africa, South Korea, Sweden, Tunisia, Turkey, and the United States. The survey was fielded online through an Internet panel for 19 of the countries. Four countries, Kenya, Nigeria, Tunisia, and Pakistan, were sampled through a computer-assisted telephone interviewing phone-based methodology. The questionnaire was presented to respondents in their local language.
Country-level data were collected from two additional sources: 2015 World Justice Project (WJP) Rule of Law Index (WJP, 2015) and the 2016 Freedom House report (Freedom House, 2016). The 2015 WJP index captures data from 2013 to 2014; their 2016 report covers temporal periods beyond 2016. The 2016 Freedom House report represents countries from 1 January 2015 to 31 December 2015. These data sources have been widely used in a variety of studies, such as studies about the Tor network (Jardine et al., 2020; Makin and Ireland, 2019), and corruption and terrorism (Bibi et al., 2019; Lane, 2016). The combination of these data sources provides an opportunity for analysis that would not be possible alone.
Table 2 presents weighted descriptive statistics for variables in the models.
Weighted descriptive statistics (n = 22,959).
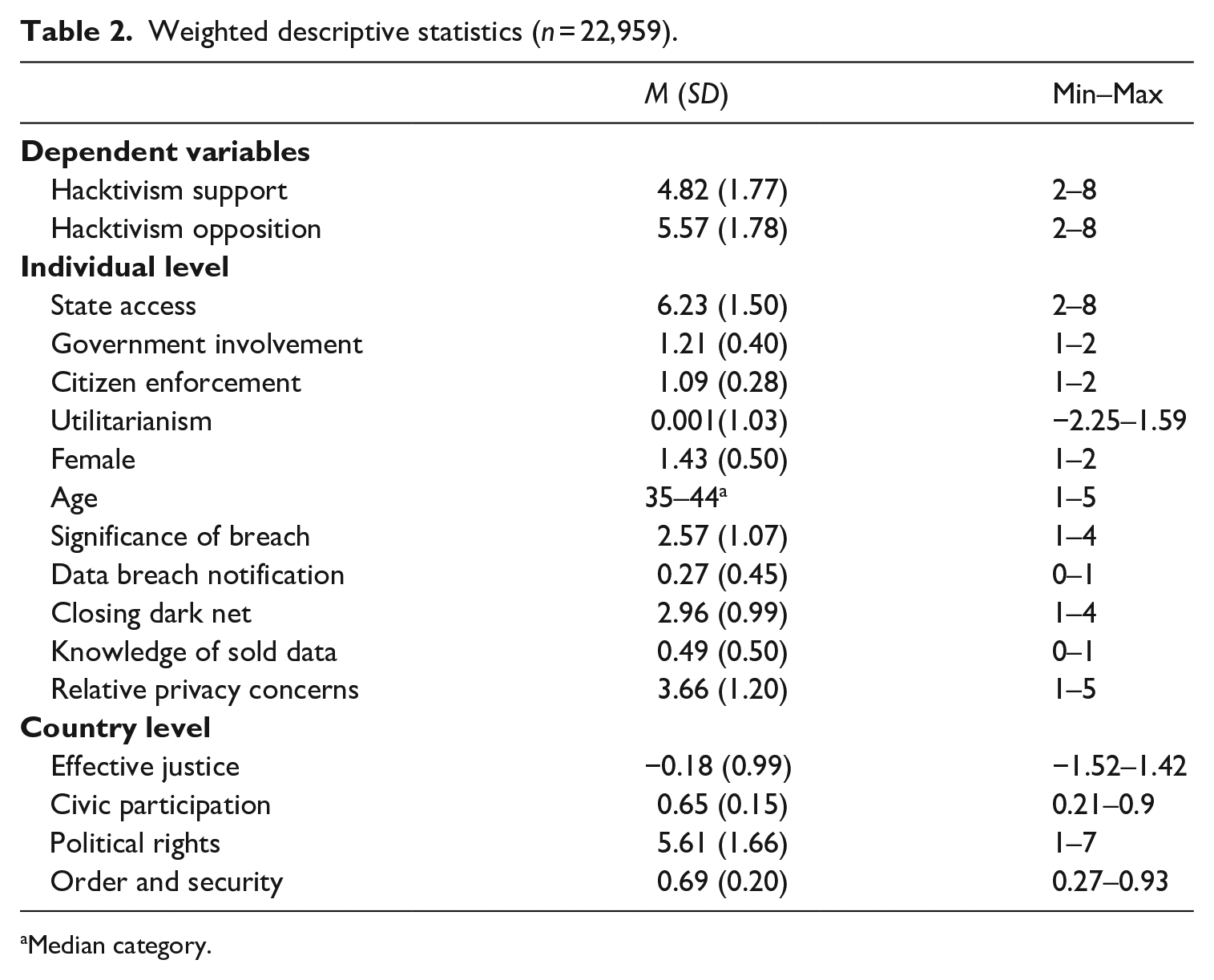
Median category.
Dependent variables
Hacktivism support
Respondents read the following information about hacktivists that focused on the releasing of confidential information: “As you may know, there are ‘hacktivist’ groups like Anonymous which hack into armed forces, government and company systems and then publish confidential material that they think the public has a right to know.” They were then asked to focus on the exposure of confidential information and indicate their agreement to statements on a 4-point Likert-type scale from strongly agree to strongly disagree.
Respondents answered four items about their support and opposition for hacktivism. Two of the items were framed in terms of support, whereas the latter two were framed in opposition. Although the items are theoretically measuring the same underlying construct of support, using principal component factor analysis with orthogonal varimax rotation, the items loaded onto two separate factors (eigenvalue = 1.92 and 1.21). Because of the distinct factors, the items worded in support and opposition were kept separate for the analysis. Since there is no reason to assume a priori that the conceptual factors outlined above behave asymmetrically, the article proceeds with the notion that support and opposition are mirror images.
Support for hacktivism was measured by combining two items: (1) “If nobody else will keep someone accountable, hacktivist groups should step in and do the job” and (2) “I have a positive view of hacktivist groups” (α = .69; r = .52). The items were reversed ordered; higher values represent stronger support.
Two of the items were combined to measure opposition to hacktivism (α = .75; r = .59). The items are (1) “Hacktivist groups are breaking the law and should be stopped” and (2) “Hacktivist groups are a nuisance and provide no real value.” The items were reversed ordered; higher values represent stronger opposition.
Country-level independent variables
Civic participation
A measure for the effectiveness of civic participation mechanisms was collected from the WJP Rule of Law Index. Their civic participation effectiveness item measures the protection of the freedoms of association, assembly, expression, and opinion. In addition, it also considers whether citizens have rights to petition governments, whether people can freely voice concerns to governmental officials, and whether governmental officials provide ample and sufficient information about decisions. Effectiveness of civic participation was measured on a scale from 0 to 1.
Effective justice
Three scores from the WJP Rule of Law Index were combined using principal component factor analysis with orthogonal varimax rotation (χ2 = 1.12e + 05, p < .001; Kaiser–Meyer–Olkin [KMO] = 0.75, α = .97). Although the high Cronbach’s alpha indicates redundancy in the factor, all three items were retained. The scores capture regulatory enforcement, civil justice, and criminal justice. Regulatory enforcement measures whether government regulations within a country are effectively enforced and enforced without improper influence or delay, and that due process is respected. Civil justice represents whether civil justice within a country is accessible; free of discrimination, corruption, or improper influence; and it is effectively enforced. Criminal justice measures whether the criminal justice system is effective, timely, impartial, free of corruption, and there is due process for the accused. Higher scores equal more effective, accessible, and impartial justice.
Individual-level independent variables
Trust in legal and state authorities
Two items were included to measure trust in legal and state authorities. First, people who believe that law enforcement should have access to online communications likely have an underlying trust in the state (state access). Two items were combined: (1) “law enforcement agencies should have a right to access the content of their citizens’ online communications for valid national security reasons” and (2) “when someone is suspected of a crime, governments should be able to find out who their suspects communicated with online” (α = .58; r = .41). The items were reversed ordered; higher values represent stronger agreeance with the statements.
In addition, another two items were combined (government involvement). Respondents indicated whether their government should help develop and enforce “new rules about how companies, governments, and other Internet users use [their] data” (0 = no; 1 = yes); no respondent opposed government involvement in both developing and enforcing rules. The combined item indicates support for either government involvement in developing or enforcing (1) or both developing and enforcing new rules (2) (α = .75; r = .60). People who support government involvement in both the enforcement and development of data laws likely have more trust in the state than those that support only one of the two ways the state can be involved.
Citizen enforcement
An item was included in the models to measure perceived trust in citizens in regulatory functions. Respondents were asked whether they supported ordinary citizens in enforcing new data rules (0 = no; 1 = yes).
Utilitarianism
The models included a factor for perceived utilitarian functions of hacktivist groups. The survey asked respondents to indicate the extent to which “hacktivists play an important role or not in keeping the following accountable”: (1) the police, (2) your government(s), (3) foreign governments, (4) large companies, (5) criminal organizations, and (6) Internet users. The items were combined using principal component factor analysis with orthogonal varimax rotation (χ2 = 76,449.80, p < .001; KMO = .90, α = .89). Factor loadings for each were 0.84, 0.86, 0.84, 0.84, 0.72, and 0.74, respectively. Higher scores indicate a perception that hacktivists play a very important utilitarian role in keeping actors accountable.
Control variables
Individual level
Demographics and personal characteristics are associated with engagement in and support for digital activism and vigilantism (Badiora, 2019; Holt and Kilger, 2012). To control for such differences, the models include a variety of demographic and personal characteristics that could correlate with the degree of expressed support for digital activism.
The models include gender (male, female) and age. To measure knowledge of technology, a proxy item was included which asked whether respondents were aware that “companies that provide free online services often sell your personal data to governments and other companies” (no or yes). A measure for relative privacy concern was added; it was measured on a 5-point Likert-type scale assessing how concerned respondents are “about their online privacy compared to one year ago.” In addition, the models include an item asking about respondents’ agreement with the following statement: “if my personal data was compromised due to a data breach, the consequences are not that significant for me, personally,” and an item for past notification of their personal data being compromised in a data breach. Finally, an item was added to the models to control for respondents’ perceptions about shutting down the dark net, a tool associated with hacktivism.
Country-level
Two country-level controls were added to the model. A measure for political rights (a 7-point scale from unfree to free) was collected from Freedom House and assesses political rights and civil liberties. An item (scale from 0 to 1) was added from the WJP Rule of Law Index measuring order and security. It represents whether crime is effectively controlled within a country, civil conflict is limited, and violence is not used to redress personal grievances.
Analysis
Two mixed-effects linear regression models were run to account for any potential dependence between respondents within the same country (Hilbe, 2009) and allow for a test of individual and country-level effects. For each model, there were 22,959 observations nested within 23 countries, with an average of 998.2 observations (min = 853 and max = 1067). The intraclass correlations (ICCs) for the two models were .01 and .03, respectively. Although the ICCs are relatively low, the clustering effect helps precaution against high Type 1 errors that can occur with even low ICCs (Musca et al., 2011).
Individual-level sampling weights were used for all models, and weighting was done on a country-by-country basis according to census information for demographic factors. The weighting makes the sample representative of the populations within each of the included countries. Robust standard errors are presented for each of the models. The Wald χ2 results for model 1 was χ2(15) = 3919.98, p < .001 and model 2 was χ2(15) = 3637.83, p < .001. Multicollinearity was within the acceptable range, with the mean variance inflation factor (VIF) being 1.95 with the highest VIF (5.49) under the commonly cited 10 VIF rules.
Results
Figure 1 illustrates the distribution of support and opposition by country with boxplots. In the figure, the box depicts the interquartile range, the thick black line represents the median, the whiskers demonstrate the 25th percentile on either side of the interquartile range, and the dots indicate outliers. Mean support for hacktivism is highest for those in India (M = 5.25, SD = 1.68, n = 1002), followed by those in Kenya (M = 5.19, SD = 1.99) and Poland (M = 5.17, SD = 1.54, n = 998). Respondents in Tunisia have the lowest mean support (M = 4.19, SD = 1.98, n = 986). Looking at the boxplot, there is large variability in support in Nigeria and Pakistan, with the middle 50% covering a wider range. Mean opposition is highest for people in Pakistan (M = 6.91, SD = 1.35, n = 853), followed by Tunisia (M = 6.48, SD = 1.86, n = 986) and Egypt (M = 6.23, SD = 1.80, n = 1000). South Korean had the lowest mean opposition (M = 5.68, SD = 1.43, n = 1002).
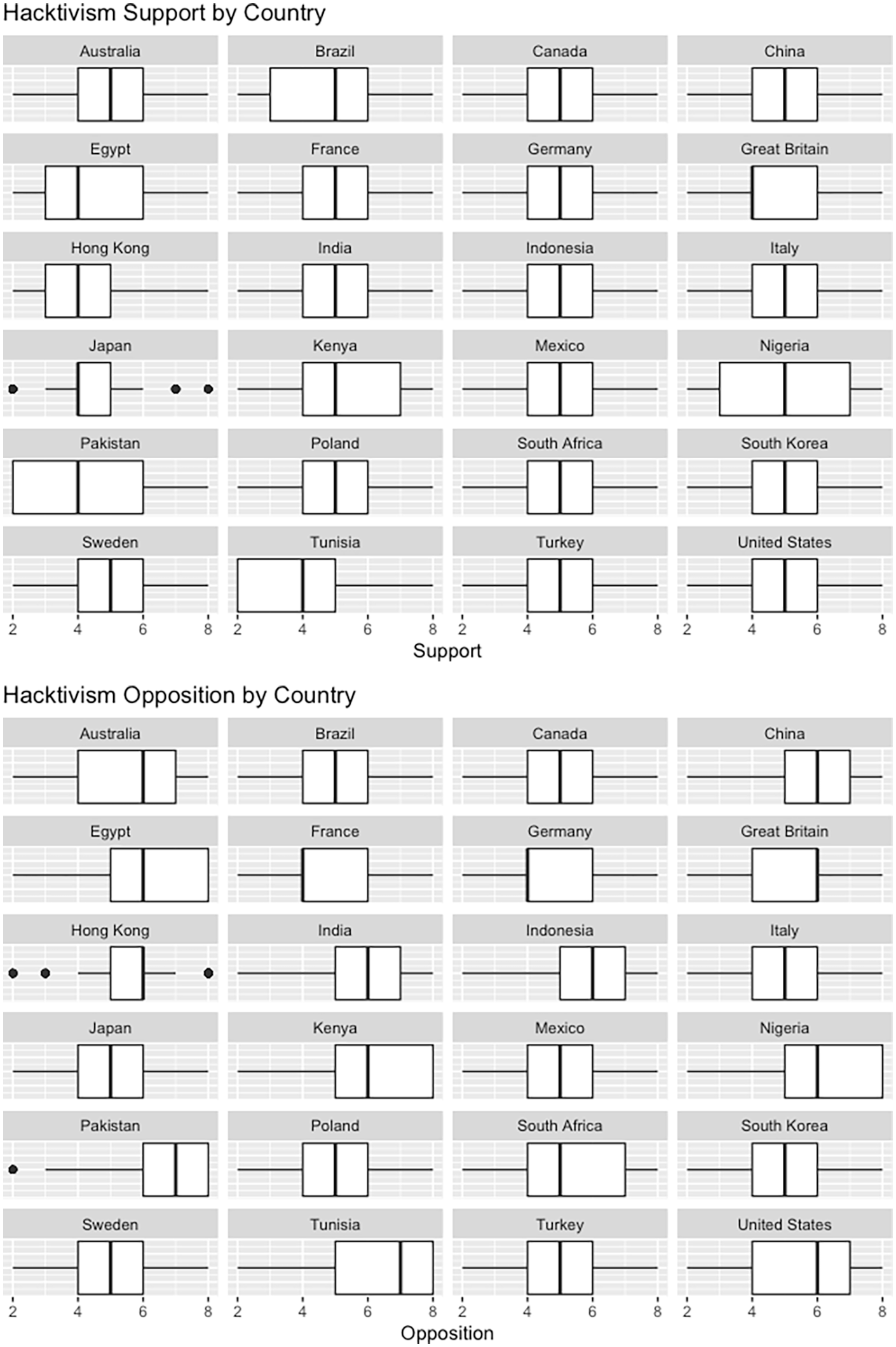
Hacktivism support and opposition by country.
Results from the mixed effect regression models, predicting support for and opposition to hacktivism, are presented in Table 3. In the following discussion, “support for hacktivism” is referred to as “positive views towards hacktivism” for a clearer read of the results.
Mixed effects regression models for support and opposition to hacktivism.
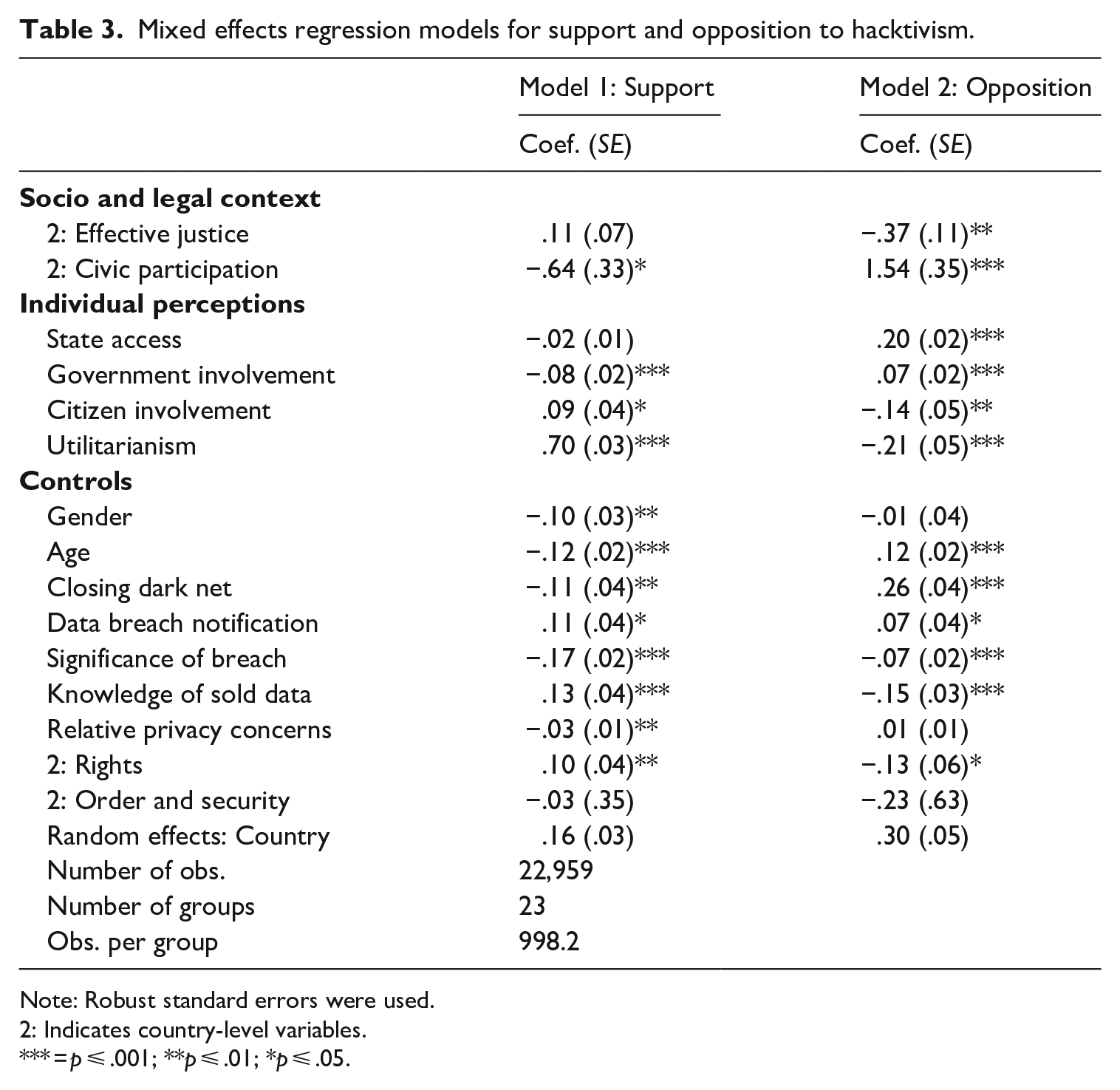
Note: Robust standard errors were used.
2: Indicates country-level variables.
= p ⩽ .001; **p ⩽ .01; *p ⩽ .05.
Model 1: support for hacktivism
The predictions of H1 were not supported. Increases in country-level effective and accessible justice are not statistically associated with increased or decreased positive views (support) toward hacktivism (b = 0.11, ns). In support of H2, increases in country-level effective civic participation are associated with decreased positive views toward hacktivism (b = −0.64, p < .05).
Hypothesis 3—increased trust in legal authorities is associated with decreased positive views for hacktivism—was somewhat supported. Government involvement in the enforcement and development of data rules and state access to online communications proxied trust in legal authorities. People who supported government involvement in both the enforcement and development of data rules reported less support for hacktivism (b = −0.08, p < .01) than those that supported their government in only one of these endeavors. State access, however, was not significantly statistically associated with positive views toward hacktivism (b = −0.02, ns). Hypothesis 4 was supported. Increases in the belief that hacktivists play an important role in keeping actors accountable were associated with increased positive views toward hacktivism (b = 0.70, p < .001). H5 was also supported. Compared to people who think citizens should not enforce new data rules, people who do think citizens should be involved in enforcement report increased positive views toward hacktivism (b = 0.09, p < 0.05).
Model 2: opposition to hacktivism
In support of H1, increases in country-level effective justice are associated with decreased opposition to hacktivism (b = −0.37, p < .01). In support of H2, increases in effective civic participation are associated with increased opposition to hacktivism (b = 1.54, p < .001). H3 was only partially supported. Greater beliefs that states should have access to communication were associated with an increase in opposition to hacktivism (b = 0.20, p < .001). Government involvement was statistically significant (b = 0.07, p < .001). People who support governments in both the enforcement and development of data rules report more resistance for hacktivism. Supporting H4, beliefs that hacktivism keeps people accountable are associated with decreased opposition to hacktivism (b = −0.21, p < .001). H5 is also supported. Compared to people who believe citizens should not enforce new data rules, people who think citizens should be involved report less opposition to hacktivism (b = −0.14, p < .01).
Discussion
Inaction from the public can be dangerous in the face of social injustice. Hacktivists are often an alternative to political disengagement (Coleman, 2013a) and, in highly publicized forms, allow the public to join in or follow along in more passive ways (Denning, 2011; George and Leidner, 2019; Jordan and Taylor, 2004; Milan, 2012). A better understanding of public support for hacktivism matters for the success of hacktivists’ activities. For collectives’ operating campaigns, for example, knowing the conditions of support can assist in getting the public’s sympathies and potentially catalyze wider societal change.
Anonymous often publishes a declaration of intention to achieve some form of public acceptance and call for action on social media (Coleman, 2013a). These messages emphasize their legitimacy and moral righteousness in their political position (Hai-Jew, 2013). In their campaign targeting Japan’s whaling program, their message directly called upon the public: “We call on you brothers and sisters to join us in a combined attack on Japan” (OpKillingBay, 2015). “Geeks” can highlight a societal problem on social media but the public needs to pick up the movement to sustain the campaign (Coleman, 2013a, 2013b). Social media messages can target these conditions of support to improve the success and effectiveness of their social movement, such as emphasizing the utilitarian motives of their campaigns.
The current study put forth and tested individual- and country-level explanations for support of and opposition to hacktivism. The findings advance our knowledge of public attitudes toward hacktivism in at least four ways. First, impartial and accessible judicial measures do not have a straightforward association with support for hacktivism. In the current findings, increases in effective and accessible judicial measures in the country people reside were not associated with more support but were associated with less opposition for hacktivism. Despite the non-significant finding in model 1, the direction of association is consistent between the two models.
One explanation for the non-significant finding for support but significant finding for opposition is a potential difference between opinions about supporting the right to engage in protesting versus supporting the actual act itself, that is, a difference between the ideal and the real. People in highly accessible, effective, and impartial justice countries might have less opposition to hacktivism because they support the right to engage in the act of protest. However, those in countries with accessible, effective, and impartial justice might not support the hacktivists’ acts themselves. They might believe there are alternative ways to engage in acts of protest or that formal processes are effective enough to make extra-judicial measures in practice inappropriate. In other words, someone in a high justice country might support people’s right to free speech and protest (i.e. have less opposition to acts of hacktivism) but might not support how other people are using these rights in practice.
The role that perceptions of effective justice seem to play, when paired with other findings in the literature, can also help to refine predictions about how public attitudes might support or oppose different types of hacktivist activity. For example, the present results indicate that effective and impartial justice correlates with decreased opposition for hacktivism. The measured item focused on disclosure of confidential information, a tactic that is often accompanied by demands or/and holding institutions accountable for their problematic (in)actions. Opposition is thus highest in countries responsive to change. In contrast, unlike some types of resistance (e.g. protesting), hacktivists that rely more strictly on system-challenging vigilantism will not rely on institutions for a response and, therefore, effective judicial systems often discourage targeted vengeance. This expectation is supported by work on vigilantism in other domains (Holt et al., 2017b; Holt and Kilger, 2012; Ireland, 2020). Hong Kong students who engage in Internet vigilantism (i.e. HFS), for example, perceived their criminal justice system to be less effective than students who were HFS bystanders, victims, or the non-participating public (Chang and Poon, 2017). These findings suggest system reform actions would positively correlate with support (and negatively with opposition), whereas system-challenging types to do the opposition in terms of public support.
Many of the other findings are more in line with past work. People in countries with more effective civic participation, for example, had decreased support and increased opposition for hacktivism. Effective civic participation includes freedom of expression and the right to petition the government. In other words, without effective means for civic participation, there is an increased need for alternative ways to express discontentment or voice concerns. In countries with blocked opportunities or lack of protection for free assembly, the attractiveness of hacktivism—often less costly, using fewer resources, and requiring little-to-no physical or public presence—is likely increased. The public likely considers this need when interpreting the actions of hacktivists. This empirical finding adds support to theoretical explanations speculated on by others (Solomon, 2017; Webber and Yip, 2018). Webber and Yip (2018), for example, theorized such a mechanism at play in the Chinese State, where alternative forms of dissent become more attractive when civic participation is suppressed.
Trust in state authorities also mattered. If the measures for legal and state trust are justifiable, increased trust in state authorities is associated with support and opposition of hacktivism. These findings extend past work that consistently finds trust of legal authorities to be a predictor of violence and vigilantism (Haas et al., 2014; Ireland, 2020; Nivette, 2016; Tankebe, 2009; Tyler and Jackson, 2014; Tyler and Sevier, 2013). People are willing to seek alternative solutions when their trust in legal/state authorities is lowered. This finding provides another incentive for states to build and maintain trust with its citizenry, as a widely beneficial step that might also reduce support for hacktivist activity.
Trusting citizens in data governance decisions increased support for hacktivism. People who believed citizens should be involved in enforcement of data regulatory decisions had increased support for hacktivism. Trust is important for public engagement in collective efforts and cooperation with other people (Van Lange, 2015). Citizens can monitor traditional authorities accountable for their actions in some manner (Slobbe and Verberkt, 2012; Tanczer, 2017; Webber and Yip, 2018). However, there needs to be some level of trust in alternative actors for people to support their efforts. Trust in hacktivist groups, however, has its concerns. In some cases, hacktivists allegedly do not engage in discussion or debate on the best approaches but pursue juvenile approaches to the problem (Mansfield-Devine, 2011). Their ideological or political agenda might also differ within the collective, which can harm trust in alternative actors in inconsistent data governance decisions. Because the identity of participants often stays unknown and, in some cases, their leaderless structure, accountability for their actions is also difficult to achieve (Hai-Jew, 2013).
Related to this point, it is important that these actors are perceived as useful in governing and/or maintaining accountability. Such perceptions are often touted in publicized hacktivist messages where their actions are framed as legitimate (DeTardo-Bora et al., 2019). Supportive of past literature (Holt et al., 2017b; PytlikZillig et al., 2015), believing hacktivists have utilitarian motives was associated with increased support for hacktivist actions. This finding also parallels how the media sometimes depicts hacktivist actions (Klein, 2015). People who adhere to this belief may perceive hacktivism as a legitimate form of protest and overlook the consequences that stem from hacktivist actions. By extension, believing that hacktivists maintain accountability, people might also be more willing to participate in campaigns, such as volunteering their computers or sharing campaign materials on social media. The utilitarian function of some hacktivist activities is questionable, however, as hacktivists themselves undermine public support by acknowledging their exploits are for personal enjoyment or the “lulz” (Coleman, 2014).
Finally, the perception of hacktivists by the public seems to align with some hacktivists self-image. Hacktivists are known to perceive themselves as security in the larger ecosystem; they improve security and increase awareness for public safety (Tanczer, 2017). Similarly, with the association between public support and state responsiveness, the public seems to believe hacktivists are a part of the system itself, not independent from it as might be depicted in some media accounts and by state officials. Hacktivists play an immune function within the wider societal system. They can keep the system in check as an overseer. In such a position, however, the capability for the system to response is essential.
Limitations
This study has limitations, each of which qualifies but does not fully undermine the findings. First, the measures for trust do not perfectly measure the underlying concepts. Beliefs about state access to communications and governmental involvement in developing and enforcing data rules, for instance, measured trust in legal and state authorities. Although related to trust, each are not a direct measure of whether the public trusts their legal institution. Future research should include direct measures of both concepts.
Second, related to the operationalizations of trust, the current study measured support and opposition of hacktivism with two items each. A broader more fleshed out scale would allow researchers to investigate support for particular actions conducted by hacktivist. Items about trust might include faith in different governmental officials in fulfilling their duties without bias or corruption.
Third, the study is limited by the included countries. Information on 23 countries was available. According to the Freedom House rankings of political rights and civil liberties, most of these 23 countries (48% or 11) are considered politically free (7 on the 7-point scale). A larger and more diverse sample of countries would provide a more in-depth investigation of country-level effects, such as the association between effective/accessible justice and civic participation. A fuller sample would also allow for an investigation of a curvilinear relationship between effective and accessible justice and support for hacktivism. Less opposition for hacktivism might be seen at the extremes of the effective and accessible scale, connecting past findings with Smith’s (2019) theoretical explanation. In addition, the analyses are by country due to the structure of the data. Some targets are cross-borders and are not limited to simply one state or legal institution.
Fourth, the data used to test the hypotheses predicting support for hacktivism are historical. The data are from 2015/2016. The findings provide a nationally representative first glimpse of the correlates between the studied mechanisms across a large number of countries. Research on the topic of support for hacktivism is currently lacking, with one exception (PytlikZillig et al., 2015). Although individual perceptions and socio-legal contexts have undoubtedly changed since 2015/2016, the associations between the mechanisms and hacktivism opinions are likely be persistent. For instance, levels of effective civic participation within a country might change throughout the years but the association between civic participation and support for extrajudicial measures likely persists.
Fifth, there are additional factors that likely associate with support for and opposition to hacktivism. Such factors include digital literacy, the policing of hacktivism, current social movements, political attitudes, and access to digital tools (Suwana, 2020). Future studies should continue to explore these alterative or complementary factors.
Sixth, there could be interpretation and translational discrepancies. The individual-level survey was presented to respondents in their local language. Languages might not have a perfect translational match for the word hacktivism. The question mentioned Anonymous as an example. Respondents might be giving their perceptions of this particular collective rather than hacktivism generally. The term hacktivism is contested and ambivalent—tactics considered activism may not be considered so by others (Tanczer, 2017).
Seventh, because the questions focus on data breaches and Anonymous—the results do not speak to all forms of hacktivism. There are forms of cyber activism that are more subtle, such as setting up free Internet access points or wireless networks (Milan and Hintz, 2013).
Finally, the study was concerned with support and opposition for hacktivism. Although there is some evidence that support for deviance or vigilantism is linked with actual engagement (Chen and Tang, 2006), the research cannot draw conclusions about actual engagement in hacktivism behaviors. Future research should investigate willingness to participate in a variety of hacktivism activities, ranging from low- to high-tech skills.
Conclusion
In conclusion, this article examined support and opposition to hacktivism, an area largely unexplored in the literature. The public can alter the course of hacktivist actions, for better or worse. They can offer up their devices, participate in low- or high-tech ways, or raise the profile of campaigns. The “geeks” may bring public attention to causes but the public needs to be brought onboard for a campaign to be sustained and spread into a social movement for wider societal change. In contrast, they can resist the activities of hacktivist by discouraging activity or campaigning for harsher penalties for hacktivism actions. It is essential that we understand what motivates the public. To do so, the article put forth and empirically tested hypotheses that considered the global context and mechanisms of judicial measures and civic participation.
Hacktivist activity in many countries has become vilified. There are often very stringent laws in place to protect the security of cyber systems, which also, intentionally or not, suppress hacktivism (Hai-Jew, 2013). Understanding the conditions in which the public is supportive of, and potentially participates in, hacktivist activity is useful for the public and policymakers to understand. It presents their work in a digestible and understandable form. Public support for campaigns can also provide an avenue for more traditional activists, Internet advocates, governmental officials to more openly engage with the hacktivist collectives (Coleman, 2013a, 2013b, 2014).
These conditions provide a better understanding of support for and opposition to hacktivism. For collectives, conditions can be incorporated into message deliverance to the public to spur further involvement and collective action. For those wanting desistance of activity, knowing what fuels support, and likely participation, is foundational. For example, the public may be morally conflicted when targeted institutions, like law enforcement, remain silent. These institutions can counteract negative sentiments toward their agency by engaging with the general public and media. If the theoretical mechanism stands, an unresponsive state or institution, for example, could spur heightened support for extralegal activity that circumvents the system completely. Much work remains to fully investigate the correlates of supporting hacktivism actions.
Footnotes
Author’s note
The manuscript is not under consideration elsewhere.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
