Abstract
Recent attention to labor trafficking as an underaddressed part of human trafficking has added urgency to the need to improve corporate supply chain actions and policies. Through a cross-case analysis of data from the agricultural sector in the United States, this paper seeks to understand labor trafficking operations through a socio-technic systems theory lens and contributes to prior literature on labor trafficking in three important ways. First, we utilize a cross-case approach to explore labor trafficking operations through a network lens and derive insights into the interconnectivity and key players in each labor trafficking operation. Second, we outline the socio-technic practices of those labor trafficking networks that maintained ties to corporate supply chains. Hence, the scope of operations management socio-technic theory is widened to also include exploitative and harmful practices. Third, we elucidate the connections between corporate and labor trafficking systems to demonstrate that corporate responsibility does not exist in a vacuum and that the interplay between legal and illicit organizations is of critical importance in combating human trafficking. Altogether, this article provides an interdisciplinary perspective using insights from operations management theory, criminology, and network design. In doing so, the assessment of socio-technic dynamics between actors broadens the operations and supply chain frame of reference beyond corporate socio-technic systems to include the illicit systems they are connected to.
Introduction
Human exploitation in global supply chains continues to be a concern for companies, governments, and civil society. In line with international laws and regulations, the United States (U.S.) criminalized human trafficking in 2000, broadly defining the crime as the exploitation of a person for labor, services, or commercial sex through force, fraud, or coercion (TVPA, 2000). Although the antihuman trafficking field has worked to increase awareness and resources to address this crime, current efforts overwhelmingly focus on sex trafficking despite the fact that recent estimates suggest 63% of global human trafficking is for forced labor (ILO, 2022). This imbalance is reflected in recent Operations Management (OM) research focused on either supply chain responsibility from a corporate decision-making perspective (Sodhi and Tang, 2019) or the identification and interdiction of sex trafficking (Keskin et al., 2021; Xie and Aros-Vera, 2022). Despite decades of human rights concerns and over 20 years of legal frameworks attempting to regulate the issue, labor trafficking networks continue to operate across global markets (ILO, 2022), leaving highly traumatizing impacts on those who have been subjected to exploitation in their work. As described in prior research, there are societal impacts and direct risks to supply chains connected to labor trafficking (Wilhelm et al., 2016) and physical and emotional health concerns for victims (Barrick et al., 2014).
The different ways in which supply chain actors are related to labor trafficking operations can inform interdiction efforts (De Vries, 2019), which is important given that the connections between labor trafficking operations and global supply chains present a major issue for companies that face increased expectations for transparency in their operations and improved social responsibility behavior (Sodhi and Tang, 2019). A common OM approach to addressing the issue has been to enhance corporate contracting and due diligence activities. Many of those activities are technical, such as maintaining information on products or performing inspections (Chen and Lee, 2017), while others may also involve social dimensions such as interviews and direct engagement (Villena, 2019).
Unlike sex trafficking, labor trafficking in the U.S. is more often identified in legal industries such as agriculture, construction, and hospitality (De Vries et al., 2020). These industries typically involve complex supply chains with corporate actors that, wittingly or unwittingly, interact with and may contribute to labor trafficking practices. These connections occur with a variety of business types including recruiting agencies, large-scale manufacturers, and small business owners, and involve otherwise legitimate supply chain behaviors such as financial transactions or logistics (Crane, 2013). Because the exploiting actors operate within the broader context of legitimate markets, labor trafficking becomes “embedded” in legitimate marketplaces (De Vries, 2019). For example, prior qualitative analyses of 30 U.S. labor trafficking and exploitation cases indicated that corporate supply chain actors are connected to labor trafficking operations through a multitude of social and economic connections (De Vries, 2019). Such connections between exploitative operations and legitimate supply chains can occur when a company outsources parts of its operations (LeBaron, 2021). Depending on whether or not corporate supply chain actors hold information about exploitation, companies may be involved in varying ways: as “defendants” or “active” contributors to exploitation; as “passive participants” when companies hold information about exploitation but do not directly contribute to such behaviors; and as “involuntary participants” when companies are (presumably) unwittingly participating in exploitation processes in the corporate supply chain they take part in (De Vries, 2019).
As many of the activities that occur in global supply chains are at the intersection of technical and social systems, we posit that the socio-technic system (STS) lens allows for a new OM frame for understanding labor trafficking in corporate supply chains. The OM literature includes legitimate STS practices (Hyer et al., 1999; Shah and Ward, 2007), but we argue that it is necessary to assess the activities that connect supply chains to trafficking networks and victims. Many of the activities of perpetrators are technical in nature (e.g., indecent payment mechanisms and falsified documents), while others involve human dimensions (e.g., recruitment and psychological coercion). As such, the STS lens can expand OM theory to create a more comprehensive picture of the ecosystems that connect labor trafficking to markets. Furthermore, understanding the structure, composition, and function of labor trafficking operations through an STS lens allows the OM field to adapt existing techniques (e.g., network interdictions, simulation models, and incentive design mechanisms) and address the connections between illicit organizations and corporate supply chains.
Therefore, while the STS lens distinguishes between social and technical ties, we additionally consider the illicit nature of these ties. Illicit actions are “illegal or disapproved of by society” (Cambridge, 2021). For labor trafficking, this would include actions such as the exertion of force, fraud, or coercion to exploit individuals (Andrees et al., 2015). To differentiate illegality from illicitness, we clarify that all illegal activities are illicit, while not all illicit activities are prohibited by law, though are frowned upon by society. We focus on illicit activities (as opposed to only illegal ones) because supply chains are often held to higher standards by customers, investors, and news media than current laws would necessitate. In sum, the STS lens allows us to understand the relationship between exploitation and supply chains and how it can be combatted.
In this paper, we conceptually and analytically examine the social, technical, and illicit practices that comprise labor trafficking operations engaged with a multitude of actors, with specific interest in corporate supply chains across a set of cases that represent different forms of labor trafficking operations. In addition to generating new insights into the ties that link legitimate social and economic contexts to illicit and victimizing practices within supply chains, our findings have implications for identification, prevention, and interdiction measures. Thus, our findings also help inform future OM decision modeling efforts that seek to effectively disrupt labor trafficking operations. Specifically, we provide insight into the structure of different sizes of labor trafficking operations (indicating that modeling approaches that seek to disrupt large, structured corporate labor trafficking networks may not be appropriate for small- or medium-sized networks), the types of ties through which actors engage in labor trafficking operations (technical, social, or illicit), and how corporate supply chains are tied to labor trafficking operations, indicating opportunities for improved governance and incentive policies to enhance supply chain transparency.
The remainder of the paper is organized as follows: Section 2 reviews the relevant literature. Section 3 describes our data and research design. Section 4 presents the analysis and results. The final Sections 5 and 6 of the paper discuss conclusions and limitations.
Literature Review
Labor Trafficking Research in OM and Supply Chain Management
The extant OM literature addressing labor trafficking has primarily focused on risk reduction for insufficient labor standards (Chen and Lee, 2017; Distelhorst et al., 2017) to minimize shareholder wealth impacts (Jacobs and Singhal, 2017; Cousins et al., 2020). However, there has been a notable shift toward understanding human trafficking networks. For example, Kougkoulos et al. (2021) use satellite remote sensing to identify migrant settlements vulnerable to exploitation, thereby contributing to early risk identification. Similarly, LeBaron (2021) describes the systemic issues that lead to exploitation. Building on this shift, we offer insights into how trafficking networks change temporally from recruitment to exploitation, which has deep implications for identification, research, and overcoming our psychological distance by better understanding trafficking (Simpson et al., 2021).
One of the tenets of STS is that it is an “interventionstrategy” to improve work systems (Bostrom and Heinen, 1977a). This aligns with the special issue in which this article appears, as we provide an understanding of network structures and STS practices that link corporate actors with illicit actors which can be used for intervention. Building on the work of Hadid and Afshin Mansouri (2014), we explicitly document STS practices to better tailor OM models to evaluate a wider range of labor trafficking interdictions based on actual practices within the labor trafficking operation, an expansion of analysis that has hitherto been missing in the OM literature. To do so, we apply an instrumental network approach to examine social, technical, and illicit practices that link various actors to a labor trafficking operation and offer insights into the OM community to better model, analyze, and interdict labor trafficking networks.
While advancements are being made to improve network interdiction theory to address the nuances of human trafficking, OM researchers continue to highlight the need for a better understanding of the network structure, composition, and function of human trafficking networks to realize the full potential of OM models (Bhimani and Song, 2016; Konrad et al., 2017). For example, Denton (2016) demonstrated the importance of prosecuted case network structures through measures such as degree centrality, transitivity, and core–periphery structures, all of which could hold interest to improve OM models of labor trafficking networks. Yet, few studies, both within and beyond the OM field, have examined the structure of labor trafficking networks. As such, little is known about the variety of network measures or socio-technic ties that connect human trafficking operations to broader societal and economic systems despite research on sex trafficking focused on the technical ties that make up a network, for example, through online advertisements (Keskin et al., 2021) or prosecuted cases (Xie and Aros-Vera, 2022). Thus, we expand interdictions beyond criminals and victims to include how legitimate businesses interact with trafficking networks based on our findings.
Furthermore, as network structures can shift (and be modeled) differently over time, we employ the three common phases of a labor trafficking operation: recruitment, movement, and exploitation (Salt and Stein, 1997). Recruiters begin by implementing strategies to target vulnerable and marginalized populations who seek better opportunities (Owens et al., 2014). From there, a labor trafficking operation will often transport victims to work venues, which may or may not involve international border crossing (Owens et al., 2014). In the final phase, the victims will work within the operation, where they are subjected to exploitative work conditions such as the use of physical, sexual, or emotional violence, isolation, withholding documents and/or pay, or hazardous labor conditions (Owens et al., 2014; Zhang et al., 2014). Labor-trafficked persons may experience force, fraud, and coercion during any or all of these three phases (De Vries and Farrell, 2018).
A Network Approach to Illicit Activities
We approach labor trafficking operations through an instrumental network lens that defines networks as being comprised of the actors (“nodes”) and the relationships (“edges” or “ties”) between them (Wasserman and Faust, 1994; Campana, 2016a). A network approach is an increasingly popular approach to studying the relations between nodes of any kind (Barabási, 2012; Lazer et al., 2009; Welles and González-Bailón, 2020). Here, we define a network as being comprised of the individuals—corporate supply chain actors and other entities—that participated in a labor trafficking operation.
An instrumental network lens helps understand the network structure of a labor trafficking operation through structural network characteristics that can reveal important organizational and operational dynamics that are important to consider when tailoring OM models to address complex social and crime problems. At the most basic level, the structural interconnectivity between all actors in a network can be described through density, which captures the observed connections as a proportion of connections that could have been present between the actors (Wasserman and Faust, 1994). Illicit networks with greater density have a greater number of ties between actors and might be more susceptible to detection and interventions than low-density networks (Milward and Raab, 2006; Morselli, 2010). Several other structural measures can help identify the key actors within illicit networks (Campana, 2016b; Morselli, 2010). For example, degree centrality indicates the number of direct connections a node has to other nodes, which may signal that node’s importance and influence within the network (e.g., greater degree centrality nodes may have a coordinating role).
Prior sex trafficking research has highlighted the importance of both degree and betweenness centrality (e.g., Mancuso, 2014), which has not been examined for labor trafficking operations. Although criminal actors with higher degree centralities may have a coordinating role, their connections are also associated with an increased risk of being detected (Morselli, 2010). Indeed, studies of other illicit networks such as drug trafficking (Morselli, 2010) and mafia networks (Calderoni, 2011) have shown that organizational leaders are not always the actors with the highest degree centrality in criminal networks. Individuals with high-degree centrality have more visibility within the network, which may increase their vulnerability to being caught. Studies have, therefore, underscored the need to examine multiple measures of centrality. Specifically, betweenness centrality—which addresses a node’s importance by measuring the extent to which it forms a “bridge” between other nodes (Carrington, 2014)—has been identified as an important metric to identify gatekeepers and brokers that connect clusters or groups to each other, such as in the context of gangs (e.g., Papachristos et al., 2013) or drug trafficking (e.g., Natarajan, 2006). Individuals with a lower status in the network may have high-degree centrality but low betweenness centrality, while individuals with higher status may have higher betweenness centrality yet lower degree centrality (Baker and Faulkner, 1993).
In this paper, we focus not only on the structure of criminal actors, but also on their connections to the legitimate business sector. Thus, the literature regarding legal supply chain network structures is also relevant. Basole and Bellamy (2014) conduct a systematic review of network analysis applied to supply chain systems and note that many studies have used centrality to explain how the network positionality of firms with high centrality affects their capabilities (Yu et al., 2008). Highly dense supply chain networks are noted to often not be beneficial or desirable given the additional coordination burden this places on supply chain members and the cost redundancies that can arise. Centrality and density measures have also been shown to influence the behavior of corporate supply chains, which Kim et al. (2011) describe as important for sustainability. Furthermore, governance mechanisms organizations used to manage lower-tier suppliers—for example, organizations working in direct contact with lower-level suppliers—to enhance tractability within the supply chain have been found to have higher network centrality measures (Tate et al., 2013; Tuni et al., 2020), which has relevance for our context of corporate involvement in supply networks.
Current Study
In our study, we employ a cross-case analysis using quantitative and qualitative information to elucidate the structural and operational relationships of labor trafficking operations. In doing so, we aim to answer the following three research questions:
What are the main characteristics of the network structures of labor trafficking operations? How do social, technical, and illicit ties feature in the overall structure of labor trafficking networks? How are corporate supply chain actors connected to labor trafficking operations?
In answering these questions, our work builds on recent OM attention to network interdictions (Keskin et al., 2021; Dimas et al., 2022; Xie and Aros-Vera, 2022) and supply chain social risk (Sodhi and Tang, 2018) to fills several gaps, including (i) exposing previously hidden relationships that exist between the corporate supply chains and labor trafficking networks, (ii) explicitly analyzing the STS practices between them, and (iii) providing a concise method to gather labor trafficking data. Importantly, our work is a first step to understanding the network structures of labor trafficking organizations and how supply chains are linked to them. This provides a rich context for future OM research seeking to develop decision models to effectively interdict labor trafficking networks.
To the best of our knowledge, no studies analyze labor trafficking networks with the breadth of entities and relationships that we do. Furthermore, no quantitative studies currently exist with analysis of labor trafficking networks and corporate supply chains through an STS lens. We begin to fill these knowledge gaps by analyzing the STS components of U.S. agricultural labor trafficking networks.
Research Design
Data Collection
Due to the difficulty obtaining primary data for illicit network operations, there is a growing trend among researchers within the OM community to turn to law enforcement and social media data to generate networks (Keskin et al., 2021; Xie and Aros-Vera, 2022). Our data collection (a) supplements publicly available law enforcement data with court and media documents and (b) explicitly captures information about corporate supply chain ties to labor trafficking, broadening the scope of actors and relationships. Although it is not without its limitations (described in Section 6), our data provides an initial opportunity to explore the connections between corporate supply chain actors and labor trafficking operations that are visible to law enforcement and the public.
The agricultural sector was chosen as our focus for examining social and technical connections within labor trafficking networks because it is one of the top three sectors with the highest number of identified labor trafficking cases in the U.S. (ILO, 2022). U.S. agriculture is a $1.05 trillion industry representing nearly 6% of the U.S. economy and supported by 21.6 million employees (USDA, 2019). The U.S. Department of Agriculture estimates that the largest group of agriculture workers are unauthorized immigrants, while 21% are authorized immigrants and 32% are naturalized U.S. citizens (USDA, 2019). While the extent of labor trafficking in the U.S. agricultural industry remains an open research topic, estimates from two recent studies found that 16% (Barrick, 2016) and 25% (Zhang et al., 2014) of undocumented migrant workers were victims of labor trafficking in local agricultural sectors in California and North Carolina, respectively.
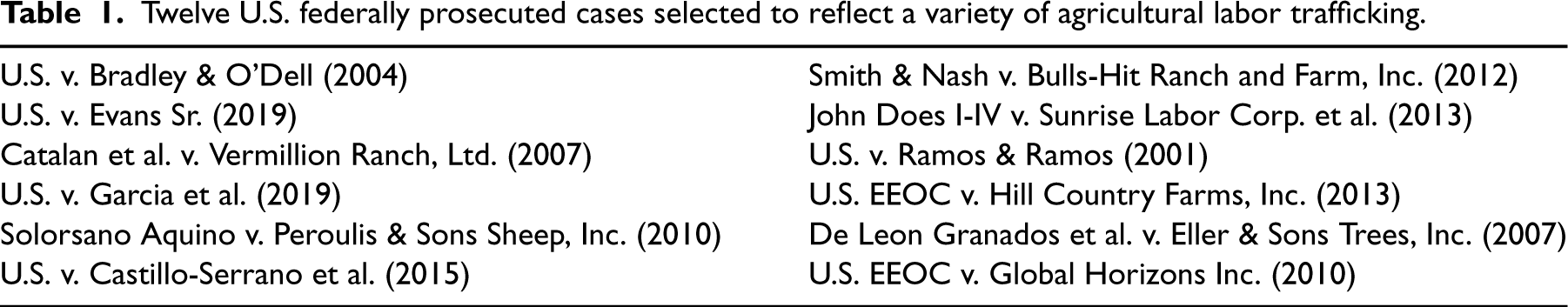
Using an overview of labor trafficking cases collected by De Vries (2019), updated with more recent cases from the Human Trafficking Database developed by the Texas Christian University 1 , we developed a list of all agricultural labor trafficking cases prosecuted under federal antitrafficking statutes, updated to include cases until 2019. This process yielded 42 agricultural labor trafficking cases. For each, we determined the agriculture type (e.g., livestock, handpicked crop, and machinery-based crop), number of victims, size of the agricultural organization (e.g., corporation vs. “mom-and-pop”), and victim legal status (e.g., U.S. Citizens, H-2A visa, H-2B visa, and Undocumented). Considering the detailed nature of the information that needed to be collected from each case to support network analysis, we employed a purposeful sampling methodology to identify a subset of cases that could be coded and analyzed within the available time and project resources and to intentionally select a sample of 12 cases (listed in Table 1) that provided a variety of agriculture types. This sampling strategy prioritizes conceptual variation over being perfectly representative of all agricultural labor trafficking cases within the U.S., a common practice for exploratory studies.
For each case, the research team collected all publicly available information on the case facts from the criminal indictment, sentencing documentation, hearing information, civil litigation documents, documentaries, news articles, and other associated documents that outline the elements of the labor trafficking crimes through Thomson Reuters Westlaw Edge, LexisNexis, and PACER. Media publications were identified by performing multiple searches on Google’s search engine using keywords associated with the case (including case name, as well as the names of businesses, worksites, and individuals identified as victims, offenders, or other prominent actors in the supply chain). This process was repeated at several points throughout the study period to ensure that the most recent reporting on the case was reflected in the collected data. This resulted in 365 total documents collected and analyzed, consisting of 271 court documents and 94 media publications.
Twelve U.S. federally prosecuted cases selected to reflect a variety of agricultural labor trafficking.
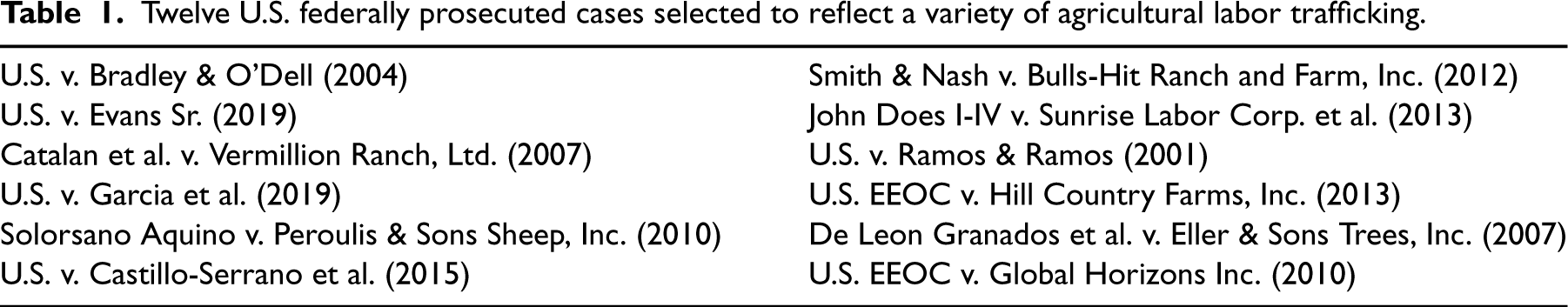
Twelve U.S. federally prosecuted cases selected to reflect a variety of agricultural labor trafficking.
Once case materials were collected for each of the 12 federally prosecuted agricultural labor trafficking cases, two trained members of our interdisciplinary research team independently qualitatively coded the material from the case documents into a structured spreadsheet to document individuals associated with the trafficking operations and the relationships and ties between them. The coding from the two independent coders was compared and deconflicted by a third coder to ensure interrater reliability and resolve all coding conflicts through a team deconfliction process.
Coding included information on companies, people, locations, relationships, recruitment, movement, exploitation, money flows, disruptions, and outcomes. As detailed in E-companion A, information was captured for each actor (person or organization) mentioned in the case (e.g., their role, age, gender, and immigration status) and information for each relationship (e.g., social, technical, and illicit; the type of STS practice; and during which phases of the trafficking network it was present).
Using the above-stated records, we constructed and compared 12 case networks that represent which actors in the labor trafficking operation were coaffiliated (e.g., because of collaboration in the supply chain, family ties, or other one-to-one affiliations), see case statistics and descriptions in E-companions B and C. Although our data cannot be used to construct whole networks representative of the true population involved in the labor trafficking case, the records provided insight into the prosecuted defendant(s) and actors that operate in their physical or social vicinity (e.g., other employees on the same farm, family members, or corporate supply chain actors). A cross-case analysis approach is well-suited to identify common features and distinct processes across designated cases (Miles and Huberman, 1994). In line with the exploratory nature of our work, the aim of cross-case analysis is not generalizability, but rather the explication of processes and investigation of the degree to which they hold under different circumstances (Kahwati and Kane, 2020).
In the 12 studied case networks, nodes represent either persons or entities such as agencies and businesses when the court records did not specify the name of a specific person. A connection between any two actors was included when records contained information that explicitly stated or signaled their coaffiliation in the pursuit of the labor trafficking operation. All connections were weighted equally: we did not have information about the level of involvement in exploitation processes and none of the actors in the constructed labor trafficking networks undertook known actions to prevent illicit activities associated with the labor trafficking operation (i.e., each actor contributed to the labor trafficking operation in some way, wittingly or unwittingly). As Table 2 shows, the networks differ substantially across the cases regarding the number of actors that were detected during the investigation and prosecution and the roles these actors had during the labor trafficking operation (ranging from 25 to 288 actors). In each case, multiple victims were identified in the court proceedings, albeit the extent to which cases involved victims in the proceedings vastly differed between the cases, ranging from approximately 14% to 63% of all actors. Besides the exploiter(s) and the detected victims, all cases involved other internal actors that were directly involved in the labor trafficking scheme, such as other employees of the company where the exploitation occurred, recruiters, or transporters (between 4% and 41% of all actors were internal actors). In addition, all cases involved at least one internal company (e.g., the company where the exploitation occurred, an internal laborer service, or an internal business partner). External companies such as businesses, business partners, or laborer services operated further down in the supply chain and were often connected to the labor trafficking operation via regular business transactions or indirect facilitation of exploitative behaviors (e.g., by profiting from cheaper end products or housing exploited workers, potentially without knowing about the labor trafficking operation). Other actors involved a variety of different actors, such as government, county, city officials, and bystanders, who were directly or indirectly co-affiliated with the defendants and wittingly or unwittingly aided the labor trafficking operation. 2
Type of roles as a % of all actors for each labor trafficking operation.
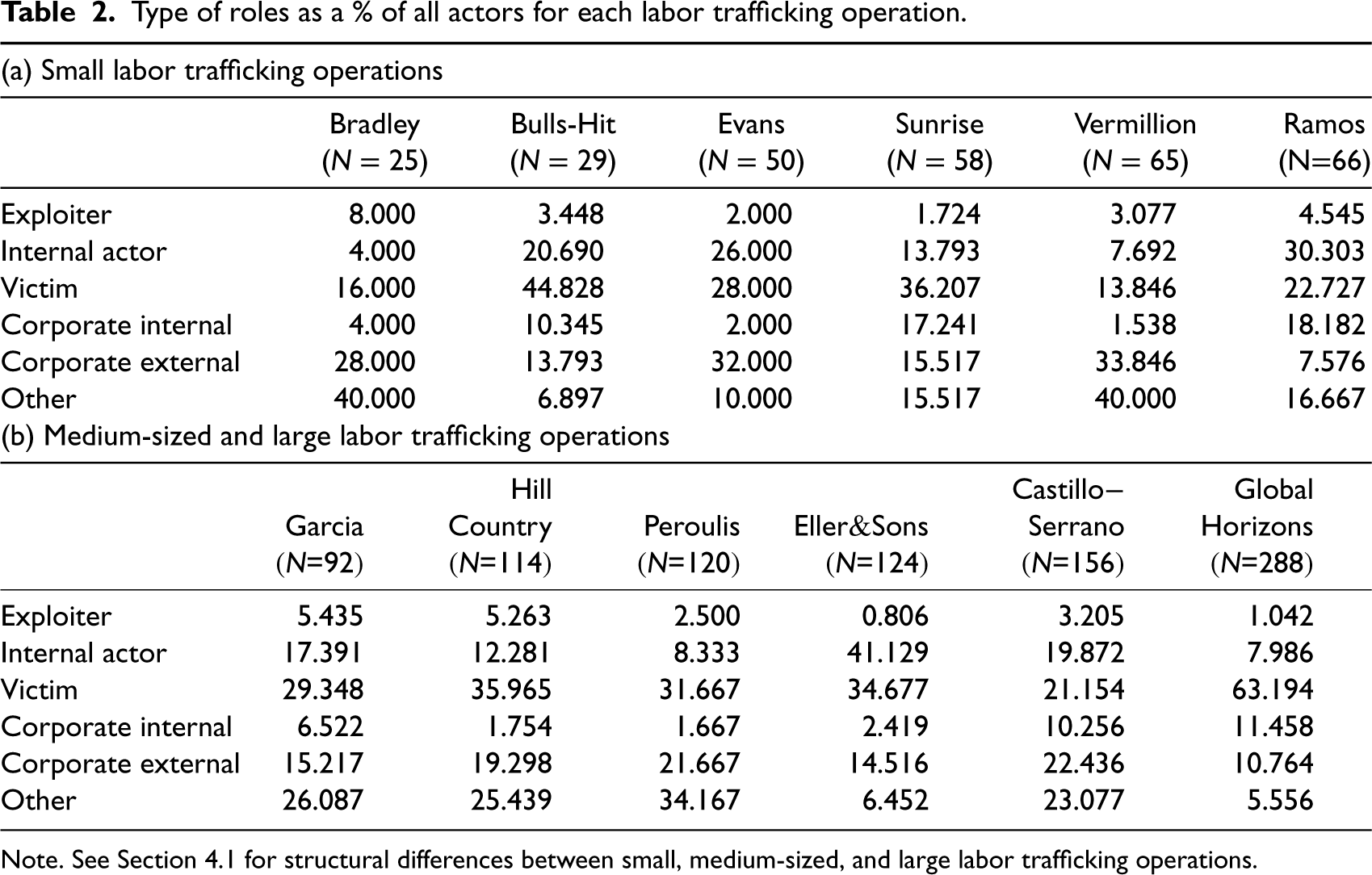
Type of roles as a % of all actors for each labor trafficking operation.
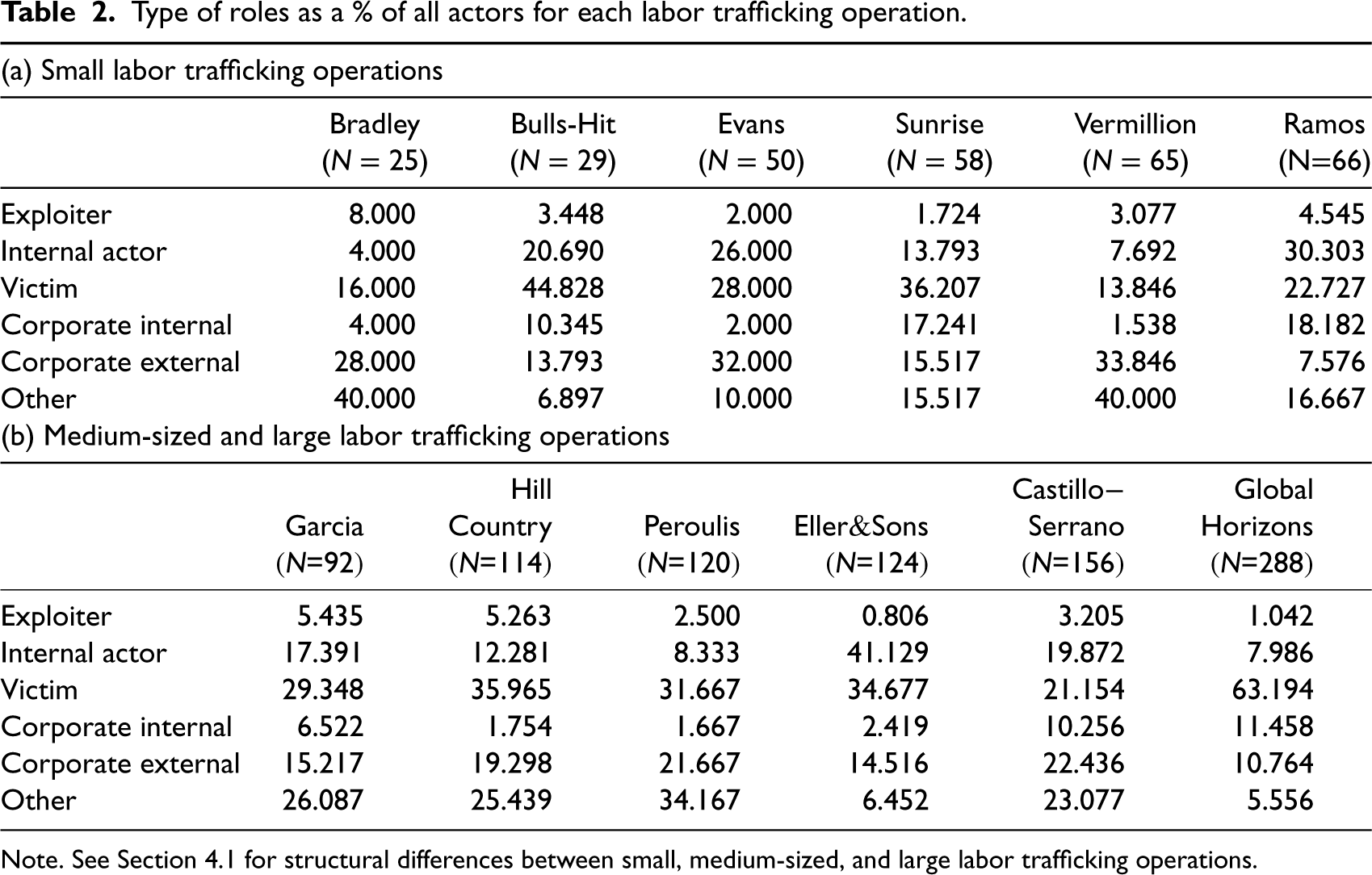
Note. See Section 4.1 for structural differences between small, medium-sized, and large labor trafficking operations.
We derived the networks from a manually developed actor-by-actor edge list, which is the complete list of connections between the actors identified in this network. This list was transformed into a symmetric one-mode actor-by-actor matrix, where each cell represents whether a connection was present between any two actors (1 = “Yes”). For each connection, we collected information about the connection type (social, technical, and/or illicit), the practice type based upon which the connection was formed (e.g., payments, housing, and transportation), and the phase in which the connection was present (recruitment, transportation, and/or exploitation).
Based on the STS literature, we define
Using these coaffiliation networks as case studies, we use three steps to explore which actors and types of underlying connections might be central to these labor trafficking operations in U.S. agriculture. First, we examine the structural features of the coaffiliation networks, such as the density of connections and the centrality of actors (explained above). Second, we explore the prevalence and types of social, technical, and illicit affiliations during recruitment, transportation, and exploitation. Third, we highlight the means through which corporate supply chain actors were involved in the labor trafficking operations by examining their individual positioning in the network and the types of ties through which they are connected to the labor trafficking operation.
This last step enables us to bridge assumptions of corporate due diligence to direct affiliations with criminal actors. It is important to note that a connection between a corporate supply chain actor and a perpetrator was only classified as an illicit connection when the interaction indicates that businesses contributed to the specific illicit practice that the relationship represents. Additionally, some relationships are best characterized as multiplex ties as they connect actors in more than one way. For example, illicit relationships might also be personal relationships (e.g., kinship-based) or legitimate in other contexts (e.g., business). Such multiplexity may underlie enduring types of relationships that are embedded in overlapping social contexts (Papachristos and Smith, 2014).
The Network Structures of the Labor Trafficking Operations
To begin answering our first research question, we present the coaffiliation networks for the 12 cases (see Figure 1), along with summary statistics for measures that describe their network structures (see Table 3). By design, all labor trafficking operations are connected graphs: Actors were linked to the labor trafficking operation if they had a connection to someone else in the labor trafficking operation. If not directly connected, actors across the cases were indirectly connected to each other through approximately two steps (see the average geodesic in Table 3, which is the average shortest distance from one actor to any other actor) and a maximum of three to eight steps (see the diameter in Table 3, which is the maximum distance from one actor to any other actor). Each stage of the trafficking process (i.e., recruitment, transportation, and exploitation) typically involved a set of different actors with varying levels of interconnectivity between these actors (see E-companions D and E for additional figures and statistics in the Supplemental Material).
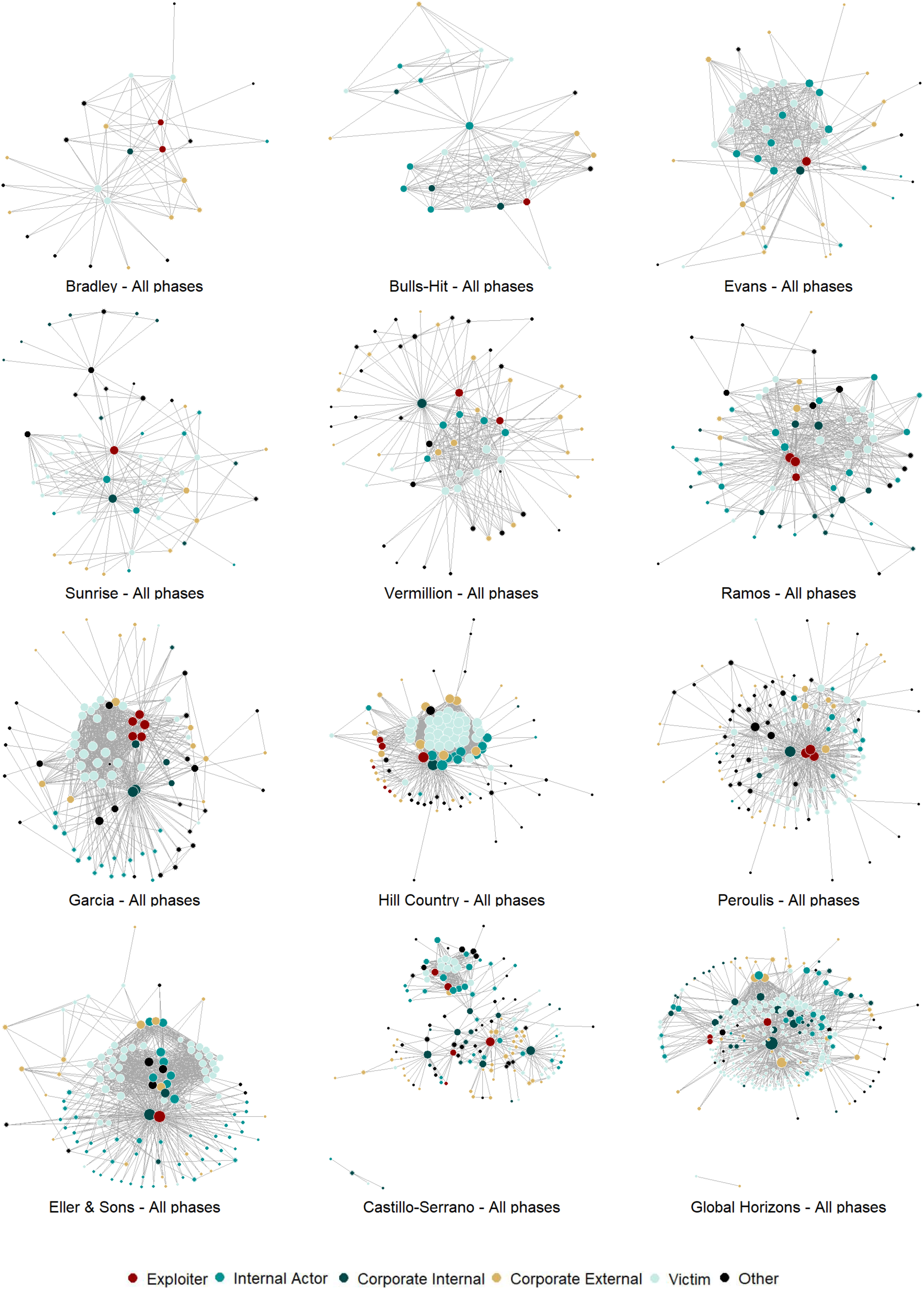
Labor trafficking network visualizations.
Network summary statistics for the labor trafficking operations.
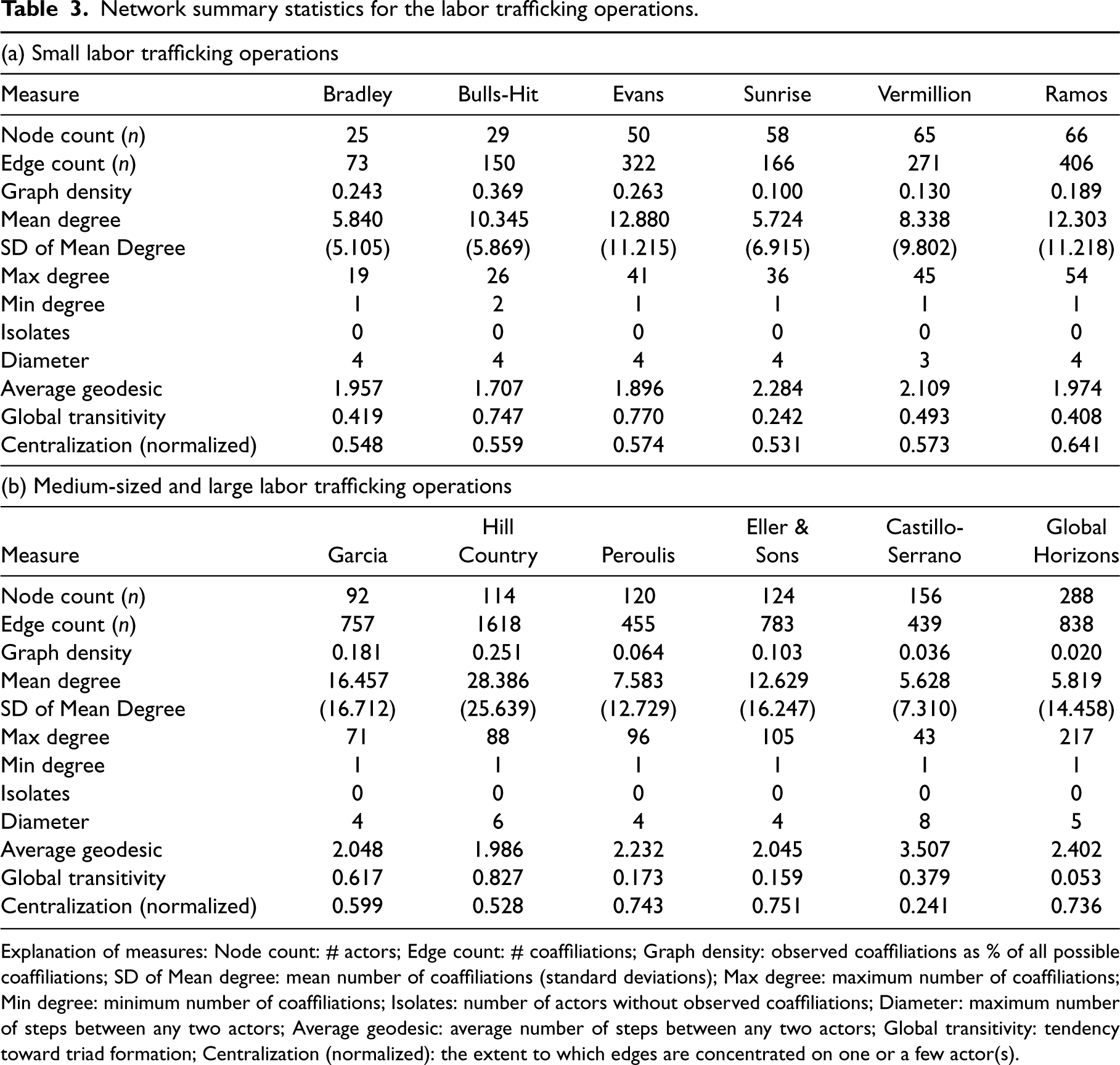
Explanation of measures: Node count: # actors; Edge count: # coaffiliations; Graph density: observed coaffiliations as % of all possible coaffiliations; SD of Mean degree: mean number of coaffiliations (standard deviations); Max degree: maximum number of coaffiliations; Min degree: minimum number of coaffiliations; Isolates: number of actors without observed coaffiliations; Diameter: maximum number of steps between any two actors; Average geodesic: average number of steps between any two actors; Global transitivity: tendency toward triad formation; Centralization (normalized): the extent to which edges are concentrated on one or a few actor(s).
Table 3 presents a summary of the network characteristics of all 12 case networks, including features such as network size, density, transitivity, and centralization. Using these network characteristics, we examined whether the 12 labor trafficking operations differ in the ways people and businesses were connected.
3
By examining the number of actors that each of the networks involved, we identified three types of labor trafficking operations that differed from one another in network size (small, medium-sized, and large): A substantive group of cases (
Although each of the labor trafficking operations studied here demonstrates unique network characteristics, a few meaningful patterns merit attention. First, the density of the networks (i.e., the number of observed ties as a proportion of the total number of possible ties) ranged from 2% (in the Global Horizon case) to 37% (in the Bulls-Hit case). In the Bulls-Hit case, a trafficking recruiter engaged with victims via homeless shelters across Florida and Georgia. Once transported to the farm in Florida, the victims were housed together in dilapidated conditions and kept dependent on the labor trafficking operation. This highly coordinated effort amongst the network recruiters, exploiters, and enforcers may explain the higher density levels exhibited compared to other cases. Across the cases, density was often observed to be the highest in the exploitation stage compared to previous stages (see E-companions D and E in the Supplemental Material). In that final stage of a labor trafficking operation, more actors collaborated with one another in the pursuit of the exploitation of workers (see also the higher degree centralities of actors in the exploitation stage), leading to our first proposition:
Network density is higher during the exploitation phase of labor trafficking operations, compared to the recruitment and transportation phases of agricultural operations.
It is important to observe that a network’s density may be associated with its size. For example, the three smallest labor trafficking operations (Bradley, Bulls-Hit, and Evans) had among the highest density levels, representing small but tightly-knit labor trafficking operations. Qualitative case descriptions indicate that laborers in these cases were exploited on farms owned by defendants who were coaffiliated through familial ties, personal relationship ties (e.g., marriage), or trusted business affiliations. For example, in the Bradley case (the smallest labor trafficking operation), it was a couple who recruited at least five Jamaican workers and exploited them at their tree removal company between 1999 and 2001. Similarly, in the Evans case, a couple operating a farm labor contracting business in Florida and North Carolina recruited laborers from homeless shelters to deceive them into work with false promises of pay and housing. Lastly, the Bulls-Hit case involved a few trusted business partners that jointly operated and managed a farm. Other small and medium-sized labor trafficking operations had generally lower, though still substantive, density levels. To illustrate, a family based tree landscaping company that exploited workers primarily from Guatemala, Mexico, Honduras, and Colombia from 1995 to 2005 engaged with a substantive number of internal employees and external business entities, though less evidence existed about coaffiliations amongst these actors (Eller & Sons). The two largest labor trafficking operations (Castillo-Serrano and Global Horizons) had the lowest density levels. This indicates that while many actors were linked to the networks, relatively few coaffiliations were observed between them.
Second, transitivity seems to be an important binding mechanism amongst defendants and their affiliates in most labor trafficking operations (especially for cases such as Bulls-Hit, Evans, Garcia, and Hill Country, see Table 3). Transitivity reflects the degree to which ties were part of triads rather than dyads, which occurs when the coaffiliation between actors i and j, and actors i and k, implies a greater likelihood that actors j and k are also coaffiliated (i.e., mirroring the social network idea that “the friend of my friend is also my friend” (Wasserman and Faust, 1994). Such triadic closure is often based on social mechanisms that establish familiarity and trust between a set of actors (Wasserman and Faust, 1994). From this observation, we propose the following:
Transitivity is a profound social binding mechanism in agricultural labor trafficking networks.
For example, in the Bulls-Hit case, high transitivity levels may have been built on the close-knit social connections among the defendants and others facilitating the operation, such as during the exploitation phase when they demonstrated a coordinated effort to keep workers from escaping by bringing in drug dealers to exploit addictions for money and labor. While transitivity was substantive across the varying phases of most labor trafficking operations (see also E-companion E in the Supplemental Material), it was remarkably lower in the largest labor trafficking operation (the Global Horizons case). This corresponds with the lowest density level in that case compared to other cases (i.e., relatively fewer connections were observed overall). Additionally, the Global Horizons case had relatively fewer social ties (32%, discussed below) compared to all other cases where the majority of ties were social ties requiring human-to-human interactions. This provides an opportunity for future research to test whether high transitivity emerges from a larger fraction of social ties in labor trafficking operations using a larger sample of cases.
Third, the normalized centralization measures (see Table 3) indicate that coaffiliations were overall strongly concentrated on a single actor or a few actors, typically the prosecuted defendants, their companies, managers, and field supervisors in the studied cases. These actors had the largest mean degree centralities and, through their central position in the network, likely the largest observed influence in the exploitative operations. 4 Compared to other labor trafficking operations, the Peroulis, Eller & Sons, and Global Horizon cases—which were among the largest—had the greatest amount of centralization (and relatively lower transitivity levels compared to other cases). However, it is important to note that the Castillo-Serrano case is a similarly sized labor trafficking operation but had the smallest amount of centralization. Across the cases, centralization was often strongest during the exploitation phase (see E-companion E in the Supplemental Material). Although these greater amounts of centralization and larger degree centralities of defendants and a few other key actors might be a reflection of investigative strategies focusing on only one or a small group of actors, it could also suggest that the exploitation process was centrally driven by these defendants and key actors, more so than in other cases that featured lower levels of centralization but higher levels of transitivity (and where the exploitation process could have been driven by trust between a set of actors rather than central coordination). Therefore, we propose:
In agricultural labor trafficking operations, coaffiliations are strongly concentrated on a few actors that have higher degree centralities than other actors.
For example, in the Garcia case, the federal indictment accused the Garcias and two others of trafficking 14 indigent Mexican men over just four months in 2016. The three Garcias were feared by victims and the central exploiters within the labor trafficking operation, with each person within the Garcia family having an integral part of the operation.
Fourth, nearly all networks studied here had an evident core–periphery structure, involving a “core” of closely connected actors and a “periphery” of actors that were more loosely connected to the core and each other (Borgatti and Everett, 2000; Gallagher et al., 2021). To determine the extent to which labor trafficking operations had core–periphery structures, we examined the correlation between the observed networks and core–periphery structures. We examined the existence of core–periphery structures for each case by fitting a discrete core–periphery model to a given network (we used the core_periphery function in the netUtils package in R, see Borgatti and Everett (2000)). For nearly all labor trafficking operations, we identified strong correlations between the observed networks and the core–periphery models, ranging between 0.54 and 0.96. Only in the Global Horizon case was the correlation between the observed network and the core–periphery model modest (
Agricultural labor trafficking networks have a core–periphery structure.
For example, in the Hill Country case, victims were directly exploited by mid-level managers through physical and mental abuse and barred from leaving. These managers and the victims made up the core of the network, whereas the main exploiter and companies within the operation (who were responsible for gross underpayment) made up the periphery.
As an example of how socio-technic practices feature in the labor trafficking operation (our second research question), we highlight that the types of ties that held nearly all networks together were predominately (
Edge types (as % of all edges in the network).
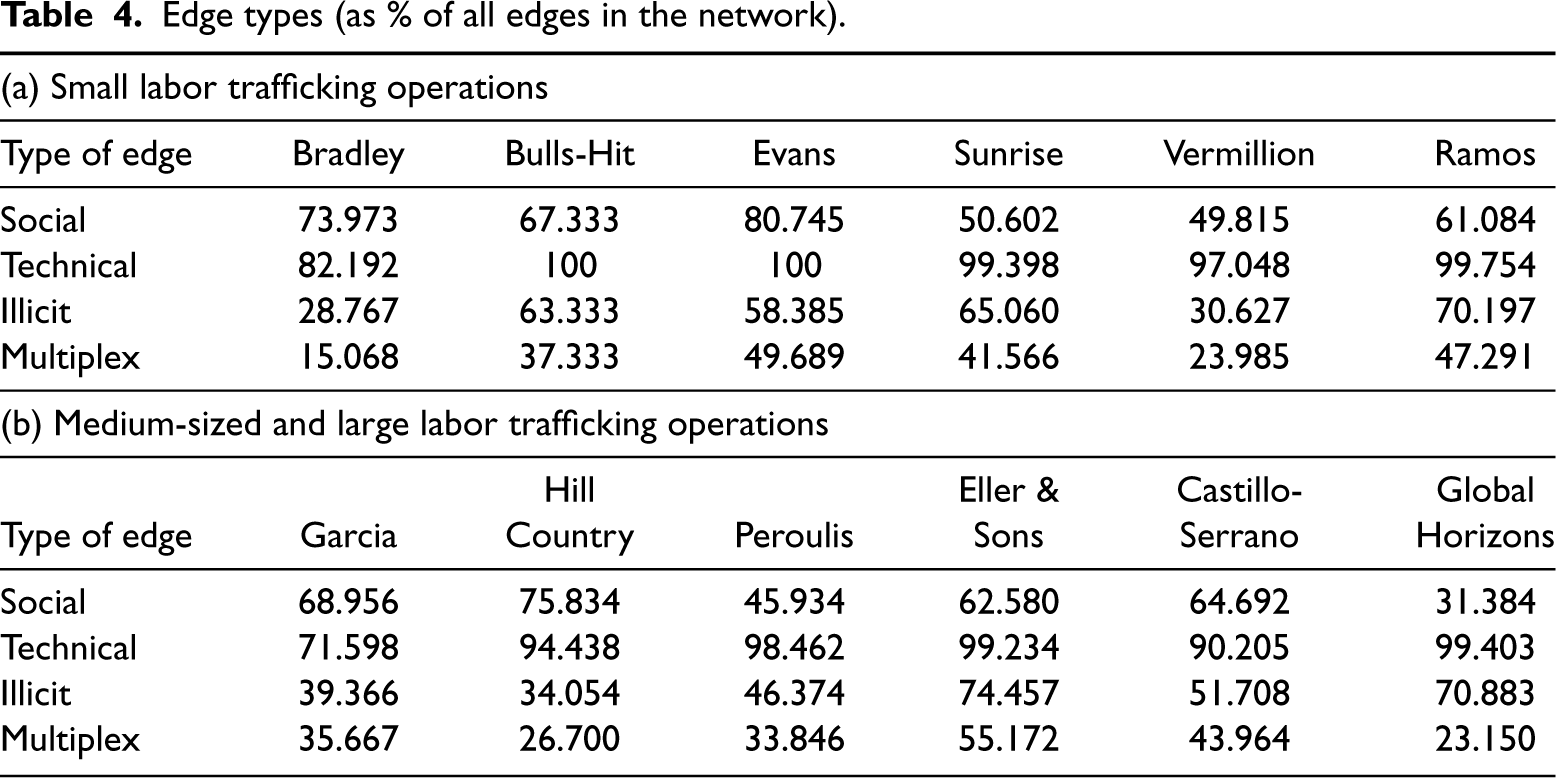
Edge types (as % of all edges in the network).
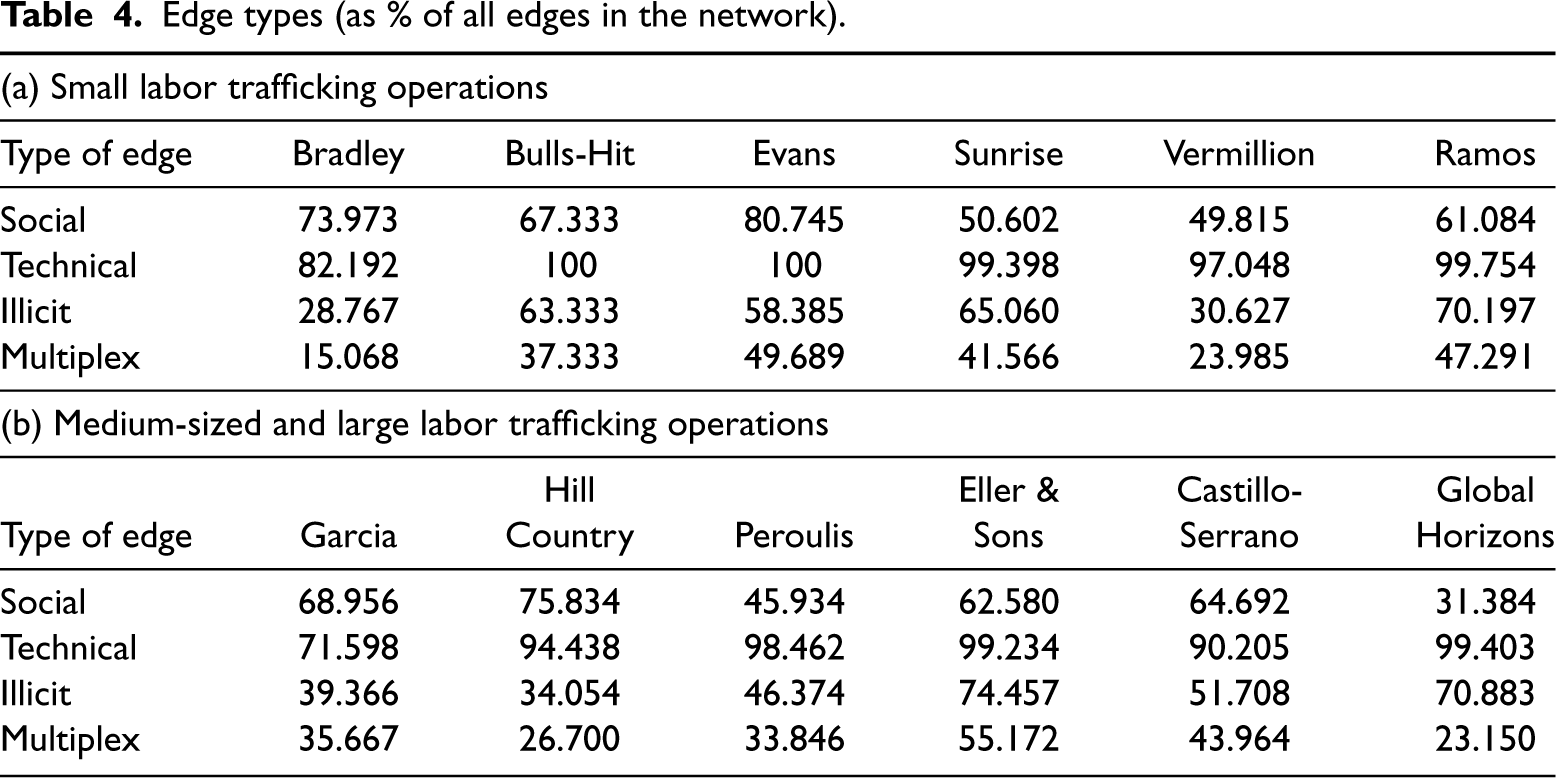
The STS practices of agricultural labor trafficking networks are predominantly technical in nature.
The technical nature of the labor trafficking networks often had to do with the day-to-day operations of the network. For example, within the Eller & Sons case, a third-party company was hired to aid with obtaining the visas for the workers, and relationships were maintained with corporate paper companies that required labor being brought in by Eller & Sons. The exceptions are two cases that had relatively fewer—though still predominately—technical ties. This concerned a small labor trafficking operation (Bradley) involving the exploitation of five Jamaican workers by a couple owning a tree removal company (82.19% of coaffiliations were technical in nature) and a medium-sized labor trafficking operation (Garcia) involving the exploitation of hundreds of Mexican immigrants on a family owned business (71.60% of the coaffiliations were technical in nature). However, substantive variation existed across cases regarding the proportion of social ties requiring human-to-human interactions (between 31.38% and 80.75%) and the proportion of illicit ties that existed for the mere or partial purpose of illicit behaviors (between 28.77% and 74.46%) such as internal recruiters purposefully connecting with a financial institution to deposit victims’ funds. Generally, fewer connections, between 15.07% and 55.17%, were considered multiplex ties, as they connected any two actors through a combination of social, technical, and illicit means. These multiplex ties capture the more enduring relationships that might be more challenging to disrupt because of a combination of practices that underpin them.
In Table 4, we summarize how often each type of tie was identified in our analysis of the labor trafficking networks. We identified 14 common practices that across all cases could facilitate social, technical, and illicit ties, see E-companions H, I, J, and K in the Supplemental Material, for details, definitions, examples, and cross-tabulations, respectively. Exploitative behaviors featured in all 12 labor trafficking operations, especially in the Global Horizons case wherein 50% of all ties were exploitative. Other relatively common STS practices across the labor trafficking operations involved ties that facilitated the recruitment or housing and transportation and ties that represented interactions with a broader community, with inspections and law enforcement, or between victims, in addition to ties that activated business processes such as operations and reporting and payment mechanisms. 6
Based on the 12 cases assessed, it is unclear whether the variation in the relative presence of social, illicit, and multiplex ties existed due to, or irrespective of, structural network characteristics such as the size, density, transitivity, or centralization of labor trafficking operations. However, it is nonetheless important to note that the Global Horizon case continues to stand out as a large labor trafficking operation with fewer social ties (31.38%) compared to all other cases. Furthermore, the majority of ties in that case were illicit (70.88%) and existed for the explicit purpose of exploitation. This raises the need for future work to test whether fewer social but more illicit ties correspond with other network features seen in the Global Horizon case (e.g., low transitivity).
To examine how external corporate supply chain actors were connected to the labor trafficking operation (our third research question), we observed that—across all 12 labor trafficking operations—a total of 209 corporate supply chain actors other than the farms where the exploitation occurred or other internal companies owned by the defendants were connected through 1,203 unique coaffiliations to the labor trafficking operations, which accounted for about a fifth of the total number of connections. On average, a case involved 17 corporate supply chain actors (SD = 10.17; range: 4–35), which accounted for an average of 100 connections (SD = 85.00; range: 24–309). The percentage of external corporate actors (see Table 2) ranged between 7.576% (in the Ramos case) and 33.846% (in the Vermillion case). Table 5 shows the relative distribution of edge types through which corporate supply chain actors were connected to other actors in the labor trafficking operation. Overall, all corporate business entities across the 12 cases were involved through technical means, except for one small-sized labor trafficking operation (Bulls-Hit) with 72.82% of the ties being technical, leading to our next proposition:
Corporate entities are primarily involved in labor trafficking operations through technical means.
Edge types with corporate supply chain actors (as % of all edges with corporate supply chain actors).
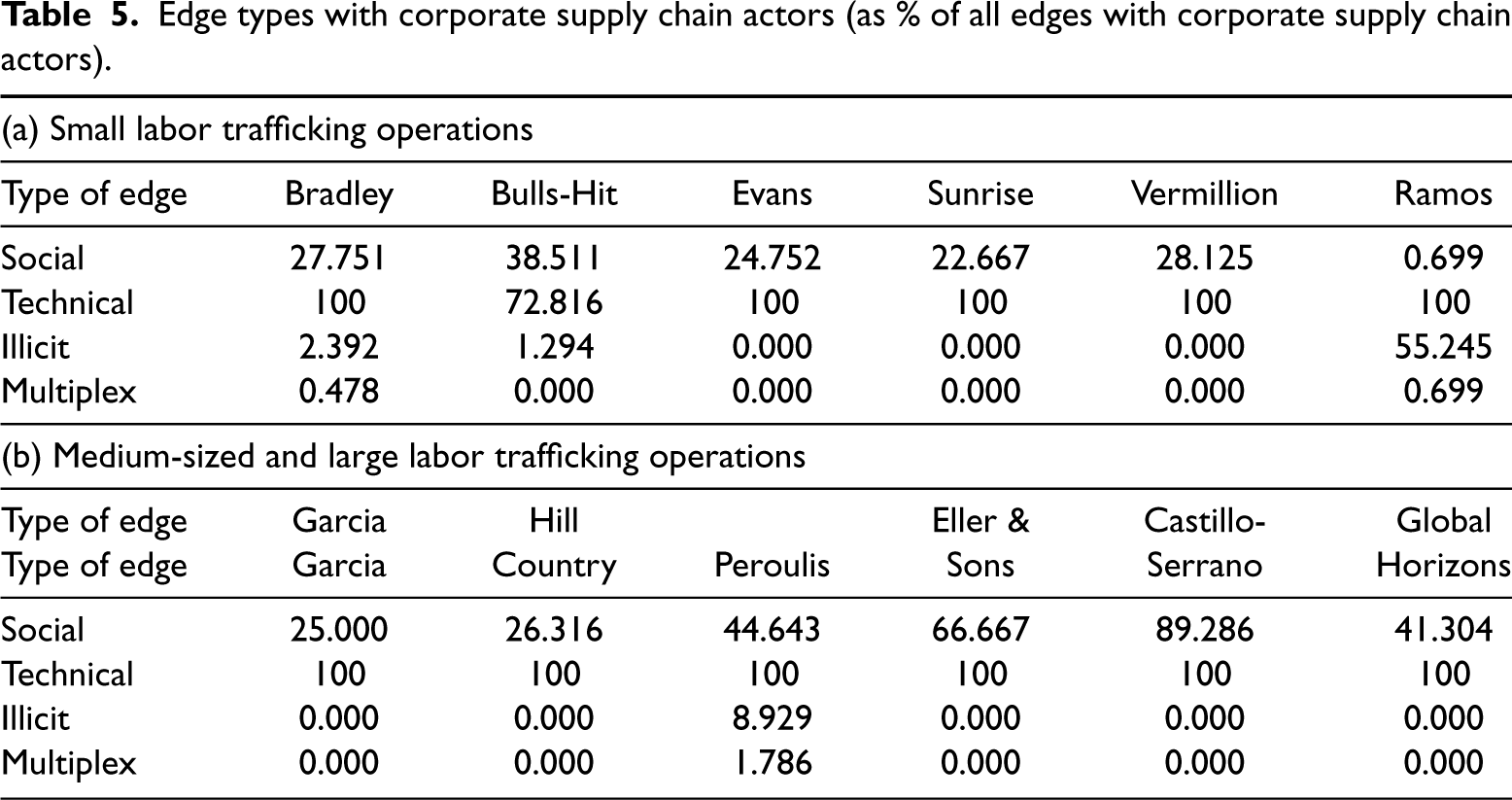
Compared to other actors, corporate entities are less frequently involved through social or illicit ties.
Compared to other actors (see also Table 4), corporate supply chain actors were overall less frequently involved through social ties: A negative correlation was observed between the fraction of social ties and the actor being a corporate supply chain actor (
To further examine the level of involvement of corporate supply chain actors relative to other actors, we evaluated each actor’s degree centrality against its betweenness centrality across all labor trafficking operations. An actor’s degree and betweenness centralities can indicate their importance to the labor trafficking operation overall. By extension, it may help inform intervention strategies more likely to be disruptive when they target actors connected to many others (i.e., have high-degree centrality) or operate as a “bridge” between actors (i.e., have high-betweenness centrality).
Figure 2 presents the scatter plots of degree centrality by betweenness centrality for all 12 labor trafficking operations and by type of actor (corporate supply chain vs. other actors). The dotted lines indicate the cutoff for low (i.e., below the mean) and high (i.e., above the mean) degree and betweenness centralities, which divided actors into four possible groups: (a) low-degree-centrality/low-betweenness-centrality; (b) low-degree-centrality/high-betweenness-centrality; (c) high-degree-centrality/low-betweenness-centrality; and (d) high-degree-centrality/high-betweenness-centrality (see, for a similar approach, Morselli, 2010). Overall, the degree and betweenness centralities of actors were significantly and strongly correlated (
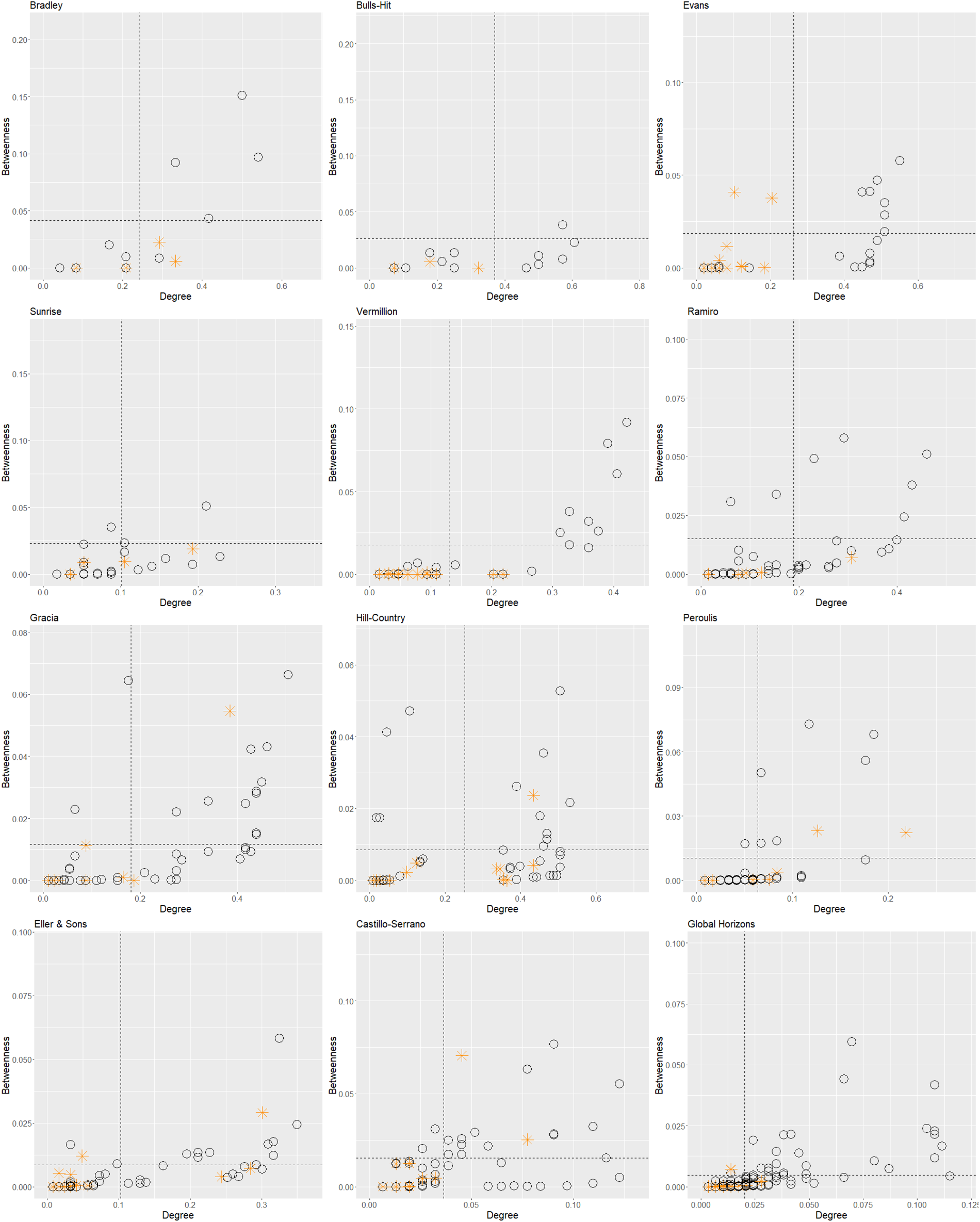
Scatterplots of degree and betweenness centralities for actors in the labor trafficking operations.Notes. Normalized degree and betweenness centralities are shown. * = corporate supply chain actor; O = other. Dotted lines indicate the cutoff point (the means) of degree and betweenness centralities. Outliers (i.e., actors with centralities two
Taking all 12 cases together, most corporate supply chain actors fall in the low-degree and/or low-betweenness groups and seem to have lower degree and betweenness centralities than other actors, which was corroborated by significant, albeit small, negative correlations between the type of actor (business or not) and degree centrality (
Most corporate supply chain actors have lower degree and betweenness centralities than other actors.
For example, within the Global Horizons case, the network partnered with companies (e.g., Thai recruiter AACO) to recruit impoverished individuals under the false pretense of a living wage. A few exceptions of corporate supply chain actors in the high-degree and/or high-betweenness group can be observed from Figure 2. To illustrate, qualitative case information revealed that some corporate actors in these central positions included representatives of the company that assisted with the visa applications and the accommodation where the workers stayed during exploitation. Because businesses with high-degree and high-betweenness centralities were central to the labor trafficking operation, targeting these types of businesses would likely result in greater disruptions compared to targeting businesses with lower centrality scores. Corporate supply chain actors with relatively higher degree and/or higher betweenness centralities were observed in some medium-sized and large labor trafficking operations (see e.g., the Eller & Sons and Global Horizons cases in Figure 2). Few corporate actors in small operations had high-degree or betweenness centralities.
This work is, to the authors’ best knowledge, the first development of a set of socio-technic practices for labor trafficking operations. Through a cross-case analysis of 12 labor trafficking networks in the U.S. agricultural sector, we examined the network structures, the types of ties that make up the networks (social, technical, and/or illicit), and the role of corporate supply chains in labor trafficking networks. While prior studies have begun to examine the social networks of human trafficking operations, few studies cover the breadth of nonillicit network connections we consider.
In summary, our analyses put forward a set of three main results. First, with regard to the network structure of the labor trafficking operations, we identified substantive variety between the cases, indicating the importance of assessing the empirical network structures of each case separately. Nonetheless, a few similarities between the majority of labor trafficking cases stand out. In particular, we observed density to be the highest in the exploitation stages compared to previous stages, suggesting that the collaboration between actors was more present—or at least more visible—in the final stage of the labor trafficking operation (Proposition 1). Furthermore, transitivity appeared to be an important binding mechanism across nearly all cases (Proposition 2), which may be linked to trust and familiarity between actors as important drivers of collaboration in illicit/exploitative operations. Moreover, the labor trafficking operations appeared to be strongly concentrated on a single actor or a few actors (Proposition 3), especially the prosecuted defendants, their companies, managers, or field supervisors (although to some extent this might be explained by the investigative focus of law enforcement, see below). Lastly, the observed labor trafficking operations had substantive core–periphery structures in which a few actors were collaborating with each other and might have had the largest influence/role in the exploitation of migrant workers (Proposition 4). Most other actors collaborated with one another in the periphery of the network. Such network distributions are likely resilient against random attacks. Such findings can act as a stepping stone for future Operations Management and Supply Chain (OSCM) models to build on based on actual organizational and operational dynamics, for example, whether interventions that may be catastrophic are those that target a specific phase, a type of network actor, or the “core” of labor trafficking operations.
By providing commonalities in baseline structural network statistics across 12 different labor trafficking operations, we seek to encourage future work to test whether labor trafficking operations significantly differ from regular supply chain operations in terms of their structural network characteristics. Furthermore, notwithstanding the commonalities between many of the labor trafficking operations assessed, future work is needed to identify and test explanatory factors for the substantive differences in network structures between the labor trafficking operations. To illustrate, we observed lower transitivity levels for larger labor trafficking operations with higher centralization levels, compared to smaller labor trafficking operations with lower centralization levels. Future work based on more cases is needed to further examine the relation between transitivity and centralization in the context of labor trafficking operations to explain which types of labor trafficking operations may be driven by transitivity versus centralization (or both) and what the implications for effective interventions are. Ultimately, the type of network structure can determine how resilient or adaptive a network is, which may be useful information for modeling and intervention strategies.
Second, the analyses elucidate the types of ties (technical, social, and/or illicit) that comprise the networks. Knowing which ties are the main binding mechanisms in labor trafficking operations can help inform which ties may be exposed and disrupted. Motivated by the prior literature on STS practices in the business domain (e.g., Bostrom and Heinen, 1977a; Trist et al., 2013; Hadid and Afshin Mansouri, 2014), we observed and analyzed 14 common STS practices between any two actors. This expands OM STS theory (Hyer et al., 1999; Shah and Ward, 2007) to include the socio-technic practices of trafficking networks—including the practices of corporate actors—overcomes prior hurdles to connect companies to trafficking (Gold et al., 2015), and adds further depth to the systemic issues that lead to exploitation (LeBaron, 2021) that can now be studied in other contexts.
Overall, our analyses indicate that technical ties were the most prevalent types of ties that held nearly all studied networks together (Proposition 5). Theste types of ties involved regular supply chain connections between actors and businesses that stem from technical procedures such as operations and reporting, payment mechanisms, and housing and transportation. The labor trafficking operations differed regarding their fractions of social ties, requiring human-to-human interaction, and illicit ties that involve actors purposefully contributing to or benefiting from the labor trafficking operation. Although all labor trafficking operations were in some way embedded in broader systems of technical, illicit, and social connections through actors taking part in larger socio-economic structures (see also Uzzi, 1996; Baker and Faulkner, 2009; Papachristos and Smith, 2014), future work comparing more labor trafficking cases is needed to identify what explains the observed variation in the fractions of social and illicit ties.
Third, our analyses document connections to corporate actors in all three phases of the labor trafficking operation. Knowing how corporate supply chain actors were involved in labor trafficking operations may help inform intervention strategies. We observed that corporate supply chain actors were typically involved through technical ties (Proposition 6a), indicating that labor trafficking may indeed be an integral part of legitimate corporate mechanisms in the 12 studied cases (Crane et al., 2019; De Vries, 2019). Though corporate supply chain actors had fewer social and illicit connections compared to other actors (Proposition 6b), the existence of technical ties where participants have knowledge and materially benefit from exploitation is sufficient for criminal liability under the Trafficking Victims Protection Act (TVPA).
Additionally, we observed that most corporate supply chain actors had lower degree and betweenness centralities than other actors (Proposition 7), which means that they had relatively few connections with other actors and did not have a strong information or gatekeeping position (i.e., they did not operate as a ‘bridge’ between other actors, see Morselli, 2010). These actors operated in the periphery of the network, had potentially less knowledge about the illicit practices within the supply chain, and were more passively involved in exploitative processes within the supply chain (see also De Vries, 2019). However, these companies are still important actors in trafficking prevention, yet tend to receive little attention in investigations, and are almost entirely missing from OM models. Previous literature suggests that awareness-raising efforts might be key among these businesses (see De Vries, 2019). In contrast, a few corporate supply chain actors had high-degree and/or high-betweenness centralities, and, therefore, arguably a more central role in the operation.
Together, these findings add to the extant literature on how corporate supply chains function and develop socio-economic connections to the labor trafficking operations, extending the findings of Chen and Paulraj (2004) on structure of long-term relationship building, Villena and Gioia (2018) on lower-tier risk, and the case for the socio-economic embeddedness of labor trafficking offered by De Vries (2019) to describe the role of the private sector through network ties between labor trafficking defendants and corporate supply chains. Furthermore, as Behdani (2012) outlined how a complex system such as a supply network can be seen from the STS lens, we now move the literature forward to apply those same concepts to labor trafficking operations and their interconnectedness with corporate supply chain actors. With our exposition of specific socio-technic practices, our findings can help ground corporate recommendations on how systems actually interact, such as those by Gold et al. (2015) who describe the challenges of connecting corporations to labor trafficking due to its hidden nature. Through our novel use of prosecuted case data, we shine a light on those connections and the socio-technic practices that facilitate them.
Insights for Corporate Supply Chains
The findings from this study inform those working in corporate supply chain labor, procurement, sourcing, and risk through our exposition of connections between legitimate businesses and labor trafficking networks. Our findings support the work of Crane et al. (2019) regarding the outsourcing of work that subjects corporations to forced labor risk in their business relationships and LeBaron et al. (2017) who acutely target thin margins in corporate contracts that make it difficult to pay fair wages. We confirmed that corporate connections (e.g., contracts) to labor trafficking existed across all 12 cases through technical systems.
Importantly, our findings also provide opportunities for the potential identification of forced labor based on the direct connections that existed between corporate entities and victims of trafficking. This helps answer calls from supply chain research (Crane, 2013; Konrad et al., 2017) to help with identification, recovery, and reintegration of survivors connected to business operations. Finally, we note that companies with corporate supply chain connections to labor trafficking networks may face liability under domestic and international laws. In the U.S., the TVPA outlines responsibility against those engaged in trafficking in persons, including corporations. This is a marked difference from merely two decades ago when such laws were not in place and such connections would have been, at most, a public relations concern. Recent international laws and penalties coupled with monitoring by civil society organizations raise the incentive for corporate monitoring of their interconnected supply chain partners (Benstead et al., 2021). Thus, as we provide direct evidence of the interconnectedness between companies and labor trafficking networks across all operation types, we highlight an ongoing risk for supply chain managers in an intensifying legal landscape.
Policy Insights for Government
This study can also help inform key policy implications for the U.S. government’s involvement (and OM models thereof) in preventing and intervening in labor trafficking operations. In particular, the structure of the labor trafficking networks draws attention to a set of core actors, including several corporate supply chain entities, who were connected to the labor trafficking operations across all three of the labor trafficking phases. This finding points to the need for governments to target their public awareness campaigns (a common feature of federal and state antitrafficking responses) to inform both the general public and industry leaders about the multiple connections industries can have to labor trafficking actors, even when actors in these industries did not have knowledge of, or necessarily benefit from, the trafficking scheme.
Insights for Law Enforcement
The findings of this study also inform law enforcement efforts to identify and respond to labor trafficking networks. Law enforcement was often alerted about victimization through victim reports to service providers or calls for service from others who suspect exploitation and abuse. Identifying illicit socio-technic ties in earlier stages of the trafficking operations necessitates information relative to payment mechanisms, housing, corporate contracts, and transportation. Such work requires specialized skills and technical expertise that are less common among investigators. Through increased partnerships with financial risk and security professionals who may have access to banking records and practices identifying risky transactions, law enforcement could enhance identification and disruption of actors in labor trafficking networks.
Conclusion and Limitations
To conclude, our findings call for the need to approach labor trafficking as an understudied, complex system comprised of multiple connections between a variety of actors, each of which may have a responsibility and/or liability to mitigate exploitative practices connected to corporate supply chains. Through our cross-case analysis of 12 labor trafficking networks, we offer a more holistic view of how multiple stakeholders (e.g., corporations, governments, and civil society) are connected to trafficking operations. Furthermore, by integrating the STS lens with an instrumental approach to networks, we examined coaffiliations and coordination across varying labor trafficking operations. A few network-driven observations lend themselves for further validation and comparison across other labor trafficking operations, especially to further examine both the generalizability and peculiarities of the trafficking operations under scrutiny.
Our results point to future OM research and policy adjustments, specifically to consider a broader set of actors and intervention mechanisms when seeking to disrupt human trafficking by intervening in the social, technical, and illicit practices that the network’s relationships are based upon. As such, our work provides foundational insights for the OM community regarding the structure, composition, and features of labor trafficking networks connected to corporate supply chain actors. In doing so, we answer the call to help OM models reach their potential (Konrad et al., 2017) by contributing that corporate supply chain actors were present across all cases, had illicit components, and should be added to OM models. Our findings point to seven propositions to be tested across future work which may also be expanded to add company, government, and law enforcement links.
Despite this work’s important contributions to informing our understanding of labor trafficking STS practices and connections to corporate supply chains, our study has limitations that may inform future research. We analyze federally prosecuted labor trafficking cases with a variety of geographies, agricultural commodities, and sizes. These cases represent a small subset of all U.S. labor trafficking schemes. Furthermore, there is reason to believe that the facts and types of evidence that are available about labor trafficking networks could be different in cases that were never identified and/or prosecuted. Cases that come to the attention of the police may have more ties to traditional criminal operations or more disorder that would attract traditional police attention. For example, in some labor trafficking situations, the police have been called to the location of exploitation due to other suspected illegal activity, violence, or disturbances. However, in the majority of cases reviewed here, the police were only alerted to the labor trafficking victimization after a victim reached out for assistance or another bystander (e.g., neighbor, customer) followed up on a suspicion about victimization. There may also be bias in the cases that are federally prosecuted based on case complexity. Federal prosecution is usually reserved for cases that involve larger numbers of actors and include an interstate operation. Federal prosecution of individual actors or small operations is less likely. On the other hand, prosecutors pursue simple and straightforward cases of exploitation because it takes more time and resources to develop prosecutions involving more illicit actors and complex criminal networks. Understanding these potential sources of bias, this study utilizes a purposeful sampling approach to limit and ensure the representation of cases of various levels of size and complexity. It is not the aim of this research to provide a nationally representative picture of STS ties in labor trafficking, but rather to explore STS practices from a targeted sample of cases that represent a variety of case structures. Future research should investigate the supply chain structure and connections for a wider range of cases regardless of prosecution.
Second, while there are important reasons to focus on exploitation in agricultural work outlined earlier, the types of networks, relationships, and operations may differ significantly from other industries where labor trafficking has been identified, such as restaurants, construction, hospitality, and domestic work. Given the small number of cases assessed, additional research is needed in these industries to determine if the types of relationships and network connections identified here are found in different types of human trafficking schemes and operations. As such, our cross-case analyses of 12 labor trafficking operations provide a platform upon which to build OM models of social and technical relationships that can exist in human trafficking contexts, test assumptions about these relationships, and further assess opportunities for disruption across relationship types.
Third, we collected all available information about the trafficking schemes, but this data is based on publicly available records, including charging, sentencing, and media documents. These sources may only provide selective information about the labor trafficking operation needed to support the prosecution of criminal cases. This is relevant as our study identified less independent social ties, suggesting that ties in labor trafficking networks were both social and technical. It may, however, be the case that multiple social ties that did not have any technical connections such as family members, friends, and other acquaintances exist but were not recorded in legal documents because they were less germane to the prosecution, yet can be considered by future research.
Despite these limitations, this study informs our understanding of the interactions of labor trafficking networks with both internal and external (e.g., corporate and government) actors from a socio-technic lens. Namely, labor trafficking operations, such as those studied here, rely on a broad ecosystem of illicit and licit actors that enable this type of exploitation to thrive in global supply chains. This study can provide baseline knowledge about labor trafficking operations to facilitate further research and discussion on the structure, practices, and operations of such networks that inform operations modeling, corporate due diligence, government policy, and the variety of multiactor interventions that can identify and stop labor trafficking from occurring.
Supplemental Material
sj-pdf-1-pao-10.1177_10591478231224917 - Supplemental material for The Ties That Link Us: Uncovering the Socio-Technic Connections of Labor Trafficking Networks
Supplemental material, sj-pdf-1-pao-10.1177_10591478231224917 for The Ties That Link Us: Uncovering the Socio-Technic Connections of Labor Trafficking Networks by Shawn Bhimani, Ieke de Vries, Aubrey Sneesby, Amy Farrell and Kayse Lee Maass in Production and Operations Management
Footnotes
Acknowledgments
We are grateful for the editorial team, reviewers, and our research students, including Chase Childress, Arezoo Jafari, Sage Shumate, Ciara Tenney, Emma Toole, and Alexis Yohros.
Declaration of Conflicting Interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The authors disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This material is based upon work supported by the National Science Foundation under Grant No. 1935618.
Notes
How to cite this article
Bhimani S (2024) The Ties That Link Us: Uncovering the Socio-Technic Connections of Labor Trafficking Networks. Production and Operations Management 34(5): 1038–1056.
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
