Abstract
Trust problems hamper many social and economic exchanges. In such situations, there are often institutions that enable trustors to share information on the performance of trustees. While the benefits of such institutions have been researched extensively, little is known about their emergence. This article presents a game-theoretic model for the understanding of investments by trustees in establishing information sharing between trustors. The model allows for a simultaneous analysis of investments in and effects of institutions for information sharing. It captures two mechanisms by which a trustee’s investment can promote trust. First, a trustee’s investment in establishing information sharing can enable network effects that facilitate trust and trustworthiness. Second, it can promote trust by serving as a signal of intrinsic trustworthiness. The analysis of the model implies predictions for how characteristics of the interaction situation affect whether these mechanisms motivate a trustee to establish information sharing.
Introduction
Exchange often requires that one party—the “trustor”—exposes herself to the risk of abuse by the other party—the “trustee” (Coleman, 1990; Dasgupta, 1988; Kreps, 1990). Buying a used car is a well-known example. The buyer (trustor) does not know the history of the car and the seller (trustee) may benefit from concealing important information. If the buyer places trust and buys, she risks paying too much. Trust problems are also salient in online trade: the buyer typically has to pay upfront without having any real guarantee that the seller will ever ship the product. Such trust problems pose a social dilemma. Both parties would benefit from fair exchange, but the exchange may not take place because the trustor has reason to mistrust the trustee (Akerlof, 1970; Coleman, 1990; Kollock, 1998). Fortunately, institutions that enable trustors to share information about trustees—as, for example, word-of-mouth networks or online reputation systems—allow actors to escape the dilemma (Buskens and Raub, 2002, 2013; Cook et al., 2009; Feinberg et al., 2014; Milinski, 2016; Resnick et al., 2000).
While it is well understood how institutions for information sharing facilitate exchange, little is known about the emergence of such institutions. There is a general theoretical idea that if certain institutions or networks have value for actors to achieve their goals, actors should be likely to set up such institutions or networks (Flap, 2004; Lin, 2002: Chap. 8; Prendergast, 1999). It also suggests itself that many institutions for information sharing have been set up purposively to facilitate exchange. In line with this idea, Guseva and Rona-Tas (2001) suggest that trust problems in credit markets led to the installment of credit bureaus in the United States and that these trust problems led Russian bankers to form extended word-of-mouth networks (see Klein, 1997 for related case studies). Still, there is a lack of theoretical models for the understanding of investments in establishing institutions for information sharing as a means to facilitate trust and trustworthiness. This article addresses this gap in the literature. It investigates theoretically under what circumstances it is likely that a trustee makes a costly investment to enable information sharing between trustors. By treating institutions for information sharing as endogenous, this article furthermore brings to attention effects of such institutions that have previously been overlooked. The article thus contributes to the understanding of the emergence and effects of institutions for information sharing.
The game-theoretic model presented in this article captures two mechanisms by which a trustee’s investment in establishing information sharing can promote exchange. First, there are the well-known network effects. Information sharing facilitates exchange by enabling trustors to learn about trustees from the experiences of other trustors. In addition, it gives trustees incentives to act honestly because developing a bad reputation could inhibit many future exchanges or require a trustee to lower his price. 1 These network effects are well-established theoretically as well as empirically (Abraham et al., 2016; Bohnet et al., 2005; Bohnet and Huck, 2004; Bolton et al., 2004; Buskens et al., 2010; Buskens and Raub, 2002, 2013; Cook and Hardin, 2001; DiMaggio and Louch, 1998; Feinberg et al., 2014; Frey and Van de Rijt, 2016; Hillmann and Aven, 2011; Huck et al., 2010; Przepiorka, 2013; Snijders and Weesie, 2009; Sosis, 2005). In the current study, I model how these network effects can motivate a trustee to set up an institution for information sharing between trustors.
Second, the model shows that a trustee’s investment in establishing information sharing can promote trust by serving as a signal of intrinsic trustworthiness. Some people are intrinsically trustworthy and behave well also in the absence of contextual factors that deter trust abuse. 2 But how could a trustee convince a trustor that he is intrinsically trustworthy given that also those with bad intentions want to be trusted? Signaling theory (e.g. Bliege Bird and Smith, 2005; Gambetta, 2009; Przepiorka and Berger, 2017; Spence, 1973; Zahavi, 1975) maintains that taking some costly, observable action can allow an actor to credibly communicate unobservable characteristics, such as intrinsic trustworthiness (Bacharach and Gambetta, 2001; Barclay, 2004; Bliege Bird and Power, 2015; Gambetta and Przepiorka, 2014; Paik and Woodley, 2012; Przepiorka and Berger, 2017; Przepiorka and Diekmann, 2013; Raub, 2004). This article shows that a trustee’s investment in establishing information sharing can serve as such a signal of intrinsic trustworthiness.
I model these network and signaling effects and how they can motivate a trustee to invest in establishing information sharing using the framework of finitely repeated Trust Games (TGs) with incomplete information (see, e.g. Buskens et al., 2017; James, 2002). The model focuses on a scenario in which several trustors interact with the same trustee. The trustors do not know whether the trustee is of the friendly type or of the opportunistic type. A trustee of the friendly type is intrinsically trustworthy and has no incentive to abuse trust. A trustee of the opportunistic type has an incentive to abuse trust, at least in the short run. At the beginning of the game, the trustee can make a costly investment to set up an institution for information sharing between the trustors. I identify under what conditions there exist (sequential) equilibria in which the trustee pledges this investment to allow the network effects or to signal that he is of the friendly type.
To my knowledge, Frey et al. (2015) and Raub et al. (2013) are the only studies that investigate how network effects can motivate actors to establish information sharing. The paper by Frey et al. (2015) is a companion paper to the current study. It investigates in a very similar game-theoretic model investments in information sharing by trustors rather than trustees. Raub et al. (2013) study a game-theoretic model that allows also investments by trustees, but their model assumes complete information about the incentives of trustees and indefinite repetition. A core result of Frey et al. (2015) and Raub et al. (2013) is that there is an inverse U-shape in the relation between the incentives to invest in establishing information sharing and the size of the trust problem. The incentives to invest are small for trust problems that are very small or very large, while the incentives to invest are large for trust problems of intermediate size. The results of this article regarding investments motivated by the network effects are in line with this prediction.
That a trustee’s investment in establishing information sharing can serve as a signal of intrinsic trustworthiness has not been studied previously. This innovation leads to new predictions on investments in information sharing as well as effects of information sharing. Furthermore, the article contributes to the broader literature on signaling trustworthiness (see Przepiorka and Berger, 2017 for a recent overview). I analyze the model for two types of friendly trustees: friendly trustees who would suffer from an internal sanction if abusing trust and friendly trustees who are trustworthy because they receive an internal reward if honoring trust. These scenarios subsume various motivations for intrinsic trustworthiness, such as inequity aversion, guilt aversion, altruism, or warm-glow. 3 We will see that the possibility to signal intrinsic trustworthiness depends crucially on what motivation leads to intrinsic trustworthiness and that results concerning signaling equilibria generalize beyond the specific context of investments in information sharing.
The game
This section describes the game
Actors, moves, and information
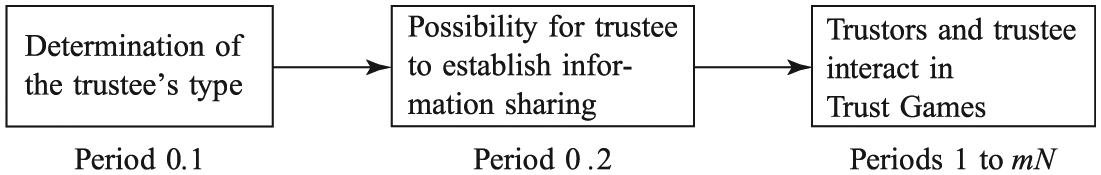
Timeline of
More specifically, in period 0.1, a random move of a pseudo-actor Nature determines the type of the trustee. With probability
In period 0.2, the trustee decides whether to invest the cost c to establish an institution for information sharing between the m trustors.
Finally, one binary TG is played in each of the periods 1 to mN. In every TG, the trustor at play, first, decides whether to place trust. If the trustor does not place trust, the TG ends. If the trustor places trust, the trustee chooses whether to honor or abuse trust and the TG ends.
The order in which the trustors play their TGs is random but each of the m trustors plays precisely N TGs with the trustee. The analysis does not require that the order of interaction is known in advance. It suffices to assume perfect recall (i.e. that players never forget information they once acquired), so that actors remember information on outcomes in specific periods and who played in which period.
If the trustee established information sharing in period 0.2, all trustors are always informed about the choices that were made in all past TGs. Information is shared truthfully among the m trustors directly after every TG. By contrast, if the trustee did not establish information sharing, each trustor knows only the outcomes of her own past TGs. I will refer to the continuation of
Payoffs
The payoffs in any TG are as follows. If the trustor i who is at play does not place trust, trustor i and the trustee earn the payoffs
In
In
An actor’s total payoff for
Analysis of the game
The aim of the analysis is to identify under what conditions there exist equilibria in which the trustee invests in establishing information sharing. A rational trustee will weigh the cost of investment c against the expected “return on investment,” namely, his expected payoff in
Throughout, I focus on sequential equilibria—a refinement of Nash equilibrium for games with incomplete information (Kreps and Wilson, 1982b; see Rasmusen, 1994: Chap. 6, for a textbook). For the analysis of investments in information sharing, I additionally employ the passive conjectures refinement (Rasmusen, 1994; Rubinstein, 1985), which will be explained below. I will often refer to sequential equilibria and sequential equilibria involving the passive conjecture for brevity as “equilibria.”
Behavior and payoffs in the TGs
We can lend from earlier work for the analysis of
If there is no information sharing
We will need some further notation. Let
Behavior and payoffs in
If there is no information sharing, what happens in the TGs between one trustor and the trustee is independent of what happens in the other trustors’ TGs. In
Then, in the next TG of trustor i, the trustee—if he is of the opportunistic type—starts to randomize. Still one TG later, trustor i begins to randomize too, placing trust with probability TEMP. In this second phase, the “randomization phase,” trustor i and the trustee (if he is of the opportunistic type) randomize until i does not place trust or until the trustee abuses
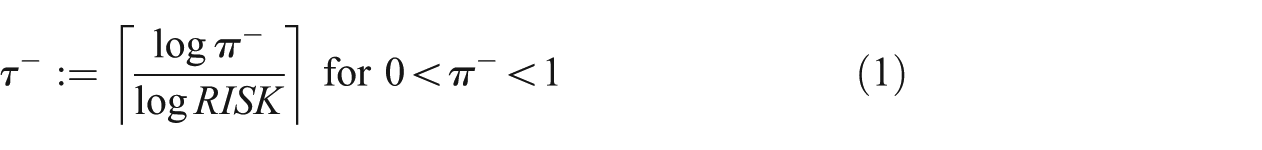
The equilibrium does not always evolve over all these phases. If the trust problem is very severe, there may be no trust at all. As equation (1) shows,
The equilibrium also does not exhibit a randomization phase if
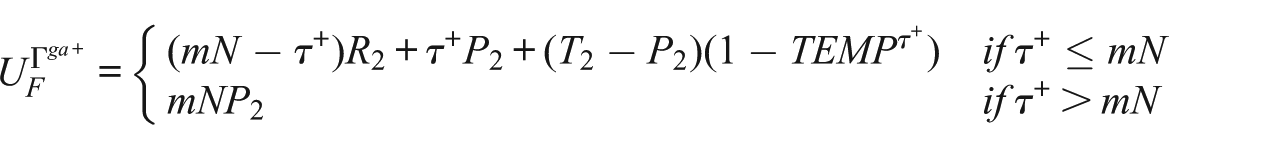
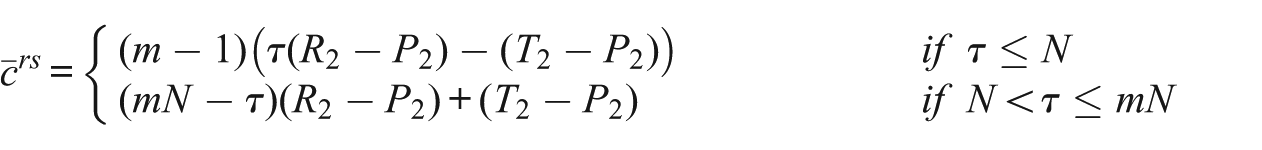
We can now specify the expected payoffs of friendly and opportunistic trustees in
Proposition 1
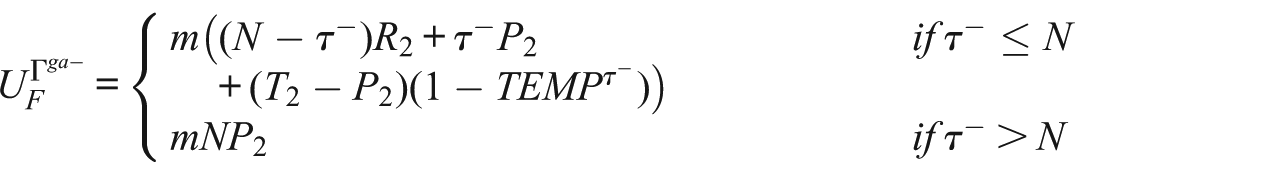
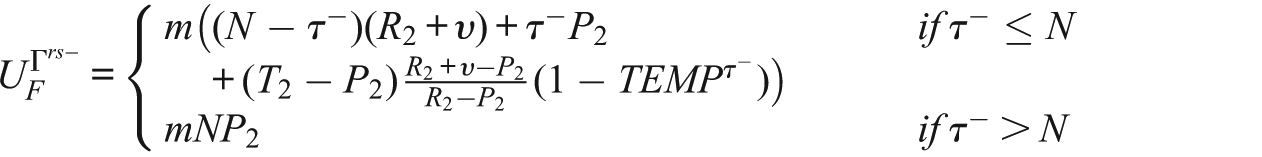
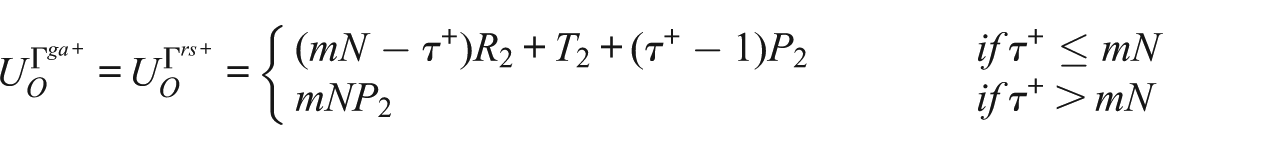
The expected payoffs of a friendly trustee in
The expected payoffs of an opportunistic trustee in
The proofs of all propositions are in Appendix 1. For the scenario that
Behavior and payoffs in
In
Specifically, in
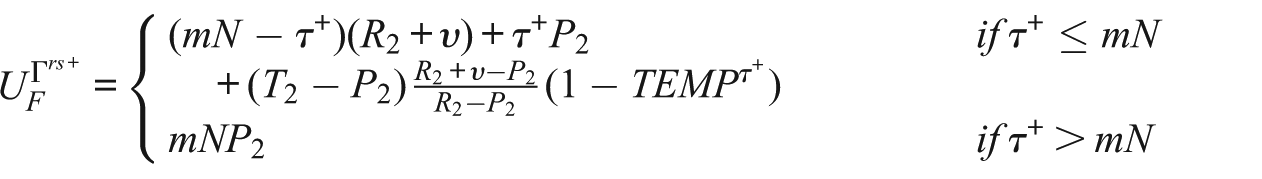
Proposition 2
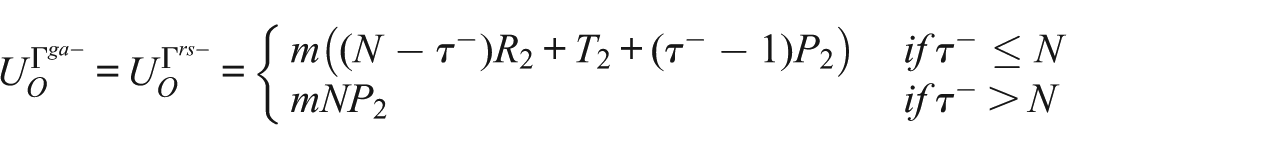
The expected payoffs of a friendly trustee in
The expected payoffs of an opportunistic trustee in
The comparison of equilibrium behavior and expected payoffs in
Investments in establishing information sharing
In this section, I establish under what conditions there exist equilibria in which the trustee establishes information sharing between the trustors. Let
For the analysis of investments in information sharing, it is important to realize that a trustee’s expected payoffs for
In the following, I establish under what conditions it is part of an equilibrium that both trustees establish information sharing (
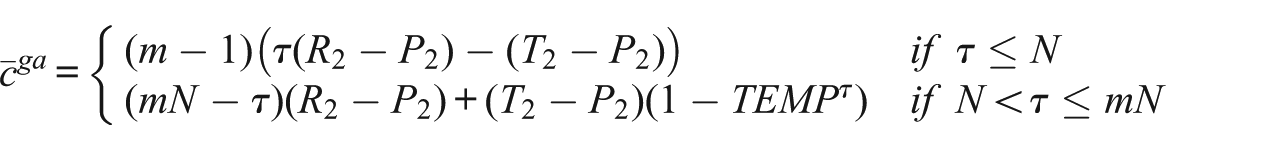
Investments in information sharing to allow network effects
In equilibria in which the trustee invests in establishing information sharing regardless of his type
Proposition 3
Proposition 3 shows that
If
The next proposition establishes how parameter changes affect
Proposition 4
The maximum cost
(1) •If
• If
(2) •If
• If
• If
• If
• If
(3) •If
• If
List (1) of Proposition 4 concerns the effects of changes in
To understand this inverse U-shape in more detail, recall that if
List (2) of Proposition 4 concerns the TG payoffs of the trustee.
List (3) of Proposition 4 shows that
An increase in N also leads to an increase in
Summarizing, the condition for the existence of pooling equilibria in which the trustee establishes information sharing to benefit from network effects is almost the same in
Investments in information sharing as signals of intrinsic trustworthiness
In equilibria in which only the friendly trustee invests in establishing information sharing (
Proposition 5
In
An equilibrium in which
A remark is in order.
Proposition 6
In
In
Summarizing, a trustee’s investment in establishing information sharing can signal that he is of the friendly type if friendly trustees are trustworthy because they derive pleasure from good behavior (as in
Conclusion and discussion
In this article, a game-theoretic model has been developed that advances our understanding of the emergence and effects of institutions for information sharing in trust situations. The model allows for a simultaneous investigation of investments in setting up an institution for information sharing and the effects of such an institution. It focuses on investments in information sharing by a trustee, and it captures two mechanisms by which a trustee’s investment can promote trust. First, the trustee’s investment can allow network effects that facilitate trust and trustworthiness. Second, the trustee’s investment can serve as a credible signal of intrinsic trustworthiness.
A core result is the prediction that there is an inverse U-shape in the relation between the size of the trust problem and the incentives for establishing information sharing in order to allow network effects. A trustee should be particularly likely to establish information sharing to enable network effects if the size of the trust problem is intermediate (if there is an intermediate probability
This inverse U-shape prediction is in line with the results of Frey et al. (2015) and Raub et al. (2013). Frey et al. (2015) report qualitatively the same effects of changes in
A second key result of this study is that a trustee’s investment in information sharing can serve as a credible signal of intrinsic trustworthiness. The analysis suggests that a trustee is particularly likely to establish information sharing to signal his intrinsic trustworthiness if he derives a large internal reward from good behavior, if there are many trustors and many interactions with each trustor, and if the investment cost is high. The analysis, furthermore, shows that signaling can only occur if intrinsically trustworthy trustees derive a larger benefit from being trusted than trustees that have a short-term incentive to abuse trust.
The article also offers new predictions on the effects of institutions for information sharing. Earlier work focused exclusively on network effects. The result that a trustee’s investment in information sharing can serve as a signal of intrinsic trustworthiness suggests that information sharing can affect behavior more strongly than previous work predicts. Network effects tend to affect behavior gradually, as in my model in which they lead to honored trust in some more TGs. Signaling can have more swiping effects. In separating equilibria in which only the intrinsically trustworthy trustee invests, the trustors never place trust if the trustee does not invest while they place trust throughout if the trustee does invest. This suggests that information sharing can promote trust more strongly if it was established by the trustee than if it is given exogenously. Another implication is that a trustee’s investment in information sharing may have a particularly strong effect on trust if the costs of investment are high.
The results on the conditions for separating equilibria also generalize beyond the context of investments in information sharing. In a separating equilibrium, the trustee’s investment is a “wasteful signal.” After having observed the investment, the trustors know for sure that they are dealing with an intrinsically trustworthy trustee. There is no more need for the network effects. Therefore, the trustee could signal his type by “burning resources” in any other way than by creating a context that would promote trust if the trustors were uncertain about the trustee’s type. In this sense, the analysis establishes under what conditions a trustee who interacts N times with m trustors sends any costly signal to convey his intrinsic trustworthiness. The results on how parameters affect the restrictiveness of the conditions for the existence of such separating equilibria are in line with results of Przepiorka and Diekmann (2013) for infinitely repeated TGs.
Although a trustee could take various actions to signal his intrinsic trustworthiness, I believe that establishing information sharing is a particularly attractive option for three reasons. First, trustors have an interest in acquiring information about a trustee’s reputation. It is therefore, for example, unlikely that it escapes the attention of potential buyers that an online seller invested in a reputation system. At least, it is probably more likely that they overlook a note that reports a charitable donation (see Fehrler and Przepiorka, 2013, 2016; Milinski et al., 2002 for studies on charitable giving as a signaling device). That is, an investment in establishing information sharing might be a signal with high “broadcast efficiency” (Bliege Bird and Smith, 2005; Gintis et al., 2001). Second, there may be a chance that trustors do not understand a trustee’s action as a signal of intrinsic trustworthiness. If the signal fails to convey its intended message, the trustee can still benefit from network effects if he tried to signal his type by establishing information sharing. Finally, trustors might not be totally convinced of the trustee’s intrinsic trustworthiness also after having observed the signal (for example, due to heterogeneity in the cost of sending the signal that can make it possible for an opportunistic trustee to afford sending the signal). Network effects can then further increase the level of trust after signaling. These considerations highlight the importance of studying how signaling can drive investments in information sharing. However, these considerations also suggest that it may be a limitation that in the presented model an investment in information sharing facilitates exchange either because it enables network effects or because it signals intrinsic trustworthiness. Future work could modify the presented model to investigate how signaling and network effects can complement one another.
Footnotes
Appendix 1
This appendix provides a lemma that specifies the equilibria of
Acknowledgements
The author thanks Vincent Buskens and Werner Raub for comments and suggestions at various stages of the research process and Jacob Dijkstra and Victor Stoica for comments on an earlier version of the manuscript.
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the Netherlands Organization for Scientific Research (NWO, Graduate Program Grant 2008/2009 for the ICS).