Abstract
A library worker’s sense of who they are at work is the result of a dynamic and complex construction. These work identities serve several functions, including the cultivation of a sense of belonging, self-esteem, meaning, and competence. While a significant amount of research has considered the role of other human actors in the construction of work identity, including its impact on salient identity functions, less research has considered the role of nonhuman actors. One nonhuman actor likely to play a pivotal role is workplace technology. In this study, 52 public library workers with identities they considered to be underrepresented, minoritized, and/or stigmatized recorded a series of audio diaries and participated in interviews about the frustrations they experienced during the workday. Findings reveal the ways in which library technology is perceived by these workers as a source of identity threats that devalue an identity, change the meanings they associate with an identity, or prevent them from enacting an identity. These threats introduced obstacles to a worker’s competence-based, worth-based, and authenticity-based self-esteem. Workers responded to these threats by redefining, reasserting, or reassessing the threatened identity. This study contributes to growing research on professional identity in librarianship by considering the role of nonhuman actors, like technology. Findings have implications for both current and future implementations of technology within libraries.
Keywords
Introduction
Technology has long played an integral role in the library profession. Whereas librarians in the 17th and 18th centuries were fully capable of mediating access to small collections, the substantial growth in collection sizes necessitated technological solutions that enabled access beyond what human librarians could facilitate on their own (Buckland, 2017). The Internet brought about significant changes in information transfer, transforming the roles and functions of library workers who were asked to embrace new ideas around service (Abbas, 1997). The collaborative and interactive technologies of “Web 2.0” represented a paradigm shift for libraries, and the emerging “Library 2.0” was more user-centered, socially rich, communally innovative, and provided a multi-media experience (Maness, 2006). Artificial Intelligence (AI) has played a role in the profession since the 1990s (Subaveerapandiyan, 2023), showing up in expert systems that responded to user questions (Waters, 1986) and routine inquiries (Payne and Bradbury, 2002); systems that enabled the browsing of software libraries (Ostertag et al., 1992); digital libraries that used natural language processing to automate metadata production (Hauptmann et al., 1997); and other essential library functions like collection development, subject indexing, and reference services (Lancaster and Smith, 1990). AI continues to play an important role in library work, showing up in common library technologies, including self-check-out systems, online public access catalogs, and library analysis software (Yoon et al., 2022). More recent advances in AI promise to revolutionize how libraries of the future operate and the services they provide (Hodonu-Wusu, 2025).
While these technologies have mostly supported library work, they have also been perceived as threats. Lancaster (1992) noted the concerns of many in the early 1990s, for instance, that the profession lacked the leadership needed to turn the threats of automation and AI into opportunities. Raitt responded to a question in 1994 about whether librarians would still be around in 2024—himself asking, “Are librarians so insecure about the profession and future?” (p. 275). Internet search called into question workers’ identities as “masters of search” (Nelson and Irwin, 2014: 904). The potential for recent advances in AI to reshape library services and roles has been perceived by some as a threat (Chhetri, 2023), with some worrying that they will lose their jobs (Cox et al., 2019). One remarkable feature of these concerns about technology’s impact on work is their consistency over time. In the 1990s, for instance, researchers (Mirvis et al., 1991) outlined considerations for the implementation of technology in the workforce—noting that over two-thirds of the workforce was using computers in their jobs and 25% of small components assembly was automated. In a world where 92% of jobs require digital skills (NSC, 2023) and activities that account for up to 30% of work hours across all industries will be automated by 2030 (Ellingrud et al., 2023), the workplace of the 1990s seems like ancient history. Yet, the recommendations provided by Mirvis et al. (1991) are surprisingly relevant to the workplace of today. They caution, for instance, that new technologies are not fully developed, that many expect more than the technologies can deliver, that many organizations lack a coherent implementation strategy, that workers may not be willing to accept changes to work processes; and that technology will increase social isolation, remote monitoring of work, and loss of operator control. The techno-stress that impacted workers in the 1980s (Brod, 1982) continues to impact workers today. This includes a worker’s sense that technology is pressuring them to work faster and longer (techno-overload); that their skills are inadequate to make use of technology (techno-complexity); that job pressures are present even when they are not at work (techno-invasion); that they may lose their job to technology (techno-insecurity); and that constant changes in technology result in a high degree of uncertainty (techno-uncertainty; Tarafdar et al., 2007).
One outcome of a worker’s interactions with technology that has been understudied is the impact of these interactions on a worker’s identity (Selenko et al., 2022). While a considerable amount of research has considered the role of human actors and institutions in a library worker’s identity construction (Campbell-Meier and Hussey, 2019; Freeburg and Klein, 2025a; Klein and Lenart, 2020; Pierson et al., 2019) and how these workers respond to identity threats sourced from human actors (Freeburg and Klein, 2025b), considerably less research has considered the role of nonhuman actors—like technology. As workers interact more with technology at work, it becomes difficult or impossible for them to maintain processes, values, and/or self-beliefs that make up their professional identities (Mirbabaie et al., 2022). The current study analyzed audio diaries from 52 public library workers, revealing insights into the identity threats posed by technology. Given that many of the issues impacting the implementation of technology have remained consistent over time, the study then considers the implications of these findings for a future library workplace that is likely to be heavily influenced by the presence of emerging AI technologies. The current study considers the following research questions:
In what ways do interactions with technology threaten a public library worker’s identity, increasing the demands on this identity or decreasing the resources available for their response? (RQ1)
What strategies do workers employ, and what resources do they utilize, in their response to identity threat demands? (RQ2)
What conditional factors moderate the impact of a technological interaction on worker identity? (RQ3)
Literature review
Work identity and threats
A person’s identity is an organized representation of their theories, attitudes, and beliefs about themselves—one that shifts over time (McCormick and Pressley, 1997: 210). This representation concerns who a person is as a member of a social group, as someone occupying a specific role, or as a unique individual (Stets and Burke, 2005). Work identities—the meanings people attach to themselves as they participate in the activities of work (Dutton et al., 2010)—are a significant part of a person’s overall sense of self. Who a person is at work represents the “focal point of their larger self-system” (Caza and Creary, 2016: 262) and “one of the primary means by which adults find their identity and form their character” (Gini, 1998: 708). Over time, occupational and professional identity has become increasingly important for workers—particularly as their affiliations with specific organizations have become less important (Anteby et al., 2016). This is true for library workers, whose identities are strongly tied to the library profession. As shown by Campbell-Meier and Hussey (2019), who applied Anteby et al.’s (2016) work to information professions, these identities can be seen through the lenses of becoming, doing, and relating (Anteby et al., 2016). Becoming includes an information worker’s socialization into the profession and shows that professional identity is influenced by formal education and on-the-job learning. Doing suggests that a worker’s behaviors also serve as a basis for professional identity, for example, connecting people with information. Library workers also derive components of their professional identity from their relationship with library users. Pierson et al. (2019) outlined similar factors in the development of professional identities in librarianship, including education, training, early socialization into the profession, professional status, professional culture, critical workplace incidents, and experience. Klein and Lenart (2020) highlighted the impact of library users on shaping the identities of library workers, noting that workers interacting with different user populations will develop somewhat different identities.
Given the centrality of work identity to a person’s overall self-construct, a considerable amount of research has considered the extent to which these identities are positive. Selenko et al. (2022) suggested that workers view work events in terms of their implications for salient identity functions, for example, the cultivation of a sense of belonging, self-esteem, meaning, competence, and social validation. Group-based identities, for instance, can be associated with power and prestige that leads to positive feelings about the self (Craig et al., 2019). Verification of role identities is associated with feelings of competence and skill (Stets and Burke, 2005). Person identities can give workers “a sense of continuity, integration, identification, and differentiation” (Hewitt, 1989: 179). Work events that represent opportunities to fulfill identity functions can result in identity enhancements as workers restructure, expand, or adapt their identity to take advantage of the opportunity. Work events that introduce barriers to the fulfillment of an identity function, however, represent identity threats that can devalue a worker’s sense of self, requiring them to engage in strategies to resolve the discrepancies to maintain a positive identity (Dutton et al., 2010; Stets and Burke, 2005). An identity threat is a recurring situation that a person appraises as holding the potential for (a) devaluing their identity, for example reducing the prestige they feel from membership in a group; (b) changing the meanings they associate with an identity, for example changing how work is done in ways that change what it means to be occupy a certain role; or (c) preventing them from enacting an identity in ways that verify who they believe themselves to be (Petriglieri, 2011).
One way to conceptualize the impact of identity threats is to consider their implications for job demands and the resources workers have access to as they respond to those demands. The Job Demands-Resources Model (J D-R) from Demerouti et al. (2001) suggests that job demands and resources impact worker motivation, well-being and performance. Thus, they should be considered when designing work—including designing the technological infrastructure of work. Demands are the things about work that exact physiological and/or psychological cost, for example, workload, physical job demands, emotional demands, and job insecurity. Resources are the things that help workers meet those demands and achieve their goals, for example, autonomy, task variety, feedback, task significance, role clarity, task complexity, opportunities to engage in problem-solving, and social support. When demands exceed resources, worker motivation, well-being, and/or performance is decreased. Viewed through the lens of J D-R, the devaluing, changed meanings, and prevented enacting of an identity threat represents an increase in demands. The extent to which a worker can respond in ways that eliminate or reduce the threat is dependent on the availability of resources.
The resources available to workers include a set of response strategies, which are categorized according to the target of the response (Petriglieri, 2011). Identity protection responses target the source of the threat and include derogation of the source in an attempt to reduce threat severity, concealing an identity in order to decrease the likelihood that a source will threaten it, and presenting positive information about a threatened identity as a means of changing other people’s perceptions of it. Identity-restructuring responses target the identity that is under threat and include changing the importance of the identity to reduce the severity of the threat, changing the meanings associated with the threatened identity to sidestep the threat, and abandoning the identity or leaving the roles associated with it. A worker’s ability to eliminate or reduce the severity and/or likelihood of an identity threat demand, then, is dependent on their access to resources that help them enact successful responses.
Workers from underrepresented or minoritized groups face additional job demands through the threats of whiteness, which “operationalize[s] the hegemonic social system that privileges [white identities] as the normative power and authority” (Irvin et al., 2024). The architecture of a library, for instance, can suggest to workers of color that they do not belong and that their culture is not valued (Brook et al., 2015). The stigmatization of disability can suggest to library workers that, to fit, they need to be able to pass as able-bodied (Pionke, 2019). Library workers with invisible disabilities or mental health challenges face repeated discrimination and stigmatization (Burns and Green, 2019; Cook and Clement, 2019). The very EDI initiatives that seek to advance the professional development of library workers also suggests that, to advance in the profession, they must suppress their authentic selves (Mehra and Gray, 2020). As the profession cycles through periods of acknowledging the presence of these additional demands—suggesting each time that their discovery is new and paradigm-shifting (Cooke and Kitzie, 2021)—these workers face the added demand of re-explaining their concerns and being asked to “speak for all the people of my racial group” (Berry, 2004). These workers need additional resources, then, in their efforts to navigate whiteness while maintaining an authentic sense of self (Irvin et al., 2024).
Technology and worker identity
An extensive amount of research has considered the role of other human actors in a worker’s identity construction. Freeburg and Klein (2025a), for instance, noted the role of patrons, colleagues, and management in regulating the identities of public library workers. Less research, however, has considered the role of nonhuman actors, for example, technology, space, artifacts. This is unfortunate given the role these nonhuman actors play. According to Actor-Network Theory (ANT), workers are part of a networked world that also includes nonhuman actors, with both sets of actors having the agency necessary to “make a difference in the course of some other agent’s action” (Latour, 2005: 71). The agency of nonhuman actors can be seen as they modify the associations between actors, bring about moral and political associations, and provide the conditions necessary for human society (Sayes, 2014). Nonhuman actors can request, demand, allow, encourage, discourage, or refuse a course of action (Davis and Chouinard, 2016). They can also play a significant role in a person’s identity construction. People perform expected identities through their clothing and accessories (White and Beaudry, 2009), reflect and structure social identity through personal adornment (Thomas and Thomas, 2005), and negotiate the self through religious objects (Loren and Beaudry, 2006).
Technological actors play a particularly significant role in a worker’s identity construction—often in ways that are identity-enhancing. Stein et al. (2013) found that workers referred to technological artifacts as landmarks, or identity referents, useful in the construction and enactment of their preferred selves. These workers constructed identities as creators of technology who maintained control, mediators who helped turn technology into something useful, gatekeepers who knew best how others should interact with technology, users of technology who improved the workplace through their use, and teachers who showed others how to use technology. Korica and Molloy (2010) considered technology as a reference point for the shifting professional identities of surgeons. Academic librarians used emerging search technologies as a reference point for definitions of themselves as leaders and “super searchers” (Hicks, 2014). Here, technology acts as a resource that supports a worker’s response to identity demands.
However, technological actors can also represent sources of identity threats, that is, demands. Craig et al. (2019) adapted Petriglieri (2011) to consider three threats posed by technology to a worker’s identities. First, workers derive a significant portion of their self-esteem from their successful completion of tasks, that is, competency-based self-esteem. This is highlighted in the doing lens on library professional identity (Campbell-Meier and Hussey, 2019). As workers struggle to adjust to technology’s redefinition of their role and the tasks they work on, they may be deprived of opportunities that verify their belief that they are good at what they do and fully embody their role. Workers who feel that their current skillsets are inadequate given the constant change in workplace technology are subject to feelings of techno-uncertainty, which can lead to role ambiguity and role stress (Tarafdar et al., 2014). AI can cause workers to worry that their skills and expertise are no longer needed (Mirbabaie et al., 2022). Nelson and Irwin (2014) showed how Internet search threatened the identities library workers had constructed around claimed expertise in information organization and search.
Second, technology can threaten the worth-based self-esteem or prestige a worker sources from their membership in a group (Craig et al., 2019). The academic librarians in Boudreau et al.’s (2014) study felt that digitization led patrons to rely on them only for clerical tasks like fixing printer jams or providing directions the bathroom—which devalued the library as a profession. Here, work experiences conflicted with what workers expected based on their socialization into the profession, that is, becoming (Campbell-Meier and Hussey, 2019). Workers of color at Amazon facilities are concentrated into jobs that are heavily controlled and disciplined by technological surveillance, which suggests a devaluing and dehumanization of their racial identity (Alimahomed-Wilson and Reese, 2021). Threats like these that target a worker’s ascribed or involuntary group identities, rather than the identities they voluntarily choose to associate with, can be particularly problematic for workers: “Giving up a professional identity may be hard, but letting go of a gender or racial identity is even harder, if possible at all” (Petriglieri, 2011, pp. 643–644).
Third, technology can be perceived by workers as a threat to their person identities, potentially depriving them of authenticity-based self-esteem (Craig et al., 2019). For instance, the techno-invasion (Tarafdar et al., 2007) felt by workers as they sense the pressures of technology outside of work can threaten their identities around the separation of work and family, leading them to prioritize work in ways that feel inauthentic. Technology also works better for some people than others, devaluing a worker’s identity by presenting more affordances for other identities (Majchrzak and Markus, 2014). In a dysaffordance, a worker is forced to misidentify themselves in order to access a given technology’s features (Wittkower, 2016). An example is the categories Facebook offers for users to describe themselves that force users to misidentity themselves in order to use Facebook (Cirucci, 2017). For library workers, these threats may add to what is already a delicate task of balancing their personal beliefs and standards with those of the profession (Irvin, 2021).
The functions of work algorithms—including establishing performance targets and goals, managing performance by displaying ratings or providing automated feedback, scheduling workers, determining pay, and terminating employment (Parent-Rocheleau and Parker, 2022)—have the potential to intensify existing identity threats or create new threats in ways that exceed a worker’s resources. For instance, because algorithmic monitoring and performance assessments are based on quantifiable data that may not accurately reflect a person’s true output, workers may perceive a threat to their role identities around competency and success. Facing the threat of algorithmic termination, workers may find themselves engaging primarily in tasks that appease the algorithm but prevent them from enacting other parts of their professional identity.
Identity conditionality
ANT does not consider non-human actors as actors in and of themselves, that is, as coming in with certain a priori characteristics or definitions. Instead, ANT emphasizes the interactivity among actors and how this performance makes and unmakes the actors (Latour, 2005: 34). This suggests that technology should also be considered in the relating lens on library professional identity (Campbell-Meier and Hussey, 2019). Recognizing that these relationships occur against the backdrop of a broader work context, Selenko et al. (2022) noted the importance of identity conditionality and suggested that the extent to which a technology like AI will threaten or enhance worker identity is dependent on factors like workplace norms and hierarchical structures. This means that the extent to which a given interaction with technology represents an identity enhancement or threat—that is, a resource or a demand—is dependent on a number of factors, including support for worker training (Brunn et al., 2020), the existence of safe spaces that enable workers to restructure and enact new identities (Chen and Reay, 2021), relationships with other actors (Caza and Creary, 2016), and the pace of implementation (Selenko et al., 2022).
Methods
Design
The current study adopted a social constructivist framework, which posits that knowledge is constructed through interaction with others as people attempt to make collective sense and meaning out of their world (McKinley, 2015). Identity construction, then, is the “meaning-making about one’s self” (Hung, 2011: 161) that is embedded within social contexts, and workers often make use of small stories to construct identities as they interact with others (Bamberg and Georgakopoulou (2008). These are stories that lack traditional narrative elements and are told in informal everyday settings. Because audio diary methods are uniquely capable of eliciting and capturing these small stories (Monrouxe, 2009), they were adapted for use in the current study. Audio diaries also enable researchers to capture a worker’s identity construction in situ, as data collection occurs closer to a participant’s experience of an event than more retrospective methods like surveys (Bolger et al., 2003).
Sample and recruitment
After receiving IRB approval, researchers used purposive sampling to recruit public library workers from across the United States. This is a non-probability sampling method that enables researchers to better match the study sample to the study objectives (Campbell et al., 2020). Given research suggesting that identity threats are more pronounced for workers with non-normative identities (Boussebaa and Brown, 2017; Gago-Rodríguez et al., 2024) and that workers with these identities can face additional threats from workplace technology (Alimahomed-Wilson and Reese, 2021; Cirucci, 2017), the target population included public library workers with these identities. Participants first completed a demographic questionnaire, and participants were eligible if their identities included any one or more of the following: race other than white, non-binary gender, sexual orientation other than heterosexual, disability, or mental illness. Participants were also given the option of describing other parts of their identity that they considered to be underrepresented, stigmatized, and/or minoritized—which would also make them eligible to participate. Researchers identified library systems in different regions of the country, emailing them a flyer that included information about the study and a QR code to the questionnaire. Sampling occurred in several rounds, with recruitment materials targeting different subgroups of workers to diversify the final sample. A total of 52 public library workers participated (Table 1). The average age of participants was 37, with the youngest participant aged 26 and the oldest aged 65.
Participant demographics.
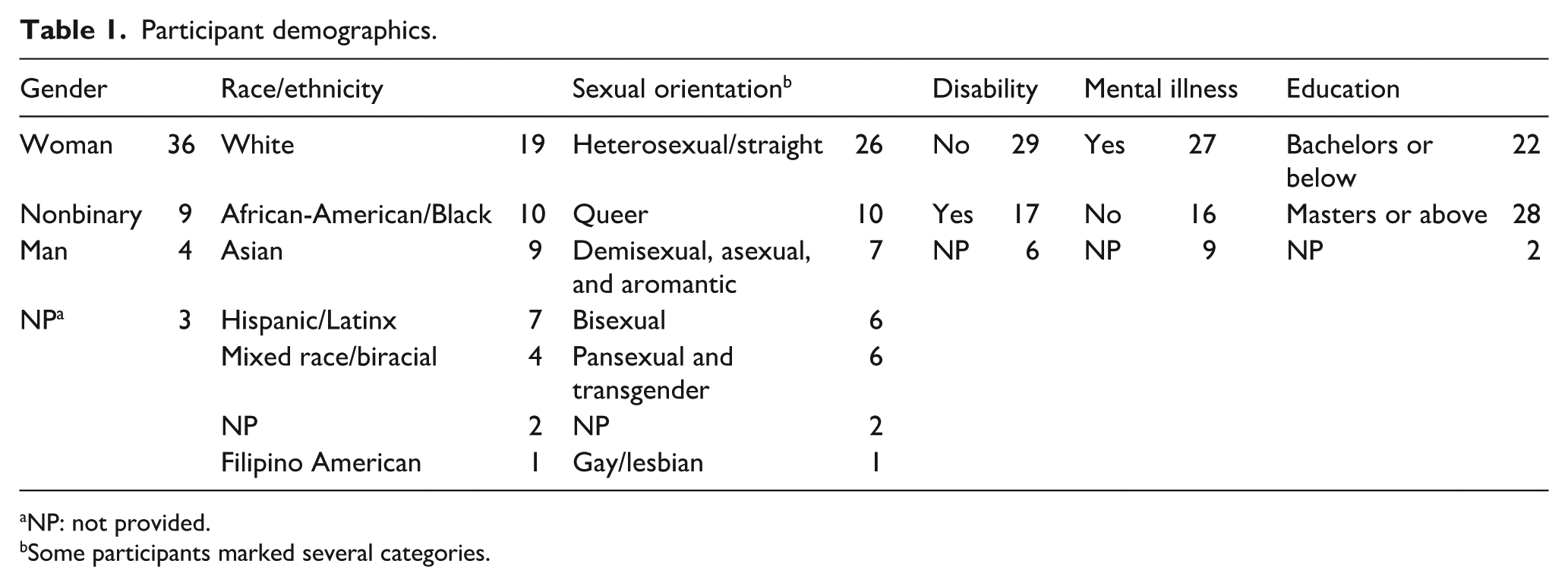
NP: not provided.
Some participants marked several categories.
Process
Participants first met with the research team, who provided an overview of the study and answered questions. Each participant was asked to keep track of times during work when they felt stuck, frustrated, or uncomfortable as they engaged in routine tasks—recording audio diaries about one of these experiences each day over five nonconsecutive days. Work routines were chosen as the focus because they have been shown to play an important role in a library worker’s construction of professional identity (Freeburg and Klein, 2024, 2025a, 2025b). Prompts were provided to give participants a place to start (Worth, 2009), but they were told they did not have to follow them as written. These prompts asked them to describe a specific experience at work that made them feel stuck, frustrated, annoyed, or uncomfortable. This included a description of the obstacle they faced, how they responded, the outcome of their response, and reflections on the experience. Dairies were uploaded by participants to a cloud folder, accessible only to the participants and researchers. Participants had control over their recordings, including what they talked about, when they recorded them, and which recorded diaries they submitted to the researchers. To increase participation and compliance, participants were sent regular emails reminding them to record their diaries (Pilbeam et al., 2016). Within 2 weeks after participants uploaded the final diary entry, they participated in a 45-minute interview.
Audio diary and interview transcripts were coded through the process of template analysis (King, 2012), a thematic coding approach that involves the creation of a list of hierarchically ordered codes that account for themes emerging from a detailed reading of transcripts. It is used often in organizational and diary-based research (Pilbeam et al., 2016). An initial template was developed collaboratively by the research team and then applied to the transcripts. Researchers met regularly to discuss coding, ensure consistent application of the template, and revise the template. Codes in the final template were grouped according to the types of identity threats outlined by Craig et al. (2019), for example, threats to worth-based, competency-based, and authenticity-based self-esteem. Within each category, codes included threat source, identity standpoint of the threat source, and worker responses to threats.
Only audio diaries coded as involving a technological identity threat were included in the analysis. Technology use included three types. The first type included communications technologies that participants used to connect with other human actors, for example, email, social media. The second type included technologies intended for patron use, for example, printers, fax machines, public access computers. The third type included technologies intended for the use of library workers and embedded into the processes that supported key library functions, for example, library management system, room reservation software, budgeting software. Some of these technologies incorporated AI components that supported the efforts of human workers (Selenko et al., 2022), for example, LMS, while other technologies incorporated limited or no AI components, for example, printers, scanners.
Results
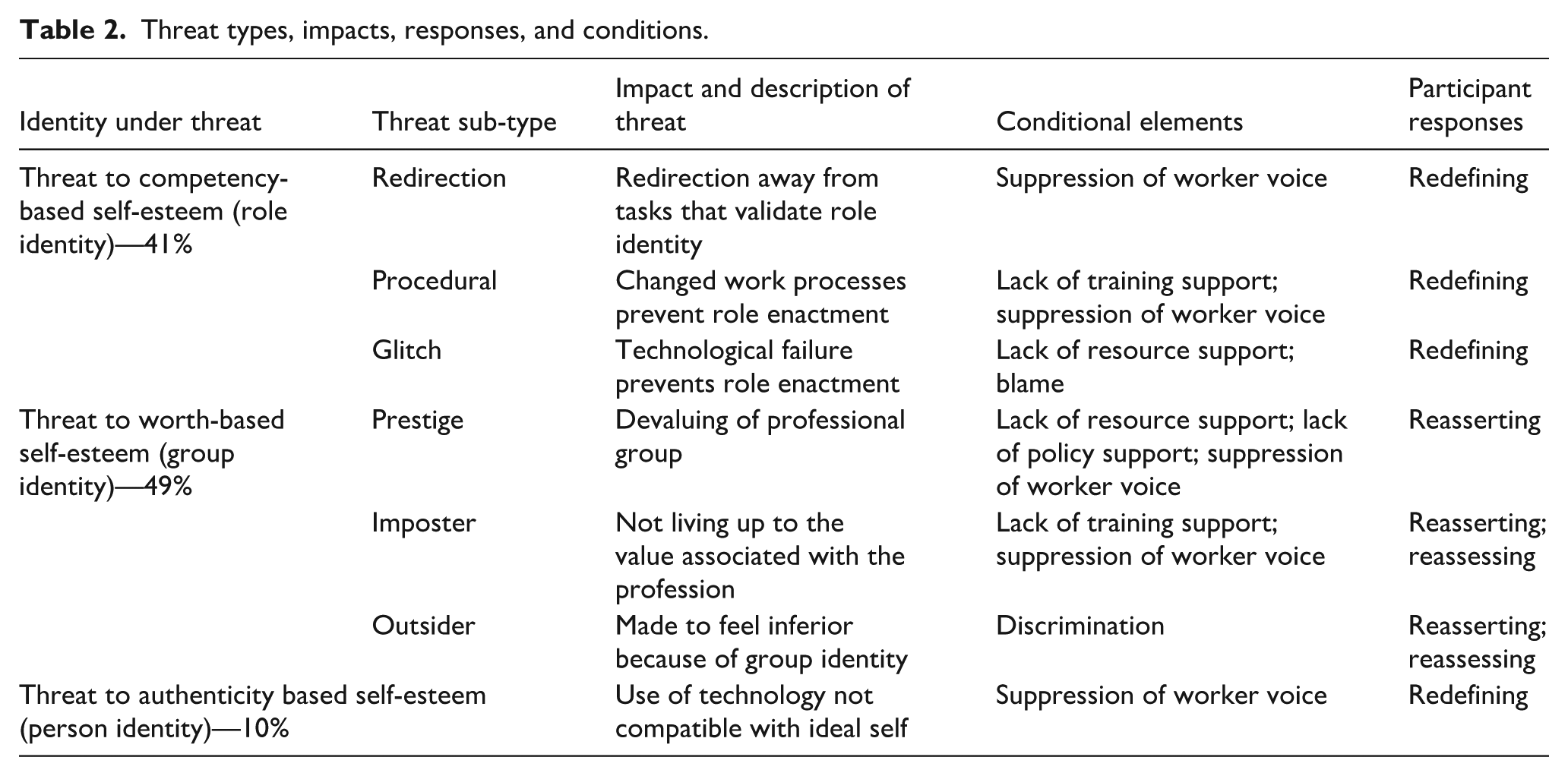
From the audio diaries, researchers coded instances when technology was perceived by a participant as representing an identity threat. This meant that a participant’s interactions with technology devalued their identity, changed the meanings they associated with an identity, or prevented them from enacting an identity. Threats were then grouped according to the specific identity function that was compromised, including competence-based self-esteem, worth-based self-esteem, and authenticity-based self-esteem. Each category was split into sub-types based on the specific nature of the threat. Participant responses to identity threats were analyzed according to Petriglieri’s (2011) framework, though not all Petriglieri’s response types were noted in the data. Finally, researchers noted any conditional elements beyond the technology itself that appeared to play a role in either the perception of a threat or a participant’s response to it. Table 2 summarizes the results. Percentages indicate the coverage of a particular threat code across all portions of the audio diaries coded as a technology identity threat.
Threat types, impacts, responses, and conditions.
Identity threats (RQ1)
Competency threats
In a competency threat (noted in 41% of threats), participants were prevented from enacting a part of their role identity in a way that made it difficult to maintain the meanings of competency and achievement they associated with that role.
In a Redirection Threat, participants were redirected from work that validated their sense of competency to work that did not. In one session of checking her email, Ava found herself applying for a summer reading committee, enrolling in an introductory language course, enrolling in a food training course, and jotting down ideas for a program—“It was lots and lots of stuff like that.” Yet, completing these tasks did not lead to feelings of accomplishment or productivity: “Today, I didn’t really achieve all that much.” By filling her day with tasks that did not validate her positive beliefs about herself, Ava was prevented from engaging in tasks that did.
In a Procedural Threat, the introduction of technology changed work processes in ways that prevented participants from enacting their role identities. Over her decades of public library experience, repetitive routine work—like checking out materials—became an easy and automatic indicator of Hannah’s skills. Yet, these routines quickly became an indicator of her deficiencies when her library implemented a new self-checkout system: “In all my years of service, I’m so used to things going a certain way and not having any issues . . . having all these years of experience, it makes you feel like, ‘Oh, okay, well you know what? You’ve been here long enough, you should be able to do that task.’” New software changed Carl’s process for completing budget reports, making him question his ability to complete a task that he had done successfully in a number of previous jobs: “There are just all these little strings of things that are frustrating and time consuming, and it makes me feel like I’m being gaslit by my company to do the job that I need to do. . . I’ve done purchasing for multiple different companies. I know how to do this.”
In a Glitch Threat, the failure of technology kept participants from enacting their role identities. Glitches in the software Tanner used to compile monthly circulation and programing statistics kept him from completing the work, making him feel like he was behind: “It’s just kind of a layer of frustration on top of a sort of a frustrating week where there’s other tasks I feel behind on. I feel like I’m running out of time before I leave.” Despite her best efforts, Aisha was unable to fulfill her role due to glitches in the LMS. This made her rethink who she was as a worker: “I guess today I kind of felt like a busy failure, to wrap it all up in one. Wow. A busy failure. Those are terms I never thought would go together.”
Worth threats
In a worth threat (noted in 49% of threats), some component of a participant’s group identity was devalued, threatening the meanings they associated with themselves as valuable members of important groups.
In a Prestige Threat, participants felt that the meanings associated with their group identities as librarians had changed in a way that lowered the prestige or standing of the profession. Alexis noted that patrons had redefined the profession as little more tech support for menial tasks like printing, faxing, and emailing: “The patron ended up, like, snapping their fingers to get my attention. That frustrated me a little bit just because there was this expectation that because [the patron] was older and doesn’t know her way around technology, that I would just do things for her.” Bailey described her library’s maker space as nothing more than a “a kiosk where you drop off an order and pick it up, versus enabling patrons to learn skills to which they can then build on and watch and help patrons really become self-sufficient in their own ways.” While the latter definition of librarianship was considered prestigious, the former was not. Amelia noted that parents would leave their children alone to play games on public access computers: “We’re not a babysitter. And even if your kids are well behaved, it’s still an imposition when you leave them there for seven, eight hours for somebody to watch over them the whole time.”
In an Imposter Threat, participants felt that they were not living up to the value they and others associated with the library profession. So, while the profession was still prestigious, they were poor examples of it. Mila struggled with the software for making room reservations, which made her feel like—compared to her colleagues—she was not a good librarian: “I’ve known how to do this since I started working, but for whatever reason I was just, like, ‘What do I do?’ Sometimes I feel like I come off as not knowing as much about my job as I feel like I do. So, I kind of defer to one of my coworkers. There are a lot of complicated emotions, I guess, with that.” Nora felt like an imposter because her library showcased information on a felt board rather than on a television screen like other libraries: “This is kind of, like, old technology, using these boards. I don’t see anyone or any other places that are using this type of information board. They are using televisions or computer screens.”
In an Outsider Threat, participants felt that others viewed them as inferior because of their group identity. This represented an othering that made them feel like they didn’t belong. When Amy worked in the makerspace, she noted the surprise in patrons when they found out that a Black woman knew things about technology: “They were like, ‘Wow, you do a lot.’ Like, compliments that sounded, not necessarily sarcastic, but just made me feel stupid—like she was impressed that I knew some very simple things.” Technology could also change work processes in ways that introduced outsider threats not present in prior versions of the process. The system Chloe used to book reservations and post information about events started requiring her to get approval from a manager before anything was posted, bringing her into contact with a person who did not value Asian women: “[The manager] drags her feet. Even if it’s 100% correct, she won’t do it . . . Can it be racial? Yes. She’s been racially motivated about a lot of different people, and it’s every color under the rainbow—just not Caucasian, because she is Caucasian herself.”
Authenticity threats
In an authenticity threat (noted in 10% of threats), participants felt that the technology they used was not compatible with their ideal self, leading to behaviors that were misaligned with their ideal self. The system for checking out materials forced Emma to put patrons on a payment plan if they had fines and restrict the number of materials they could check out: “I think the way that we, you know, restrict and treat people on payment plans just is not great.” So, while Emma’s ideal self was not someone who penalized patrons for late fees, the technology asked her to do just that. Maya noted the discomfort of Zoom meetings, which came with an expectation that she would turn her camera and microphone on: “I have developed a lot of anxiety from Zoom. Being in a Zoom meeting creates more anxiety for me than being in an in-person meeting. So, that is another thing that is an obstacle for me and my personality.” Authenticity was also threatened when participants felt that they could not react to things like glitches or changed processes in authentic ways. Frustrated with the scanner, Amy noted the restriction placed on her emotional response: “I think there’s a lot of pressure sometimes, like you have to just put on a happy face and stuff. And I think sometimes that’s really hard for me personally just to not show my feelings.”
Responses to identity threats (RQ2)
Faced with these identity threats, participants employed one of three response strategies.
Redefining
The most common response to both competency and authenticity threats was changed meaning. Here, participants attempted to redefine the threatened identity to eliminate or reduce the severity of the threat. Unable to help patrons due to computer glitches, Toni redefined her role in light of customer service expectations: “I would like to say I actually did meet people’s expectations, not in fixing the issue, but in being professional.” This suggests that participants defined their roles in multiple ways, shifting among these definitions as needed in response to threats. Asked to keep track of late colleagues, which he perceived as an authenticity threat, Carl shifted the meanings he associated with his ideal self by merging them with the concerns and interests of management: “We are trying to keep the library staffed and personed in a way that helps keep the library running.” Aisha tried to redefine her role identity when technology changed routine work processes: “For me it was more of a trying to wrap my head around that things are changing. . . That’s another thing that I have to retrain myself. But this is a change, and these are the changes that have been happening.”
Reasserting
The most common response to worth threats was to positively distinguish the threatened identity. Here, participants shared positive information about the identity under threat in an effort to convince others—or themselves—that the meanings they associated with that identity were still valuable. In response to prestige threats, Alexis restated the ideal meanings associated with her role identity in effort to mark those meanings as ideal: “I was, like, ‘I can show you how to do it.’ And [the patron] responded with, ‘Well, there’s no point in doing that because I’m not going to remember how to do it.’ And I was like, ‘I’m still gonna walk you through it.’” Amy’s reasserting response to being treated like an outside in the makerspace was more implicit: “I probably, unconsciously, was giving her more information to, in some way, prove that I, in fact, was capable of both answering her questions and working in the space that she first questioned me of working within.” Participants used the diary recordings themselves as a means of presenting positive information about their threatened identity, though only to themselves. Recalling an imposter threat, Aisha told herself: “You’ve done so many programs before. Some of them have been successful, some of them have failed, but you continue to try another day.”
Reassessing
Participants responded to some threats by decreasing the importance of the threatened identity to decrease the significance of the threat. Chloe responded to management’s threat to her identity as a respected and valued person of color by telling herself that the inability to retain that identity was not important enough for her to quit: “I am feeling still frustrated and annoyed every day, but I am able to tolerate it, because this job is important to me for monetary reasons, and I’m not quite ready to retire yet. I’ve got tons more to do in the library district. And so, I am gonna stick around.” Participants also re-engaged in the primary threat appraisal in an attempt to stop seeing an event as a threat. April told herself that being slow was not a threat to her value as a librarian, because patrons did not really care: “Looking back at it now, I know it’s not a huge deal for them to have to wait, like, five minutes for a library card. Generally, people will go browse around the books.”
Identity conditionality (RQ3)
The extent to which a given interaction with technology was perceived as a threat was the result of several factors beyond the technology itself.
Lack of support
Many of the threats experienced by participants were the result of a lack of support. This included a lack of training, as noted in Carl’s struggle with budgeting software: “Our finance team has a very minimal instruction booklet on how to use [the system] and how to do some of these situations—how to handle some of them.” A lack of support included forced reliance on outdated or insufficient technology. While glitches in the computers contributed to the threat to Ella’s sense of competency, she sourced this threat to management’s unwillingness to purchase new computers: “These are really old computers. They’re old Dell workstations from God—I remember even having those in college years ago. And they’re just not working.” A lack of support also included inconsistent implementation of policy. Amelia noted that part of the reason she felt like the profession had changed to little more than babysitting was a lack of support from management when she tried to enforce policies: “Last year, there was a lot of verbal warnings but no real consequences. I did not feel empowered by my two bosses, which is a theme for a larger issue, to actually enact those consequences. There was a real attitude I felt like, I was seen as way too punitive.” Finally, a lack of support could look like active blame. Sam noted that the IT department shifted responsibility for a glitch, calling it user error: “They kind of blamed it on me saying that it was because I kept knocking the cord or that I wasn’t leaving it plugged all the way, or I wasn’t putting the right settings in. And that made me really frustrated; I’m trying to think of a workaround and yet I feel like people are working against me.”
Suppression of worker voice
A participant’s perception that their voices were heard and that they could provide meaningful input influenced the extent to which an interaction with technology represented a threat. Faced with work that redirected her from enacting her definition of her role, Chloe noted: “I have brought that up several times, but my boss doesn’t want to give it up so quickly. She wants to continue having it done, even if it’s not effective.” Nora noted that a suppression of worker voice was evident in management’s hasty implementation of technology, as TVs were “installed too high on the wall to reach and to close to the wall to plug in storage devices.” As a result, the physical TVs became a constant reminder of what she perceived to be the farcical nature of her library compared to others: “Every day when I come to work, I have to walk past these unused television sets that cost the library district thousands of dollars. And it’s just two pieces of artwork up there on the walls as far as I’m concerned, because we’re not able to use them in the way that we’re supposed to be using them.”
Discrimination
Identity threats were also the result of explicit discriminatory thoughts and practices. There was nothing, for instance, in the makerspace itself that suggested Amy did not belong. Rather, these threats were the result of patrons bringing their discriminatory beliefs into the library. Yet, participants like Amy struggled to determine the exact nature of these beliefs and the specific components of their identity that were threatened: “Due to the complexity of the identities that I hold, I never know if the question is being asked because I am female presenting in a mostly male dominated library makerspace where most of the other employees there are men, or if it’s to do with being a person of color in that space.”
Discussion
Based on an analysis of audio diaries, the current study uncovered several identity threats that were present during a library worker’s interactions with technology. Results also show that workers actively responded to these threats, and several conditional factors influenced the extent to which a given technological interaction was perceived as a threat. These findings have several theoretical and practical implications.
Identity threats as techno-stress (RQ1)
Findings suggest several sub-types of technology identity threats, which increase the demand on worker identity without increasing their access to resources—representing distinct forms of techno-stress (Tarafdar et al., 2007). For instance, because procedural threats changed processes participants relied on as indicators of their competency, they represent a form of techno-overload. Redirection threats also represent techno-overload to the extent that workers feel that technology brings them more work than they can handle. Given that many of the imposter threats were present because participants did not fully understand technology or how to work around obstacles, they represent a form of techno-complexity. Authenticity threats can also be viewed as a form of techno-insecurity. However, rather than fearing the loss of a job, participants feared self-alienation. As these identity threats increase demands on workers and work stress, they have the potential to lead to worry, anxiety, negative self-views, decreased job satisfaction, emotional exhaustion, decreased productivity, and decreased worker well-being (La Torre et al., 2019). Given of the nature of the study sample, it is important to note that these demands are being added to workers who are already burdened with excess demands because of their non-normative identities (Cook and Clement, 2019; Mehra and Gray, 2020; Pionke, 2019).
Findings also suggest additional types of techno-stress. For instance, participants seemed less concerned with technology replacing them (techno-insecurity) than they were with technology not being good enough and making them look like incompetent librarians. This is in contrast with research that suggests technologies, like those used in search, lead library workers to worry that they are no longer needed (Nelson and Irwin, 2014). Thus, techno-obsolescence may represent an additional type of stress, which was noted in certain glitch and imposter threats and is tied into the conditional factors surrounding the provision of modern technological resources. Prestige threats suggest that the ways in which technology is used by patrons can introduce stress by devaluing a worker’s sense of professionalism. This is consistent with the sentiments of academic librarians in Boudreau’s study who worried that digitization devalued the profession by introducing significant clerical work. Thus, techno-minimization may represent another type of techno-stress. Here, workers worry, not about losing their jobs, but about the ways in which technology reduces the scope of their work. Finally, it is interesting to note that Tarafdar et al.’s (2007) conceptualization of techno-stress did not account for the ways in which technology reinforces discrimination, suggesting the need for a conceptualization of techno-discrimination as a significant stressor. This was present in Outsider Threats and resulted from the targeting of a worker’s non-normative identities. This is not to say that discrimination is isolated to this specific threat sub-type, however. Technology threats to competency and professional worth, for instance, are also likely the result of discrimination given that these threats mirror discriminatory threats introduced by human actors, for example, management overproceduralization of the work of Black library workers (Ossom-Williamson et al., 2021) threatens their competency-based self-esteem.
Threat responses (RQ2)
Participant responses to technology identity threats can be understood through the lens of Petriglieri’s (2011) Identity Threat Response Framework. For instance, findings show that participants engaged more often in identity restructuring responses, for example, redefining, reassessing, than identity-protection responses, for example, reasserting. This makes sense given Petriglieri’s first proposition—that restructuring responses are more likely for threats that are stronger in terms of magnitude and/or frequency. Because participants were asked to talk about work that was routine, which represents work that is frequently repeated, the threats they faced were more frequent and, thus, they engaged more often in restructuring responses. Petriglieri’s second proposition is that the more social support a person has, the more likely they are to engage in identity-protection responses. The current study clarifies what that social support looks like. Clear policies supported participant efforts to reassert the prestige they associated with their role and push back against patron redefinitions, for example, tech support and babysitter. Clear role definitions, like putting women of color in charge of the makerspace, supported participant efforts to reassert the worth they attached to their group identities because they represented a highly visible sign of the library’s legitimization of their identity. Petriglieri’s fourth proposition is that positive-distinctiveness responses like reasserting are more likely with identities that a person considers to be central to their goals, values, and sense of self. Because participants used this approach almost exclusively for identities that targeted the sense of worth they derived from group identities, these group identities seem to be more central to a participant’s sense of self than role or person identities were.
The absence of certain threat response types in the current study is also notable. Derogation responses, for instance, were not present in the current study. This is likely because of the saliency of participants’ professional identities, which may be seen as inconsistent with derogation. Knowing that researchers from a library school would listen to the diaries, participants might have feared coming across as unprofessional. Concealment responses were also notably absent. This is likely the result of participants feeling that the components of their identity that were threatened could not be hidden. This is true for racial and gender identities, but also for professional and role identities. Finally, identity exit was not noted. One way to exit a role identity is to quit a job, but since the study involved current library workers, this response had not been taken by any of them. Furthermore, for threats that centered around a participant’s ascribed group identities, like gender and race, exit was not an option.
Identity conditionality (RQ3)
Answers to RQ3 contribute to research on the conditional factors that play a role in IT identity threats. Given that threats were exacerbated by the suppression of participants’ voices in selection and implementation, libraries will need to provide plentiful opportunities to solicit worker input on technology decisions. This is particularly true for workers with non-normative identities, whose voice is more likely to be disproportionately suppressed (Mehra and Gray, 2020). Given what some participants viewed as a hasty implementation, libraries will also want to consider a more paced approach to the implementation of technology, rather than radical changes (Ashforth and Schinoff, 2016). Finally, as a study of underrepresented library workers, findings have additional implications for addressing technology’s potential discriminatory effects. Minoritized woman, for instance, are already increasingly susceptible to impostership syndrome in library work (Lee and Morfitt, 2020). Black workers are more susceptible to blame and accompanying competency and worth threats because their mistakes are exaggerated and scrutinized in ways that the errors of their white colleagues are not (Settles et al., 2019; Wingfield, 2019). Libraries will need to proactively guard against these discriminatory effects.
Implications for AI
One limitation to any study on library technology is that this technology is continuously and rapidly changing, potentially making any findings irrelevant after a short amount of time. The perception might be that, for instance, that as these technologies are replaced, any threats they introduced will be fundamentally altered. However, it is important to consider the threats that persist through technological advances. Recent developments in AI, for instance, extend the technology into tasks traditionally viewed as the realm of human work and introduces unique concerns around worker privacy and autonomy (Selenko et al., 2022). The technology is capable of autonomous learning without explicit programing (Parent-Rocheleau and Parker, 2022), decision-making on a scale that far exceeds that of humans (Robert et al., 2020), and it represents a more totalizing form of worker surveillance (Jarrahi et al., 2021). However, a singular focus on what is unique about today’s AI at the expense of longstanding contextual issues impacting the implementation of any technology can result in a repetition of significant mistakes. This is because, as Fleming (2019) noted: “It is not technology that determines employment patterns or organizational design but the other way around. The specific use of machinery is informed by socio-organizational forces, with power being a particularly salient factor” (p. 27). Many of these forces persist through technological changes. Thus, the current study’s analysis of the factors influencing a library worker’s interactions with existing technology can reveal insights that are likely to play a role in the implementation of technology in the future.
First, findings show that the work tasks that threatened the prestige associated with library work were those that were the simplest and required the least amount of skill, for example, fixing printers, helping patrons send email. Algorithmic management has the potential to exacerbate these threats by establishing monitoring, goal setting, performance management, and other functions around these less prestigious work tasks (Parent-Rocheleau and Parker, 2022). This is likely to happen, because it is much easier to quantify something like how many times a worker helps a patron print something than it is to quantify more complex tasks like helping a patron navigate a complex research topic. This could result in a negative feedback loop where workers engage more often in simple—and less prestigious—quantifiable tasks because the more complex tasks that require more problem-solving take longer to complete and are less likely to be captured by the algorithm. This furthers the phenomenon known as working for data, which involves a fixation on data-satisfying tasks that can detract from an organization’s focus on operations or customers (Evans and Kitchin, 2018). Thus, in addition to threatening the prestige library workers associate with the profession, AI also has the potential to threaten a library’s capacity to meet its core objectives.
Second, findings show that imposter threats were the result of comparisons with others perceived as possessing superior characteristics. This aligns with research suggesting that, while upward social comparison can inspire people to become more like others, it can also result in decreased self-esteem and well-being (Vogel et al., 2014). AI has the potential to exacerbate upward social comparison through the gamification of algorithmic rewarding (Kellogg et al., 2020), which presents fun visualizations of a worker’s performance as compared to that of their colleagues. This provides workers with an overly simplified, yet powerful, tool of comparison. At the same time, these games can also decrease social support, an important work resource, by creating a climate of competition among workers (Parent-Rocheleau and Parker, 2022). Furthermore, algorithmic monitoring and rewarding reduces a worker’s performance to a set of data points that may not reflect their true performance. This can result in a perception of algorithmic reductionism—when workers perceive that the algorithm eliminates the qualitative aspects of their work in favor of more quantitative aspects and, as a result, that their work is not fairly considered within its broader context (Newman et al., 2020). This perception of unfairness can, in turn, reduce the extent to which a worker wants to remain with the organization. Workers who feel that an algorithm fails to reflect their true competencies may also express feelings of humiliation and demoralization (Kantor and Sandaram, 2022).
Third, findings show that outsider threats could be perceived, not because of something in the technology itself, but rather because of the ways in which technology increased a participant’s interactions with other people who devalued some component of their identity. This has implications for the implementation of algorithmic scheduling. The use of algorithms to automate scheduling has been shown to introduce discrimination by shifting some workers to part-time, thus taking away health benefits (Kaplan, 2013); providing schedules to workers only a few days before they are implemented (Kantor and Sandaram, 2022); and introducing unpredictability to scheduling (Wood, 2021). The current study suggests that, because algorithmic scheduling automates work schedules using data on things like customer demand and seasonal patterns (Jarrahi et al., 2021; Parent-Rocheleau and Parker, 2022), it might also struggle to account for a coworker’s exposure to discriminatory actions or microaggressions from problematic colleagues—furthering the outsider threats a worker faces.
Fourth, AI has the potential to exacerbate authenticity threats. The reductions in worker autonomy introduced by algorithmic monitoring and rewarding (Parent-Rocheleau and Parker, 2022), for instance, might force workers into behaviors that appease the algorithm but are inconsistent with their values or beliefs. This can result in self-alienation, in which workers feel that who they are is “an alien corporate self” (Costas and Fleming, 2009). Authenticity threats were also the result of emotional regulation, as participants felt compelled by management to suppress their personal feelings as they interacting with frustrating technology. AI represents a powerful tool for monitoring and guiding workers into the display of appropriate emotions. Waber (2013), for instance, conceived of a sociometric badge capable of monitoring a worker’s tone of voice while they interacted with colleagues. For Waber, this represented a powerful tool for nudging how employees engaged with each other—which he noted was an important part of an organization’s success. Over time, this suppression of authentic emotions in favor of management’s prescribed emotions can estrange workers from their authentic emotions (Hoschild, 2012).
Limitations
Because the audio diary prompts asked participants to talk about moments of frustration, the study was not capable of capturing moments when technology supported the functions of workplace identity or were perceived by participants as identity-enhancing. This is a likely outcome given previous research, for example, library workers as “super searchers” (Hicks, 2014). Additional research is needed, then, that considers the ways in which a library worker’s interactions with technology enhance competency-based, worth-based, or authenticity-based self-esteem. Demographic data were collected to enrich the findings and ensure that the sample included workers with identities they perceived as being underrepresented, minoritized, and/or stigmatized in some way. This was important given the evidence that identity threats are more prominent for workers with these identities (Boussebaa and Brown, 2017; Gago-Rodríguez et al., 2024). However, the sample size and method precluded generalizations or conclusions about the role of specific demographic traits in a worker’s interactions with technology and the impact of those interactions on worker identity. Future research is needed to isolate specific demographic traits to identity potential patterns in how these traits mediate technology identity threats.
Conclusion
Based on an analysis of audio diaries, the current study uncovered several identity threats that were present during a library worker’s interactions with technology. These threats obstructed a worker’s competence-based, worth-based, and authenticity-based self-esteem. Yet, findings show that workers were active in crafting and implementing responses to these threats to fulfill the identity function of increased self-esteem. Findings also suggest several conditional factors that influenced the extent to which a given technological interaction was perceived as a threat. This study contributes to research on professional identity in librarianship by considering the role of nonhuman actors, like technology. It also provides a novel setting for the consideration of IT identity threats. Findings have important implications for both current and future implementations of technology within libraries. This includes AI, and libraries framing their implementation of AI in light of these findings will be in a better position to avoid previous mistakes.
Footnotes
Author’s Note
Katie Klein is now affiliated to University of North Texas–Denton, TX, USA.
Ethical considerations
This study was approved as exempt from Human Research Subject Regulations by the IRB at the University of South Carolina.
Funding
The authors disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research was funded by a grant from the Institute of Museum and Library Services [RE-254858-OLS-23]. The views, findings, conclusions or recommendations expressed in this article do not necessarily represent those of the Institute of Museum and Library Services.
Declaration of conflicting interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Data availability statement
Data include personal identifiable information about participants. To protect the privacy of these participants, the raw data are not shared.
Generative AI use
No generative AI was used in writing this paper.
