Abstract
Data breaches are an everyday occurrence, exposing the personal details of millions globally. The victim impacts of data breaches can be considerable, including a range of financial harms such as fraud and identity crime, as well as non-financial harms, such as declines in emotional and psychological wellbeing. While these harms are documented, there is less research exploring how data breaches in particular expose victims to further victimisation, specifically through phishing attacks by offenders. Using survey data from 2,019 victims of the Optus and Medibank/AHM data breaches in Australia in 2022, this article examines factors which relate to phishing attempts on these individuals. Results indicate limited factors in predicting those targeted by phishing attempts. This highlights the opportunistic nature of phishing attacks in the aftermath of these two data breaches and a more generalised approach taken by offenders to gain additional details. It also demonstrates a need for continued community education and awareness to protect further personal information from being accessed by offenders into the future.
Introduction
Data breaches are an everyday occurrence given the level of digitisation of personal information coupled with the difficulty of tracking the type of data shared with organisations (Andrew et al., 2023). There have been many examples of data breaches exposing the personal details of millions of individuals around the globe over the last two decades (Africk & Levy, 2021). In the United States, there have been several large-scale breaches including Twitter, Facebook, Equifax, Capital One, The Marriott, Target, and Office of Personnel Management (OPM) to name a few (Coffey, 2019; Khan et al., 2021). The ongoing prevalence of data breaches has seen a desensitisation from society to both their occurrence and their impacts (Khan et al., 2021).
Australia is not immune to data breaches, as many government and private sector organisations have been impacted including Australian National University (Andrew et al., 2023) and Red Cross (OAIC, 2017). In 2024, there were 1,113 data breaches reported to the Office of the Australian Information Commission (OAIC), up from 890 in 2023 (OAIC, 2025; 2024). This is indicative of an upward trend across several years. Most notably, in 2022, Australia experienced two of the largest recorded data breaches in its history in quick succession, targeting Optus and Medibank/AHM. These two breaches exposed an array of personal information from 9.8 and 9.7 million Australians, respectively (Optus, 2022; UpGuard, 2022).
As the number of known data breaches has increased in recent years, so has evidence that they cause both financial and non-financial impacts to victims (Harrell & Thompson, 2023; Maher & Hayes, 2024). Though beneficial, few have considered the extent to which data breaches create opportunities for subsequent victimisation outside of any direct losses incurred through the breach. The kinds of data compromised in breaches, particularly names, addresses, phone numbers, and email addresses, create immediate avenues for offenders to target individuals with phishing emails and related schemes (Coffey, 2019; Garrison & Ncube, 2011; Holt, 2013). Additionally, phishing attempts appear to increase in the aftermath of natural disasters and crisis events, such as the COVID-19 pandemic which enabled schemes targeting people around the globe (Bitaab et al., 2020; Chang & Chong, 2021; Taodang & Gundur, 2023; Verma et al., 2018). Large-scale data breaches that affect large segments of the population would seemingly fit with this pattern.
Given this gap in the research literature, there is a need to explore the extent to which data breach victims experience subsequent phishing and fraud attempts, and any factors that may be associated with this targeting. This study attempted to address this issue using quantitative analyses of survey responses from a general population sample of individuals who were affected by the Australian Optus and Medibank/AHM breaches. Using Routine Activities Theory as an analytical framework, two binary logistic regression models were estimated for individuals affected by each breach to assess any significant relationships between specific data losses and behavioural and demographic factors. The implications of this study for our understanding of data breach victimisation and cybercrime victimisation are discussed in detail.
Understanding Data Breaches
At a high level, data breaches can be defined as ‘an occasion when private information can be seen by people who should not be able to see it’ (Gaglione, 2019: 1137). A breach occurs when a third party gains unauthorised access to information which can lead to a range of negative outcomes, from exposure to theft or misuse (Spanca & Salihu, 2024). The data lost in most breaches falls into several categories, including personal health information, personally identifiable information, trade secrets, or intellectual property (Strzelecki & Rizun, 2022: 2).
There are multiple causes of data breaches which cut across both online and offline environments (Holtfreter & Harrington, 2015). There is a strong focus on those which are perpetrated by malicious actors outside of organisations, such as through phishing or malicious software-based attacks (Algarni & Malaiya, 2016). At the same time, breaches can result from accidental or unintentional actions, usually on a smaller scale, such as mishandling laptops or flash drives containing sensitive data (Romanosky et al., 2011, see also OAIC, 2025 for specific examples).
The type of information exposed in a data breach will arguably determine its impact on victims, such as the ability of victims to repair and/or restore their identity. This is evident in the categorisation of ‘reversible’ and ‘irreversible’ data breach victimisation (Ayaburi, 2023: 98). Reversible data breach victimisation is minimal, involving information that ‘could easily be repaired through mechanisms such as the closure of a compromised bank account or replacement of a stolen credit card number’ (Ayaburi, 2023: 98). Irreversible data breach victimisation includes instances where ‘the perception of loss of private information has long-term irreparable impact’ and may render victims unable to ‘completely forget about the damages resulting from the data breach’ (Ayaburi, 2023: 98).
Financial harms resulting from fraud and identity crimes are some of the most well-established consequences of a data breach (Acquisti et al., 2006; Aivazpour et al., 2022; Burdon et al., 2012; Gaglione, 2019; Gibson & Harfield, 2021; Ong, 2023). The loss of personally identifiable information can facilitate a range of fraud types, including existing account fraud or new account fraud (Harrell & Thompson, 2023; Roberds & Schreft, 2009). Acquiring social security numbers and other personal information allow offenders to sell this information to facilitate identity crimes (Burdon et al., 2012).
Research indicates that appearing in a breach creates an overall ‘low risk of identity theft’ (Smyth, 2013, p. 181), though some victims can experience identity theft within 2 weeks of a breach (Garrison & Ncube, 2011). For some victims, it is the perpetration of fraud or identity crime which alerts them to their details having been exposed in a data breach (Harrell & Thompson, 2023). One study suggests that 31.7% of data breach victims will have identity theft perpetrated against them (Coffey, 2019). This is largely supported by research into identity crimes more broadly. For example, one Australian study recorded 30% of respondents having experienced identity crime in their lifetime, and 20% of respondents having experienced identity crime in the past 12 months (McAlister et al., 2023).
Optus and Medibank/AHM Data Breaches
In the second half of 2022, Australians experienced two of the largest data breaches in Australia at that time. Optus was the first entity to experience a breach in September 2022. The company is the second largest telecommunications provider in Australia (behind Telstra). The scope of customers harmed was between 2.5 million to 9.7 million customers (Smith, 2022), though some reports indicate it may have been as many as 10 million (Riches, 2022). The breach exposed customers’ names, phone numbers, email addresses, dates of birth, addresses, and ID documents, as well as Australian Business Numbers and Australian Company Numbers (iDcare, 2022).
Less than a month later, Australians were notified of their involvement in another large-scale data breach affecting the large Australian private medical insurer, Medibank, who also supports a smaller company, AHM. In October 2022, hackers were able to acquire 200 GB of unauthorised customer data (Mason et al., 2022). The breach led to the compromise of the following credentials for 9.7 million customers: first names and surnames; addresses; dates of birth; Medicare numbers; policy numbers; phone numbers; [and] some claims data, including the location of where a customer received medical services and codes relating to their diagnoses and procedures (UpGuard, 2022).
Data Breaches and Phishing
These metrics only reflect the ability of victims to directly connect their losses to a data breach and may not include instances where individuals’ data is used to facilitate other forms of cybercrime. Researchers have argued that phishing, which typically involves the use of deceptive email or other electronic communications to obtain sensitive information from the targeted person, is equally relevant for targeting individual victims in the wake of a breach (Gibson & Harfield, 2021; Lastdrager, 2014). Phishing can be used to gain personal information and credentials that can then be used to commit further crimes, such as fraud and identity theft.
As noted by Acquisti and colleagues (2006: 1565), ‘even when no actual fraud directly follows from a breach, the victim may be at an increased risk of phishing’. Data breaches allow offenders to harvest massive email lists from companies and retailers that facilitate targeted phishing campaigns that may increase the likelihood of victim responses. For instance, online illicit markets regularly sell email addresses and other contact points for spam and phishing email distribution (Dupont et al., 2017; Holt, 2013; Holt & Lampke, 2010).
There are two ways that offenders can deploy phishing attacks relevant to data breaches. The first is to target individual victims who were involved in the data breach. In these cases, offenders may have relevant credentials of individuals, like email addresses and phone numbers. They must acquire additional information, such as bank account details, in order to perpetrate subsequent offences like financial fraud (e.g. Brown, 2016; FTC, 2025; Thomas et al., 2017). Offenders will then tailor the phishing attack to the individual with the specific purpose of extracting the additional personal information they need.
The second is to target the general population more broadly, regardless of whether they were directly affected by the breach or not. The sheer size and scale of many data breaches (Optus and Medibank/AHM included) enables offenders to deploy large-scale phishing attacks and potentially contact individuals who have been involved in the incident (Brown, 2016; Thomas et al., 2017). These generalised approaches can solicit a wide range of personal details and have the same intention as more targeted approaches to facilitate other criminal activities. Phishing attacks may be successful when deployed in relation to data breaches as they frequently invoke a sense of urgency and authority (Steinmetz & Cross, 2023; Thomas et al., 2017). Furthermore, they often demand instant decision making as opposed to thinking it through and consulting with family, friends or authorities.
Offenders could easily tailor fraud campaigns to victims, using strategies like posing as the retailer who was compromised to get victims to provide credentials to log into accounts or confirm their identity to avoid further victimisation (Leukfeldt, 2014; van’t Hoff-de Goede et al., 2024). A similar dynamic was observed by Verma and colleagues (2018) who examined phishing emails targeted at individuals in the aftermath of Hurricane Harvey. This study demonstrated an increase in vulnerability of those affected by Hurricane Harvey to click on links in emails or downloaded attachments that they would not have previously actioned.
The quantities and qualities of the Optus and Medibank breaches suggest there is significant potential for phishing attempts in the weeks and months after the public acknowledgement of the breaches. Several organisations issued warning and alerts to the general public, such as the Australian Competition and Consumer Commission which released public statements on the potential for phishing attacks in the wake of both the Optus and Medibank breaches (Scamwatch, 2022a, 2022b). Fact sheets were created for both incidents, highlighting the perceived risk of phishing and educational materials on how to protect oneself from harm. The Australian Media Communications Authority (ACMA) put out a warning to Optus customers several months later, reiterating the ongoing threat of phishing emails (ACMA, 2023).
Understanding Correlates of Phishing Stemming from Data Breaches
The potential for phishing schemes to be launched in the wake of a data breach calls to question what factors increase individual risk of victimisation. One of the key frameworks to assess such risks is Cohen and Felson’s (1979) routine activity theory. This well-tested theory argues that crime occurs as a result of the convergence of motivated offenders, a lack of guardianship, and a suitable target in time and space. Researchers have used this theory to account for victimisation in on and offline settings (e.g. Ahmad & Thurasamy, 2022; Engström, 2021; Hayes & Maher, 2024), and in multiple studies related to phishing victimisation risk (e.g. Lee et al., 2022; Leukfeldt & Yar, 2016; Maimon et al., 2023; van’t Hoff-de Goede et al., 2024).
One of the key arguments of this framework is that individuals’ personal characteristics and routine behaviours make them suitable targets for specific forms of crime (Cohen & Felson, 1979). Target suitability has largely been categorised around the symbolic or economic value of an individual or item, depending on the offence, and its value, inertia, visibility, and accessibility to the offender (Leukfeldt & Yar, 2016; Newman & Clarke, 2003; Yar, 2005).
Prior research on phishing and fraud targeting generally suggests that victims’ exposure, or visibility and accessibility to the target, has the greatest relationship to risk (Gan et al., 2024; Pratt et al., 2010; van Wilsem, 2011). Time generally spent online and in certain environments, like shopping sites, increased individuals’ risk of being victimised (Gan et al., 2024; Leukfeldt & Yar, 2016; Pratt et al., 2010; van Wilsem, 2011). The evidence is mixed, with some finding no relationship to online exposure or activity variables (Hutchings & Hayes, 2009; Leukfeldt, 2014; Ngo & Paternoster, 2011; van’t Hoff-de Goede et al., 2024).
Applying these findings to phishing after a data breach may have less value, as offenders have ways to access potential victims in their possession by virtue of the data stolen. There should be an association between the loss of specific pieces of data in a breach and an increased risk of receiving phishing emails. The loss of contact points, such as email addresses, phone numbers, and names, would enable phishers to more easily engage in targeted messaging against a range of potential victims (Cross & Holt, 2025; Thomas et al., 2017). The same is true for information more sensitive information that may enable more tailored messaging, like individuals’ date of birth. Thus, the loss of information in a data breach may serve as a target suitability factor by making a subset of potentially attractive victims more visible and accessible to motivated offenders (Newman & Clarke, 2003; Yar, 2005).
In addition, it is likely that individuals who experienced both the Optus and Medibank breaches have a greater risk of exposure to offenders. The quantity and quality of data available about individuals in each breach was substantial (e.g. iDcare, 2022; Mason et al., 2022). Appearing in both incidents may increase individuals’ general visibility to offenders and engender a greater risk of receiving phishing emails.
The relationship between individual demographics and the risk of victimisation through phishing is quite mixed (Martins et al., 2023). Research suggests that gender, age, and race are generally unrelated to fraud and phishing risks (Leukfeldt & Yar, 2016; Martins et al., 2023; Ngo & Paternoster, 2011). Income, education, and age have some association with fraud and victimisation, though it is unclear if these factors are an indirect result of online activities that increase exposure to offenders (e.g. Leukfeldt & Yar, 2016; Ngo & Paternoster, 2011; Reyns, 2015). Additionally, some studies have found no association between socioeconomic factors and phishing victimisation (Leukfeldt, 2014; Martins et al., 2023).
Regarding phishing as a result of data breaches, it may be that there are inconsistent significant relationships to demographic factors. Some offenders may take a ‘spray and pray’ approach, whereby as many individuals are targeted as possible to increase the likelihood of responses (Leukfeldt, 2014; Ngo & Paternoster, 2011). As a result, there may be little correlation between demographic factors and victimisation risk as everyone has equal risk of targeting.
At the same time, marginalised groups and populations with differential knowledge of cybersecurity threats may be more likely to respond to certain pressures. For instance, individuals living in lower income brackets may be less aware of cybersecurity issues, and thereby more likely to respond to phishing emails (Leukfeldt & Yar, 2016). The same may be true for the elderly, non-native English speakers, and Indigenous or non-native Australians may be more attractive targets for phishing threats.
This study attempted to explore these relationships by examining the extent to which those involved in Optus and/or Medibank/AHM data breaches were targeted by offenders by phishing attempts in the aftermath of these incidents. Using a quantitative sample of respondents in Australia, this study utilised binary logistic regression modelling to determine what (if any) correlates are relevant to those in these two breaches who were targeted.
The Present Study
Given the empirical data associated with traditional phishing victimisation risks, it is plausible that some of the dynamics also predict the likelihood of phishing contacts following data breaches. This study attempted to test the following routine activities-based hypotheses to assess the relationship between phishing contacts in the wake of the Optus and Medibank/AHM breaches:
Loss of specific contact data points should increase the risk of phishing targeting.
Appearing in both the Optus and Medibank/AHM breaches increases the risk of phishing targeting.
Marginalised groups will experience an increased risk of phishing targeting. Univariate and multivariate statistics were used to test these hypotheses using a population of Australian respondents who experienced these two breaches.
Methodology
In 2021, a survey was conducted with Australians on the topic of data breaches (Cross & Holt, 2025). In the aftermath of the Optus and Medibank/AHM data breaches, this survey was revised, redistributed, and forms the basis for the current analysis. In particular, the survey was reworked to specifically capture the experiences of individuals who were directly involved in the Optus and/or Medibank/AHM data breaches. Given the scale of the two data breaches (9.8 million and 9.7 million victims, respectively), the ability to recruit a sample was not foreseen to be problematic.
Qualtrics (online survey panel provider) was used to recruit respondents to the online survey. Responses were collected from 2019 participants during May 2023. Eligibility to this survey comprised of those who were aged 18 years and older, currently lived in Australia, and were able to give consent to participate in the survey. Further, eligibility to the survey required that the respondent knew they were involved in the Optus and/or Medibank/AHM data breaches (which occurred in September and October 2022). A variation to the original ethics approval was received to conduct this second survey (Queensland University of Technology Human Research Ethics Committee approval #4011).
The survey consisted predominantly of close ended questions which were mandatory. There were a small number of open-ended questions throughout, which were optional, to elicit further details where relevant. To ensure participants had a consistent definition for what constitutes a data breach, the following language was presented to participants at the beginning of the survey: A data breach ‘occurs when an organisation experiences an unauthorised leak or loss of a customer’s personal information’. This can also be referred to as a third-party data breach (meaning the data is compromised by someone other than yourself).
For the purposes of the current survey, respondents were directed to this only being applicable to the Optus and/or Medibank/AHM data breaches and not to capture any other data breaches that they may have been involved in.
A total of 2019 respondents completed the survey, with the sample generally representing the population demographics of Australia. A simple majority of respondents were female (52.5%) and closely resembled the age distribution (37.9 years average; 38.3 years national average as per AIHW, 2024) and educational composition of the nation (30.2%; 32% per Statista, 2024). The sample also over-represented Aboriginal and/or Torres Strait Islanders (8.8% compared to 3.8% national average as per ABS, 2023).
Only those respondents who reported their data appeared in either the Optus or Medibank/AHM data breaches were included in this analysis. A total of 1,666 (82.5%) respondents noted their data was lost in the Optus breach, while 857 (42.4%) reported experiencing the Medibank/AHM data breach. A small proportion of respondents were excluded from each sample due to missing data leaving a final population of 1549 respondents who experienced the Optus breach and 778 affected by the Medibank/AHM breach. It should be noted that while the extent of both data breaches were similar in numbers, the current data set comprises roughly twice the number of Optus victims compared to those involved in the Medibank/AHM data breach. There is no immediate reason for this sampling pattern, as eligibility targeted those across both data breaches.
Descriptive Statistics
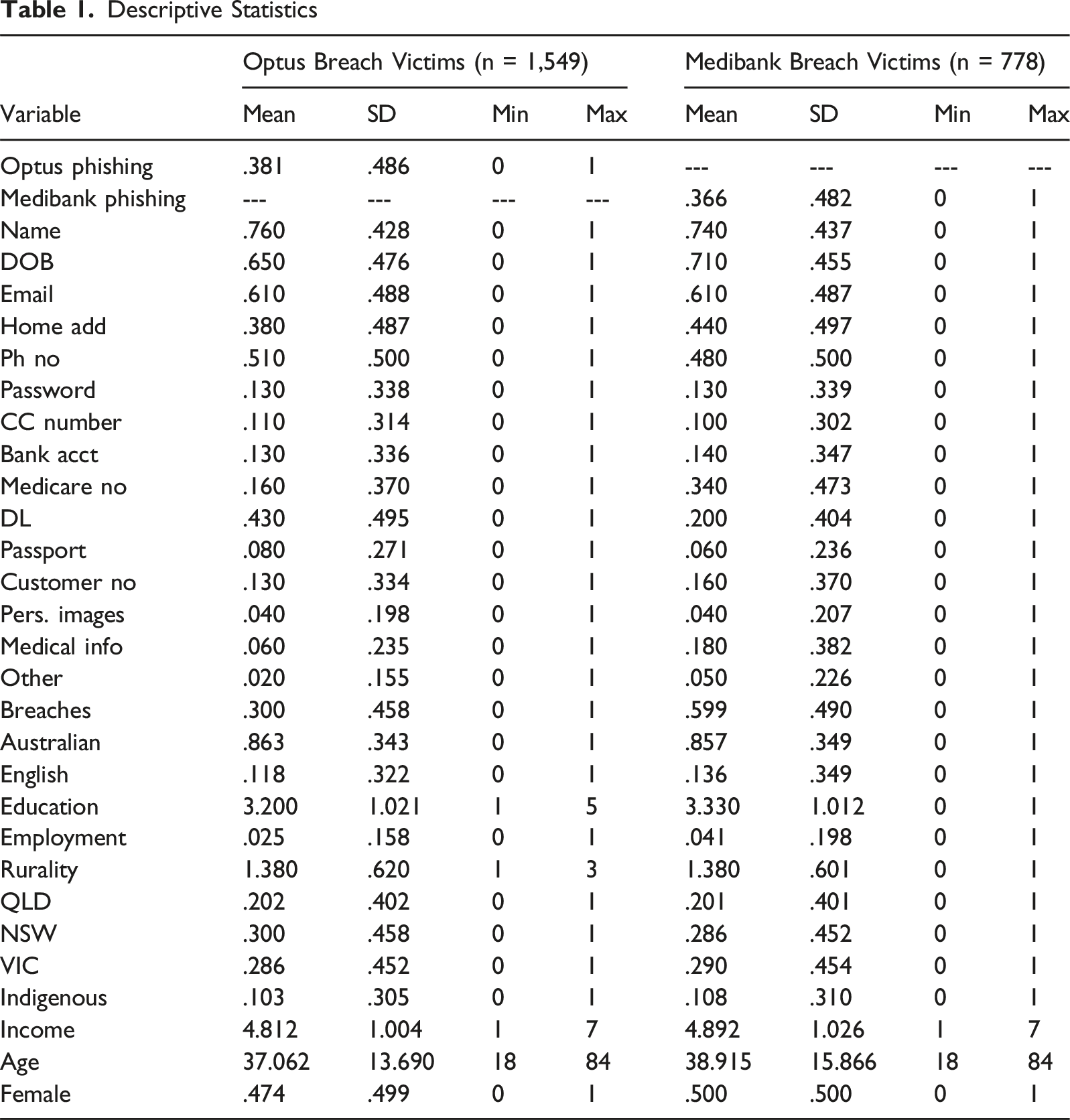
Dependent Variables
Respondents were asked in the context of having experienced the Optus and/or Medibank breaches: ‘Have you received any calls, texts, emails, or other communications since having your details exposed, which have asked you for money or for further personal information?’ Responses included (1) yes, (2) no, and (3) unsure, though this was collapsed into a binary measure, with all no and unsure responses subsumed into 0, while yes was coded as 1 (see Table 1). Disseminating the survey approximately 7 months following both breaches allowed for a sufficient length of time for victims to have experienced some degree of contact from potential phishers and scammers. There was relative parity across both breach incidents, as 38.1% of Optus victims and 36.6% of Medibank/AHS victims reported receiving contacts asking for additional data or funds.
It should be noted that the self-report nature of this data relies upon individuals’ recollection of being targeted in the aftermath of the two data breaches. Receiving such a request may not be a direct result of appearing in the breach, though individuals may have been made more cognisant of the risk of being targeted for phishing attacks post-breach. Furthermore, it is possible that there may be some under-representation of requests as some phishing emails may have been diverted to a junk folder or deleted as part of an inbox filter, or calls and texts blocked by telecommunications providers. Capturing individuals’ awareness of potential fraud targeting is, however, essential to better understand how data breaches may impact both perceived and real risk of further victimisation.
Independent Variables
To assess any relationship between the kind of data lost in the breach and the risk of secondary victimisation attempts, a series of 16 items were included. Respondents were asked for each breach, ‘What information do you know was breached (please select all that apply)’ with the following items: (1) name; (2) date of birth; (3) email address; (4) home address; (5) phone number; (6) password/s; (7) credit card number; (8) bank account details; (9) Medicare number; (10) drivers licence number; (11) passport number; (12) passport number; (13) customer number; (14) personal/private images; (15) medical information; (16) other. Each item was included as a binary (0 = no; 1 = yes) to explore any significant risk to the likelihood of secondary fraud contacts.
An additional measure was created to capture repeat victimisation. Specifically, responses to the question did you lose data in the Optus and Medibank/AHS breaches were combined to create a binary measure of whether respondents experienced one or both breaches (0 = one breach; 1 = two breaches).
A series of 11 independent variables were included to identify any specific demographic correlates associated with being a victim of these breaches. First, respondents were asked ‘In what country were you born?’ to capture Australian birth heritage (0 = yes; 1 = no). To capture English language use, respondents were asked ‘Do you speak a language other than English at home?’ A three-item response was provided (1 = yes, 2 = no, and 3 = prefer not to say), with the small proportion of non-respondents being excluded in order to create a binary measure (0 = no; 1 = yes).
An additional measure was included to assess formal education based on responses to the question: ‘What is the highest level of formal education you have completed?’ Responses included (1) primary or elementary school; (2) secondary or high school; (3) tertiary diploma/trade certificate; (4) University undergraduate degree; and (5) University postgraduate degree.
To assess employment, the following question was presented to respondents: ‘Which one of these BEST describes your main activity at the moment’. A ten-item response was provided: (1) university postgraduate degree; (2) employed (full time, part-time, self-employed, casual); (3) unemployed; (4) student; (5) retired or on a pension; (6) stay-at-home parent/carer; (7) unpaid household duties; (8) other; (9) unsure; and 10) prefer not to say. A binary measure was created, collapsing those who indicated employed into one category (0) compared to all other activities (1). Those who were unsure or preferred not to say were excluded from this sample (n = 14).
To measure risk based on urbanity, respondents were also asked ‘Which of the following best describes your current location?’ with a three-item response provided: (1) urban or metropolitan; (2) regional; and (3) rural. Respondents were also asked ‘What Australian jurisdiction do you currently live in’ with eight response options: (1) Queensland; (2) New South Wales; (3) Victoria; (4) Tasmania; (5) South Australia; (6) Western Australia; (7) Northern Territory; and (8) Australian Capital Territory. The majority of respondents (77.9%) reported living in Victoria (28.9%), New South Wales (28.5%), and Queensland (20.5%). Thus, three binary control variables were included to control for individuals living in these three territories (QLD = 0 no; 1 = yes; NSW = 0 = no; 1 = yes; VIC = 0 = no; 1 = yes).
An additional measure was included asking respondents if they were Aboriginal or Torres Strait Islander. Responses included (1) no; (2) yes – Aboriginal; (3) yes – Torres Strait Islander; (4) yes-both; (5) unsure; and (6) prefer not to say. To provide the most accurate response, those who were unsure (n-15) or preferred not to respond (n = 16) were excluded from the sample. The measure was then recoded into a binary measure reflecting all those who indicated no (0) and those with Aboriginal and/or Torres Strait Islander identity (1).
Age was measured as a continuous variable (mean = 37.93 years). Income was a categorical variable, measured using the question ‘Before tax or other deductions, what is your total annual income? Please include wages and salaries, government pensions, benefits and allowances, and income from interest, dividends or other sources’. Responses included: (1) negative income; (2) 0–$18,200 (0–$350 per week); (3) $18,201–$45,000 (351–865 per week); (4) $45,001–$120,000 ($866–$,2307 per week); (5) $120,001–$180,000 ($2,308–$3,461 per week); (6) $180,001 and over ($3,462 and over per week); and (7) Unsure or prefer not to say. The small number of non-respondents was excluded to create a six-item measure for income.
Gender was measured using a four-item response: female; male; non-binary/gender diverse; and prefer not to say. Due to the very limited representation of non-binary (n = 13) and those who preferred not to respond (n = 3), those individuals were excluded from the analysis. A single binary measure was used reflecting female (0) and male (1).
Results
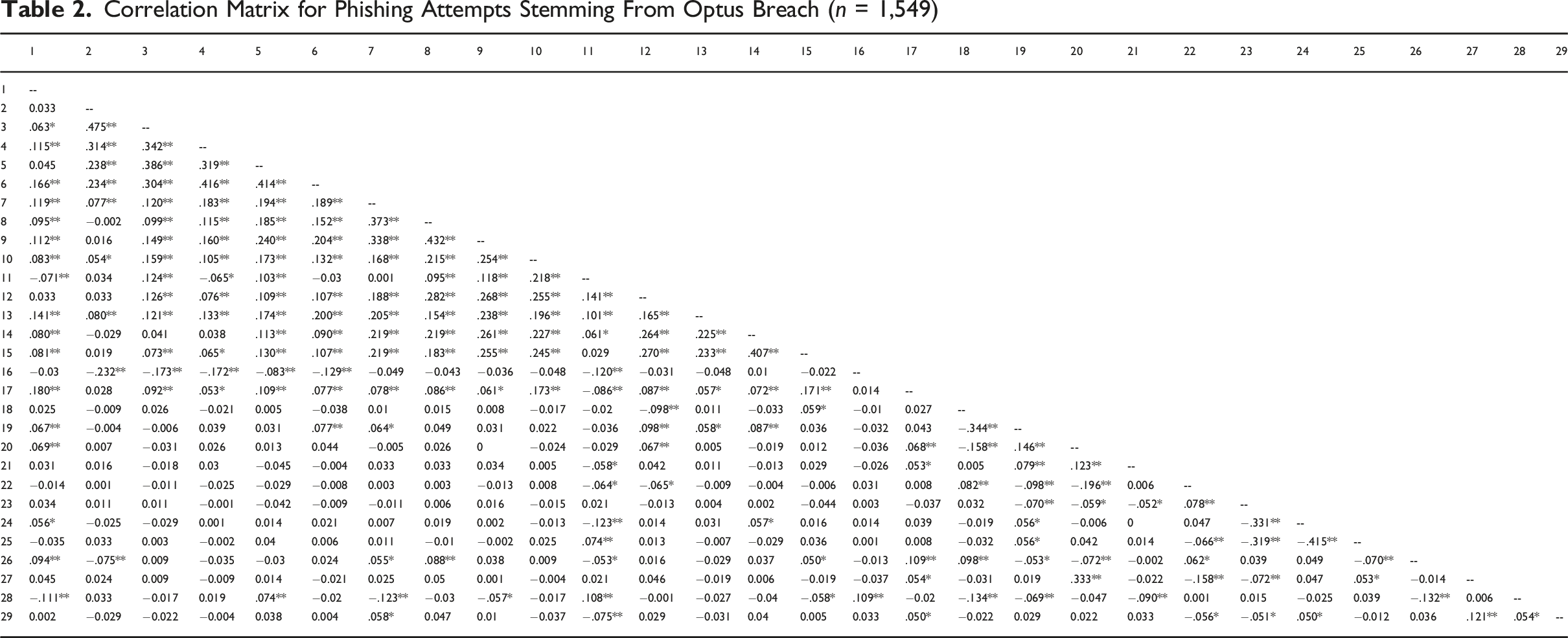
Correlation Matrix for Phishing Attempts Stemming From Optus Breach (n = 1,549)
Correlation Matrix for Phishing Attempts Stemming From Medibank/AHM Breach (n = 778)
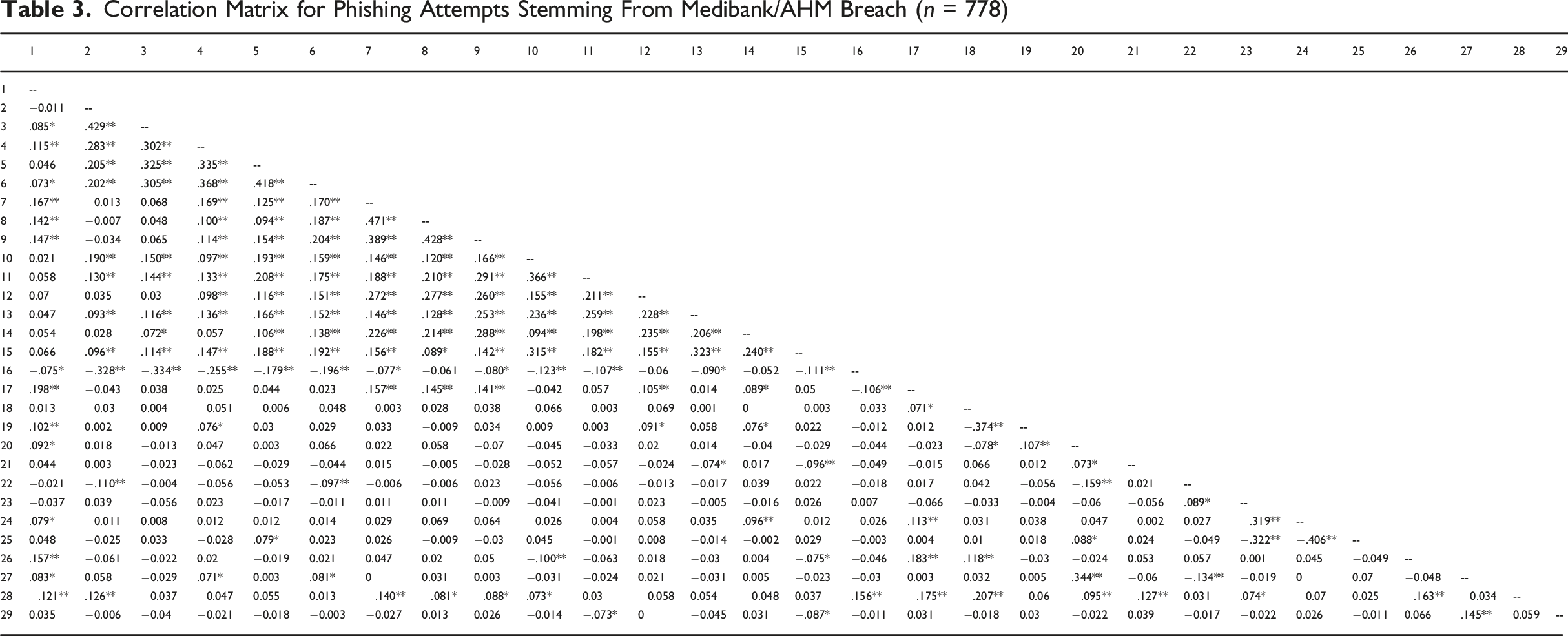
The relationships identified in the correlation matrix provided sufficient evidence to justify multivariate analyses. Two binary logistic regression models were estimated in SPSS version 26 software to examine the relationships between phishing messages and the various independent variables included. There was no evidence of multicollinearity as the lowest tolerance was .585 and the highest VIF was 1.718.
Binary Logistic Regression Estimating Phishing Attempts Stemming From Optus Breach (n = 1549)
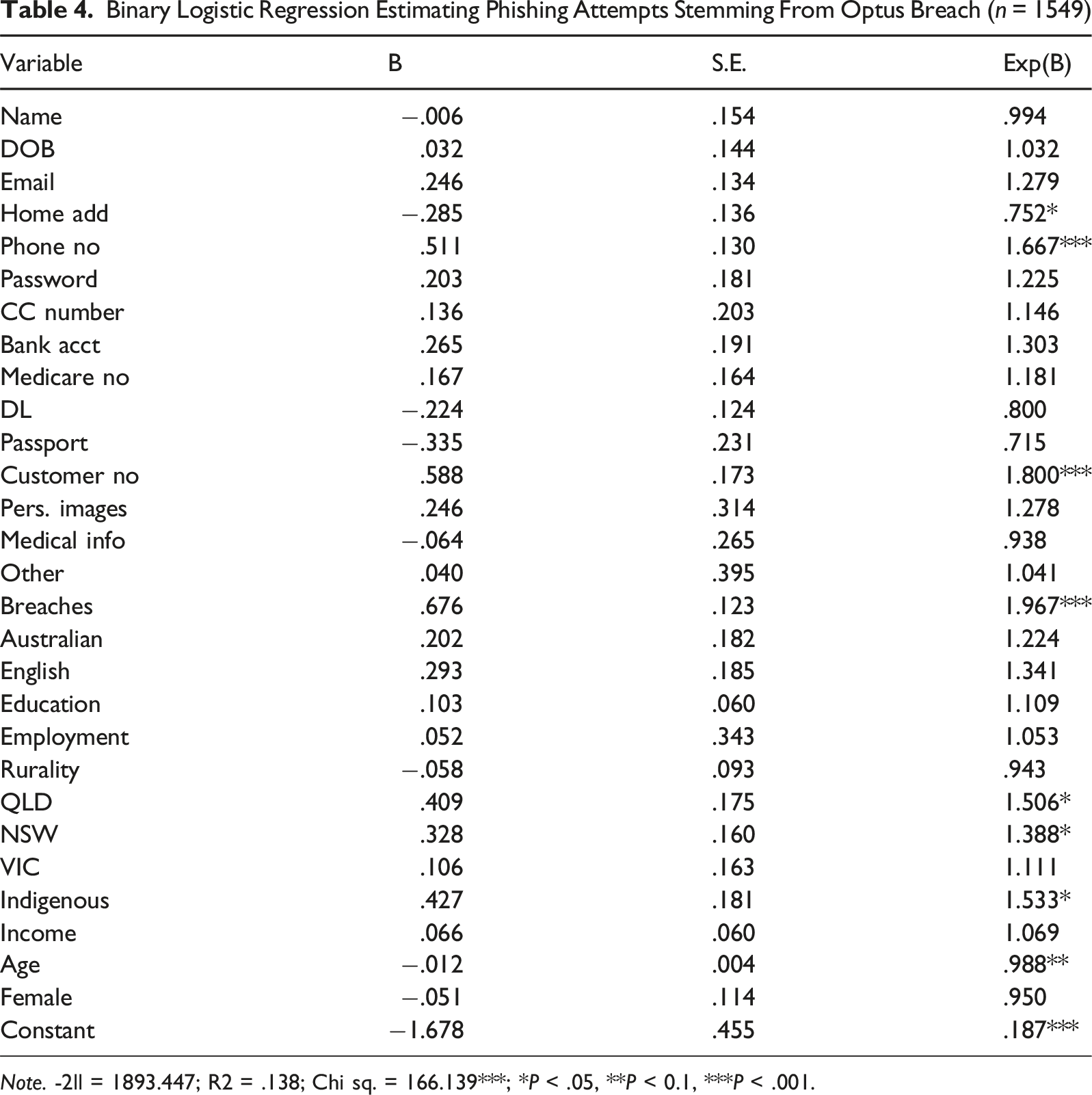
Note. -2ll = 1893.447; R2 = .138; Chi sq. = 166.139***; *P < .05, **P < 0.1, ***P < .001.
Binary Logistic Regression Estimating Phishing Attempts Stemming From Medibank Breach (n = 778)
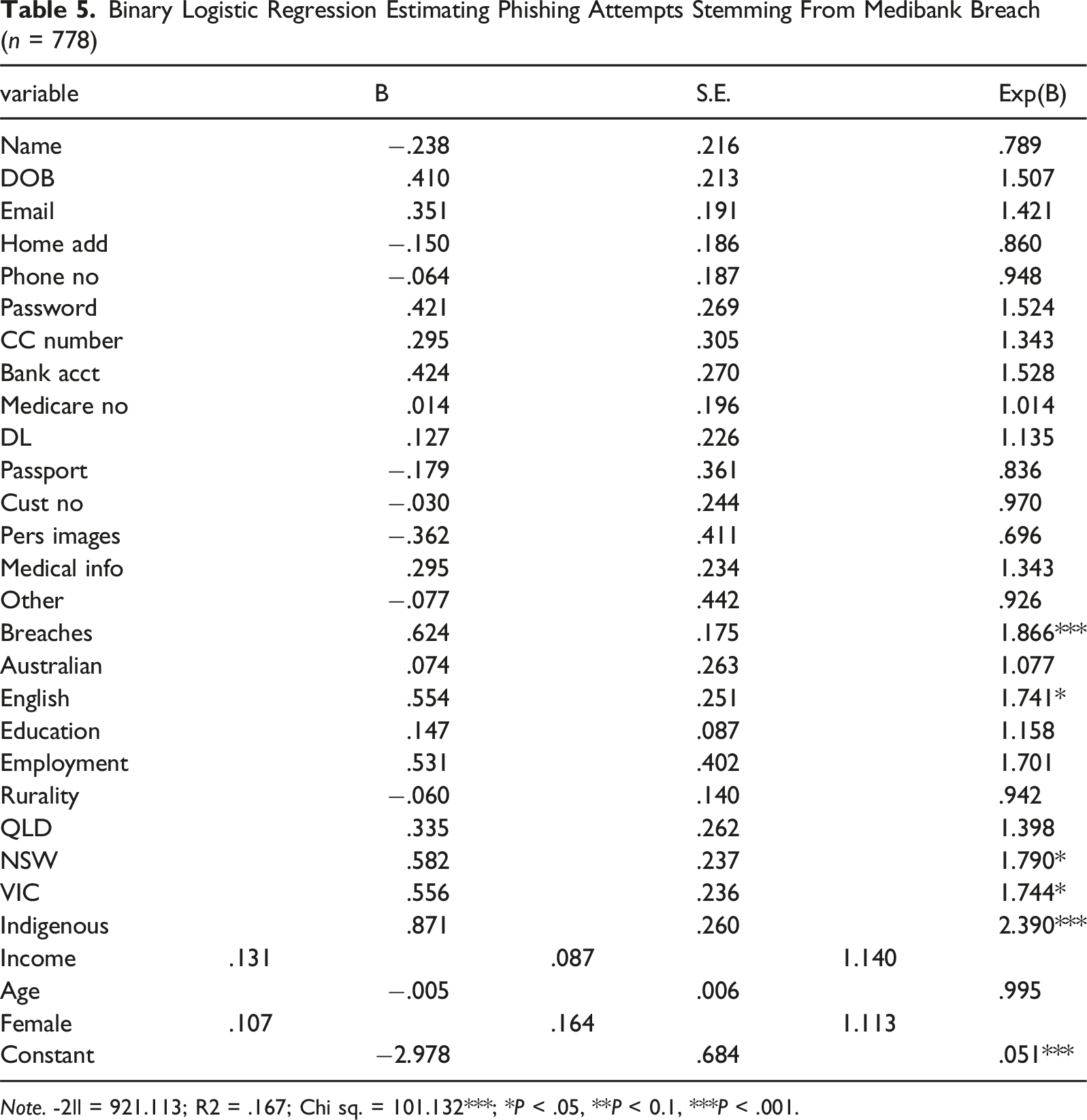
Note. -2ll = 921.113; R2 = .167; Chi sq. = 101.132***; *P < .05, **P < 0.1, ***P < .001.
Discussion and Conclusion
The current analysis attempted to explore the incidence of additional victimisation in the aftermath of the Optus and Medibank/AHM data breaches. These incidents led to a substantial loss of personal information for victims who appeared in one or both breaches, with enough information to readily enable them to be victimised further (FTC, 2025; Thomas et al., 2017). The focus of this study was on exploring the risk factors for phishing attempts, defined as unsolicited requests for additional funds or personal information, following appearing in a data breach through an application of routine activities theory (Cohen & Felson, 1979).
The results indicate mixed findings. Notably, the type of data lost was only associated with the Optus data breach, particularly losing phone number and customer number. This is sensible as offenders could utilise this data to more readily access victim populations for vishing, or phone based phishing attacks. Access to customer numbers also allows for more tailored approach that can personalise the message to each recipient to make a more convincing scam message. The lack of significance for Medibank/AHM was somewhat unexpected, particularly given the amount of sensitive information available to offenders as a result of the breach.
The significant relationship between appearing in both breaches suggests that offenders may not be specifically seeking to obtain specified credentials but engaging in a more generalised blanket approach to their efforts (Leukfeldt, 2014; Ngo & Paternoster, 2011; Thomas et al., 2017). Victims of multiple breaches may have more information about themselves available to offenders through underground markets and online data dumps, thereby creating generally greater opportunities for offenders to target individuals (Holt & Lampke, 2010; Thomas et al., 2017). This highlights the opportunistic nature that data breaches afford for offenders, and their willingness to capitalise on the uncertainty and anxiety created.
In terms of demographics, Indigenous status was positively correlated in both breaches. This finding is worth exploring in greater detail, to determine what (if any) reason appears to make Indigenous Australians a higher target of phishing in the aftermath of a data breach. It is unclear if Indigenous status is also associated with some other risk factors, such as differential technological skill or cybersecurity awareness. Further research is needed to examine these issues in detail to understand what factors drive differential phishing risk among Indigenous groups. The findings, however, justify the need for tailored education and awareness to Indigenous individuals and communities to highlight the elevated risk this study suggests they may experience. This is also relevant for other CALD communities, given the correlation between those who spoke another language and being targeted in the Medibank/AHM data breach.
While the current analysis focused heavily on the potential for phishing attempts received by data breach victims, there is a need to explore the relationship between appearing in a breach and being extorted in different ways. Offenders are known to blackmail and extort victims involved in data breaches, particularly when the breach is sensitive. A prominent example of this was the 2015 Ashley Madison data breach, which exposed the details of those allegedly subscribed to the extra-marital affairs website (Cross et al., 2019).
Blackmail attempts were made in relation to the Optus data breach (AFP, 2022) and it is likely that with the sensitive nature of the Medibank/AHM data, that extortion attempts may also have occurred. At a larger scale, it is estimated that Operation Guardian (AFP) linked 11,000 cybercrime incidents to the Medibank/AHM data breach (Victoria Police, 2023). Future research is needed to differentiate between risk factors for both phishing attempts and extortion related to a data breach to better understand these offences further.
The lack of statistical findings across many categories of data as well as demographic factors are important in and of themselves. It suggests that offenders who perpetrate phishing attacks in the aftermath of a data breach, are somewhat opportunistic and seeking to target all individuals through a blanket approach, rather than focussing on a select cohort or individual victims. The findings reinforce the need for public education and awareness of the need for vigilance in the aftermath of a data breach. In the case of Optus and Medibank/AHM, several agencies did put out media releases warning the public of increased phishing activity and the potential for attacks (ACMA, 2023; Scamwatch, 2022b; Scamwatch, 2022a).
The current findings support this as a means of creating public awareness, not only to data breaches, but also to other significant events whereby offenders are likely to leverage events for their own benefit. Financial service providers, charitable organisations, and companies alike could engage in targeted education campaigns regarding the risk of phishing increasing in the wake of data breaches or other incidents that may influence the odds of targeted phishing campaigns. Such information could help to improve general awareness and potentially reduce the odds of responding to phishing messages. A good example of this is the Australian Competition and Consumer Commission (ACCC) who release regular scam alerts, and who released a specific warning to the public in the aftermath of the Optus breach (ACCC, 2022). While these are arguably valuable for the general public, these findings also suggest a need to explore potential partnerships between government, banks, and other relevant organisations to better develop targeted support for those who are vulnerable to potential victimisation.
From a criminological perspective, this analysis found limited utility in the application of routine activities theory to account for phishing victimisation attempts following appearing in a data breach. This is somewhat in line with the broader literature on the application of this theory to phishing victimisation (e.g. Leukfeldt & Yar, 2016; Ngo & Paternoster, 2011; Van’t Hoff-de Goede et al., 2024). As a result, there is a need to further explore the utility of this theory in more specific contexts with phishing and vishing victimisation, whether in general incidents or targeted after data breaches to better understand is limitations and value.
Overall, this analysis highlights the limited ability of demographics and types of information to predict those targeted for further phishing attacks in the aftermath of these two large-scale breaches. This suggests offenders are more opportunistic than targeted in their efforts to gain further credentials from potential victims (Leukfeldt, 2014; Thomas et al., 2017). This finding largely supports the need for public awareness and education campaigns which advocate for a generalised vigilance against phishing attacks, as well as targeted campaigns in the aftermath of notable data breaches, to remind individuals of their vulnerability and need to be on alert (FTC, 2025; iDcare, 2022). Further, this analysis only examined those who recognised receiving a phishing attempt after these two data breaches. It would be beneficial to extend this analysis to determine who responded to these requests, with either personal details or money, to ascertain if any of the factors explored (across both demographics and type of information lost) better predict actual victimisation rather than just attempts.
Despite the overall utility of the models presented, there are several limitations that need to be addressed. The first is the non-representative nature of the data. The survey targeted a specific group of known data breach victims, those within Optus and/or Medibank/AHM. It may not be indicative of the broader group of victims across both data breaches. This is especially so, given the strong representation of Optus victims compared to Medibank/AHM. Future research is needed in the wake of large-scale data breaches in different nations to better understand this dynamic across place.
Second, this survey relies upon individuals acknowledging that they were in fact victims of the Optus and/or Medibank/AHM data breaches. While these were two significant data breaches which garnered a lot of public attention compared to many other breaches, there still may be those who were unaware of their exposure. While Australia does have mandatory reporting legislation (Gibson & Harfield, 2021) and both organisations were required to notify those affected, this may not have captured everyone.
Third, the self-report nature of this data relies upon individuals’ recollection of being targeted in the aftermath of the two data breaches. The data collection occurred approximately 7 months after the breach, capturing a relatively long period during which victims may have been targeted for phishing attempts. Future study is needed to capture a longer period of time, such as a full 12-month window after a given breach incident to assess phishing incidents longitudinally.
It also assumes that any phishing attempts were received by the respondents and directly associated with their appearance in these breaches. It is possible that respondents may have conflated a phishing message received as a result of appearing a prior breach, or independent of any breach incident, as being associated with either or both the Optus and Medibank/AHM breaches. Thus further study is needed with different data sources, such as tracking spam filtering and telecommunications data to assess any overall trends in messaging rates to triangulate phishing attempts post-breach incidents.
Fourth, there was an over sampling of Optus victims compared to Medibank/AHM. There is no discernible explanation for this, as both breaches affected a similar number of individuals across Australia overall. Given the ordering of the Optus data breach as first, there may have been an increased recognition of involvement in this breach compared to Medibank/AHM, but this cannot be accounted for. It aligns with the previous limitation of the self-reporting nature of this data and the reliance on individuals to self-identify as a victim of the Optus data breach, the Medibank/AHM data breach, or both.
Finally, this study did not capture a population of non-victims to compare against those who experienced the Optus and Medibank/AHM breaches. The lack of a comparative population makes it difficult to extrapolate differences among the overall population relative to those who experienced these breaches and were contacted about phishing attempts. Future research is needed that explores the issue of phishing attempt experiences among both victim and non-victim populations to better understand the prevalence and incidence of contacts, as well as significant differences in risk across demographic groups.
Footnotes
Acknowledgements
The authors acknowledge the Queensland University of Technology Centre for Justice who provided funding for the survey used in this article.
Ethical Approval
This project received ethics approval from Queensland University of Technology Human Research Ethics Committee approval #4011.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: this work was supported by the QUT Centre for Justice.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Data Availability Statement
The data used in this analysis is not available for sharing as per the project’s ethics approval.
