Abstract
The healthcare sector is in crisis as Internet-based actors attack the digital infrastructure necessary for operations. The growing complexity of systems and events on the world stage have given rise to a dynamic threat landscape that includes nation-states affiliates. Challenging even private industry, healthcare systems and budgets already strained by COVID-19 are struggling to cope. A pandemic style response with new investment and legislation is needed.
Introduction
Cyberattacks are offensive actions against computer systems, networks, and infrastructure typically intended to cause direct harm by crippling related systems, or through the theft, alteration, or destruction of data. As news of these have become commonplace, the word “cyber” has entered the public lexicon as a prefix to mean computer or Internet related. Although no industry has been spared, healthcare has been disproportionately affected with a recent study finding that 89% of U.S. hospitals had weathered one or more cyberattacks in 2022. In those cases of hospitals breached by the attack known as ransomware, the impacts included lost revenues, delays in treatment, and in 24% of cases, an increase in mortality rates. 1 In Canada, the average cost of a breach across all industries was $5.64 million (USD). For healthcare, the average was $10.1 million (USD), reflecting a 41.6% increase since 2020 and the highest cost by industry for 12 years running. 2
Indeed, healthcare has emerged as an apparent preferred target but response by our sector has been hampered by a failure to appreciate the nature and severity of this problem. Unlike the comparatively benign hacks and hackers of the preceding decades, modern cyberattacks and cyberthreat actors are highly advanced and destructive. The explosive and continued growth of interconnected and Internet connected systems have resulted in increased vulnerability to attack, but healthcare budgets for information technology have not kept pace. New investments to improve technological resilience and address cybersecurity challenges are urgently needed.
Further compounding this has been lagging responses at the regulatory and legislative levels. Just as with people, interconnected services and systems provide a means to spread cyberinfection between organizations through the compromise of trusted partners and supply-chain attacks. A bewildering variety of approaches and underlying technologies paired with persistent shortages for cybersecurity professionals makes it challenging for many organizations to understand how to protect themselves. Efforts by breached organizations to manage their own legal liability frequently prevent the timely release of critical information that others could use to proactively protect themselves. This must be met by regulatory requirements and legislation defining minimum standards for security and reporting responsibilities when a breach occurs.
As the frequency and scale of cyberattacks increase and the costs associated with a breach balloon, decisive and immediate action is needed. Cybersecurity is the healthcare sector’s pandemic, and a pandemic style response is needed.
Healthcare in crisis
Over the last 30 years, advancements in Information Technology (IT), mobile computing, and Internet connectivity have had a transformative effect on nearly all aspects of modern life. Modern medicine and the healthcare sector are almost entirely dependent on IT for everything from hospital operations to medical treatments. When that technology fails or is rendered inoperable by cyberattack, the effects are devastating.
In late 2019, the Canadian laboratory company LifeLabs announced it had paid an extortion demand to recover personal data of 15 million individuals after they were breached by the malicious software (malware) appropriately known as ransomware. 3 Once unleashed on a network, ransomware uses encryption to lock critical files making computer systems dependent on them unable to function until an extortion demand is paid to receive the decryption key. As with the LifeLabs attack, some variants also exfiltrate (steal) sensitive data for blackmail by the attackers.
Preceded by news throughout 2019 of hospitals around the world crippled by ransomware (including three in Ontario 4 within a span of weeks), LifeLabs was not the first laid low nor have they been the last. In the years following, other notable examples include: the Kaseya VSA breach on July 2, 2021 that also compromised more than 1,000 downstream organizations, 5 the Newfoundland & Labrador Centre for Health Information on October 30, 2021, 6 the Scarborough Health Network breach on January 25, 2022, and more recently the ransomware attack on Toronto’s Hospital for Sick Kids on December 18, 2022. 7
In truth, it is only the largest attacks and breaches that typically make the news as there are far too many examples to list otherwise. Other forms of cyberattacks such as e-mail enabled forms of fraud (phishing), infection by precursor malware through compromised web sites, and direct attempts to exploit network and software vulnerabilities are a daily occurrence for many healthcare organizations. Ransomware is arguably the worst, but all forms of cyberattack can have a very real impact on hospital operations even when they are successfully defended against. The healthcare sector is in crisis and needs help; acknowledging and understanding the problem is the first step.
The cyberthreat landscape
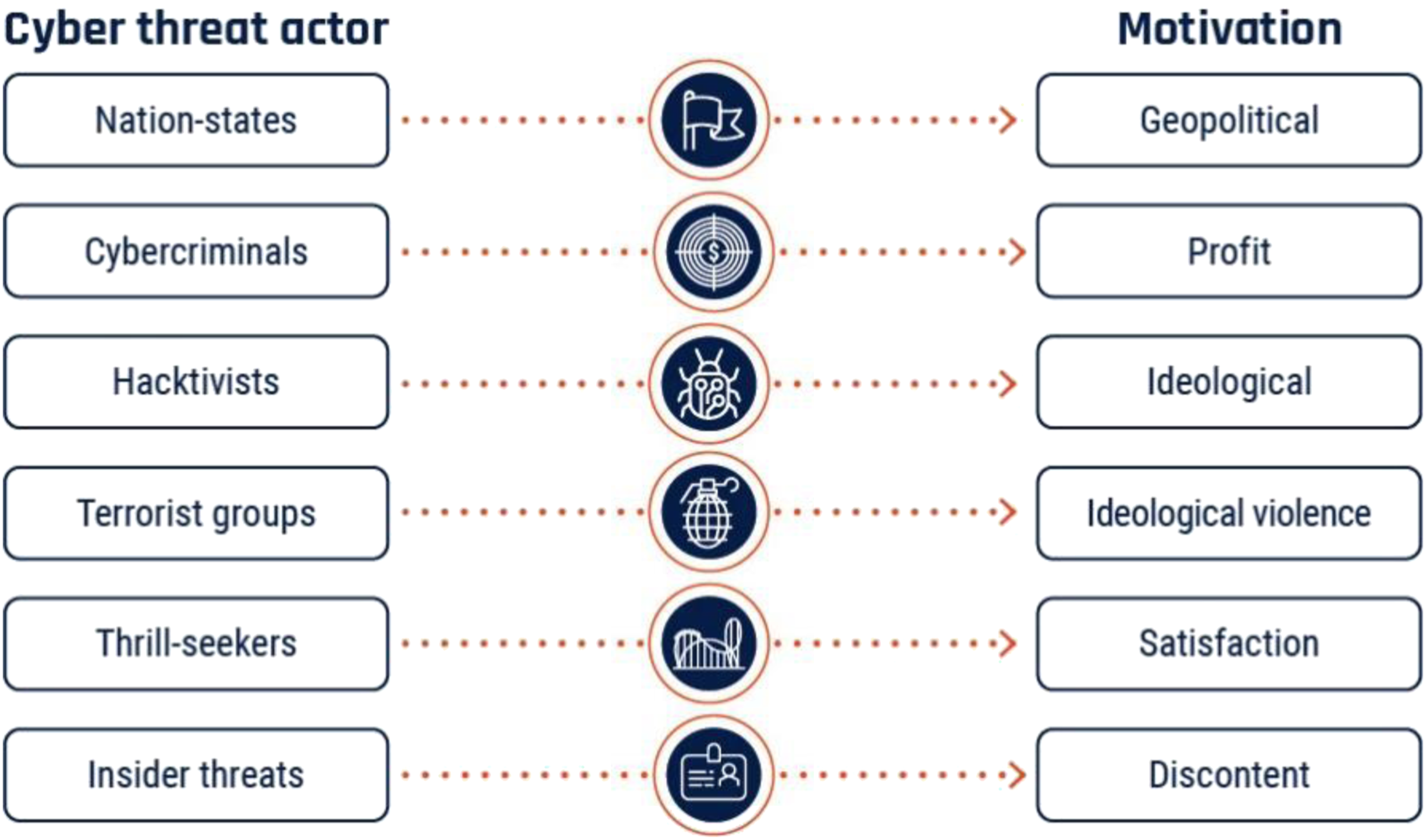
In simple terms, the cyberthreat landscape is the combination of attackers, the technologies (and industries) they target, and the prevalence of vectors for attack. While most people understand the concept of “hacking,” the word “hacker” conjures an image of a shadowy individual in a hoodie backlit by a computer monitor or at worst amateur hacker groups like Anonymous that became infamous in the 2000s. Both are just small parts of a broader ecosystem ranging from individual amateurs all the way up to professional cybercriminal syndicates, and nation-state agencies that are highly sophisticated and selective about whom they target. Cyberattacks have become big business with events on the world stage also leading to the weaponization of cyberattacks against perceived geopolitical rivals.
To help understand the risk to organizations across all sectors, security researchers typically categorize cyberthreat actors by their motivations for attack (Figure 1). Cyberthreat actors, Canadian Centre for Cyber Security.
8
Advanced persistent threats
Sitting at the apex are those groups also known as Advanced Persistent Threats (APTs), directly referring to their sophistication, ability to evade detection, and the longevity of both their campaigns and organizations.
The most well-known of the APTs are the ransomware gangs like North Korea’s Lazarus Group that was responsible for the worldwide WannaCry event in May 2017, 9 and the Russian ransomware groups Ryuk, Hive, and REvil that are responsible for many of the ransomware attacks referenced in this article. Espionage is the primary focus for other APTs such as Russia’s Cozy Bear that was responsible Solar Winds supply-chain attack in 2021 that compromised the likes of Microsoft, Mandiant, Intel, the U.S. Departments of Justice, Homeland Defense, and many, many more. 10 China’s HAFNIUM is the APT attributed to the 2021 Microsoft Exchange Server breach that compromised more than 250,000 on-premises e-mail servers. 11
Hacktivists, terrorist groups, thrill-seekers, and insider threats (amateurs)
The remaining classifications apply to amateur groups, but these too operate with advanced capabilities as resources from APTs do not take long to circulate downward. Even amateur hacker groups using low tech methods such as social engineering (fraud) combined with technical savvy still truly earn the moniker of “threat actor.”
The former Lapsus$ group made up entirely of teenagers compromised government and industry luminaries alike before being caught and arrested. 12 Ironically, this was due to sloppy operational security of their own. Some prolific APTs like LockBit even operate “ransomware as a service” 13 and directly provide tools and support to other groups through a profit-sharing arrangement.
Relevance to healthcare
Knowing
For example, Kingston Health Sciences Centre (KHSC) is comprised of two acute care hospitals, a regional cancer centre, and a research institute. It is a medium-sized organization with a significant annual budget and large workforce and therefore has broad exposure to the cyberthreat landscape.
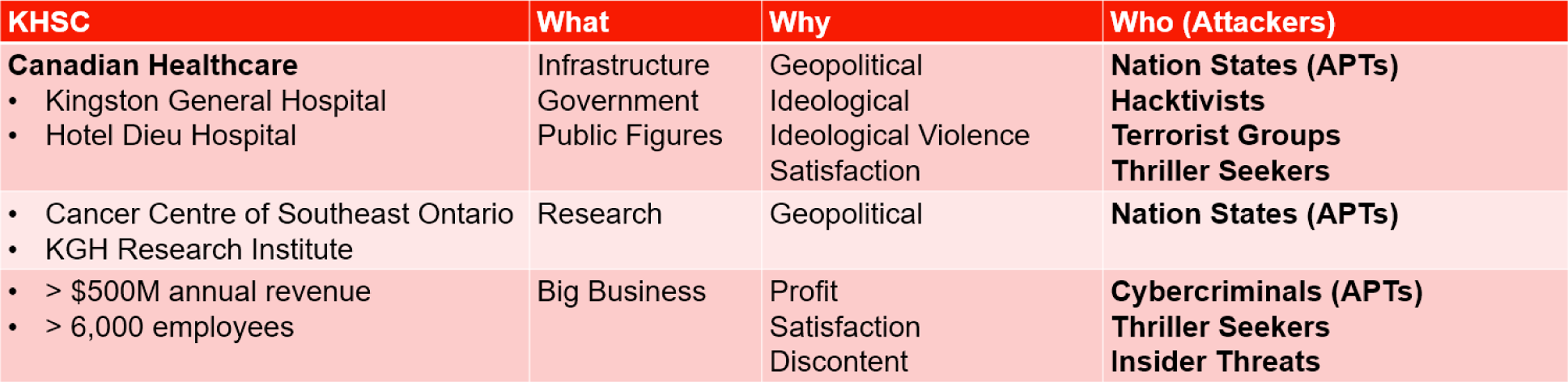
Even healthcare organizations too small to interest cybercriminal APTs also have broad exposure by virtue of being Canadian healthcare alone.
Despite having comparable technology footprints, IT spending by healthcare has consistently lagged behind the private sector. 14 A growing awareness of this fact along with the value of the data healthcare systems are charged with protecting in turn helps drive target selection by cyberthreat actors. Efforts to extend healthcare budgets through the use of computer software and hardware beyond their supported end of life have resulted in mixed technology environments that are increasingly vulnerable to attack. To put it another way, a rusty scalpel will still cut but with unacceptable risks of secondary damage and increased chances for infection. Rusty IT systems carry the same risk in this context. With the COVID-19 pandemic, increased and emergency funding were needed to help care for an ailing population. In this cyberpandemic, it is our healthcare systems themselves are at risk and the same response is needed. However, funding alone is an insufficient panacea; to ensure money spent on cybersecurity and related efforts are even and effective, they must be matched with equivalent action from healthcare regulators and government legislators.
Regulation and legislation
Spurred by the advent of the World Wide Web and new model of doing business “on-line” circa 1995, concerns about the collection, use, and disclosure of personal information by corporate and government entities started becoming widespread. This in turn drove the creation of privacy legislation throughout the world such as Canada’s Personal Information Protection and Electronic Documents Act (PIPEDA) that became law on April 13, 2000. Building upon The Privacy Act of 1983 that set rules for the Government of Canada’s collection, use, and disclosure of personal information, PIPEDA applied similar rules to the private sector. As it also allowed “substantially similar” provincial legislation to take precedence, PIPEDA was soon followed by bespoke private-sector legislation for British Columbia, Alberta, and Quebec. Further legislation governing the public sector’s collection, use, and disclosure Personal Health Information (PHI) was also passed by the provinces in the form of Ontario’s Personal Health Information Protection Act (PHIPA), New Brunswick’s Personal Health Information Privacy & Access Act (PHIPAA), and the identically named but separate Personal Health Information Acts (PHIA) of Nova Scotia and Newfoundland & Labrador. Like PIPEDA, they also went beyond just the use of PHI and established requirements for reporting and remediation when a breach or leak occurred. By enshrining these requirements in law, it forced organizations to prioritize privacy protections, arguably to the benefit of everyone who consumes on-line services today. But even as stronger privacy laws like the European Union’s General Data Protection Regulation 2.0 or Canada’s Bill C-27 emerge, no equivalent cybersecurity laws exist.
While the Criminal Code of Canada has long included prohibitions against illicit computer use, 15 they are only effective as a deterrent when they are enforceable. In the case of attacks conducted by hostile nation-state APTs, they offer no realistic deterrent value at all. Even when offenders are brought to justice, it does little to correct the harm caused and any legislation should therefore focus on prevention first. Canada made some progress in that regard when Bill C-26, “An Act respecting cybersecurity, amending the Telecommunications Act and making consequential amendments to other Acts,” received its second reading in parliament on March 27, 2023. The second part of the bill would enact the “Critical Cyber Systems Protection Act” (CCSPA) with the goal of creating a framework to protect “critical cybersystems.” Unfortunately, this law only applies to industries that the Minister in Council has proactively defined as “critical.” The CCSPA is currently limited to telecommunications, federal transportation systems, interprovincial energy infrastructure, nuclear energy, and banking. The bill has also been criticized for its lack of specificity about what is required for compliance, and a lack of substantial penalties for non-compliance. 16 Bill C-26 and the CCSPA are roughly comparable to The Privacy Act of 1983: a foundational first step, but otherwise not near enough.
As with privacy, cybersecurity legislation for organizations acting as custodians for sensitive data must clearly define the minimum standards for protection, set enforceable requirements for reporting when a breach occurs, and include effective penalties and remedies when reasonable efforts to comply are not made. Particularly for regulated and government industries like healthcare, requirements for reporting could help ensure timely notification and sharing of the information needed for individuals and organizations to protect themselves against similar attacks.
In the current landscape, breach notifications are slow unless stipulated in service contracts. For example, LifeLabs did not report their breach until Dec. 17, 2019, despite it having occurred months earlier. By the same token, reporting and intelligence-sharing of Indicators of Compromise (IOCs) across all industries are inconsistent or non-existent. IOCs detail the who, what, and how and a cyberattack; knowing the IOCs of an attack can help others proactively determine if they have been compromised and preventatively close those avenues of attack if they have not. In the healthcare sector where there is increasing interconnectedness between providers, this type of sharing is vital to stop cyberinfections from spreading. Newfoundland did not disclose their full IOCs until nearly two years after the attack in March 2023.
Specific restrictions against paying ransomware demands could see profit-motivated attackers reconsider their targets and related underground markets completely dry up. It would also prevent public funds from being used to fund further crime and war, such as North Korea’s missile program, which has generated billions of dollars from cybercrime. 17
Lastly, appropriately crafted cybersecurity legislation and regulatory requirements that is descriptive rather than prescriptive will ensure that it becomes a collective responsibility and help future-proof related efforts. No responsible organization today believes Privacy is a one-time effort, and the same must occur with cybersecurity. Even as we get a grasp on current technologies and the problems their abuse can cause new technologies are emerging that threaten to start the cycle over again. There is an understandable temptation to treat cybersecurity as a purely technological problem that can be solved with bespoke solutions, but history has shown this to be little more than an ineffective game of whack-a-mole—although in this case we feel more like the moles instead of the hammer.
Conclusion: Even Internet clouds can have silver linings
The WannaCry event of May 2017 was the first worldwide ransomware attack, affecting more than 300,000 computer systems in three days. In the world of healthcare, nobody was more affected that the United Kingdom’s National Health Service (NHS), suffering an estimated $116.4 million (USD) in losses and leading to 19,000 cancelled appointments. The NHS took it as a wake-up call and responded accordingly, with a follow-up report in 2020 noting that the NHS only suffered six successful ransomware attacks in the following three years since WannaCry compared to 203 successful attacks in the three years prior. 18
With Canada’s healthcare sector being continually targeted by extremely sophisticated threat actors that possess the capabilities and willingness to severely compromise and damage our critical infrastructure, this is our wake-up call. Each time a hospital or community healthcare provider is knocked off-line for days or weeks, the cost and impact to our communities is profound.
Effective treatment of disease often requires a medical intervention; Canada’s digital healthcare infrastructure is ailing, and a digital intervention is needed to secure our collective preparedness in the near future.
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
Ethical approval
Institutional Review Board approval was not required.
