Abstract
Cybersecurity constitutes a major concern for corporations. Given the disciplinary barriers that fragment existing research on cybersecurity, we conduct a systemic review of 203 empirical studies on the determinants and consequences of corporate cybersecurity risk across 12 disciplines. By consolidating multidisciplinary research, we develop a novel framework mapping the inter-relationships between the drivers of cybersecurity risk, impacts of cyberattacks, and potential feedback mechanisms enabling firms to learn from breaches to improve cybersecurity outcomes. We provide a taxonomy of both cybersecurity risk factors and impacts of cybersecurity breaches. Our study provides valuable insights to executives, investors, and regulators by enhancing risk awareness and enabling industry practitioners and policymakers to harness the power of academic research to strengthen corporate cybersecurity resilience.
JEL Classification:
Keywords
1. Introduction
Cybersecurity constitutes a growing concern for businesses worldwide, as demonstrated by high-profile breaches such as the Optus incident, which exposed data of approximately 10 million customers. Despite calls for increased corporate attention and investment in managing cybersecurity risk to protect stakeholder interests (Stupp, 2022), a key challenge remains the lack of comprehensive resources to enable corporate managers to understand the risks and assess the consequences of cybersecurity breaches. Current research on cybersecurity is scattered across multiple disciplines, such as computer science, engineering, and business fields (e.g. Chatterjee and Daniel, 2021; Schlackl et al., 2022; Spanos and Angelis, 2016). This disciplinary fragmentation hinders access to a unified body of knowledge on the impacts of cybersecurity risks and mitigation strategies, leading Falco et al. (2019) to advocate for a more interdisciplinary approach to cybersecurity research.
Our study responds to this call for interdisciplinary research by systematically reviewing empirical studies on cybersecurity risk and data breaches across numerous fields of study. We employ a three-pronged search strategy, comprising journal-specific, publisher-specific, and Google Scholar searches, to cover a broad range of disciplines with a focus on corporations and businesses. Our study addresses the dual needs for an interdisciplinary mapping of existing empirical evidence for researchers and a consolidated knowledge base to guide industry practitioners. 1 We fill this gap in the literature by synthesizing cross-disciplinary research and creating a comprehensive taxonomy of cybersecurity risk factors and impacts, offering novel insights for both academics and practitioners.
We examine cybersecurity research from two broad perspectives: (1) factors that determine a firm’s risk of cybersecurity breaches, and (2) the consequences of cyberattacks on breached firms. Our review of empirical evidence integrates these perspectives into a novel framework, offering insights and recommendations for academics, businesses, executives, and policymakers. We identify four categories of risk factors—managerial characteristics, firm operations, information technology (IT) practices, and broader institutional factors—which inform mitigation strategies to reduce cybersecurity risks. Once potential cybersecurity risk is realized upon the occurrence of a cybersecurity breach, we document six categories of direct and indirect impacts, specifically on stock market performance, corporate reputation, firm operations, IT practices, management, and industry peers. Our framework highlights the interrelations between prevention, disclosure, and crisis response strategies and identifies potential feedback mechanisms for firms to learn from past cyberattacks to enhance future cybersecurity.
Our study makes several contributions to the academic literature. First, this study provides the first comprehensive overview of the determinants and consequences of corporate cybersecurity risk by synthesizing interdisciplinary research, creating a valuable mapping of the existing research landscape and producing a consolidated knowledge base for future researchers. Second, our novel framework integrates fragmented cross-disciplinary literature, presenting a taxonomy of relevant risk factors and identifying complex interrelations among the determinants and impacts of cybersecurity breaches. Third, based on our conceptual framework and synthesized evidence, we highlight significant gaps in the extant literature and identify value-adding avenues for future research.
Beyond academic contributions, our findings offer practical insights for businesses, investors, regulators, and managers seeking to mitigate cybersecurity risk. We provide an accessible resource for practitioners to identify relevant risk factors and guide their efforts in reducing cybersecurity risk exposure. Our study also informs practitioners of the nature and extent of the consequences of cybersecurity breaches, aiding executives in making informed decisions about cybersecurity investments. In addition, we identify practical strategies to help protect shareholder wealth in the event of breaches, offering a valuable toolkit for practitioners to mitigate post-breach losses. Finally, from policymaking and regulatory perspectives, given the growing expectation for corporations to safeguard data privacy as a form of social responsibility, our evidence helps regulators assess the market-imposed penalties for cybersecurity failures and informs potential legislative or regulatory measures to incentivize improvements in cybersecurity practices.
The remainder of this article is organized as follows: Section 2 outlines the research methodology. Section 3 presents the conceptual framework. Sections 4 and 5 synthesize research findings. Section 6 discusses implications, future research directions, and concluding remarks.
2. Data and methodology
2.1. Review methodology
This study conducts a systematic review of empirical research on the determinants and impacts of cybersecurity risk for corporations. Our data-collection process, conducted in January 2023, involved three parallel search methods: (1) journal-specific searches within high-quality business journals to cover relevant business-discipline research; (2) publisher-specific searches across major platforms, including online archives of unpublished papers and conference proceedings; and (3) Google Scholar–wide searches to ensure comprehensive coverage of interdisciplinary literature.
First, we conduct keyword searches in specific business journals across finance, accounting, and management disciplines, using the following keywords: “cyber” OR “cybersecurity” OR “data breach” OR “data breaches”. 2 Our second parallel searching method involves conducting keyword searches on publisher websites—Cambridge University Press, Elsevier, HeinOnline, JSTOR, ProQuest, SAGE, SpringerLink, Oxford Academic, The University of Chicago Press, and Wiley—using the keyword combinations: “cyber” OR “cybersecurity” OR “data breach” OR “data breaches” AND (“corporate” OR “corporation” OR “business”). Since these publishing platforms cover diverse fields, including technical aspects of cybersecurity (e.g. programming or hardware technicalities), we use the “AND” condition to ensure the studies focus specifically on corporations. We also conduct these keyword searches using two online archives, arXiv (arxiv.org) and the Association for Computing Machinery (ACM) Digital Library, to include unpublished papers and conference proceedings, which constitute an important source of academic research in computer science and related fields. To ensure the quality of the conference proceedings and unpublished work included in this review, we employ an additional screening criterion: for unpublished papers, we include only recent articles within the past 5 years or those that are subsequently published; for conference proceedings, we require the conference to be ranked as A*, A, or “National: USA” in the Computing Research and Education (CORE) ranking. 3 Third, we search through Google Scholar using the same keywords as our publisher-specific searches to achieve comprehensive coverage. We manually screen the search results to ensure that each article has an apparent connection to the subject matter of this review. We eliminate duplicate results from these three parallel search methods. The initial searches have returned a total of 496 academic studies.
In the selection stage, we review the abstract of each article to determine its inclusion in the systematic review based on two inclusion criteria. First, the article must address either determinants/risk factors or consequences of cybersecurity risk for corporations or businesses. Second, the study must employ an empirical methodology supported by data analysis. Articles which solely contain commentary, policy recommendations, theoretical modeling, or doctrinal legal research are excluded. Applying these criteria, we exclude 293 articles, resulting in a final sample of 203 reviewed studies, as summarized in Table 1.
Data collection and selection.
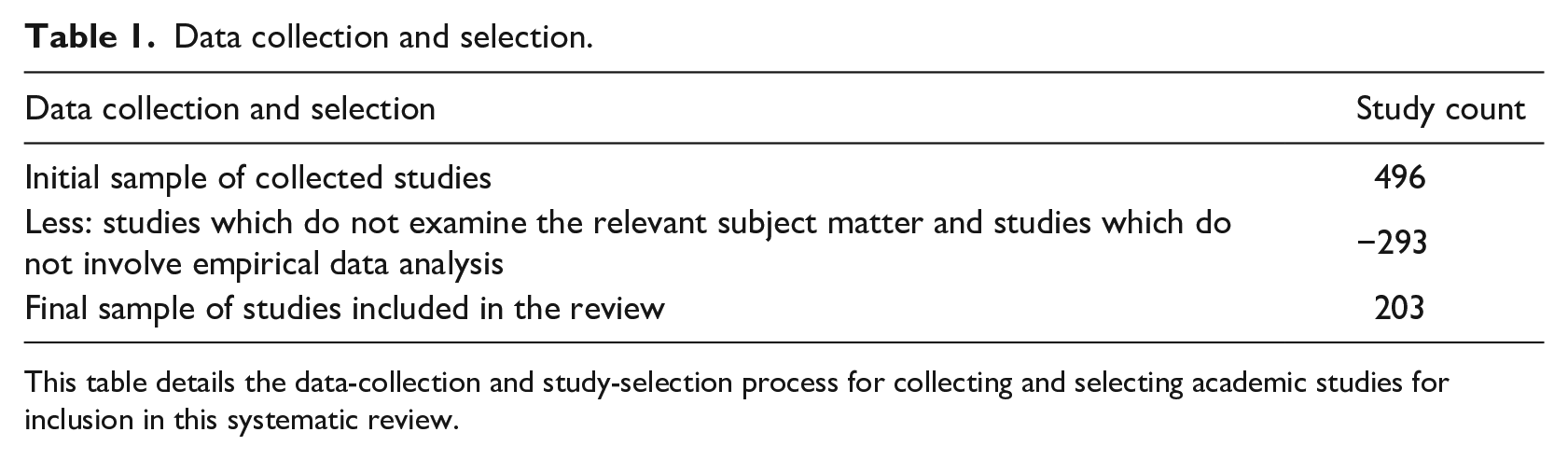
This table details the data-collection and study-selection process for collecting and selecting academic studies for inclusion in this systematic review.
2.2. Descriptive statistics
The sample of 203 studies is published in 90 peer-reviewed journals across 12 disciplines: accounting, business, computer science, economics, engineering, finance, information systems, interdisciplinary, law, management, marketing, mathematics, in addition to a small number of books, theses, and unpublished papers categorized as “unsorted.” Table 2 outlines the number of unique journals and studies from each discipline, with the top three disciplines being information systems (54 studies), accounting (30), and finance (26). Across geographic regions (detailed in Table 3), most studies use US data (163 studies or 80%), followed by multi-country or international data (13%). Other studies employ data from a variety of institutional settings including Canada, Europe (e.g. Germany, UK, France), and Asia (e.g. Japan and South Korea), covering a diverse range of interdisciplinary research evidence.
Discipline breakdown.
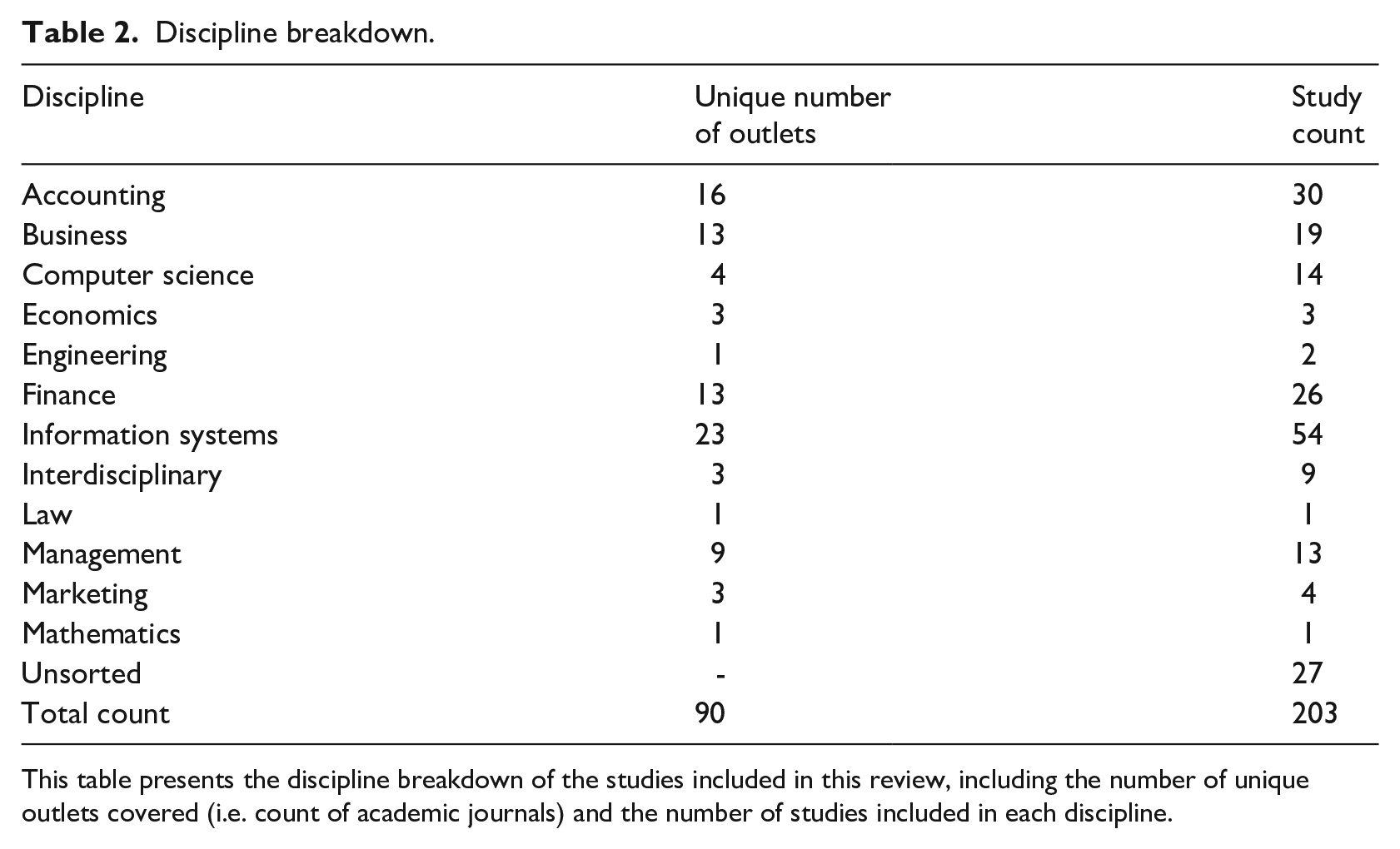
This table presents the discipline breakdown of the studies included in this review, including the number of unique outlets covered (i.e. count of academic journals) and the number of studies included in each discipline.
Country breakdown.
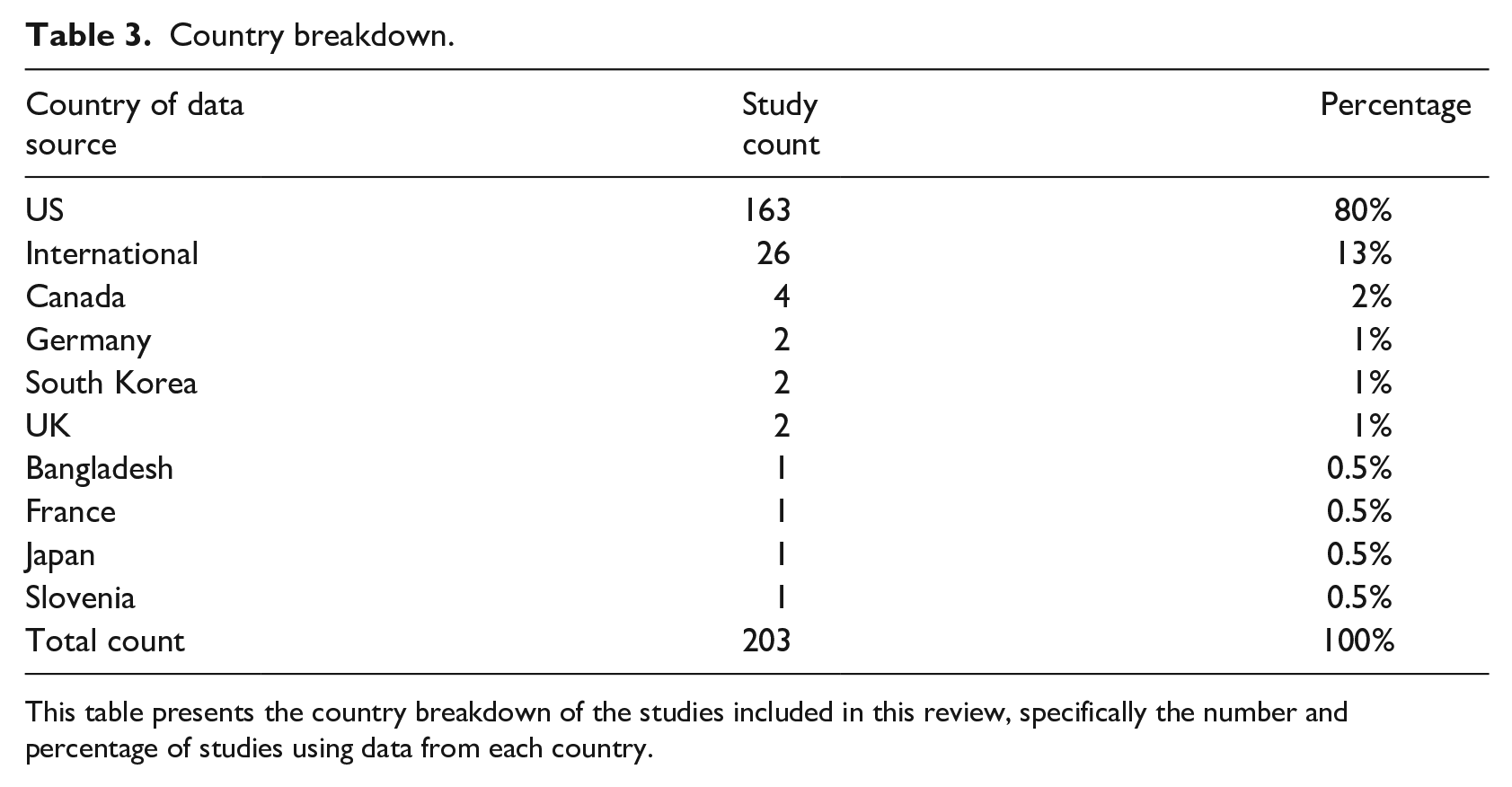
This table presents the country breakdown of the studies included in this review, specifically the number and percentage of studies using data from each country.
Figure 1 illustrates the trend in empirical research on corporate cybersecurity risk over recent decades. The data demonstrate that research interest in this field emerged in 2003 4 with a steady increase in the number of studies over time. 5 This trend reflects the growing interest in cybersecurity issues among researchers, businesses, and society.
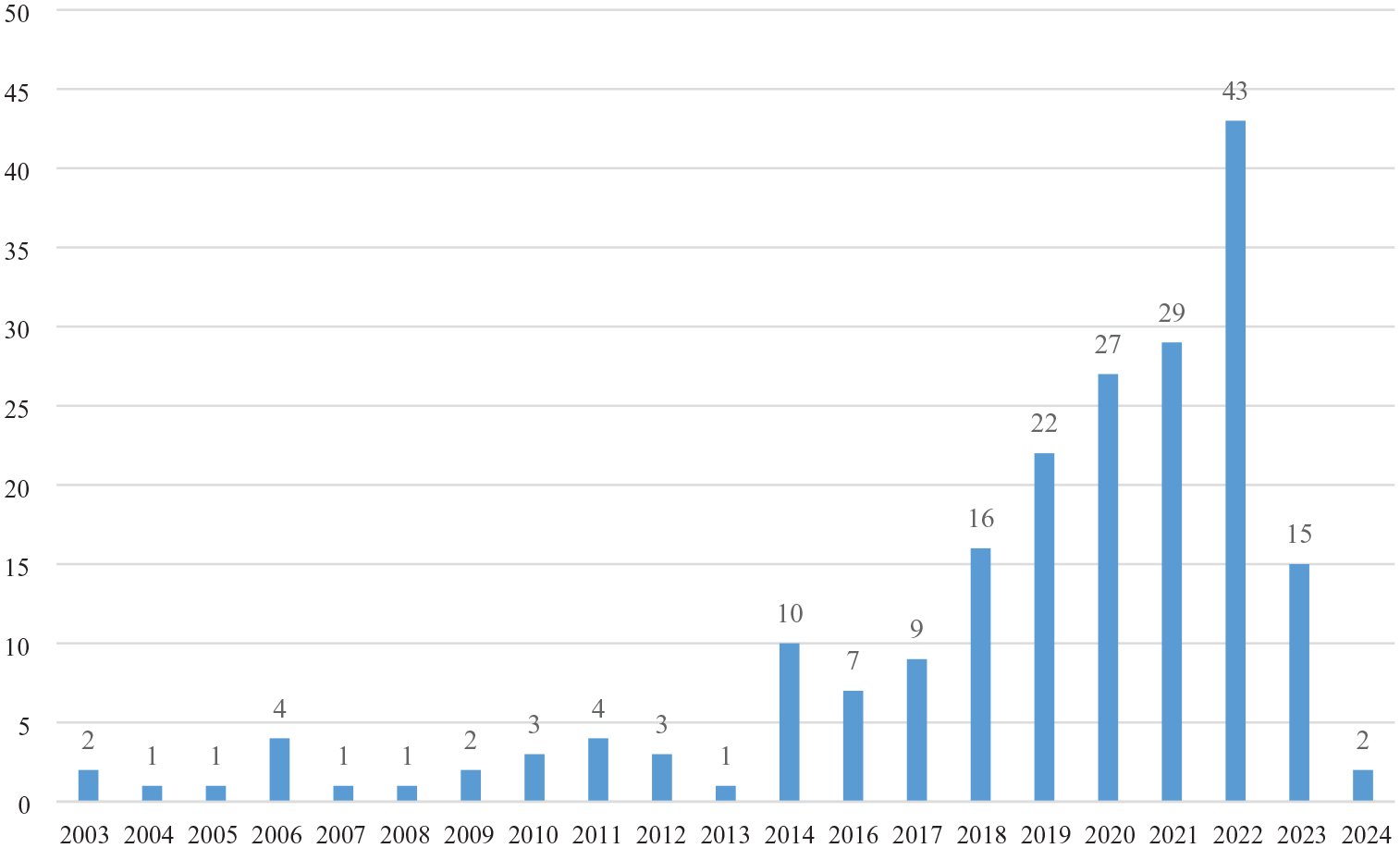
Number of publications during 2003–2024.
3. Conceptual framework
Cyberattacks on corporations can be driven by a range of strategic or financial motives. While cyberattacks are often carried out for financial gains, such as extorting ransom or selling stolen data to third parties, attackers may also be motivated by strategic objectives, such as industrial espionage or thefts of valuable intellectual property (Vrhovec and Markelj, 2024), political activism, and disruption and sabotage by targeting critical infrastructure (Pattnaik et al., 2023). Common forms of cyberattacks include malware, phishing, and spoofing attacks (Haruna et al., 2022). Malware and phishing aim to access confidential data with resalable or strategic proprietary value (Gordon et al., 2015b; Sarker et al., 2024), whereas spoofing involves impersonating users to gain unlawful access (Haruna et al., 2022). In the context of these relevant motives driving cyberattacks, our article reviews evidence on the determinants and consequences of cybersecurity for corporations targeted by these attacks.
We synthesize existing research and develop a novel conceptual framework to outline key avenues of investigation and empirical evidence. Previous studies mainly explore corporate cybersecurity risk from two perspectives: one strand of research investigates factors that predict a firm’s exposure to cybersecurity risk (the “determinants”), and the other strand examines the impacts of cyberattacks on the breached firms (the “consequences”).
Figure 2 illustrates our conceptual framework mapping the relationship between these two strands of literature. The first strand explores factors at the firm, management, and institutional levels that mitigate or exacerbate corporate cybersecurity risk, which is typically measured as the likelihood or frequency of encountering cybersecurity breaches. We categorize these factors into four areas that influence a firm’s exposure to cybersecurity risk: (1) executive and director attributes, (2) firm characteristics and policies, (3) IT practices and procedures, and (4) broader institutional factors beyond the firm’s control. Figure 2 shows that these multifaceted factors collectively impact on a firm’s cybersecurity risk. The second strand of research examines the consequences of cybersecurity breaches on the attacked organizations, as breach events are considered realizations of potential cybersecurity risk. The impacts of cybersecurity breaches fall into six categories: stock market consequences, reputational damage, operational impacts, IT practice changes, managerial repercussions, and industry peer effects. Cybersecurity breaches can lead to (1) immediate negative stock price reactions due to investors’ concerns about the associated economic losses, both direct and indirect, which include (2) reputational damage with stakeholders, (3) impacts on firm operations and policies, (4) changes in IT practices, and (5) managerial consequences such as executive turnover and board restructuring. In addition, we observe (6) repercussions for non-breached peer firms in industry spillover effects. The evidence shows that cybersecurity breaches impose extensive and enduring effects on not only the breached firms but also on their stakeholders and competitors.
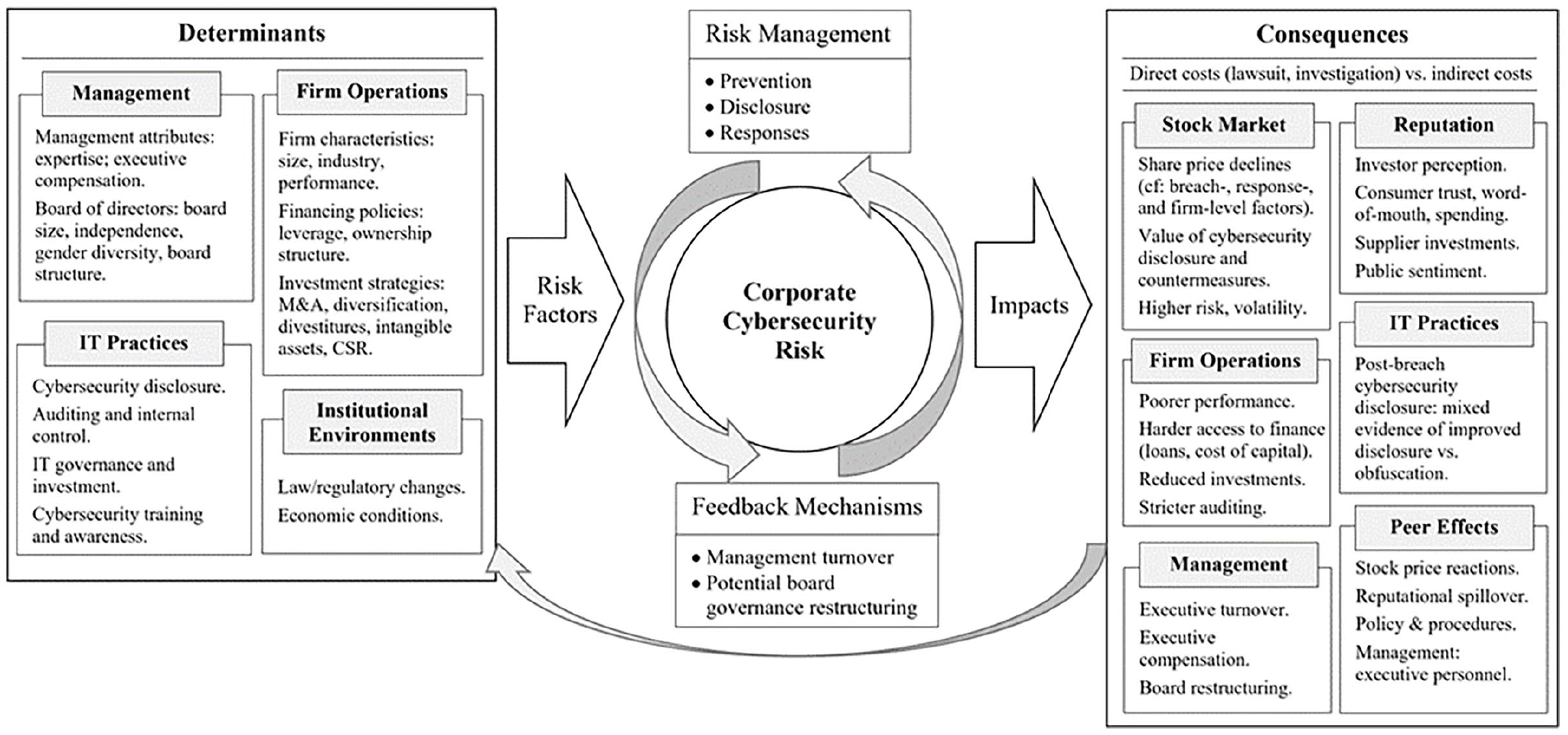
Conceptual framework.
Under this framework in Figure 2, we conceptualize a potential feedback loop linking the determinants and consequences of cybersecurity risk. As firms gain awareness of cybersecurity risk factors and understand the consequences of breaches, they are motivated to engage in cybersecurity risk management, including prevention, disclosure, and post-breach response strategies, aimed at reducing the likelihood and minimizing the impacts of breaches. We posit that experiencing a cybersecurity breach can lead a firm to reassess its risk exposure and implement remediation strategies aimed at preventing future attacks. These feedback mechanisms allow firms to learn from past cybersecurity breaches, improve cyber governance capabilities and practices, and strengthen defenses to reduce future risk exposure, thereby completing the feedback loop.
4. Determinants of cybersecurity risk and practices
In this section, we review research evidence on determinants of corporate cybersecurity risk. Prior studies commonly use the occurrence of cybersecurity breaches as an empirical proxy for a firm’s cybersecurity risk (e.g. Chen et al., 2022; Ettredge et al., 2018; Hughes et al., 2023; Lending et al., 2018). Studies also investigate corporate cybersecurity disclosure as a key cybersecurity practice (e.g. Radu and Smaili, 2022). We categorize myriad factors that determine corporate cybersecurity risk and outcomes into four groups: first, attributes of managers and directors play a role in shaping cybersecurity practices and risk. Second, firm characteristics and policies are relevant. Third, IT policies and practices are pertinent to determining cybersecurity risks. Fourth, broader institutional and environmental factors such as economic conditions and regulatory changes also impact on firm cybersecurity risk. Each category is detailed in the following sections.
4.1. Management attributes
4.1.1. Top management team
Corporate managers oversee cybersecurity strategies, making decisions on investment and shaping policies and practices. IT expertise in the top management team (TMT) adds value: chief executive officers (CEOs) and chief financial officers (CFOs) with IT expertise are more likely to prioritize cybersecurity risk mitigation and identify critical investment to prevent breaches (Haislip et al., 2021). Firms may also appoint IT executives, such as chief information/technology officers (CIO/CTOs): some evidence shows IT executives in the TMT reduce breaches, especially if they receive higher compensation (Haislip et al., 2021; Kwon et al., 2013), while other research suggests that firms with CIOs experience more breaches (Smith et al., 2021), which may be attributable to the possibility that firms with higher inherent cyber risk are more likely to appoint CIOs. The gender and age of information security decision-makers also affect threat awareness (Vrhovec and Markelj, 2024). Evidence on the impact of CIO turnover after breach remains inconclusive: some studies document reduced future risk after CIO turnover (Li et al., 2021b), while others find no significant changes (Say and Vasudeva, 2020). Overall, while IT expertise in managerial teams generally enhances cybersecurity, the role of IT-specific executives requires further investigation.
4.1.2. Board of directors
Boards of directors are crucial in determining corporate cybersecurity practices and risk (Hartmann and Carmenate, 2021). More effective boards with smaller size (Lending et al., 2018) and financial expertise (Lending et al., 2018) 6 are linked to reduced breach risks. Conversely, firms with busy directors (Hsu and Wang, 2021) and separate technology committees (Higgs et al., 2016) face higher exposure to breaches. Interviews with corporate directors reveal that directors’ cybersecurity expertise is important to providing effective oversight (Lowry et al., 2021), particularly when serving on audit committees (Chen et al., 2022; Thiéry and Fass, 2020). Supporting this view, survey evidence links directors’ self-assessed levels of IT expertise to more mature risk management practices (Vincent et al., 2019).
Cybersecurity disclosure, as a key corporate practice, improves a firm’s information environment and tends to be more extensive under effective board governance, as represented by higher independence (Héroux and Fortin, 2022; Mazumder and Hossain, 2023; Smaili et al., 2023), gender diversity (Mazumder and Hossain, 2023; Radu and Smaili, 2022), technical expertise (Héroux and Fortin, 2022; Smaili et al., 2023), cybersecurity subcommittees (Héroux and Fortin, 2022), and higher shareholder confidence (Smaili et al., 2023). In contrast, firms with entrenched directors tend to disclose less cybersecurity information (Héroux and Fortin, 2022). 7 Overall, executives and board directors significantly influence corporate cybersecurity risks through their impact on cybersecurity investment, practices, and disclosure.
4.2. Firm characteristics and policies
4.2.1. Firm characteristics and operations
Different companies face varying levels of cybersecurity risk due to their operations and characteristics, such as size, industry, and financial success. Larger firms, including those on the Fortune 500 list, are more often targeted by hackers in cyberattacks (Kamiya et al., 2021; Pei et al., 2020) and generally spend more on cybersecurity (Aldasoro et al., 2022) and build greater digital trust (Kluiters et al., 2023). However, some researchers find smaller firms face higher data-breach risks (Keppo and Niemela, 2021). Industry also affects cybersecurity risk, with finance (Aldasoro et al., 2022), wholesale & retail, service, transportation & communication sectors (Kamiya et al., 2021), and less competitive industries being more frequently targeted (Kamiya et al., 2021). Furthermore, financially successful firms (e.g. with higher stock valuation and lower financial constraints) are more prone to cyberattacks (Kamiya et al., 2021).
4.2.2. Financing policies
Corporate financing policies and ownership structure significantly affect cybersecurity risks and disclosure practices. Firms with greater financial risk (higher leverage ratios) are more likely to experience data breaches (Pei et al., 2020). Cross-listed firms are found to provide less cybersecurity disclosure (Barry et al., 2022).
4.2.3. Investment strategies
Corporate investment policies and strategies impact cybersecurity risks. Rapid expansion through mergers and acquisitions (M&A) increases vulnerability to data breaches (Tanriverdi et al., 2019), while diversification (Wang and Ngai, 2022) and divestitures reduce data breach risk (Say and Vasudeva, 2020; Tanriverdi et al., 2019). Firms that possess more intangible assets, such as trade secrets and confidential contract information (Ettredge et al., 2018; Hughes et al., 2023), face higher cyberattack risks (Kamiya et al., 2021; Pei et al., 2020), suggesting that hackers deliberately target companies for their valuable confidential information, consistent with theoretical expectation (Gordon et al., 2015b), especially when the firms are younger, smaller (with fewer employees), and operating in less-concentrated industries (Ettredge et al., 2018).
The impact of corporate social responsibility (CSR) on cybersecurity risk remains debated. One perspective suggests that CSR reduces cyberattack risk by fostering societal goodwill, supported by evidence that firms with stronger CSR engagement in certain areas such as environmental and product safety face fewer cyberattacks (Lending et al., 2018), whereas firms committing social irresponsibility are more prone to cyberattacks (Xu et al., 2022). In contrast, a competing view suggests that excessive CSR investment, especially in areas unrelated to core operations, may increase cybersecurity risk (D’Arcy et al., 2020).
4.3. IT process-related factors
Corporate IT policies and practices are crucial to mitigating cybersecurity risks. Research has examined firm-level IT policies and procedures from four perspectives: (1) cybersecurity disclosure, (2) auditing and internal control, (3) IT governance and investment, and (4) cybersecurity training and awareness.
4.3.1. Cybersecurity disclosure
Cybersecurity disclosure allows investors and stakeholders to assess firm risk and helps firms attract investors at a lower cost, especially when supported by third-party assurance (Elmawazini et al., 2022; Frank et al., 2019). The quality and quantity of such disclosures vary widely (Andrew et al., 2023), and methods for measuring disclosure are still evolving (Ramírez et al., 2022). Firms facing regulatory deadlines make faster but less detailed disclosure (Ashraf et al., 2022). Research on whether more disclosure mitigates or exacerbates data breach risk has produced mixed evidence: some studies link more disclosure to higher breach risks (Li, 2017; Li et al., 2018; Peng and Li, 2022), whereas others find no significant correlation (Arora et al., 2006).
4.3.2. Auditing and internal control
Auditing and internal control help reduce cybersecurity risks, as internal control weaknesses within corporate IT systems can lead to such risks (Gordon et al., 2008; Westland, 2020). External auditors play a vital role (Liu, 2020; Westland, 2022). Auditors with experience in data breaches can help reduce a firm’s breach risk (Liu, 2020). Lower-quality audits, characterized by narrower scope and lower fees, are associated with higher credit card fraud (Westland, 2022), indicating that thorough auditing helps prevent cybersecurity misconduct. Firms with past cyberattacks incur higher audit fees, which lead to fewer subsequent breaches (Li et al., 2020), underscoring the importance of external audits in identifying and addressing cybersecurity vulnerabilities.
Internal auditing also supports corporate risk management (Islam et al., 2018; Steinbart et al., 2012), although its effectiveness in preventing cyberattacks remains under investigation (Slapničar et al., 2022). Management support is necessary for internal audits to improve IT security functions, identify internal control weaknesses, and improve breach detection (Steinbart et al., 2018). 8
4.3.3. IT investment and governance
IT security investment provides defense against cybersecurity risks (Aldasoro et al., 2022; Angst et al., 2017; Li et al., 2021a). IT investments are influenced by firm-level economic decision-making (Gordon and Loeb, 2002; Gordon et al., 2015a, 2015c). Companies weigh the investment cost against the nature of the information being protected, including its vulnerability and the potential losses from breaches (Gordon and Loeb, 2002; Gordon et al., 2015b). Firms are motivated to invest in IT security to protect their strategic proprietary information (Gordon et al., 2015b). Given that cybersecurity breaches have broader societal impacts beyond the affected firm (Gordon et al., 2015b), regulations may be needed to address underinvestment in IT security (Gordon et al., 2016; Gordon et al., 2015c).
Firms invest more on cybersecurity when they have formal IT security policies (Tanaka et al., 2005), view cybersecurity as important to internal control (Gordon et al., 2018), and when prioritized by the CFO (Fleischman et al., 2022). Higher cybersecurity investments lead to lower breach risks (Aldasoro et al., 2022; Angst et al., 2017; Li et al., 2021a) and reduce costs of future incidents (Aldasoro et al., 2022). However, merely increasing IT security usage does not necessarily reduce breaches, as effective integrating of IT security into processes is essential, whereas symbolic adoption diminishes IT security effectiveness and increases breach risks (Angst et al., 2017). Breach risks are also reduced by centralized IT governance (Liu et al., 2020) and investing in anti-virus and intrusion detection systems (Li et al., 2021a). Finally, transparent data management can mitigate the negative impacts of customer data vulnerability (Martin et al., 2017).
4.3.4. Cybersecurity training and awareness
Human behavior remains a major source of cyber risk (Eling and Wirfs, 2019), underscoring the importance of understanding cybersecurity in the full context of business operations (Tonkin et al., 2023). Employee errors and portable media/device usage are primary causes of data losses (Ayyagari, 2012; Osei Yeboah-Boateng and Boaten, 2016). Cybersecurity training and awareness programs strengthen defenses (Chatterjee and Daniel, 2021), enhance IT self-efficacy (Thangavelu et al., 2021), and reduce breach risks (Kweon et al., 2021).
4.4. Institutional and environmental factors
Institutional and environmental factors, such as geographical location (Ma et al., 2022), government regulations (Gordon et al., 2006; Klein et al., 2022), and macroeconomic and geopolitical conditions (Png et al., 2008), affect corporate cybersecurity risks and practices. Cybersecurity disclosure increases in response to regulatory changes such as the Sarbanes-Oxley Act (Gordon et al., 2006) and Securities and Exchange Commission (SEC) comment letters on cybersecurity (Calderon and Gao, 2022). Regulations such as the General Data Protection Regulation (GDPR) lead firms to add IT experts to their boards (Klein et al., 2022).
5. Consequences of cybersecurity risk and data breaches
Technological advances, coupled with increased networks reliance and data digitalization, have heightened corporate exposure to cybersecurity risk (Uddin et al., 2020). This section reviews the evidence on the impacts of cybersecurity breaches (e.g. Chatterjee and Daniel, 2021; Schlackl et al., 2022), which impose both direct and indirect costs on the attacked firms (Caldwell, 2014; Dongre et al., 2019; Gardner, 2014). Direct costs include legal fees, investigation expenses, and the costs of supporting affected customers (Dongre et al., 2019). Indirect costs encompass long-term reputational damage, increased operational costs, and decreased productivity, as stakeholders penalize firms in the process of repeated contracting (Caldwell, 2014; Kamiya et al., 2021). Updating IT systems and security to prevent future breaches can also be costly (Dongre et al., 2019; Kamiya et al., 2021). Cybersecurity breaches often trigger stock price declines due to these various costs and the overall financial impact on shareholder wealth (e.g. Kamiya et al., 2021). Estimating the financial cost of data breaches varies widely (Romanosky, 2016), from $7.2 million (Ayyagari, 2012) to $43.49 million (Eling and Wirfs, 2019). Variations may stem from different cost definitions and firm- and incident-specific factors, such as existing cybersecurity weaknesses (Eling et al., 2022), breach scale (Aldasoro et al., 2022), and information accessed (Poyraz et al., 2020; Romanosky et al., 2014).
We discuss each category of the impacts of cybersecurity breaches in the following sections: stock market consequences (Section 5.1), reputational damage (Section 5.2), effects on firm operations and policies (Section 5.3), changes in IT practices (Section 5.4), managerial repercussions (Section 5.5), and industry spillovers (Section 5.6).
5.1. Stock market consequences
Cybersecurity breaches commonly lead to negative stock price reactions (Ali et al., 2021; Spanos and Angelis, 2016), reflecting investors’ assessment of the economic losses from both direct and indirect impacts of a breach. This section reviews evidence on the nature and extent of firm value losses and synthesizes the factors that exacerbate or mitigate these valuation declines.
5.1.1. Stock price reactions to data breaches
Cybersecurity breaches generally lead to stock price declines. 9 Market reactions range from small declines of less than 0.3% (Richardson et al., 2019) to significant losses of 2.1% (equivalent to $1.65 billion per breach) (Cavusoglu et al., 2004), with most evidence falling somewhere in between (e.g. 0.84% found by Kamiya et al., 2021). As the magnitude of stock price reactions varies widely and is context-dependent, Section 5.1.2 will review the factors that influence the extent of market reactions to cybersecurity breaches.
5.1.2. Determinants of stock market reactions
We synthesize empirical evidence on the factors influencing stock price reactions to cybersecurity breaches, which we categorize into four groups: (1) cyberattack incident characteristics, (2) corporate responses, (3) firm-specific characteristics, and (4) macro-/environmental or temporal factors beyond firms’ control.
First, breach-related factors significantly predict stock market reactions, including the type, preventability, and scale of the cyberattacks. Different cyberattacks types carry varying risks (Eling and Loperfido, 2017; Malavasi et al., 2022), with investors responding more negatively to denial of service (Gordon et al., 2011; McShane and Nguyen, 2020; Yayla and Hu, 2011) and phishing (McShane and Nguyen, 2020), compared with unauthorized data access. 10 The nature of the stolen information is also crucial: losses of customer personal data trigger more severe reactions (Hogan et al., 2020; Masuch et al., 2022), especially confidential (Campbell et al., 2003; Tanimura and Wehrly, 2009) or financial information (Kamiya et al., 2021; McShane and Nguyen, 2020; Peng et al., 2023). The preventability of the attacks also affects market reactions, with worse reactions for preventable (Morse et al., 2011) and second-time breaches (Peng et al., 2023). 11 Larger-scale attacks affecting more customers and high-profile attacks covered by major news outlets lead to worse market reactions (Bolster et al., 2010; Chatterjee et al., 2019).
Second, how firms respond to cyberattacks, particularly the timing and response strategies, significantly affects stock market reactions. Timely communication is generally preferred (Knight and Nurse, 2020) and mitigates market value losses (Amir et al., 2018; Song et al., 2017), whereas delaying or withholding information leads to worse market reactions (Ashraf et al., 2022; Gatzlaff and McCullough, 2010). Corporate response strategies also play a crucial role: 12 apology, excuses, and denial are ineffective in curbing stock price declines (Gwebu et al., 2018; Masuch et al., 2022). In contrast, strategies such as image renewal, ingratiation, and justification are more effective at cushioning stock price declines (Gwebu et al., 2018). Social media exposure, especially announcement via a company’s Twitter account (Rosati et al., 2019a), can worsen market reactions to breaches. 13 Firms’ remedial actions after post-breach, such as replacing their CEOs, can mitigate the market reactions to subsequent breaches (Peng et al., 2023).
Third, firm-level factors impact market reactions to cyberattacks. Generally, stock markets react less negatively to breaches at larger firms (Gatzlaff and McCullough, 2010) and subsidiaries (Gatzlaff and McCullough, 2010), but more negatively for older (Kamiya et al., 2021) and more highly-valued firms (Gatzlaff and McCullough, 2010). Firm industry is also relevant: worse market reactions occur in retail and service industries (Hogan et al., 2020; Kamiya et al., 2021; McShane and Nguyen, 2020), financial firms (Tweneboah-Kodua et al., 2018), 14 and less-competitive industries (Grundy et al., 2022). Evidence on technology firms is mixed: some find stronger reactions to breaches (Pirounias et al., 2014), 15 while others report weaker reactions due to their superior capacity to handle cyberattacks (Tweneboah-Kodua et al., 2018). Corporate governance can mitigate market reactions to data breaches: firms experience less negative reactions when their boards have technology committees (Higgs et al., 2016) and pay more attention to risk management (Kamiya et al., 2021). Corporate reputation also cushions post-breach stock price declines (Gwebu et al., 2018). Firms suffer worse market reactions if the breaches decrease future sales growth (Kamiya et al., 2021), if they have higher put-call ratios (Piccotti and Wang, 2022), or if breach announcements are accompanied by short-selling activities (Wang et al., 2022).
Fourth, macro-environmental factors also influence the magnitude of market reactions to cybersecurity breaches, which have changed over time (Gordon et al., 2011; Hovav et al., 2017; Kannan et al., 2007). Some researchers find stronger market reactions in more recent years (Gatzlaff and McCullough, 2010), whereas others report diminished reactions in recent years as investors become desensitized to cyberattacks (Yayla and Hu, 2011). Some evidence shows a non-linear U-shaped trend in market reactions over time (McShane and Nguyen, 2020). Investor perceptions of cyberattacks are influenced by major events, such as the dot-com bubble and September 11 attack (Gordon et al., 2011; Kannan et al., 2007), 16 adoption of privacy laws, and increased public awareness of data protection (Hovav et al., 2017).
5.1.3. Cybersecurity practices and firm value
Firms can mitigate the negative stock market impact of cybersecurity breaches by voluntarily disclosing cybersecurity risk information. As digital trust is positively valued by investors (Kluiters et al., 2023), proactive cybersecurity disclosure enhances market valuation (Barry et al., 2022; Gordon et al., 2010; Tsang, 2020) and protects firm value in the event of breaches (Chen et al., 2023; Jasa, 2020). Cybersecurity countermeasures such as improvements in awareness and anti-identity theft tools are also positively valued by investors (Berkman et al., 2018; Bose and Leung, 2019).
5.1.4. Other stock market consequences
Cybersecurity breaches and disclosure affect firms’ stock market performance beyond short-term price impacts. Breached firms typically experience worse long-term performance (Chang et al., 2020; Hogan et al., 2020; Ko et al., 2009), while firms facing higher cybersecurity risk are expected to generate higher long-term returns to compensate for the risk (Florackis et al., 2023; Jiang et al., 2022). Data breaches prompt the market to reassess a firm’s cybersecurity risk, significantly increasing stock price volatility (Alhusaini et al., 2022; Corbet and Gurdgiev, 2019; Goodell and Corbet, 2022), risk (Alan et al., 2021; Malliouris and Simpson, 2020), trading volume (Mitts and Talley, 2019; Rosati et al., 2017; Tosun, 2021), liquidity (Tosun, 2021), and information asymmetry (Alhusaini et al., 2022; Rosati et al., 2017). Short selling around breaches amplifies negative stock price reactions (Wang et al., 2022). In some instances, hackers use stolen information to engage in insider trading, affecting stock prices (Akey et al., 2022).
5.2. Reputational impacts
Cybersecurity risk impacts not only corporations but also their stakeholders, including investors, customers, suppliers, employees, and communities (Confente et al., 2019; Hovav and Gray, 2014; Tanimura and Wehrly, 2009). Cybersecurity breaches can damage corporate reputation by diminishing stakeholder trust. Following cyberattacks, stakeholders negatively reassess the breached firm and impose penalties in the process of repeated contracting, leading to increased future costs.
5.2.1. Investors
Data breaches lead to a decline in both shareholder and bondholder wealth (Iyer et al., 2020). Experimental research shows that investors view breached firms less favorably (Juma'h and Alnsour, 2021), even when firms self-disclose breach information (Cheng and Walton, 2019). To counteract this negative perception, firms can engage cybersecurity assurance services, which positively influence investor assessments (Perols, 2023; Perols and Murthy, 2021).
5.2.2. Customers
Cybersecurity breaches often involve unauthorized access to private customer data, leading to customer dissatisfaction (Martin et al., 2017), loss of trust (Bansal, 2014; Nofer et al., 2014), impaired brand capital (Hsu et al., 2022), negative word of mouth (Labrecque et al., 2021; Zhang et al., 2019), decreased consumer spending (Janakiraman et al., 2018), and switching to other businesses (Ablon et al., 2016; Labrecque et al., 2021). Customer fear and anger significantly affect post-breach stock market valuation losses (Chatterjee et al., 2019). Customers also change data-related behaviors post-cyberattack, such as falsifying personal information (Labrecque et al., 2021) and undertaking protection actions by monitoring files and freezing access to credit reports (Mikhed and Vogan, 2018). However, some studies report increased brand capital (Makridis, 2021) and minimal impact on customer personal security intentions (Curtis et al., 2018).
Firm responses to data breaches are crucial in mitigating reputational damage. Apologies from CEOs can restore customer trust (Bansal, 2014), while denial of responsibility harms reputation (Kuipers and Schonheit, 2022), and blame attribution has little impact (Angelis and Miller, 2021). Consistent and timely compensation and rectification strategies can aid in reputational recovery (Bentley and Ma, 2020; Kuipers and Schonheit, 2022), as perceptions of justice and feelings of violation affect customer post-breach behaviors (Choi et al., 2016). CSR initiatives can also help restore reputation (Bansal, 2018). Post-breach reputational damage varies by context, depending on firms’ existing reputations (Gwebu et al., 2018) and consumer culture (Madan et al., 2023). Such variability explains the differing customer responses to data breaches (Angelis and Miller, 2021; Kuipers and Schonheit, 2022).
5.2.3. Suppliers and communities
Following data breaches, suppliers also reassess the breached firms by reducing relationship-specific investments and becoming more likely to terminate their supplier-customer relationships (He et al., 2020a). This indicates that the loss of reputational capital for the breached firm extends beyond customers to affect other stakeholders’ actions. Finally, breached firms experience more negative sentiment from the public and community, evident in both news media (Hsu et al., 2022) and social media such as Twitter (Safi, 2020; Syed, 2019), but the extent of reputational damage can be mitigated by the firms’ social media marketing capabilities (Mathur, 2019).
5.3. Firm operations
Stock price declines triggered by cybersecurity breaches also reflect anticipated impairments in future operations and profitability, as estimated by stock market participants. This section reviews evidence on how cybersecurity breaches affect the overall performance of breached firms as well as specific corporate policies and outcomes.
5.3.1. Operating performance
Companies typically face poorer operating performance following cybersecurity breaches, evidenced by reduced profitability for 1–4 years (Gwebu et al., 2014; Hsu et al., 2022; Ko and Dorantes, 2006; Ko et al., 2009; Zafar et al., 2012). This decline is attributable to lower productivity arising from diversion of employee and management focus (Hsu et al., 2022; Makridis and Dean, 2018), decreased sales (Frimpong and Chen, 2021; Lending et al., 2018; Richardson et al., 2019) and slower revenue growth due to consumer backlash (Hsu et al., 2022; Kamiya et al., 2021), and increased expenses such as higher inventory costs from suppliers (Durowoju et al., 2022), reflecting the reputational damage and stakeholder-imposed penalties (discussed in Section 5.2).
Firms can counteract these impacts by investing in cybersecurity and improving disclosure, which positively affect profitability (Havakhor et al., 2021), valuation (Yang et al., 2020), and returns on R&D investment (Gutiérrez Ponce et al., 2023). However, these benefits can take time to eventuate (2 years or more), as IT investments yield long-term rather than immediate short-term gains (Havakhor et al., 2021).
5.3.2. Financing policies and outcomes
Cybersecurity breaches affect firms’ financing policies and access to capital. Breached firms tend to reduce dividends (Tosun, 2021) and increase cash-holdings (Boasiako and Keefe, 2021; Garg, 2020; He et al., 2020b) 17 to prepare for potential legal costs or other financial repercussions from the breach. Firms that engage in more cybersecurity disclosure also hold more cash (Boasiako and Keefe, 2021). Breached firms face more challenging capital-raising conditions, including decreased credit ratings (Kamiya et al., 2021), higher cost of debt (Huang and Wang, 2020; Sheneman, 2022), reduced access to bank loans (Huang and Wang, 2020), and more restrictive loan terms (Huang and Wang, 2020). These negative consequences can be mitigated through remedial actions by investing in and disclosing cybersecurity measures, which help alleviate the adverse impacts on loan terms and cost of capital (Havakhor et al., 2021; Huang and Wang, 2020).
5.3.3. Investment policies and outcomes
Cybersecurity breaches hamper corporate investment opportunities and outcomes. Breached firms decrease R&D expenditures (He et al., 2020b; Tosun, 2021), and experience diminished innovation outcomes, including fewer patents and lower asset intangibility (Lattanzio and Ma, 2021; Wang et al., 2024). Firms facing greater cybersecurity risks produce simpler patents with lower returns on R&D investments (Lattanzio and Ma, 2021). Mandatory cybersecurity disclosure regulations also reduce innovation and patenting activities (Liu and Ni, 2023).
Cybersecurity breaches limit corporate expansions and curb existing investments (Say and Vasudeva, 2020). Firms facing higher cybersecurity risks are less likely to pursue M&A (Lattanzio and Taillard, 2022) and more likely to engage in divestitures (Say and Vasudeva, 2020). In contrast, firms with lower cybersecurity risks pursue more M&A deals and experience better post-merger performance (Lattanzio and Taillard, 2022), as excessive cybersecurity risks may lead firms to seek lower-quality M&A opportunities to combat cybersecurity risk (Moskowitz, 2017).
Data breaches can be perceived as failures in social responsibility (Opderbeck, 2017), reducing the value of existing CSR investments (Akey et al., 2021). To mitigate breach-induced reputational damage, firms boost CSR investments (Akey et al., 2021; Jasa, 2020; Lending et al., 2018) and increase lobbying efforts (Li et al., 2022) to restore social and political capital.
5.3.4. Auditing and accounting
Strengthening auditing processes contributes to combatting cybersecurity risk, either through regular or specialized audits (Schoenfeld, 2022). Data breaches heighten firms’ awareness of cybersecurity risks, particularly after recurring incidents (Li, 2017), leading to enhanced audit quality (Rosati et al., 2022) and increased audit fees (Li, 2017; Li et al., 2020; Rosati et al., 2019b; Yen et al., 2018). 18 Increases in audit fees may reflect auditors pricing the risk of litigation exposure as a result of needing to audit unstructured big data (Alderman, 2021; La Torre et al., 2021). This fee increase can be mitigated by strong corporate governance, such as board-level risk committees (Smith et al., 2019). Transparent cybersecurity disclosures also help reduce audit fees (Calderon and Gao, 2021). When auditors experience data breaches, this can undermine their credibility and negatively affect their clients, such as reducing demands for the latter’s shares in IPOs (Alhusaini et al., 2022).
Cybersecurity risks and data breaches also impact firms’ financial reporting quality (e.g. Haapamäki and Sihvonen, 2019), but empirical findings are mixed. Some research shows that breached firms exhibit higher financial reporting quality with reduced earnings management and restatements (Rosati et al., 2022), which may be due to increased auditor scrutiny (Rosati et al., 2019b). Conversely, other studies find that data breaches lead to decreased information transparency (Gwebu et al., 2014) and reduced earnings quality (Nie and Xu, 2021). Cybersecurity disclosures negatively affect financial reporting quality (Masoud and Al- Utaibi, 2022), and mandatory disclosure laws are linked to increased earnings manipulation (Liu and Ni, 2023). Despite the Sarbanes-Oxley Act of 2002 requiring firms to report internal control weaknesses under Section 404, data breaches do not appear to increase the likelihood of such disclosures (Richardson et al., 2019).
5.4. IT process and policies
Despite the significant costs of cybersecurity breaches, there is limited evidence of substantial improvements in IT policies and practices post-breach. Research focuses on corporate cybersecurity disclosure practices with mixed findings. Generally, firms provide limited disclosure with varying quality (Héroux and Fortin, 2020). Some studies find increased cybersecurity disclosure following breaches, particularly severe ones (Chen et al., 2023; Swift et al., 2020), and improved IT governance disclosure (Lankton et al., 2021), supporting the view that cybersecurity exposure motivates firms to improve disclosure transparency (Campbell et al., 2014). In contrast, other research shows limited change (Hilary et al., 2016) or even reduced disclosure following breaches, as evidenced by usage of concise and legalistic language (Gao et al., 2020), with no improvements in readability (Gao et al., 2020; Swift et al., 2020). Overall, the impact of data breaches on cybersecurity disclosure remains debated.
5.5. Management and board
5.5.1. Executive turnover
Successful cyberattacks can reveal weaknesses in a corporation’s cybersecurity management and prompt changes in the management team. Research has investigated whether data breaches increase the risk of job losses for corporate executives, including CEOs, CIOs/CTOs, CFOs, and other top-five executives (Banker and Feng, 2019; Hilary et al., 2016; Lending et al., 2018; Say and Vasudeva, 2020), producing mixed findings. Some studies document increased post-breach turnover for CEOs and CIOs/CTOs (Banker and Feng, 2019; Lending et al., 2018; Say and Vasudeva, 2020). Other studies find no evidence of increased turnover of CEOs (Tosun, 2021), CIOs (Li et al., 2021b), CFOs (Banker and Feng, 2019), or other top-five executives (Hilary et al., 2016). The variation may be attributable to the nature of the breach (e.g. whether caused by system deficiency) as well as firm- and executive-specific factors (such as disclosure transparency and CIO expertise) (Banker and Feng, 2019; Li et al., 2021b; Jasa, 2020).
Evidence remains inconclusive on the important question of whether replacing executive officers effectively prevents future breaches: some evidence shows that CIO turnover facilitates the remediation of IT control weaknesses (Li et al., 2021b), while others find no significant impact of post-cyberattack CIO turnover on future breaches (Say and Vasudeva, 2020). This suggests that sometimes these turnovers may represent scapegoating rather than meaningful improvements.
5.5.2. Executive compensation
Data breaches can lead to changes in executive compensation structure (Kamiya et al., 2021). Some evidence shows increased incentive compensation for CEOs post-breach (Tosun, 2021), whereas others find no change in overall CEO equity incentive compensation, but CEOs see a reduction in bonus pay, an increase in restricted stock grants, and a decrease in stock options (Kamiya et al., 2021). This shift suggests that stock options are replaced with restricted stocks to reduce CEO risk-taking incentives (Kamiya et al., 2021).
5.5.3. Board restructuring
Boards of directors play an important role in shaping and overseeing cybersecurity strategies. While legal liability for data breaches is often attributed to software providers (August and Tunca, 2011; Cezar et al., 2014), directors and managers face increasing exposure to personal liability (Dinger and Wade, 2022), especially for repeated breaches (Frank et al., 2021). Despite this pressure, most boards do not implement systematic governance changes following breaches, with governance responses remaining rare and only enacted after costly breaches (Georg- Schaffner and Prinz, 2022; Shaikh and Siponen, 2023).
In response to data breaches, some firms enhance their governance practices to mitigate future cybersecurity risks. These changes include increasing managerial attention to cybersecurity (Kamiya et al., 2021; Shaikh and Siponen, 2023), formalizing oversight duties (Georg- Schaffner and Prinz, 2022; Kamiya et al., 2021), incorporating IT governance into audit committee charters (Lankton et al., 2021), conducting security risk assessments (Shaikh and Siponen, 2023), and enhancing corporate governance quality in general (Lending et al., 2018). Although not universal, these changes reflect efforts by corporations to improve cybersecurity governance and prevent future breaches.
5.6. Peer effects
5.6.1. Spillover and contagion
Cyberattacks impact not only the breached firms but also their industry peers. One perspective on stock market performance is that rivals benefit from a breach against an industry peer, as customers of the breached firm switch to its competitors, thereby increasing their market share (Ko and Dorantes, 2006; Zafar et al., 2012). Evidence supports this substitution effect by showing that industry peer firms experience positive stock price changes after a rival’s data breach (Aytes et al., 2006; Jeong et al., 2019).
A competing view is that data breaches reveal negative information about the entire industry, which can harm the stock prices of industry peers (Kamiya et al., 2021). This contagion effect is evidenced by stock price declines among peer firms which are not directly involved in a breach (Haislip et al., 2019; Kamiya et al., 2021; Kashmiri et al., 2016; Martin et al., 2017). Reputational contagion further impacts peer firms’ brand capital (Corbet and Goodell, 2022; Hsu et al., 2022), and breached firms’ stock price reactions predict peer firms’ stock price changes (Kamiya et al., 2021). In addition, peer firms experience decreased liquidity (Eisenbach et al., 2022), volatility transfer (Corbet and Goodell, 2022), and increased trading volume following breaches (Islam et al., 2022).
The conflicting evidence on substitution versus contagion effects on industry peers may be due to firm-level differences. Stock price reactions differ among peer firms (Kashmiri et al., 2016), with stronger negative contagion when rivals are similar in size and product markets or share governance features with breached firms; contagion is weaker when peer firms have influential IT management or CSR engagement.
5.6.2. Increased awareness and mitigation
In response to a rival firm’s data breach, industry peers improve their own cybersecurity by addressing internal control weaknesses (Ashraf, 2021), increasing auditing spending (Haislip et al., 2019), and adopting positive tones in cybersecurity disclosure to combat negative reputational contagion (Tian et al., 2021). Peer firms also appoint IT experts onto their TMTs (Ashraf, 2021), which helps peer firms mitigate reputational contagion (Islam et al., 2022).
6. Discussions and directions for future research
Our study synthesizes evidence from 203 academic studies to provide a comprehensive overview of the determinants and consequences of cybersecurity risk for corporations. Our findings show that corporate exposure to cybersecurity risk is influenced by wide-ranging factors in four broad categories: managerial characteristics, firm operations, IT practices, and institutional environments. Firms can mitigate cybersecurity risk by adopting effective risk-management strategies to prevent or reduce the adverse impacts of cyberattacks. Cybersecurity breaches lead to severe and long-term consequences, including stock price declines, reputational damage, negative effects on operations and policies, changes in IT practices, managerial repercussions, and spillover effects on industry peers. We discuss the implications of these findings, suggest directions for future research, and offer concluding remarks.
Our findings provide numerous practical insights for mitigating cybersecurity risk, benefiting corporate managers, investors, regulators, and policymakers. First, we offer a roadmap for understanding and addressing specific risk factors affecting corporate cybersecurity exposure, helping corporate decision-makers identify areas for improvement to reduce vulnerability to cyberattacks. For instance, as firms expand and become more profitable, managers need to be aware that such enhanced visibility and financial success increase their risk of cyberattacks. These insights enable managers to adopt effective mitigating strategies, such as by enhancing risk management from both technical and governance perspectives. Effective mitigation requires strong managerial support and careful integration of risk management systems to achieve meaningful improvements, rather than merely increasing firms’ cybersecurity budgets.
Second, investing in cybersecurity defenses is vital to protecting firms against potential threats. However, cybersecurity investment decisions require cost-benefit analyses. To prevent under-investment, practitioners must understand the full consequences of cybersecurity breaches. Our study offers detailed insights into both short-term and long-term impacts of cyberattacks, providing a toolkit for executives and directors to gain a thorough and in-depth understanding of the costs associated with breaches. These insights help practitioners make informed decisions on resource allocation for cybersecurity, aiding optimized investment in cyber defenses.
Third, in light of concerns among investors and managers regarding stock price declines caused by cyberattacks, our findings highlight strategies to mitigate these impacts and protect shareholder value. We provide practical recommendations distilled from extensive evidence on firm-, breach-, and response-related factors that affect stock market reactions to cybersecurity breaches. Effective strategies include proactive risk management, appropriate crisis responses, and implementing post-breach changes to minimize negative market reactions to subsequent breaches. In addition, communicating cybersecurity investments through disclosure can positively influence investor perceptions and enhance stock market valuation.
Fourth, from a policy perspective, legislators face increasing public pressure to address corporate cybersecurity failings, as seen in the 2022 Optus data breach in Australia. Such breaches can cause widespread disruptions and significant negative externalities (Pattnaik et al., 2023). In response, lawmakers have imposed stricter penalties such as fines to hold firms accountable and encourage improvements in cybersecurity defenses (Belot, 2022; Bogle, 2022; Tillett et al., 2022). Our findings provide crucial and timely evidence on the market-imposed penalties for breached firms—such as economic penalties imposed by customers, suppliers, and investors—which incentivize corporations to reduce exposure to cyberattacks. This information is valuable to policymakers in determining whether, and to what extent, additional regulatory measures are necessary to supplement the market-driven penalties and effectively motivate corporations to strengthen cybersecurity. Overall, our study provides a comprehensive resource for corporate managers, investors, cybersecurity practitioners, and policymakers to harness the power of two decades of high-quality academic research to aid informed decision-making.
Our study not only provides practical insights but also introduces a novel conceptual framework, making significant theoretical contributions to the literature. We bridge interdisciplinary barriers by integrating cybersecurity research from different fields including business, information systems, computer science, and engineering, in response to the call by Falco et al. (2019) to transcend disciplinary boundaries and unify diverse fields of study. Using a three-pronged search strategy across journals, publishers/archives, and Google Scholar to provide comprehensive coverage, we consolidate wide-ranging studies with a focus on corporations, amalgamating previously fragmented research. This synthesis produces a unique framework categorizing the risk factors that drive corporate cybersecurity risk and the impacts of cyberattacks. This framework outlines inter-relationships among the determinants and consequences of cybersecurity risk, highlights feedback mechanisms for improving risk management, and offers researchers a roadmap for navigating the interdisciplinary landscape of cybersecurity research.
Our study identifies key gaps in the existing literature and offers important directions for future research. First, most prior research focuses on either determinants of corporate cybersecurity risk or breach consequences, treating these as distinct questions. Our framework demonstrates that risk management is crucial both for preventing breaches and in post-breach rectification, creating a continuous cycle of corporate learning and improvements. While some research documents post-breach remediation such as executive turnover (Li et al., 2021b; Peng et al., 2023), broader investigations are warranted into potential strategies for strengthening cybersecurity defenses following breach incidents and their effectiveness in preventing future attacks. Investigating how firms can leverage past breach experiences to enhance future cybersecurity presents a valuable opportunity for empirical research.
Second, future research can benefit from exploring firm-level heterogeneity in determining the impacts of, and responses to, cyberattacks. While prior studies have considered firm-specific characteristics primarily in investigating short-term stock market reactions, firm-level differences should also be explored when examining long-term consequences of cyberattacks and corporate responses. For instance, firms exhibit significant cross-sectional differences in post-breach operational performance depending on firm size and industry (Kamiya et al., 2021), indicating that susceptibility to cyberattack-induced backlash varies across firms. In-depth investigations into firm characteristics and cross-sectional differences can yield valuable insights and help practitioners tailor response strategies to firm-specific needs.
Third, existing research has produced conflicting evidence on numerous important research questions. For example, the effect of cybersecurity breaches on financial reporting quality remains debated, with some studies showing improved reporting quality (Rosati et al., 2022) and others finding reduced information transparency (Gwebu et al., 2014). Another unresolved question concerns the peer effects of cybersecurity breaches on competitors’ stock prices: some studies report a negative contagion effect (Haislip et al., 2019; Kashmiri et al., 2016; Martin et al., 2017), while others find a positive substitution effect (Aytes et al., 2006; Jeong et al., 2019). In addition, the effectiveness of post-breach response strategies, such as replacing CIOs, remains unclear and warrants further investigation (Li et al., 2021b; Say and Vasudeva, 2020). Further research is needed to undertake more nuanced approaches and explore firm- and industry-level heterogeneity to resolve these conflicts in existing evidence and reconcile prior findings. Furthermore, puzzles remain in existing research findings. For instance, contrary to expectations that data breach disclosure laws would enhance information transparency and reduce stock price crash risk, evidence shows that such laws at the state level in the US are linked to increased stock price crash risk (Liu and Ni, 2023). Further research is needed to understand this unexpected phenomenon.
Finally, cybersecurity breaches create significant social externalities, resulting in broader societal costs beyond the breached firms. Cybersecurity is increasingly regarded as an aspect of CSR (Opderbeck, 2017). Future research should explore cybersecurity as a component of firms’ environmental, social, and governance (ESG) commitments, in order to inform the existing ESG measurement framework and develop new avenues of investigation.
Key practical and research implications
Investors: Investors can consider the exposure and impacts of cybersecurity breaches identified in this study, both direct and indirect, when evaluating investments.
Footnotes
Acknowledgements
The authors wish to thank Eva Balan-Vnuk, Helge Janicke, Leonie Simpson, and participants at the SOCRATES Industry Day at The University of Adelaide and the Australasian Lab of Cyber Security Ideas (ALCSI) Conference 2024 for their helpful comments and discussions.
Final transcript accepted 1 October 2024 by Andrew Jackson (Editor-in-Chief ).
Funding
The authors acknowledge research funding support from Cyber Security Cooperative Research Center (CSCRC) as a part of the SOCRATES Project.
1.
Prior studies that conduct systematic literature reviews have either undertaken a narrower focus (e.g. the study by Schlackl et al. (2022) which focuses solely on data breaches as a subset of the manifestation of cybersecurity risk) or examined only one aspect of the consequences on cyberattacks, such as stock price reactions (Ali et al., 2021; Spanos and Angelis, 2016).
2.
Our journal-specific searches cover the following A*-ranked journals (according to the Australian Business Deans Council (ABDC) journal ranking): Critical Finance Review, Insurance: Mathematics & Economics, Journal of Banking & Finance, Journal of Corporate Finance, Journal of Financial and Quantitative Analysis, Journal of Financial Economics, Journal of Financial Intermediation, Journal of Financial Markets, Review of Asset Pricing Studies, Review of Corporate Finance Studies, Review of Finance, The Journal of Finance, The Review of Financial Studies, Accounting Auditing and Accountability Journal, British Accounting Review, Journal of Business Finance & Accounting, Journal of Management Accounting Research, Accounting, Organizations and Society, Auditing: A Journal of Practice and Theory, Contemporary Accounting Research, Journal of Accounting and Economics, Journal of Accounting Research, Management Accounting Research, Review of Accounting Studies, The Accounting Review, The European Accounting Review, Academy of Management Journal, Academy of Management Review, Administrative Science Quarterly, Journal of Business Venturing, Journal of International Business, Journal of Management, Management Science, Organization Science, RAND Journal of Economics, and Strategic Management Journal. In addition, we also include several regional A-ranked journals to ensure coverage of relevant studies, specifically Accounting and Finance, Australian Journal of Management, Corporate Governance: An International Review, Financial Management, International Review of Financial Analysis, Journal of Accounting Auditing and Finance, Journal of Accounting and Public Policy, Journal of Contemporary Accounting and Economics, Journal of International Accounting Research, and Pacific-Basin Finance Journal.
3.
4.
We did not restrict our data collection to a particular timeframe.
5.
The data collection in this study was conducted in January 2023, which accounted for the decline in the number of articles published in 2023 and 2024. To be included in this review, articles had to be published online at the time of the data collection. The reviewed articles include a small number of “forthcoming” studies which had been accepted for publication at the time of the data collection and were subsequently published in 2023 or 2024.
6.
7.
Studies have also examined board size (Mazumder and Hossain, 2023) and director age (Héroux and Fortin, 2022) but found no significant impact on cybersecurity disclosure.
8.
Practitioners can obtain internal control insights from cyber breach reports, which however contain too little information to help firms strengthen internal control systems and reduce risk (Blakely et al., 2022).
9.
This body of research encompasses a large number of studies (Akey et al., 2021; Amir et al., 2018; Bolster et al., 2010; Campbell et al., 2003; Cavusoglu et al., 2004; Chang et al., 2020; Chatterjee et al., 2019; Corbet and Gurdgiev, 2019; Foecking et al., 2021; Garg et al., 2003; Gatzlaff and McCullough, 2010; Gordon et al., 2011; Grundy et al., 2022; Gwebu et al., 2018; Hilary et al., 2016; Hogan et al., 2020; Hovav et al., 2017; Kamiya et al., 2021; Kammoun et al., 2019; Kashmiri et al., 2017; McShane and Nguyen, 2020; Martin et al., 2017; Masuch et al., 2022; Morse et al., 2011; Peng et al., 2023; Piccotti and Wang, 2022; Pirounias et al., 2014; Richardson et al., 2019; Rosati et al., 2019a; Song et al., 2017; Tanimura and Wehrly, 2009; Tosun, 2021; Tripathi and Mukhopadhyay, 2022; Tweneboah-Kodua et al., 2018; Yayla and Hu, 2011). Prior systematic reviews conducted by Spanos and Angelis (2016) and ![]() have reviewed this subset of the literature examining stock price reactions to data breaches.
have reviewed this subset of the literature examining stock price reactions to data breaches.
10.
However, which cyberattack types trigger worse market reactions can change over time: for example, in South Korea, cyberattacks involving denial-of-service and data corruption previously trigger more serious market reactions pre-2007, but since the passage of privacy laws in 2007, attacks that involve access to private information trigger worse market reactions post-2007 (Hovav et al., 2017).
11.
However, there is no evidence to show that such worsened stock market reactions persist for subsequent breaches after the initial two breaches suffered by a firm.
12.
Gwebu et al. (2018) group response strategies into four categories: image renewal (through correction commitment and stakeholder/value commitment), defensive (e.g. denial, excuses), moderating (ingratiation, justification), and accommodative strategies (apology, remedial). However, these strategies matter less for highly reputable firms (Gwebu et al., 2018).
13.
However, for firms that have low visibility on traditional media, social media exposure of a data breach can save the firms from experiencing negative stock price changes (Rosati et al., 2019a).
14.
But some evidence shows that this could be due to market overaction (Hogan et al., 2020).
15.
Similarly, e-commerce firms are also found to suffer worse market reactions to data breaches (Yayla and Hu, 2011).
16.
Although the direction of the latter’s influence is still open to debate (Gordon et al., 2011; Kannan et al., 2007), Kannan et al. (2007) find more significantly negative market reactions to cyberattacks after September 11th, whereas ![]() find weaker market reactions.
find weaker market reactions.
17.
18.
However, some researchers find no significant differences in audit fees between breached and non-breached firms (Richardson et al., 2019).
