Abstract
This article pursues a translational approach to the securitization of migration. It argues that sociotechnical processes of identification at the border can be conceived of as translations into legible identities of individuals who are unknown to authorities. The article contributes to the materiality debate on securitization across Critical Security Studies (CSS) and Science and Technology Studies (STS) by answering the call to conduct empirical explorations of security, and by revisiting the potential of the early sociology of translation (i.e. actor-network theory) to account for the identification of border crossers. Data collection was conducted at four identification facilities in the Hellenic Republic. Three sets of implications for the CSS-STS debate on the materiality of securitization are discussed. First, a translational approach can replace a representational understanding of identity with a performative apprehension of identification. Second, adopting a translational approach leads to acknowledge that the identification encounter is mediated by multiple, heterogeneous actors. It thus helps to open technological black boxes and reveal the key role of material qualities, affordances and limitations of artefacts. Third, a translational approach to the securitization of migration can help advance the field of ‘alterity processing’ by appreciating the de facto re-arrangements of institutional orders elicited by techno-political alignments with global security regimes.
The relationship that individuals entertain with security authorities is never bilateral. This claim is most evidently revealed when nationals unknown to authorities try to cross borders. 1 Under contemporary securitized mobility regimes (see Curtin, 2017), entering a country requires foreign nationals to be known to authorities well before they reach the border. Their data must be entered beforehand in visa or entry/exit information systems. If they are not, or their records do not match, they slip into the category of ‘the irregular’. In Europe, for example, third-country nationals who are caught at the border and whose travel is not pre-authorized in the European Visa Information System (VIS) 2 are classified as ‘irregular’. Most crucially for this article, information systems are performative of this irregularity. This calls for renewed attention to the processes of identification of ‘irregular’ border crossers by studies that investigate the material infrastructures of securitization.
In this article I pursue a translational approach to the securitization of migration. I argue that sociotechnical processes of identification at the border can be conceived of as translations of individuals who are unknown to authorities into legible identities. Through the steps of this translation border crossers become ‘irregular’, subjects of security practices. My overarching goal is to contribute to the materiality debate across Critical Security Studies (CSS) and Science and Technology Studies (STS). 3 I intend to do so first by reacting to the call to conduct empirical explorations of security in actual sites (Amicelle et al., 2015) and, second, by revisiting the potential of the sociology of translation 4 to account for the identification of border crossers.
Concepts like ‘shifting’ (Latour, 1992), ‘spokespersons’ and ‘interessement device’ (Callon, 1984) constitute the core of the sociology of translation. However, they have not received sufficient attention so far in the literature on security, borders and materiality. I suggest that adopting such conceptualizations has some potentialities. First, it eventually allows replacing a representational understanding of identity with an apprehension of identification as enactment. Early criticisms of the identification encounter argued that identification
Second, a translational approach most evidently reveals that border crossers are made legible by involving them in networks featuring heterogeneous actors, including non-state ones. The encounter between border crossers and state security authorities is mediated by actors that transcend national borders, governmental missions and security epistemologies. While this argument has been put forward by some authors in migration and security studies (Andersson, 2015; Sontowski, 2018; Tsianos and Karakayali, 2010), the translational framework enables us to open the technological black boxes and reveals how the material qualities of artefacts act to involve diverse actors in the identification encounter.
Finally, in fostering a translational approach to the identification of border crossers in the name of security, my secondary goal is to advance the field of what I have called ‘alterity processing’. The processing of alterity refers to the material practices and data infrastructures used for the informational management of migration, practices and infrastructures that can eventually shape institutional orders and polities (Pelizza, 2020). As the evidence below shows, the databased translation of unknown people into legible identities de facto alters the institutional orders, the ‘geographies of responsibilities’ (Oudshoorn, 2011) that are prescribed in law, regulations and treaties.
This article relies on data collected in Europe in the context of the ‘Processing Citizenship’ research program. The research was made possible by unprecedented access to information systems, interviews, documents and observation of identification procedures in the Hellenic Republic. 5 Data collection was mainly conducted from March to October 2018 at four identification facilities (i.e. three ‘Hotspots’ and one identification centre) through observation of border crossers’ identification procedures, in-situ interviews with applicants and officers from the Hellenic Asylum Service, the Hellenic Police and the Hellenic First Reception Service (RIS), further off-site interviews, including with European officers, and the analysis of information systems, procurement and other technical documents.
Migration studies between identity and identification
Studies focusing on the processing of alterity at the border maintain a topical interest in the encounter between the state and border crossers. The nation-state is seen as having a prominent role in grounding ‘the political context that produces displaced people in the first place [because of] the violence its reproduction involves’ (Casas-Cortes et al., 2015: 71). Similarly, Krause and Williams (2002) have stressed that states remain prevalent actors in the realm of organized violence. It is therefore not surprising that one of the main concerns of studies about border encounters has addressed the (re)production of migrant subjectivities by state authorities.
Since the late 1990s, state-led reproduction has been interpreted in the light of a distinction between
Yet, I suggest, the gap between identification and identity re-proposes the distinction between object and subject, the material and the semiotic. It lingers in a representationalist paradigm, in which a full but unachievable semiotic essence of the human individual (i.e. identity) would be poorly represented by reductionist technologies (i.e. identification). As Barad (2007: 86) has recalled, ‘representationalism is the belief that words, concepts, ideas, and the like accurately reflect or mirror the things to which they refer’. It is only against the expected accuracy of representation that identification can be assessed as a reduction. Biometrics, for example, is criticized because digital traces do not accurately reflect the sociocultural depth of individuals.
Representationalism may entail unbalanced attention to discourse. The distinction between identity and identification seems to forget that ‘the making of the subject’ is not only discursive. Faced with fingerprint and retina scanning, DNA testing and interoperable databases, early migration studies developed a justified suspicion toward the informational and technical aspects of border crossers’ identification. In so doing, however, they have paid scarce attention to
To move forward, I take up Barad’s invitation to adopt a performative stance. ‘The move toward performative alternatives to representationalism shifts the focus from questions of correspondence between descriptions and reality (e.g. do they mirror nature or culture?) to matters of practices, doings, and actions’ (Barad, 2007: 135). In our case, I shift focus from achieving a non-reductionist representation of identity to tracking how always partial forms of identification are materially processed, who/what they involve or exclude, and with which consequences to the distribution of power. If identity is not an essence that should be represented as faithfully as possible, but the transient result of sociotechnical processes, those processes must be investigated.
A similar call, to take seriously the medium through which identity is built, has long been formulated in feminist technology studies, especially those concerned with the oppressive elements of surveillance (e.g. Prainsack and Toom, 2010) or with databased self-diagnosis (e.g. Egher and Wyatt, 2016). I suggest adopting a similar approach in research that investigates identification at the securitized border. Instead of interpreting the distinction between identification and identity as an impoverished form of representation, I propose to view it as an articulation of process and results, agency and the provisional outcome of that agency. In this sense, identification ought not be associated only with the state. 6
An emergent trend in migration studies has investigated the artefacts mobilized in the identification encounter at the border (Besters and Brom, 2010; Broeders and Engbersen, 2007; Dijstelbloem and Meijer, 2011; Pollozek and Passoth, 2017; Trauttmansdorff, 2017; Van der Kist and Rosset, 2020). Kuster and Tsianos (2016) have called for analyses that elucidate how databases like Eurodac do borders. Similar studies have shown how the presence or absence of bureaucratic documents exert agency not only on the state’s regulation of asylum, but also on migrants’ conditions of freedom (Cabot, 2012). Tazzioli (2019) argues, for example, that financial artefacts can constitute an alternative mode of governing refugee populations in transit, subjectivizing them as clients.
Most of these studies have focused on biometric technologies as biopolitical tools facilitating the triage of identities at the border (Van der Ploeg, 1999; Van der Ploeg and Pridmore, 2016; Van der Ploeg and Sprenkels, 2011). Ajana (2013a, 2013b), for example, has conceived of biometric profiling and fingerprinting as practices that make migrants’ exclusion from the official juridico-political structure an ‘inclusive exclusion’. Allen and Vollmer (2018) have described the UK e-Borders as an assemblage that is dynamically constructed through heterogeneous elements. An overtly performative stance has been adopted in some cases. According to Pötzsch (2015), the sociotechnical apparatuses of identification that he names ‘iBorder’ (i.e. biometric, algorithmic, and automated border work) enact, rather than merely process, contingent subjectivities and frames for practice. For Kloppenburg and Van der Ploeg (2020), biometric technologies are ‘producing and enacting [new] gender and ethnic classifications and identities’ (p. 57).
As a consequence of these performative approaches, some studies have acknowledged that the encounter between border crossers and security authorities involves broader networks than the state. Tsianos and Karakayali (2010: 375) see a ‘multitude of actors whose practices relate to each other, without, however, being ordered in the form of a central logic or rationality.’ Sontowski (2018) describes the contentious politics that have accompanied the development of biometric bordering. In his analysis of the EU’s Smart Borders Package, the technical design of the Entry/Exit systems emerged as the result of harsh negotiations among the European Parliament and Council, Member States, EU agencies like the European Agency for the Operational Management of Large-Scale IT Systems in the Area of Freedom, Security and Justice (eu-LISA), business pilots and global consultancies. Similar tensions between states and border agencies have been documented by Andersson (2015), who conceives of border technologies as catalysts of new institutional orders and relationships. Crucially, Andersson has highlighted the composite, ‘industrial’ nature of border management and its potentiality to create areas for collaboration and competition, compliance and conflict across sectors. Similar considerations have led Broeders and Dijstelbloem (2016) to see the state as a mediator of tensions taking place between non-state actors.
That sociotechnologies of identification can de facto alter institutional orders is also implicit in the work by Carrera and Hernanz (2015). According to them, European Smart Borders biometric programs mark not only emergent modes of making people on the move visible, but also mistrust in border guard national authorities, and re-allocation of trust in large-scale European databases using biometric technologies. Thanks to such systems, the country-centric approach underlying the Schengen tractates is de facto being replaced by a person-centric approach that classifies non-EU population beyond national categories.
All in all, this emergent body of literature has overstepped the distinction between identity and identification, and – at least in some cases – moved beyond a representationalist epistemology. This suggests acknowledging the proliferation of heterogeneous actors indirectly involved in the identification encounter, and technologies’ role as catalysts of new institutional orders. Yet I have the impression that a method that explains the identification encounter in light of the material qualities, limitations and affordances of artefacts and infrastructures is still difficult to achieve. Biometrics and other data infrastructures are analysed either in their process of coming into being or in their effects, while the role of their inner workings in bringing about those effects is an underdeveloped field of research. This article intends to further this research field: a translational approach might be equipped to open the many black boxes of identification.
The ‘material turn’ in CSS: Translation and heterogeneity of actors
Over the last years, the materiality debate spanning international relations, security and technology studies has followed appeals to open the securitization debate to non-essentialist conceptualizations of security (Stritzel, 2011). The so called ‘material turn’ in security studies has constituted one of the most interesting debates outside the niche in which new materialism originally developed. It has contributed to grounding an interest in the co-development of security devices, actors and practices (Barry, 2013; Best and Walters, 2013; Dijstelbloem et al., 2017; Salter, 2015; Walters, 2002). It has also coincided with an expansion in the range of security actors. A new focus on artefacts has gone hand in hand with a renewed attention to more diverse security actors than the state.
Notwithstanding differences in focus, theoretical strands and goals, materialist security literature shares some common features. First, studies have focused on the production and use of artefacts in security practices. This has led to an acknowledgement of forms of non-human agency. According to Bellanova and Glouftsios (2020), for example, the design of the Schengen Information System (SIS II) has conditioned the management of international mobility across the EU. Studies in this field have also shown how an attention to artefacts can render visible asymmetries usually buried in design and governance programs (Bellanova and Duez, 2012; Valkenburg and Van der Ploeg, 2015; Walters, 2014).
Second, the focus on devices has allowed the field to expand the security framework. As Amicelle et al. (2015: 300) have put it, ‘attending to devices takes us beyond the critique of dominant logics of security, which has already been aptly formulated in critical approaches. It allows us to develop a multifaceted account of political agency.’ Analyses have thus concerned the relationship between the state and the targets of security policies, relations within the state itself, and relationships between diverse governmental bodies and authorities and non-governmental actors. Interest has also been shown in blurring the divide between the public and the private (Berndtsson and Stern, 2011; Schouten, 2014). As De Goede (2018: 25) has put it, ‘private companies, in many ways, have become security actors in their own right’.
Third, a few conceptualizations have mobilized the notion of ‘translation’. Translation has been conceived of either as purely discursive (Freeman, 2009, quoted in Stritzel, 2011), or more often as material-semiotic transformation. Such an approach has built upon the early sociology of translation, as in the case of De Goede’s (2018) notion of ‘security chain’ that accounts for paths of suspicious financial transactions as translational chains involving public and private actors (see also Jeandesboz, 2016). In some cases, translation has been conceived of as a future-oriented, non-linear process of transformation that activates future imaginations and anticipations (Bourne et al., 2015).
Fourth and related, most security studies engaged in the materiality debate have embraced a performativity approach to challenge the naturalness of security actors and of stabilized subjects (Aradau, 2010; De Goede et al., 2014). An ‘analytics of security devices’ has further advocated a performative understanding of security by challenging the limits of the original material turn, which allegedly draws attention to objects as opposed to humans. According to a device-based analytics, ‘we need to supplement existing readings of performativity … with empirical explorations of how security is performed in different sites’ (Amicelle et al., 2015: 299).
I see a possibility of contributing to this developing debate with an interest in the material qualities, affordances and limitations through which the identification encounter takes place. In doing so, the goal is twofold. First, I wish to respond to Amicelle et al.’s (2015) call to conduct empirical explorations of how security is performed in actual sites. In what follows I reconstruct identification procedures and infrastructures as observed at four European identification centres in the Hellenic Republic. Second, despite its engaged dialogue with STS and its mobilization of the concept of translation, I believe that the debate on security and materiality has not yet fully unpacked the possibilities that the sociology of translation can offer. The concepts of ‘shifting’ (Latour, 1992), ‘spokespersons’ and ‘interessement device’ (Callon, 1984) that lie at the core of the sociology of translation can constitute a key set of ‘thinking tools’ (Leander, 2008). They are helpful to investigate the inner workings of ‘security devices’ and steer the analysis toward not only singled-out artefacts, but also sociotechnical processes and infrastructures.
Security and identification in STS
STS have engaged with the materiality debate around securitization by investigating sociotechnical practices and infrastructures of (in)security production, their speculative methods, intrinsic inconsistencies and reproductive resources (Rappert, 2005; Rappert et al., 2008). Valkenburg and Van der Ploeg (2015), for example, have pointed out how ‘security’ in airport settings emerges as the outcome of shifts, unexpected transformations and late alignments with the socio-material practices in which it comes to matter. Lisle and Bourne (2019) have discussed the contestations of anthropocentrism in the working practices of officers who use automated airport security. Other studies have explored the persistence of gendered and racialized politics in the imagination, design and deployment of security devices (e.g. Olson and Labuski, 2018; Wilke, 2017).
Suchman et al. (2017) have recently called for a renewed attention to the material-semiotic dynamics through which security practices reproduce asymmetry and de facto insecurity. Taking part in the debate with CSS, Suchman (2016) has engaged with a conception of security as a kind of predictive technoscience, a form of knowledge that turns the suspect into an anticipatory target. The performativity of securitization is well summarized by the notion of ‘apparatus of recognition’, the apparatus ‘through which the architecture of enmity is put in place and into practice’ (Suchman, 2020: 2). This article shares with this body of work an attention to the materiality of apparatuses of recognition, and an understanding of security subjects as the result of sociotechnical practices that enact them as enmity or, in the migration management jargon, ‘irregular’.
Some STS studies on securitization have also given attention to the boundaries of state power. Follis (2017) has argued that the technologically mediated expansion of vision in the policing of the external borders of the European Union has fundamentally altered the nature of national borders. Elish (2017) has suggested that state’s search for security is all but granted, and it is only by paying attention to divisions of labour that we can understand the everyday practices and invisible infrastructures that sustain this search. The trend of questioning the boundaries of state power is also a topic in recent STS scholarship openly concerned with identification. For Smith (2017), security-focused identification grounded in global law enforcement is aligned with a scientific shift toward corporate-owned DNA identification. García-Deister and López-Beltrán (2015) have shown that in a context of war-like violence like contemporary Mexico, the publics of genomic and forensic identification are not just the passive objects of state power, but show differentiated economies of trust and mistrust that transcend state boundaries.
All in all, the analysis of STS literature on security suggests the potential value of investigating the nexus between identification, material-semiotic dynamics of (in)security production and the boundaries of state power. Such a nexus seems to imply that – when the materiality of identification, the ‘apparatus of recognition’, is taken into account – the security relationship comes to transcend state boundaries.
‘Shifting’, ‘spokespersons’ and ‘interessement devices’
Early conceptualizations developed by the sociology of translation have inspired studies concerned with the material-semiotic entanglements of securitization (Barry, 2013; De Goede, 2018; Jeandesboz, 2016). Yet key concepts like ‘shifting’ (Latour, 1992), ‘spokespersons’ and ‘interessement device’ (Callon, 1984) have not received adequate attention so far. This is a loss, not only because these concepts lie at the core of the translational framework, but especially because they can be helpful in opening the black boxes of identification and revealing
Here I mobilize a theoretical framework with which most STS readers are familiar. 7 My goal, though, is to bring it to work in the domain of the production of irregularity at the border, with the aim of nurturing the materiality debate ongoing with security studies readers. To this end, in this section I provide a concise summary of the premises of a sociology of translation, and the meaning of ‘shifting’ (Latour, 1992), ‘spokespersons’ and ‘interessement device’ (Callon, 1984) .
According to Callon (1984), translation is a process composed of multiple stages: (a) problematization, (b) interessement, (c) enrolment and (d) mobilization. Problematization corresponds to the hypothetical attempt by an interested set of technological initiators to attribute roles and skills to other actors, so that a given sociotechnical goal can become a shared endeavour. In order for actors to accept the roles and skills attributed to them, during the interessement stage initiators involve ‘interessement devices’. Interessement devices push actors to adopt the expected roles and behaviors; they are ‘devices which can be placed between actors and all other entities who want to define their identities otherwise’ (Callon, 1984: 133). Interessement devices are deployed to exclude some potential participants and include the preferred ones. As Figure 1 shows, an interessement artefact (i.e. the arrow) interests A and B and cuts the links between B and the group of other entities C, D, E.
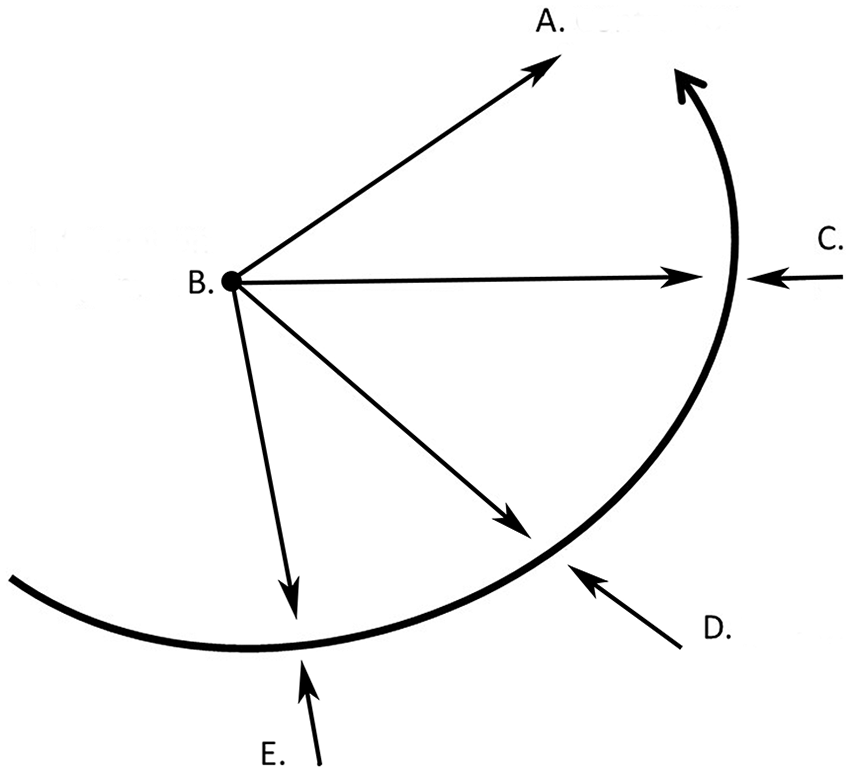
Interessement device.
Actors can accept being enrolled (i.e. successful enrolment which leads to mobilization), or not (i.e. unsuccessful enrolment). Each of these stages is reversible, and further interessement devices can be utilized to assure the successful outcome. If enrolment is successful, during the last stage of mobilization (d) ‘spokespersons’ emerge. As the name goes, spokespersons ‘speak for’ the previous links in the chain of translation, which they represent but also enact (see also Akrich et al., 2002). For example, a mayor can act as spokesperson of a community, speaking on its behalf; a scholarly presentation can act as spokesperson of many years of data collection by summarizing the results; a spreadsheet can act as spokesperson of an animal stock by numbering it. As these examples show, someone or something can act as a spokesperson because they literally speak for someone else (the mayor), or because they replace the preceding link in the chain of action and translate it into a different materiality (the spreadsheet representing the living stock).
Analysing the constitution of European border security, for example, Jeandesboz (2016) reports a case of spokespersons acting verbally: members of the European Parliament who are not present at a meeting are ‘represented, in spoken words, writings’ by colleagues (p. 300). That is, their words are uttered by someone else, but they do not change material form. Less diffused are studies that account for the second kind of spokespersons acting materially. Akrich (1992) and Latour (1992) introduced a detailed vocabulary to describe the work of spokespersons who do not verbally speak for someone else, but materially. Notably, Latour (1992) distinguished between ‘shifting up’ and ‘shifting down’. 8 Shifting up refers to the translation of artefacts into signs or texts. Instruction manuals are typical shifting up, as they translate the use of an artefact into written worlds. Shifting down refers to the opposite movement of translation from signs to artefacts. The classical example is the alarm sound that replaces the sentence ‘fasten the seat belt’ when riding in a car.
This early formulation of shiftings constitutes the missing dash in ‘material-semiotics’. Not only does it introduce a distinction between two different types of translation, but it explains it by analogy with the ‘shifting out’ and ‘shifting in’ proper to semiotic analyses. Indeed, in structuralist literary studies, ‘shifting out’ ( In storytelling, one calls
In summary, shifting in, out, up and down correspond to different kinds of translation: discursive – for shifting in and out, material – for shifting up and down. In turn, material translation can proceed from artefacts to texts (i.e. shifting up), or vice versa from texts to artefacts (i.e. shifting down).
While these early distinctions have not received much attention so far in the literature on security and materiality, I suggest that they can help analyse the identification encounter conducted in the name of security. In the next two sections, I analyse practices and infrastructures of border crossers’ identification at the Hellenic border by drawing on the notions of ‘shifting’, ‘spokespersons’ and ‘interessement device’.
First contribution: Interessement devices and spokespersons beyond representationalism
At first sight, identification is the authority-led process that associates a name with a body. As trivial as it may sound, this procedure can turn out to be extremely demanding when it comes to unknown individuals at the border. How can it establish what speaks for a name and a body across different phonetic representations, naming conventions and physical configurations? More than representation, identification qualifies as betrayal and translation (Law, 1999). This is clearly revealed in my ethnographic observations of identification of people on the move caught at the Hellenic border.
I first provide a description of the procedure of identification at the Hellenic border, as I have reconstructed it through interviews, documents and direct observation in the period from March to October 2018.
9
The actual procedure is made of three steps:
After the first interview with Policeman1, we (i.e., author and a facilitator/translator)
12
are waiting outside the modular building where registrations are conducted. We wait for him to call us back to observe registrations, as he had promised. Policeman1 comes and invites us to follow the interview of a Syrian couple which is expected to be ‘fast and easy’. We take seats around a different desk from that where Policeman1 sits and where the interview will take place, but still at close hearing and seeing distance. We can even see the computer screen from where we sit. A woman and a man, both in their late 20s, enter the modular building. They look disoriented and cautious. The interpreter joins, as well. The three take a seat: the couple sits in front of Policeman1, on the other side of the desk, so that they cannot see the screen. The interpreter sits on the short side of the desk, between Policeman1 and the couple, he can see the screen diagonally. Policeman1 introduces the interpreter as ‘objectively translating’ from Arabic. He also mentions our presence as researchers; I ask the couple’s permission by orally quoting the Informed Consent sheet and Policeman1 repeats that we can stay only if they agree. The interpreter translates into Arabic. The couple agrees. Policeman1 asks about the relationship between the young man and the young woman – ‘your wife, or your sister?’. The young man answers the lady is his wife. Policeman1 asks whether she is pregnant. She obviously is. She confirms. Policeman1 preliminarily asks their nationality. The man answers they are from Syria. Policeman1 addresses first the man and asks him in English to write down his name.
13
He specifies: ‘If you cannot write in English, we have the interpreter who can do it for you.’ Policeman1 hands over a pen and a blank paper to the man and keeps a paper form in front of himself for cross-checking; the form reports photocopied hand-written categories and original hand-written data. This form was provided by colleagues who had previously initiated the registration process in the photo modular building. Policeman1 also uses two printed spreadsheets: One reports just one line, the other more lines, each line corresponding to an individual. The second spreadsheet thus reports data of a group of people. One line is highlighted. The two spreadsheets were provided by the First Reception Service’s (RIS) secretarial office in the Centre. Policeman1 asks the young man to spell out his grandfather’s name or family name. The interpreter points out that ‘the mother’s name is more difficult’. The interpreter talks to the man in Arabic, presumably translating the request to write down his name. The young man writes his name in Arabic characters on the blank paper. The interpreter tries to transliterate the name in Latin characters on the same paper, then communicates it to Policeman1, both orally and by handing over the paper. Policeman1 copies the name as transliterated by the interpreter to another blank paper and cross-checks this latter version with the hand-written photocopied form. Only at the end of this chain of comparisons between paper sheets, Policeman1 writes the name in Latin characters in the digital Hellenic Register of Foreigners (but without sending it to the database). Policeman1 continues asking questions about the man’s desire to apply for asylum, profession, languages spoken, marital status, etc., sometimes even using Arabic words, and notes the answers down. Policeman1 asks the interpreter to ask the man about his study degree. The interpreter asks, the man replies and the interpreter translates ‘bachelor’. Policeman1 asks ‘baccalaureat?,’ the interpreter repeats ‘bachelor’. Policeman1 is clearly trying to fit this answer in the limited number of scroll down menu options that the Register of Foreigners offers. Taking a decision, he says ‘higher education’, and passes to the screening questions, which are meant to verify the man’s knowledge of Syria’s anthem, geography and ruling family. At the end, Policeman1 prints out two copies of the registration answers. The interpreter spontaneously collects them from the office printer, without being asked. The young man is given one copy and asked to check the name. Another copy is given to the interpreter for signature. In checking the name, the young man finds out that the family name reports only a part of the full name, and asks for integration. Again, he is asked to write the full name on a paper sheet. Once he has done so, the interpreter transliterates it in Latin characters. Two alternative transliterations are possible, and the interpreter asks the young man which one is correct. The man looks both the interpreter and Policeman1 straight in their eyes, expressing his helplessness. In English, he says that both can work and there is no way to assure the full correspondence with one of the two transliterations. Distressed, he repeats several times that ‘at the police station they have seen a copy of my passport’. Policeman1 chooses one of the two transliterations and inputs it into the Register of Foreigners.
This vignette provides a prime example of what I mean by identification as translation. The applicant’s name is digitally inputted in the Register of Foreigners only at the end of a chain of translations that involve oral communication and paper technologies. The chain is composed as follows: the applicant transforms the name from oral to written by writing it down in Arabic on a paper sheet, the interpreter transliterates the name in Latin characters on the same paper and communicates it orally to Policeman1, Policeman1 copies the transliterated name to another paper sheet and cross-checks this version with a hand-written form. At the end of this chain of shiftings, Policeman1 inputs the name so obtained in the digital information system. This final version of the name is expected to ‘speak for’ all the previous versions, for the applicant and for his family. However, as the first version of the name failed to enrol, the process was started from scratch a second time.
This chain reveals a hierarchy between analogue and digital techniques of data creation and storage. Inputting data in the Hellenic Register of Foreigners seems to mark their official status. It is only at the end of a careful collective process, which resorts to analogue techniques, that data achieve a degree of legitimation sufficient to be entered in the database. The material qualities, affordances and limitations of paper and digital supports can explain this hierarchy.
On the one hand, the process that leads to official status must be quick (European Commission, 2015). Yet it must also triangulate heterogeneous forms of knowledge: the applicant’s local expertise, the interpreter’s knowledge of both Syrian and European systems, Policeman1’s knowledge of Hellenic and European requirements, the Register’s own classification and limitations, as shown by the case of the applicant’s degree that refused to ‘enrol’ in one of the scroll down menu options offered by the system. Such triangulation requires the collective interpretive effort of all human participants, as well as paper sheets as interessement devices. When Arabic sounds refuse to be enrolled in Latin characters and Syrian degrees refuse to be enrolled in scroll down menu options, the impasse is addressed by introducing blank sheets and photocopied forms. Being on paper, these interessement devices can only be shared among the participants in the here-and-now of the identification encounter. They exclude anyone who is not physically present in that moment. Furthermore, as they can be easily destroyed without leaving trace, they can host attempts, failures and negotiations.
On the other hand, once entered into the digital Register of Foreigners, data can travel: they become available to an indeterminate range of authorities for an indefinite period. Furthermore, as it emerged from interviews, a high degree of compartmentalization characterizes identification procedures. Almost none of the street level officers interviewed knew whom their work was to benefit down the workflow, nor who was to have access to the digitized data, besides the general reassurance that only authorized colleagues (in Athens? in Brussels?) were. On top of this, data erasure is extremely complicated and requires the intervention of high-level ministerial officers in Athens (Pelizza, 2020). Digital circulation, indeterminacy and erasure difficulties explain why the Register of Foreigners lies at the end of the chain of translation and speaks for the official identity of the applicant.
In contrast, in the above vignette paper sheets support the creation of shared interpretive agency, which eventually re-enacts the participants in the identification encounter. The applicant is being literally translated as his name changes from Arabic to Latin characters, the interpreter attunes his North-African Arabic to the Syrian pronunciation, Policeman1 makes the effort to speak and learn some Arabic. That the identification encounter entails enactment, and not the mere representation of pre-existing identities, is also revealed by the applicant’s helpless glance at the two men. He knows that both transliterations are equally possible, and yet no one is correct. He knows that there is no way to assure the exclusive correspondence of the Arabic writing of his name as reported in the passport with one of the two Latin transliterations. He knows that no accurate representation of his name is possible, as what is at stake is not reflecting a pre-existent identity, but performing a new one. While Policeman1 and the interpreter seem to believe in representations, the young man knows that any translation is a betrayal.
Second contribution: Interessement devices and chain of shiftings to account for heterogeneous actors
The vignette discussed above shows the limits of a representationalist approach to identification. It also shows that analysing identification as a chain of material shiftings allows opening the black box of devices and accounting for the role of material limitations and affordances. It should also be noted that a translational understanding of identification reveals a mixture of low- and high-techs at the border. Such acknowledgement is not only key to avoiding developmental views of sociotechnologies of security that neglect low-tech artefacts (Amicelle et al., 2015; Bonelli and Ragazzi, 2014), but also to appreciating the collective interpretive work required to bring data into existence. Such work was only possible thanks to the support of paper sheets that allowed the temporary alignment and re-enactment of the participants’ roles in ways that were not possible with the formalized digital information system.
Yet a question arises. If identity is not ontologically grounded, how can we hold on to a kind of non-representationalist understanding of the reduction of people to data? The following vignette mobilizes the notions of ‘shifting’, ‘spokesperson’ and ‘interessement device’ to illustrate the broader network of actors involved in the identification encounter. It reconstructs in detail fingerprinting, the third stage of the identification procedure.
According to our informants, fingerprinting is the most important step of the identification procedure. It takes place in a separate modular building where border crossers are called in family groups. A specialized officer has been fingerprinting since early this morning, without shifts. My facilitator negotiated that we could spend as much time as we needed in observing fingerprinting, so we can observe dozens. For each person, a preparation stage precedes the actual fingerprinting. The officer moistens the applicant’s fingers, palms and upper palms with water, so that they are legible by the scanner. After preparation, the officer places the persons’ hands on the scanner surface and runs the digitizing software by selecting the ‘Eurodac’ tab in the Hellenic Register of Foreigners. The digitizing software is provided by the European Commission and is integrated with the Hellenic Register only at the interface level: the Hellenic and the European systems do not share data pools. The software is compliant with ANSI-NIST US standards for fingerprinting. Scanners are developed by a multinational corporation based in Florida and were provided to the Hellenic border authorities by the European Commission as part of the 2015 ‘Hotspot approach.’ The scanned digital images are quality checked by the officer. Sometimes images are not of good quality, and then the officer repeats the scanning. In some cases, even the second scanning does not solve the problem, as fingerprints are worn. If image quality is sufficient, they are uploaded. The officer, like most of his colleagues, is not sure where they are uploaded and stored. After a few interviews, we understand they are initially uploaded on the Hellenic Criminal Agency database. From there, they are uploaded on
As shown by Figure 2, the fingerprinting procedure can be analysed as a chain of shiftings, translations. During preparation, the body replaces the individual person, flesh and blood are assumed to ‘speak for’ the person’s identity (i.e. shifting down). What the early literature names reduction refers to this first shifting. It is this specific kind of shifting identity down into flesh and blood that nurtures the gap between identity and identification. Yet this is not the only material shifting possible. Voice, DNA, but also political discourses, personal memories, writings and certificates could constitute alternative material forms establishing who someone is. Previous research has shown that border crossers often demand that different forms of evidence are considered as spokespersons of their identities: school certificates, family trees, linguistic skills (Pelizza, 2020). What for Latour (1992) is only a designer’s choice here acquires political relevance. Translating identity into flesh and blood enacts border crossers very differently than translating it into personal memories, family links or working permits. What for migration studies is a matter of ‘reduction’, under a translational approach appears as a matter of ‘selection’: selection of one material form instead of another.
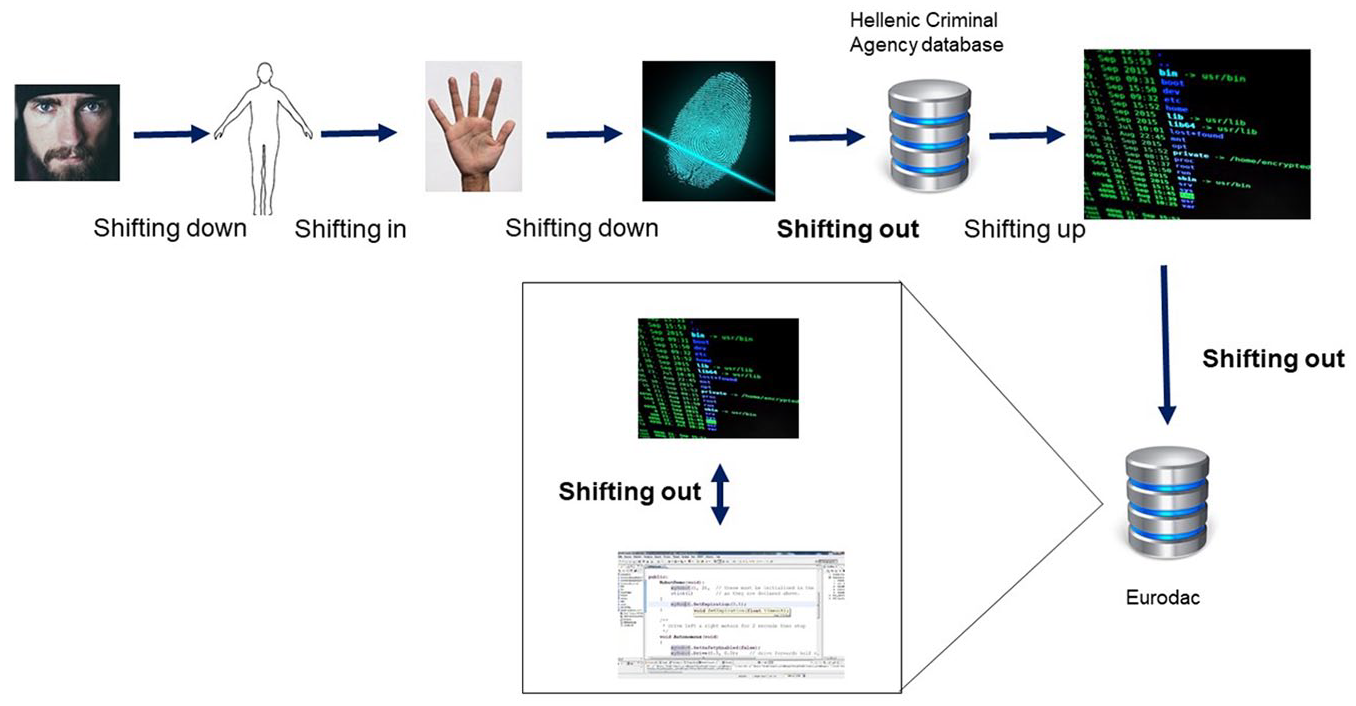
Fingerprinting as chain of shiftings.
The second shifting concerns fingers, palms and palm parts, that come to act as a spokesperson of the whole body. As a synecdoche, they are the parts that represent the whole (shifting in). 14 Yet fingers and palms can be reluctant to enrol. This can happen in the case of dryness. In this case water spray acts as an interessement device: it moistens them in order to support their successful enrolment. More dramatic cases in which fingers refuse enrolment are revealed by burned or worn fingertips. In these cases, resistance to the security apparatus of recognition takes the form of illegible fingertips acting as interessement devices that separate the body from the scanner.
The third shifting concerns digitally scanned images of flesh and blood fingers and palms. Digitization is a case of material shifting down: It translates flesh into digital images. Again, some interessement devices are needed for this translation to be successful. In 2015, the financially compromised Hellenic Republic’s technical infrastructure at the border was renewed with new scanners and digitizing software as part of the EU Commission’s ‘Hotspot approach’ and Agenda on Migration (European Commission, 2015). Hardware and software are produced by US corporate manufacturers and implement ANSI-NIST standards developed by US authorities. ANSI-NIST standards are thought to assure compatibility with the Federal Bureau of Investigations’ (FBI) systems. Scanners, software and ANSI-NIST standards are interessement devices that – while supporting the identification encounter at the Hellenic border – at the same time create trans-national associations with the EU Commission, corporate contractors and the US security regime.
Fourth, scanned fingerprint images are uploaded from the Hellenic Register of Foreigners used at the border into the national Hellenic Criminal Agency database hosted in Athens. This transfer qualifies as shifting out: images are dislocated to another space and time, namely the 24-hour datacentre in Athens. While the ANSI-NIST standards create an association between the Hellenic border and the US security regime, interoperable categories, standards and protocols developed by the Hellenic Police act as interessement devices that create an intra-national association between the Agency in Athens and the border.
Once uploaded on the national datacentre, images must be transferred to the European database
The resistance to enrolment was thus resolved through the introduction of an interessement device, a conversion algorithm that created an association between fingerprints collected at the border and European information systems. As with any interessement device, though, the conversion algorithm has also created disjunctions. As a DG Home and Migration officer recalled in an interview, the algorithm was developed by the contracted supplier and is thus proprietary. As such, its code is not known by competitors, who might thus encounter difficulties in adjudicating future tenders. 16
A sixth shifting occurs, once, eventually codified as bit-strings, fingerprints are uploaded from the Hellenic Criminal Agency database to Eurodac (i.e. shifting out). Eurodac supports fingerprint queries to check whether an individual has already applied for asylum in another Member State. For example, a Hellenic officer can compare the fingerprints of a border crosser lodging an asylum request at the border, and find out that they had already lodged a request in Hungary; in this case the Hellenic asylum will refer the border crosser to the Hungarian asylum service. Given this mechanism, Eurodac is an interessement device by definition.
Finally, the inner frame of Figure 2 shows the translations taking place inside Eurodac. The new fingerprints received from the Hellenic border (blue screen) are compared with a reference population of fingerprints previously acquired by other European Member States or agencies (white screen). The outcome of this comparison can be a hit (i.e. the new fingerprints correspond to stored ones) or a no-hit (i.e. no correspondence). If a match is found, fingerprints previously stored on Eurodac add information from another time and space (i.e. shifting out). For example, the stored set of fingerprints might indicate the reasons for previous identification and the country of first entry.
In summary, the fingerprinting procedure can be conceived of as a long chain of shiftings featuring heterogeneous spokespersons (Figure 2) and diverse interessement devices (Figure 3). Ultimately, such a chain is meant to create an equivalence between an individual caught in the here-and-now of the Hellenic border and a population of bit-strings stored in European databases and previously collected in Member States. Eventually, it is in this exercise of linking together past and present, here and there, that unknown individuals become ‘irregular migrants’ or ‘refugees’. In this sense, identification is never only about individuals: it always links individuals to collectives (M’charek, 2008; see also Ruppert, 2011). Paraphrasing Schwartz-Marín et al. (2015: 863), an individual border crosser ‘needs a population’ to gain their meaning.
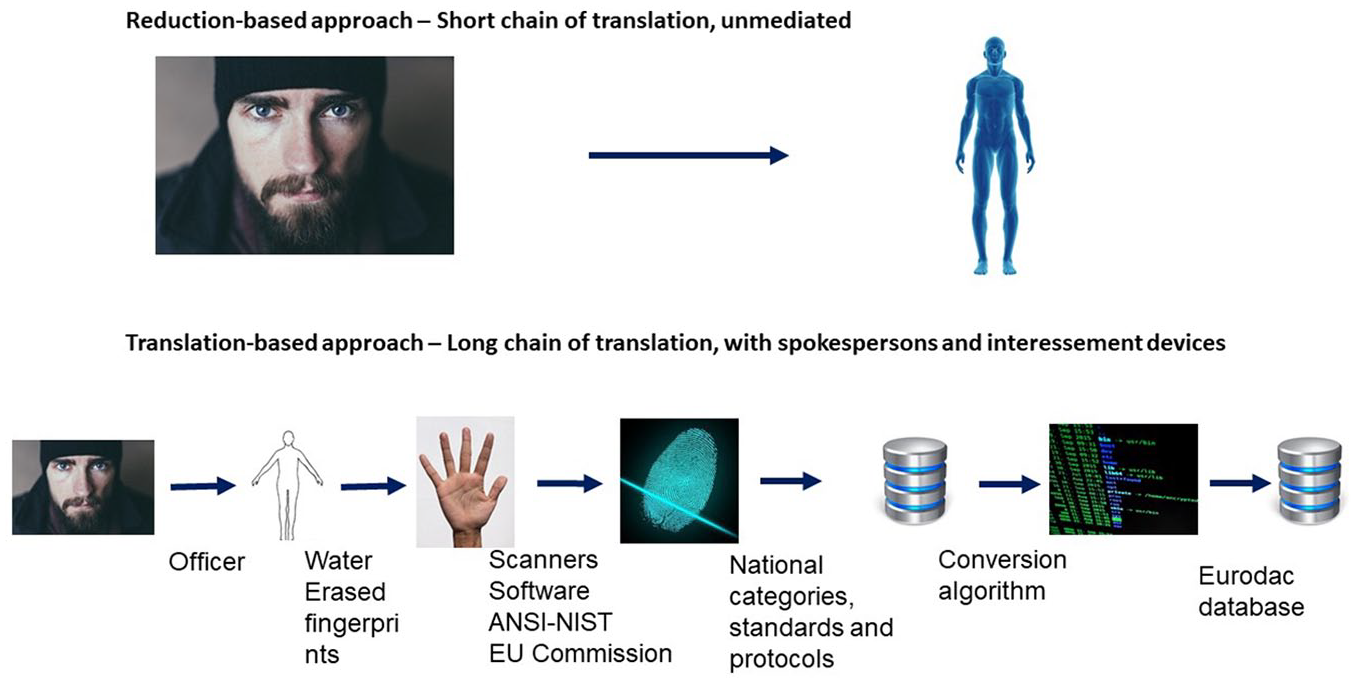
Representationalist and translational approaches to identification.
Three considerations are triggered by this analysis. First, unpacking identification as a chain of shiftings shows that the translation of unknown people into security subjects does not simply reduce a rich sociocultural identity to a biologically bare body. Rather than an exercise of reduction, identification configures as an effort in proliferation. As Figure 3 shows, it requires much longer chains of translation than a reductionist perspective would suggest. What is usually referred to by the reductionist approach corresponds only to the first shifting. Quite the opposite of bare bodies, border crossers are enacted as the outcome of material-semiotic chains made of many – rather than fewer – spokespersons.
Second, a translational approach allows appreciating the material qualities, limitations and affordances of artefacts and infrastructures. By distinguishing between the different types of shifting, my analysis traces how the matter of spokespersons changes. Diverse forms of materiality entail diverse possibilities and limitations: A flesh and blood body cannot be transferred across Europe in real time, a digitized fingerprint can. The image of a fingerprint cannot be uploaded on European servers, though a bit-string can. A digital system requires a level of data formalization that a piece of paper shared only among those present does not. These material transformations deeply affect power dynamics: It takes an oral denial for an applicant to refuse to allow her fingerprints to be scanned, but it is almost impossible to delete the same fingerprints in bit-string format once they are uploaded on Eurodac.
Third, the analysis shows that the identification encounter is never bilateral, but involves a multiplicity of actors, thanks to interessement devices. Interessement devices create associations with actors that are not present in the here-and-there of the identification encounter, but nevertheless affect it: global corporate contractors, the FBI and the US security regime, the EU Commission, national authorities in Athens, and thousands of fingerprinted individuals, to name a few. The state is only one of these actors, enacted by the police officer and the Hellenic Criminal Agency. Far from leaving the individual alone with the state, the identification encounter rather enrols border crossers within broader networks made also by trans-national authorities, business actors and diverse epistemic forms.
Conclusions and third contribution: Implications for the order of alterity processing
Conceiving of identification as a chain of translation presents three sets of implications for the CSS-STS debate on the material infrastructures of securitization. First, conceiving of identification as translation supports replacing a representational understanding of identity, which criticizes identification as inaccurate reflection, with an apprehension of identification as enactment. The translation of unknown border crossers into legible identities does not simply reduce individuals to bare bodies, nor does it fail to represent them. Rather, border crossers are enacted as security subjects, ‘irregulars’, as the outcome of long chains of translation that involve many spokespersons. Power relations are nested and can be contested at each of link of the chain. As we have seen, representationalism is endorsed by authorities: both Policeman1 and Eurodac ask for accurate reflections of ‘reality.’ A different understanding is suggested by the young Syrian man at the border, who acknowledges that there is no
Second, my analyses show that the encounter between border crossers and security authorities is mediated by diverse actors that are not directly involved in the identification encounter. At each translational step heterogeneous actors that transcend national borders, governmental missions and security epistemologies are brought in by interessement devices. A translational approach most evidently reveals that far from being caught in a bilateral relationship with the state, border crossers are made legible by enrolling them in networks featuring heterogeneous actors, including non-state ones. While this argument has already been formulated in the materiality debate in security studies and STS, the translational framework allows opening the technological black boxes and revealing
Finally, this article advances the field of alterity processing (Pelizza, 2017, 2020; Pelizza and Van Rossem, 2021) by bringing further evidence of the de facto alteration of institutional orders at the nexus of securitization and informational migration management (Follis, 2017). The translation of unknown people into legible identities in the name of security does not only involve more and more heterogeneous actors. It also de facto alters institutional orders, what Oudshoorn (2011) has called the geographies of responsibilities. Once the European Commission provides frontline Member States with fingerprinting software that complies with US standards, its role transcends mere operational support. It introduces techno-political requirements for European Member States to align with the US security regime, and the global order of ‘travelling software’ (Pollock et al., 2007). How sociotechnical requirements de facto influence institutional orders is a question deserving further attention.
Footnotes
Acknowledgements
The author wishes to thank the anonymous informants at different governmental and non-governmental organizations who believed in this project and made the fieldwork possible. This research has led me to acknowledge and appreciate the invisible work of many who act at the margins (of Europe and of society), but make the difference. A special thanks to Ermioni Frezouli for fieldwork facilitation and translation in the Hellenic Republic, and Aristotle Tympas for networking support during the initial stages of fieldwork. A word of thanks to the Paris Institute of Advanced Studies, where the Author was Resident Fellow in 2017 and begun developing the first ideas about this article. The author also wishes to thank
Funding
The author disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This article was written in the context of the “Processing Citizenship” project (2017–2022), which has received funding from the European Research Council (ERC) under the European Union’s Horizon 2020 research and innovation program under grant agreement No 714463.
Notes
Author biography
![]() ) research group, supported by the European Research Council. The team investigates data infrastructures for migration management (‘alterity processing’) as activities of European transformation. Pelizza previously worked with government and engineering companies, developing large-scale IT infrastructures.
) research group, supported by the European Research Council. The team investigates data infrastructures for migration management (‘alterity processing’) as activities of European transformation. Pelizza previously worked with government and engineering companies, developing large-scale IT infrastructures.
