Abstract
This paper examines Moria hotspot in Greece as a logistical site which fulfills two different functions within the European migration and border regime. It locates, contains, and sorts individuals locally at the external borders of the EU and creates, inserts, and processes data for controlling people on the move. Based on ethnographic fieldwork in Greece, including interviews with local administrators from the Registration and Identification Service, Médecins du Monde, Frontex and Hellenic Police and a collection of internal and publicly available planning, policy, and management documents and handbooks, the paper scrutinizes how both the movement of migrants and data is organized at the site. By developing an analytic lens of logistics, it outlines a specific mode of infrastructuring which aligns staff from different organizations with databases, devices, and migrants all in one place and organizes mundane practices such as filling out forms, taking fingerprints, signing, and entering datasets along a chain. That way the hotspot is able to locate, sort, and detain those who arrive at the hardened EU border and to create a data infrastructure for controlling, monitoring, and governing further movement by processing data through the bureaucratic channels of the EU’s transnational control assemblages.
Introduction
In May 2015, the EU Commission (2015) presented the European Agenda of Migration and announced the development of a new hotspot approach as part of an immediate action package to assist “frontline” member states in “managing exceptional migratory flow”. The hotspot approach stated that EU agencies – namely Frontex, European Asylum Support Service (EASO), the European Police Office (Europol), and the European Union’s Judicial Cooperation Unit (Eurojust) – should work with Italian and Greek authorities on the ground to help them process identification procedures, asylum applications and return operations. In the following months, 11 hotspots were set up, and the Moria hotspot on Lesvos was put into operation in October 2015 (Deutsche Welle, 2015). As registration, assessment, and redistribution points near the EU external border, the hotspots channel migration flows, letting pass those who are in need of international protection and sending back those who are not (EU Commission, 2016).
With the implementation of the EU-Turkey Deal (European Council, The Council of the European Union, 2016), a special arrangement came into force, stating that all migrants who arrived on islands in the Aegean Sea after 20 March 2016 will be deported back to Turkey, unless “they can prove that Turkey is not a safe third country for them” (Hess and Heck, 2016: 3) or they are categorized as vulnerable by the Hellenic Asylum Service (HAS).
The Schengen System initiated an extensive transformation process of border control and a “re-bordering” of nation states within the EU. In contrast to voices which, especially in the 1990s, proclaimed a deborderization of Europe – where goods, people, and capital could circulate smoothly and freely – Walters (2006) states that the implementation of Schengen was counterbalanced with a series of “flanking measures”. On the one hand, there is a hardened exterior frontier with watchtowers, fences, and detection devices (Walters, 2002: 573). On the other hand, Walters observes a “spread of surveillance into the hinterland” (Foucher, 1998: 238), which he describes in terms of Deleuze’s (1995) notion of control. Migration and border control has a networked form with many centers, which is no longer territorially fixed. Its aim is not to territorialize, to govern individuals and to shape identities by institutions such as the school or the prison but to produce filters and gateways for people on the move separating the bad from the good and producing channels of (im)mobility by re-identification arrangements (Adey, 2012: 196). As Walters (2006) points out, this is related with databanks, identifiers – such as fingerprints which work as passwords – scanners, and security professionals (197).
In this paper, we argue that the hotspot can be understood as a merging point of both sides of the European migration regime, being part of the hardened exterior frontier of the EU and of transnational control assemblages – in one place. Drawing on ethnographic fieldwork including interviews with local administrators from the Registration and Identification Service (RIS), Médecins du Monde (MdM), Frontex, and Hellenic Police and internal and publicly available policy and management documents and handbooks, we will ask how processes and practices at the hotspot make people governable and containable at the site as well as how the hotspot is organized so that (re)identification and control is distributed to actors at numerous other sites by multiplying data identities within information infrastructures. The hotspot, we argue, is a logistical device which locates, sorts, and detains those who arrive at the hardened EU border and creates a data infrastructure for controlling, monitoring, and governing further movement by processing data through the bureaucratic channels of the EU’s transnational control assemblages.
Our account draws on two important, but seemingly contradictory, interpretations of what the hotspot (ontologically) is in recent literature in critical migration studies, science & technology studies (STS) and surveillance studies approaches. On the one hand, it is a space of containment aimed at regaining “control over migrants’ autonomous geographies” (Tazzioli and Garelli, 2018: 2) by keeping migrants in a local set-up of fences, gates, containers, and in many cases, such as the Greek hotspots or the hotspot on Lampedusa, on islands which are mostly (but not only) located at the margins of Europe. However, as Pallister-Wilkins (2016) argues, barriers at the exterior frontier of the EU are not so much about building up a “Fortress of Europe” to prevent people from crossing the border at all, but about channeling mobilities in an organized way. Tazzioli and Garelli (2018: 2) have a similar stance and understand the hotspot as a site where both forms of containment and channels of mobility are generated. Drawing on field work on Lesvos, Tazzioli and Garelli understand hotspots as chokepoints in sorting migrants into different institutional tracks and organizing channels of “forced convoluted mobility” (Tazzioli and Garelli, 2018: 9). While some are relocated within the EU by the European Asylum Support Office (EASO) and the Office of the United Nations High Commissioner for Refugees (UNHCR), some are eligible for asylum in Greece and may move to the mainland and others are detained and repatriated (Antonakaki et al., 2016).
Alison Mountz (2011) conceptualizes such island set-ups as components of a broader pattern of remote detention that “hide asylum-seekers from view of media, human rights monitors, and publics at large” (118). Although this is not true for all hotspots in the EU, such an approach allows us to see how temporal incarceration is one crucial component of channeling mobilities and how hotspots are part of a broader strategy of a European border regime which seeks to contain sites and issues of organizing mobilities at “enforcement archipelagos” (Mountz, 2011: 118) at the external border of the EU.
On the other hand, the hotspots can be understood as crucial components of EU-wide
Processes of datafication are tightly connected with what Muller (2010) calls “biopolitical governance”. He observes how the focal point of governance shifts away from the territorial borders to the elements in motion – the migrants – who then are assessed in terms of risk. The digitalization of registering migrants as well as biometrics play a crucial role in such a regime by turning individuals into traceable and sortable objects and making the exchange of information between agencies possible (Adey, 2004: 507). In this context, Salter (2005: 47) speaks about “hyper-documentation”, as it is the collected and exchanged information about a traveler, which reveals “intentions – risk factors – which the individual him/herself will not reveal”. Processes of datafication do not only bring data doubles to circulation but also make them applicable to many different purposes and regimes of governing. Franke (2009) for example shows how the UNHCR pushed the electronic registration of refugees forward by developing portable workstations, manuals, and validation measurements and sandwiched the data doubles of the refugees with other data. With the help of different applications such as Geographical Information Systems (GIS) the UNHCR then developed tools for a spatial analysis of camps, where geographies and places, different characteristics of populations (such as women and vulnerable people), and incidents (such as rapes) were related to each other. Similarly, Frontex adds up registrations of migrants taking place at Greek hotspots and brings the data together with data from Frontex incident, intelligence, and debriefing reports in order to create maps of migratory routes at the EU’s external border, risk analysis for operational planning and reports for the EU Commission and EU member states (Tazzioli and Walters, 2016).
The Greek hotspots are the “entry points” not only for migrants but also for the creation of data doubles in several databases. Data entries are created in the Hellenic Police, HAS, RIS, and Eurodac databases, which lay the foundation for re-identification via passwords – which can be names, identification numbers, or biometrical ones such as fingerprints – at a later time and another place. With that, the Greek hotspots as logistical set-ups realize
In what follows, we will zoom into the Moria hotspot at Lesvos and give an empirical account of its material set-up with its containers, barriers, and fences as well as of the staff doing registration and identification and the chain of identifying, tagging, processing and sorting. Studying such a site empirically helps both to bring some of the more technocratic and anxious diagnoses down to earth and to see some of the connections between the various transformations of contemporary borders in highlighted detail. We will use the analytic lens of logistics, which allows us to look at how machinery of aligning different organizations, personnel, databases, forms and migrants and processing different channels is set up and maintained. Before we turn to the main empirical part of this paper, we will describe and situate this analytic lens as a concept and heuristic device. In the last part of the text, we will show how the vocabulary of logistics enables us to understand
Logistics as a concept and heuristic device
A conceptual and methodological warning message is needed before we can focus on the registration practices and related data infrastructures at the hotspots in detail. The analysis we present is an ethnographic account, and as all ethnographic accounts are, it is a serious but always reconfiguring exercise of “writing culture” (Clifford and Marcus, 2010). The data we use in this particular piece of writing are based on fieldwork that one of the authors is still conducting at Moria hotspot on Lesvos and on a collaborative analysis of transcripts from interviews with Frontex officers, Greek bureaucrats and members of various NGOs as well as of forms, handbooks, and interrogation guidelines used in the registration process. There are three important reasons why we will explicitly not wallow in the well-known “rhetorics of field access” (Meyer, 2013) and refrain from producing ethnographic narratives that give situated accounts of the visual and atmospheric set-up or name key informants by their made up names.
The first reason is conceptual. In this paper, we draw mainly on Actor-Network Theory (ANT), an approach from the interdisciplinary field of STS that has prominently stressed the role of non-humans – devices, procedures, circumstances, even scallops (Callon, 1986), and microbes (Latour, 1993). Although ANT has moved away from stories about non-humans and turned to questions about the political ontology of devices and other entities and the multiplicity and heterogeneity of infrastructures, this conceptual legacy urges us methodologically towards a “sociology after humanism” (Breslau, 2000). Ethnographic narratives about informants at least have to be symmetrically supplemented by narratives about the devices and circumstances in place. We will come back to some of the conceptual avenues for further analysis beyond the scope of this paper at the very end.
The second reason is methodological. We use logistical terms in this article as an epistemological and alienating device (Hirschauer and Amann, 1997) to carve out the organization of labeling and tagging, localizing, moving and caring for people at the Registration and Identification Center (RIC). With logistics we refer to “the management of the movement of people and things in the interests of communication, transport, and economic efficiencies” (Mezzadra and Neilson, 2013: 206), and we use these terms intentionally as rhetorical tools to produce accounts that stick to the devices, technologies, procedures and categories, data, identities, forms and bodies that are produced, circulated and thereby transformed, aggregated and assembled in very specific ways. We are fully aware of the cold and maybe even terrifying impression that such a language might create – especially when we are dealing with migration and the personal and collective sorrow, grief, and despair that many practices of migration and border control constitute. Nevertheless, we use these terms to create a narrative that is as far away as possible from the accounts that populate our media ecology and the consternation and outrage that fuel the current public debate. Instead, it helps us focus on the bureaucratic details of the management of and the care for the flow of bodies and data at the hotspot.
The third reason is empirical. There is a growing body of evidence that logistics has grown out of a niche existence as a field of specialization and expertise and an auxiliary service and has conquered some of the most consequential production sites of contemporary social order during the last three decades. We are increasingly living in “logistical worlds” (Rossiter, 2014) organized by “tracking and tracing” (Kanngieser, 2013) that “calibrates and co-ordinates movements across different borders, taking into account the varying conditions that apply across them” (Neilson, 2010: 133). We have reason to suppose that logistical practices are at the core of the contemporary machinery of governance – the way that registration practices and related data infrastructures at the hotspots are organized is a telling example.
Logistics of the Registration and Identification Center (RIC) at Moria hotspot
In the introduction of this paper, we sketched how the hotspot approach is conceptualized in EU policy and how different scholars in critical security and migration studies connect the hotspots with different modes of governing. In this section, we will focus on one of the implementation sites, the RIC at Moria hotspot on Lesvos in Greece, and examine how people and data are processed and sorted into different channels by creating different data identities as a practical accomplishment. 1
Moria camp is located in the south-east of the island and ca. six kilometers away from the island capital Mytilini. It was built in a former military camp and is surrounded with fences, walls, and gates. The main entrance is guarded by Hellenic Police officers and RIS staff. However, it is open for people living and working in the camp. In the camp, you find several residential areas, which are ethnically separated, and a kind of central road with small stores and stalls leading to a central place with benches, an information point and a distribution point for non-food items, as well as to a heavily fenced area of the HAS and EASO. Moreover, there are closed sections guarded by Hellenic Police for people to be repatriated and for unaccompanied minors. And finally, there is the so-called RIC, where arrivals are first brought by buses from all over the island in order to be identified and registered. This is the place the paper is about.
The busses transport the migrants to a closed area with a big tent and a system of seven containers used for basic registration purposes as well as a first contact point with various NGOs (see figure 1).
Registration and identification, Center Moria, October 2016. The process of identification and registration, Moria, October 2016.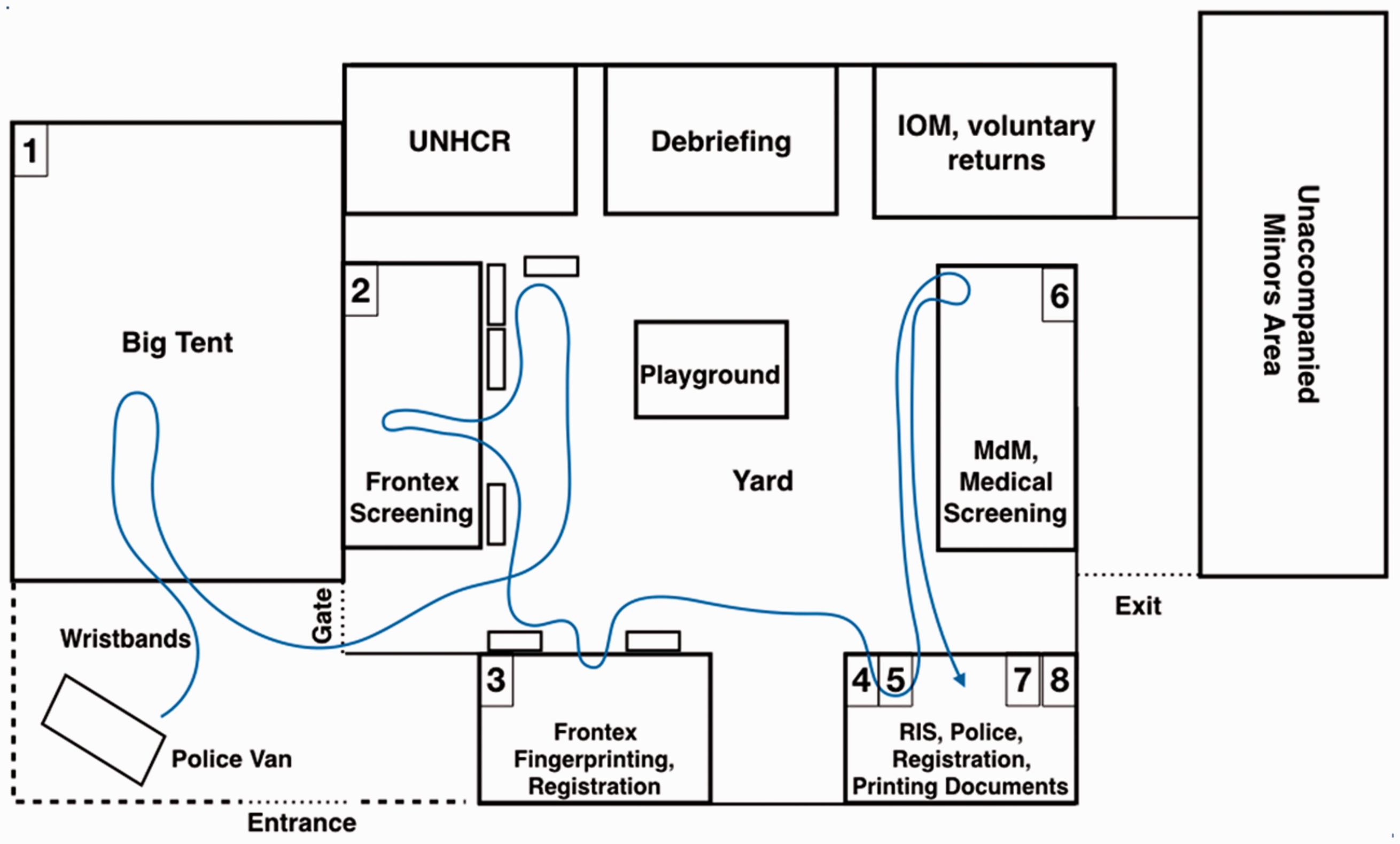
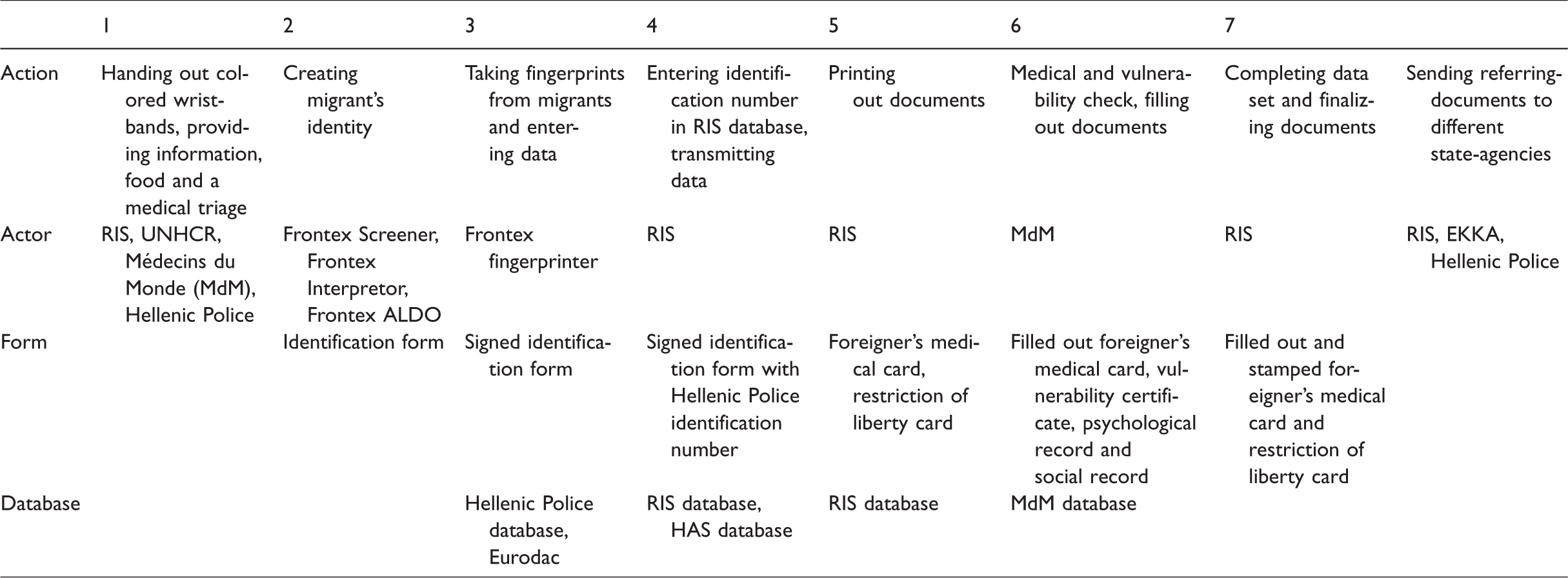
To facilitate counting, arrivals are usually equipped with a colored wristband marked with a number. The color marks them as one cohort, a number consecutively counts and queues them – first in, first out. The size of the incoming batch has to match the registered batch at the end of the procedure. By that, incoming people are transformed into logistical entities like cohorts and single “stock keeping units”, and a monitoring mechanism of numbers of in- and output is installed. In the big tent – the first station for the arrivals – basic information, food and drinks and a quick medical triage is provided. It is similar to a “deposit” (Kemp and Young, 1971: 31), as groups of people are kept for further transportation at one place and divided into smaller units by a Greek police officer who, as a “flow manager”, then forwards the units one by one through the different stations of the identification and registration procedure. She also makes sure that migrants and documents stay together.
The analytics lens of logistics allows us to make sense of these processes and practices. Logistics is about the organization, standardization, and stability of processes that deal with flows and with entities that move. Whatever is stored, it is only contained to enable further processing. In exactly this way, grouping and monitoring are not just practices of detainment, they are part of an arrangement of managing continuous flows of people that are treated as of the same kind. However, as Frontex officers stationed on Lesvos in 2016 told us, arrivals often did not wear any wristbands. Instead, numbers on pieces of paper were handed out and those to be registered were called into the containers one by one. Sometimes there was not any numbering at all, and the arrivals negotiated amongst themselves who was next. On hot summer days, people often did not wait in the big tent, but were taken directly to the yard to sit down under a big awning and wait for registration. Sometimes hundreds of people were sleeping, talking, and playing there. It also sometimes happened that the big tent was still occupied by arrivals of the day before, as housing in Moria camp could not always be organized that quickly. All these cases show that the logistics only work if the arrivals cooperate – for example, by waiting patiently and paying attention to who is next or who might need help. Dockets and routing slips, for example, are not just attached by officers and flow managers, but are collaboratively produced. We will turn to this procedure in the next section.
Enacting truthful subjects and valid identification in Frontex screening procedure
The first step to enact a governable migrant subject is to produce and enact a valid identity. This is done in the screening section. The container is equipped with four tables with one Frontex Screener and one Frontex Interpreter each and another table with a Frontex Document Expert and a Frontex Interpreter. All incoming migrants are screened, one by one, except accompanied minors under 14. Screening is about creating and enacting characteristics of the arrival, which decisively prepares the grounds for the further institutional procedure. The core problem of screening is to discern a valid identification, even against contradictory claims by the interviewed migrant and often without having any “hard” verifier like passports or birth certificates (Coordinator RIS, 2017, personal communication).
A form is used in this screening process, which is composed of a limited number of classifiers that have been added and modified repeatedly. The current version encompasses 11 obligatory items like “language”, “name”, “date and place of birth”, “address” and “nationality” or “willingness of applying international protection”, and six “additional items” like “vulnerable group”, “owner of passport”, “reasons of flee” or “final destination”. Identification is completed when the obligatory items are filled out, concluded as valid, and authenticated by the parties involved. One screener, one interpreter, and the migrant being interviewed, as well as different indication tools are involved in the screening arrangement, which very much resembles an interrogation (Frontex Screener, 2016, personal communication). Multiple indicators in combination are supposed to give hints as to if the interviewees are lying (Frontex Screener, 2017, personal communication). The interaction keeps going, as long as the screener doubts statements of the interviewee. In this process, the interviewed migrant gives more and more information about a life that she claims to be hers.
The migrant subject is enacted in this continuum between registration and investigation. If, for example, a valid passport can be shown, then the screening is over in five minutes, as the document can state who the migrant is. Neither biographical, local nor cultural knowledge is needed. But in case of a lack of such testifiers, a subject is enacted, which stands “behind” the statements as a guarantor, which has to be acknowledged as truthful (enough). The screening is very much about finding this subject at the end, which is accounted as not-lying (Frontex Screener, 2016, personal communication) and trustworthy, and which is able to furnish particulars on the items on the identification form. In the screening interviews, this occurs often when the interviewed migrant makes a confession at the end and reveals where she “really” is from (Frontex Screener, 2017, personal communication). The process of constituting a subject accounted as trustworthy is a result of a collaborative effort, but this collaboration is asymmetrical by design.
Finalizing identification – Filling out the identification form
It is the screener who decides how the identification form gets filled out. Once she feels sure about who the interviewed migrant actually is, she inserts discrete and unambiguous items. The identification form consists of different sections: a header, boxes for a profile picture and for the language spoken, then a battery of items in a table giving details of the interviewed migrant, signatures and a list to name accompanied minors as well as a space for additional notes. Objections, differentiations, or negotiations of the screening process are invisiblized in the form – or silenced by using residual categories (Star and Bowker, 2007): if the interviewee is not willing to cooperate and the screener does not know at the end where she is coming from, the screener fills in “unknown” (Frontex Screener, 2017, personal communication), and if the interviewee is willing to talk, but the screener is unable to come to a conclusion about her nationality, the screener can enter “not identified” (Frontex presentation, 2016, personal communication). Moreover, the new version of the identification form draws a distinction between “claimed” and “presumed” nationality, where both answers can be entered even if they contradict. However, the final decision on the nationality is delegated to the RIS later on, which decides in favor of the Frontex Screeners and in absence of the migrants. By doing this, the identification is finalized, fixed as well as authenticated and it becomes the basic scaffolding of a migrant subject after leaving the registration procedure.
The identification form, with its collected characteristics of the migrant, serves as a blueprint and a backup for further digital identities produced on this registration and identification track. This again is a logistical operation: instead of working with the sorted and stored items, logistics as an efficient technology and an epistemic field of optimizing and controlling flows works with data and representations. Forms are sorted, stored, and counted, and data from these forms is rearranged, recalculated, and aggregated while the items themselves can either be kept in one place or moved around. The materiality of this paper-based form guarantees immutability because it is authenticated by a fixed structure of reference, which makes it a packing unit for transport and circulation that is not further divisible. It ensures the surveyed characteristics are bound to a name and to a migrant subject represented by their signature, but also that the screening procedure has been processed, finalized and accepted by the signatures of all parties involved.
By the end of the screening procedure, an identity of the screened migrant has been set up consisting of a set of predefined categories. Its characteristics are limited and discrete and are materialized and preserved in the paper-based identification form. Confirmation and authentication by the Frontex Screener, Frontex Interpreter and the screened migrant make this form to a warrantor of the only valid identity and let the administrative procedure continue. However, the actor-network of screened migrant, identification form, and flow manager only build a loose connection between the stated identity and the body of the migrant.
Enacting data identities in Hellenic Police database application
In the next container, some of the data collected on the identification form is inserted into several databases and applications, namely of Hellenic Police, Hellenic Asylum Service (HAS), Registration and Identification Service (RIS) and European Commission, and different identifiers are attached. As we will see, these registrations build the basis for subsequent administrative work by enacting
A Frontex officer takes a portrait picture of the migrant, copies it on her computer’s desktop and starts entering the characteristics from the identification form into single entry fields of the national web-based database Kartographisi Kikloforias Allodapon (Mapping of Foreigners’ Circulation) of the Hellenic Police. As neither the signatures of the interviewed migrant, interpreter, and Frontex Screener nor the names of the latter two are entered in the database, the references to the construction site of data are cut. Instead, after inserting all entries, the photo is uploaded and added, and the data entries are linked with an identification number – an identifier, which is then also noted on the identification form by hand (Frontex Fingerprinter, 2017a, personal communication).
Migration from paper form to database turns out to be complicated and potentially error-prone, as the Hellenic Police system is only available in Greek and with Greek letters, which only a few Frontex officers can read and use (Frontex Fingerprinter, 2017b, personal communication). To register someone, most of the Frontex officers therefore do this in a parrot-fashion way of just clicking through the system. In cases of mistakes or wrong clicks Frontex officers often need assistance from a Greek police officer from another container. An informant told us that often there is a match between the new data entry and other data entries within the Hellenic Police database. In such a case, the screen lights up in red and a list of entries pop up in a window. Then Frontex officers also have to bring the Hellenic Police in. As a hit too often turned out to be a false alarm, Greek officers got annoyed and Frontex officers started to ignore the alert (Frontex Fingerprinter, 2017a, personal communication).
Feeding databases is crucial for logistics. Single characteristics of the fixed set-up on the identification form are turned into packing units that can, as data, be mobilized, moved around, and reassembled. Standardized entries next to other entries in an information system are much more compatible and connectable to bureaucratic practices. They can be searched, accessed, and modified easily at different points in time and space. As additional data can be inserted also from somewhere else and at a later time, data identities can grow and change over time and a biography of incidents and encounters can emerge.
However, data identities are not just there in the database, they need to be enacted by identifiers. Identifiers are for example a name, a number or fingerprints, and they link data to a dataset. In our case, a profile of an individual, what we call a data identity, is enacted. Identifiers are crucial for all kinds of logistical set-ups, as they make datasets traceable and connect (digital) addresses to entities such as bodies or goods (Dodge and Kitchin, 2005). In the Hellenic Police database, there are identification numbers used for all different kinds of entries, not only for those of illegal border crossing. As identification numbers are consecutive, they ensure that one number enacts one and only one data identity. Numbers are more precise and reliable than names, as the latter could be misspelled with troubling consequences. The entry, for example, could not be found in the future and duplicate entries could be created, or different registrations under identical names could cause commingling of data in subsequent procedures. That is also why the identification number is on the temporary ID (“operational note”) which states the suspension of deportation for 30 days and is handed out to the migrant at the end of the overall procedure.
With their registration in the Hellenic Police database, individuals can be re-identified at different re-identification arrangements, for example by police at airports or police stations, but also by mobile units. In the process of checking ID-documents and crosschecking the data with the police database, the individual is urged to give an account about who she is. In case of a match in the database, a digital identity is enacted, which verifies or falsifies the account of the screened. Re-identification of people being registered on Lesvos and having a temporary and territorially restricted ID also turns out to be a localizing tool which basically says: “You are A, you have been registered in X and you are allowed to stay in Y. But you are here in Z, and that is why you have to go back to Y”. In such a case, the screened will be searched, arrested, and readmitted to the initial place where the migrant was registered for detention (Hellenic Police, 2016: 3).
Enacting data identities in European Dactyloscopy (Eurodac)
After completing the data entry from the identification form into the Hellenic Police system, the Frontex fingerprinter clicks on a button labeled with “Eurodac”. A program opens and guides through the fingerprinting procedure, displaying one finger after another. The scans are automatically checked if they are good enough. If the screen lights up red – which happens quite often, as informants told us – the scan has to be repeated. In most cases, however, the quality of the fingerprints is judged by the system as “sufficient” and the screen flashes yellow. In only very few cases is the scan evaluated as “good”, which would cause a green flash. If some fingers, or even the whole palm, is missing due to amputation or injuries, it is quite tricky to enter that information into the system. The Eurodac application is rigid in that regard: it needs to be fed with a scan in order to move on to the next step, the next finger or palm. Frontex staff deals with that by scanning any other finger or the other palm. When all fingerprints are taken, the fingerprinters click on “confirm” and the fingerprint data along with some other data automatically added by the system is sent to the Eurodac office in Athens. 2 After some time, which could take a few minutes or up to an hour, the screen lights up green, data entry is marked as successful, and a Eurodac identification number is added to the dataset linked with the identification number (Frontex Fingerprinter, 2017a, 2017b, personal communication).
The idea of Eurodac is that national asylum and immigration services, and since 2013 also police authorities of EU member states and Europol, can check if a migrant has already been registered by another member state (European Commission, 2013: 9) by processing a re-identification procedure. Fingerprints are used as identifiers that turn parts of the body into “stigmata – signs on the flesh” (Van der Ploeg, 1999: 301) corresponding to the pattern of an image in a database. They are used to make bodies accountable without needing to rely on a subject participating in the collaborative process of identification – for example, by claiming who someone is and where someone comes from. Kuster and Tsianos (2013) speak about bodies, which are made legible without the need of making somebody intelligible. When fingerprint images are uploaded to Eurodac, they are automatically matched to all other representations of fingerprints in the database. In the case of a hit, a data identity from the database is enacted.
In contrast to systems, like the national police or national asylum databases, that keep track of a case history which can be modified, extended or linked with additional records and events, data identities enacted in Eurodac are only about making the starting point of a migrant’s history within the institutional route of the EU visible. They refer to the “date on which the fingerprints were taken”, “date on which the data were transmitted to the Central System”, or to the “Member State of origin, place and date of the apprehension” (EU Commission, 2013: 11). The enacted data identity also leaves a trail to the data entry within the Hellenic Police database, as it includes the “reference number used by the Member State of origin” (EU Commission, 2013: 11), which is in our case the identification number of Hellenic police database. Except from “sex”, personal characteristics such as name, nationality, date of birth, and the like listed in Hellenic Police database are not included.
Not only does the data-identity in Eurodac enacted by matching fingerprints look different than in the Hellenic Police database, but so does the form of addressing a subject. In the case of a hit, it basically says: “we identify you, even though we do
RIS: Finalizing ID-entities and sorting migrants
While Frontex officers take care of the registration in the Hellenic Police and Eurodac databases, RIS personnel is responsible for the registration in the RIS database. Frontex officers add the identification number for the Hellenic Police database manually to the paper-based identification form, along with two “secret” signs like a circle and a triangle to confirm that Frontex identification screening and registration have been finalized. Then the identification form is handed over to RIS personnel, who have been working inside the fingerprinting container at separate tables equipped with their own computers since June 2016. As far as we could find out, Hellenic Police, RIS, and HAS have one common web-based platform with three different database applications, one for each organization. Each application can approach data with some restrictions and on a need-to-know basis. As the identification number from the Hellenic Police database is written on the identification form, RIS staff types it into their own application and the data attached to the identifier pops up. RIS data identity is enacted with an additional identification number, numbering all first reception cases consequently. In case the “willingness for applying international protection – yes” is stated on the identification form, RIS staff is supposed to tick a similar box within the RIS online application. By doing this, HAS staff has access to these datasets, too. In contrast to the police and HAS databases, the RIS database is not built for piling up a case history, but rather for providing a basic identity as a backup for the other institutions with all the relevant data stored for subsequent procedures. It thereby has to be kept updated, for example, if it turns out that certain characteristics like nationality, age, or vulnerability have to be changed. RIS is also responsible for archiving the paper-based identification forms.
After creating a RIS identification number, RIS staff copies the data and puts it into various templates such as the “Foreigner’s medical card” and the “Restriction of liberty card”, which are then printed out and handed over to the migrant accompanied with the admonition of not losing it. These two documents are used as identification papers at the hotspot. Migrants should carry them all the time and agencies require them for any kind of service. The migrant with the “Foreigner’s medical card” is sent to the MdM container for medical screening. A nurse fills out the medical card and inserts the characteristics in the MdM database, issues a vulnerability certificate, and sends card, certificate, and migrant back to RIS staff. There the vulnerability certificate is taken and its characteristics are inserted into the RIS database. With that the RIS data identity is officially completed. The “Restriction of liberty card” is the official document which attests not only name, gender, nationality, and a facial image but also the illegal entering in Greece and the temporary suspension of deportation (Kuster and Tsianos, 2016). Equipped with a set of identifiers (name, face, Hellenic Police identification number), this ID-entity makes it possible to enact its digital counterparts in the Hellenic Police, RIS, and HAS databases. At the same time, it subjectifies its carrier by stating a name, date and place of birth, sex, and legal status. At the end it is stamped by Hellenic Police and the tie between body and identity is certified officially. In other words, this initiation act incarnates a legalized subject accredited as a non-asylum applicant, as asylum applicant or as vulnerable, that will go through the following procedures, and that can officially be moved or kept in place.
Besides updating and finalizing identities, handing out ID-entities and enacting legalized subjects, RIS additionally produces official referring-documents assigning responsibility to other authorities. Identities on the transferring document with the item “Willingness of applying for Asylum: No” are sorted into the category “Non Asylum Applicant” and forwarded to the Hellenic Police, identities with the item “Willingness of applying for Asylum: Yes” are sent to the HAS and those classified as vulnerable by MdM go to E.K.K.A. (National Centre for Social Solidarity). For those who are classified as unaccompanied minors, RIS remains in charge. The documents produced by RIS go to the other agencies via email and as paper forms, forwarding responsibility to the other organizations. With that, the registration and identification procedure is completed and people are sorted into different institutional tracks, which produce “asymmetries of mobility and exclusionary partitions” (Tazzioli, 2017: 2769).
Modes of infrastructuring migration and border control and the politics of mobility
In the previous sections, we examined the logistical set-up of the RIC at Moria hotspot. The question that guided our analysis was: How do processes and practices at the hotspot make people governable and containable at the site, and at the same time how are processes and practices organized so that (re)identification and control is distributed to actors at other sites by multiplying data identities within information infrastructures? By following the flow of people and data through the RIC at Moria hotspot, we reconstructed how
As we can see, the circulation both of people and data operates by set-ups where not only a variety of actors but also different infrastructures and information systems are interconnected. This empirical account of the local set-up and of the practices of connecting, forwarding, and making fit also contributes to recent works on “politics of mobility” (Squire, 2011) by conceptualizing circulation in terms of infrastructure (Xiang and Lindquist, 2014) and logistics. In such an understanding, mobility is viewed as an effect of “infrastructural moorings” (Urry, 2003). In a programmatic paper, Lin et al. (2017) emphasize and encourage a perspective that “shifts away from the people who move (as most migration and mobilities research tends to fixate on) towards those human
Turning to a vocabulary of logistics, we argue, enables us to understand
This understanding of logistics as a lens to conceptualize modes of infrastructuring as practices of chaining things, people, and data through time and space can be pushed even a little further by referring to recent work in STS, more precisely in “Actor-Network Theory and After” (Law and Hassard, 1999) or “Post-ANT” (Gad and Jensen, 2010). This is not the place for an in-depth conceptual discussion, but we think that it might be useful for further work on politics of mobility, infrastructure, and logistics as well as on border and migration assemblages to highlight three fruitful avenues for further research and conceptualization.
Firstly, ANT focuses on “how local events tie up with one another” (Michael, 2017: 25) and thus brings chaining activities across different actors and sites into view. It also analyzes local settings but additionally asks how they are extended in time and space through networks (Latour, 1996a). Studying “control assemblages”, “logistical spaces” or “spaces of containment” thus means to not describe them from a bird’s-eye view as homogeneous macro-structures characterized by functions and logics but from a perspective which is right in the middle of events and which examines how distant pasts, faraway places and absent actors are made present in situations and how situations lead to other points of time, places, and actors.
Secondly, Post-ANT critically inquires seemingly stable entities such as subjects and objects as well as bodies, technology, markets, and states. Law (2008: 635) recommends turning to a “sociology of verbs” to understand how networks and their material and semiotic elements are enacted through practices in heterogeneous and multiple ways (Passoth and Rowland, 2010: 827). How these multiples (Mol, 2002) are brought together coherently, or if they are at all, is not only a practical matter but also an achievement which can change over time (Law, 2007: 13). Such thinking has already gained some traction in critical migration and security studies. Amicelle et al. (2015) for example emphasize a focus on devices – which they understand as “non-linear result[s] of struggles, controversies and translations” (297).
Thirdly, ANT has developed concepts for describing struggles, competition, and re-translation activities in building actor-networks. Entities can refuse being enrolled any more (Callon, 1986), re-translate relations or forge new alliances (Latour, 1996b). Such an approach does not only focus on the objects and subjects being brought to circulation – in our case migrants, forms, and data – but also on the relations among the actors which make circulation possible. Andersson (2016) for example draws on Callon’s (1986) concept of enrollment and gives instructive insights of how the Spanish Civil Guard could extend its power, facilitate information flows, and expand cooperation in an asymmetrical way by mobilizing different actants for the projects Seahorse and Eurosur (Andersson, 2016: 34f.).
Finally, (Post)ANT shows how power and forms of subjugation, resistance, and subversion are located right in the middle of actor-networks. An analysis of infrastructures of migration and border control, which takes into account how absent events and actors are made present in local settings, multiplicities are enacted, and actors are enrolled, grounds a critical inquiry in specific material set-ups. But it also makes it more complex, as multiple forms of power relations have to be carved out. If infrastructure is understood as a multi-linear ensemble with different lines, variations, bifurcations, and derivations, then a critical inquiry also could be conceptualized as a multiple bringing different accounts of subjugation, resistance, and subversion together. Although this was not the scope of the paper, as we tried to develop a detailed empirical account of the logistical processes, it hints at some issues such as the enactment of multiple data identities and subject positions, or asymmetries between screeners and migrants as well as between Frontex and Hellenic Police officers. This could be a starting point for further investigation.
Footnotes
Acknowledgements
An earlier version of this paper was presented at the “Peopling Europe through Data Practices” conference at Tate Gallery of Modern Art in London in March 2017 organised by Evelyn Ruppert and the Arithmus project team. We are grateful to them, to the anonymous reviewers and the journal editors for their very helpful comments, as well as to Bernd Kasparek and Dimitris Parsanoglou for giving valuable insights into the involvement of governmental and nongovernmental actors at the Hotspots in Greece during the initial stages of fieldwork. Finally, the authors thank all the informants who supported the fieldwork.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article. This article is funded by Deutsche Forschungsgemeinschaft and Exzellenzinitiative des Bundes und der Länder.
