Abstract
Information security is one of the most crucial considerations in digitising Oil and Gas (O&G) organisations. For ensuring information security policy compliance, O&G organisations enforce heavy security requirements. The purpose of this article is to assess how O&G employees cope with stressful information security tasks and how security-related stress (SRS) is related to information security policy violations among O&G employees in developing countries. Based on the coping theory, this article develops a theoretical framework to examine O&G employees’ intention to violate information security policies. The framework is tested using a survey of 270 managers/executives from 150 Malaysian O&G organisations. The results indicated that O&G employees perceive security requirements as stressful to follow and adopt avoidance coping strategies that lead them to violate organisational information security policies. For practitioners, the study findings demonstrate the prevalence of technostress in O&G organisations and suggest alternative mechanisms to address the stressful effects of information security requirements. This article contributes to the information system security literature by testing procrastination and psychological detachment with SRS in the context of developing countries' O&G organisations’ employees and provides an understanding of how O&G employees adopt avoidance coping.
Keywords
1. Introduction
Oil and Gas (O&G) are an important sector for many mineral-extracting developing countries. Critical energy infrastructures (CIEs), which include installations for extracting O&G, terminals, storage facilities, refineries and so on [1] are paramount to the O&G sector. Attacks on CIE have proliferated over the past years [2]. Cyber-attacks on CIE in recent years have raised national concerns to protect such infrastructures to ensure economic stability and sustenance [2]. Cyber-attacks in the O&G sector have been reported in several forms ranging from malware espionage to high-level intrusions that disrupt operational functioning and controls [3]. Many organisations, including those in the O&G sector, depend upon corporate information systems and networks. It is, therefore, pertinent that efforts are made to secure such systems. Normally, comprehensive security controls are put in place to deal with security threats and violations. Such controls often focus on containing external sources of threats such as malware and virus attacks and less attention is paid to human-related factors, including workers’ misuse of information and information technology (IT) resources [3]. Indeed, many information security incidents occur due to the negligence and casual behaviour of employees who pose a serious internal threat to the organisational information systems’ integrity.
Information systems security of critical infrastructures is considered an emerging area of research. However, some important research gaps in the O&G sector identified by Albrechtsen and Hovden [4] and Stergiopoulos et al. [5] remain open in the context of behavioural information security regarding the O&G sector. The first research gap is, there are very few frameworks available for the assessment of information security violations for O&G organisations. However, Eirik Albrechtsen provided multiple frameworks regarding incident management for Norwegian O&G organisations, but no framework available to assess violations and enhance information security policy compliance specifically for O&G organisations. Furthermore, in a similar study, Hagen et al. [6] emphasises the need of a comprehensive investigation on information security policy compliance in O&G organisations. Although there are several studies that investigated O&G organisations regarding information security, for instance, Ra’ed and Keating [3] and Ochieng et al. [7] have provided insights of O&G sector regarding the complex structure and vulnerability of critical infrastructures. Moreover, in their study, they suggested that there must be an investigation of behavioural information security controls in O&G organisations. Likewise, Nguyen et al. [9] and Tsakalidis et al. [9] investigated the O&G sector regarding the adoption of industry 4.0 and technical information security controls and provided several solutions regarding data and security breaches in O&G organisations and established lack of compliance with organisational ISP is a severe problem. However, the studies mentioned above investigated the O&G sector and information security in developed countries. On the other hand, Zakaria et al. [10] published a study on fraud management systems and detection in O&G organisations. Their study indicated an overall poor management control in O&G organisations in Malaysia. None of the aforementioned studies are conducted in any developing country; therefore, their findings cannot be generalised upon developing countries. The Second research gap stems from the previous literature about workplace stress in developing countries [11–14]. These researchers have suggested multiple solutions regarding workplace stress and coping strategies among employees. However, most of the studies incorporated social and cognitive coping strategies. For instance, Mohd Zukri and Noor Hassim [13] only focused on occupational stress and social coping.
Moreover, Sathasivam and Kumaraswamy [14] only focused on the electronics industry managers and mostly on cognitive and social coping solutions. No previous study has investigated employees’ stress caused by security policies in developing country O&G organisations; neither of the studies has incorporated avoidance coping strategies in a developing country’s organisational culture. Therefore, an exhaustive investigation is required to implement a comprehensive framework and provide suggestions to deal with behavioural information security stress in O&G organisations in developing countries.
This study investigates developing countries’ O&G organisations’ employees to assess the non-compliance with ISPs because of SRS and avoidance coping. Studies have shown that employees deal with workplace stress using avoidance coping strategies such as procrastination (PC) and psychological detachment (PD) [13]. Several avoidance coping strategies are enlisted in psychology literature; however, IS security literature mostly focused on neutralisation (NZ), moral disengagement, apathy and value conflicts [15]. For the first time, Xue and Guo [16] incorporated PC and physiological detachment as avoidance coping in the IS security literature and explained that perceived externalities and triage are the main causes for less effortful behaviour of employees towards information security. O&G organisations employees have a heavy work routine, and they must perform their duties on a very restrained schedule [17]. There are plenty of chances they might perceive ISPs as an external factor and indulge in the aforementioned avoidance coping strategies. The aim of this study is to investigate the O&G employees regarding SRS and their adopted avoidance coping strategies specifically PC and PD. Another goal of the study is to advance previous IS researchers’ efforts to focus on PC and PD specifically for IS security context.
We have selected Malaysia as a suitable research case for this study. Malaysian O&G organisations lack a systematic theoretical and practical investigation of the adverse effects of complex security requirements on employees’ behaviours [18,19]. Malaysia has the fourth highest O&G reserves in the southeast Asian region [20]. Furthermore, Malaysian O&G organisations have more advanced tools and techniques than most developing countries, but their behavioural information security controls still need improvement [17]. This study’s primary objective is to address the above-mentioned gaps by investigating this pressing security issue using a systematic theoretical and practical approach. The current study focuses only on SRS, avoidance coping strategies and NZ to assess O&G employees’ volitional intentions towards organisational ISPs. We developed a research framework with coping theory, the theory of NZ and SRS factors to achieve this goal. There may be many other reasons for employee violation intent, but we narrowed this study’s scope to the aforementioned factors. The proposed framework is developed using three well-established constructs of SRS, including overload (OL), complexity (CL) and uncertainty (UC) [21]. We only took avoidance coping strategies (PC and PD) and NZ [16]. All the constructs were taken from existing literature on IS security policy compliance.
No previous study has linked the aforementioned constructs to assess information security policy violations in a single research framework (Figure 1). Furthermore, none of the studies investigated SRS, PC and PD in Malaysian organisational culture. It is believed that the integration and investigation of these constructs in the developing countries’ O&G industry will shed more light on the triggers of deviant behaviours towards organisational ISPs’ non-compliance intentions. Hence, this article incorporates to investigate and answer the following research questions.
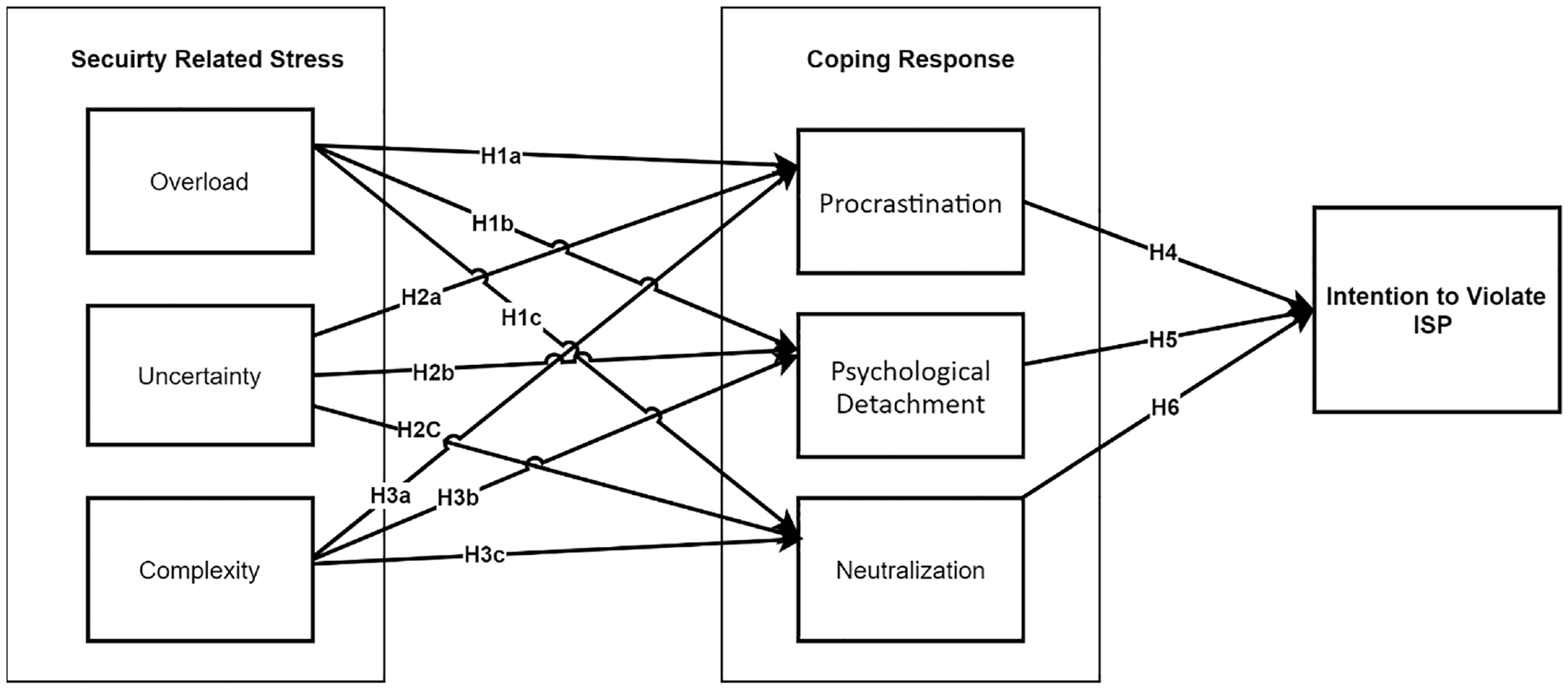
Proposed research framework.
2. Related literature
Of all the risks, the most intimidating one with enormous practical and operational consequences for O&G organisations is the risk of cyber security breaches. According to a related study, cyber security risks can be caused by technical and administrative mistakes, and almost 95% of security breaches occur due to human negligence [3]. Lack of security awareness and training is considered as the top reason for the behavioural information security breach. Trond Winther, CEO of Proactima and former Manager of operations at DNV-GL, identified the top 10 cyber security vulnerabilities in O&G organisations. He recognised a lack of attachment and security awareness among O&G employees as the top reason [22] for cyber security breaches in such organisations. Another study showed that most developing countries’ O&G organisations are not following ISPs [23]. Furthermore, the study referred to a minimal number of employees who know about the organisation’s ISP. Several studies focus on information security policy non-compliance in O&G organisations. However, none of the studies investigated SRS, avoidance coping and NZ in O&G organisations in developing countries.
Multiple studies showed that several stress factors contributing to the organisational culture of multiple developing countries. For example, Salleh et al. [24] indicated southeast Asian industry employees face various significant workplace stressors such as work pressure, time and deadlines pressure, incompetent boss and unrealistic job objectives. Similarly, Ahsan et al. [25] provided reasons for employees’ stress in developing countries organisation; their results indicated that long work hours, excessive workloads, insufficient staff and competition in career development are the significant causes of stress among developing countries workers. Mohd Zukri and Noor Hassim [13] found that almost 50% of developing countries’ managers/correlational officers perceive stress from workplace policies and progressions. Furthermore, their study shows that employees deal with such stress with various avoidance coping techniques. In a similar study, Syed Ismail et al. [26] investigated the level, sources of occupational stress and coping strategies among several developing countries’ construction industry employees. Their empirical study has shown that workers perceive occupational stress because of role ambiguity and lack of support from superiors and coworkers. Mukosolu et al. [12] evaluated workplace stress and avoidance copings among Malaysian academia staff. In their study, it was stated that use of avoidance coping strategies, anxiety and depression were found to be significant sources of occupational stress in developing counties’ organisational culture.
Various coping strategies adopted by employees were reported and enlisted in the previous literature. Multiple IS researchers used PC (intentional or non-intentional delay in compliance with ISPs) and PD (lack of motivation towards ISP tasks) in their studies. Some researchers used PC as a behavioural construct; for instance, Ifinedo [27] investigated the non-malicious deviant behaviours of end-users and categorised PC as a type of non-malicious end-user deviant behaviour. Furthermore, Bélanger et al. [28] presented a study measuring early conformance with information security policies. They have classified participants into three groups early conformers (those who do not adopt procrastinated behaviour), late conformers (those who adopt PC but comply at the very end) and non-conformers (those who deliberately adopted PC and never comply with ISPs). Bélanger et al. [28] concluded that PC could be used to assess employee early confirmation with organisational ISPs, and it can be significantly beneficial for IS managers. Likewise, May and Dhillon [29] provided a semiotic six-layered research framework to draw a holistic approach to bring down social and technical information security problems together. They have identified PC and PD as a semantic layer problem. Furthermore, their results showed that a successful implementation of responsibility structures attribution of the blame could solve these problems.
Although these prior efforts have enhanced understanding of SRS and information security policy non-compliance, it is evident that much work still needs to be done. The literature shows that not many studies have used variables of interest in this current initiative. This present study aims to increase previous perspectives and contribute to the body of work investigating SRS, avoidance coping and employees’ intentions to violate organisational ISPs.
3. Theoretical research framework and hypotheses
3.1. SRS and avoidance coping
Workplace stress is a global problem across professionals and industries of different cultures [30]. Workplace stress can be external (climate change, noise, etc.) or internal (psychological, administrative). External stressors are easy to deal with, while internal stressors are difficult to identify. Stress at work is a combination of many diverse factors, such as employee matters, organisational culture, socioeconomic factors and the adoption of new technologies [3]. Various studies consider technology adoption as a stressor for employees and referred to it as technostress. However, most studies found employee’s behaviour towards technology adoption to be resistive [31]. Information security policy adoption is considered a sub-type of technostress and deemed a challenging task for employees. D’Arcy et al. [21], first time, referred to this stress as SRS. Nowadays, information security is a challenge for every sector, and every organisation implies complex security guidelines and regulations. According to D’Arcy et al. [21], employees find it challenging to understand security policies and procedures, which later become a stressor. Furthermore, D’Arcy et al. [21] also laid down three significant dimensions of SRS, including OL, UC and CL.
The OL of SRS can be defined as the increased workload due to a security requirement. The employee often feels overloaded because of security requirements. For example, if an employee has to meet the work deadline and is unable to install and use the required software because of insufficient access privileges on the work computer, he must wait for the installation. This situation may cause a work OL on an employee, and he may feel stressed because of an information security constraint. Such OL is addressed as SRS OL. Various studies proved that such security requirements influence employees’ work productivity [32]. Although most professionals in O&G organisations do not work with information security directly, security requirements often add extra stress to their duties. Most of the time, employees bypass information security policies and guidelines because of SRS OL and apply multiple avoidance coping strategies [33]. Hence, this study hypothesises the following:
H1a. Employee’s perceived SRS OL is positively associated with PC.
H1b. Employee’s perceived SRS OL is positively associated with PD.
H1c. Employee’s perceived SRS OL is positively associated with NZ.
SRS UC is defined as the stress-induced from continuous security upgrades in an organisation’s ISPs [21]. There can be multiple causes of security requirement change arising from internal or industry regulations to changed government laws. There are several examples where new requirements affected the organisation’s security, for example, change in network information systems and data protection regulations [2]. Employees often use information systems for work purposes, and they do not consider information security as their responsibility. Employees think that security is the job of an IT administrator, and he or she will be responsible for every IT-related problem. Various studies suggest that employees consider new security regulations as an external matter and indulge in PC and PD [16]. Based on the above argument, we argue that employees consider new security regulations as an external matter.
They feel stressed to adopt such: requirements and engage themselves in volitional behaviour using avoidance coping strategies; hence, this article hypothesises the following:
H2a. Employee’s perceived SRS UC is positively associated with PC.
H2b. Employee’s perceived SRS UC is positively associated with PD.
H2c. Employee’s perceived SRS UC is positively associated with NZ.
SRS CL can be defined as the stressors stemming from the complex information security policy and procedures, that is, forcing O&G employees to spend some extra time to learn security policy and procedures or imposing extra training and education programmes in employee’s daily work routine. Another example is to use proper documentation and a checklist for every software-related procedure. It is challenging for employees to understand information security jargon and technical terms [34]. According to psychology, individuals deal with such stressful situations using avoidance coping, for example, PC and PD [33]. Adhering to a complicated security procedure is a stressful situation because some employees do not have a direct relation with information security. Employees often bypass complex security requirements and develop a ‘do it later’ behaviour. Thus, in light of the above explanation, this study hypothesises the following:
H3a. Employee’s perceived SRS CL is positively associated with PC.
H3b. Employee’s perceived SRS CL is positively associated with PD.
H3c. Employee’s perceived SRS CL is positively associated with NZ.
3.2. PC and PD as coping response
The coping theory has been used in information systems literature in various studies to evaluate different IS behaviours. A study [35] examined IT threat avoidance behaviour. They discussed that the main predictor of a user’s cybersecurity threat avoidance is avoidance motivation, a type of problem-focused coping. Likewise, Beaudry and Pinsonneault [36] examined users coping behaviours related to ISPC acceptance. They argued that emotion-focused coping have an impact on IT use. D’Arcy et al. [21] applied coping theory and argued that complex security requirements cause stress on employees and develop moral disengagement (a type of emotion coping) behaviour. D’Arcy and Teh [15] presented a theoretical framework for the assessment of SRS. They showed that SRS caused frustration and fatigue as an emotional response in employees. Because of these emotional responses, employees violate security policies and neutralise their violations as a coping response. We argue that in the context of O&G, emotion-focused coping is more probably to happen than problem-focused. A probable reason is that information security requirement is imposed by IT management; employees do not have any control over them, which triggers emotion-focused coping.
As discussed in the above paragraph, employees respond with avoidance coping strategies while facing SRS. We argue that employees will most probably respond with three avoidance strategies: PC, PD and NZ.
PC is defined in the psychology and management literature as a voluntary delay in some activities (probably stressful). For example, students delay their homework or assignments until the last minute or delay the exam preparation until the last day. Another example is people delaying a healthy diet and physical activities while promising themselves to do it later on in some suitable timeframe. PC is seen as a maladaptive coping behaviour in the psychology and management literature [37]. Employees can use the same strategy in the context of information security that is, procrastinating to do the security task later or will follow the security policy later. Employees may be aware of security risks and implications thereof but choose to postpone security procedures. A security procedure may never be followed because of repetitive PC, and security tasks can never be completed [16]. For example, changing user passwords periodically is an established Information Security task. IT management announces to change passwords every week, but because of ‘to do it later’ behaviour, an update of the password may never happen. Thus, this article hypothesises the following:
H4. PC is positively associated with the employee’s intention to violate ISPs.
Other avoidance coping strategy employees can adopt is PD. PD is a state in which employees do not think about their job-related tasks. They feel not fit in the role they are performing. In the management literature, PD is a mental state caused by any stress and makes an employee disengage himself from his work [38]. This is a similar concept to psychological distancing [36] and mental disengagement [39]. Because employees often think security is not their responsibility, they can adopt the same coping strategy for security-related requirements [16]. Employees do not want to spend time and effort on security tasks because it may hurt their main job-related tasks. Moreover, attaining specific skills and technical knowledge required to accomplish a security-related task can cause psychological stress. Thus, employees may choose to detach mentally from the security-related tasks. When employees are psychologically detached from the security tasks, they are more probably to violate organisation’s ISP. Hence, this article hypotheses the following:
H5. PD is positively associated with the employee’s intention to violate ISPs.
3.3. NZ as an avoidance coping response
Security tasks demand efforts (rule-following, remember and recall) from employees, while employees perceive security tasks as an extra burden for their daily work routine. Multiple studies showed that employees bypass the security-related tasks and requirements to complete their daily work tasks in time [27,40]. Several other studies have shown that when employees overrule the security policies deliberately, they justify their actions with several NZ techniques presented by Sykes and Matza [41] and Siponen and Vance [42] and use NZ as an avoidance coping response. As security requirements are imposed by organisations’ management and beyond employees’ control, which triggers negative emotions in employees’ behaviour [15]. To overcome those negative emotions, employees may violate organisational ISPs deliberately or accidentally. More specific in our framework, we proposed that employees use NZ as an avoidance coping response to negative emotions induced by SRS and tried to examine NZ with coping theory.
The coping theory describes that emotional reactions to stressful situations produce multiple coping responses. We proposed NZ as an avoidance coping response to SRS. NZ involves several mental techniques, which employees invoke, to justify their illicit behaviour. However, many NZ techniques are discussed in the literature, but the original NZ theory defined five basic techniques [41]. These basic techniques include denial of the victim, condemnation of the condemner, appeal to higher loyalties, denial of responsibility and denial of injury. Through these psychological techniques, employees can neutralise their wrongdoings, moral values and illicit behaviour. Specific NZ techniques are better suited for different emotions. For this purpose, researchers often utilise various techniques for different problems according to their study scope. Research on negative emotions provides general evidence to predict the stress of meeting security requirements. Research on negative emotions provides a general basis for predicting that, stress from security-related requirements will lead towards NZ of violations of ISPs [15]. Hence, this article hypotheses the following:
H6. NZ is positively associated with the employee’s intention to violate ISPs.
4. Research methodology
The research reflects the mixed method style of study including a pilot study, qualitative study and a quantitative study. A detailed research design selection and flowchart have shown in Table 1 and Figure 2.
Research design comparison.
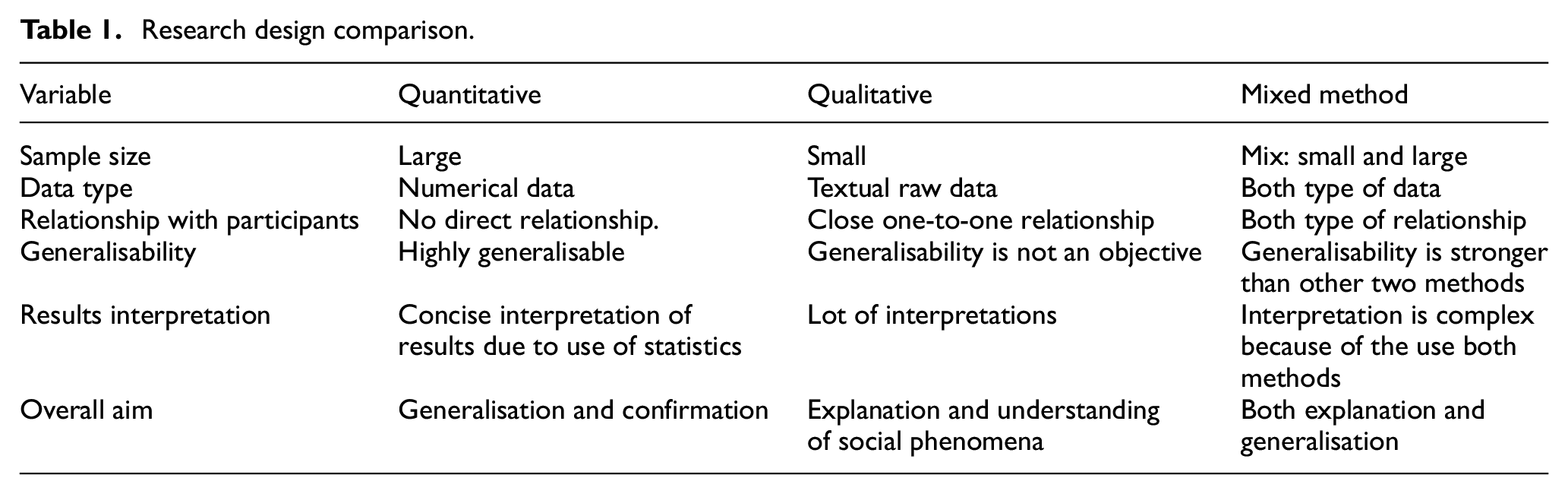
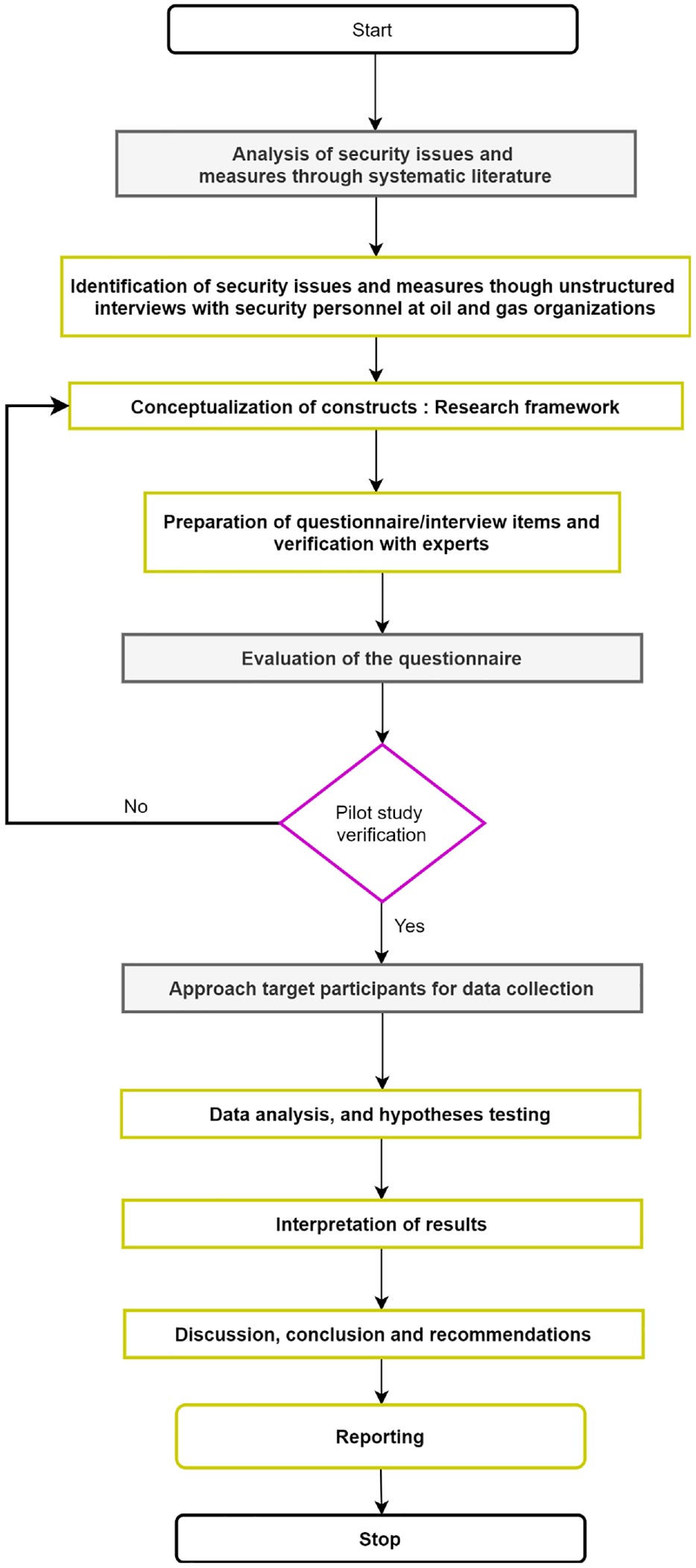
A step-by-step research flowchart.
4.1. Qualitative study
A qualitative study is conducted, with the help of semi-structured interviews, to assess SRS and coping techniques from O&G professionals. Interviews were conducted with the personnel of four selected O&G companies in Malaysia. The primary purpose of conducting a qualitative study was to develop relevant research frameworks and instruments for quantitative analysis. Interpreting the experience of O&G professionals with information security helped develop a useful research framework. Questions for the questionnaire were adopted from related studies. However, questions were trimmed according to the scope of this research. After developing the questionnaire, with the help of O&G professionals, we sent that questionnaire to the academic practitioners for their expert opinion. A pilot study was conducted after the successful finalisation of the questionnaire.
4.2. Pilot study
A questionnaire was developed with the help of O&G professionals using existing information security and the stress-related psychology literature. The convenience sampling method was used for the pilot study because of its usefulness in pilot studies. The questionnaire was distributed among five O&G organisations in Malaysia via an online google form. A total of 100 emails were sent to the organisations’ managers, and 70 responses were received. From 70 responses, 67 were found usable for descriptive analysis. The primary purpose of conducting a pilot study was to assess the questionnaire constructs’ reliability and validity. Male respondents were higher in numbers than female respondents. All recorded respondents were highly experienced managers from O&G organisations. The measures assessed by this pilot study were daily computer usage, IT competence, knowledge about the organisation’s ISP and work routines. Recorded values included a daily computer usage of 4–12 hr for managers, and most of the managers knew about information security but unaware of complications relating to ISP.
4.3. Sampling procedure and sample size
The sample for this research study consisted of managers and executives of O&G organisations from Malaysia. According to the Malaysian O&G services council (MOGSC), there are 435 registered companies in Malaysia [20]. The O&G sector is further categorised by MOGSC in two categories, that is, services and products. It was deemed challenging to distribute the questionnaire to the whole sector. Therefore, to generalise the findings, we extracted the sample population according to Krejcie and Morgan [43]. We gathered data from services as well as product-based companies. However, it was not feasible for us to gather data from all 435 companies; therefore, sample companies were chosen based on capital and market shares. One hundred fifty companies with more significant capital and market share in Malaysia’s O&G sector were selected. Companies were selected according to the scope of the research.
Due to this research and its scope, it was not feasible to approach all managers in 150 selected companies. Therefore, sample collection was performed using random sampling with the help of HR departments of all companies. Finally, managers and executives were selected randomly from each organisation for this study. The researcher gathered data from a self-administrative questionnaire. The questionnaire was distributed through email addresses acquired by the HR department. We intended to perform data analysis using partial least squares based structural equation modelling (SEM-PLS). According to Hair et al. [44], 200–400 respondents are deemed enough for valid research analysis. We sent a questionnaire to 502 respondents and received 280 responses. After data screening, 10 responses were not appropriate; therefore, 270 responses were qualified for further data analysis. SPSS-23 is used for initial data analysis, and PLS 3.0 is used for SEM analysis.
4.4. Measurement scale
A questionnaire is considered a fundamental tool for survey-based research [44]. Therefore, this study adopted questionnaire items from the existing literature and updated it according to the study’s scope. Measurements were done on a five-point Likert-type scale ranging from 5, strongly disagree, to 1, strongly agree. SRS has three sub-constructs: OL, UC, and CL. OL was measured by four items developed by D’Arcy et al. [21]. UC was measured by four items developed by D’Arcy et al. [21], and CL was measured by four items developed by D’Arcy et al. [21]. The coping response also has three sub-constructs: PC, PD and NZ. PC was measured by four items developed by Xu and Guo [16]. The PD was measured by four items developed by Xu and Guo [16]. NZ was measured by four items developed by D’Arcy and Teh [15], and intention to violate ISP was measured by four items adopted from Vance et al. [45].
5. Data analysis and results
The researcher used partial least squares (PLS) modelling using the SmartPLS version 3.0 [46] as the statistical tool to examine the structural and measurement model as it does not require normality assumption, and survey research usually is not normally distributed [47]. Since data were collected using a single source, therefore, researchers investigated the threat of common method bias following the suggestions of Kock [48] and Kock and Lynn [49], by testing the full collinearity of the data. In the full collinearity test, all variables regressed against a common variable, and if the VIF ≤ 3.3, then there is no bias from the single source data collection. The analysis showed that all VIF values are less than 3.3, therefore single source biasness is not a serious problem in our data. Table 2 presented the results of full collinearity test.
Full collinearity test results.
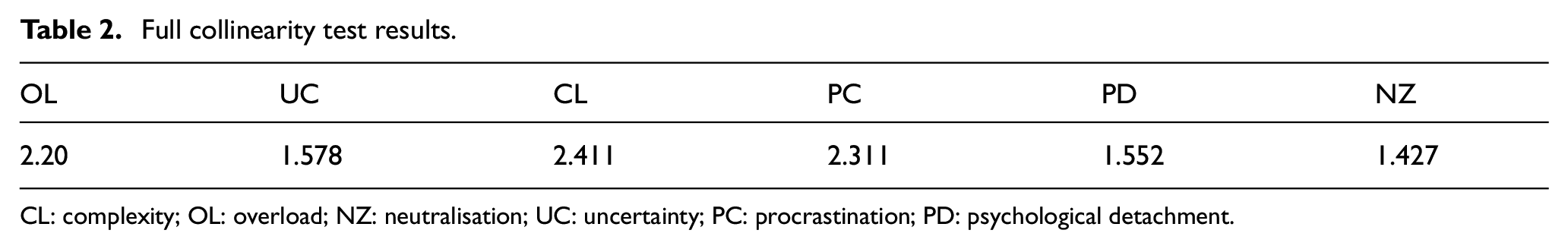
CL: complexity; OL: overload; NZ: neutralisation; UC: uncertainty; PC: procrastination; PD: psychological detachment.
5.1. Demography analysis
Table 3 represents the demographic profile of the participants. The statistics indicated that 52% of managers were below the age of 50. Most of the managers completed their undergraduate degrees, and almost 44% of these managers held graduate degrees. Sixty-four percent of the participants were from government organisations. Seventy-three percent of participants were aware of an information security policy, with a 51% high rate of ICT competence. However, they do not know the deep complications related to information security violations.
Demographic statistics.
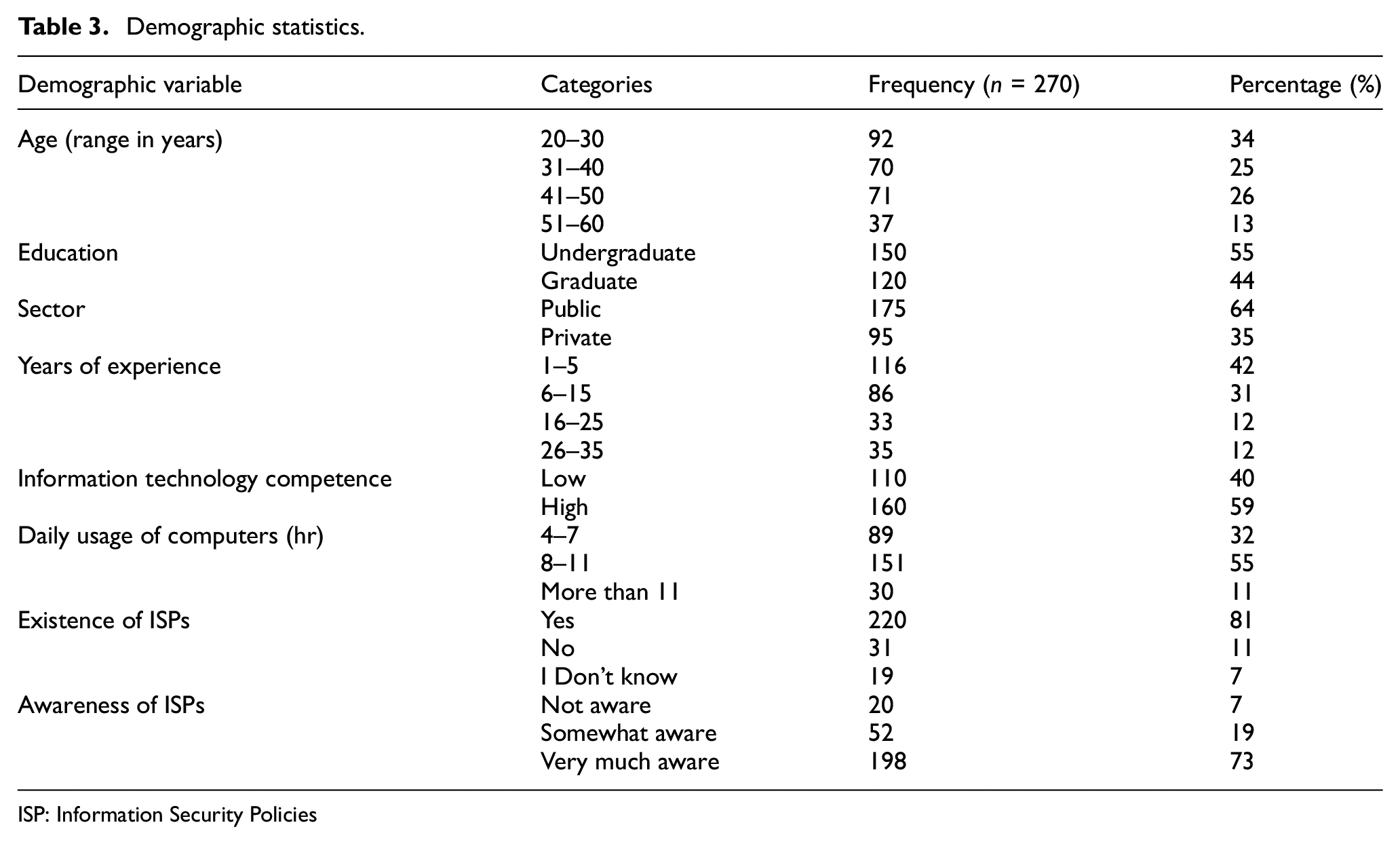
ISP: Information Security Policies
5.2. Assessment of measurement model
The researcher tests the model using a two-step approach suggested by Anderson and Gerbing [50]. First, we tested the instrument’s validity and reliability using the guidelines of Hair et al. [51] and Ramayah et al. [52]. Second, we execute a structural model to test the developed hypothesis. The model is assessed through structural equation modelling (SEM), and SmartPLS 3.0. The model assessment was further divided into two tests, convergent validity and discriminant validity.
5.2.1. Convergent validity
The measuring model was initially evaluated in terms of the factor loading, reliability, and validity of constructs. Table 4 indicates the factor loading values, Cronbach’s alpha, composite reliability (CR) and average variance extracted (AVE). According to Hair et al. [51], the values of loadings should be ≥0.5; however, the loadings were also acceptable with only one or two loadings less than 0.708. Meanwhile, Cronbach’s alpha coefficient value indicates the internal consistency of the constructs. However, it is recommended that the minimum threshold value of Cronbach’s alpha coefficient should exceed 0.70 [44]. On the contrary, CR is evaluated based on consistent loading with the minimum threshold value of 0.70 [53]. The AVE value exceeding 0.05 indicates the appropriateness of each construct [53].
Convergent validity.
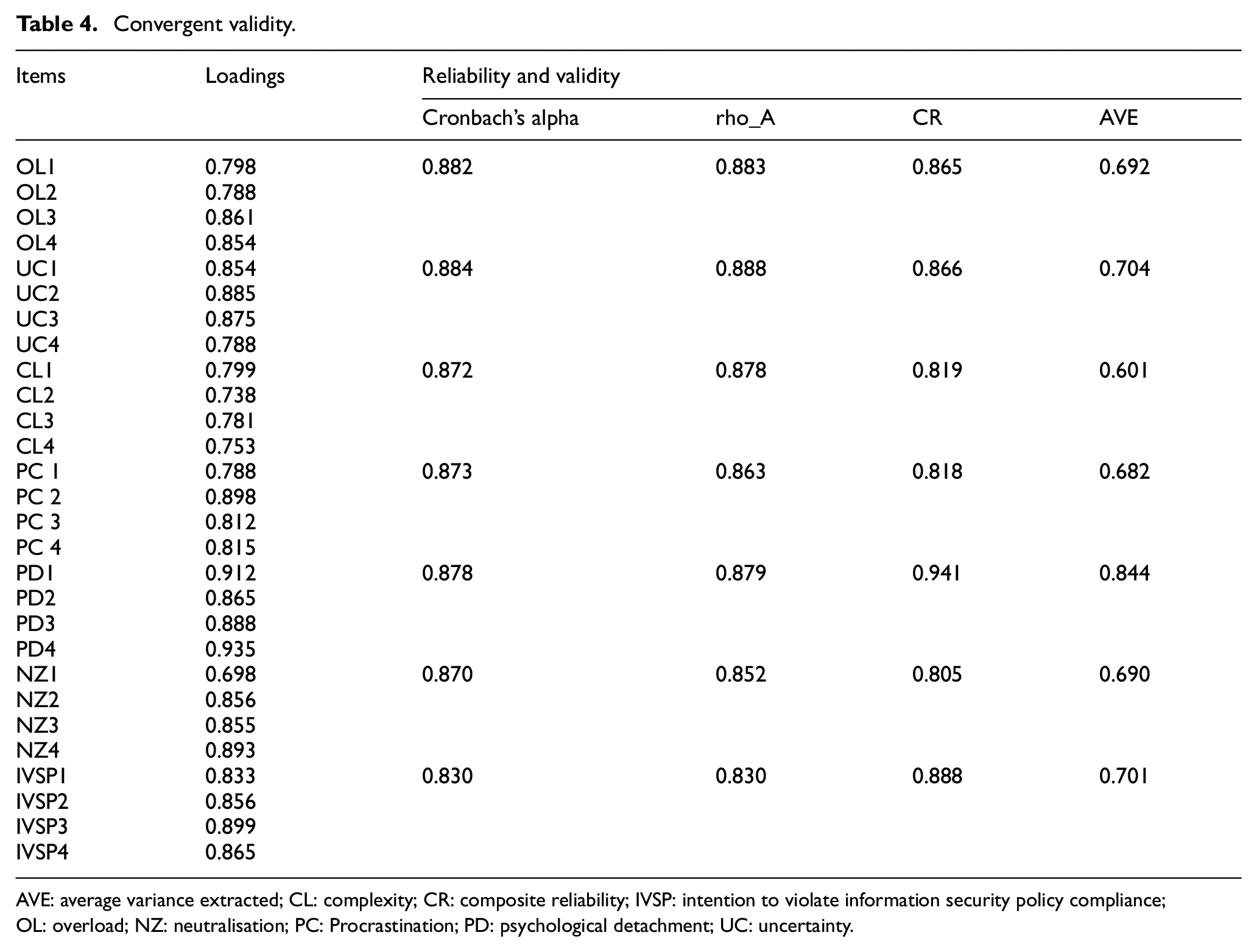
AVE: average variance extracted; CL: complexity; CR: composite reliability; IVSP: intention to violate information security policy compliance;OL: overload; NZ: neutralisation; PC: Procrastination; PD: psychological detachment; UC: uncertainty.
Researchers have measured internal consistency between constructs using CR and Cronbach’s alpha. The values of reliability coefficients exceeding 0.70 determine the reliability of items for their respective measurements. In this article, researchers have also measured each construct’s reliability with Joreskog’s rho, which is proved to be more effective than Cronbach’s alpha coefficient in the SEM technique [54]. It has been shown that, for all constructs, rho values above 0.70 are a sign of appropriate reliability. Chin [54] further described that Joreskog’s rho is more reliable because it is based on item loadings rather than correlations. Furthermore, Table 4 indicates that all constructs’ AVE value is above 0.05, which determines the adequacy of each construct’s convergent validity [54,55].
5.2.2. Discriminant validity
Discriminant validity examines theoretical and statistical differences between constructs [53]. Precise evaluation is critical as each construct should capture a phenomenon from the empirical aspects. The Heterotrait–monotrait ratio of correlation (HTMT) criterion was applied to measure discriminant validity because the HTMT criterion proved to be more precise than any other method as suggested by Henseler et al. [53]. The value of HTMT < 0.85 is considered to be acceptable [53]. It has been shown in Table 5 that each construct involved in this study meets the required threshold values. Therefore, we can conclude that the respondents understood that the seven constructs are distinct.
Discriminant validity.
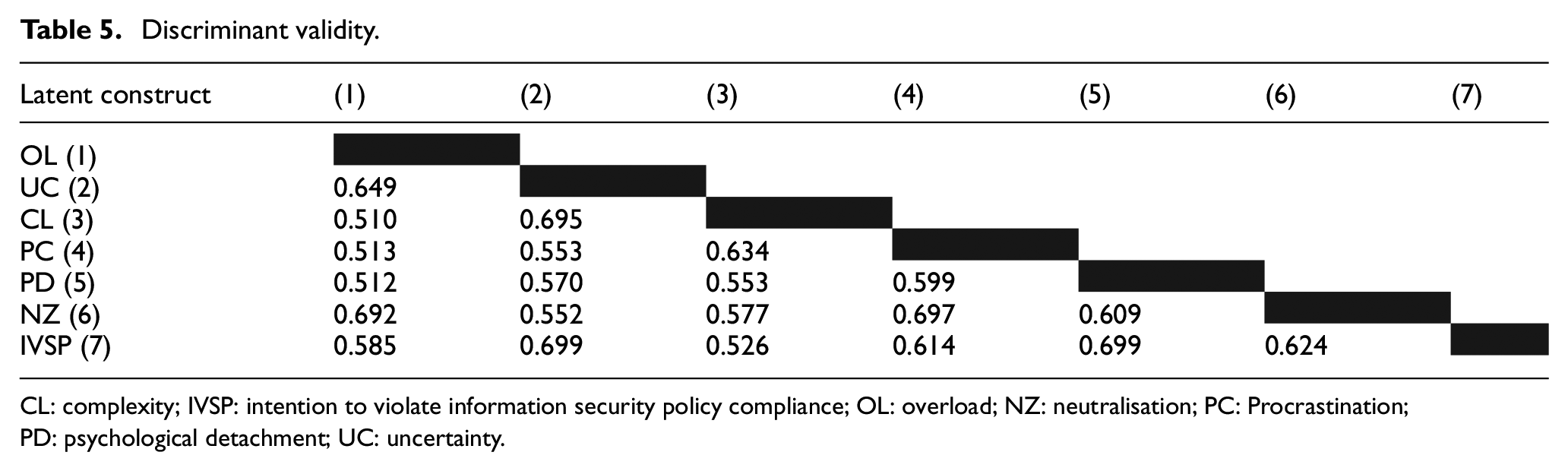
CL: complexity; IVSP: intention to violate information security policy compliance; OL: overload; NZ: neutralisation; PC: Procrastination; PD: psychological detachment; UC: uncertainty.
5.3. Assessment of structural model
The assessment of the structural model was conducted in two non-exclusive ways, namely, model fit and approximate model fit. The model fit test relies on the geodesic discrepancy (dG) and unweighted least square discrepancy (dULS), whereas the approximate model fit test involves standardised root mean square residuals (SRMR) and normed fit index (NFI). The value of SRMR that is below 0.08 [56] and the value of NFI that exceeds 0.9 are deemed acceptable [57]. However, goodness-of-fit is potentially useful for purely confirmatory research. Furthermore, the absolute application of any fit measure remains not fully developed [51]. Table 6 shows the acceptable fit indices and obtained fit values.
Model fit measures.
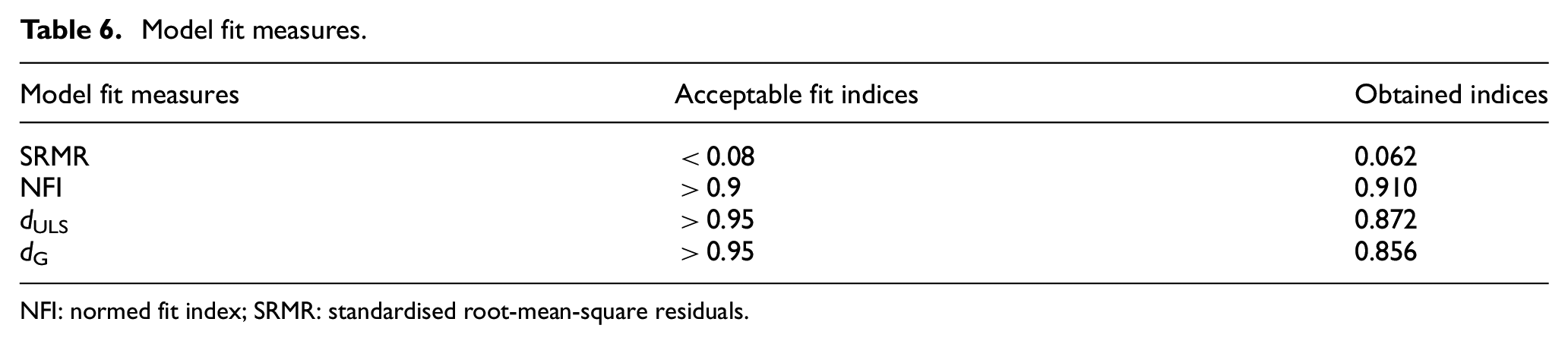
NFI: normed fit index; SRMR: standardised root-mean-square residuals.
According to Cain et al. [58] and Hair et al. [59], researchers evaluated the multivariate skewness and kurtosis. The outcomes showed that the data we have collected was not multivariate normal. Mardia’s multivariate kurtosis (β = 62.566, p < 0.01) and multivariate skewness (β = 5.115, p < 0.01); therefore, following the Hair et al. [51], we reported the standard errors, path coefficients, p-values and t-values for the structural model using a 4999-sample re-sample bootstrapping procedure [52]. Furthermore, based on the criticism of Hahn and Ang [60], p-values are not good criteria for testing the significance of hypothesis and suggested to use a combination of criteria such as confidence intervals, p-values and effect sizes. Table 7 shows the summary of the criteria we have used to test the developed hypotheses.
Hypotheses testing results.
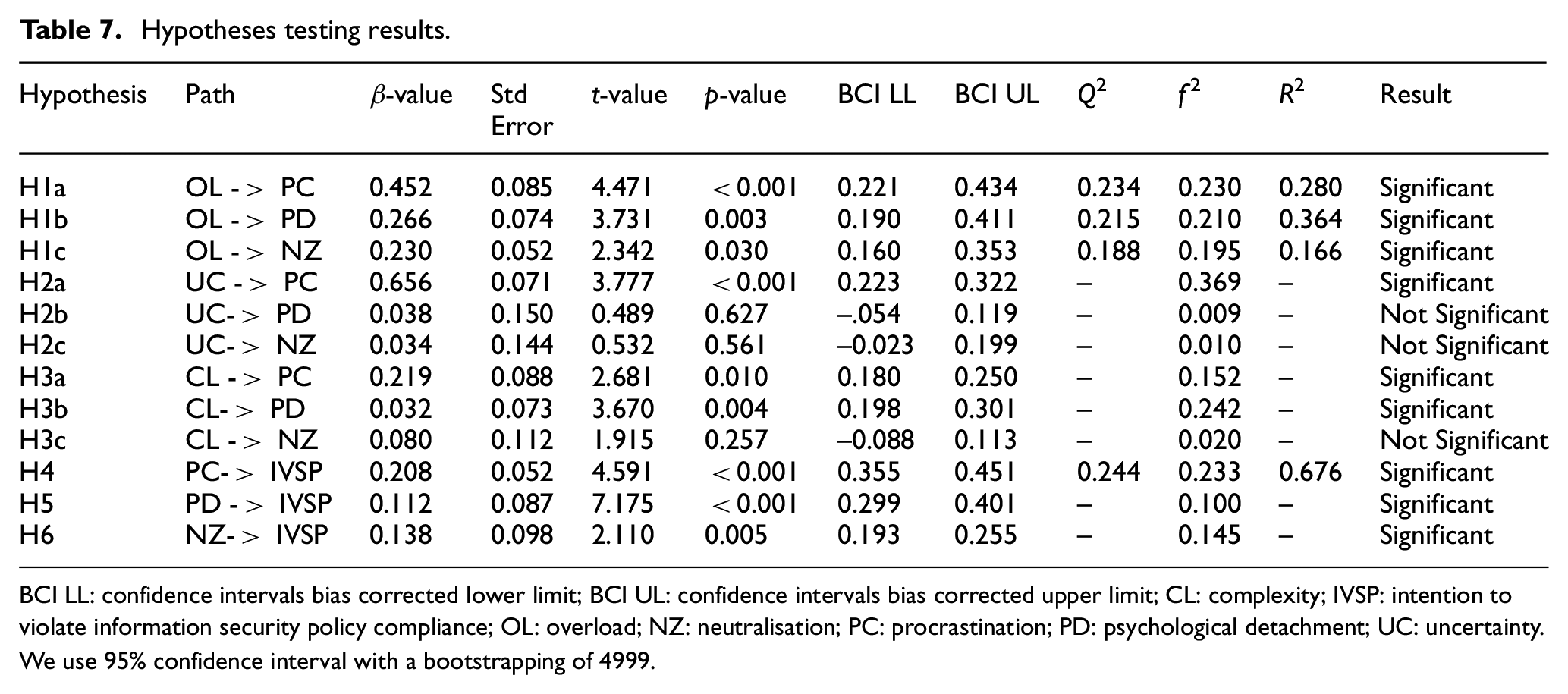
BCI LL: confidence intervals bias corrected lower limit; BCI UL: confidence intervals bias corrected upper limit; CL: complexity; IVSP: intention to violate information security policy compliance; OL: overload; NZ: neutralisation; PC: procrastination; PD: psychological detachment; UC: uncertainty.
We use 95% confidence interval with a bootstrapping of 4999.
Analysis of data showed that the hypothesised association between SRS OL and avoidance coping strategies were supported with beta values (0.368, 0.95 and 0.235) with significant p-values, effect size (f 2) and confidence intervals bias corrected lower limit (BCI LL) and confidence intervals bias corrected upper limit (BCI UL), which led to the acceptance of H1a, H1b and H1c. The relationship between SRS UC and PC is supported with beta value 0.222, p value 0.001 and f 2 value 0.369 which refers a significant effect size therefore, so we accept H2a. However, UC has shown very low significance towards PD and NZ with beta values 0.041 and 0.50 and p values 0.627 and 0.561, respectively, so we reject H2b and H2c furthermore, BCI LL and BCI UL also not met the criteria both are shown a combination of positive and negative values which led us to reject these hypotheses statistically and substantively. SRS CL had shown positive associations towards PC and PD with beta values 0.151 and 0.355 and p values 0.010 and 0.004, respectively; but no significance towards NZ with beta value 0.053 and p value of 0.257 and BCI LL and BCI UL cross combination of positive values. Therefore, the researcher accepted H3a, H3b, and rejected H3c. Avoidance coping methods (PC, PD and NZ) provided a strong association with the intention to violate the security policy beta values 0.318, 0.92 and 0.216 and p values 0.001, 0.000, and 0.005. Therefore, researchers accept H4, H5 and H6.
Data analysis further revealed that avoidance coping response is significant towards IVSP with R 2 value equal to 0.676, which shows that all predictors explained 67.6% of the variance in IVSP. Figure 3 illustrates the hypotheses testing outcomes. It has been shown that SRS affects the coping response of employees where R 2 values for PC, PD and NZ are 0.280, 0.364 and 0.166, respectively. Furthermore, results showed that both PC (β = 0.318, p < 0.001) and PD (β = 0.392, p < 0.00) have a strong association with IVSP. Whereas, NZ revealed a moderate association with IVSP (β = 0.216, p < 0.005). The R 2 values for PC, PD and NZ are 0.280, 0.364 and 0.166, respectively, which shows that SRS constructs explained 28% variance in PC, 36% of variance in PD and 16% of variance in NZ.
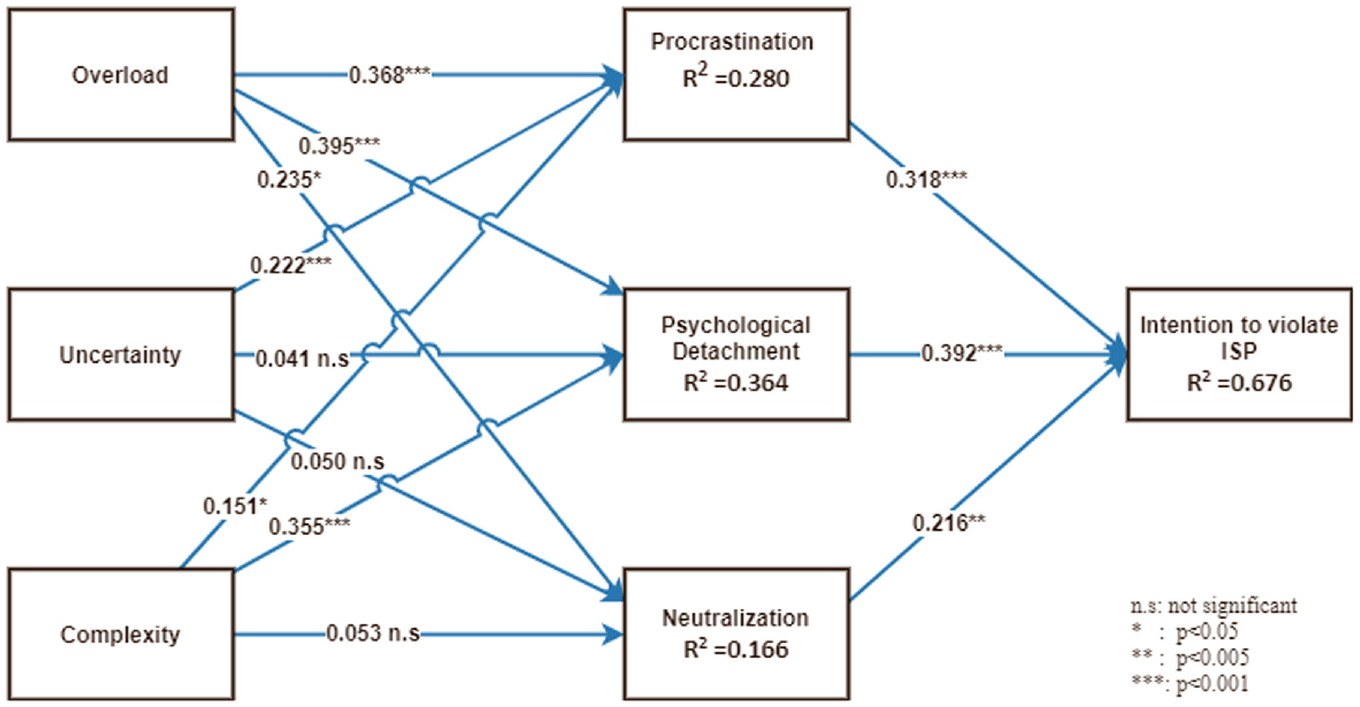
PLS results diagram.
As Hair et al. [61] have suggested evaluating the change in the R 2 value to see the effect size, f 2, Table 7 shows the results of f 2 disclosing acceptable effect size for the study hypotheses, following the Cohen [62] guideline. We examined for multi collinearity among the constructs in our model and did not find any cause for concern using the full collinearity, which showed in Table 1 all construct level VIF values were below the suggested value 3.3 [44]. Finally, we also assessed the model’s predictive relevance through the blindfolding procedure shown in Table 7, as suggested by Hair et al. [59]. The Q 2 values for PC (Q 2 = 0.234), PD (Q 2= 0.215), NZ (Q 2 = 0.188) and IVSP (Q 2 = 0.244) are greater than 0, suggesting that the model has enough predictive relevance.
6. Discussion
This article contributes theoretically and practically towards ISP violations among O&G organisations employees in developing countries, detailed discussion of the research is presented below.
This work has a direct relation with information security violations in O&G organisations. The analysis of data revealed that employees perceived SRS in the form of OL, UC and CL. We discovered that SRS occurrences were linked to feelings of irritation and exhaustion. Employees’ annoyance and exhaustion in response to occurrences of SRS confirms the coping theory-based prediction that events that obstruct progress towards one’s desired goals elicit negative emotions. As an emotional response, SRS tends to elicit frustration more than weariness; nonetheless, given the results of our subsample analysis, the influence of exhaustion emitted by SRS should not be dismissed. All three constructs of SRS have been positively associated with avoidance coping strategies. OL has a positive relation with PC, PD and NZ. This indicates employees’ tendency to perceive security requirements as OL, which most probably leads to develop avoidance behaviour towards ISP compliance (21). Our findings showed that emotions of work OL brought on by security requirements manifest themselves in more NZ of ISP transgressions, resulting in lower ISP compliance. We provide new insights into the previously recognised relationship between SRS and rationalisations of ISP breaches by demonstrating frustration and exhaustion as underlying mechanisms that link SRS and avoidance coping mechanisms. Data analysis also showed that employees, perceiving security requirements as uncertain, will probably adopt PC behaviour. Individuals may underestimate the ethical consequences of a decision in high-UC work contexts, according to research (11). The busier and more harried people are, the fewer cognitive resources they have to think through ethical implications of a decision. Cognitive psychology research supports this viewpoint, demonstrating that moral standards can be harmed when people are under psychological stress. As multiple psychological and IS literature proved, employees adopt ‘do it later’ behaviour in perceived UC for some task [15,33,63].
Furthermore, employees who perceived UC because of security requirements will not induce PD and NZ. The reasons for the failure of these hypotheses might be the measurement items used for these constructs. Moreover, previous psychological literature has been stated that stress caused by UC is variable, and it varies from person to person [64,65]. In addition, the data analysis showed that O&G employees have difficulties in understanding complex security requirements, which leads them to PC and PD. However, employees having SRS, UC, and CL issues are less probably to indulge themselves in NZ. Complimentary to this finding [15] provided enough evidence in their study about SRS, emotions, and NZ that SRS (OL, UC and CL) has a precarious relationship with NZ. They have stated that SRS is not the only motivator of NZ; it is more dependent on other factors such as organisational justice, workplace capabilities and so on. This research also contributes to the body of literature by analysing NZ in this context. To our knowledge no previous study examined NZ as an avoidance coping response.
Our empirical results have shown that employees adopting avoidance coping strategies are more probably to violate the organisation’s information security policy. Results proved that employees with PC coping responses have a strong relationship with the intention to violate. As proved in the psychology literature, individuals with stress often adopt PC behaviour, leading them into deviance (37,66]. As results indicated that PC is a severe problem with O&G employees and the major reason for this behaviour is work OL. As during the data collection phase researcher also faced a lot of problems just because of employees’ procrastic behaviour. Employees were merely willing to fill out the questionnaire because of their heavy operational workloads and unrelatedness with organisational information security. Similarly, data analysis also provided enough evidence that employees having PD are most probably to deviate from ISP. As indicated in many IS and psychology studies, individuals adopt PD in different stress situations [38,67]. Our results show that OL and CL of security requirements cause PD in O&G organisations’ employees, which leads them to violate the ISP. This result is in line with [16]. Finally, we found that NZ has a moderate influence on employees’ intention to violate ISP. SRS were found to predict variability in NZ, which in turn predicted variable in ISP compliance. Because previous information systems research have implicitly assumed that NZ is a stable concept, with, for example, some employees being more probably to neutralise their ISP violations than others, the variation in NZ is a noteworthy result. Beyond confirming the function of emotions in linking SRS to NZ, our findings suggest that emotions play a moderating role in both the SRS-to-NZ relationship and the NZ-to-ISP compliance relationship. As (15) stated in their study, NZ is not a stable phenomenon, and it needs further research to understand the relationship between NZ and compliance. In this study, we examined NZ as an avoidance coping response as Willison and Warkentin [68] stated that further investigation is needed to understand how NZ can influence ISP non-compliance.
7. Implications
7.1. General implications
The findings of current study indicated that using technological and product-based security solutions alone does not guarantee a safe working environment [69]. Acceptable human information security behaviour is the product of a combination of robust security technologies and techniques, as well as a willingness to comply [70]. In the realm of information protection, technology or human factors alone cannot be relied upon for security settings [71]. Too many security checks and controls impede employee productivity and can lead to bypassing security measures [72]. Intentional or unintended disregard for security protocols, on the other hand, is a severe threat to information security. End-user perceptions should be taken into account when identifying, designing and implementing security protocols to achieve better compliance.
This research study focused on information security policies’ compliance in O&G organisations. O&G organisations are considered process-oriented critical infrastructures. To ensure smooth working processes, O&G organisations follow ISA-95 standard guidelines of automation [2]. ISA-95 has five levels (level 4–level 0) of automation from the business and logistics level to the production level. At each level of ISA-95, there are different software utilised to perform daily work operations. At the business and logistics level (level 4), enterprise resource and planning (ERPs) software deployed to perform business tasks. At the manufacturing and operations level (level 3), manufacturing enterprise systems (MES) are installed for performing manufacturing processes effectively. Similarly, at the monitoring and supervising level (level 2) supervisory control and data acquisition (SCADA) software being deployed to handle all the monitoring and supervisory operations. At sensing and manipulation (level 1), programmable logic controllers (PLCs) are deployed. Likewise at the production level (level 0), multiple sensors and signal-based hardware are deployed. To enhance behavioural information security in O&G organisations, one must understand the automation structure of these organisations. Furthermore, to investigate information security issues, researchers incorporated levels of automation (from level 4 to level 2) adopted by O&G organisations.
This study was an effort to identify the non-compliance with ISPs in O&G organisations at ISA-95 level 4 to 2 due to SRS. The study results successfully indicated that due to heavy work routines and information security regulations O&G employees perceive these regulations as a barrier in their work routine which causes SRS. To mitigate non-compliance with information security policies established by O&G organisations at each level of ISA-95, improvement in understanding about security controls is needed. Studies suggested that to enhance understanding about overall security controls, organisational governance can play a vital role [73]. Effective organisational governance should provide security education training, in-line security policies and procedures, adequate physical security monitoring at each level and an enhanced risk assessment regarding information security-related issues to the employees [73].
7.2. Theoretical implications
The findings of this study have important theoretical implications for behavioural IS security literature. First, we examine PC and PD as avoidance coping responses in Malaysian organisational culture. The conceptualisation of these two constructs with SRS, can help expand the theoretical bases to evaluate employees’ emotional coping responses caused by SRS.
Second, by drawing on coping theory, our research offers nuanced insights into how workers should cope with the challenging security demands. Our results indicate that employees perceive security tasks as external; they think information security is something related to IT department and they had nothing to do with it. As coping with security demands required some efforts from employees and it is hard for them to put effort into some external task. In this contrast, our findings indicated that employees sometimes stop thinking about security policies (to avoid stress) and may temporarily switch off their mental processes (by PC) or permanently by completely detach psychologically from the security issues. Thus, the findings provide more proof of possible adverse effects on employee conduct from the SRS [15,16,21].
Third, our findings provide an alternate interpretation of mixed outcomes of deterrence in the IS security literature [69,74,75]. If employees switch off their mental processes temporarily or permanently, deterrence may not be effective in such scenarios. Although we did not examine deterrence in the current study, future research may incorporate deterrence with coping strategies to investigate its effects on an individual’s decision making when dealing with SRS.
Finally, this study showed that individual demographic variables such as gender, age and level of education do not have any effects on employees’ IS behaviour. From all the underline study control variables only, sector groups (public and private) showed significant differences in means towards IVSP. As current study conducted upon private and public O&G organisations, this finding is consistent with previous information systems and management studies, as private sector organisations are more concerned about rules and regulations than government sector organisations [72,76]. This finding may be only significant for Malaysian O&G organisations as previous studies have mixed results about demographic variables’ effects upon employees’ IS behaviour [74].
7.3. Practical implications
The results of this research have revealed multiple practical implications for information security violations in O&G organisations. First, Complex security requirements will probably trigger the employee’s avoidance coping, which leads them to violate the ISP. Our findings indicate a significant explanation towards employees considering security tasks as external and irrelevant to their daily work routine. Therefore, organisations should design a security measure relevant to their employees. To do this, information security professionals must understand the employees’ daily work practice and their computing needs. Security measures that do not interfere yet facilitate employees to work are probably appropriate to them. Security professionals try to design effortless security measures for employees. However, if some security task needs efforts to perform, security professionals should elaborate on the procedure for such tasks. For example, most of the organisational computers need administrator approvals for installing software. The approval procedure should be more precise and easier to understand. Perhaps, if software or installation is not approved, security professionals must provide an alternative to employees’ daily work without any mental stress.
Second, security practitioners should prevent employees from adopting psychologically detached or procrastinated behaviour. One of the practical and widely used approaches is security awareness and training (SETA) programmes. Security practitioners should design SETA programmes according to their organisational needs. One of the main reasons for employee deviance towards the ISP is using the traditional SETA programmes by security practitioners [77]. Security training is necessary as it should not be expected that employees have an equal understanding of security issues as security professionals.
Third, to elevate SRS and related negative emotions, organisations should train their employees with stress management techniques for dealing with SRS as our results suggest that employees adopt avoidance coping to deal with such negative emotions. Organisations need to concentrate on enhancing positive coping strategies (e.g. mental relaxation, negative emotion management). Nonetheless, previous research shows that constructive techniques for controlling emotions can be successful in organisational settings and are easy to instil [78].
7.4. Limitations and future research
Like every empirical study, this study also has some limitations. The first limitation arises from the fact that O&G considered as critical infrastructures and data collection from O&G sector is a very default task [79]; therefore, study was conducted only in one country – Malaysia, and the cultural context may be different from other countries. For example, Malaysian employees may have different views about information security than other region’s employees. Thus, more research could be required for the generalisation of the analysis beyond the Malaysian cultural context. In this regard future, cross-cultural research may provide new perspectives and verification with our results. Second, the data are collected from both types of respondents who have formal ISP’s implemented in their organisations and the ones without it. The inclusion of both types of respondents might have adverse effects on the results. Complementary to this, the questionnaire that was used provided complete information about this study to the respondents. In fact, comparisons of the responses of both groups did not establish any significant statistical difference. The third limitation is that the researchers only considered three avoidance coping types from emotion-focused avoidance, while coping is a complex subject. Therefore, future research may incorporate more coping strategies (emotion-focused and problem-focused) to measure employee’s responses against SRS. Such integrative research will provide a full picture of how employees manage information security issues.
8. Conclusion
O&G organisations have become a soft target for information security attackers. Last year, nearly 70% of O&G organisations faced at least one cybersecurity attack worldwide. These security attacks occur due to technical and administrative/behavioural reasons. Most of the time, cybersecurity attacks occur due to non-compliance with organisations’ information security policies. This article investigates employees’ intention to violate information security policy due to stress caused by security requirements enforced by O&G organisations.
Our results proved that O&G employees perceive security requirements as complex to follow, causing work OL and inducing UC in the work environment. Due to SRS, employees try to avoid these types of situations and adopt maladaptive coping strategies such as PC, PD and NZ. This article demonstrated that stressful security requirements cause avoidance coping, which later leads to non-compliance behaviour. The hectic work routine of O&G organisations employees often leads them into SRS and different types of value conflicts. To measure SRS in O&G organisations, a comprehensive and practical framework is examined and validated using proven statistical measures.
Cyber security not only refers to the defence of the information superhighway but also the workforce and assets of the susceptible organisation. Potential cyber-attacks can be lethal to operational controls, financial information and the workforce associated with the organisation under attack. The risks of these attacks can be mitigated/minimised by organisational arrangements and support for information security policy compliance. In addition, with this sensitive issue under investigation, O&G organisations need to focus on strategic and acceptable information security policies within the organisation. Fear of losing critical organisational information due to difficult or unrealistic security policy patterns can be dealt with by involving end-users of computing and network facilities (employees) in decisive stages of implementation of information security policies. It is time to focus upon shared visions/goals of dealing with cyber-attacks in critical energy infrastructures, especially in the O&G sector.
Supplemental Material
sj-doc-2-jis-10.1177_01655515221087680 – Supplemental material for Investigation of information security policy violations among oil and gas employees: A security-related stress and avoidance coping perspective
Supplemental material, sj-doc-2-jis-10.1177_01655515221087680 for Investigation of information security policy violations among oil and gas employees: A security-related stress and avoidance coping perspective by Rao Faizan Ali and PDD Dominic in Journal of Information Science
Supplemental Material
sj-docx-1-jis-10.1177_01655515221087680 – Supplemental material for Investigation of information security policy violations among oil and gas employees: A security-related stress and avoidance coping perspective
Supplemental material, sj-docx-1-jis-10.1177_01655515221087680 for Investigation of information security policy violations among oil and gas employees: A security-related stress and avoidance coping perspective by Rao Faizan Ali and PDD Dominic in Journal of Information Science
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship and/or publication of this article: This work was supported in part by YUTP-FRG Grant 015LCO-171 PETRONAS.
Supplemental material
Supplemental material for this article is available online.
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
