Abstract
Interpersonal trusting relationships frequently experience relational threats that require both parties to engage actively in trust maintenance efforts. Yet, trust research has tended to focus on trust formation, or trust repair in the case of a violation, and offers us little insight regarding how these more ambiguous threats to trusting relationships are experienced and overcome relationally. To provide novel insight on this topic, this exploratory study gathers dyadic interview data from 26 manager–employee trusting relationships regarding their experience of relational threats and their proactive efforts to overcome these negative relational experiences. Findings show that the experience of a relational threat triggers a three-stage trust maintenance process that includes an assessment phase, an active maintenance phase, and an outcome phase. Threats are assessed at the individual level via cognitive and affective sensemaking, while trust maintenance efforts (creating a shared mental model, cognitive and structural reassurance, and dyadic problem solving) require dyadic counterparts to act with mutual agency to overcome the relational threat and avoid a loss of trust. Trust maintenance processes support dyads to either maintain or strengthen their existing trusting relationships. Our findings advance our theoretical understanding of interpersonal trust maintenance by demonstrating that this process unfolds across three phases and can lead to different outcomes for dyads’ trusting relationships. We offer practical guidelines to safeguard existing trusting relationships, as well as a new agenda for trust scholars to extend our theorizing.
Introduction
Trust is essential in facilitating healthy work relationships, with its value evident across multiple referents (Fulmer & Gelfand, 2012). Although trust permeates all organizational relationships, the manager–employee relationship is positioned as a particularly critical intra-organizational trusting relationship (Ferris, Liden, Munyon, Summers, Basik, & Buckley, 2009; Jawahar Stone, & Kluemper, 2019). This is warranted given that a trusting manager–employee relationship affords increased performance, citizenship behaviors, and reduced counterproductive behavior (Colquitt, Scott, & LePine, 2007; Dirks & Ferrin, 2002; Legood, van der Werff, Lee, & Den Hartog, 2021). Owing to the desirable outcomes associated with trusting manager–employee relationships, an abundance of research over the previous decades has sought to understand how trust develops at this conceptual level (Baer, Frank, Matta, Luciano, & Wellman, 2021; Brower, Lester, Korsgaard, & Dineen, 2009; Child & Möllering, 2003). Although some ongoing debate endures, trust scholars have largely reached a consensus that the aggregate workings of one’s cognitive, affective, and motivational systems support trust development (Mayer, Davis, & Schoorman, 1995; McAllister, 1995; van der Werff, Legood, Buckley, Weibel, & de Cremer, 2019; Williams, 2001).
Despite this valuable insight into how trusting is achieved, trust does not exist in a vacuum, and established trusting relationships are vulnerable to the actions of internal parties and external uncertainty (Williams & Belkin, 2016). While we continue to make great strides in developing theory on trust repair (e.g., Bachmann, Gillespie, & Priem, 2015; Sala & Pratt, 2023), theoretical advances in interpersonal trust have been hampered by the assumption that trust is maintained in the absence of violations (Williams & Belkin, 2016). In reality, trusting relationships frequently experience threats that require mutual effort from counterparts to maintain trust (Gustafsson, Gillespie, Searle, Hope Hailey, & Dietz, 2021; Weibel, Schafheitle, & Van der Werff, 2023). Indeed, as organizations continue to become flatter and more knowledge-based, workers must increasingly depend on one another (Parker, Morgeson, & Johns, 2017). This heightened interdependence often creates more pressurized work relationships wherein counterparts are more likely to clash with one another (Korsgaard, Brodt, & Whitener, 2002). At the same time, novel and disruptive organizational events have downstream consequences experienced by all members (Morgeson, Mitchell, & Liu, 2015). As interpersonal relationships navigate their changing contextual landscape and respond to discrete organizational events, their normal patterns of trust can be disrupted (Korsgaard, Kautz, Bliese, Samson, & Kostyszyn, 2018). We define these disruptions as relational threats and argue that they are frequent occurrences that remain unexplored in the context of interpersonal trust.
While we conceptualize a relational threat as something that destabilizes but does not necessarily damage established trusting relationships, a lack of theorizing about how to overcome them leaves us ill-equipped to advise organizations and their employees about how to ensure they do not result in trust violation. This is a particular cause for concern as interpersonal trust repair is a multi-stage, time-consuming process (Kramer & Lewicki, 2010). Further, persistent relational conflict impacts a trustor’s ability to self-regulate, diminishing their resources and making the chance of repair less likely (van der Werff et al., 2019). Therefore, it is imperative to intervene before trusting relationships break down and face a long and complex road to recovery—one that often does not lead to pre-violation levels of trust (Schilke, Reimann, & Cook, 2013). Recent scholarship has taught us that trust in organizations can be maintained in times of heightened uncertainty (Gustafsson et al., 2021; Weibel et al., 2023), but trust scholars caution about using findings from different levels of analysis interchangeably (Fulmer & Gelfand, 2012; Gillespie & Dietz, 2009). Coupled with that, this small body of research focuses on threats to the trusting relationship attributed to external sources; however, in the context of our focal relationship, threats from an internal source are also highly plausible. This implies a lack of completeness for existing theory and our understanding of trust maintenance. Practically speaking, this means managers and employees are not prepared to deal with the frequent relational threats their trusting relationships will likely experience. As a result, existing trusting relationships that hold value at multiple levels across the organization may unnecessarily break down.
Our research sets out to address this incomplete theoretical and practical understanding of interpersonal trust maintenance. To achieve this, we are guided by the research question: How does the process of interpersonal trust maintenance unfold following the experience of a relational threat? By adopting a broad focus on relational threats, we can identify patterns in how the trust maintenance process plays out across our sample, positioning us to generate new theory regarding the maintenance of interpersonal trusting relationships (Saunders, Lewis, & Thornhill, 2019; Van Maanen, Sørensen, & Mitchell, 2007). Specifically, we theorize that interpersonal trust maintenance can take different forms depending on subjective assessments of the threat experience and that the overall process can support dyads to either maintain or strengthen their trusting relationships. Given the interdependence between managers and employees, they represent a fitting sample to explore trust maintenance in the context of relational threats. Further, our dyadic data moves us beyond a unidirectional view of trusting (Jones & Shah, 2016; Korsgaard, Brower, & Lester, 2015) and allows us to tap into the experience and efforts of both parties, as well as their mutual agency, in the dynamic process of trust maintenance (Korsgaard et al., 2018; McEvily, Zaheer, & Kamal, 2017).
Our paper makes several important contributions to theory and practice. First, we contribute to trust theory by illustrating how relational threats can be harnessed to strengthen manager–employee trusting relationships. We contend that the new information dyads access about one another, and the shared vulnerability dyads experience when they face a relational threat, strengthens their trusting relationship. Second, we add to the promising but nascent stream of research on trust maintenance (Gustafsson et al., 2021; Weibel et al., 2023; Williams & Belkin, 2016) by contributing the first empirically derived model of interpersonal trust maintenance. Within our process model, we outline different ways that dyadic counterparts can work with mutual agency to overcome negative relational experiences and maintain their existing trusting relationships. This addresses a criticism of the broader trust literature for treating trust as unidirectional (Korsgaard et al., 2015) and extends trust repair literature (and the nascent trust maintenance literature) that focuses on the (re)active strategies used by one party (for a review, see Sharma, Schoorman, & Ballinger, 2023). Finally, we extend the work of Tomlinson and Mayer (2009) to understand the role of attribution and emotion in the maintenance of interpersonal trusting relationships in the absence of violation. All of this has important implications for practice—including improvements to leadership, teamwork, and conflict management programs—and addresses recent calls for scholarly work on trust to provide “practical, actionable insights for managers and organizations” (Dirks & de Jong 2022: 23).
Theoretical Background
Interpersonal Trusting Relationships
Trust is defined as “a psychological state comprising the intention to accept vulnerability based upon positive expectations of the intentions or behavior of another” (Rousseau, Sitkin, Burt, & Camerer, 1998: 395). Trust exists at multiple conceptual levels (e.g. individual, dyadic, team, organizational) and can be directed toward different referents (e.g. employee, peer, leader, organization; Fulmer & Gelfand, 2012). Our focus is on interpersonal trusting relationships between managers and employees—that is, relational trust between two specified counterparts in a dyad (Zaheer, McEvily, & Perrone, 1998). At this person-to-person level, trust offers the expectancy that individuals will not take advantage of one another’s vulnerabilities, and encourages risk-taking behavior, i.e., trusting action (Mayer et al., 1995). Given the intersubjective nature of trust, both parties in the dyad are simultaneously acting as the trustee, i.e., the individual being trusted, and the trustor, i.e., the individual making trust-related judgments (Jones & Shah, 2016). This relational ontology addresses a common pitfall of trust research that exclusively focuses on employees’ trust in their managers (for an exception see Brower et al., 2009) and allows the consideration of how the trusting relationship is jointly produced (McEvily et al., 2017; Möllering, 2013).
Although a growing body of literature recognizes trusting as an active process (e.g., Child & Möllering, 2003; Williams, 2007), traditional models tended to overlook the active role each party in a trust dyad adopts to support the development and maintenance of trust (e.g., Lewicki & Bunker, 1996; Mayer et al., 1995). While these models greatly advanced our understanding of the dynamic nature of trust—such that the level and nature of trust evolve as the trustor gathers information about the trustworthiness of the trustee via repeated interactions (Lewicki & Bunker, 1996; Mayer et al., 1995)—they do not portray either party to intentionally interfere with the natural rhythms of trust processes. As put by Kramer and Lewicki, trustors are viewed as “vigilant social perceivers” who evaluate the presence or absence of cues about the “trust-warranting properties” (2010: 257). Meanwhile, trustees are modeled as passive actors who do not exert effort to build or maintain trust or try to influence the evaluation of their trustworthiness (Williams, 2007). An alternative argument is available via the concept of active trust, which views trust as an ongoing accomplishment that requires continuous work by actors, even once established (Möllering, 2006, 2013). Our thinking aligns with this conceptualization of trusting as a co-created process, developed and sustained by the interplay of efforts from both the trustee and trustor (Giddens, 1994; McEvily et al., 2017). Hence, we see both parties in a trusting relationship as dynamic agents, acting with motive and intentionality. Where this becomes particularly salient is when trusting relationships experience a relational threat that disrupts their familiar patterns of trusting.
Relational Threats
We conceptualize a relational threat as: “any disruption, from an internal or external source that disturbs the familiar patterns of trusting in an existing relationship, and has the potential to damage the trust, if not proactively dealt with.” For example, a change in one party’s role, or a discrete organizational event, such as the acquisition of the trusting party’s organization, that has downstream consequences for the trusting relationship (Morgeson et al., 2015). Such experiences destabilize an existing trusting relationship and transform the relational context from being more predictable to one characterized by heightened uncertainty and vulnerability. This shift in context creates the need for action by those in the trusting relationship as individuals attempt to return the relationship to its familiar world (Luhmann, 2000, 2017). Therefore, building on previous theorizing about disruptive relational experiences (e.g., Gustafsson et al., 2021; van der Werff et al., 2019; Williams, 2007), we depict a relational threat to trigger more intentional, proactive efforts by individuals to maintain the existing trust in their relationship. Our theorizing extends previous work in two important ways. First, we move beyond threats that are attributed to an external source and take a broader view by including anything that threatens to damage an existing trusting relationship. Second, we are curious about the relational experience of the threat and how trusting relationships can be interpersonally maintained. To explore this notion of mutual agency in trust maintenance, we diverge from previous theorizing at this conceptual level that focuses on the active response of one party to a disruption (e.g., van der Werff et al., 2019; Williams & Belkin, 2016).
The experience of a relational threat differs from a trust violation where a negative event initially results in trust being damaged or lost, and the efforts are directed at restoring trust to a past state (Kramer & Lewicki, 2010). In contrast, a relational threat is any disruption that brings trust into question because of its destabilizing effect on the relationship, but does not necessarily lower trust. Indeed, by its very definition, a threat is something that has the potential to cause harm or loss as opposed to something that has already done so (see Lazarus & Folkman, 1984). This is reflected in Gustafsson and colleagues’ distinction between trust repair and preservation and their framing of preservation as something that attempts to “avoid a loss of trust” (2021: 1414). Further, a trust violation is depicted as having a polarizing effect, such that interpersonal trust repair mostly involves one party (the violator) engaging in strategies in an attempt to restore trust to pre-violation levels (Kramer & Lewicki, 2010; Sharma et al., 2023). In comparison, a relational threat that heightens both parties’ sense of uncertainty is anticipated to trigger mutual efforts by parties to reduce this uncertainty and return the familiar patterns of trusting to their existing relationship (Luhmann, 2017).
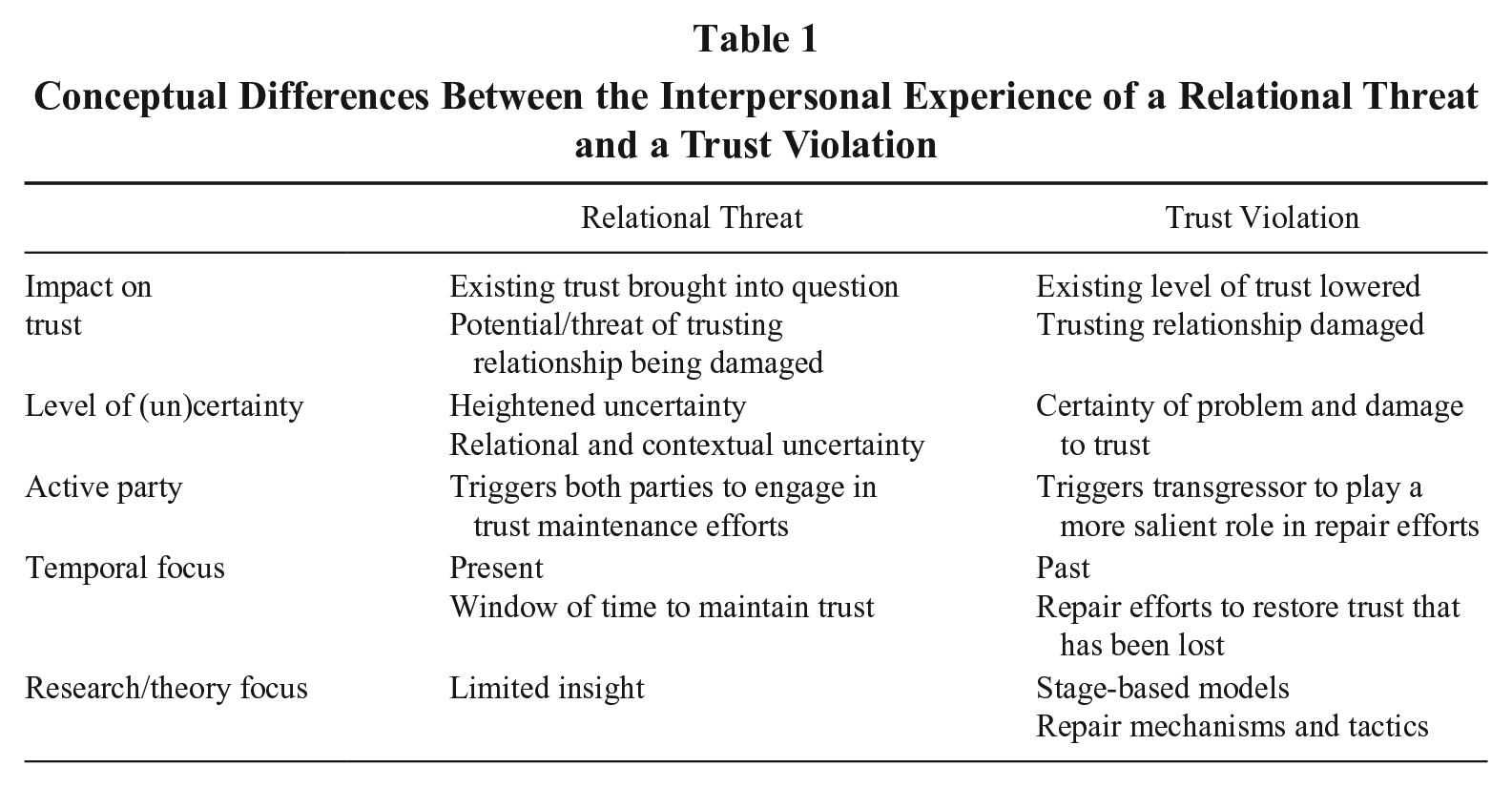
Despite early scholars recognizing that every unmet expectation does not result in a trust breach (Jones & George, 1998; Luhmann, 2000), the idea that negative relational experiences can be overcome without damaging existing trust has been mostly neglected in trust scholarship, which has predominantly focused on trust-violating experiences (Williams & Belkin, 2016). Recent theorizing acknowledges that the relational context in which trust-violating events are experienced, as well as the perception of the transgressor’s response, influence how flexibly such events are processed, and the victim’s subsequent cooperation (Williams, Belkin, & Chen, 2020). While these moderate violations are distinguished from violations in the form of catastrophic anchoring events (see Ballinger & Rockmann, 2010), they are still characterized as experiences of violation. We argue that Williams and colleagues’ (2020) theorizing extends beyond trust-violating events to other negative relational experiences that occur in existing trusting relationships and trigger both parties’ proactive efforts to re-stabilize the relationship and avoid a loss of trust. However, trust scholarship offers us little insight regarding how these more ambiguous threats to trusting relationships are experienced and overcome relationally. Therefore, based on its conceptual differences from a trust violation (see Table 1) and the general lack of theorizing on relational threats, we see this as a novel concept that enables us to further understand interpersonal trust maintenance. Given that relational threats are likely frequent occurrences for interdependent manager–employee relationships, they provide a useful lens to examine active trust and the ongoing efforts of trusting individuals in this regard (Giddens, 1994; Möllering, 2006, 2013).
Conceptual Differences Between the Interpersonal Experience of a Relational Threat and a Trust Violation
Active Trust Maintenance
At an organizational level, recent maintenance theory agrees with the trust repair literature that when trusting relationships are destabilized, active investment is needed to protect and maintain trust (Gustafsson et al., 2021; Weibel et al., 2023). At the interpersonal level, trust maintenance efforts have been depicted as trustee attempts to shift attribution away from her/himself, via the use of meaning-making processes, when they behave in a way that could be perceived as harmful (Williams & Belkin, 2016). From the trustor perspective, engaging in self-regulation of trust cognitions, emotions, or behavior can support trustors to overcome disruptions and realign them to their trust goal, i.e., maintaining their trusting relationship (van der Werff et al., 2019). In the context of maintaining trust in the organization, researchers argue that if leaders (who act as representatives for the organization) utilize active maintenance strategies that prioritize and involve employees during times of disruption, they will continue to trust the organization (Gustafsson et al., 2021; Weibel et al., 2023). Taken together, this growing body of literature lends valuable insight into what each party in a trusting relationship can do to maintain trust. We build on this and adopt a relational lens to expand theorizing on trust maintenance by exploring the mutual agency of dyadic counterparts.
Although some overlap can be observed in the maintenance efforts portrayed in existing literature, they also diverge in other ways. This provokes speculation regarding whether different strategies may be more or less fitting to support trust maintenance in different scenarios. Trust regulation theory tells us that a disruption to the trusting relationship can evoke a cognitive, affective, or behavioral regulation strategy, depending on the nature of the event (van der Werff et al., 2019). In line with this theorizing, Weibel and colleagues (2023) depict different maintenance strategies to reduce the salience of different forms of employee vulnerability (discontinuity vulnerability or socio-emotional vulnerability; see Misztal, 2012), triggered by technological advancement in their organization. By tapping into specific mechanisms through which strategies support maintenance, authors start to delineate which strategies are more or less effective for certain situations. This offers a meaningful extension to previous work which portrays the cumulative effect of overall strategies to maintain trust (Gustafsson et al., 2021; Williams & Belkin, 2016). That said, the harnessing of new technologies may be perceived as somewhat out of the organization’s control (comparable to a financial crisis; see Gustafsson et al., 2021). Trust maintenance, amid such unavoidable disruptions, is anticipated to differ from what would maintain trust in the case of a relational threat perceived as avoidable, given their external and uncontrollable nature. At present, trust literature offers us no empirical insights into how trust can be maintained when the disruption is attributed to an internal party—in addition to a lack of insight on externally attributed threats in the case of interpersonal trust maintenance.
In summary, owing to varying foci in terms of trust referents and contexts, the literature does not offer a clear conceptualization of the trust maintenance process. Further, the most up-to-date research has focused on trust in the organization as opposed to interpersonal trusting relationships (Gustafsson et al., 2021; Weibel et al., 2023). Considering previous warnings that assumptions regarding interpersonal trust are not always interchangeable with trust in an organization (Fulmer & Gelfand, 2012; Gillespie & Dietz, 2009), we believe the same assumptions should not be made in reverse. Therefore, despite the valuable insights gained from research to date, we do not have a clear understanding of how trust maintenance unfolds interpersonally. This is particularly salient in the context of relational threats, which, we have argued, are frequent occurrences in manager–employee work relationships. We aim to address this shortcoming by providing an empirically informed response to the following question: How does the process of interpersonal trust maintenance unfold following the experience of a relational threat?
Methods
Design and Data Collection
We designed qualitative, exploratory research to align with our aim of generating theory about interpersonal trust maintenance (Edmondson & McManus, 2007; Strauss & Corbin, 1998; Van Maanen et al., 2007). Specifically, we analyzed the experience of a relational threat as a means to unpack trust maintenance in our sample. In line with our research aim, and trust scholars’ methodological recommendations (Hughes & Saunders, 2021; Korsgaard et al., 2015), we employed a dyadic approach, eliciting data from both parties in the trusting relationship. This positioned us appropriately to consider trusting as socially co-constructed (Luhmann, 2017).
Data were collected via semi-structured, in-depth, conversational interviews with managers and employees (n = 52). This approach was deemed the most appropriate as it allowed participants to reflect openly on their subjective lived experience of trusting (Lamont & Swidler, 2014), which could be extended or redirected in response to probes by the interviewer (Saunders et al., 2019). We initially sampled conveniently (Patton, 1990) from our professional networks by asking individuals who had a willing manager or employee counterpart to volunteer to take part in the study. We also used a snowball sampling technique such that we asked our networks and the research participants to share the research details with their networks and identify potential dyads who may be willing to take part in the study (Patton, 1990). The details of the study were also shared with those completing executive education programs at the authors’ university, who could subsequently volunteer to participate. This combination of sampling approaches allowed us to recruit dyads from outside our networks, with whom none of the researchers had a professional connection. Our final sample consisted of 26 manager–employee dyads (see Table 2 for a breakdown of dyad demographics). Although there is no definitive guidance on the number of dyads needed for qualitative research, given the goal of theoretical saturation (Eisenhardt, 1989), the sample size is in line with recommendations for interview data from Saunders and Townsend (2016) who estimated that around 50 participants are sufficient for research that recruited participants from multiple organizations. In the later stages of interviewing, we stopped observing new theoretical insights and were therefore satisfied that theoretical saturation had been reached (Eisenhardt, 1989).
Breakdown of Dyad Demographics
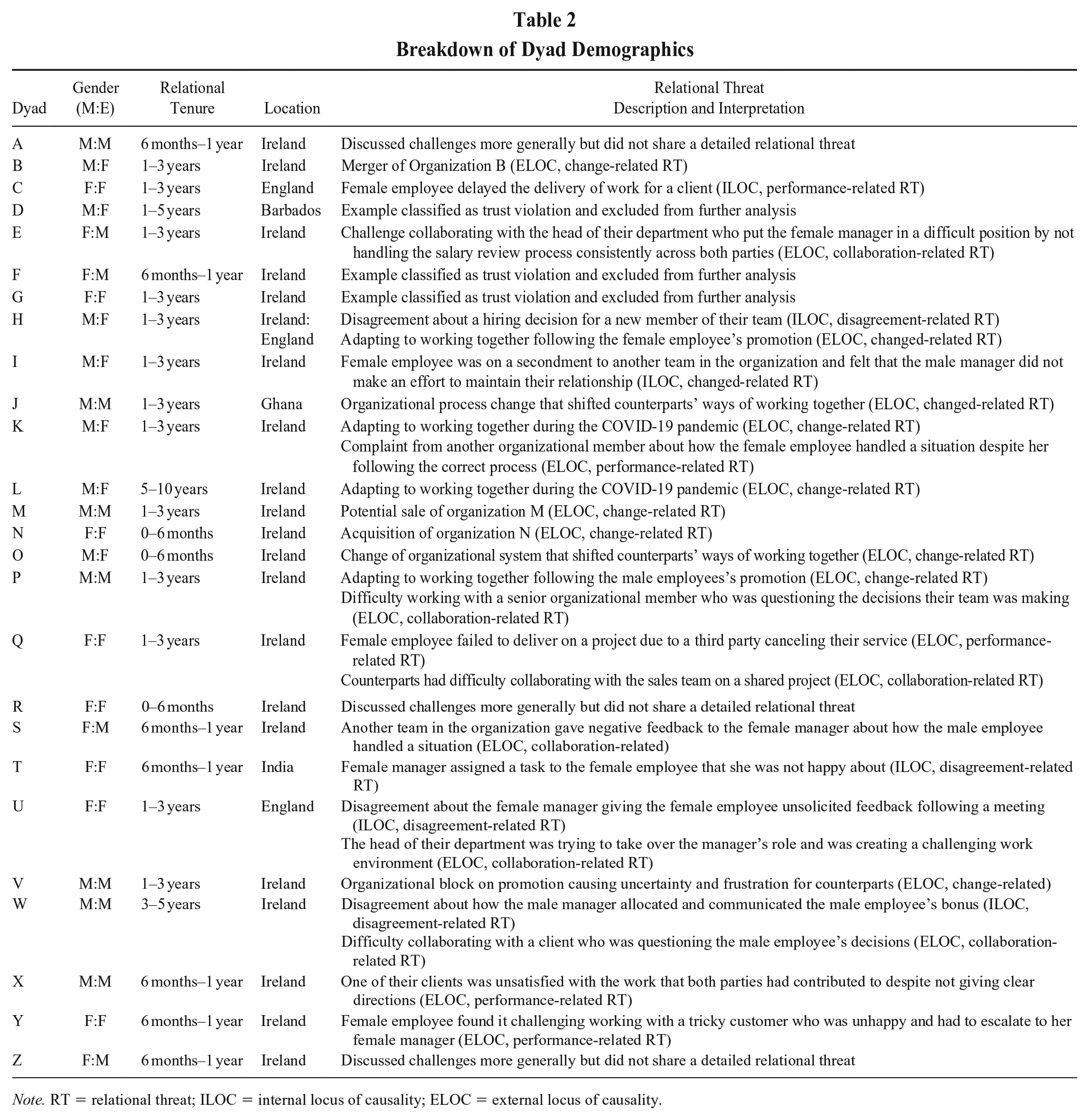
Note. RT = relational threat; ILOC = internal locus of causality; ELOC = external locus of causality.
Interviews were conducted on an individual basis and took place either in person or online via Zoom, depending on the participant’s preference and their geographical location. Interviews lasted approximately 1 hour; some were slightly shorter, lasting 40 to 45 minutes, and others up to 90 minutes. All interviews were recorded and transcribed. Data was anonymized and participants were assured of the confidentiality and anonymity of any quotes used. Dyads were labeled from A to Z, with all managers labeled as Number 1, for example, A1, and all employees labeled as Number 2, for example, A2. In line with best practice, throughout the interviewing period (September 2021 to August 2022), we took field notes to capture rich descriptions of interviewees and their context (Phillippi & Lauderdale, 2018) and met regularly to discuss emerging theory (Corley & Gioia, 2011).
The interview protocol was designed to generate detailed accounts of the trust maintenance process within manager and employee dyads (unit of analysis). Participants were first asked several questions about the relationship more generally (e.g., can you please tell me about your working relationship with your manager/employee?), before honing in on trust more specifically (e.g., how important is trust in this relationship?). These questions were deliberately broad to avoid leading participants and to allow empirical “puzzles” to emerge (Grodal, Anteby, & Holm, 2021). Participants were then asked to think about a time when their existing trusting relationship had experienced a challenge they had sucessfully overcome and to reflect on how this was achieved. This critical incident method has been previously adopted to study trust (Breuer, Hüffmeier, Hibben, & Hertel, 2020; Korsgaard et al., 2002; Williams, 2007), as it is useful to cue participants to a specific event when trying to elicit their particular actions or behaviors. This approach also helped us to address the issue of recall bias, as participants are more readily able to recall specific behavioral details when recalling a particularly meaningful time (Münscher & Kühlmann, 2012). In line with methodological guidance, we started analysis as early as possible (Saunders et al., 2019), which allowed us to check that the data we were eliciting from our participants was appropriate to answer our research question.
Data Analysis
Identifying inclusion criteria
Although our focus was on challenges that dyads had experienced and overcome without damaging their trusting relationships, some examples shared by participants were closer conceptually to violations of trust. Therefore, we recognized the need to incorporate a step within our analysis that distinguished relational threats from trust violations to inform our inclusion and exclusion criteria. This was an important step as it ensured that our findings were exclusively focused on the process of interpersonal trust maintenance as outlined by our sample.
To gain conceptual clarity between trust violations and relational threats, we adopted an abductive approach, iterating between the data and existing literature (Saunders et al., 2019; Suddaby, 2006). We consulted with existing trust violation and repair literature (e.g., Lewicki & Brinsfield, 2017; Sharma et al., 2023) to understand what constitutes a trust breach or violation and how the trust repair process is conceptualized. Although the terms are often used interchangeably, it is accepted within the repair literature that both refer to instances characterized by unmet expectations that resulted in a loss of trust (Chen, Saparito, & Belkin, 2011; Kramer & Lewicki, 2010) and require repair efforts to improve or restore the level of trust (Sharma et al., 2023). We also consulted with the existing literature on trust maintenance (e.g., Gustafsson et al., 2021; Weibel et al., 2023) to understand how disruptions to trust that did not result in a loss of trust—i.e., a “jolt” (Gustafsson et al., 2021: 1413) or “small, erratic surprises” (Weibel et al., 2023: 2)—were conceptualized and differentiated from violations. While these experiences heighten one’s sense of vulnerability and uncertainty, a loss of trust can be avoided with more systematic processing and proactive efforts (Gustafsson et al., 2021; Weibel et al., 2023).
We simultaneously referred to our data to differentiate the experience of a relational threat from a trust violation by attending to participants’ language. We compared this with how experiences of violation versus experiences that avoided a loss of trust (i.e., jolts, small erratic surprises) were conceptualized. For example, participants’ experiences of disruption that “damaged” (S2) or “impacted the trust” (D2) were deemed closer conceptually to a violation, which is characterized by a loss of trust (Lewicki & Brinsfield, 2017). Other participants talked about experiences that “threatened to derail the relationship” (B1), or where “the trust was being tested” (C2), or made them “confused as to how to feel about it [the threat]” (U2). Here participants’ language is more closely aligned with a sense of heightened uncertainty (see Gustafsson et al., 2021; Weibel et al., 2023) and our conceptualization of a relational threat as a disruption that has the potential to damage trust, if not proactively dealt with. All of this helped us to draw conceptual boundaries between relational threats and trust violations, and to delineate experiences shared by our participants where trust had been lost, or instances where a loss of trust had been avoided. In cases where trust was maintained, we were struck by how dyads overcame these experiences with mutual agency, and we chose “relational threat” to portray this relational experience of disruption to dyads’ existing trust.
Distinguishing relational threats from violations was more straightforward in the case of more severe violations (see Lewicki & Brinsfield, 2017) where participants could clearly articulate that “trust was gone” (E2) or from threats caused by an external source. For example, dyads reflected on working together during the COVID-19 pandemic and how this disrupted the ongoing rhythms of their existing relationships. Although these experiences could have damaged trust if dyadic counterparts did not proactively respond to the situation, they were easier to distinguish from violations as a result of being attributed to an “external source” (S2), meaning they were less likely to be experienced as a violation of trust between dyadic counterparts. While some relational threats may have caused damage to other trusting relationships (e.g., internal or external collaborators, or in the organization itself), our focus was on the interpersonal relationships between managers and employees.
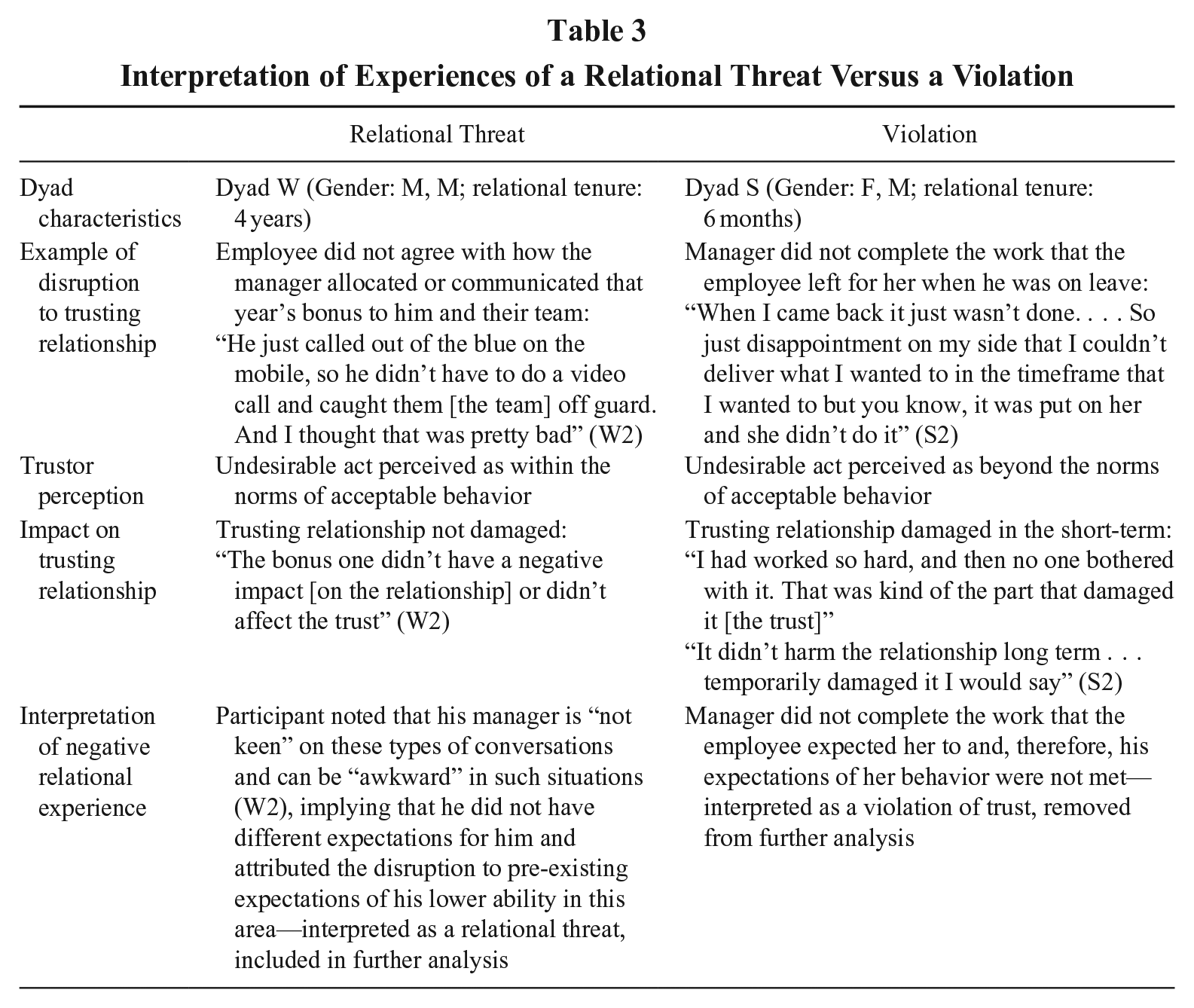
In comparison, threats caused by a party within the dyad are closer conceptually to trust violations that are less severe in magnitude (see Williams et al., 2020). For example, in Dyad S and Dyad W, the disruptions experienced resulted in both employees being somewhat let down by or disappointed with their manager’s actions (see Table 3). However, further interpretation of these examples uncovered that one undesirable act was perceived by the trustor as beyond the norms of acceptable behavior and resulted in a short-term, minor violation that “temporarily damaged” the trust (Dyad S). In comparison, the other undesirable act was perceived as within the norms of acceptable behavior for this relationship and “didn’t affect the trust” (Dyad W), and, therefore, was interpreted as a relational threat. This distinction emphasizes the importance of attending to how undesirable acts are interpreted by the trustor—as opposed to the act/behavior itself. It is important to note that the context of the relationship in which the disruptions are experienced should also be considered, and the norms of acceptable behavior are not absolute (a point we return to in our discussion).
Interpretation of Experiences of a Relational Threat Versus a Violation
Once we were satisfied that we had distinguished relational threats from violations, we reviewed all the examples of disruptions shared by participants to isolate experiences of relational threats and remove any cases of violation. This resulted in 26 relational threats being isolated for inclusion in further analysis, and five examples of violations being excluded. Participants discussed a broad range of relational threats ranging from disagreements with one another to adjusting to organizational changes. We grouped these into change-related, performance-related, collaboration-related, and disagreement-related relational threats (see Table 2). As part of our analysis, we considered whether the content of the threat influenced the process of interpersonal trust maintenance.
Phases of analysis
In our analysis, we took an interpretive approach, scanning the data for underlying meanings, contradictions, puzzles, and potentially different interpretations (Alvesson & Sköldberg, 2017). To guide us in achieving this, we used Braun and Clarke’s (2006) thematic analysis. This approach was judged as a suitable choice as its six phases offer a systematic and rigorous approach to the analytical process, while at the same time allowing us to remain flexible and open-minded to different interpretations and discoveries within the data (Braun, Clarke, & Hayfield, 2022). We also incorporated techniques from multiple case study analysis into the analytical process to search for cross-case patterns in the sample (Eisenhardt, 1989).
The purpose of the first phase of analysis—familiarization with the data (Braun & Clarke, 2006)—was to immerse ourselves in the data to ensure in-depth familiarity. This involved the transcription of recorded interviews, and then reading each transcript several times to gain an intimate understanding of participants’ lived experience. Following other scholars’ recent approach to dyadic theory generation (e.g., Freeney, van der Werff, & Collings, 2022), we initially focused on the individual level and then moved our analysis to the dyadic level. Once at the dyadic level, we engaged in within-case analysis, which involved in-depth familiarization of the intricacies of each trusting dyad, and creating a comprehensive memo for each dyad (Eisenhardt, 1989). This step helped us to cope with the volume of data and to more readily identify generalized patterns across cases.
Once the familiarization phase “the bedrock for the rest of the analysis” was completed, we then started to move through the next four phases of the thematic analysis that make up the coding process: generating initial codes, searching for themes, reviewing themes, and defining and naming themes (Braun & Clarke, 2006: 87). The aim of the coding process is abstraction from the raw data to meaningful groups and themes (Miles & Huberman, 1994). Initial coding involved the production of first-order codes from the raw data that appeared interesting and relevant to the research questions (Braun & Clarke, 2006). Data were coded with a combination of descriptive codes, that is, using a word or short phrase representing its meaning as a label, and in vivo codes, that is, using participants’ own language as a code (Saldaña, 2016). For example, a participant’s reflection about “working together to try and figure it out” (N1) was coded descriptively as dyadic sensemaking, while another participant highlighting the need to “look at it [the relational threat]” from another team’s “perspective” (Q2) became an in vivo code of perspective-taking.
The next three phases of thematic analysis were focused on abstraction from initial codes to themes, i.e., constructing themes, reviewing potential themes, and defining and naming themes (Braun & Clarke, 2006). Initially, this involved reviewing first-order codes, removing and/or combining duplicates, and then grouping first-order codes into second-order codes based on similarities and patterns. Once this was completed, second-order codes were reviewed and grouped in the same way as themes (Saunders et al., 2019). To give an example of the coding process from the data set, an initial code of “brainstorming” evolved into a second-order code of “dyadic problem-solving,” which ultimately ended up in the overarching theme named “trust maintenance strategies” (see Figure 1). Naturally, all of this was not a linear process and involved iterating between phases, as well as contemplating our findings in the context of existing trust research in line with our abductive approach (Saunders et al., 2019; Van Maanen et al., 2007).
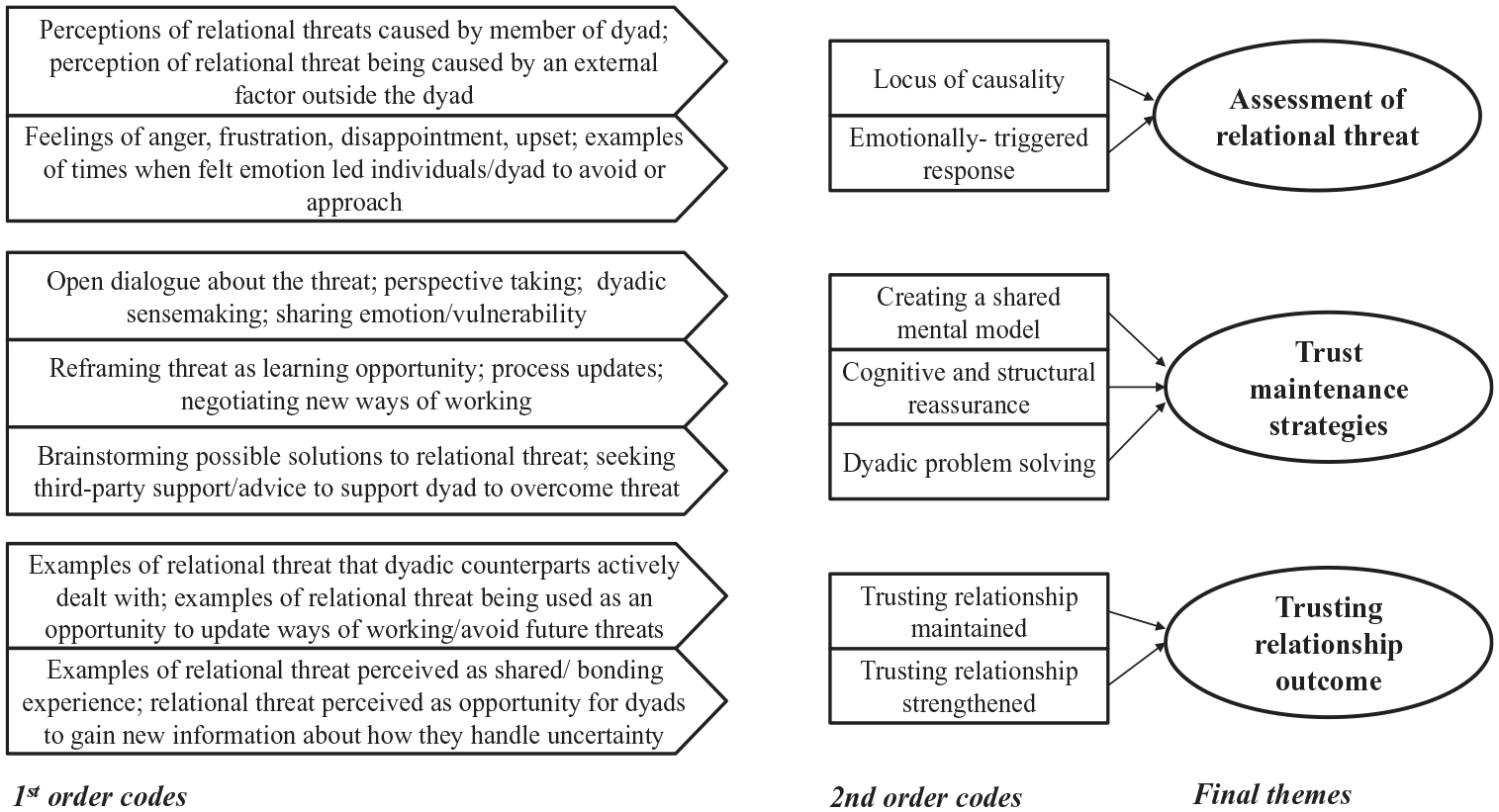
Data Structure
Next, we used our themes to search for cross-case patterns of similarity or differences across our sample (Eisenhardt, 1989). This was supported by the use of tables, which enabled us to condense rich data to display evidence in a way that helped reveal meaningful patterns and insights relevant to our research questions (Cloutier & Ravasi, 2021). While the coding process helped to identify the salient themes across the data set, it did not interrogate any differences across cases. For example, through the coding process, we uncovered the overarching trust maintenance strategies; however, the cross-case analysis supported us to interpret why dyads used different combinations of these strategies and reported different trust outcomes, i.e., the different pathways in the process of interpersonal trust maintenance. All of this served as the building blocks for the model development. Throughout this analytical process, there was an ongoing discussion among the researchers to refine the emerging theory (Corley & Gioia, 2011). Finally, once we were satisfied that the analysis process adhered to the standards of trustworthy research (Lincoln & Guba, 1985), we produced the final model of interpersonal trust maintenance and completed the last phase of thematic analysis: producing a scholarly report of the analysis (Braun & Clarke, 2006).
Findings
In this section, we outline the process of interpersonal trust maintenance following the experience of a relational threat as uncovered in our sample of manager–employee dyads. Our findings illustrate that this process involved three phases: an assessment phase; an active maintenance phase; and an outcome phase; and that dyads followed one of three pathways in the trust maintenance process, determined by how they assessed the relational threat. Dyadic counterparts typically made their own subjective assessment of the relational threat, while efforts to overcome the threat, via trust maintenance strategies, required dyads’ mutual agency. Our findings also highlight that, depending on the pathway dyads followed, the process of interpersonal trust maintenance resulted in different trust outcomes. Specifically, dyads either maintained their trusting relationships, or the experience of a relational threat was harnessed to strengthen their trusting relationship (see Figure 2).
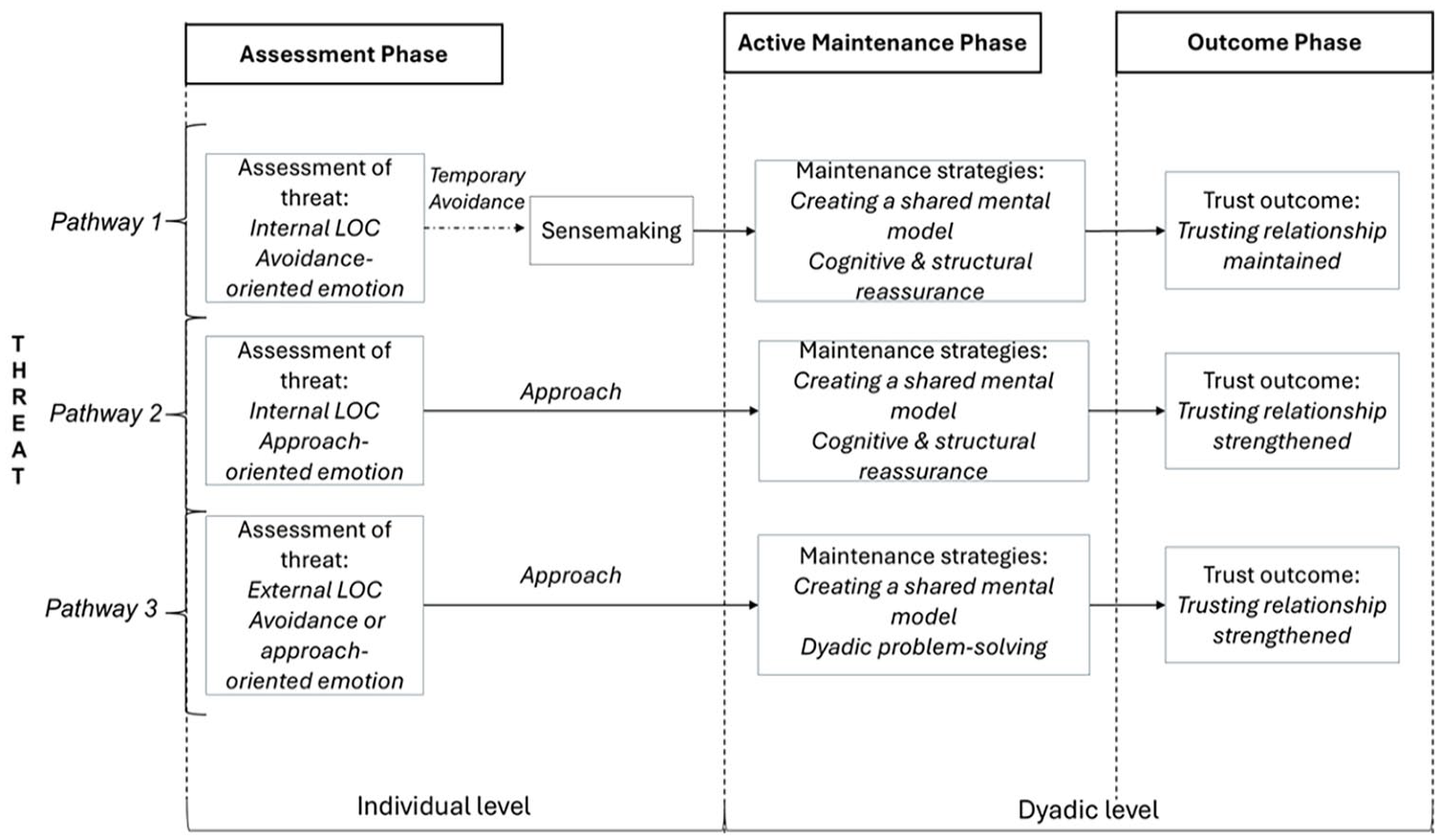
Process Model of Interpersonal Trust Maintenance
Assessment Phase
The experience of a relational threat triggered a need for individuals to engage in cognitive and affective sensemaking, as evidenced by one employee recognizing that her manager’s actions resulted in her being: “Confused as to how to feel about it, I didn’t know where it was coming from, like if it was coming from a good place or not” (U2).
Sensemaking aided individuals to gain a clearer understanding of the threat and how it made them feel. Cognitively this involved an attribution process, wherein individuals determined who the threat should be attributed to, i.e., the locus of causality (LOC) of the threat (Weiner, 1985). Threats were either perceived as having an internal locus of causality (ILOC) or an external locus of causality (ELOC). This meant that individuals either perceived someone inside the dyad as being responsible for the threat (i.e., ILOC) or attributed the threat to a source outside the dyad (i.e., ELOC). Individuals also made sense of and reflected on how the relational threats made them feel, which ranged from “upset” (K2) or “worried” (Q1), to being “annoyed” (C2) or “frustrated” (B2). Individuals’ assessment of the threat determined which pathway they followed in the trust maintenance process, i.e., pathway one, two, or three.
Internal LOC relational threats (pathways one and two)
Following the experience of relational threats that were determined to have an ILOC, dyads either followed pathway one or two. Although these threats were attributed to a source within the dyad, some participants described how their assessment of ILOC relational threats resulted in them initially pulling away from their counterpart (pathway one), while others described pulling towards their dyadic counterpart (pathway two). Those who initially pulled away took some more time to make sense of the threat—and how to handle it—before attempting to resolve the threat with their counterpart. For example, one employee talked about a situation in which he felt “frustrated” (W2) with how his manager handled his bonus allocation and described how he needed some space to think about it: “I was like I don’t accept this as okay, I go look, you’ve caught me off guard completely, which is a bit much. I need to digest that, take that away, and think about it myself” (W2).
Once the employee had a chance to do so, he then “voiced my [his] opinion” (W2) and started to work towards a resolution with his manager. Meanwhile, another employee referred to a time when she felt “upset” as a consequence of receiving unsolicited feedback from her manager, but approached her immediately to share that she “really didn’t think it was fair” (U2). Responsible parties typically mirrored counterparts’ emotional responses, such that they gave angry counterparts their desired space and approached upset counterparts. Therefore, at this point, the distinction between pathways one and two is whether one counterpart initially pulled away from the other and engaged in prolonged sensemaking, or whether dyadic counterparts came together to deal with the threat.
Given that both threats were attributed to an ILOC, we interpreted that the assessment of how the relational threat made individuals feel determined whether they pulled away from or pulled towards their counterpart. Specifically, we characterized the emotions experienced during the assessment phase according to Methot, Melwani, and Rothman’s (2017) distinction between approach-oriented versus avoidance-oriented emotions. This is based on the emotions as social information model (Van Kleef, 2009), and distinguishes approach emotions (e.g, upset, worry, guilt) that serve the interpersonal functions of establishing or maintaining connection from avoidance emotions (e.g., annoyed, frustrated, angry) that signal coldness or disapproval, and are linked to separation between relational partners (Methot et al., 2017). This distinction aligned with the responses described by our sample whereby in dyads where one party expressed an approach emotion (e.g., U2) counterparts pulled towards one another, compared to when one party expressed an avoidance emotion (e.g., W2) and initially pulled away from their counterpart. Therefore, interpreting our findings in line with the distinction of approach-oriented versus avoidance-oriented emotions (Methot et al., 2017) explained individuals’ different responses to ILOC relational threats, which we refer to as emotionally triggered responses. Given that avoidance responses described by our participants were short-term and these dyads also overcame relational threats with mutual agency in the active maintenance phase, we labeled these responses as temporary avoidance. Importantly, these different emotionally triggered responses to ILOC threats made apparent that the pathways followed by dyads were determined by their cognitive and affective sensemaking of the threat, with neither alone being able to explain the dyads’ responses fully. Further, Dyads U and W followed different pathways despite experiencing the same type of ILOC threat (i.e., disagreement-related), demonstrating that the assessment of the threat—rather than the content of the threat—determined which pathway they followed in the trust maintenance process.
External LOC relational threats (pathway three)
Following the experience of an ELOC relational threat, dyads described coming together to face the threat with mutual agency, regardless of the type of threat or how it made them feel. For example, one dyad reflected on feeling “frustrated” (S1, S2) by their difficulties collaborating with another team in their organization, who they felt was “stepping on their toes” (S2), and described how this culminated in the team sharing feedback with the manager about how the employee was handling the situation. Although this had the potential to damage the manager’s trust in the employee, she was able to recognize the root of the issue: “The company is growing so quickly; there are a lot of people trying to establish what it is they’re here to do, and how they’re gonna do it” (S1). Despite feeling “frustrated” by the overall situation, she approached the employee to clarify: “What was his side of it, this is what I’m hearing externally, does that marry back?” (S1). Therefore, because the threat was attributed to an ELOC, any negative emotion that dyadic counterparts felt was not directed toward one another.
This was further evidenced by another dyad, whose ongoing trusting relationship was disrupted by their organization reporting a company-wide block on promotions which caused uncertainty about their future at the organization and, therefore, their work relationship. Despite being “frustrated” by the relational threat, there was an acknowledgment that this was not with one another: We’re both frustrated at the fact that the failing is the kind of management structure is holding us back. And I think that’s caused frustration in our relationship as well, because we’re both frustrated at the same thing: while not being at each other, there is frustration there about it. (V2)
Overall, in the case of threats assessed as having an ELOC, regardless of the type of threat or the emotion the experience evoked, dyadic counterparts approached one another to deal with the threat together.
Active Maintenance Phase
Having moved through the assessment phase and making sense of the relational threat at an individual level, dyads then proactively dealt with the threat to avoid a loss of trust, and to maintain their existing trusting relationships. Our analysis highlighted that dyads acted with mutual agency to maintain their trusting relationship via the use of three overarching trust maintenance strategies: creating a shared mental model, cognitive and structural reassurance, and dyadic problem-solving (see Table 4). Moreover, we uncovered a pattern, such that dyads who experienced an ILOC threat (pathways one and two) enacted creating a shared mental model and cognitive and structural reassurance, while dyads who experienced an ELOC relational threat (pathway three) enacted creating a shared mental model and dyadic problem-solving.
Supporting Evidence for Trust Maintenance Strategies
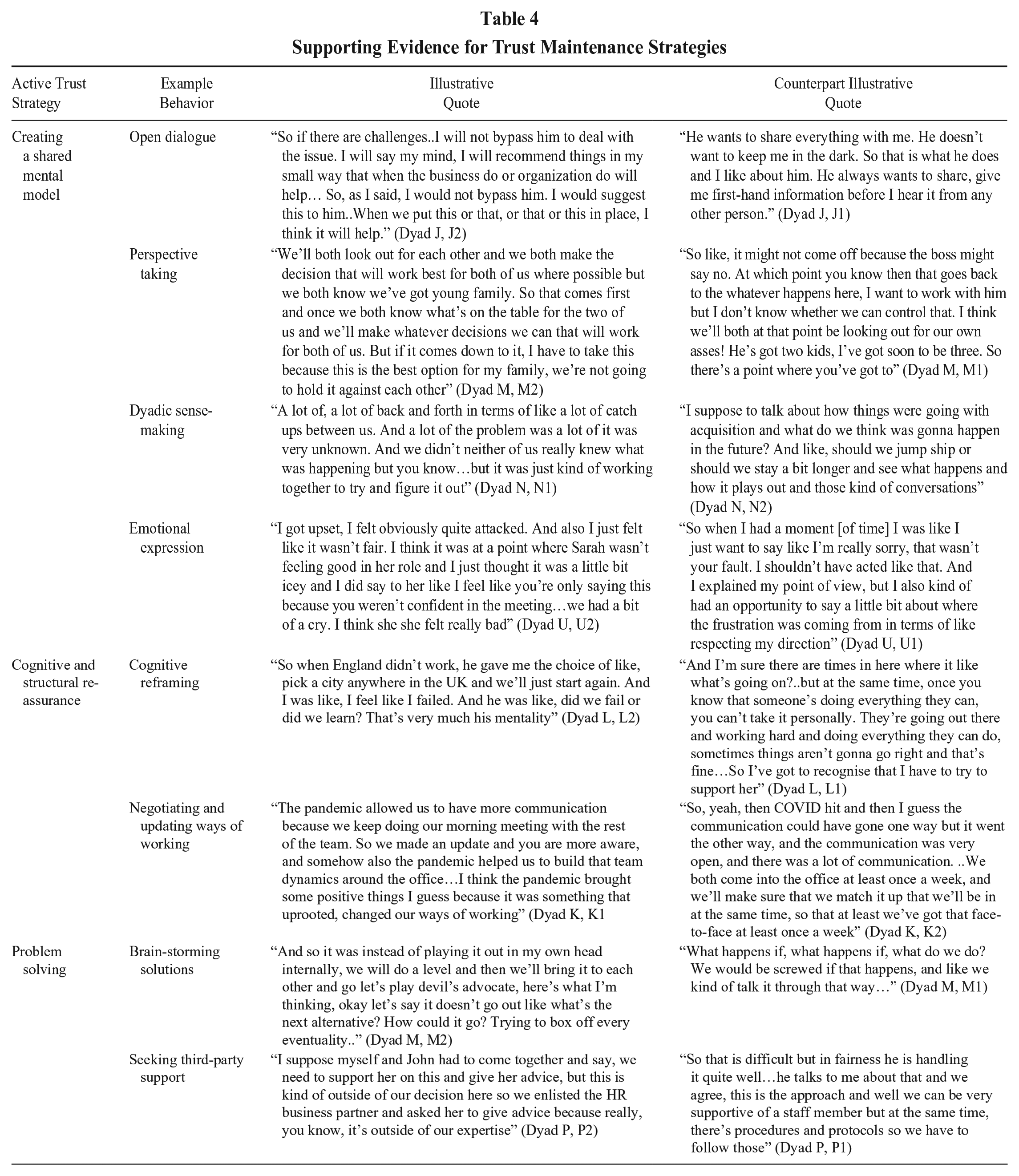
Creating a shared mental model (pathways one, two, and three)
Creating a shared mental model (Weick & Roberts, 1993) represents dyads’ attempts to get on the same page about the relational threat, and to position themselves to move forward to overcome the threat. This was uncovered as an important first step in the trust maintenance process, and all dyads—regardless of the pathway they followed—enacted this strategy. Some of the groundwork for this was done via sensemaking in the assessment phase, meaning dyads had already started to interpret the threat individually, and could use this as a springboard to create a shared mental model with their counterpart. This is in line with learning theory which positions interpreting as blending quite naturally into integrating as individuals move away from feelings and hunches towards a collective mind (Crossan, Lane, & White, 1999, Weick & Roberts, 1993). The specific behaviors that supported dyads to create a shared mental model were open dialogue, perspective-taking, dyadic sensemaking, and emotional expression.
Open dialogue was an essential strategy for dyads to create a shared mental model. Put simply, open dialogue provided dyads with an important opportunity to come together to: “Just talk to each other and tell each other where we’re at” (M2). Dyads themselves recognized its vitality in the maintenance process, with one employee noting: “The biggest thing was just that we were able to communicate really clearly with one another” (Y2).
Perspective-taking allowed individuals to consider their counterpart’s position—that is, to “see where they are coming from” (J1)—and helped dyads to create a shared mental model of the relational threat. Vitally, this enabled individuals to challenge or shift their way of thinking about their counterpart or the threat. For example, in one dyad an employee noted that perspective-taking helped her see that her manager’s feedback was intended to support her growth: “I understand also she was coming from a perspective like look you can literally do anything. I want you to grow and I just think if you conducted yourself sometimes like that it would make you even better” (U2).
Dyadic sensemaking involves counterparts coming together to collectively interpret a relational threat. Compared to one party considering their counterpart’s perspective, this was a more collective effort by dyads to make sense of the threat. For example, one employee described how she and her manager came together to make sense of their organization’s acquisition and figure out what this meant for their roles and their future at the company: I would have questioned my position in the company, for sure and I actually would have had that conversation with Shane, as Shane would have had that conversation with me, because I know he found it very difficult, he told me he found it very difficult. And I think we kind of both came to the same crossroads like you know where are we going from here sort of thing. (B2)
Emotional expression represents dyadic counterparts’ deliberate expression of emotion to one another. Such expressions of emotion aided counterparts to empathize with how the threat had made their counterpart feel, while also providing a platform to reciprocate (emotionally)—in some cases also creating a sense of shared vulnerability. For example, one manager expressed her annoyance about her counterpart’s performance on a project and, in doing so, presented an opportunity for both parties to air their grievances with one another, create a shared understanding of how the threat had affected one another, and move forward towards a resolution: We sent it to the client, and she then calls us up and she’s like, basically do you understand why I’m annoyed here today? I’m like yes totally, I didn’t do X Y Z, oh, and by the way, you’re annoying because of this. Maybe not in those words, but the point is that with that level of transparency with her making the call it makes Monday morning really easy because you’ve blown off everything that happened on Sunday. (C2)
Cognitive and structural reassurance (pathways one and two)
Cognitive and structural reassurance involved making adjustments (cognitive and physical) that enabled dyads to move past relational threats. This was achieved through two mechanisms: by shifting one’s thinking about the relational threat and making physical changes to how counterparts work together. As noted, dyads following pathway one or two in the trust maintenance process enacted cognitive and structural reassurance as a follow-on strategy after they had created a shared mental model of the relational threat. For these dyads, the responsibility of causing the relational threat was attributed to a party within the dyad, meaning that it was essential for dyads to adjust their way of thinking about the threat and put assurances in place to avoid future reoccurrence of the threat. Behavioral examples of how dyads achieved this include cognitive reframing and negotiating and updating future ways of working together.
Cognitive reframing of threats involved dyads shifting their way of thinking about a relational threat. Dyads themselves talked about this as “trying to see the positives” (N1) that could come from experiencing the threat as opposed to dwelling on the negative. Therefore, by engaging in cognitive reframing, individuals made a conscious decision to view a situation in a different light, which enabled them to avoid further confrontation with their counterpart and move beyond the relational threat. For example, in one dyad, the employee reflected on a disagreement with her manager about a hiring decision and the choice she made to avoid blaming or provoking him, and to learn from the situation: It could be very easy for me to be like, “well, I told you so!” I told you not to hire them. But it was more that we can all learn from this . . . it was more that okay, that happened, but it’s good that it happened because we can learn from it. (H2)
Negotiating and updating future ways of working involved dyads making changes to how they worked together or handled specific activities that were associated with the relational threat. Dyads coupled this with cognitive adjustments, meaning that they reframed their thinking about the threat and put measures in place to ensure the threat would not reoccur. For example, after reframing their hiring decision disagreement as a “learning,” Dyad H used this as an opportunity to improve their future hiring process: “We talked a lot about it, ‘okay, how can we improve our process and what we’re looking for?’ and that kind of thing” (H2). Within some dyads, this change was driven by one party, such that they negotiated with their counterpart how the activity or process that caused the threat would be dealt with in the future. For example, one employee who disagreed with his bonus allocation ensured that he and his manager agreed on how this would be handled next year: If this is the approach you’re taking that even though I’ve done a really good job, we’ve had a bad year on the team, then the opposite needs to be thought about for going forward. . . . So I suppose whilst, as I said, the outcome was the number didn’t change, that was how we resolved it being to make sure of that piece you know, I need to make sure we get a good bonus the following year if the team does, even if some jobs fall away. And he said “oh yeah, that all make sense.” (W2)
Dyadic problem solving of relational threat (pathway three)
Dyadic problem-solving involved counterparts coming together to come up with a solution to the threat facing their trusting relationship. Dyads following pathway three enacted dyadic problem-solving as a follow-on strategy after they had created a shared mental model of the relational threat. The rationale was that counterparts attributed the threat to an external source and the perception of a shared threat to their relationship brought dyads together to find a solution. Behavioral examples of this trust maintenance strategy include brainstorming solutions and seeking third-party support.
Brainstorming solutions involved dyads coming together to discuss potential ways of dealing with the relational threat and work towards a “resolution.” This was evident in Dyad Q when something went wrong with their project at the last minute. The manager refused to give up, striving for the dyad to: “Find the solution together to make it work, because all the other pieces were in place, and it was just one thing” (Q1). Her counterpart explained how they achieved this via brainstorming solutions: So I was like, “Well, I’d do this,” and I did sort of suggest maybe, I was like, “Oh, maybe we can meet them in the middle and do X, Y, Z.” And she was like, “No, I don’t think we should do that, I think we should do X or Y, but not Z. (Q2)
For some dyads, it was not within their scope to resolve a threat in its entirety, but members of the dyad could work together to minimize or partially resolve it. For example, one dyad talked about their challenges collaborating with another team in the organization. Although they could not control the roles and responsibilities of another team within the organization, one member of the dyad talked about how they worked together to leverage the situation: We just really discussed the ways of working with this team. And like we’re not going to shut down their operation, but let’s like, figure out how we can work with them . . .just very much being clever about it and working together, brainstorming, impromptu meetings (S2).
Seeking third-party support involved dyads looking to external sources to help them deal with relational threats. The goal here was for dyads to seek the perspective of someone on the “outside looking in” (B2) whom could help them understand things in “a different way” (B1). For example, one dyad talked about struggling to deal with a difficult client and sought advice from colleagues whom they speculated may have dealt with a similar situation. In this case, the manager first sought advice from a colleague and then encouraged his employee to do the same: He went away and then spoke with another partner in Org W to get their view. He told me, you know, maybe chat with someone on another team at your level to see what their view is . . . and then I suppose, how we came about it, you know, putting out different scenarios and discussing the matters between ourselves. (W2)
Outcome Phase
Following the experience of a relational threat, dyads followed one of three pathways in the trust maintenance process. Depending on the pathway dyads followed, the trust maintenance process unfolded differently, including having different outcomes for dyads’ trusting relationships. Through our analysis process, we identified a pattern such that dyads who followed pathway one maintained their trusting relationship, while dyads who followed pathway two or three strengthened their trusting relationship.
Trusting relationship maintained (pathway one)
Those dyads who followed pathway one maintained their trusting relationship. The rationale is that, within our sample, parties responsible for causing the relational threat were willing to accept their responsibility and work with their counterpart to overcome the disruption to their trusting relationship. For example, one employee acknowledged her role in delaying the dyad’s work getting sent to their client and accepted her manager’s emotional response: “I did get why she was annoyed. I slept in, unintentionally—like the alarm was set or whatever; it shouldn’t have happened” (C2). Here, the acceptance of responsibility by one party supported dyads to reach a shared attribution of the LOC of the threat, which served as an important stepping stone for dyads to create a shared mental model of the relational threat. Dyads who experienced ILOC threats also shifted their way of thinking about the threat and made changes regarding how they would handle the specific work activity or process that caused the threat in the future. This supported dyads to view the threat as “learning” (H2, I2, T1), and something that they are not concerned will cause a future threat to their trusting relationship. For example, although an employee disagreed with how his manager handled the bonus situation, he reflected on being content with how the dyad worked through the experience of the relational threat, and how this supported them in maintaining their trusting relationship: It at least allowed me to voice how I felt about it. And I thought he was accepting in a way and accepting of the work that I did, which was good. . . . [It had] no impact on the relationship in that sense in terms of trust because I continued as in and look there is always next year. (W2)
Therefore, dyads’ proactive responses to dealing with relational threats—before trust was damaged—supported them in maintaining their existing trusting relationship. In the absence of dyads’ proactive responses, it is conceivable that some of the experiences of relational threats that participants shared could have resulted in a loss of trust. Participants themselves recognize that their active maintenance supported the dyad to “blow off everything that happened,” noting that otherwise they “would still be in the same situation but the tension and resentment and everything else that builds up could effectively continue” (C2).
Reflecting on a situation within a previous work relationship, one participant noted that, rather than coming to her when another organizational member complained about her, her manager “let it fester and then it all came out at a board meeting” (S1). Here, the participant highlighted that her manager’s approach to dealing with a disruption—and her lack of proactive response in the first place—resulted in the experience damaging their trusting relationship: Rather than coming to me and saying we need to have a conversation about x, y, and z, which we would have just worked out what we needed to pick up. I saw her saving face by doing it, confronting me in front of, you know, everybody else, so I totally lost trust in her. (S1)
Trusting relationships strengthened (pathways two and three)
Our data points to two explanations for the experience of a relational threat strengthening dyads’ trusting relationships. First, relational threats served as an opportunity for counterparts to demonstrate who they are when “their backs against the wall” and to gather new information about how they handle such disruptions: “If everything was just plain sailing, and you weren’t coming up against different scenarios or situations like you wouldn’t, I wouldn’t see this side to her? So I would just have a one-dimensional view of her” (Q2).
This is further evidenced by Dyad K who talked about their experience of adapting to working together during the COVID-19 pandemic. From both perspectives, they felt this was handled well, with the manager referring to this as a “period of building the trust, because you need to set up some new process. And we’re doing it together” (K1). This strengthening outcome was reinforced by an employee who also reflected that new information made available via the experience of a relational threat also provided them with assurance about their trusting relationship’s resilience to future threats: The trust only has grown from it because it was such a thing, a very intense situation that we both came together and worked as a team. . . . If one of these situations were to come up again, I know we both have each other’s back, and we could do it again because that one was extremely stressful. (K2)
Second, dyads who strengthened their trusting relationships described a sense of shared emotion and vulnerability to relational threats. For example, one participant reflected that the dyads shared experience of struggling to work with the head of their department “bolstered our trust between us because we kind of felt like we had a common enemy” (E1). Another dyad talked about experiencing “shared adversity” when their organization was being sold and both parties felt “frustrated by the same thing” (M1). Despite perceiving that they were “both in the bunker,” the dyad reported that they had “gone through the whole experience together” (M2), which resulted in a shared sense of “camaraderie” (M1). Therefore, despite dyads being faced with relational threats that were often associated with avoidance-oriented emotions, dyads perceived these as a shared experience that served to strengthen their trust.
This was further evidenced by another dyad reflecting on how the experience of a relational threat strengthened their trusting relationship. For example, the manager reflected that she and her counterpart have: “gotten closer with all the things that have happened and like facing the challenge in the team has gelled us a lot more” (U1). Her counterpart attributed the strengthening of their trusting relationships to the shared emotion and heightened vulnerability associated with experiencing a relational threat: I think actually it built our trust more because I understood more where she was coming from and maybe she saw a more vulnerable side to me. . . . It’s nice in a relationship when you have both see each other like feel upset or feel stressed out, you know, those things like it does make you feel closer. (U2)
Discussion
Interpersonal relationships are likely to experience threats to their existing trusting relationships as they navigate their changing contextual landscape and respond to discrete organizational events (Korsgaard et al., 2018). This research aimed to empirically explore how the process of interpersonal trust maintenance unfolds following the experience of a relational threat. Our findings illustrate that dyadic counterparts initially assessed the threat at the individual level, before working to overcome the threat with their dyadic counterpart via trust maintenance strategies. Depending on their assessment of the threat, dyads followed one of three pathways in the overall process of trust maintenance. This determined the combination of trust maintenance strategies they used, and their trust outcome—i.e., whether they maintained or strengthened their trusting relationship. These findings allow us to offer several contributions to theory and practice.
Contributions to Theory
Our research makes three important contributions to theory. First, we contribute to trust theory by illustrating how relational threats can be harnessed to strengthen manager–employee trusting relationships. To date, the dominant focus has been on how negative relational experiences undermine trust, and how this can be restored (for a review see Sharma et al., 2023), or, most recently, on how trust can be preserved or maintained (Gustafsson et al., 2021; Weibel et al., 2023). Our observations (unexpectedly) revealed that navigating a relational threat strengthened many of our dyads’ trusting relationships. We suggest this strengthening occurs because new information becomes available to dyads when relational threats disrupt the rhythms of a trusting relationship (Korsgaard et al., 2018) and trigger dyads to look for new ways of trusting (Möllering, 2013; Weibel et al., 2023). This shift in their usual way of doing things allows individuals to discern how their relational counterparts respond in such instances. Indeed, Ballinger and Rockmann (2010) suggest that certain events can cause a durable positive or negative change in organizational relationships because they override an individual’s heuristic about their counterpart. For example, individuals’ threat-reducing behavior and trust repair efforts can override counterparts’ initial trustworthiness assessments with new perceptions, impacting future trusting behavior (Campagna, Mislin, Dirks, & Elfenbein, 2022; Williams, 2007). Hence, dyads who successfully navigate a relational threat acquire new information about one another—and the resilience of their trusting relationship—which replaces their existing trust belief (heuristic) and strengthens their trusting relationship.
A further explanation is that dyads experience a relational threat as a shared experience, characterized by shared vulnerability. This was particularly salient for ELOC threats, as dyadic counterparts were in a position of shared vulnerability to external disruption. For such dyads, counterparts’ volitional will to be vulnerable to one another remains (van der Werff et al., 2019), but vulnerability also becomes a contextual feature of the environment their relationship is operating in, and something that is experienced together. We extend Misztal’s (2012) and Weibel and colleagues’ (2023) theorizing on vulnerability by demonstrating that dyads experience vulnerability relationally and argue this sense of shared vulnerability strengthens their bond. Importantly, despite an ILOC relational threat initially triggering a sense of heightened vulnerability for one party, those who opt to share their feelings engage in active vulnerability (Nienaber, Hofeditz, & Romeike, 2015) and provide a platform for reciprocal vulnerability. This shifts the vulnerability from being more salient for one party to being shared and experienced relationally. Taken together, these insights represent a useful extension as—despite acknowledging vulnerability as a relational construct— scholarship has mostly conceptualized it as experienced by the trustor or trustee individually (Nienaber et al., 2015). Finally, our observations of contextual and active vulnerability also add value to the ongoing debate of whether vulnerability is an existential condition or a deliberate decision (Schafheitle, Weibel, & Möllering, 2023).
Our second contribution is an empirically derived model of interpersonal trust maintenance. This is the first of its kind and represents an important addition to the trust literature—particularly given the challenges in applying insights drawn from one conceptual level of trust to another (Fulmer & Gelfand, 2012). We put forward a model that portrays the process of interpersonal trust maintenance to occur across three phases and at multiple conceptual levels (see Figure 2). Specifically, we illustrate that individual parties each make a subjective assessment of a relational threat in the assessment phase before dyadic counterparts work together to overcome the relational threat via trust maintenance strategies in the active maintenance phase, and finally enter the outcome phase. We also delineate different pathways that dyads follow in the trust maintenance process, which are determined by their assessment of the relational threat. Depending on the pathway dyads follow, they use a different combination of trust maintenance strategies, and the process of overcoming the relational threat with mutual agency results in dyads either maintaining or strengthening their existing trusting relationship. Such insights into the processual dynamics of trust maintenance extend previous research, which has primarily focused on the strategies trustees can adopt to avoid a loss of their counterpart’s trust (Gustafsson et al., 2021, Weibel et al., 2023, Williams & Belkin, 2016). Therefore, by shifting the focus to the relational experience of disruption, we lend novel insight into how dyads overcome threats to maintain their existing trusting relationship.
In comparison to the strategies put forward in previous work, we see both similarities and differences to the trust maintenance strategies in our model (i.e., creating a shared mental model, cognitive and structural reassurance, and dyadic problem-solving). For example, dyads initially creating a shared mental model before using one or other follow-on strategy aligns with the idea that individuals use interpersonal sensemaking and perspective-taking to determine how they should approach trust maintenance (Williams, 2007; Williams & Belkin, 2016). Further, in line with Gustafsson and colleagues’ (2021) trust preservation practices, our strategies also have emotional, cognitive, and behavioral components. That said, we move theory forward by delineating which strategies are aligned to dealing with relational threats attributed to different sources. Specifically, we contend that cognitive strategies that shift dyads’ thinking about threats are more fitting for ILOC threats, while behavioral solution-focused strategies are more fitting for ELOC threats. This builds on recent theorizing by Weibel et al. (2023) that positions certain strategies best to deal with specific core trust issues and types of vulnerability (differentiating between symbolic and substantive strategies). Compared to maintaining trust in an organization where such symbolic strategies that serve visionary purposes are fitting (see Gustafsson et al., 2021, Weibel et al., 2023), interpersonal maintenance strictly involves the use of tangible strategies geared towards overcoming the relational threat (i.e., substantive strategies). This difference is likely attributable to our interpersonal lens, wherein interdependent managers and employees are dealing directly with one another to overcome a relational threat that is affecting both parties.
Our final contribution is an empirical illustration of the role of attribution and emotion in interpersonal trust maintenance. While Weiner’s (1985) causality attribution theory has advanced our understanding of trust development and repair (e.g., Dirks, Lewicki, & Zaheer, 2009; Korsgaard et al., 2018; Lewicki & Bunker, 1996; Tomlinson & Mayer, 2009), our research represents its first application in the trust maintenance literature. In trust development and repair, the attribution process enables individuals to make sense of the factors that caused a specific outcome, and to shift attribution towards or away from their counterpart in favor of trust development or repair (Korsgaard et al., 2018; Tomlinson & Mayer, 2009). In the context of trust maintenance, both parties’ assessment of the LOC formed part of the overall sensemaking process, triggered by the experience of a relational threat. This assessment is functional, such that it delineates the appropriate active trust maintenance strategies for dyads to overcome the relational threat depending on the LOC—thus extending the relevance of the assessment beyond just assigning or shifting blame. Moreover, relational threats attributed to external sources are still seen as disrupting the ongoing norms in trusting relationships and in need of maintenance efforts. This differs from the attribution of a trust-violating event to an external source that implies “trust repair is moot” (Tomlinson & Mayer, 2009: 101). Therefore, by shifting the focus to negative relational experiences that present a risk to existing trusting relationships, we offer new insight into the role of attribution and outline a process whereby dyads can work together with mutual agency to overcome relational threats from both internal and external sources.
We also add valuable insight into the role of emotion in the trust maintenance process. As noted, following the experience of ILOC relational threats, individuals either had an approach or temporary avoidance emotionally triggered response following their assessment of the threat, meaning the LOC assessment alone was not enough to explain these different responses. Further, negative emotions, such as upset or anger, resulted in different responses, implying that the patterns we found in our data were more nuanced than whether emotions were positive or negative (Lerner, Li, Valdesolo, & Kassam, 2015). By applying learnings from the emotions literature, we interpreted that the function of the emotion individuals felt in reaction to the relational threat determined their emotionally triggered response (Van Kleef, 2009). Specifically, emotions serve an interpersonal function of either making one feel further from a counterpart (avoidance-oriented emotions, e.g., anger) or closer to them (approach-oriented emotions, e.g., upset; Methot et al., 2017). Given that dyadic counterparts in our sample responded in the same way and did not report any approach-avoidance conflicts, our findings support that interpersonal functions of emotions can operate at the relational level, as opposed to the observer being drawn to or away from their relational counterpart (Van Kleef, 2009). Overall, applying insights from the emotions and broader relationships literature enabled us to make sense of the intricacies of emotional responses that individuals reported, and simultaneously address a call for research studying emotion and trust to look beyond general positive and negative affect (Lee, Dirks, & Campagna, 2023).
Beyond the role of emotion in determining dyads’ approach or avoidance responses, emotional expression supported some dyads to create a shared mental model of the relational threat, and the experience of shared emotion partially explains some dyads strengthening their trusting relationships. This implies that the role of emotion is thoroughly reflected throughout our model, addressing recent criticism of its absence in trust literature (Dirks & de Jong, 2022; Lee et al., 2023). Finally, our research does not consider the role of attribution or emotion in interpersonal trust maintenance in isolation or at different stages along the lines of what we have seen in the trust repair literature (e.g., Tomlinson & Mayer, 2009). Instead, our theorizing suggests that cognitive and affective sensemaking processes happened simultaneously and, together, have important implications for how dyads deal with relational threats. This idea that cognition and affect interact to influence each other is consistent with other recent developments in the trust literature (e.g., Lee et al., 2023; Legood et al., 2023).
Practical Implications
Building on these contributions to theory, our research also has significant practical value. We discovered that disruptions to the normal rhythms of trusting relationships amplify the need for dyads to engage in active trust maintenance efforts. Given the increasingly uncertain environment trusting relationships are operating in, uncovering tangible strategies that can be used to maintain trust is a top agenda item for organizations (Dirks & de Jong, 2022)—which, we argue, is particularly salient in the context of interdependent manager-employee relationships. We address this by outlining three overarching trust maintenance strategies: creating a shared mental model; cognitive and structural reassurance; and dyadic problem solving, which dyads can use to proactively maintain their trusting relationship in the face of a relational threat. We offer examples of how these higher-level strategies can be enacted at the behavioral level and delineate which strategies are more or less fitting for threats with certain characteristics. This focus on behavioral-level examples extends the work of Williams (2007), who offers specific threat-reducing behavioral examples of how interpersonal emotion management strategies can be enacted to support trust development and ongoing cooperation. In essence, we provide a blueprint for organizations in terms of the specific behaviors that will support managers and employees to maintain trust, which holds significant relational and organizational value. This builds on recent empirical research by Sala and Pratt (2023), who contribute a trust repair template for organizations, and together address a recent call to action by Dirks and de Jong (2022) for trust scholars to ensure their work has practical value for organizations and society alike.
In conjunction with the practical strategies, our research also offers organizations and their employees a more holistic understanding of the trust maintenance process and certain nuances they should be aware of. For example, by highlighting the different emotionally triggered responses that form part of the maintenance process, individuals are made aware that in certain instances their counterparts may need some space before they are ready to engage in maintenance efforts. Awareness of these nuances will promote fluidity in the maintenance of valuable organizational relationships. At the same time, our research is practically important for learning and development professionals in organizations. Specifically, we see the insights from our research supplementing conflict management training, socialization programs, and team or leadership development programs. In some cases, embedding a mock relational threat into programs could be a worthwhile endeavor (Ballinger & Rockmann, 2010) that would allow individuals to practice enacting maintenance strategies in a controlled environment. This would instill confidence in individuals to deal with threats their trusting relationships will inevitably face.
Limitations and Future Research
As with all research, our study is not without limitations. Our research is limited in its focus on manager–employee relationships, meaning that what we uncovered in this relational context may unfold differently in another trusting relationship (Fulmer & Gelfand, 2012). The relational context is important to consider, as individuals may be motivated to trust a specific referent depending on certain characteristics of the relationship (van der Werff et al., 2019). Given our focus on interdependent manager–employee relationships, we were curious about power imbalance, which is often referenced as a key characteristic of such work relationships (Brower et al., 2000). However, we did not interpret power dynamics to significantly influence dyads’ maintenance efforts. For example, both managers and employees willingly made themselves vulnerable by accepting responsibility for causing ILOC threats. Further, employees freely expressed disapproval of their managers’ behavior towards them and negotiated their preferred way of working together in the future, all of which signals a more equal distribution of power. We argue that the experience of an ELOC threat makes the distinct roles of trustee and trustor less salient due to the threat being perceived as something that dyads face together, creating a sense of shared vulnerability regardless of any hierarchical differences. Based on these insights, we believe that our findings could also be generalized beyond employee–manager relationships to other work and potentially non-work relationships; however, further research is required to test these boundary conditions. That said, we appreciate that maintenance efforts may be more important in certain relationships wherein the dyadic partners are embedded in a shared, changing context—future research should also explore this idea. By shifting the research focus to other relationships, as well as from dyads to triads (see Dirks & de Jong, 2022) or to the team level, future research could compare if the processual dynamics play out in the same way across different relationships or levels of analysis.
Future research should also consider how other dyad characteristics, for example, gender, relational tenure, culture, and industry, influence the experience of a relational threat and the maintenance dynamics. In particular, research should explore how the context of the relationship in which a threat is interpreted may influence individuals’ acceptable norms of behavior. For example, recent research shows that women are more sensitive than men to benevolence when forming trust judgments (Qiu, Kesebir, Günaydin, Selçuk, & Wasti, 2022), indicating that gender may influence tolerance levels to certain types of relational threats. Relational tenure is another worthwhile consideration as research indicates that the history of interactions in a trusting relationship influences how negative relational experiences are evaluated (Lewicki et al., 2006; Tomlinson & Mayer, 2009). Other factors, such as culture and industry, could also be influential in terms of shaping what individuals value, making them more or less accepting of certain behaviors. Our sample was limited in its cultural diversity; however, despite being gender-balanced and having variation across different industries, we did not interpret these characteristics to influence the processual dynamics. When drawing comparisons between dyads’ experiences of disruption to identify our inclusion criteria, we noticed that dyads with longer relational tenures were more likely to experience disruptions that appeared conceptually close to minor violations as relational threats. It is important to note that our ability to attribute this or any differences to dyad characteristics is limited, as there were other points of difference surrounding dyads’ experiences of relational threats. In particular, dyads talked about a broad range of threats, meaning differences could be explained by characteristics of the threat. One interesting approach would be for future research to control for this variation by focusing explicitly on one type of disruption. This would allow meaningful interpretations regarding how dyad characteristics influence the threshold for threat across relationships and enable researchers to extend theorizing on how the acceptable norms of behavior are not fixed or absolute.
Another avenue for future research is to examine how the strength of the relationship and/or preexisting levels of trust influence the experience of a relational threat. In our sample, the dyads who overcame threats attributed to an internal source reported having strong relationships beforehand. This aligns with Williams and colleagues’ theorizing that positive interpersonal affective bonds support individuals to respond to perceived threats and trust-violating events more cooperatively (Williams, 2007; Williams et al., 2020). Relatedly, Robinson (1996) found that employees with initially higher levels of trust in their employer were less likely to report the perception of a psychological contract breach a year later. However, given the qualitative nature of our research, we did not measure the strength of dyads’ (trusting) relationships. Future research should explicitly measure relationship strength and preexisting levels of trust before the experience of a relational threat to explore how this influences dyads’ threshold for interpreting the event as a threat. Building on this, experimental studies could modify the severity of threats to determine if the tipping point, in terms of what causes a trust violation, varies depending on the strength of the relationship, and further clarify the boundary conditions between a relational threat and trust violation.
A related idea would be to vary the time between a relational threat and when participants engaged in maintenance efforts to determine the window of time to intervene before a relational threat may result in a loss of trust. As noted, participants recognized their proactive responses to dealing with relational threats as important to maintain their trusting relationships, as well as ascribing a loss in trust to a lack of action in the cases of violation. Compared with dyads who had temporary avoidance emotionally triggered responses and then came back together to actively maintain their trusting relationship, it seems probable that a longer-term avoidance response would harm dyads’ trusting relationships. Accordingly, it would be an important endeavor for future research to gain more precise clarity regarding the cutoff point whereby maintenance efforts may no longer be effective, and when a lack of action or longer-term avoidance may result in a loss of trust. Interestingly, findings that support dyads initially pulling away in response to avoidance emotions go against recent appraisal theories of emotion which indicate that anger relates to approach motivational tendencies (for a review see Carver & Harmon-Jones, 2009). In this view, anger arises when movement toward a desired goal is blocked, and this motivates efforts to reopen the path to the desired goal (Frijda, 1986). While this was not the immediate response observed in dyads in the present research, the avoidance responses were temporary. The comparative experience of dyadic counterparts who felt upset and approached one another without delay suggests that threats that evoke anger-based emotions may take individuals longer to make sense of. Future research should further examine this idea and how it affects the window of time for intervention.
Future research should adopt a longitudinal design to address these ideas and explore how trusting dynamics unfold over time more broadly (e.g., van der Werff & Buckley, 2017). In particular, it would also be interesting to observe if the nature of trust was changed by the experience of relational threats and whether this impacts dyads’ future trusting behavior. Some dyads reported feeling more resilient to future threats; however, this was something that dyads who experience ELOC threats more commonly reflected on. It makes sense that dyads who overcame a threat attributed to an external source would feel more resilient to future threats as these represent a unifying experience wherein dyadic counterparts came together to overcome a common threat (Flade, Klar, & Imhoff, 2019). Future research should examine if the process of trust maintenance supports all dyads to feel more resilient to future threats, or influences trust in other ways: for example, in the case of ILOC threats, if the party not responsible for causing the threat continues to trust at the same level, or cooperate to the same degree, but is less certain in their trust judgment (see Holtz, De Cremer, Hu, Kim, & Giacalone, 2020). It would be hugely interesting to empirically examine if their future behavior reflects this uncertainty, i.e., if they are more considerate in future trusting behavior, or if they are willing to assume risk by engaging in trusting to the same degree as before the relational threat (Mayer et al., 1995).
Another related idea would be to build on the work of Legood and colleagues (2023) and apply insights from Lerner and colleagues’ (2015) review on emotion and decision-making more broadly to trust, and to tease out how emotion influences individuals’ decision to trust following a relational threat. Recent trust scholarship uses the distinction of prospect emotions (see Ortony, Clore, & Collins, 1990) to illustrate that trusting is followed by a vulnerability phase that is characterized by different emotional reactions—such as hope or fear (Ballinger, Schoorman, & Sharma, 2024). This distinction is fitting to explore relational threats caused by a party within the dyad, which may induce fear about the potential of future threats, versus relational threats attributed to an external source that had a strengthening effect on trusting relationships, which may induce hope. Future research should further unpack the longer-term cognitive and affective implications of experiencing different types of relational threats, and extend our theorizing on how ongoing trusting dynamics unfold over time.
Conclusion
This study provides novel insights into interpersonal trust maintenance. We explore how the process of trust maintenance takes form in our sample of manager–employee dyads, following the experience of a relational threat. Our research extends the nascent stream of research on trust maintenance by illustrating how this process unfolds interpersonally, across multiple phases. We believe that trusting relationships will inevitably continue to experience relational threats, given the heightened interdependence that accompanies today’s working world. Therefore, our research offers timely theoretical and practical value, as well as a new agenda for trust scholars to extend our theorizing.
Footnotes
Acknowledgements
This research was conducted with the support of the Irish Research Council under the Government of Ireland postgraduate scholarship and Dublin City University Business School postgraduate scholarship. The authors extend their gratitude to the editor, Nicky Dries, and the two anonymous reviewers for their valuable and constructive feedback throughout the review process. The authors would also like to thank Michele Williams, Finian Buckley, and Simon Schafheitle for providing insightful feedback on earlier iterations of the manuscript, as well as the wider First International Network of Trust (FINT) community for their thoughtful input on the research presented at the 12th FINT conference in June 2023.
