Abstract
This paper focuses on the mixed
Introduction
Networked control systems (NCSs) have become a hot research field, which have attracted increasing attention because of their applications in manufacturing plants, remote processes, and mobile sensor networks (Qiu et al., 2013; Tong et al., 2022; Zhang et al., 2020a). Although they have many practical advantages, there might be network-induced phenomena in the networked systems, such as network-induced time delay, quantization, and packet loss. These phenomena can have an impact on the system performance. Therefore, it is practical to study the network-induced phenomena in the NCSs (Bahreini et al., 2021; Wang et al., 2020; Zou et al., 2016). These network-induced phenomena are mainly caused by the process of data transmission in the network.
In general, the limited network bandwidth has a great influence on the transmission of data. Then, some methods have been proposed to overcome the challenge. On the one hand, the signal must be quantized before transmission through the network channels. Up to now, the research on quantization has obtained abundant research results (Chen and Chang, 2022; Wang and Yu, 2018; Wu et al., 2021). In general, the quantization strategies can be divided into static quantization and dynamic quantization. As for the static quantization, the common method is a sector boundary, which regards the quantization error as norm-bounded uncertainty (Fu and Xie, 2005; Gao et al., 2008). However, static quantization is required to have the limited quantization level. Compared with the static quantization, dynamic quantization is time-varying (Brockett and Liberzon, 2000). The quantization range of dynamic quantizer can be adjusted by the quantization parameter, which can scale the quantization level. Therefore, dynamic quantization is more general and has attracted the attention of a large number of scholars. On the other hand, network communication protocol is an effective method to solve the problems of data conflicts and channel congestion caused by the limited bandwidth. During the transmission of data through network channel, special transmission rules can be designed. According to the special rules, each node in the network can be assigned transmission rights at specific instants. As the result of which, the communication burden of the network can be reduced. Thus, it is of practical significance to study the communication protocols, and there have been many research results on communication protocols. At present, RR protocol (Shen et al., 2020; Zhao et al., 2020), weighted try-once-discard protocol (Zhang et al., 2020b; Zou et al., 2016), and stochastic communication protocol (Ren et al., 2021) are the most studied communication protocols. Among them, the RR protocol is a static protocol, which evenly distributes the network usage rights to all network nodes through a preset token ring. Because of its unique characteristics, the RR protocol naturally receives attention in load balancing and security monitoring (Wang et al., 2018; Zhao et al., 2020).
During the transmission of data through network channels, not only the problem of the limited bandwidth needs attention but also the cybersecurity deserves attention. When data are transmitted through the network channels, it may be subject to malicious attacks (Liu et al., 2018; Xiong et al., 2020; Yu and Chang, 2022). Due to the attacks, the receiver may not receive data or receive an incorrect data. Generally speaking, the common attacks include denial-of-service attacks and deception attacks, among which deception attacks are one of the most dangerous network attacks. The means of deception attacks is to inject pseudo data into normal data during transmission, with the purpose of destroying normal transmission to obtain confidential information or forge data (Du et al., 2019; Yuan et al., 2020). Recently, some important works about security control against network attacks had been launched. Wang et al. (2020) studied the problem of resilient memory event-triggered control for a new NCSs model under random deception attacks. Zhao et al. (2022) proposed a dynamic detection method based on rotor speed observer/estimator to identify false data injection attacks. After the location attacks, the adaptive resilient control strategy of generator torque is realized to ensure the control target of optimal power tracking. In the work by Li and Zhao (2021), the problem of resilient adaptive dynamic surface control was researched for more general nonlinear network physical systems, and an attack compensator was constructed to mitigate the impact of sensor and actuator attacks.
Not only can the network-induced phenomena have an influence on the performance and stability of NCSs but also the uncertainty and external disturbance may affect them (Xu et al., 2021). Due to the sensor aging and other factors, there always are uncertainties in networked systems. The robust control method can be used to eliminate the impact of uncertainties on system performance, including
Motivated by the observations above, the aim of this paper is devoted to solve the mixed
A unified framework of the mixed
A new performance analysis index is proposed to handle the same-dimensional constraint of control output and external disturbance.
Sufficient conditions for the design of the mode-dependent resilient controller and the dynamic quantizer are presented to ensure the stochastic stability and specified mixed
The paper is organized as follows. The system description, communication network with quantization, deception attacks, and the RR protocol, and the closed-loop system are provided in section “Problem formulation.” Section “Main results” gives the main results. Section “Simulation results” presents a simulation result to show the feasibility of the proposed method. The conclusion is drawn in section “Conclusion.”
Problem formulation
System description
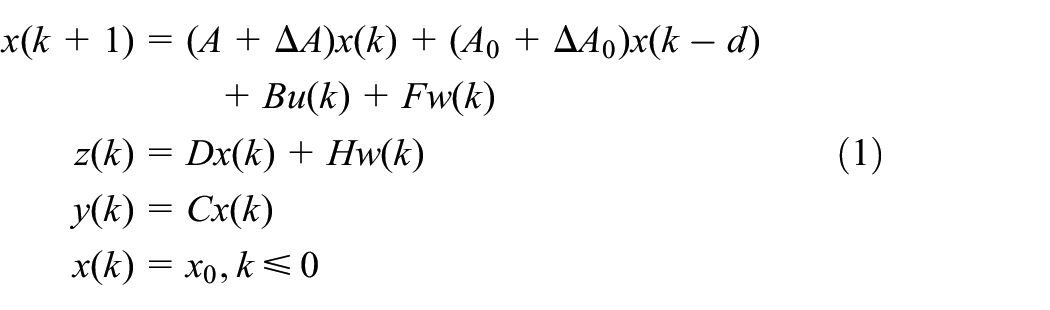
Consider a class of uncertain discrete time-delay systems described by the equation of state
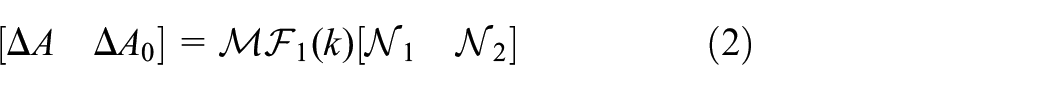
where
where
Communication network
In general, for network communication channels with limited bandwidth, it is inevitable that the signal is usually quantized before transmission, and the RR protocol is considered to avoid data conflict in the process of information transmission. With the use of commercial operating systems, the possibility of network systems being attacked increases greatly. Most deception attacks are directed to fraudulently inject signals from the transmitter to the processor. When it happens, the network system becomes weak, which leads to the decline of system performance. The system architecture is given in Figure 1 to incorporate these dynamic properties. In the coming part, the detailed description of the measurement output affected by dynamic quantization, random deception attacks, and RR protocol will be presented.
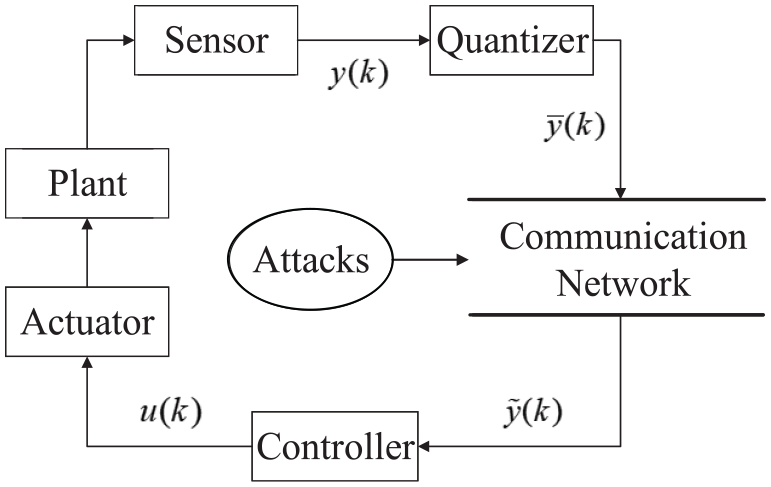
Structure of NCSs.
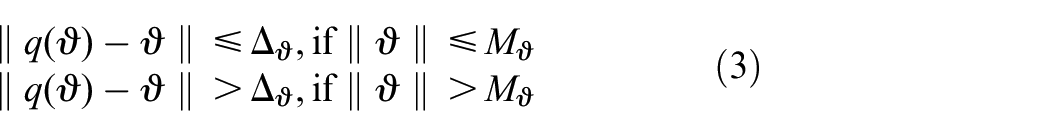
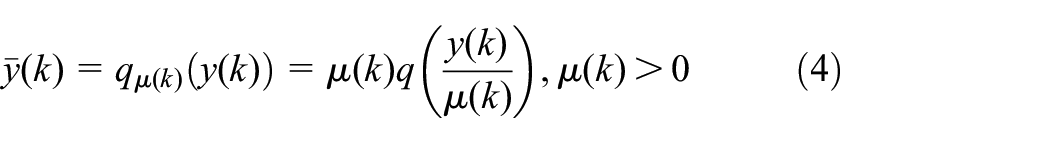
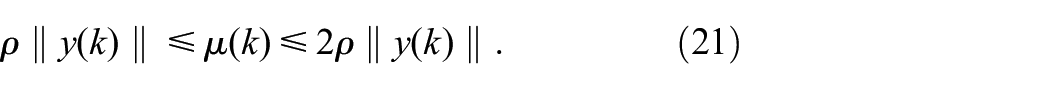
First, the dynamic quantizer with general form in Brockett and Liberzon (2000) is adopted for quantization of the measurement output, whose property is introduced as follows
where
where
In this paper, it is assumed that there are
where the function “
In addition, deception attacks may occur in the transmission process of measurement outputs because of the openness of the network. That is to say, the transmitted quantized signal
where
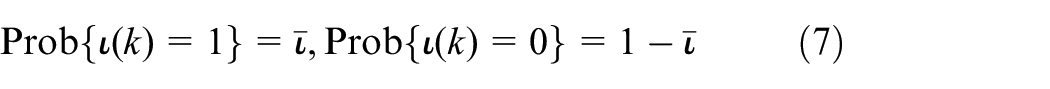
and has the following some statistical properties
where
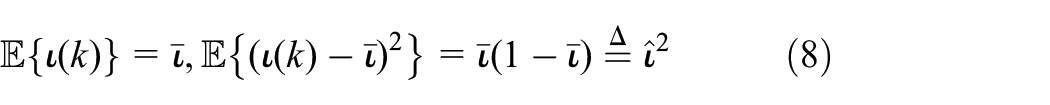
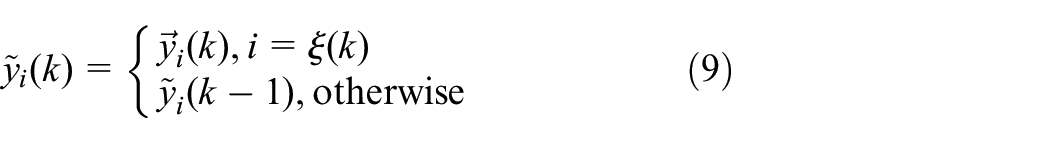
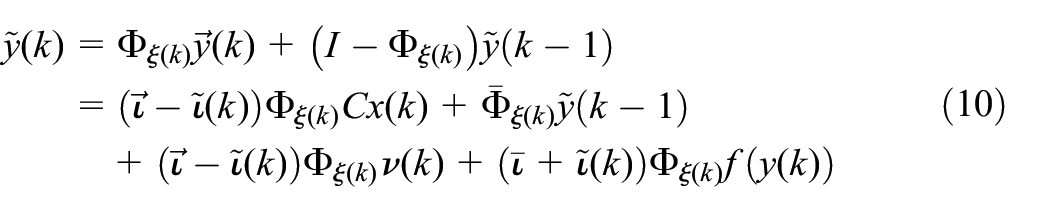
Analogously, the combination of received measurement output
Then, defining the update matrix
where
where
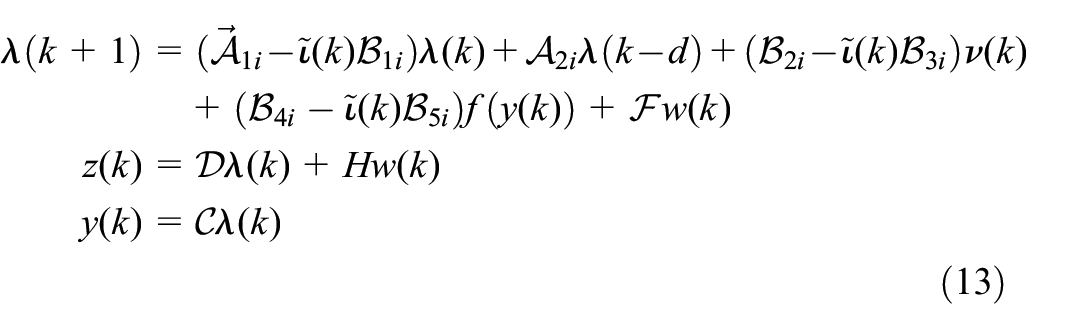
Closed-loop system
The control strategy will be developed in this part, where a mode-dependent resilient controller with gain fluctuation is considered to stabilize system (1) and improve its robustness, which is shown as
where
where
To articulate the control aim of this paper, the following definitions should be provided first.
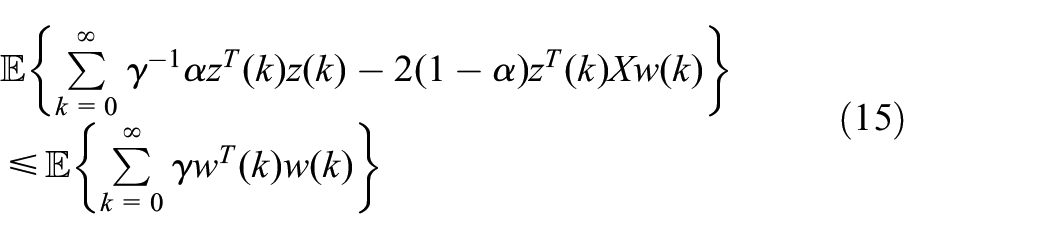
Then, the objective of this paper can be summarized to design a desired controller, so that resulting system (13) can guarantee the stochastic stability and a mixed
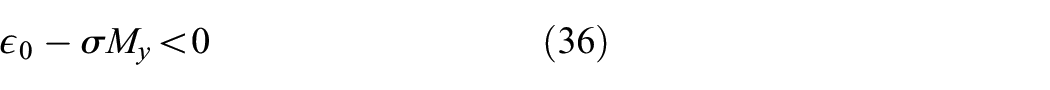
the necessary and sufficient conditions for the above establishment if there exits a scalar
is fulfilled if the following condition holds
Main results
Mixed
and passivity performance analysis
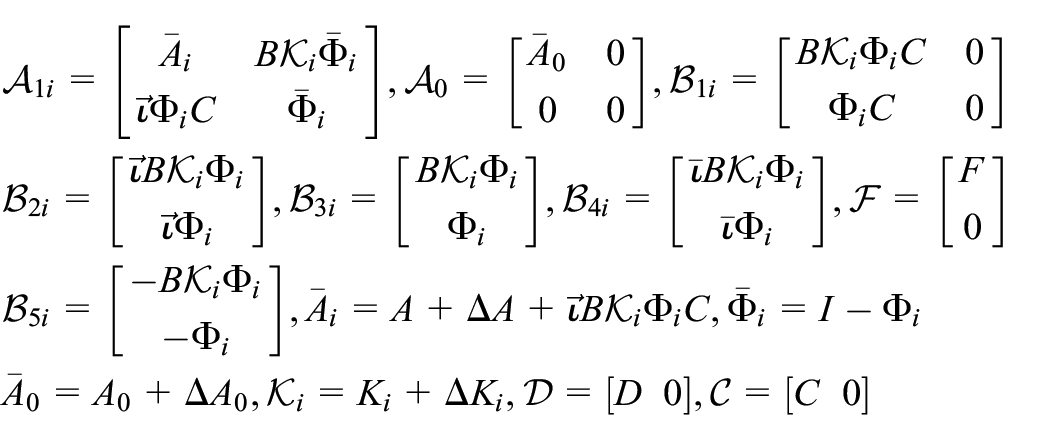
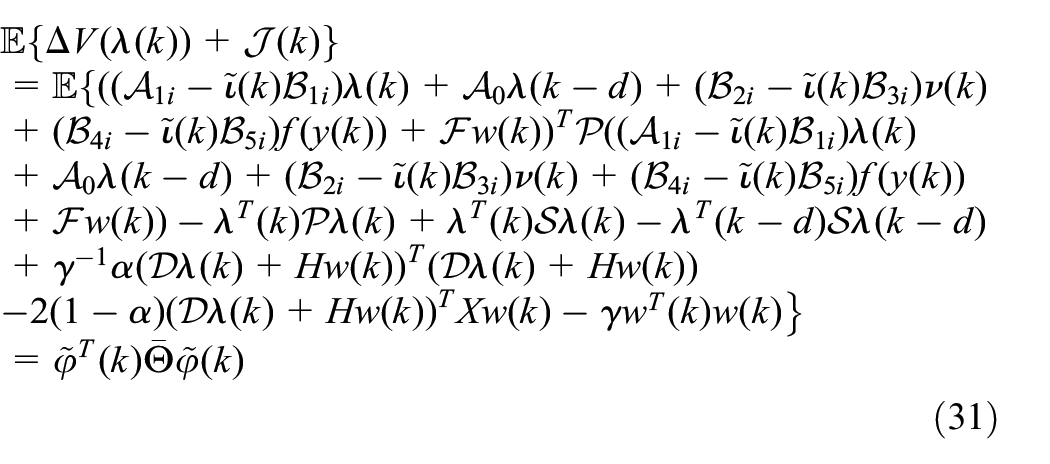
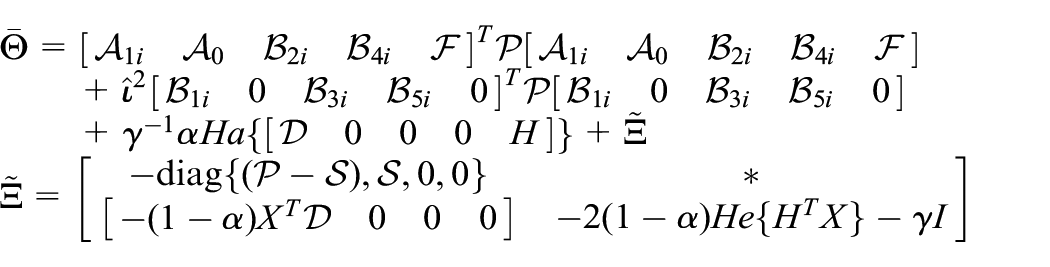
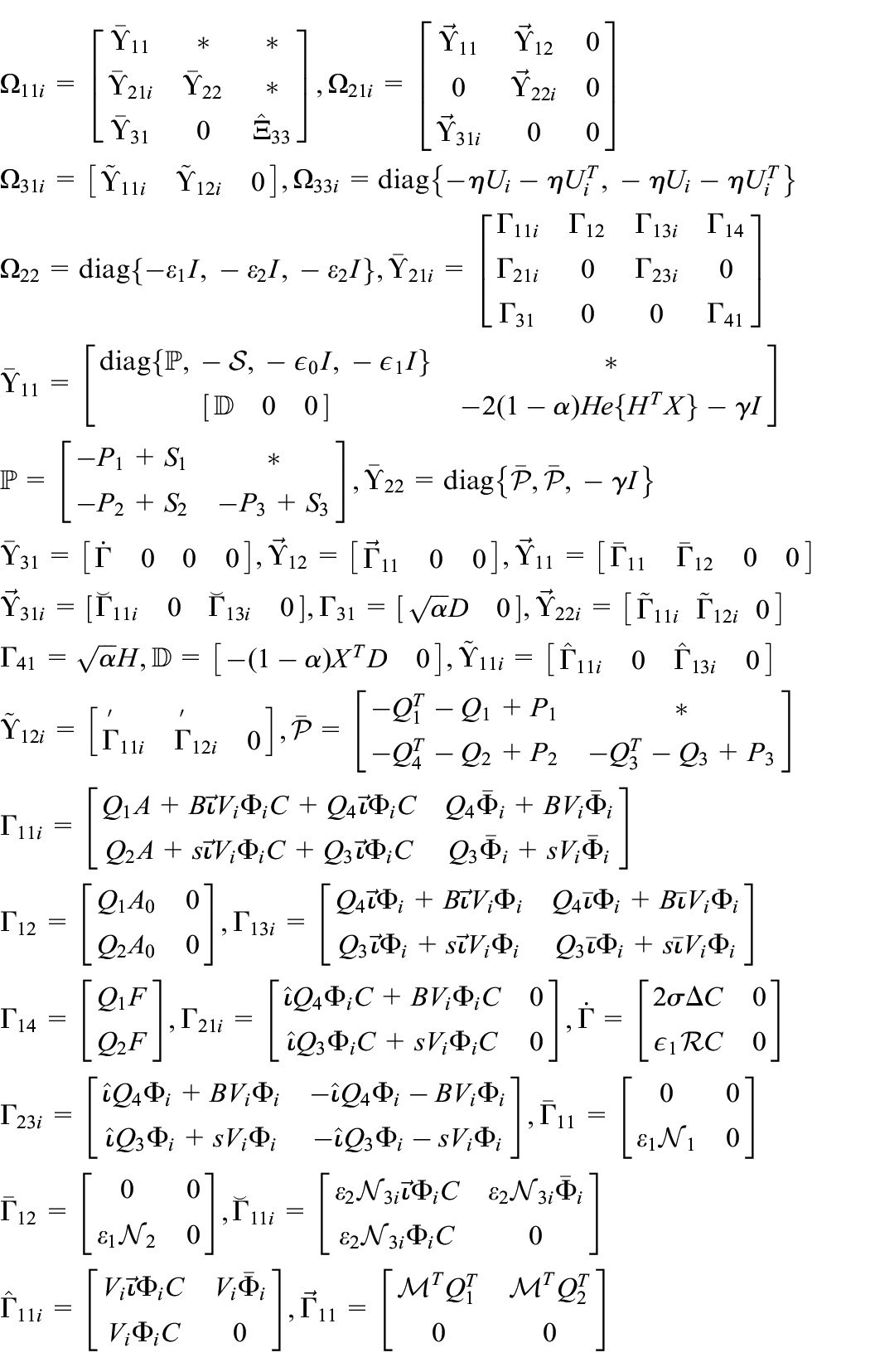
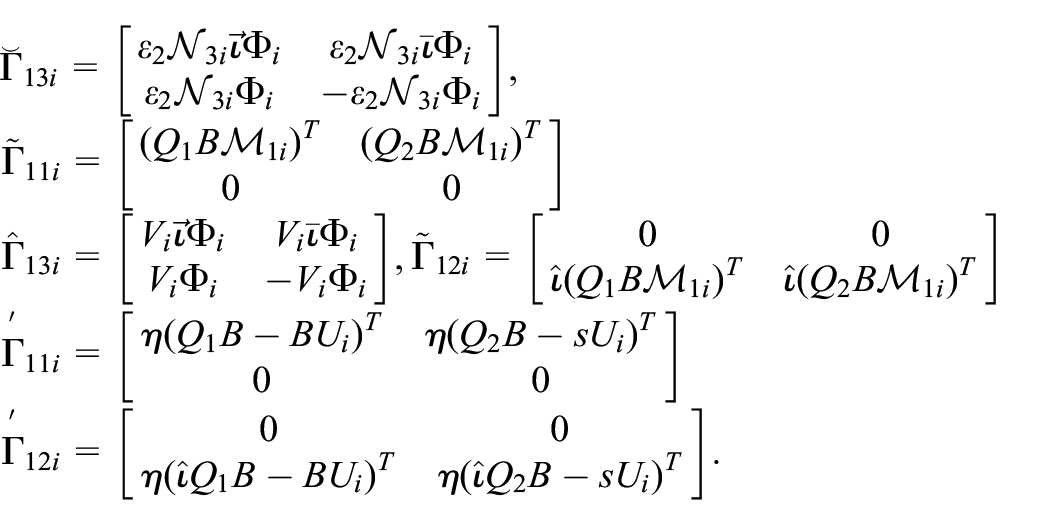
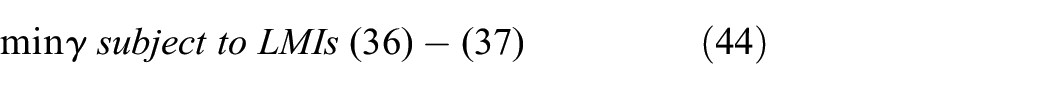
In this section, some principal results are performed. First, a new performance analysis criteria are provided for closed-loop system (13) under the effect of system uncertainties, controller gain perturbation, time delay, dynamic quantization, deception attacks, and RR protocol. Then based on this important result, sufficient conditions are given for parameterized representations of the controller and quantizer.
where
and dynamic quantizer’s parameters
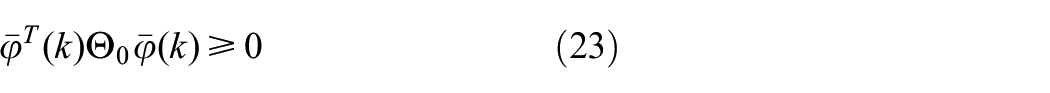
Then, defining
where
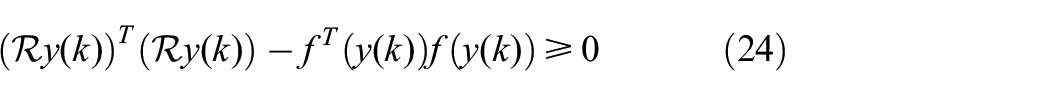
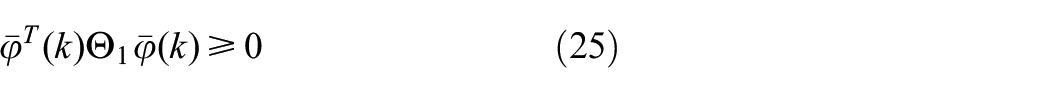
On the other side, the restrictions given in Assumption 1 can be further described as
Similar to the above, we have
where
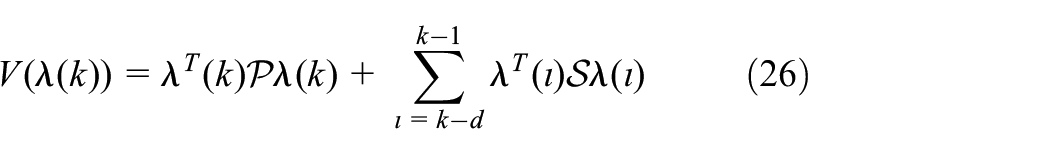
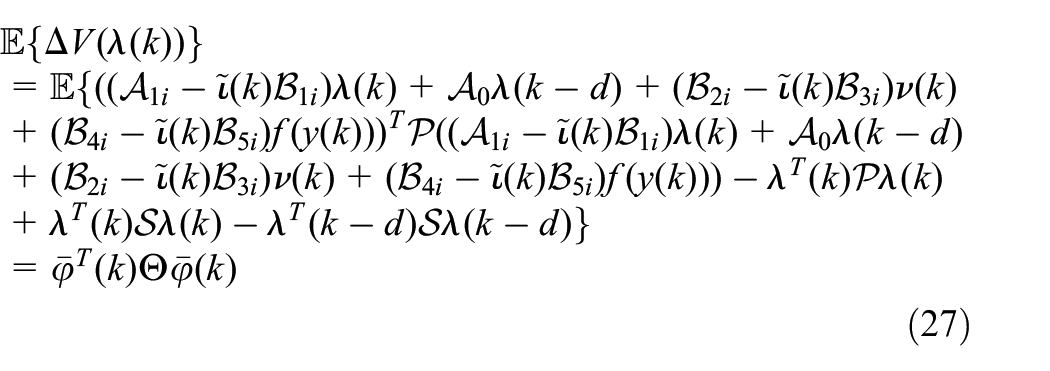
Now, consider the Lyapunov function candidate as
with
with
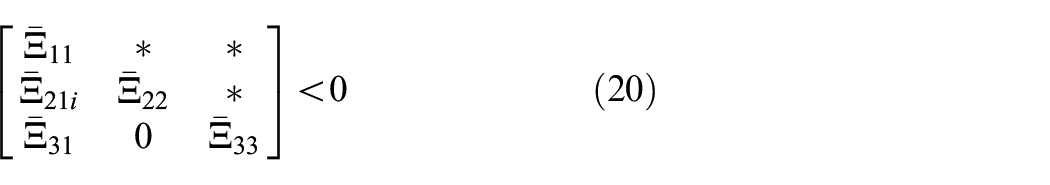
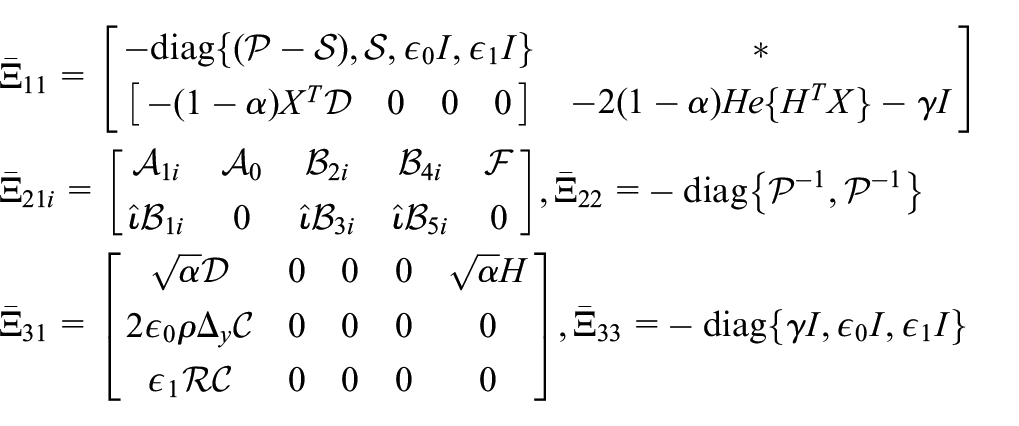
It can be noted that the following inequality is derived from equation (20) with
where
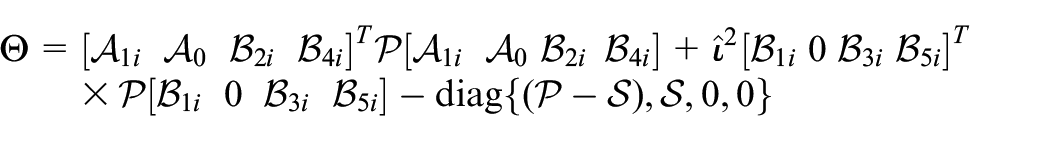
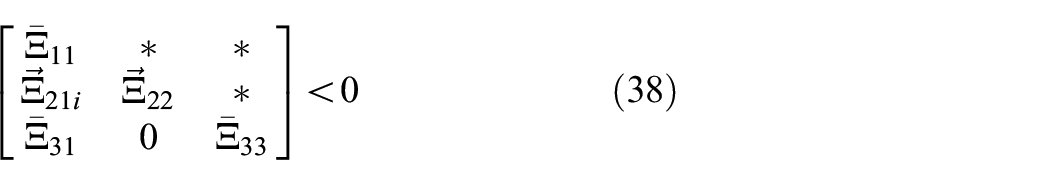
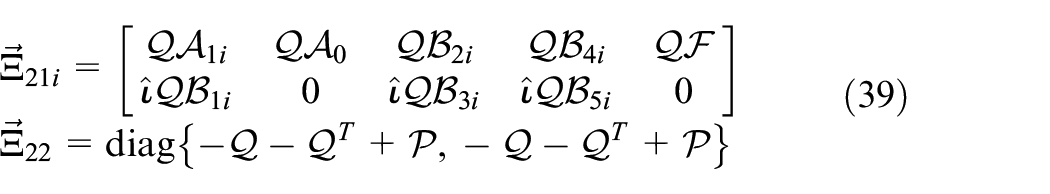
Accordingly, in the light of Schur complement, it is equivalent to the inequality
Furthermore, letting
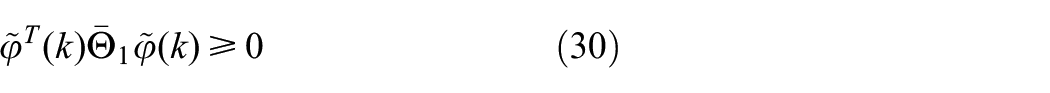
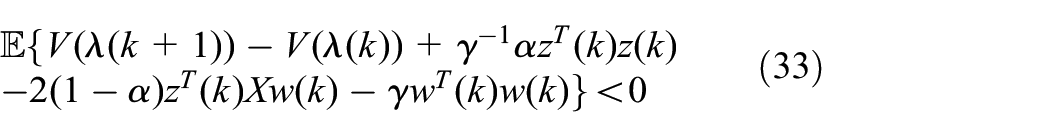
In the coming part, the mixed
where
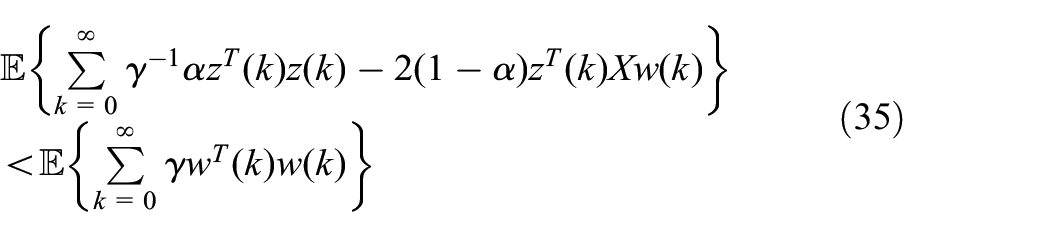
For another, the performance index
where
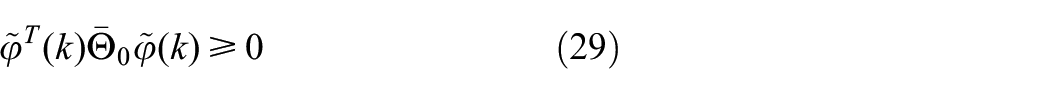
Similarly, the above-mentioned analysis process is reviewed again based on the S-procedure, if inequality (20) is established, the following condition can be obtained
which indicates that
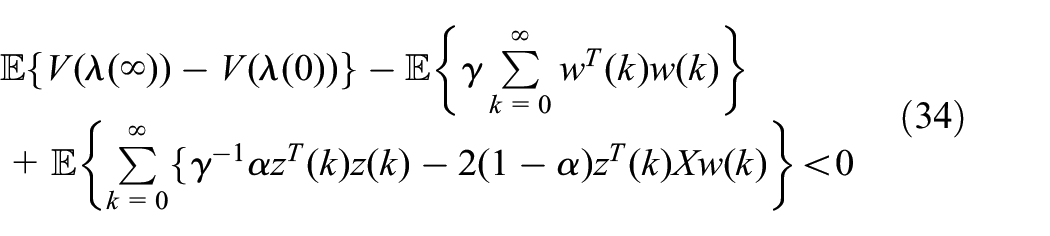
Then, by summing the left and right sides of equation (33) for
Because of the zero-initial condition
which means that resulting system (13) is stochastically stable and satisfies the prescribed mixed
Mixed
and passive control design
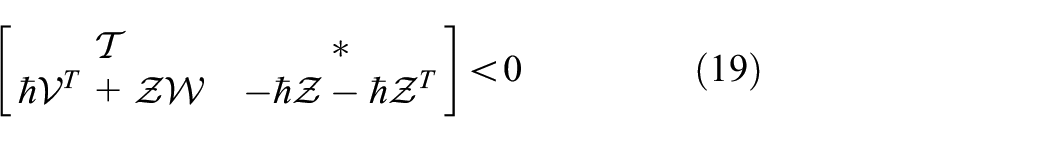
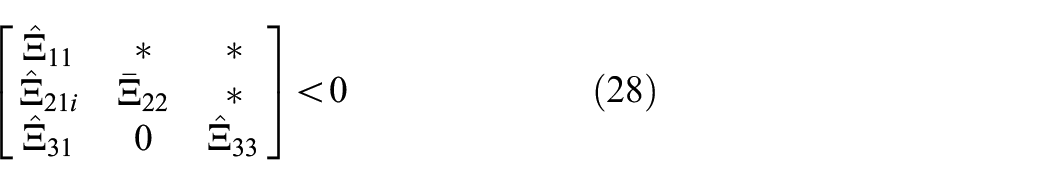
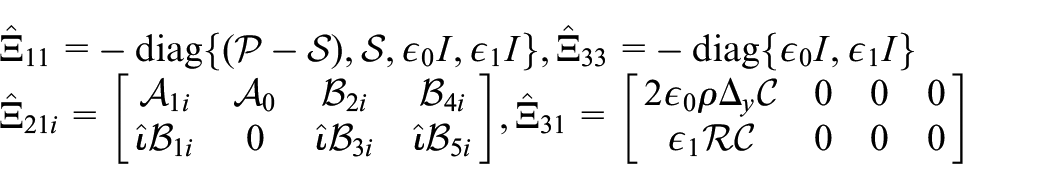
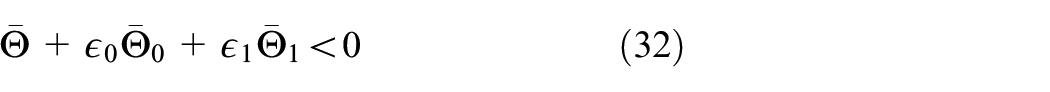
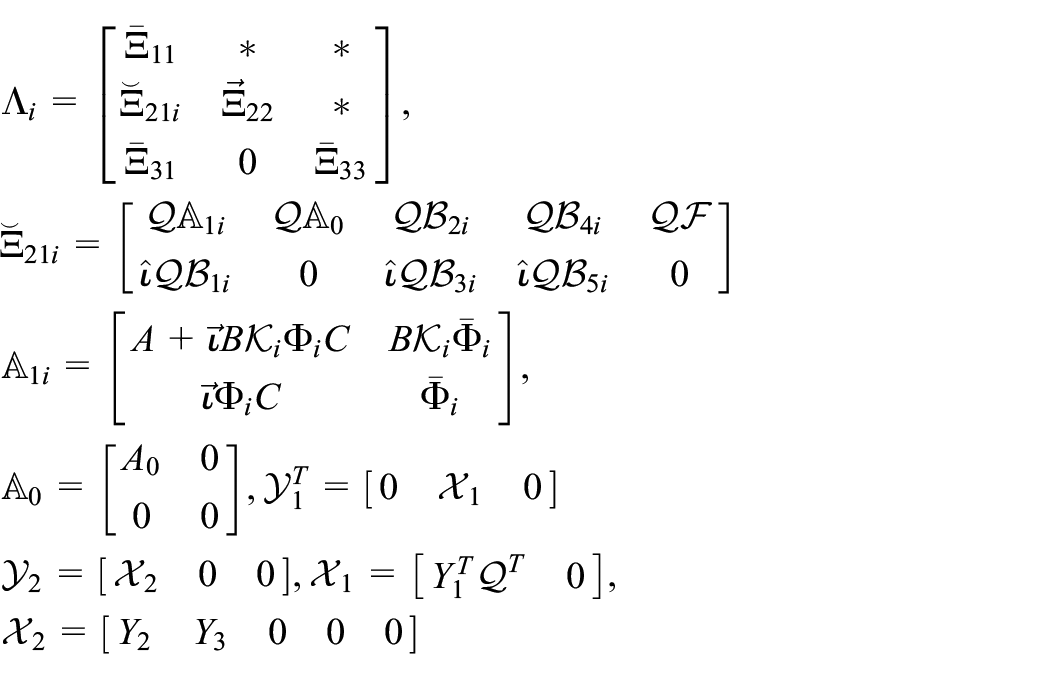
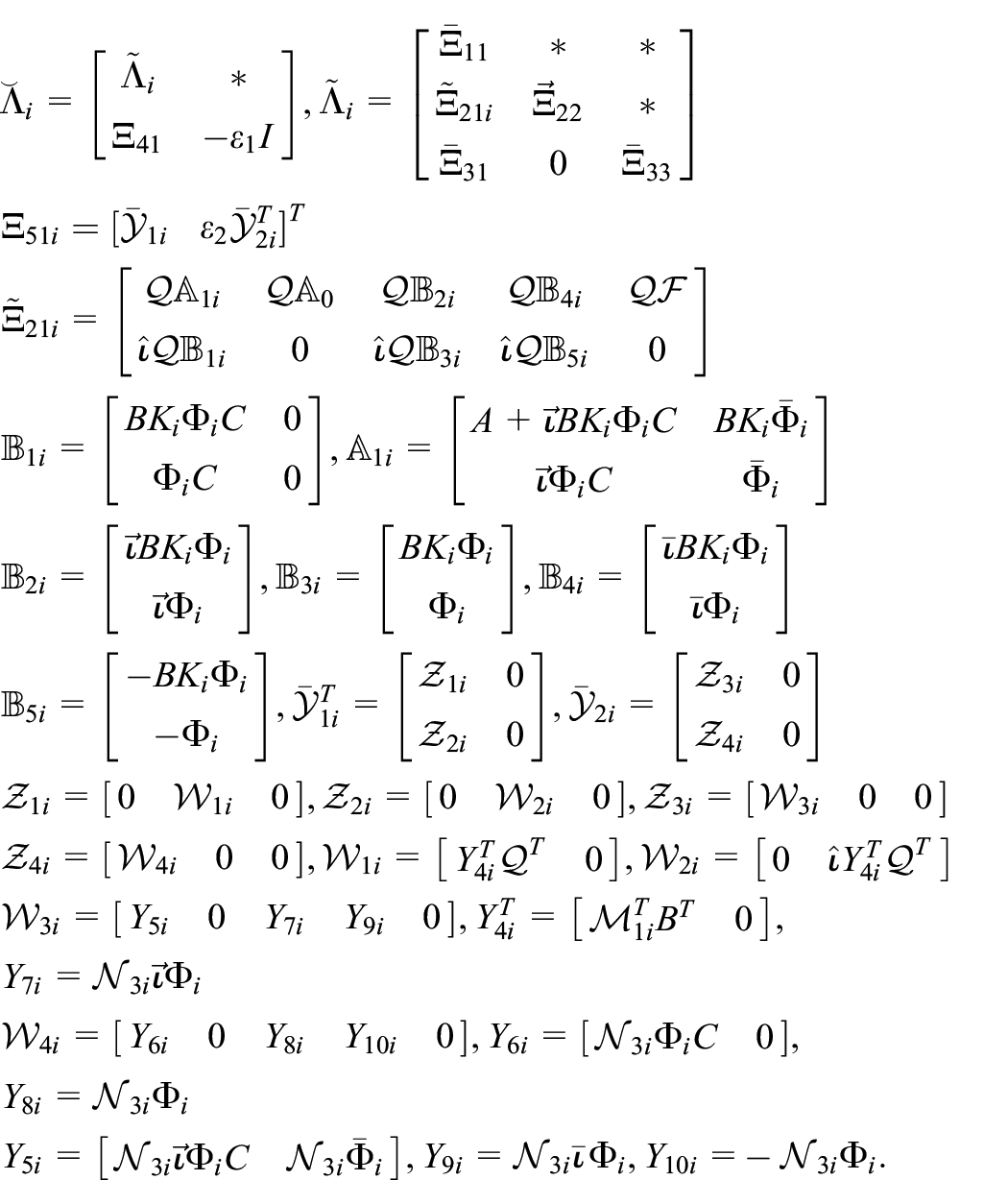
From what has been mentioned in the past, an important result of the mixed
where
Furthermore, the online adjustment strategy of quantizer parameter is given in equation (21) with
where
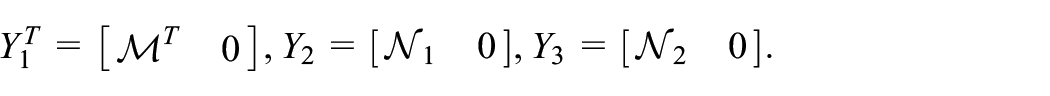
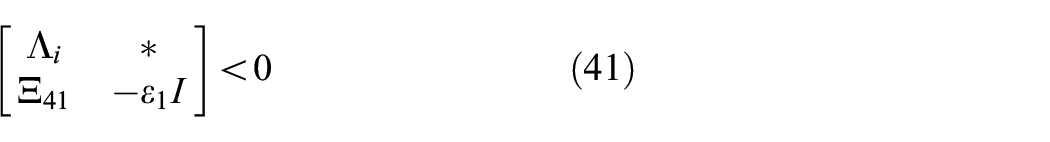
The removal of the uncertain terms containing
where
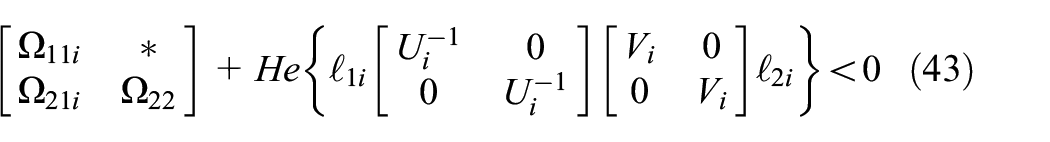
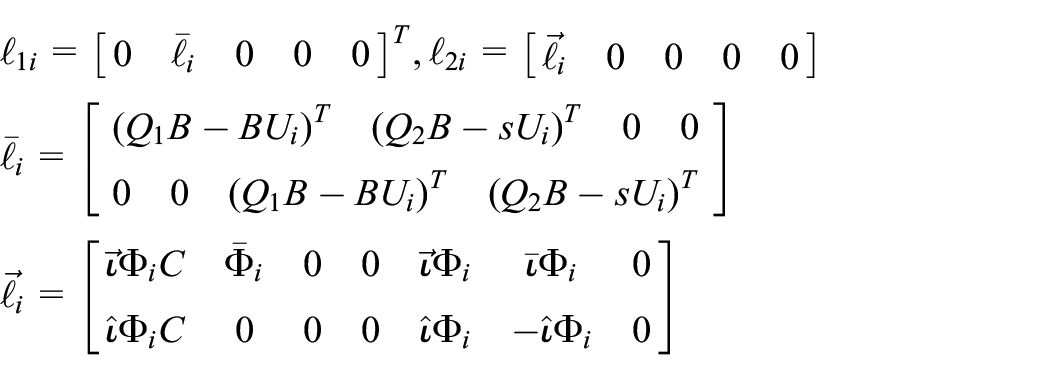
By invoking Lemma 1 and Schur complement to inequality (40), the following inequality is satisfied
where
where
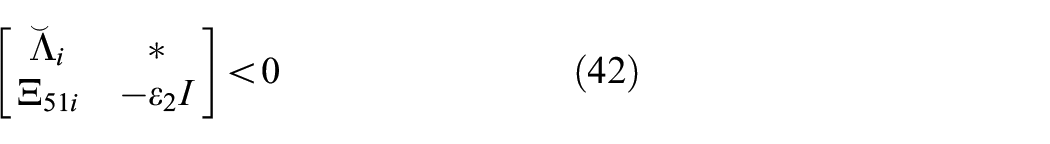
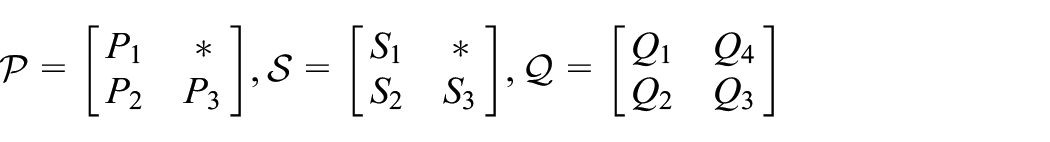
Accordingly, all uncertainties existing in the system and controller have been eliminated. In inequality (42), there are still nonlinear coupling terms, so it is not a strict condition of linear matrix inequality. Next, we will resort to a decoupling method based on Lemma 2 to deal with these coupling terms. Without losing generality, choosing
and defining
is satisfied, where
and s denotes the dimension adjustment matrix, which be defined as the following forms,
Simulation results
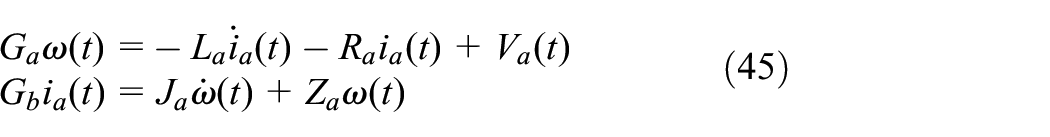
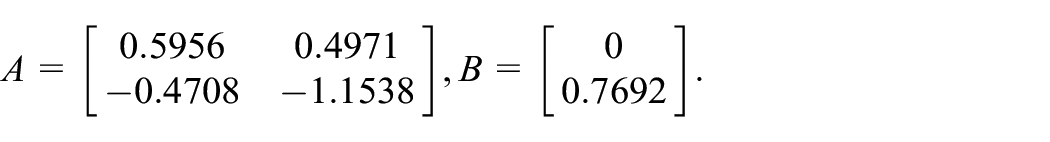
In this section, a DC motor device (Yin et al., 2014) driving an inertial load is considered as an application example to demonstrate the effectiveness and applicability of the proposed results. The terminal voltage
Then, the following state-space model for the DC motor is generally written as
where
Parameters of DC motor device.
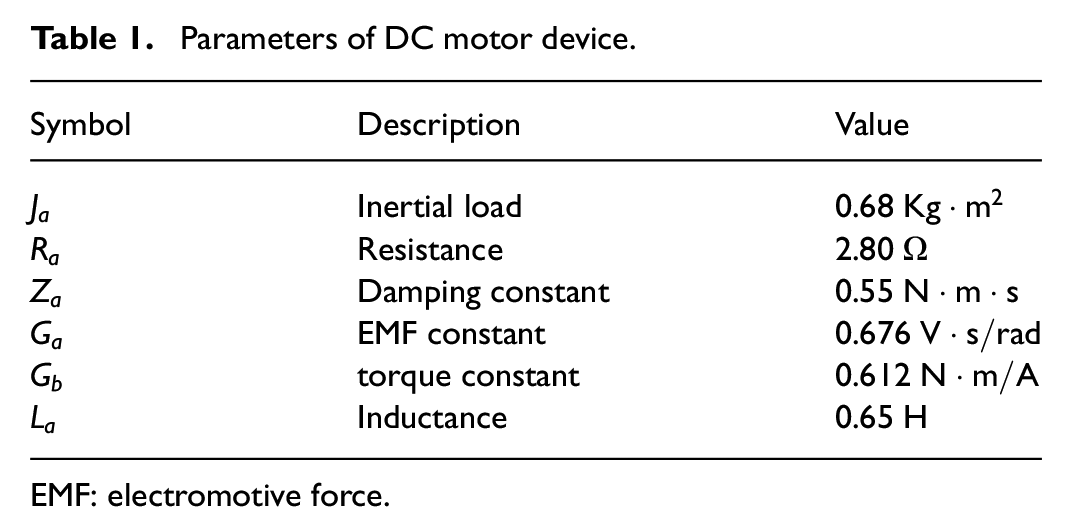
EMF: electromotive force.
The eigenvalue of A is 0.4496, −1.0078. Obviously, the system is unstable without a controller. For the model, the inevitable time delay and uncertainties caused by armature reaction are considered simultaneously, so the other parameters are given as follows
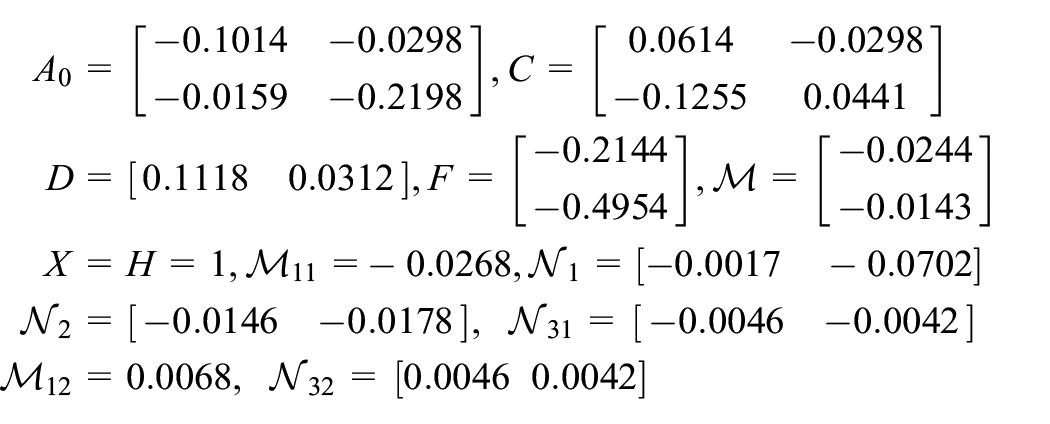
In this simulation, given some parameters
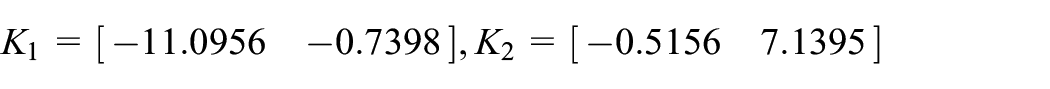
and the designed scalar
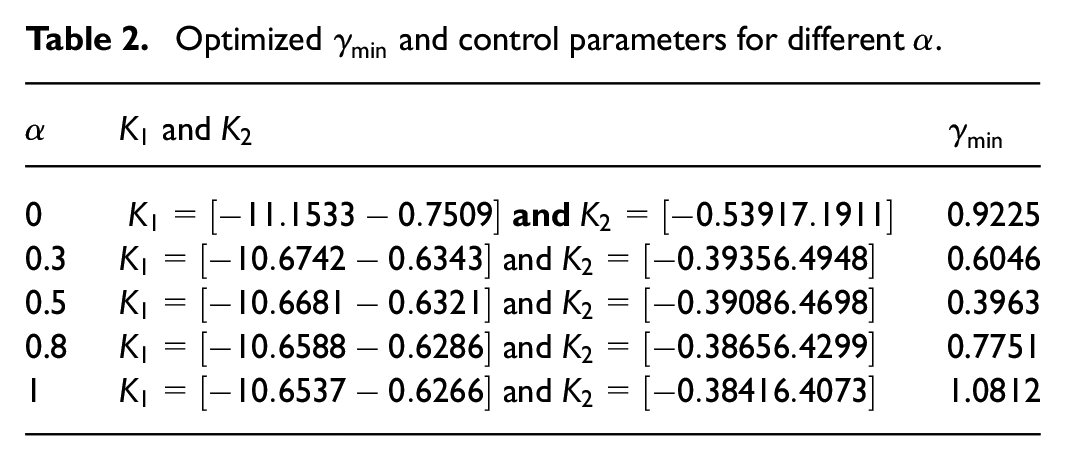
Optimized
Assume that the initial condition is
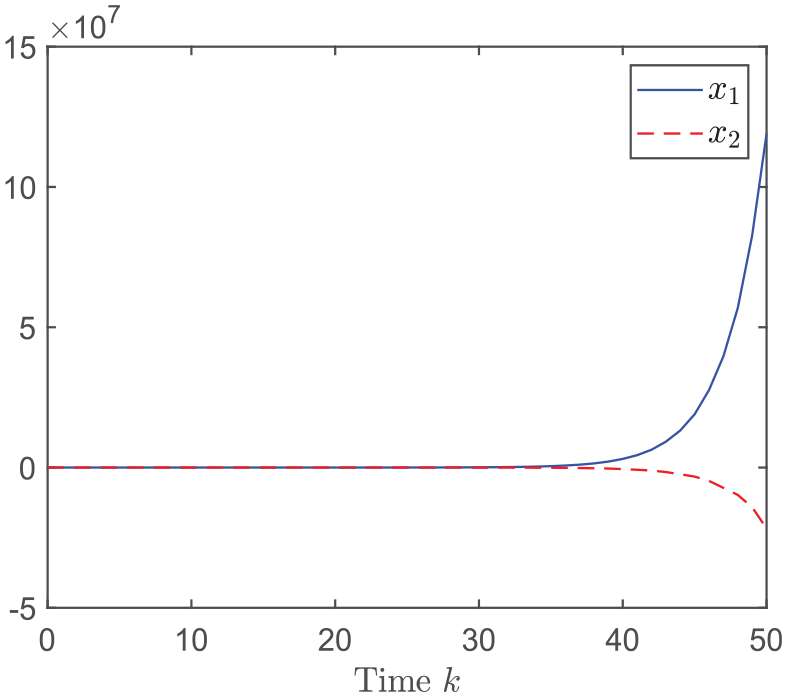
State responses of the open-loop system.
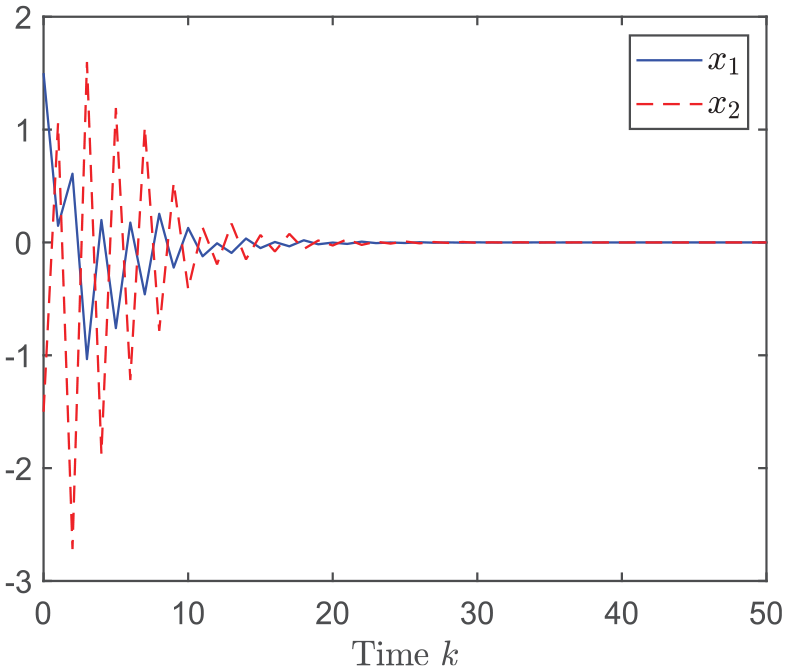
State responses of the closed-loop system.
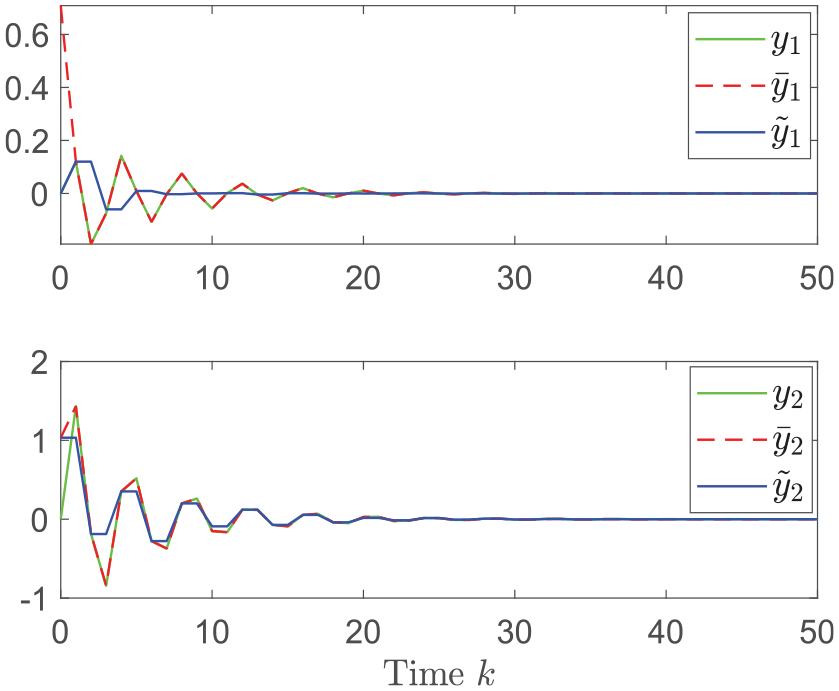
Response of
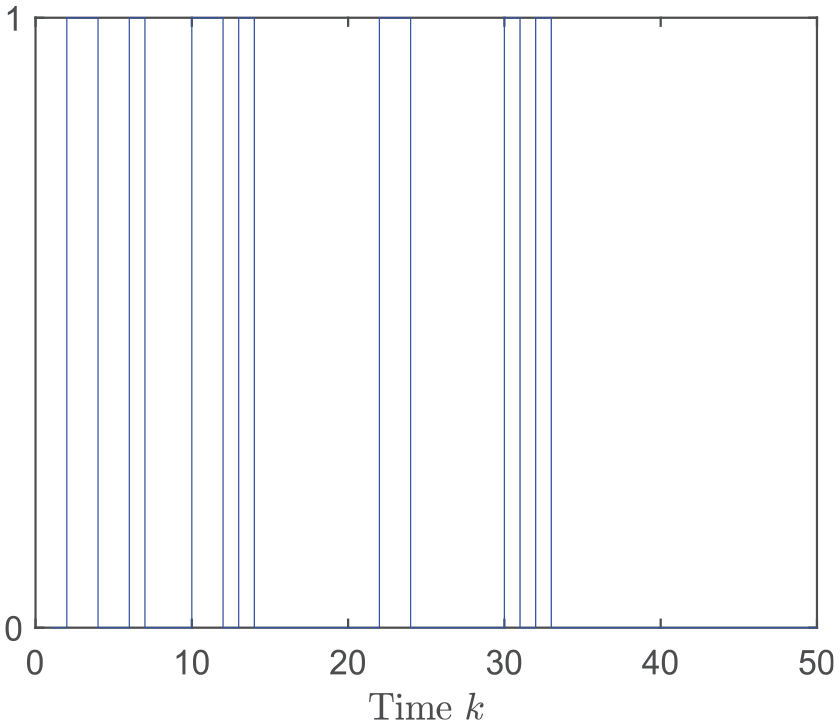
Occurrence instants of deception attacks.
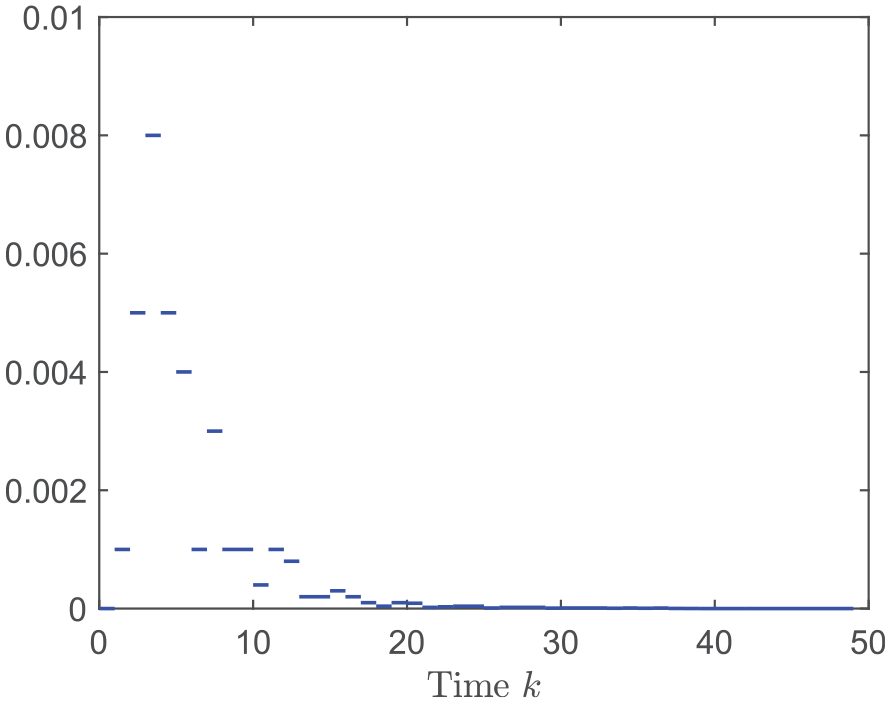
Dynamic quantizer’s parameter
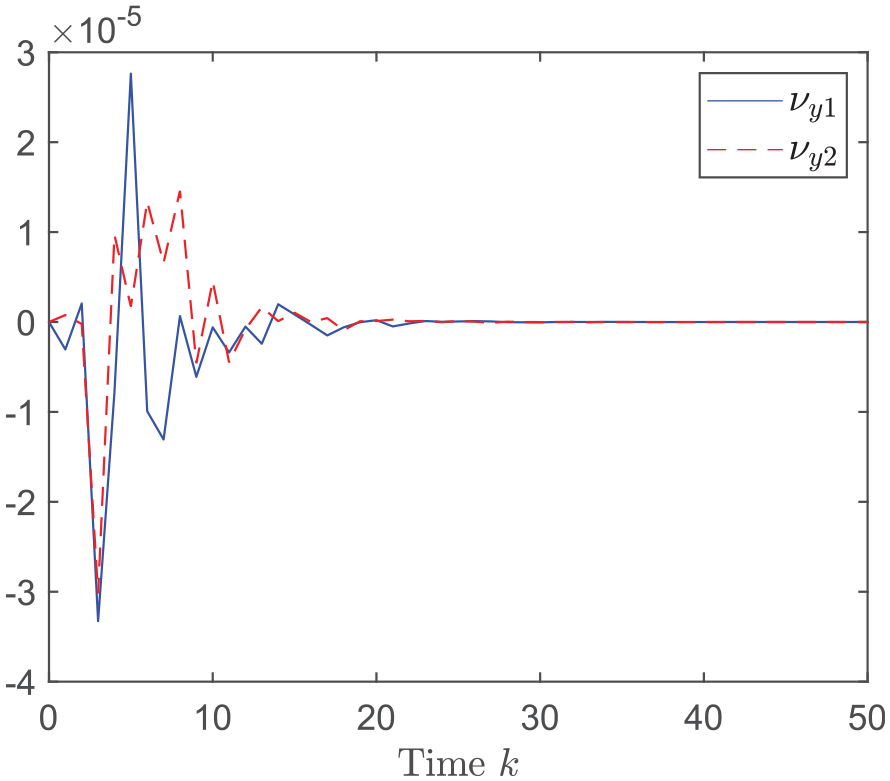
Quantization error
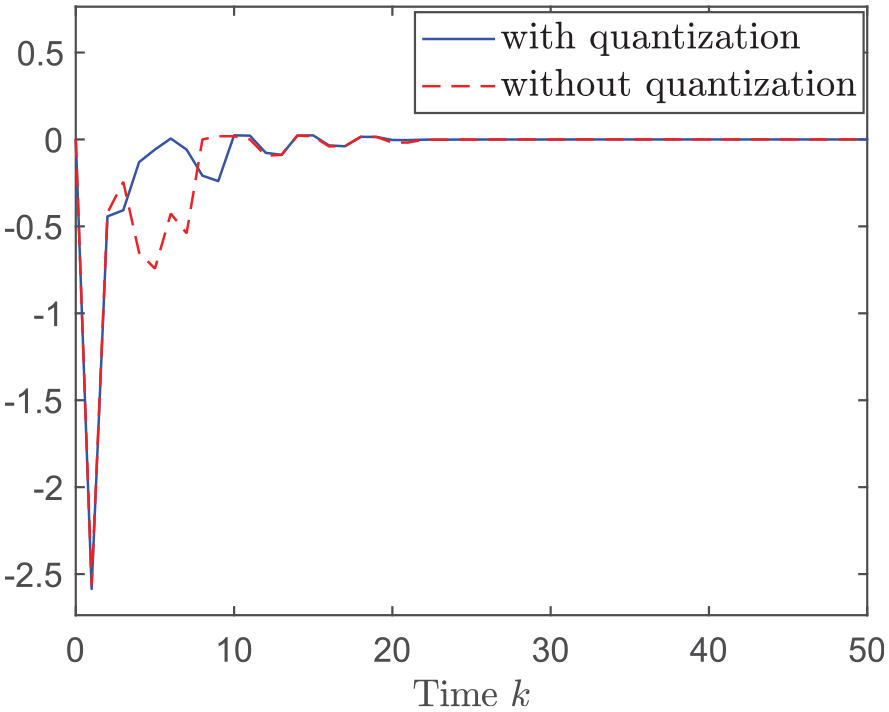
Control response with and without quantization.
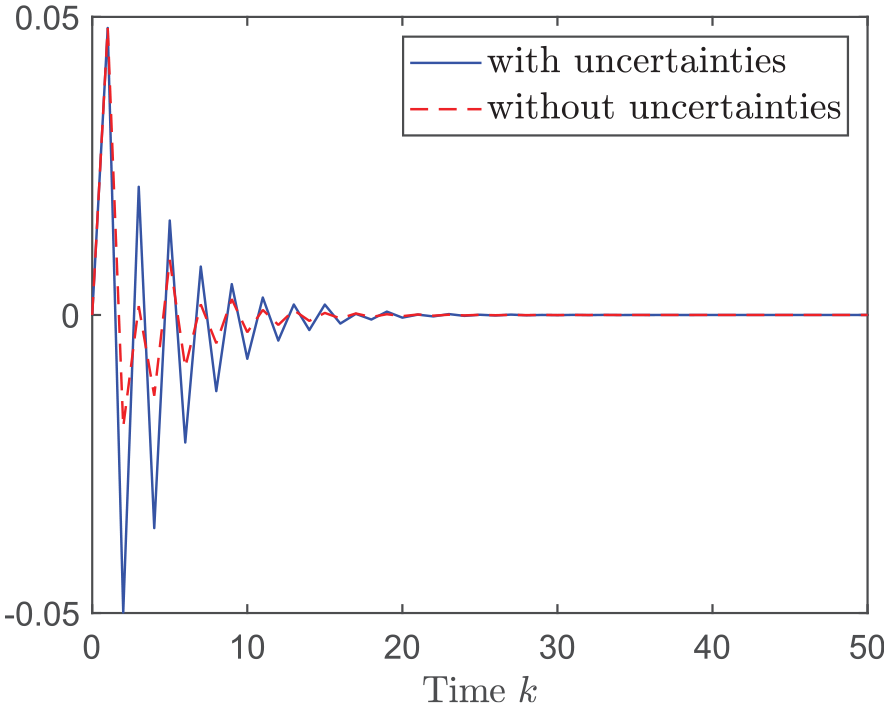
Controlled output response with and without uncertainties.
Comparative explanations: In contrast to the existing results on mixed
Conclusion
In this paper, the problem of mixed
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the National Natural Science Foundation of China (grant nos. 61773298 and 62173261).