Abstract
This work deals with the language-based opacity verification and enforcement problems in discrete event systems modeled with labeled Petri nets. Opacity is a security property that relates to privacy protection by hiding secret information of a system from an external observer called an “intruder”. A secret can be a subset of a system's language. In this case, opacity is referred to as language-based opacity. A system is said to be language-based opaque if an intruder, with a partial observation on the system's behavior, cannot deduce whether the sequences of events corresponding to the generated observations are included in the secret language or not. We propose a novel and efficient approach for language-based opacity verification and enforcement, using the concepts of basis markings and basis partition. First, a sufficient condition is formulated to check language-based opacity for labeled Petri nets by solving an integer-programming problem. A unique graph, called a modified basis reachability graph (MBRG), is then derived to verify different language-based opacity properties. The proposed method relaxes the acyclicity assumption of the unobservable transition subnet thanks to the basis partition notion. A new embedded insertion function technique is also provided to deal with opacity enforcement. This technique ensures that no new observed behavior is created. A verification algorithm is developed to check the enforceability of a system. Finally, once a system is proved to be enforceable, an algorithm is given to construct a new structure, called an insertion automaton, which synthesizes all possible insertion functions that ensure opacity.
Introduction
With more and more information exchanges in cyber systems, ensuring information flow properties, in particular opacity, has become a new preoccupation in discrete event systems (DESs). Opacity reflects the ability of a system to hide a given secret from an intruder during the system evolution. The strength of opacity lies in the fact that it can formalize the majority of information flow properties. Therefore, it can be used not only to formalize security and privacy, but also to unify three important properties of DESs, namely detectability, diagnosability, and observability, as special cases. The opacity notion is first introduced in 1 for transition systems and extended later in 2 and 3 using Petri nets and automata. In DESs, opacity can be classified mainly into two classes: state-based opacity (SBO), in which a secret is defined as a state sub-space, and language-based opacity (LBO), where a secret is defined as a subset of a system’s language.
This work focuses on language-based opacity verification and enforcement in DESs modeled with Petri nets. Here, the following setting is involved: (1) a system has a secret behavior, (2) an intruder has full knowledge of the system structure, and (3) the intruder has a partial observation of the system evolution. We have chosen to model the studied system with labeled Petri nets (LPNs) since they are extensively used to model discrete event systems to address many problems such as deadlocks, fault diagnosis, fault identification 4 , and opacity verification. As well, LPNs are chosen in order to present the observation structure of the studied system 5 , to benefit from the advantages of the compact representation of a traditional state space, and to exploit some computation results on reachability in PNs to verify opacity.
The work in 6 introduced language-based opacity for the first time in the context of automata. Two properties of language-based opacity are defined later in 7 : strong and weak opacity. A language is strongly (resp. weakly) opaque with respect to another language if all (resp. some (not all)) strings in the former are confused with some strings in the latter. Verification and enforcement of opacity properties are addressed using both automata and Petri nets. The opacity verification problem has been treated in various ways to deal with different categories of opacity8–10. If the opacity is violated, several approaches have been proposed to solve the opacity enforcement problem in diverse manners, such as supervisory control 11 , dynamic observer 12 , and enforcement mechanisms 13 .
In the context of automaton framework, the work in 7 proposed algorithms to verify both strong and weak LBO, in which the author assumed that the languages involved in a system should be all regular and the information mapping should be a state-based projection. This work requires the construction of nine types of graphs, while the opacity verification in our research demands only the construction of one graph without any requirement to exhaustively enumerate the whole reachability set. The two approaches are computationally expensive. However, the approach in this work is easier to implement. Later, weak opacity has been checked by a polynomial time complexity algorithm proposed in 14 . Furthermore, the verification approach in this work not only verifies the different properties of LBO but also identifies the non-opaque secret words that must be distinguished in order to smooth the path of the enforcement, which represents a gap in 7 and 14 .
Petri nets have been recognized as a powerful modeling formalism for DESs in a wide variety of applications15,16. Nevertheless, only works in
17
and
18
studied language-based opacity verification using Petri nets. The study in
17
verifies language-based opacity using a special structure called a verifier, under the assumption that an intruder is interested in the set of observable transitions only. This work constructs the basis reachability graph (BRG) of a given PN and apply the related approach proposed in
7
. The verifier graph has to be reconstructed each time to check all the elements of the secret language, which means that if the cardinality of a secret language is n, the verifier needs to be reconstructed n times, where the complexity to construct the verifier at a time is
The notion of modified basis reachability graph (MBRG) has been used for couple of years. However, an MBRG is specifically generated depending on the purpose of the research. For instance, the work in
19
constructed an MBRG based on fault transitions through a particular equation in order to compute a graph called basis reachability diagnoser (BRD) to test diagnosability. Meanwhile, in our work, the MBRG construction is based on the properties of the computed basis markings, that is, they are misleading or not misleading. In a similar way, the work in
5
studied current-state opacity in Petri nets using a modified basis reachability graph. As mentioned above, in this work, we relaxed the acyclicity assumption of the subnet derived from
For opacity enforcement, the use of enforcement mechanisms allows a system to fully execute its behavior. An insertion function is one of the most popular techniques for these enforcement mechanisms. Such a technique is first introduced in
20
and extended later in
21
and
13
in the context of automaton framework. This insertion function monitors a system by inserting additional events to the observed behavior of a system when necessary at a run-time. However, the proposed insertion function in this work is embedded into the system itself, rather than being an output monitoring interface. After that, the authors in
22
provide an embedded version of the insertion function proposed in
20
. Recently, the work in
23
focuses on opacity enforcement as well by proposing an extended insertion technique of the one proposed in
22
. This technique can enforce opacity in a practical manner, i.e., in an embedded way, by inserting symbols before and after an actual system output. The approach in
23
appears to be very close to our proposed enforcement approach. However, herein, we address opacity verification and enforcement while the work in
23
deals with opacity enforcement only. In this manuscript, the insertion function is more powerful for enforcing opacity than the documented ones in the literature as it considers additional enforcement cases that are not previously touched upon in the existing approaches. In the same manner as the proposed function in
23
and contrary to the one proposed in
22
, the embedded function in this paper inserts not only additional events before an observable event, but it can insert an additional event after the occurrence of an observable event, in which the additional event could be either an observable event or
In this work, we focus on language-based opacity verification and enforcement in DESs modeled with LPNs. First, based on the notion of explanation, a sufficient condition is provided to decide the opacity of a system by solving an integer programming problem. Unobservable events are then exploited to hide secret information. A unique graph called a modified basis reachability graph (MBRG) is proposed to verify different properties of LBO (strongly opaque, weakly opaque, and non-opaque). The proposed verification approach is based on the concept of basis marking. Thus, there does not exist any requirement to exhaustively enumerate the whole reachability set, which is an important advancement in terms of computational efficiency. In addition to that, the proposed MBRG is exploited to address LBO enforcement, where a new enforcement technique using an embedded insertion function is provided. This technique modifies the observations that reveal secret information with respect to the original language of a system. The provided embedded insertion function is more powerful for enforcing opacity than the earlier proposed ones as it considers additional enforcement cases that are not previously considered in the formerly documented approaches. A verification algorithm for enforceablity is introduced to check whether a system is enforceable or not. Finally, once a system is proved to be enforceable, an algorithm is reported to construct an insertion automaton (IA) that synthesizes all the possible insertion functions.
The remainder of the paper is organized as follows. Some necessary concepts are recalled in Section PRELIMINARIES. The proposed MBRG is shown in Section LANGUAGE-BASED OPACITY VERIFICATION APPROACH. In Section LANGUAGE-BASED OPACITY ENFORCEMENT APPROACH, based on the proposed graph, a new insertion function technique is proposed to address the enforcement of a verified non-opaque system. Conclusions are reached in Section CONCLUSION, where the future work is outlined.
Preliminaries
Petri Net
A Petri net is a four-tuple
A marking is a mapping
A Petri net system
A marking M is said to be reachable in
Labeled Petri Net
Taking into account the partially observed behavior of a system, the set E is partitioned into two disjoint parts: namely
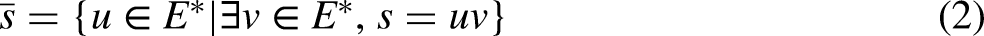
Given an event
The language generated by an LPN system
Basis reachability graph
An observer for a net system, called a basis reachability graph (BRG), is first introduced in 24 . A generalization of BRG is later introduced in 25 to provide a more basic structure, containing basis markings only, regardless of the system's observability, to deal with more general reachability problems.
Given a Petri net
Given a Petri net
In other words, the firing of any implicit transition sequence
Given a Petri net
Given a Petri net
If
Note that
Given a Petri net
the state set
the event set
the transition relation
the initial marking
Language-based opacity
The definition of LBO of DESs is initially formulated based on automata 6 and then consistently extended to the Petri net framework 17 , where a secret is represented as a set of transition sequences. However, in this work, the secret is defined as a set of sequences of events (labels) consistent with what is usually suggested in the context of automaton.
Given an LPN
Given an LPN
Strongly opaque if
Weakly opaque if
Non-opaque if
In other words, by Definition 7,
Language-based opacity verification approach
In this section, a novel approach for LBO verification using the notions of basis partition and basis markings is presented. The idea consists in defining a new modified BRG (MBRG) to effectively check language opacity without enumerating the whole reachability set. The proposed approach deals not only with opacity verification but also opacity enforcement. To guarantee that the behavior of a system can be described by the proposed graph, the set of observable transitions
In this paper, the transition set of a Petri net is partitioned into explicit and implicit transitions instead of observable and unobservable events. This partition is proposed to avoid being restricted by a system’s structure. Thus, the chosen partition allows the proposed approach to be widely applied to any Petri net structure, regardless of its observation. The chosen basis partition helps then to apply easily our approach to a wide range of Petri nets while conserving the system's observation since the set of observable transitions
The use of the generalized BRG makes A1 negligible compared with the assumption used in 17 and 18 , where the unobservable transition subnet requires to be acyclic. The acyclicity assumption in 17 and 18 is related to the structure of the system, while the acyclicity assumption made in this paper is not based on the structure of a system but on the chosen basis partition. Therefore, our proposed approach can be applied to a wide range of net systems, where the unobservable subnet is cyclic.
Verification of language-based opacity
Let
Given an LPN
By Definition 6, an opaque system means that for all
Given an LPN
Suppose that for all
We consider the LPN in Figure 1, where
The condition in Proposition 1 is sufficient to check the opacity of a system. However, if not satisfied, we cannot conclude that a system is non-opaque. Hence, Proposition 2 presents another sufficient condition to decide the opacity of a system when Propositions 1 is not satisfied.

A Labeled Petri net.
Given an LPN
Let us suppose that for all
In order to guarantee the opacity of a net system
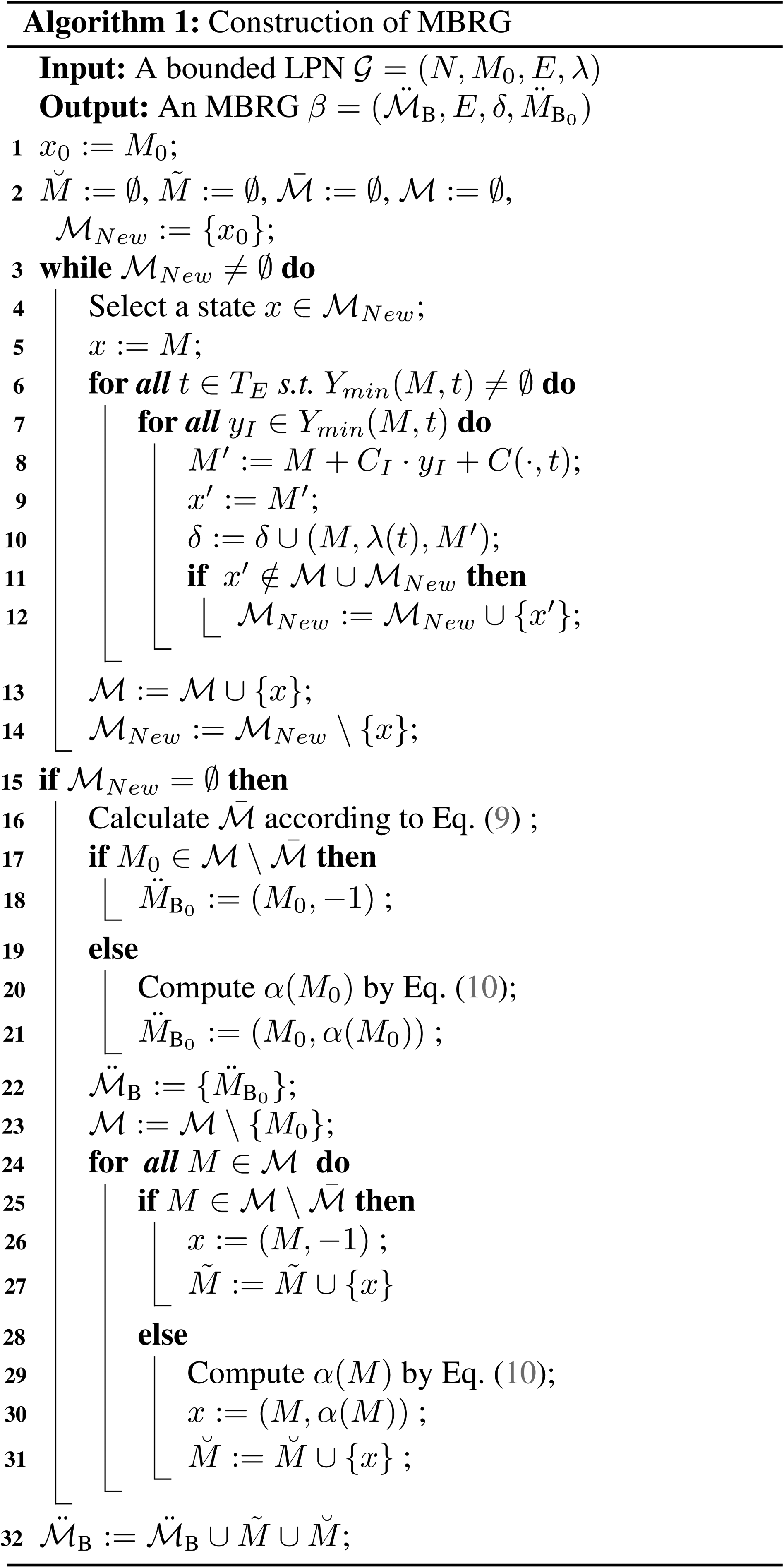
Modified basis reachability graph (MBRG)
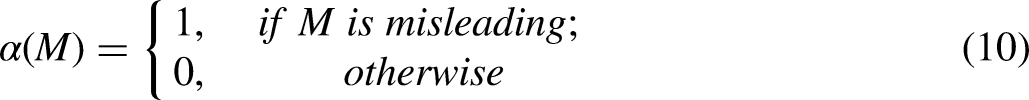
To verify different properties of LBO, a modified BRG (MBRG) is proposed. We assume that an LPN is bounded to guarantee that its MBRG is finite. Given an LPN
Let
Based on Definition 8, given an LPN
Given an LPN
the state set
the set E is the set of events.
the transition relation
In plain words, the set of modified basis markings of
The language generated by an MBRG

The procedure of constructing MBRG is summarized in Algorithm 1. First,
The construction of an MBRG avoids the exhaustive enumeration to the whole reachability set. The computation of
Given an LPN
(i) Strongly opaque if and only if there does not exist
(ii) Non-opaque if and only if there does not exist
(iii) Weakly opaque if and only if there exists
Let
Second, let us now suppose that for all
In summary, we conclude that
Consider the LPN system
Language-based opacity enforcement approach
In this section, we propose a new enforcement strategy for LBO that takes the advantages of the proposed MBRG. The proposed strategy is inspired by the insertion function technique proposed in. 20 and 22 The insertion function inserts additional dummy events to the event sequences that reveal a secret in order to mislead the intruder and establish the opacity of a system.

An LPN

The MBRG of the LPN in Figure 2.
In this paper, the proposed strategy is presented in the context of PNs unlike the strategies in
20
and
22
that are established in the context of automaton framework. As the same as the one proposed in,
22
the insertion function here is embedded into the structure of a system, while the one proposed in
20
is a run-time monitoring interface at the output of a system. Here, similar to the insertion function proposed in,
23
the embedded function inserts not only additional events before an observable event, but also inserts an additional event after an observable event, in which the additional event could be either an observable event or
Consider the net system
Insertion function
Given a non-opaque or a weakly opaque system, we assume that an intruder is unable to distinguish the inserted events from the genuine ones. The inserted events are denoted by a virtual label
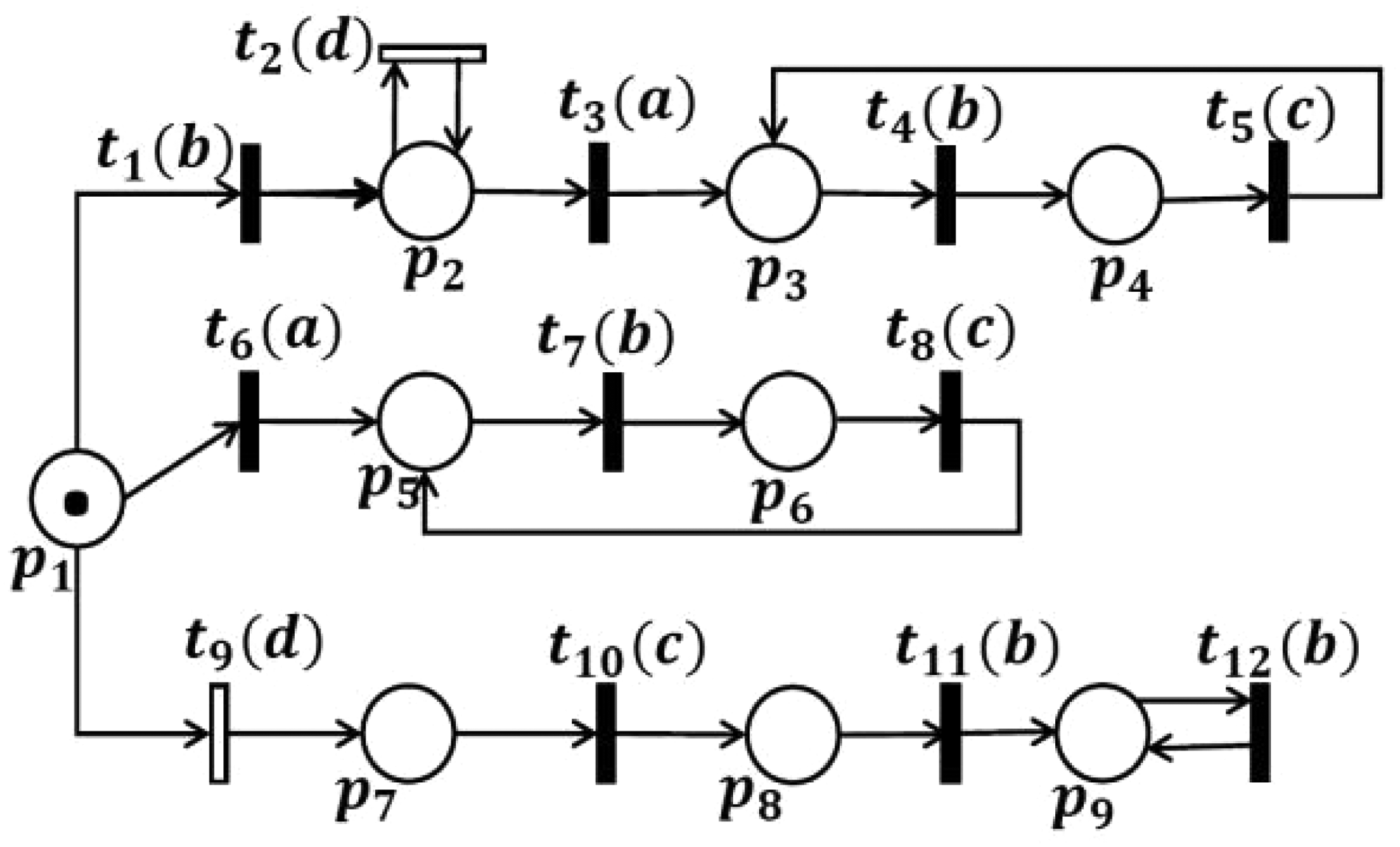
An LPN example.

MBRG of LPN in example 3.
For all

The insertion function here can insert additional virtual events
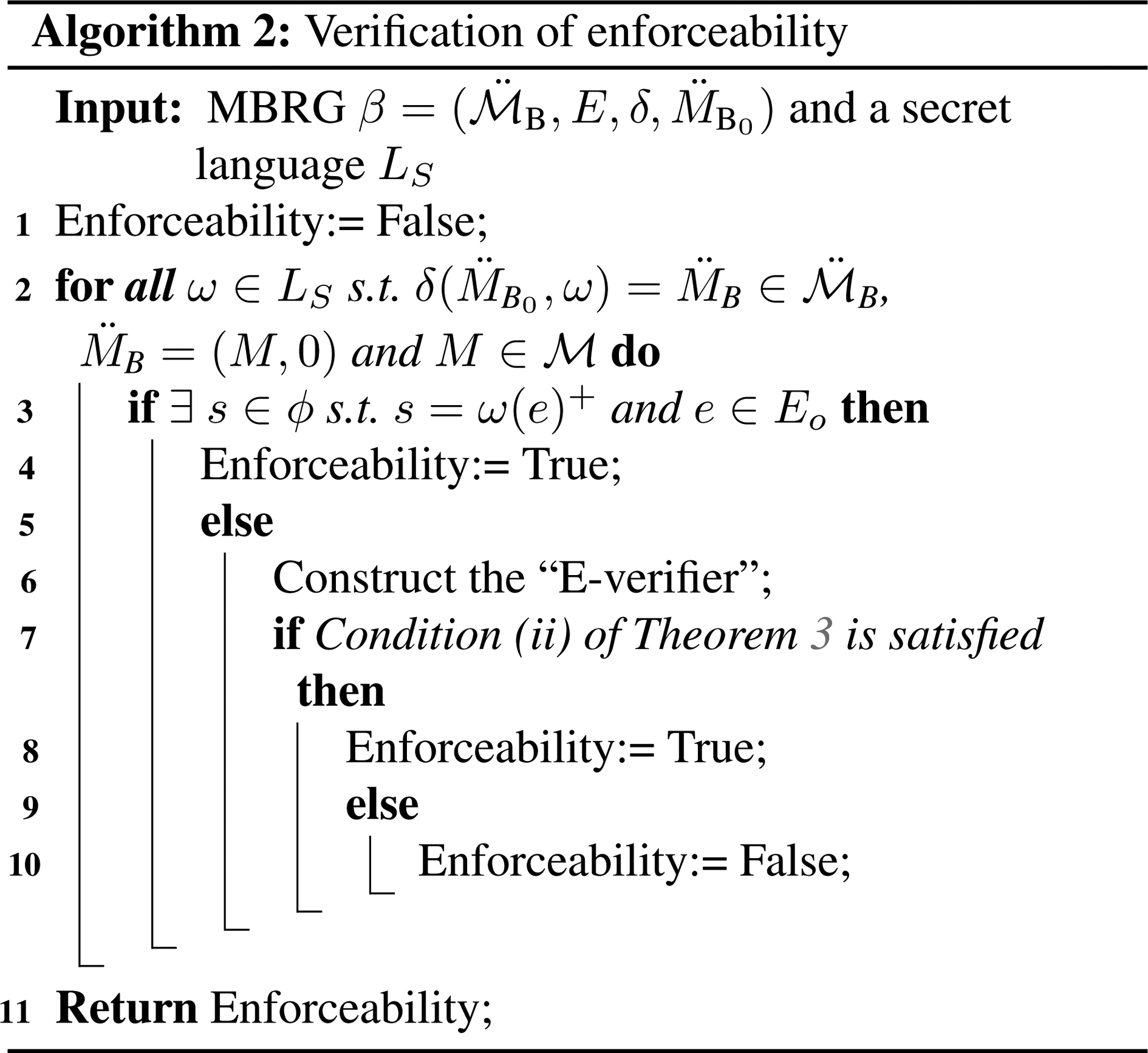
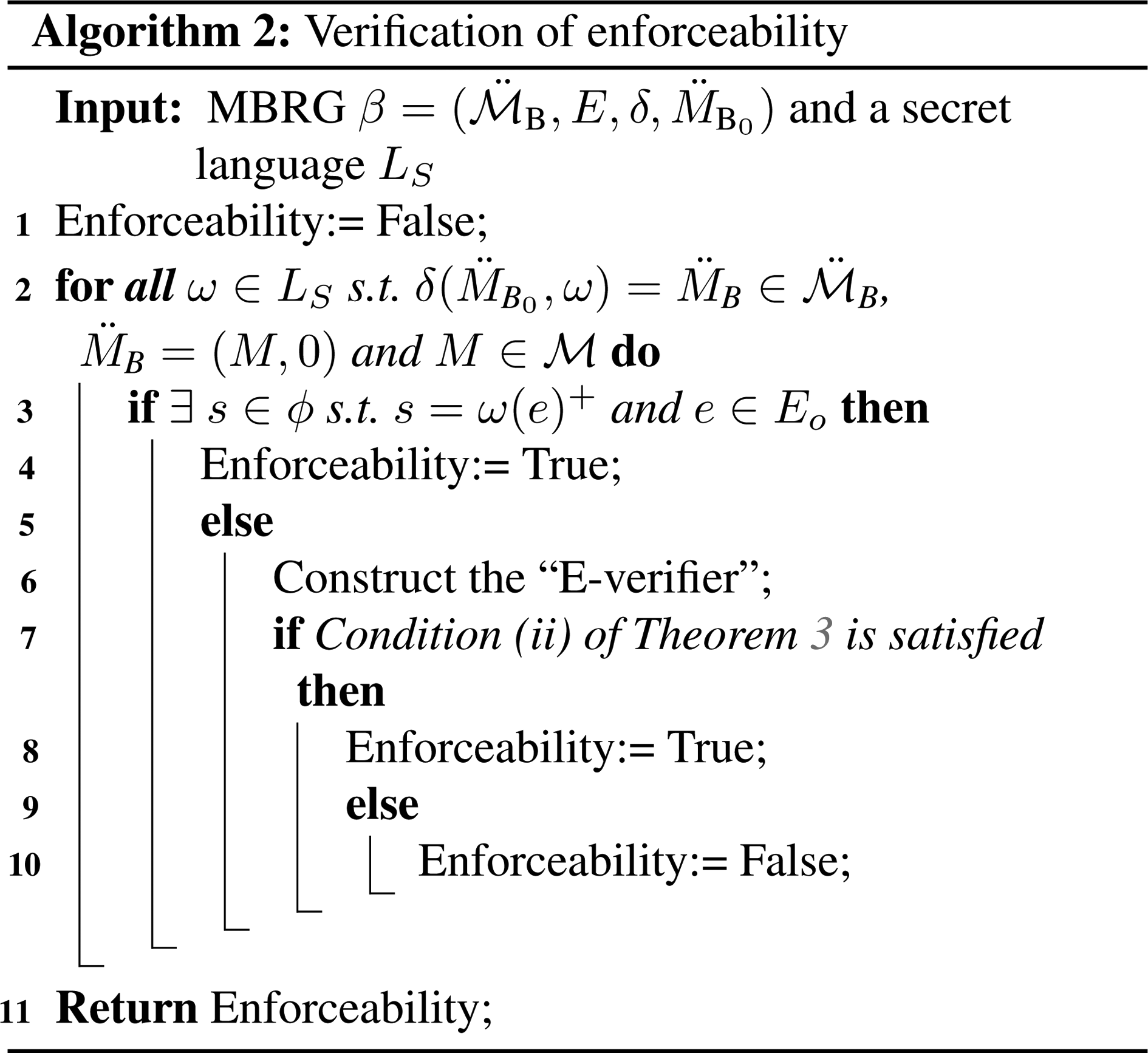
Verification of enforceability
Compared with other existing enforcement mechanisms, an insertion function allows all the behavior of a system and does not create a new observation that does not exist in the original behavior of a system. To ensure this property, the following definitions are proposed.
Let
In other words, an insertion sequence of a given secret word
Let
Given an MBRG
In this paper, we refer to the enforceability verification of a system as the i-enforceability property, which is defined in.
20
Checking enforceability may require the construction of a structure called “E-verifier”. The E-verifier construction starts by building the desired estimator
Given an I-verifier

Consider again the net system

MBRG of LPN in example 4.

(A) The desired estimator
To construct the applicable estimator, the set
The feasible estimator
In the same way, the required estimator is extracted from the desired estimator

The synchronization result
Finally, V is the resulting automaton after pruning the blocking and excess states (represented with dashed red lines in Figure 8) from

(a) The E-verifier V and (b) the rest estimator.
Given a non-opaque system
There exists a string
There exists a state
Suppose that
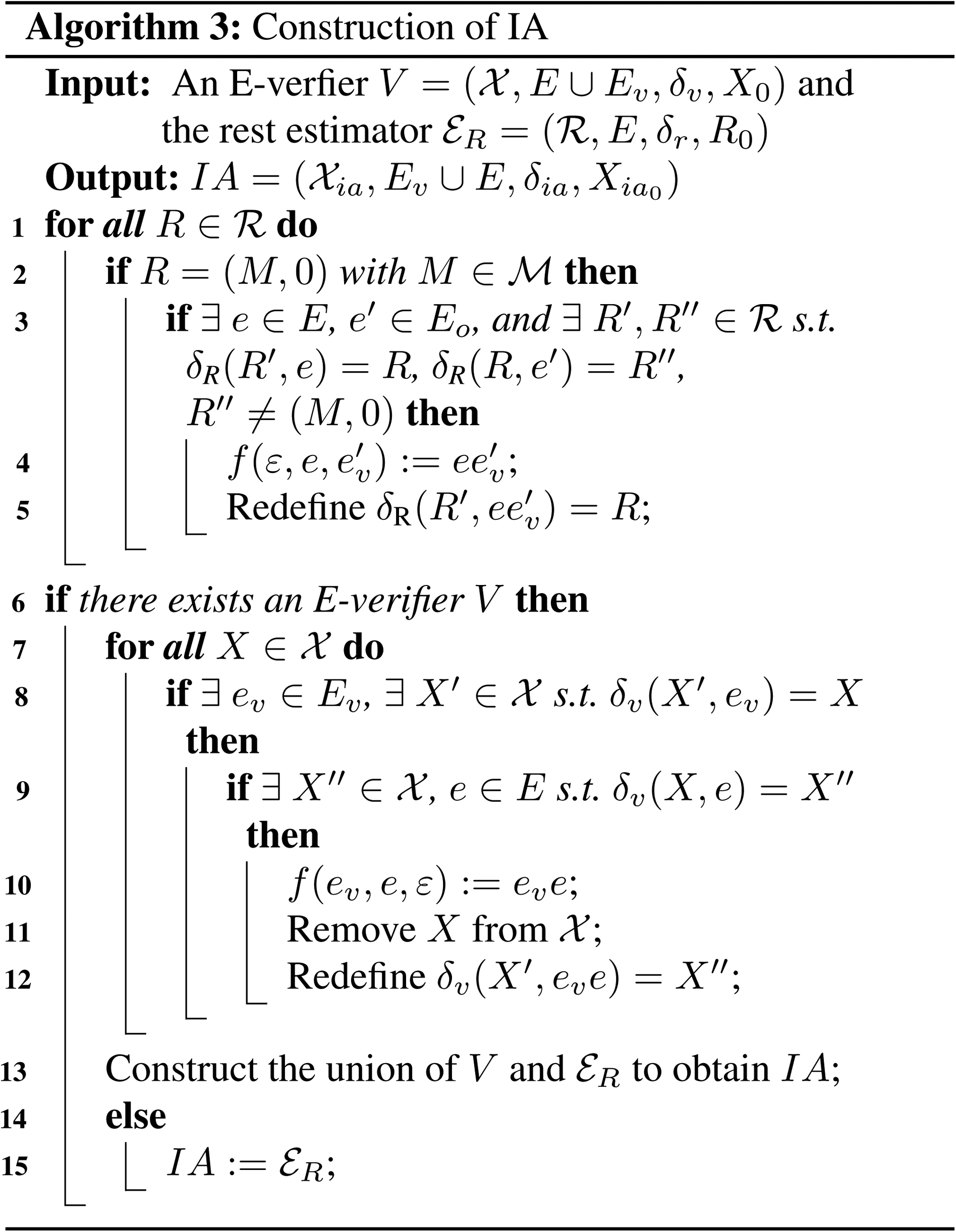
LBO enforcement
Once a given system
Given an MBRG
The possible insertion functions are encoded as an insertion automaton (IA). The IA construction is summarized in Algorithm 4. The construction of IA requires the construction of the rest estimator and the E-verifier. Therefore, the computational complexity of IA depends of the calculation of the worst-case space complexity of both rest estimator and E-verifier. Overall, the complexity analysis of IA building is
Continue with Example 4. The system

Conclusion
In this paper, a novel approach that does not require an exhaustive enumeration of the whole state space is proposed to verify different LBO types and enforce non-opaque secret words in the context of LPN under a generalization partition of transitions. Indeed, a unique graph called MBRG is designed to deal with the opacity verification issue by considering the unobservable transitions for hiding secret strings. The proposed MBRG is then investigated to deal with the opacity enforcement issue. A verification algorithm for checking the enforceability is given. An embedded insertion technique that is more general and powerful than the previously proposed techniques is provided to enforce a verified non-opaque system by adding fictitious occurrences of explicit transitions to change the system's output that is visible to an intruder. Finally, an algorithm is proposed to construct an insertion automaton (IA) that synthesizes different possible insertion functions.

The IA of example 7.
For future work, we are interested in studying the verification and enforcement of opacity under external attacks and extending the enforcement strategy to an edit mechanism (add/erase events).