Abstract
Offensive cyber operations are an increasingly important tool of authoritarian statecraft, used in the pursuit of foreign policy objectives and functioning as an expression of state power. Our article informs Canadian cybersecurity policy by pulling lessons from Russia's use of cyber aggression against Ukraine between 2014 and 2022. Our analysis explores the nexus between Russian cyber operations and foreign and domestic policy, the relationship between private and public cybersecurity organizations, and the purported intent and effectiveness of Russian cyber operations.
Keywords
Understanding offensive cyber operations
Offensive cyber operations are defined as the “employment of cyber capabilities to achieve objectives in or through cyberspace,” and relate to cyberattack, understood as deliberate actions meant to “alter, disrupt, deny, deceive, degrade, or destroy computer systems and services.” 1 Offensive cyber operations can have an operational and strategic function, performing as both an essential tool and an additional instrument of state power. Moreover, cyber offense can be used to facilitate or complement the effects of conventional operations, crossing the digital-physical divide. The goal, in this case, is to achieve strategic results by maximizing the effects of a kinetic attack by combining it with a cyber operation. Borrowing from the logic of traditional deterrence theory, Max Smeets distinguishes offensive cyber operations between counter-value and counter-force capabilities: the former targets a state's critical national civilian infrastructure, while the latter targets a state's critical operational and military infrastructure. 2
Several other characteristics follow. Especially capable states, for instance, may rely on cyber offense in a persistent and ongoing fashion rather than as one-off events. At least part of the reason for this offensive disposition is that definitively attributing cyber operations to states or their proxies remains a perennial dilemma, providing their use with certain advantages. There is, however, an apparent time delay between the period in which a state builds a novel cyber capability and later employs it. The reason here is that some cyber offensive capabilities are single use: once they are fired or revealed, adversaries may be able to patch the chink in the digital armour that facilitated the weapon's success. In comparison to kinetic weapons, then, the upfront R&D costs and benefits are potentially extravagant and fleeting. 3 But gauging the effectiveness of offensive cyber operations remains contentious. Some practitioners and scholars suggest that they have limited lasting consequences; others assume that they help shape desired outcomes when measured against narrow, grey-zone objectives. Others argue, however, that even cyber operations that are only temporarily disruptive but have noticeable public effects can result in crucial psychological impacts on a target population. And still others point to competing endlines: some regimes rely on offensive cyber operations for both foreign and domestic effects (e.g., greater control over citizens’ digital activities), complicating measurements of success or failure. 4
At times, cyber operations can be less burdensome to a state's reputation, especially when conducted clandestinely, and may reduce the risk of military confrontation and escalation vis-à-vis other kinetic operations as a result. There also appears to be a correlation between the speed, intensity, and control of a cyber operation, a phenomenon Lennart Maschmeyer dubbed the Subversive Trilemma. Only two of the three factors can be maximized at any one time (e.g., an operation that is quick to employ and powerful when used will be difficult to contain), forcing a state to contemplate and evaluate competing trade-offs. 5
What follows next is a summary account of nearly a decade of Russian cyber aggression against Ukraine. For the purposes of our argument, Russia functions as a typical example of authoritarian use of cyber offense shaded by specific caveats relating to its geopolitical position, military capability, and political clout, and—in relation to Ukraine in particular—historical conflicts. 6
Russian cyber offensive in Ukraine
The Russia-Ukraine War began with Russia's invasion and annexation of Crimea in 2014, followed by the Russian-backed uprising in the Donetsk and Luhansk regions of Ukraine, and then by Russia's full-scale invasion in February 2022. This escalating process of physical aggression has a cyber parallel: Russian cyber operations targeting Ukraine steadily increased leading up to and after the 2022 invasion. According to data provided by the Council on Foreign Relations Cyber Operations data set, Russia is a leading sponsor of offensive cyber operations. Broken down by type, Russian operations are often more destructive relative to those used by other authoritarian countries. Though cyber espionage constitutes the majority of Russia's known cyber operations—something it shares with all other authoritarian states—its destructive offensive cyber operations, which include attacks that destroy data as well as sabotage, defacement, and denial of service attacks, stood at 20 percent of the total between 2005 and 2021, far higher than other authoritarian states. Importantly, this percentage rose precipitously to 42 percent following Russia's 2022 invasion of Ukraine, suggesting that Russian cyber operations grew more destructive as its foreign policy did, too. 7 (See Figure 1 for details.)
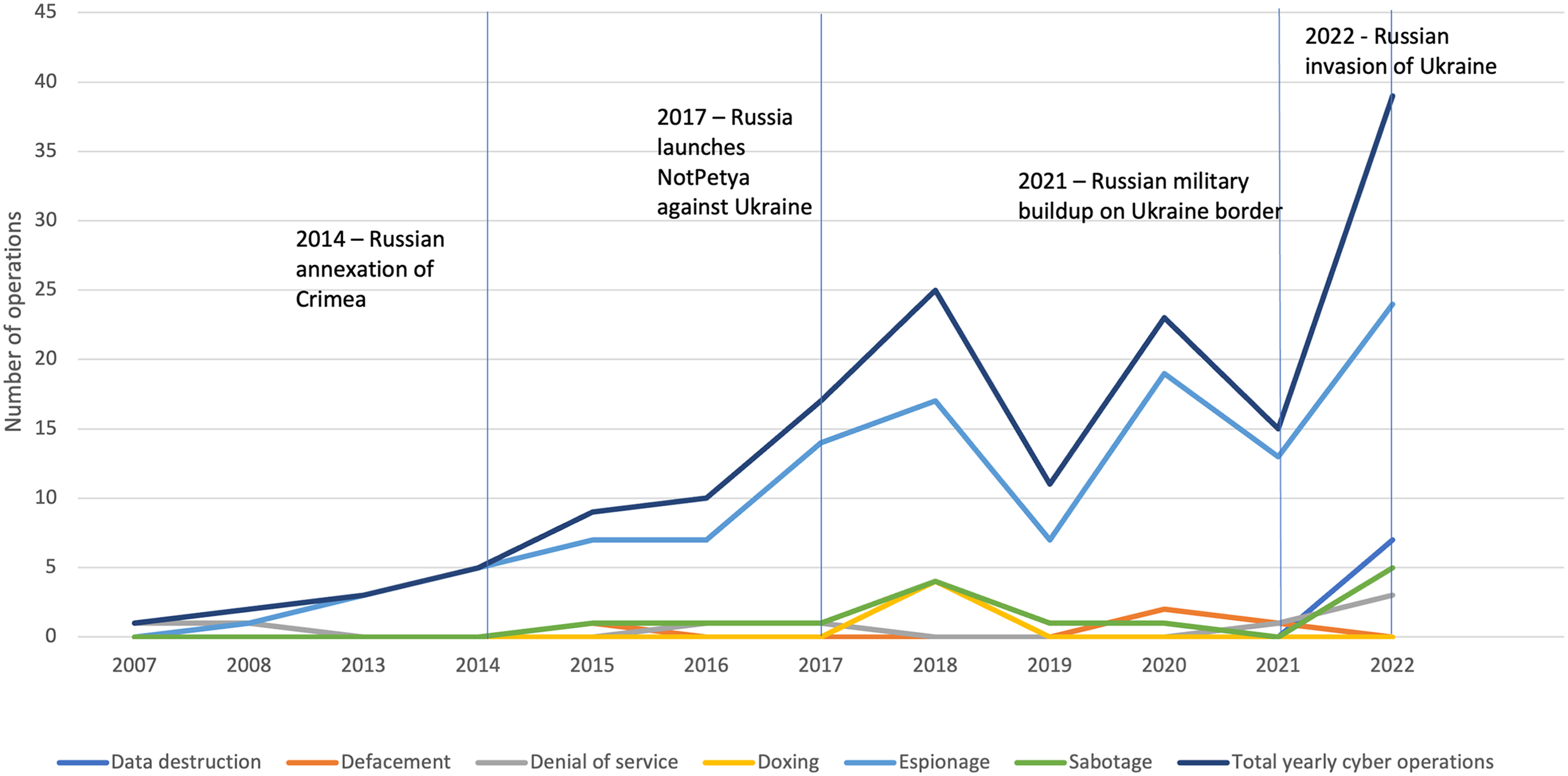
Type of Russian cyber operations per year.
Russia conceptualizes cyber operations as one component of a broader information warfare strategy, with the overall aim of disrupting and controlling information to its benefit. As a result, in Ukraine, Russia uses all forms of cyber operations, including cyber espionage, information operations through cyberspace, and destructive cyberattacks, for the purposes of achieving information control, disrupting Kyiv's information space, and undermining its will and ability to fight. Specifically, cyber espionage has been a Russian priority in Ukraine: it is used for its primary intelligence value, in preparation for future cyber operations, and to help further Russia's information and conventional military operations. Additionally, Russia uses cyber operations to conduct information operations through cyberspace, which are fundamentally aimed at achieving desired effects short of escalating to the actual use of conventional military force. Finally, Russia has used destructive cyber operations (e.g., denial of service, data-wiper attacks) against Ukraine to achieve both tactical and strategic effects. 8
A rough timeline of Russia's cyber aggression against Ukraine includes several milestones. During its limited invasion of Crimea and Donbas/Luhansk in 2014, Russia placed less importance on offensive and destructive cyber operations, and its attempts had limited strategic effectiveness: Russia's bid to interfere in Ukraine's 2014 election was detected and largely prevented; its attack on Ukraine's electric grids and water filtration system (2015–2018) resulted in only minor disruptions; and its surveillance of a mobile app used by the Ukrainian military (2014–2016) had only a brief tactical impact. Other, more widely known attacks from this era can likewise be interpreted as failures. Russia's NotPetya malware operation (2017), for illustration, was meant to cripple every facet of Ukraine's digital infrastructure. But Ukraine's GDP dipped by only 0.5 percent, hardly a long-term destabilizing blow. Nor did NotPetya undermine Ukraine's relations with the West. Rather, it cost Russia, which suffered diplomatic and economic censure once it lost control over the malware. These results occurred despite Ukraine's general lack of cyber preparedness and its inability to leverage widespread Western support.
This phase of Russia's cyber aggression was followed by a relative lull in offensive operations. As Table One illustrates, Russia appears to have spent the years preceding its full-scale invasion of Ukraine developing, pre-positioning, and gathering intelligence on their best use, rather than deploying its offensive cyber capabilities. When kinetic operations began once again in 2022, Russian cyber operations significantly rose instep, suggesting the importance of offensive cyber to Moscow's overall war strategy. The latest wave began with distributed denial of service and destructive attacks targeting Ukrainian critical infrastructure and government services, an attempt to undermine Ukraine's information space and the public's confidence in Kyiv. Over 30 percent of these cyberattacks targeted Ukrainian government entities, while more than 40 percent targeted critical infrastructure. The ViaSat cyberattack stands out. Launched on 24 February 2022, the very day Russian forces crossed into Ukraine, it rendered tens of thousands of European modems inoperable. As in previous engagements, Ukraine was able to blunt many of the expected effects of Russia's latest round of cyber operations, having greatly improved its defensive capabilities in cooperation with several allied governments and cybersecurity companies.
What can Canada and its allies learn about the evolving nature of contemporary power and conflict from Russia's near decade-long cyber onslaught against Ukraine? Five lessons, described below, stand out.
Cyber as coercive foreign policy
First, Russia uses cyber operations as an extension of its coercive foreign policy with the goal of destabilizing, dominating, and dictating an adversary's information space to help expand Russian influence and counter perceived threats. Coercion, in this context, refers to the use and threat of use of discrete but limited actions (e.g., show of force, limited incursions, acts of violence) to further intimidate, deter, or compel a target in a way that meets particular objectives. 9 Russia has repeatedly attempted to absorb Ukraine's cyber and information space into its own since 2014, through a combination of cyber espionage, information warfare, and destructive operations. Cyber espionage remains the dominant component of Russian cyber operations and is frequently used to advance Russia's coercive foreign policy both in and of itself, and for shaping information, kinetic, and destructive cyber operations. 10 Cyber espionage sets the table for follow-up operations. Furthermore, while Russia has aimed to destroy or seize Ukraine's cyber and information infrastructure, its attacks on foreign private sector infrastructure that have sided with Ukraine have focused on cyber espionage. The end goal is the same, however: to absorb Ukraine's information and cyber space by preventing Kyiv from being able to maintain an independent information space. Meanwhile, Russia's destructive cyber operations—like the NotPetya and the ViaSat attacks—have sought to destroy critical systems and undermine Ukrainian capabilities and confidence.
Russian cyber operations against Ukraine are likewise one component of a combined arms approach. Cyber operations are an incomplete substitute for conventional kinetic military operations; they require a great deal of R&D and planning, and face challenges in their levels of destructiveness and predictability. Moreover, offensive operations may result in desired impacts and access to data, but these effects diminish over time, as victims learn to adapt their responses. Conversely, kinetic operations that result in territorial occupation can create access and impact simultaneously and immediately, and can lead to further beneficial effects over time (i.e., directly shaping the views of an occupied population). While Russian cyber and kinetic operations have targeted the same Ukrainian assets—by mid-2022, for instance, Russia destroyed upwards of 20 percent of Ukraine's telecommunications infrastructure through cyber and kinetic operations—the latter have proven far more destructive and nominally effective than the former. Furthermore, Russia's use of cyber offense as part of a combined arms approach mirrors Russia's conceptualization of cyber operations as information warfare: when cyber and kinetic attacks are combined, the former usually focus on achieving information effects within the larger conflict. At times the aim is to gather and manipulate information for strategic effects by disrupting an opponent's information space and causing confusion, uncertainty, and chaos. 11
For Canada and its allies, the sum result is that Russia uses offensive cyber operations not as a discrete tool of state power, but rather as part of a broader set of cyber, information, and conventional military tools and techniques, all feeding into an attempt to expand Russian power and influence.
By crook, hook, or proxy
Second, Russia uses a variety of proxy actors, including criminal hacktivists, private firms, and paramilitaries, to conduct a wide range of cyber operations against Ukraine. Since the 2022 invasion Russian cybercriminals have evolved to increasingly mimic Russian government actors by conducting destructive cyber operations and hack-and-leak operations against Ukrainian targets, marking a departure from their traditional profit-seeking practices. Paramilitary proxies like Wagner PMC have likewise been documented engaging in cyber operations to further both their own and the Russian governments’ interests around the globe (e.g., in Mali, Nigeria, and the Central African Republic). Russia applies its information warfare strategy via proxies to secure victory over an opponent without engaging in open, attributable, or conventional military means. Sometimes referred to as grey zone operations, the use of proxies has helped Russia pursue its strategic objectives without risking undue and unwanted attention or escalation. Nonetheless, Russian grey zone cyber operations are at times counterproductive, especially when governments, including Ukraine's, publicly identify and attribute them. 12
Carving out an appropriate solution to Russian-driven, proxy-led cyber aggression will require that Canada and its partners decipher the web of interactions and devise flexible responsive mechanisms able to address the emerging nexus between commercial services, non-state violence, statecraft, and warfare.
Shaping the home game within the away game
Third, Russia's use of cyber operations to further its coercive foreign policy also reflects Russian domestic ambitions. Specifically, Russia has treated control of its domestic cyber and information space as central to its national security and foreign policy since the mid-2010s and has attempted to develop a sovereign internet to both control information domestically and protect Russian cyber infrastructure from attacks and interference. Russian foreign information operations are, at times, focused as much on a domestic audience as they are on a foreign one. Tellingly, nearly 95 percent of Russia's known information operations since February 2022 were conducted in Russian. Moscow also leverages proxy actors, including Russian private sector and criminal entities, to help maintain control of its domestic information environment. To a certain degree, Russian cyber operations represent a continuum between its foreign and domestic policies with the larger aim of maintaining regime stability while expanding influence and power abroad. 13
Countering authoritarian use of offensive cyber operations may require that Canada and its allies find creative ways to better tie together their foreign policy (i.e., providing Ukraine with the cyber and kinetic means needed to defeat Russia) and normative (i.e., bolstering international cyber rules, norms, laws, and principles) objectives.
The private sector's oversized role
Fourth, the private sector plays an increasingly critical role across all aspects of Russian cyber operations, an inevitability given that much of global cyber infrastructure is privately owned and operated. As such, coordination between the private sector and Russia's government and military has proven vital in facilitating Russian cyber aggression against Ukraine. Russia and its non-state proxies have both partnered with domestic firms to develop and launch cyber weapons and receive training in cybersecurity. A fair degree of cross-flow between Russia's private sector, proxy actors, and government agencies conducting cyber operations has been identified, with cyber experts moving between various private and public roles throughout their careers. The movement of personnel provides Russia's government with the ability to rely on private sector actors made up of former government employees as proxies to conduct cyber operations on its behalf, shielding itself against culpability. 14
During the latest conflagration, international private sector actors have likewise played a critical role in establishing a collective defensive effort for Ukraine, tying it closer to Western governments and their private industries. Foreign firms have played an “integral” part in defending all aspects of Ukraine against Russian cyber operations, by delivering cyber defences at scale, migrating government data and digital services to American private sector cloud storage, and ensuring continued digital and internet connectivity. This has denied Russia the means to access or destroy Ukrainian data. Furthermore, foreign private actors have tied Ukrainian defences to global preparedness: within hours of a Russian cyber capability being detected in Ukraine, anti-virus solutions can be meted out internationally to counter Russian malware elsewhere. Ukraine's own private sector has likewise played a role in undermining Russia's cyber strategy. For instance, domestic telecommunication providers have bolstered their networks by installing equipment donated by foreign entities and have engaged in self-sabotage in areas under Russian occupation to prevent Ukrainian infrastructure from being taken over. 15
For Canada, the lesson is that engaging with cyber conflict will require both leveraging and deterring private sector capabilities while threading the needle between competing national security and economic interests.
The slippery concept of success
Finally, despite Russia's intentions, its use of cyber operations as a form and function of coercive foreign policy has nonetheless struggled to achieve a desired outcome. Offensive cyber operations tend to have both short-term and long-term effects, with the former being predominantly tactical in nature. On the surface, under 30 percent of Russian cyber operations have succeeded in penetrating and exploiting a target. Nonetheless, the long-term consequences of cyber operations—including those deemed a tactical success—can be difficult to determine: effectiveness should be judged not by the degree of network penetration or disruption of services or theft of data, but rather on whether or not desired and expected strategic and military outcomes were achieved. Russia's engagements in Ukraine have sought to accomplish broad information-shaping effects as a long-term and indirect substitute to conventional military operations. Against this backdrop, Russia's cyber operations have not undermined Ukraine's will to fight and have otherwise been unable to compensate for Russia's apparent conventional military weaknesses. This is even true in cases where Russia has purposefully combined cyber operations with conventional kinetic operations. 16
Moreover, the effectiveness of Russian cyber operations against Ukraine has been offset by greater coordination and cooperation between Kyiv and a variety of allied governments and private sector actors. At least part of Russia's failure is due to Ukraine's defensive successes, mudding the tally sheet. But gauging Russian success in Ukraine is further complicated by the fact that Russian cyber operations may be constrained by self-imposed strategic limits: Moscow has long viewed cyber operations as information warfare aimed at achieving a desired strategic effect without needing to escalate to conventional force, but this approach has begun to shift as a result of the war in Ukraine, such that cyber operations are now being increasingly used to try to compensate for the perceived failures of Russia's conventional military campaign. 17
Canada and its partners should seek ways to drive these Russian failures home, establishing a perception that destructive cyber operations are a costly substitute for kinetic operations.
Footnotes
Declaration of conflicting interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
Notes
Author Biographies
Dr. Alex S. Wilner is an associate professor at the Norman Paterson School of International Affairs (NPSIA), Carleton University, Canada. His books include Deterring Rational Fanatics (University of Pennsylvania Press, 2015), Deterring Terrorism: Theory and Practice (eds., Stanford University Press, 2012), and Deterrence by Denial: Theory and Practice (eds., Cambria Press, 2021).
Gabriel Williams, Mattias Thuns-Rondeau, Nathanaël Beaulieu and Veronique Cossette-Sharkey are graduates of the Norman Paterson School of International Affairs, and were part of the 2023 Capstone research project that helped produce the article.
