Abstract
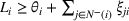
Firms in interorganizational networks are exposed to interdependent risks that are transferable across partner firms, such as contamination in food supply chains or data breaches in technology networks. They can be decomposed into intrinsic risks a firm faces from its own operations and extrinsic risks transferred from its partners. Firms have access to two security strategies: either they can independently eliminate both intrinsic and extrinsic risks by securing their links with partners or, alternatively, firms can cooperate with partners to eliminate sources of intrinsic risk in the network. We develop a graph‐theoretic model of interdependent security and demonstrate that the network‐optimal security strategy can be computed in polynomial time. Then, we use cooperative game‐theoretic tools to examine, under different informational assumptions, whether firms can sustain the network‐optimal security strategy via suitable cost‐sharing mechanisms. We design a novel cost‐sharing mechanism: a restricted variant of the well‐known Shapley value, the
Keywords
INTRODUCTION AND RELATED LITERATURE
Firms increasingly belong to a variety of interorganizational networks, such as complex supply chains, strategic alliances, or other types of partnerships. Membership in these networks can evidently yield economic benefits, but they also necessitate substantial additional security investments due to increased exposure to interdependent or contagion risks (Kunreuther & Heal, 2003). For instance, in January 2013, the European food industry endured a horse‐meat contamination scandal (Lawrence, 2013). Meat products from several retailers and fast‐food chains in the United Kingdom and Ireland, advertised as containing beef, were discovered upon testing to have been contaminated with horse‐meat. Further investigation revealed that in the complex meat supply networks, with contractors and subcontractors spread all across Europe, a particular supplier had indulged in deliberate contamination in a bid to cut costs. Several retailers, including Britain's largest retailer, TESCO, that had sourced the contaminated meat, faced economic repercussions from a drop in sales and reputational harm. Other notable cases of supply contamination include the adulteration of milk with melamine (Levi et al., 2020; Mu et al., 2016) and the 2008 heparin adulteration scandal (Babich & Tang, 2012). Contamination in supply networks, upon discovery, typically results in product recalls, regulatory fines, and brand equity loss, often entailing substantial costs for the concerned firms.
Besides supply networks, interdependent risks can arise in other contexts too. For instance, businesses have a growing recognition that they bear a social responsibility to secure their consumer data from cyber threats (Pollach, 2011). Malware infecting the systems of a company in an interfirm network can gain access to the IT systems of its partner firms. Due to poor cyber‐security practices by partner firms, companies such as Target and Home Depot have been the victims of high‐profile data and privacy breaches (McAfee, 2015). In today's highly interconnected networks, risks like contamination in food supply chains or consumer data breaches assume an interdependent nature. That is, the risks faced by a firm depend not only on internal risks arising from their own operations but also on the risk transferred from partner firms in the network. Further, the above examples involve risks transferred between networked partners with ongoing and frequent repeated interactions. Thus, a firm vulnerable to internal risks is near‐certain to transfer this risk to its partner firms if these partners do not take appropriate remedial actions.
Therefore, to secure themselves against interdependent risks, two general strategies are available to networked firms. First, firms in the network can choose to invest cooperatively in securing themselves, thereby removing sources of risk. Second, alternatively, firms can choose to independently secure themselves by eliminating risk from internal operations and then investing in security across the links that connect them to the other firms in the network. So, for example, firms could cooperatively share the costs of supplier quality improvements, thereby investing in suppliers' embracing responsible operational practices. Alternatively, a retailer can implement quality standards for internal processes and, simultaneously, inspect and quality test incoming products supplied by direct partners. The latter would correspond to the
Security against interdependent risks is associated with positive externalities since other firms are benefited from the presence of a secured firm in the network. This would intuitively suggest that cooperative network‐wide security against interdependent risks can be a cost‐effective strategy as compared to each firm in the network independently securing itself. However, cooperation can be hindered by disagreements over cost‐sharing arrangements. Firms, in general, are heterogeneous, both, in the costs they incur to secure themselves as well as in the penalties that they may face in case of a realized risk. Thus, a priori, it is not clear whether there will always exist a stable and fair sharing of security costs that can sustain network‐wide cooperation. Furthermore, networked firms typically have visibility and mechanisms to cooperate and monitor with only immediate partners. For instance, extended multitier supply chains are often associated with a loss in visibility over firms further away in the network (Caro et al., 2021). Thus, it is also unclear whether one can find suitable mechanisms to implement cost‐sharing arrangements that circumvent coordination across firms that are not immediate or direct partners.1
To address these issues, in this paper, we consider an interdependent security model on a network and an associated cost‐sharing game. In our model, as motivated above, firms face an intrinsic risk from their internal operations and an extrinsic risk from their unsecured partners in the network. Firms in the network are heterogeneous in the costs they incur to secure themselves and the penalties they face in case of an actualized threat.
Further, we also consider our network security model under differing informational assumptions. In our
The network‐optimal security strategy under all informational assumptions is identical, and we demonstrate that it can be computed in polynomial time using a minimum weighted cut network‐flow algorithm. Then, we adopt a cooperative game‐theoretic approach to assess whether agents have an incentive to cooperate across the entire network and share the security investment costs. We show that, under the private information setting, agents have a clear incentive to cooperate globally, that is, form the grand coalition and share the resulting security costs. However, with even some information being public in the network, we show that, in general, there do not exist cost‐sharing mechanisms that can ensure the stability of the grand coalition. This can be explained by two drivers: first, with public information, the benefit from additional information acquisition is lowered. Thus, the benefits from cooperative security in the public information setting are arguably lower. Second, public information engenders free‐riding since firms can now anticipate and observe the security actions of other firms in the network and benefit from the cooperation of other firms in the network without participating in the grand coalition and sharing security costs. In similar cooperative settings with externalities, free‐rider concerns are acknowledged as a fundamental reason often precluding the stability of the grand coalition (see, e.g., Yi, 1997).
Importantly, we then introduce the notion of 

To analyze the effects of network structure on the existence of the agreeable allocation, we consider the special case of quasi‐homogeneous networks, that is, networks where the security cost parameters are equal. We then provide a structural graph‐theoretic characterization for the existence of the agreeable allocation in these networks. Specifically, we show that the local density of networks plays a key role in determining whether the agreeable allocation exists.
In summary, one can view our work in both descriptive and normative terms. Descriptively, we observe that network‐wide security cooperation is efficient and, in some cases, this cooperation can be sustained with suitable cost‐sharing arrangements. However, when concerns pertaining to computability and implementability of these cost‐sharing mechanisms are incorporated, network‐wide security cooperation is rendered more challenging. Normatively, via our analysis of the agreeable allocation and its extensions, we are able to provide insights into when and how these implementation challenges can be surmounted.
Overview of related literature
This work is related to three distinct streams of literature. First, it contributes to extant work on social responsibility and risk management in supply chains. Second, our work is closely tied to interdependent security models introduced by Kunreuther and Heal (2003). One of our aims is to bridge these two bodies of literature. Finally, our work adds to the growing literature on applications of cooperative game theory to operations management.
Supply chain social responsibility and risk management
There is a vast literature investigating the role of several instruments such as auditing (Caro et al., 2018; J. Chen et al., 2020; Fang & Cho, 2020; Plambeck & Taylor, 2016), inspection and testing (Babich & Tang, 2012; Lee & Li, 2018), and more recently, contracts (Dhingra & Krishnan, 2021), in mitigating social responsibility risks associated with extended global supply chains. We refer the interested reader to Dawande and Qi (2021) for a recent review. While previously, most of this literature dealt with two firm or dyadic scenarios, recently, several studies also deal with multitier supply chains, for example, supply networks with three tiers or other network structures (J. Chen et al., 2020; L. Huang et al., 2020; Zhang et al., 2022). Also closely related to our work, Feng et al. (2021) study the implementation of environmental and social responsibility (ESR) programs in general supply networks and gain sharing via a bilateral bargaining framework that generalizes a conventional Shapley value based cooperative‐game theoretic approach. Recently, Blaettchen et al. (2021) also study the optimal adoption seeding of traceability technologies which carry several implications for sustainable practices in supply networks. While we view our work as contributing to this stream of literature, we note that it bears some differences. For instance, we consider a general network structure and do not impose any structural assumptions. Second, our work deals with only interdependent risks. That is risks that are contagion risks spreading via the network. These scenarios include cases such as food contamination risks or data breach threats as motivated in the introduction.
Interdependent security
In terms of model development, our work is most closely related to the interdependent security literature. Interdependent security models were introduced by Kunreuther and Heal (2003) and have since spawned a rich literature on the intersection of economics and computer science that studies various related models (see, e.g., Laszka et al., 2014, for a review). In these models, as in ours, the security of agents depends on an agent's own actions (direct risk, or as we term it, intrinsic risk) and those of other agents (indirect or extrinsic risk). The present work aims to bridge the interdependent security literature with the rich stream of work on socially responsible operations in supply networks. While this research stream inspires our model, our work differs from existing literature in some crucial ways. First, in several of the existing models, the agents can only curb their own intrinsic risk and cannot mitigate extrinsic risks. Second, a majority of the interdependent security literature adopts a noncooperative (game‐theoretic) perspective. They assume that players in the network act to secure themselves independently and then characterize and compute the noncooperative equilibria of these games. Kearns and Ortiz (2003) and Chan et al. (2012) develop algorithms to compute the equilibria of classes of interdependent security games. Heal and Kunreuther (2007) also consider the Nash equilibria of such games and study conditions to tipping suboptimal equilibria to an optimal one. Chan and Ortiz (2014) consider a more general model where agents can influence the transfer of extrinsic risk and then analyze equilibria computations. However, this literature largely ignores issues of cooperation in networks and the problem of when and how cooperation can be sustained. In practice, agents can and indeed do cooperatively secure themselves against interdependent risks. This, therefore, is the central focus of this present paper.
Cooperative game theory in operations management
Finally, we also contribute to the growing body of work dealing with applying cooperative game theory to problems in operations management. For a review of this literature, we refer the reader to Nagarajan and Sošić (2008). Benefits of cooperation can be realized and therefore studied in several diverse settings. Some recent applications include inventory pooling (Kemahlıoğlu‐Ziya & Bartholdi, 2011), inventory transshipments (Granot & Sošić, 2003; Sošić, 2006), demand information sharing (Leng & Parlar, 2009), supplier alliances to mitigate order default risk (X. Huang et al., 2016), production schedule coordination (Aydinliyim & Vairaktarakis, 2010), supply chain emissions management and reduction (Gopalakrishnan et al., 2021a, 2021b), recycling (Gui et al., 2018; Tian et al., 2020), humanitarian operations (Ergun et al., 2014), vaccine distribution (Westerink‐Duijzer et al., 2020), and so forth. Related to our work, Mu et al. (2019) study quality management in milk cooperatives. In dairy cooperatives, individual farmers can shirk on quality and free‐ride on the higher quality milk produced by other farmers in the cooperative. Mu et al. (2019), therefore, develop a revenue allocation rule that achieves quantity and quality efficiency with minimal testing while incorporating other practical implementation considerations.
A NETWORK SECURITY MODEL
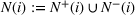
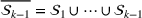
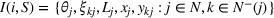
We consider a set of heterogeneous players2 denoted by 








Each player faces two independent sources of risk: an 





As outlined in Section 1, firms can derive two distinct advantages from cooperative security in networks: first, the benefit of interdependence, which involves internalizing the positive externality of security, and, second, the advantage of information acquisition. Accordingly, we first consider two extreme informational assumptions, a
Private information model
In the private information model, we assume that all cost parameters including the cost of securing against intrinsic risk, 




Public information model
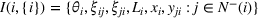
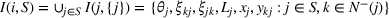
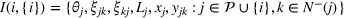
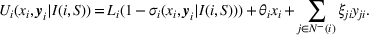
In contrast, in the public information model, we assume that all firms can observe each other's cost parameters and security actions even in the absence of cooperation. Then, the information set of a player 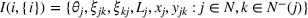

Partial information model
In practice, even in the absence of explicit cooperation, the security costs and actions of certain firms may be public knowledge, due to regulatory requirements or strategic disclosures, whereas the costs and actions of other firms may only be known privately. Thus, we also consider a more general partial information model which assumes that the costs and actions of a subset of firms, 



Security actions
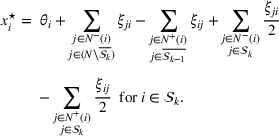
Players in the network choose security actions, 














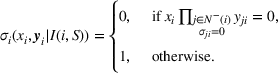
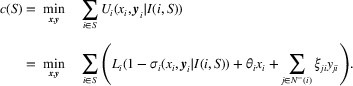
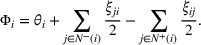
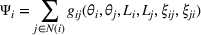
Thus, the expected security cost incurred by a player
The first term in (2) corresponds to the expected penalty from a realized risk and is incurred only when the player
In Sections 3 and 4, we analyze cooperative security strategies and the associated security cost‐sharing problem in the private information model whereas in Section 6 we study the public information model. This sequence is chosen for expositional clarity. Further, in the interest of parsimony, we relegate the analysis under the general
SECURITY STRATEGIES UNDER PRIVATE INFORMATION
Under the private information assumption, since a player cannot observe or infer the security actions of other players, we assume a player 








We now consider two forms of security strategies in the network: the
Independent security strategy
Since the players are not cooperating with each other on their security actions, as noted previously, the information set of each player A player 








The above proposition captures two straightforward notions in the private information setting: (i) the independent security strategy is based on a simple trade‐off between the cost of security and the expected penalty incurred from not securing itself, (ii) for an agent acting independently, it is not optimal to partially invest in securing some links and not others.
Network‐optimal security strategy
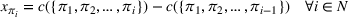
In this setting of full network‐wide cooperation, the information set of each player contains all the security costs and expected penalties of all other players in the network. The players act to minimize the total expected security cost of the network.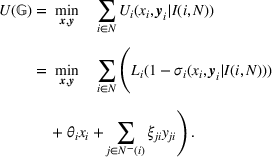
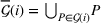
We denote the set of all players in Every player independently secured is also secured under the network‐optimal security strategy, 


However, the positive externalities, inherent to this context, may result in certain nodes being secured under the network‐optimal security strategy which are unsecured when acting independently. That is, we note that the above inclusion can be strict. We demonstrate this with Example EC.1 in the Supporting Information.
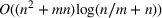
We now provide a key result demonstrating that the network‐optimal security strategy and equivalently, 



Construction of the auxiliary network


The node set of Suppose the minimum weight cut separating 


















Auxiliary network 
Also, from (1), it follows that if











In the private information model, the network‐optimal security strategy resolves two distinct kinds of inefficiencies engendered by the individually rational security strategies of the players. The first inefficiency arises from the canonical underinvestment of efforts resulting from a failure to internalize positive externalities. This is well recognized in the interdependent security literature (see, e.g., Acemoglu et al., 2016). Therefore, some agents for whom it was individually rational to not invest in security efforts are now secured since these erstwhile externalities are now internalized in the network‐level optimization. This reflects the strategic complementarity inherent in situations with interdependent risks. The second source of inefficiency arises, in the private information model, as a consequence of security costs being privately held information. Equivalently, the noninferability of security efforts of a player by other players who are not cooperating with it results in the inefficient duplication of security investments across the network. This provides an economic rationale for anecdotal evidence from diverse supply chain security contexts that bear out this source of inefficiency (ASEM, 2013).
Finally, we note the necessity of cost‐sharing mechanisms in order to implement the network‐optimal security strategy. For a player in the network, given the security states of all of its direct partner firms, the network‐optimal security action is not necessarily individually rational. That is, the network‐optimal security strategy is not always a Nash equilibrium strategy as demonstrated by Example EC.2 provided in the Supporting Information.
SECURITY COST SHARING MECHANISMS
The next natural question is therefore to ask whether network‐wide security cooperation in the private information model can be sustained with suitable cost‐sharing mechanisms. Equivalently, we are interested in finding whether and when cooperation can be made individually rational and the network‐wide efficiency gains can be shared among the firms in a
Cooperative game theory primarily addresses the question of whether cooperation can be sustained across a group of agents and, closely tied to this, is the problem of 







Interdependent security cost sharing
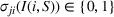
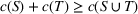
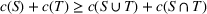
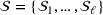
Consider the set of agents 

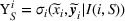
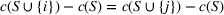
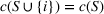
We define an indicator function A player 












Further, the pair 
The following proposition indicates that





An efficient security cost‐sharing mechanism is defined as The coalition‐optimal security cost, 

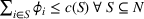


Before we proceed to derive and analyze specific security cost‐sharing mechanisms, we observe that if a player is unsecured under the network‐optimal security strategy, then, the player is allocated 





Shapley value based security cost sharing
The convexity of 

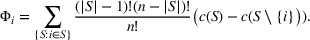
The Shapley value rewards players for their marginal contributions to various coalitions, and, to that extent, it can be argued as exemplifying a certain notion of fairness. Further, Φ is the unique








Of these properties, we note that the symmetry property formalizes the idea that players which are “identical” in terms of their marginal contributions should receive an identical share of the value created by cooperation. This is, arguably, an innocent fairness criterion which, along with the marginal contribution interpretation discussed before, we shall return to later on in this work. The Shapley value is widely adopted as a cost sharing or a profit sharing, as the case may be, allocation method in diverse contexts, including several mentioned in Section 1.1, such as inventory pooling (Kemahlıoğlu‐Ziya & Bartholdi, 2011), capacity allocation and scheduling (Aydinliyim & Vairaktarakis, 2010), group purchasing (R. R. Chen & Yin, 2010), disaster preparedness (Rodríguez‐Pereira et al., 2021), and so forth. However, for our game, we establish a link between the computation of the Shapley value and the classical subset sum problem. In fact, this connection demonstrates that computing the Shapley value of interdependent security games is a computationally hard problem. There is no polynomial time algorithm that computes the Shapley value for a given player in the interdependent security cost‐sharing game unless P = NP.
Further, from the proof of Theorem 3, we note that even for simple structures such as the assembly supply network, computing the Shapley value is hard. Beyond computational interest, the above result on the complexity of the Shapley value is of interest to us for reasons of implementation. In general, equilibrium concepts in noncooperative game theory or solution concepts in cooperative games that are computationally intractable raise the question of feasibility of whether self‐interested agents can identify and implement these mechanisms in practice.4
For a notable special case, however, the Shapley value can be computed easily. In fact, when the expected penalties, in case of a realized risk, are sufficiently large for all players, then the Shapley value has a straightforward closed form expression. If 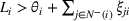



In this scenario, when the expected penalties are sufficiently large, it is individually rational for all players to secure themselves (i.e., under the independent security strategy). That is, since all players choose to secure themselves even without cooperation, the network‐optimal security strategy resolves only one kind of inefficiency, that arising from duplication of security efforts. Under the Shapley value based security cost‐sharing mechanism, in this scenario, the cost savings from avoiding duplication of security efforts across each link are equally shared by both parties.
Extreme core allocations
However, this still leaves open the question of whether, in general interfirm networks, there exist stable security cost‐sharing arrangements sustaining network‐wide cooperation that can also be computed easily. We now provide an affirmative answer to this question. Consider an arbitrary permutation π of the players in For every permutation π of 

The proof of Proposition 5 relies on the convexity of the game and the characterization of the core of convex games as developed by Shapley (1971). Further, we demonstrate that the extreme core points of the interdependent security cost‐sharing game can be computed in polynomial time, thereby, allowing us to identify easily computable and stable security cost‐sharing arrangements. However, it can easily be seen that extreme core allocations as identified in Proposition 5 do not satisfy a basic notion of fairness as embodied in the symmetry property introduced earlier. The security cost‐sharing allocation 
Our discussion, thus far, uncovers what appears to be an “impossible” trilemma:
BILATERAL AND MULTILATERAL IMPLEMENTABILITY
In Section 4, we considered a narrow version of implementability. Specifically, we presumed a security cost‐sharing mechanism that is easily computable is implementable. However, implementing cost‐sharing mechanisms via transfer payments across the network, even between firms that are not direct partners, is administratively challenging, perhaps even infeasible. Firms often have limited visibility let alone an ability to enter into cost‐sharing arrangements with indirect network members. Therefore, in this section, we are prompted to study whether there exist stable and fair cost‐sharing mechanisms that can be implemented via transfer payments only involving firms that are direct partners in the network. Indeed, since alliance networks are often comprised of a series of bilateral alliances in the first place, we develop a realistic bilateral implementation framework that can allow firms to sustain network‐wide security cooperation against interdependent risks.5
To this end, we define the 






First, we examine the bilateral implementability of the Shapley value based security cost‐sharing allocation discussed in Section 4. We introduce some definitions. For a given player Consider the Shapley value based security cost‐sharing allocation Φ. Φ is bilaterally implementable if for all players Φ is not bilaterally implementable if there exists a player 












Theorem 5 provides characterizing conditions for when the Shapley value based cost‐sharing arrangement is bilaterally implementable. Observe that minimal coalitionally rational security sets formalize the externalities that secured players induce on other players in the network. Therefore, roughly speaking, the above theorem demonstrates that as the extent of positive externalities of security in the network increases, the Shapley value based security cost‐sharing fails to be bilaterally implementable. As a corollary, we observe that for the special case discussed in Theorem 4, the Shapley value cost‐sharing mechanism is clearly bilaterally implementable.
Theorem 5, in conjunction with Theorem 3, arguably also demonstrates the impracticality of adopting a Shapley value based security cost‐sharing arrangement in all but a narrow class of networks. Specifically, since it is neither computable efficiently nor bilaterally implementable, in general, we argue that this renders it contextually untenable. We now propose a novel security cost‐sharing mechanism that builds on the extreme core allocations considered in Proposition 5.
Extreme core allocations and the agreeable allocation
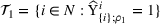
In light of Lemma EC.1, we limit our attention to networks where all firms are secured in the grand coalition. We further recall the previously defined indicator function 



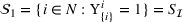


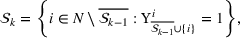















We note that it is possible in certain networks and associated cost parameter vectors for no 


Furthermore, recall that extreme core allocations are not symmetric, therefore, arguably, violating a basic notion of fairness. To remedy this, we are now in a position to propose our novel security cost‐sharing mechanism, the The agreeable allocation of network‐wide security costs, when it exists, (i) belongs to the core and is (ii) polynomial‐time computable, (iii) symmetric, and (iv) bilaterally implementable. Further, it also satisfies (v) marginality and the (vi) null player property. Moreover, the security cost allocated to player 
Observe that the network‐wide security cost apportioned to each player by the agreeable allocation depends only on its own security cost parameters and that of its direct partners, and, therefore, it is bilaterally implementable. Also, importantly, we note that the agreeable allocation attempts to resolve the tension between
We also remark that for the special case considered in Theorem 4, that is, when 
Multilateral implementability and δ‐agreeable allocations
The agreeable allocation is indeed appealing since its bilateral implementability minimizes the coordination challenges involved in sustaining the network‐optimal security strategy. However, sometimes firms that are not direct partners may regardless cooperate via suitable transfer payments when it can be mutually beneficial. Consider a network 






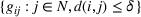

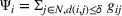




While our general approach to construct a For a given integer 



The δ‐agreeable allocation satisfies the generalized notion of Consider the interdependent security cost‐sharing game under private information. If for an integer For every integer The The 












Theorem 8 clarifies a hierarchy of existence for δ‐agreeable allocations. As δ increases, and firms that are farther away from each other in the network are allowed to cooperate with each other via suitable transfer payments, the δ‐agreeable allocation is more likely to exist. However, naturally, as δ increases, arguably, the δ‐agreeable allocation becomes more challenging to implement than the agreeable allocation since it requires coordination between firms that are farther away in the network. Further, it follows from Theorem 8(iv), and since, in general, the Shapley value allocation involves transfer payments between any two firms in the network, δ‐agreeable allocations are (weakly) less challenging to implement than the Shapley value.
NETWORK SECURITY MODEL WITH PUBLIC INFORMATION
In this section, we consider the public information model, as presented in Section 2, wherein all network cost parameters and actions are known to all players in the network. That is, the information set of every player 


Characterizing the security strategy of a coalition, or even the independent security strategy, in the public information model poses some challenges. In our network security model, as is often the case in network games with public information (Galeotti et al., 2010), there could be multiple Nash equilibria. Further, in the public information setting, the actions of a player or a coalition also depend on the actions of other players, and, therefore, naturally on whether other players in the network are cooperating with each other. Therefore, we cannot analyze the security actions of a player or a coalition in isolation. We instead need to consider the cooperation structure across the entire network. This is in contrast to the interdependent security cost‐sharing game developed in Section 3, wherein the security cost of a coalition 

Again, we first consider the security actions of players when they are all acting independently. That is, ρ consists of singleton sets of players. Each player 

Algorithm 3 computes an equilibrium security state of player 



We then obtain the total security cost of a coalition 
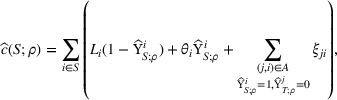
where 



We demonstrate that in the interdependent security cost‐sharing game under public information, The grand coalition in the interdependent security cost‐sharing game under public information, 

We now, however, show that the agreeable allocation can be extended to the public information setting while retaining several of its desirable properties. Notably, we prove that, analogous to Theorem 6, the public information version of the agreeable allocation, when it exists, satisfies individual rationality, a weaker notion of stability wherein each player is better off in the grand coalition (i.e., with full cooperation) as compared to the independent coalitions (i.e., no‐cooperation) scenario.
Agreeable allocation with public information
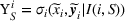
Again, for ease of exposition, we restrict our attention to networks where all firms are secured in the grand coalition. We recursively define a finite family of mutually exclusive sets 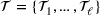



















Suppose there exists The agreeable allocation under public information, 






Therefore, while the agreeable allocation cannot guarantee that the grand coalition is stable to defections by subsets of players (indeed no cost‐sharing allocation can), it still satisfies a weaker notion of stability. It ensures that all players will prefer to remain in the grand coalition structure For a given network 



Here, we briefly comment on some main implications of our analysis of the general partial information model in Section EC.4. First, we demonstrate that the agreeable allocation can be naturally extended to the partial information model thereby generalizing Theorem 9. Therein, we observe that Corollary 2 also generalizes and the existence of the agreeable allocation is not contingent on the informational assumption in the network. Finally, and importantly, we clarify that even in the presence of partial public information in the network, the grand coalition may be unstable and that if the grand coalition is unstable with a certain level of public information in the network, it remains unstable at higher levels of information provisioning in the network.
QUASI‐HOMOGENEOUS NETWORKS
The chief deficiency of the agreeable allocation, under all informational assumptions is that, in general, depending on the structure of the interfirm network, or the associated security costs, it may not exist. To the extent that an agreeable allocation is viewed as desirable for its fairness, bilateral implementability, and other properties as documented in Theorem 6 and Theorem 9, this offers a rationale for when interfirm networks will find it challenging to cooperatively secure themselves. In order to examine the role of the network structure on the existence of the agreeable allocation, we now consider 








Analyzing quasi‐homogeneous networks permits us to isolate the effects of the network structure on the existence of the agreeable allocation. A priori, it is qualitatively unclear what the role of network structure would be on the existence of the bilaterally implementable agreeable allocation. For instance, denser networks can render it easier for efficient and stable cost‐sharing arrangements to be bilaterally implementable since there are more bilateral links. However, denser networks may also result in wider positive externalities to securing oneself necessitating multilateral cooperation.
We now introduce some graph‐theoretic definitions that aid us in identifying when quasi‐homogeneous networks admit and do not admit an agreeable allocation of security costs. We define a Consider a quasi‐homogeneous network






















The two parts of Theorem 10 provide distinct sufficient and necessary conditions, respectively, for the existence of the agreeable allocation in quasi‐homogeneous networks. From a descriptive standpoint, it implies qualitatively that the agreeable allocation is guaranteed to exist in (quasi‐homogeneous) networks so long as they are not sufficiently locally dense. This refines our earlier intuition on the role of interfirm network structure on the existence of the agreeable allocation. Further, in graphs that contain sufficiently dense and sufficiently local clusters, the agreeable allocation is guaranteed to not exist.
NUMERICAL CASE STUDY
We now present a case study analyzing the feasibility of cost‐sharing mechanisms to sustain network‐wide cooperative security in real‐world interfirm networks that can face interdependent risks. Specifically, we use the Refinitiv SDC Alliance database to extract all alliances in the food manufacturing sector formed between 2006 to 2020. The database contains 2339 alliances formed between 3073 unique firms in our industry of interest. Typically, these are bilateral alliances formed between two firms, while, on occasion, alliances are formed between three or more firms. For example, one of the alliances in the database is between Optibiotix Health Plc, a biotechnology company that manufactures SlimBiome, a weight management supplement, and John Morley (Importers) Ltd, which manufactures prepared perishable foods. Optibiotix Health would supply the weight management supplement to be included in prepared muesli packs manufactured by John Morley Ltd within the United Kingdom. In this example, the presence of an interdependent risk is evident. Over time, larger networks of alliances arise and we identify 792 distinct interfirm networks. Of these, the largest connected network of firms contains 1092 nodes. The other networks are smaller, and we remove all networks consisting of only two firms since these networks trivially permit bilaterally implementable cost‐sharing mechanisms. We in fact restrict our attention to alliance networks that are of size at least five, and we obtain exactly 50 such alliance networks.10 We depict two of these networks in Figure 2.
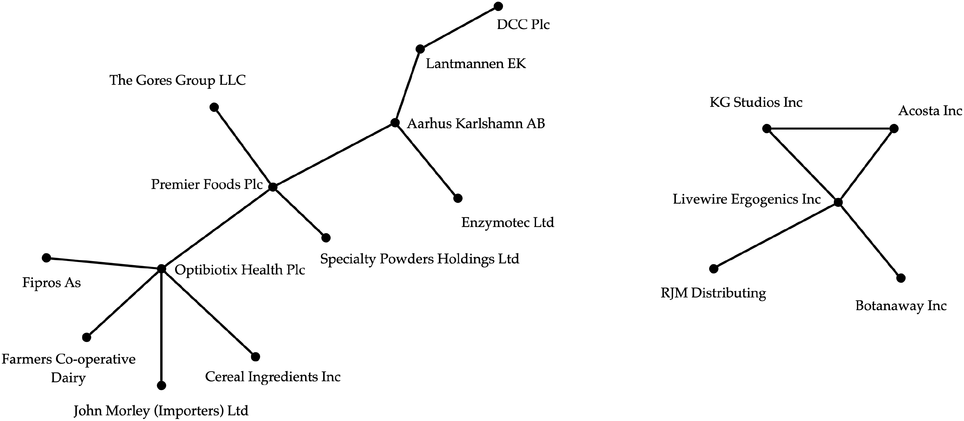
Examples of alliance networks in the food manufacturing sector.
We leverage the algorithmic results obtained in previous sections to numerically test whether the agreeable allocation exists, and when it exists, compute the network‐wide security cost apportioned by the allocation. These results are meant to be illustrative since the existence of the agreeable allocation naturally depends on the precise security cost parameter specifications. However, the security cost parameters and the penalties are simulated in a systematic manner. Across all simulated networks, we set the parameter 



First, we observe that in 56.7% of the simulated networks, the agreeable allocation exists. In contrast, in only 0.79% of the simulated networks, the Shapley value based security cost‐sharing allocation is of the form given by Theorem 4 and, hence, bilaterally implementable. This, in conjunction with the straightforward implementation mechanism described in Section 5, demonstrates the practical relevance of our proposed security cost‐sharing allocation. Second, we find, interestingly, that the alliance network permitting the agreeable allocation to exist with the highest likelihood of 74.3%, is a star network. Finally, we observe that the networks which rarely permit the existence of the agreeable allocation, in only 2.6% and 4% of the simulations, respectively, are both completely connected networks, that is, cliques of size six. This lends further evidence in support of Theorem 10 that densely connected networks preclude the existence of the agreeable allocation.
In the above numerical experiment, the cost parameters for all nodes in a network were drawn from the same distributions. However, in real‐world networks, there is usually a significant asymmetry in the penalties incurred by firms in case of a realized risk. Consumer‐facing firms typically incur substantially larger penalties than others. To incorporate this in our simulation, we obtain the Standard Industrial Classification (SIC) codes of the firms from the SDC database. We then denote firms in the retail industry (with a SIC code in the range of 5200–5999) as consumer‐facing firms. Of the 3073 unique firms in our dataset, we identify 154 such (potentially) consumer‐facing firms. In our second numerical experiment, we simulate the cost parameter 


CONCLUDING REMARKS
Networked firms are exposed to a variety of interdependent, or contagion, risks such as supply chain contamination, deliberate adulteration, or cybersecurity threats and data breaches. The fundamental distinction that sets apart these risks from other types of risks faced by firms is their transferable nature. In this paper, we develop a network model to study the cooperative management of interdependent risks by networked firms.
The network‐wide cooperative security strategy in our interdependent risk model can be computed in polynomial time via a minimum‐weight cut network flow algorithm. Assuming that the security costs and actions are private information known only to the respective players, we find that firms have a clear incentive to cooperate and that there exist stable security cost‐sharing mechanisms that can sustain network‐wide cooperation. However, in the presence of public information, we find that, in general, there do not exist cost‐sharing mechanisms that can ensure the stability of the grand coalition. Thus, it appears that interdependence of network security is alone insufficient to sustain network‐wide cooperation.
Introducing the notion of bilateral implementability, we uncover a fundamental trilemma between stability, fairness, and implementability of network security cost‐sharing mechanisms. We then develop a novel cost‐sharing mechanism, the 
Moreover, to study the role of network structure on the existence of the agreeable allocation, we consider quasi‐homogeneous networks (i.e., networks with homogeneous costs of security and expected penalties in case of realized risk) and find that networks without sufficiently dense clusters admit an agreeable allocation. Whereas, networks containing sufficiently dense and local clusters do not permit an agreeable allocation of network‐wide security costs. Finally, using the SDC alliance database, we extract all alliances formed in the food manufacturing sector between 2006 and 2020. With numerical experiments and simulated cost parameters, we argue the practical feasibility and relevance of employing the agreeable allocation as a bilateral security cost‐sharing mechanism in real‐world alliances to sustain network‐wide cooperative security against interdependent risks.
This work develops, to the best of our knowledge, for the first time, an economic theory of cooperative security against interdependent risks in networks. However, we acknowledge several limitations and open problems arising from our study.
Limitations
First, for instance, the question of the general existence (or nonexistence) of a bilaterally implementable and stable cost‐sharing mechanism remains open. Second, and crucially, in this paper, we consider interfirm networks characterized by repeated and ongoing interactions between firms. Thus, a vulnerable firm is nearly certain to transfer risks to its partner firms if the partner firms do not secure the corresponding link. A richer model of interdependent security would allow for a stochastic transmission and propagation of risk in the network. However, this richer stochastic model of interdependent network security is challenging to analyze. Particularly, the characterization of cooperative security strategies in this stochastic model of interdependent security is a nontrivial problem. Finally, we assume that the considered networks are static whereas, in reality, networks tend to change dynamically, with new alliances being formed, and existing alliances being broken over time. Bilaterally implementable cost‐sharing mechanisms, in particular, may be well‐suited to sustain cooperation in dynamic alliances, as we have noted earlier.
Footnotes
ACKNOWLEDGMENTS
1
Relatedly, Dawande and Qi (![]() ), in a review of recent research on socially responsible operations management, note that “a topic that has not received much attention yet is the design of cooperative strategies among stakeholders in different tiers of a supply chain to collectively ensure socially responsible actions across the supply chain … the utilities of different players from actions such as auditing, inspections, and testing become interconnected in a complex manner. Consequently, the sharing of costs in a fair manner to incentivize cooperation across tiers becomes challenging.”
), in a review of recent research on socially responsible operations management, note that “a topic that has not received much attention yet is the design of cooperative strategies among stakeholders in different tiers of a supply chain to collectively ensure socially responsible actions across the supply chain … the utilities of different players from actions such as auditing, inspections, and testing become interconnected in a complex manner. Consequently, the sharing of costs in a fair manner to incentivize cooperation across tiers becomes challenging.”
2
The terms
3
In the interdependent security literature, intrinsic and extrinsic risks are sometimes referred to as
4
Relatedly, Roughgarden (![]() ) observes “(A) complexity‐theoretic hardness result can diminish the predictive interpretation of an equilibrium concept and suggests more tractable alternatives […] In a practical design context, it is obvious that a mechanism that is actually implemented had better be computationally tractable to run, like the deferred acceptance algorithm, and also easy to play, in the sense that participants should not need to perform difficult computations.”
) observes “(A) complexity‐theoretic hardness result can diminish the predictive interpretation of an equilibrium concept and suggests more tractable alternatives […] In a practical design context, it is obvious that a mechanism that is actually implemented had better be computationally tractable to run, like the deferred acceptance algorithm, and also easy to play, in the sense that participants should not need to perform difficult computations.”
5
Furthermore, a purely cooperative‐game theoretic approach to cost‐sharing problems on occasion faces some criticism, as, for example, in Feng et al. (![]() ), of providing “no implication for implementation in terms of how firms interact in the network and how financial payments are made among the firms.”
), of providing “no implication for implementation in terms of how firms interact in the network and how financial payments are made among the firms.”
6
7
In the general partial information model analyzed in Section EC.4, firm
8
9
Conventionally,
10
The largest alliance network comprises 1092 firms and 2624 partnerships (i.e., arcs). The other 49 alliance networks are smaller and qualitatively bear structural similarities containing an average of 6.79 nodes (a median of six nodes) and 14.28 arcs (a median of 12). The average degree of each node across the 50 alliance networks (i.e., the average number of partners for a firm) is 2.13. We also observe that 28 of these 50 alliance networks are
11
12
Not surprisingly, we also observed a substantial advantage in terms of the computational time required to obtain the agreeable allocation in comparison to the Shapley value.
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
