Abstract
We consider a grid-based deployment scheme in which keys are predistributed in sensor nodes following a transversal design. This scheme was first proposed by Ruj, Maitra, and Roy in [19]. In their scheme the RF region was considered to be the a square of appropriate dimension. In this article, we consider the RF region to be the Lee sphere of appropriate radius. This is a better approximation than the square RF region and all calculations of connectivity and resiliency is done with respect to this parameter.
Keywords
Introduction
Sensor networks consist of resource constrained devices and deployed for both military and civilian purposes. To carry on communication in a secure manner, any two sensor nodes should communicate in an encrypted manner using a common secret key. Towards secure communication, it is important that any two sensor nodes should communicate in an encrypted manner using a common secret key. The designer may predistribute the keys in each sensor node or on-line key agreement strategies may be used. For on-line key agreement strategies, some kind of public key infrastructure is required. Public key techniques involve huge computational costs and are therefore not suitable for the resource constraint sensor nodes. Hence keys are preloaded in the sensors before deployment. Several key predistribution techniques have been discussed in literature. [1–4, 14–17].
To increase resiliency, deployment knowledge may be used. Deployment knowledge has been used in [1, 6, 7, 12, 15, 19, 21, 28]. In [19] Ruj, Maitra, and Roy proposed a grid-based deployment scheme in which keys are predistributed in the sensor nodes using combinatorial designs called transversal designs. As mentioned in [19], grid-based designs have several applications for both military and civilian purposes. They are used in intrusion detection as mentioned in [24] and [18]. Other applications of such a deployment pattern can be used to monitor temperature and pressure in a factory, monitor vehicles in a parking lot, monitor goods in a warehouse, monitor trees in a plantation. To protect commercial confidentiality, sensors may be placed in square grids. In this paper, we consider the grid-based deployment scheme where key predistribution is done according to the Transversal Design TD (k, r). We consider the Lee sphere while calculating the connectivity ratio and resiliency. We study the connectivity and resiliency of the network taking the Lee distance into account. The importance of such analysis of Lee distance lies in the fact that we can change the Lee distance according to power requirements.
Given any kind of deployment, the key predistribution techniques may be randomized, deterministic, or hybrid. Key predistribution in sensor networks was first discussed in by Eschenauer and Gligor in [9]. Other key predistribution schemes were discussed in [5, 8, 13–15, 23]. For application of combinatorial designs in key predistribution, one may refer to [2, 4, 16, 17, 20]. In particular, in [16] Lee and Stinson transversal designs for key predistribution has been presented that has been extended later in [4] by Chakrabarti, Maitra, and Roy.
We consider r2 blocks (identify them as sensor nodes) of the TD which are placed on a deployment grid of dimension r × r. The connectivity of the network is then analyzed taking into account the Lee distance. The block indexed by (i, j) is placed in the (i, j) th location of the grid. We give a comparison of our scheme with that given by Ruj, Maitra, and Roy in [19]. We show how the connectivity ratio changes with the change of the Lee distance and number of keys in each node. The main idea where our proposal differs from the scheme given by Lee and Stinson [16] in that in their scheme sensor nodes are scattered randomly on an unknown geometry unlike our model where we consider a known grid based deployment.
The rest of this article is organized in the following way. In Section 2, we define basic concepts. In Section 3, we calculate the connectivity ratio (the fraction of nodes that a given node can communicate with within the Lee distance). For interior nodes we calculate the exact number of nodes with which it can communicate, for any given Lee distance. In Section 4, we study the resiliency of the network. We give two parameters for resiliency and find a tight theoretical bound for the first parameter and present experimental results for the second. We conclude in Section 5 with some open problems.
Preliminaries
X is a set of kr elements (varieties), G = {G1, G2, …, Gk} is a family of k sets (each of size r) which form a partition of X, A is a family of k-sets (or blocks) of varieties such that each k-set in A intersects each group Gi in precisely one variety, and any pair of varieties which belong to different groups occur together in precisely λ blocks in A.
We denote a transversal design with λ = 1 as TD(k, r). It can be shown that if there exists a TD(k, r), then there exists a (v, b, r, k) design with v = kr, b = r2.
Let us now explain X, A in a transversal design TD(k, r).
X = {(x, y): 0 ≤ x < k, 0 ≤ y < r}, For all i, Gi = {(i, y): 0 ≤ y < r}, A = {Ai,j: 0 ≤ i < r & 0 ≤ j < r}.
We define a block Ai,j by
We consider an r × r grid such that there are r2 points of intersection. For our purpose, we take a prime power r. We map the r2 blocks to the r2 sensor nodes and place block Ai, j at the location (i, j) of the grid as shown in Fig. 1a. We represent the node at (i, j) by ni, j. The varieties are mapped on to the secret keys in the sensor nodes. Thus we establish a correspondence between TD(k, r) and the placement of sensor nodes on a r × r square grid. Note that any two blocks have either no key or one key in common and the algorithm to check whether the two nodes actually share a common secret key is efficient (see [16] for more details).

A 7 × 7 grid with k = 3, ρ = 2. The physical neighbors of the node at (3, 3) occur along the dark lines and the key sharing neighbors are marked by crosses.
The sensor nodes can carry on effective communication only inside a particular range called the Radio Frequency (RF) range. The RF range with respect to a particular point is actually a circular region with center as that point and some radius around that. The Manhattan distance between two points is the sum of the horizontal and vertical distance between the points.
Consider a square grid (as shown in Fig. 1a). A Lee Sphere [1] of radius ρ centered at a given point P consists of the set of points that lie at a Manhattan distance of at most ρ from P. ρ is called the Lee distance. The triangle inequality implies that the Manhattan distance between two nodes is greater than the Euclidean distance. This implies that all the nodes within the Lee sphere of radius ρ centered at a point P are also contained in the RF region of radius ρ centered at P. We see that a Lee sphere is a better approximation than a square RF region. (As given in Fig. 1a and b). We assume that two nodes can communicate with each other provided they are within Lee distance and have a common key.
Definition 1. Physical neighbor
For a given node a located at (i, j) and a given Lee Distance ρ, a node β (≠ α) located at (i′, j′) is said to be a physical neighbor of α, if β is within the Lee sphere of radius ρ centered at α. Mathematically, |i − i′| ≤ p and |j − j′| + |i − i′| ≤ p.
Note that the maximum number of physical neighbors is 2ρ(ρ + 1). For nodes at (or close to) the boundary, the number of physical neighbors is less.
Definition 2. Key sharing neighbor
For a given node a located at (i, j) and its physical neighbor γ (≠ α) located at (i′, j′), γ is said to be a key sharing neighbor of α, if γ has a key common with α.
We now present the key exchange protocol between two sensor nodes. We consider a r × r grid, where r is a prime power, such that each node contains k keys. The Lee Distance ρ is small for practical purposes and can be assumed to be much less than
Connectivity Analysis
In this section we calculate the number of nodes within Lee distance which share a common key with a given node.
Fix a node α located at (i, j) and Lee distance ρ. Consider the set
We call a node ni,j an interior node (not around the boundary), if i ≥ p, (r- 1 - i) ≥ p, j ≥ p, (r − 1 - j) ≥ p. For all the interior nodes ni, j,
Definition 3. Connectivity Ratio
The connectivity ratio
We calculate the value of connectivity ratio for an interior node.
We give the value of
Note that the key (x, y) occurs in nodes n0, y, n1, y-x, …, nn-1, y-x(n-1) mod r.
The node ni, j contains the keys (x, y = xi + j mod r) where 0 ≤ x < k. By Eq. (3), if n i + t, j′ is a key sharing node of ni,j, then j′ = (y - x(i + t)) mod r. So j′ = (j - xt) mod r. The key sharing neighbors of ni, j which share the key (x, y) are the following: ni+1,j-x, ni+2,j-2x, …, n i+t, j-xt and ni-1, j+x, ni-2, j+2x, …, n i-t, j+xt .
To find (ni′,j′ the key sharing neighbors of ni, j, we refer to the Fig. 2. We find the key sharing neighbors in the four quadrants. The following cases arise.

A n × n grid showing the four types of neighboring nodes.
Case a. When i′ < i, we consider the nodes (i − 1, j + x), (i − 2, j + 2x), …, (i - t, j + tx), where 0 ≤ x ≤ k − 1.
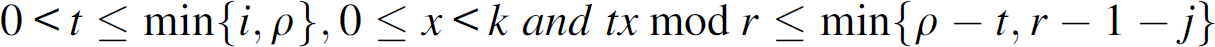
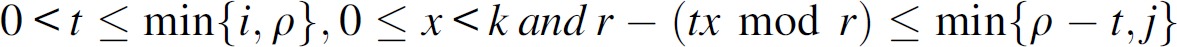
If j ≤ j′ (when the neighboring nodes are in quadrant I), then the following conditions must be satisfied.
If j > j′ (when the neighboring nodes are in quadrant II), then the following conditions must be satisfied.
Case b. When i′ > i, we consider the nodes (i + 1, j - x), (i + 2, j − 2x), …, (i + t, j - tx), where 0 ≤ x ≤ k − 1.
If j ≥ j′ (when the neighboring nodes are in quadrant IV), then the following conditions must be satisfied.
If j < j′ (when the neighboring nodes are in quadrant III), then the following conditions must be satisfied.
Now we consider an interior node ni, j. We find the key-sharing neighbors of ni, j. We consider the neighbors in the four quadrants. Since r - i − 1 ≥ ρ, r - i − 1 ≥ ρ - t, and min{r - i − 1, ρ - t} = ρ - t. Hence Eq. (4a) reduces to (6a). Similarly we obtain the other equations, Eqs. (6b), (7a), and (7a) from (4a), (4b), (5a), and (5b).
Case a. When i′ < i, we consider the nodes (i − 1, j + x), (i − 2, j + 2x), …, (i - t, j + tx), where 0 ≤ x < k.
If j ≤ j′ (when the neighboring nodes are the quadrant I), then the following conditions must be satisfied.
If j > j′ (when the neighboring nodes are in quadrant II), then the following conditions must be satisfied.
Case b. When i′ > i, we consider the nodes (i + 1, j - x), (i + 2, j − 2x), …, (i + t, j - tx), where 0 ≤ x < k.
If j ≥ j′ (when the neighboring nodes are in quadrant IV), then the following conditions must be satisfied.
If j < j′ (when the neighboring nodes are in quadrant III), then the following conditions must be satisfied.
So, the number of solutions (t, x) satisfying the above Eqs. (6a), (6b), (7a), and (7b) give the number of the interior node ni, j within the Lee distance ρ which share key (x, y).
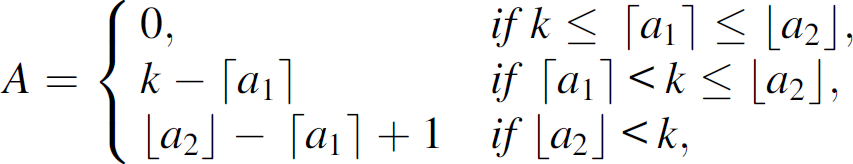
The following lemma is crucial in finding the exact value of
Lemma 1
Let w be a prime such that w ≥ 2T − 1. Then the number of solutions (t, x) satisfying the equation
Proof
When t = 1, three conditions can arise.
When t = 2, three conditions can arise.
When Case (iii) arises, then again consider the three sub cases.
So there are
Note that for
Proceeding as above, t = m, three conditions can arise.
When Case (iii) arises, then again consider the three sub cases.
Note that for
Again for Case (iii c), three cases can arise. Continuing similarly, we notice that if
Note that for
Hence for all values of t, 1 ≤ t ≤ T, there are
We give the example given in [19] to demonstrate the above theorem. We consider the equation
Note that w is a prime and w ≥ 2T − 1. For t = 1, the tuples (1, 1), (1, 2), (1, 3), (1, 4) satisfy (9). So, there are four solutions when t = 1. Here
For t = 2, the tuples (2, 1), (2, 2), (2, 4) satisfy (9). So, there are three solutions when t = 2. When l = 0, ⌈u1⌉ = 1, ⌊u2⌋ = 2. Since X > 2, there are ⌊u2⌋ + 1 − ⌈u1⌉ = 2 + 1 − 1 = 2 solutions. When l = 1, ⌈u1⌉ = 4, ⌊u2⌋ = 6. Since ⌈u1⌉ < X + 1 ≤ ⌊u2⌋, there are X + 1 − ⌈u1⌉ = 4 + 1 − 4 = 1 solutions.
For t = 3, the tuples (3, 1), (3, 3), (3, 4) satisfy (9). So, there are three solutions when t = 2. When l = 0, ⌈u1⌉ = 1, ⌊u2⌋ = 1. Since X > 1, there is ⌊u2⌋ + 1 − ⌈u1⌉ = 1 + 1 − 1 = 1 solutions. When l = 1, ⌈u1⌉ = 3, ⌊u2⌋ = 4. Since X ≥ ⌊u2⌋, there are ⌊u2⌋ − ⌈u1⌉ = 4 − 3 + 1 = 2 solutions. When l = 2, ⌈u1⌉ = 5, ⌊u2⌋ = 6. Since X + 1 ≤ 5, there is no solution. All these three cases provide the overall count.
Using Lemma 1 and conditions (6a), (6b), (7a), and (7b) we arrive at the following theorem.
Theorem 1
and
Proof
When x = 0, (i − 1, 0), (i − 2, 0), …, (i − ρ, 0) satisfy (6a).
For x ≠ 0, we can map (6a) to Lemma 1. Here, w = r, S′ = 1, S = ρ - t, T = ρ − 1, X = k − 1. So the number of solutions satisfying (6a) is given by
Since we are considering the interior node, the number of key sharing neighbors in quadrant IV is the same as quadrant I and the number of key sharing neighbors in quadrant III is the same as quadrant II. Hence the total number of key sharing neighbors of ni, j will be
Note that the value of
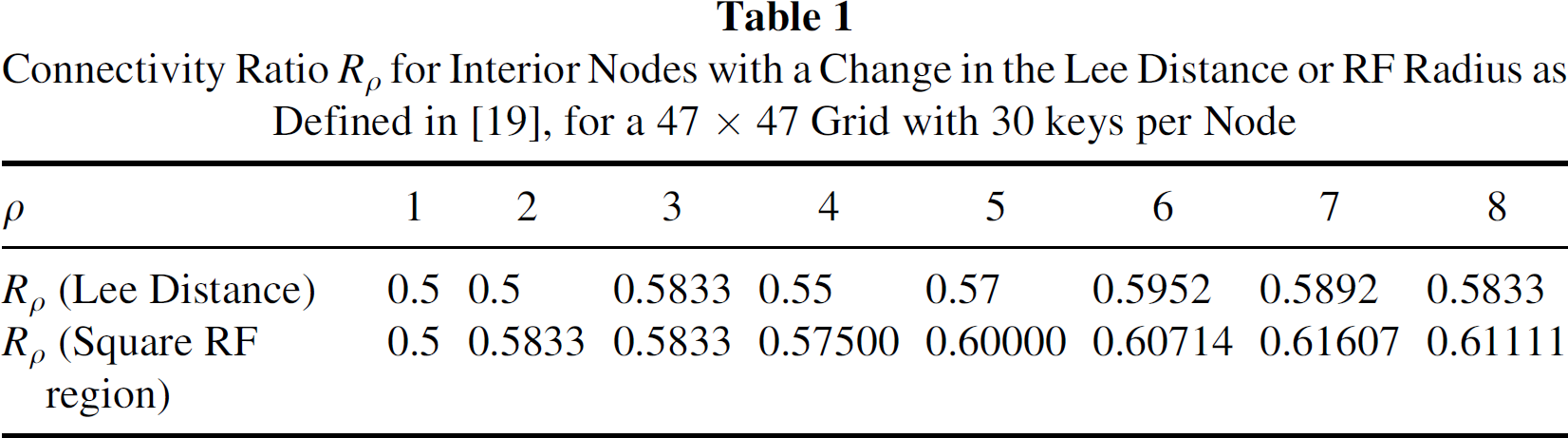
Table 1 compares the connectivity ratio with respect to the Lee sphere are square RF regions for an interior node. Though the connectivity ratio for square RF region is better we can see from the figures that Lee sphere is a better approximation of RF region. Figure 3 presents the connectivity ratio with varying k (the number of keys in each sensor). We see that as the number of keys increases, the connectivity ration increases.
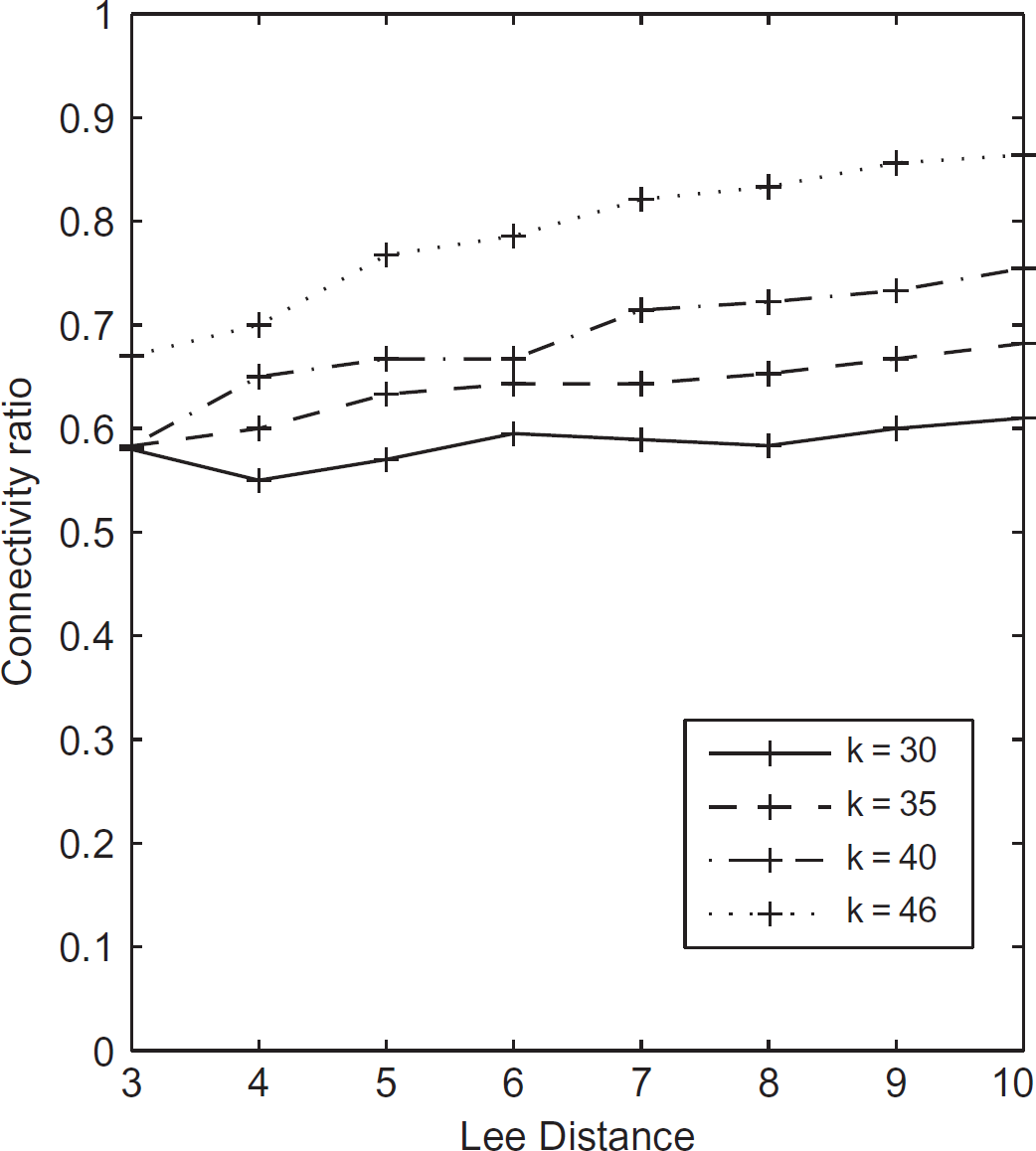
Comparison of connectivity ratio Rρ with changing lee distance ρ and number of keys k on 47 × 47 grid.
Connectivity Ratio Rρ for Interior Nodes with a Change in the Lee Distance or RF Radius as Defined in [19], for a 47 × 47 Grid with 30 keys per Node
Sensor nodes are prone to failure and node capture or compromise. In case of node compromise, all the keys present in the compromised nodes are rendered ineffective. According to our design any two nodes share at most one common key. So all links which communicate via an exposed key are compromised (exposed). We give two parameters of resiliency of a Wireless Sensor Network (WSN), one based on the proportion of links that are broken and the other based on the proportion of nodes being disconnected.
E(s), which is defined as
V(s) which is the probability of a node (which is not among the compromised nodes) being disconnected when s nodes are compromised. A node (which is not among the compromised nodes) is considered disconnected if all the keys in the disconnected node are present in one or more compromised nodes.
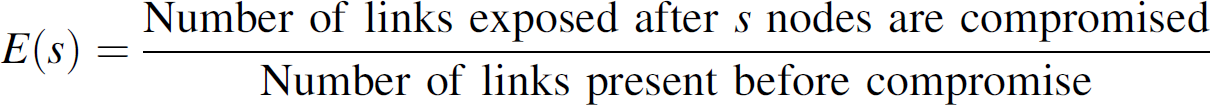
We find an upper bound for E(s) and give some experimental results for V(s).
Estimation of E(s)
Let us denote the total number of links by T. Hence
There are a total of rk keys. If the nodes are compromised such that all rk keys are compromised, then all the links are broken. However, for simplicity we assume that only a small fraction of the nodes are compromised. Suppose s nodes are compromised. Maximum number of links are broken when the nodes compromised have disjoint sets of keys and occur in the interior.
Let the number of links broken when s nodes are compromised be denoted by Cs.
Consider a node ni,j which has been compromised. Let it contain key (x, y). We find the nodes ni′,j′ within Lee distance of ni,j which share the key (x, y). By the analysis of 
and

We consider a key (x, y). Let us denote the number of links compromised when (x, y) is compromised is less than cx. Let the following keys be exposed when s nodes are compromised. (x1, y11), (x1, y12) …, (x1, y1s1), (x2, y21), (x2, y22), … (x2, y2s2), …, (xk-1, yk-11), (x1, y
5-12
), …, (x1, yk-1sk-1). Each key occurs r times. So the number of links compromised is less than
We give the experimental values of E(s) in Table 2.
Experimental Value of E(s) for 100 Runs and Bound for E(s), when Number of Nodes in the Grid is r2, Keys per Node is k and the Lee Distance (RF radius) is ρ

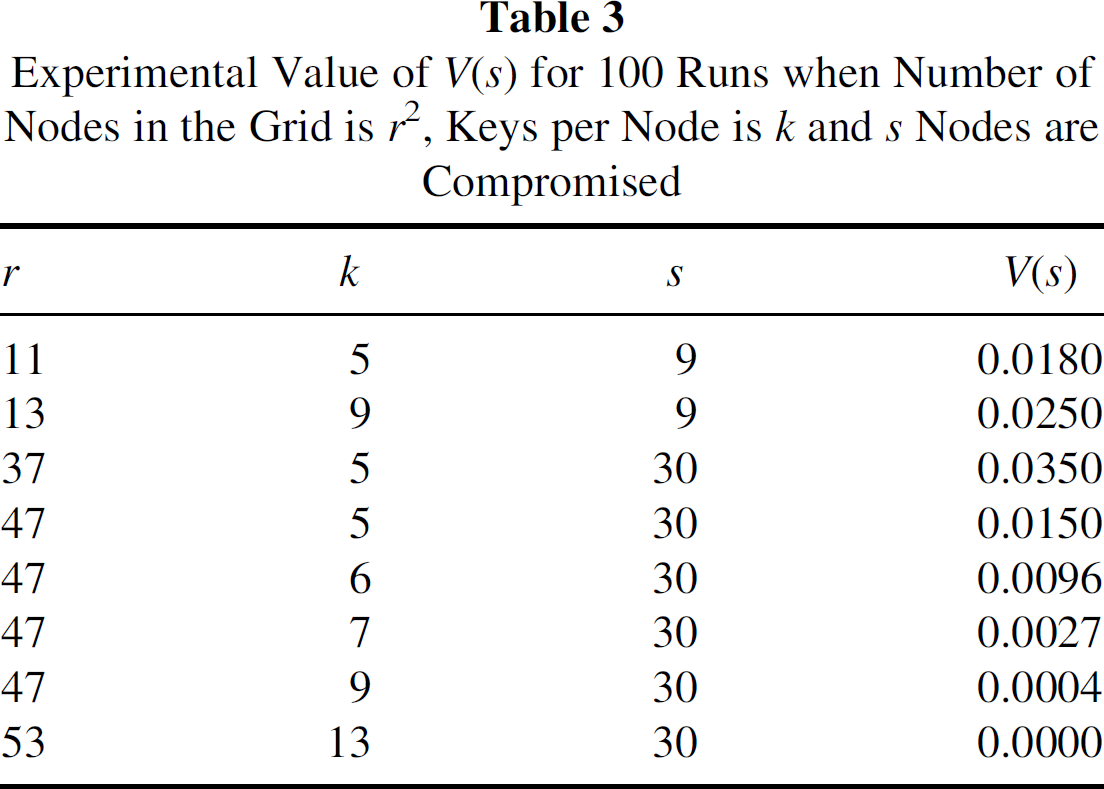
V(s) can be defined as the probability that a node is disconnected, given that s nodes are compromised. Mathematically,

As discussed in [19] if s < k, no node is disconnected. For any node to be disconnected each of its k keys must be present in some compromised node. However, no two or more keys that are present in the disconnected node can be present in any compromised node, since any pair of nodes share at most one key. Hence there is no node which will have all the k keys in the compromised s sensor nodes.
Since the number of nodes disconnected when s nodes are compromised does not depend on the RF radius, we get the same results for V(s) as obtained in [19].
The experimental results for the calculation of V(s) is given in Table 3.
Experimental Value of V(s) for 100 Runs when Number of Nodes in the Grid is r2, Keys per Node is k and s Nodes are Compromised
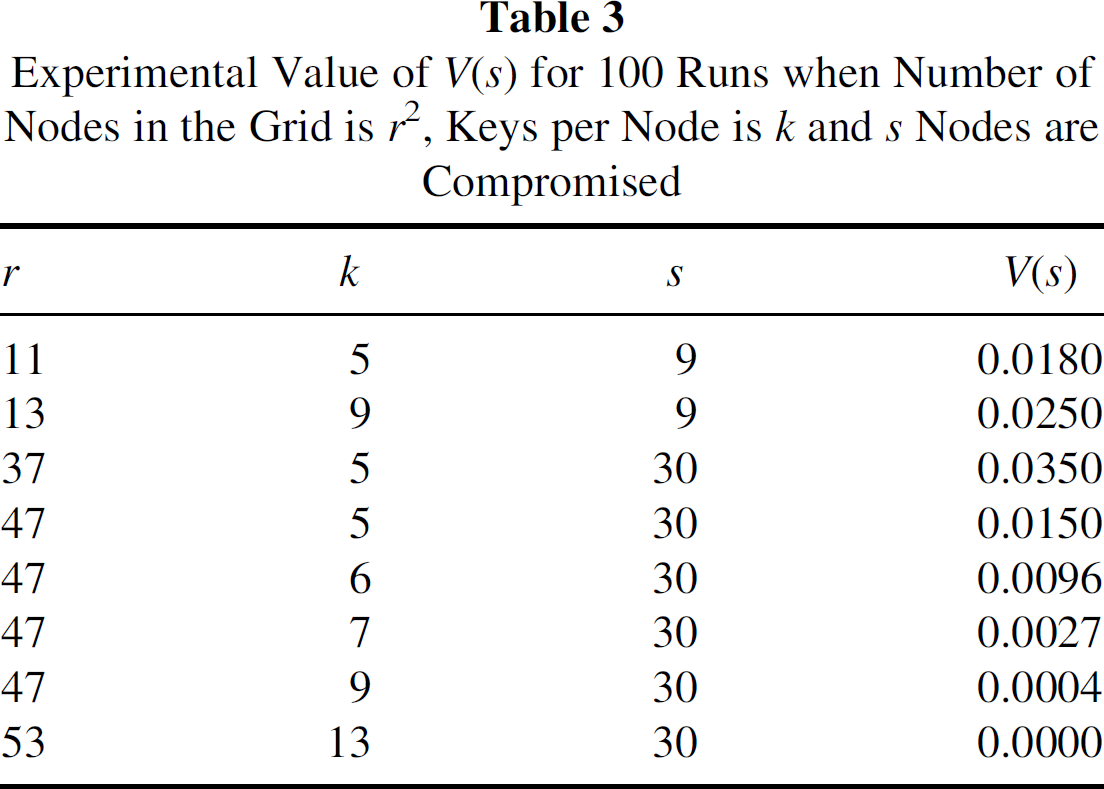
Experimental Value of V(s) for 100 Runs when Number of Nodes in the Grid is r2, Keys per Node is k and s Nodes are Compromised
Key predistribution using deployment knowledge has been studied in [1, 6, 7, 12, 15, 21, 28]. In this article, we use the Lee sphere approximation of RF region as discussed by Blackburn, Etzion, Martin, and Paterson in [1]. In [1] Blackburn, Etzion, Martin, and Paterson proposed a key predistribution scheme for a grid-based deployment scheme. They used combinatorial structures like Costas arrays and Distinct - difference configuration for key predistribution. However, their design is applicable, provided suitable Costas arrays and Distinct-difference configurations exist. The construction of Distinct-difference configuration which matches the desired requirements has not been presented in the paper. In our scheme all nodes are connected by a maximum of two-hop paths. However, using Costas arrays this is not guaranteed. (As the example of 3 × 3 Costas array in [1] shows.) Our design is simple and results in high resiliency in terms of V(s) and E(s) as already mentioned in the previous section. Though the number of groups is chosen to be r2, where r is a prime power, the design discussed above works in all those cases where the dimension n of the grid is not a prime power. This can be done by simply choosing a prime power r > n and neglect the regions which fall out of the n × n grid.
Conclusion and Future Research
In this article, we revisit the grid-based deployment scheme as proposed by Ruj, Maitra, and Roy in [19]. Transversal designs are used for key predistribution. RF region is assumed to be a square of appropriate dimension in [19]. In [1] Blackburn et al. introduced Lee sphere as an approximation of the RF region. We use Lee distance while calculating the connectivity ratio and resiliency of the grid based network as proposed in [19]. The main reason for doing so is that Lee sphere provides a better approximation than the square RF region. This scheme is much better than the scheme proposed by Blackburn et al. mainly because it is very simple to construct transversal designs.
However, in the discussed key predistribution scheme a particular node may share keys with nodes which are not within its Lee distance. This is clearly a underutilization of resources. In future we would like to construct key predistribution schemes such that only nodes which are within Lee distance share keys with one another.