Abstract
In cloning attacks, an adversary captures a sensor node, reprograms it, makes multiple copies, and inserts these copies, into the network. Cloned nodes subvert sensor network processing from within. In a companion paper [2], we show how to detect and remove clones from sensor networks using random key predistribution security measures. Keys that are present on the cloned nodes are detected by using authentication statistics based on key usage frequency. For consistency with existing random key predistribution literature, and ease of explanation, the network in that paper used an Erdos-Renyi topology. In the Erdos-Renyi topology, the probability of connection between any two nodes in the network is uniform. Since the communications ranges of sensor nodes are limited, this topology is flawed. This article applies the clone detection approach from [2] to more realistic network topologies. Grid and ad hoc topologies reflect the node connectivity patterns of networks of nodes with range limits. We provide analytical methods for choosing detection thresholds that accurately detect clones. We use simulations to verify our method. In particular we find the limitations of this approach, such as the number of nodes that can be inserted without being detected.
Keywords
Introduction
Sensor networks deployed in hostile environments are vulnerable to physical attacks; including node cloning. In a cloning attack, an adversary captures a sensor node and copies its state. She reverse engineers the node, reprograms it, makes multiple copies of it, and inserts these copies back into the network. Chan and Perrig [1] explain how clones can falsify sensor data; extract data from the network; and/or stage denial of service attacks. A typical sensor network will contain hundreds or thousands of nodes in a hostile environment. It will not be possible to constantly monitor nodes to detect potential tampering. Therefore it is necessary to develop a security approach for detecting and removing cloned nodes.
In [2] we present a statistical approach for detecting cloning attacks in networks whose security guarantees are based on random key predistribution. In random key predistribution, first introduced in [3], before deployment each node is equipped with a key-ring of
Each node uses its keys as an authentication token. We analyze statistics on how often keys are used for authentication to determine which keys are being used by cloned nodes. Note that node authentication occurs only during network initialization. In this paper key usage refers only to the node authentication process, it does not refer to the number of times a key is used to encrypt or decrypt individual packets in the sensor network.
Each node constructs a Bloom filter [4] of the keys it has in common with its neighbors (i.e., the neighbor's authentication credentials). This Bloom filter is securely transmitted to a server that records key usage data. The use of Bloom filters significantly reduces the traffic volume and provides greater security since keys are not sent over the network. The server creates a key usage histogram from the Bloom filters. An extension of this approach that does not require a centralized collection point is in [5]. We do not present that approach, since it contains complications that are not relevant to determining the clone detection thresholds discussed here. In [2], we derive the probability density function for key usage, and show how the false positive rate
Keys whose use exceeds the threshold value are thought to be used by clones and are ostracized from the network. The key detection protocol succeeds in removing all cloned keys from the network when a high false positive rate
Unfortunately the Erdos-Renyi model is not realistic for wireless sensor networks. It posits that a connection between any two nodes is equally likely, which does not match wireless communication with limited communications ranges. The Erdos-Renyi model is used in the literature [3, 6] because of its simplicity and because it has been widely studied in Mathematics literature [7].
This paper adapts the approach from [2] to grid and
The remainder of this paper is organized as follows. Section 2 discusses the network models under consideration. Section 3 presents the clone detection protocol. Section 4 analyzes the proposed method and explains how we determine a threshold value for the number of times a key may be used. Simulation results verifying our analysis are presented in Section 5. Section 6 gives conclusions and possible future extensions to our research.
Sensor Network Topologies
This section presents two sensor network topologies, which we will use to analyze clone detection for realistic sensor networks using random key predistribution security.
Grid Network Topology
Grid network topologies are regular tessellations of the sensor field. The use of this topology for analyzing sensor networks originates in [8]. When users control node placement, nodes are often distributed in a regular pattern. Grid topology analysis relies on results from percolation theory [9].
In this paper we analyze a two-dimensional rectangular grid. The same approach can easily be adapted to other tessellations, like those in [9]. Every node in the network (ignoring edge effects) has exactly four nodes in its neighborhood. Communications between a node and its neighbors occur only when they share a common key.
Figure 1a shows a 2-dimensional grid of nodes in a 100 by 100 meter square region. The 100 sensor nodes are placed at regular intervals with 10 meters between neighboring nodes. Figure 1b shows the communications links that are established between nodes that use a random key predistribution scheme.
(a) A 2-dimensional grid of nodes and (b) communications links where neighbors share a key.
In
[10]'s ad hoc model assumes that two nodes within range of each other communicate with probability 1. We allow nodes within range of each other to communicate with probability 
Figure 2a shows an example distribution of nodes in a square region. Again, 100 sensor nodes are placed in a 100 by 100 meter region. Figure 1b shows the communication links enabled by random key predistribution.

(a) Random distribution of sensor nodes and (b) its associated ad hoc network.
Unlike the Erdos-Renyi topology, nodes can not communicate if they are separated by a distance greater than the radio range
As shown in [2], cloning attacks can be detected by analyzing key usage statistics. We use the fact that each node randomly selects
When clones are inserted into the network this key usage distribution is changed, since the cloned keys are present on a greater number of nodes than normal. The keys are therefore used more frequently than keys that have not been cloned. By collecting key usage statistics we can determine which keys have been cloned. Note that we consider only the use of keys to create a communications link between two nodes during network initialization.
The sensor network has a pool of
We use counting Bloom filters to collect key usage statistics. Each node makes a counting Bloom filter of the keys it uses to communicate with neighboring nodes. It appends a random number (nonce) to the Bloom filter and encrypts the result using
Keys used too often are considered cloned.
Threshold Detection
A sensor network has
Theorem
The expected number of times a key is used for making connections in the network is:

with variance:

(Note that 
In the case of Erdos-Renyi networks,


The expected number of times a key that is on exactly 
Since the neighborhood size is 
Because key 
For the grid network 
Figure 3 shows simulation results and predicted values for mean key usage and variance as network size increases for grid networks.
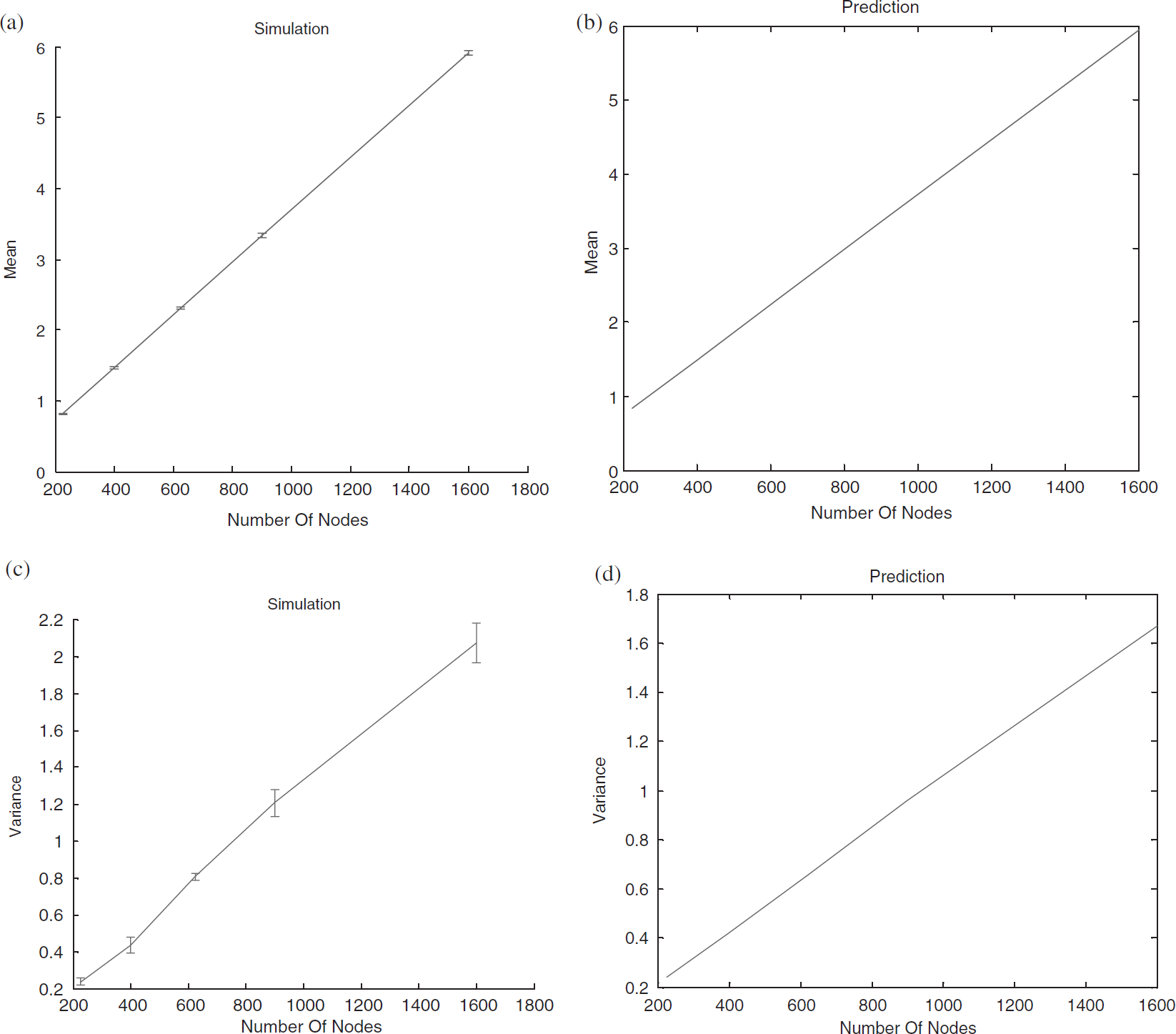
Mean number of times a key is used to create communications links in a grid sensor network: simulation (a) and analytical prediction (b). The associated variance: simulation (c) and analytical prediction (d). For all the graphs,

Where
Since all nodes have the same probability pr of landing in the neighborhood, the number of nodes in the neighborhood will follow a binomial distribution. The probability that any node has i nodes in its neighborhood becomes:

The expected degree of a node in the network is therefore (where pc is given by (1)):
In practice, nodes at a distance of

Mean number of times a key is used to create communications links in an
We determine whether or not a key is cloned by comparing a normal curve or the distribution from Theorem with likelihood less than false positive rate
The value
For an ad hoc sensor network of 900 nodes, key pool size P 1000, key ring size k 50, and range r 10 m in a 100 m by 100 m region, Table 1 gives threshold values for various settings of
Key Use Thresholds for Ad Hoc Networks

Figure 5 compares analytical predictions of the number of keys (out of 1000 keys) detected by the algorithm as clones for different values of false positive rate

Number of keys detected as cloned in an
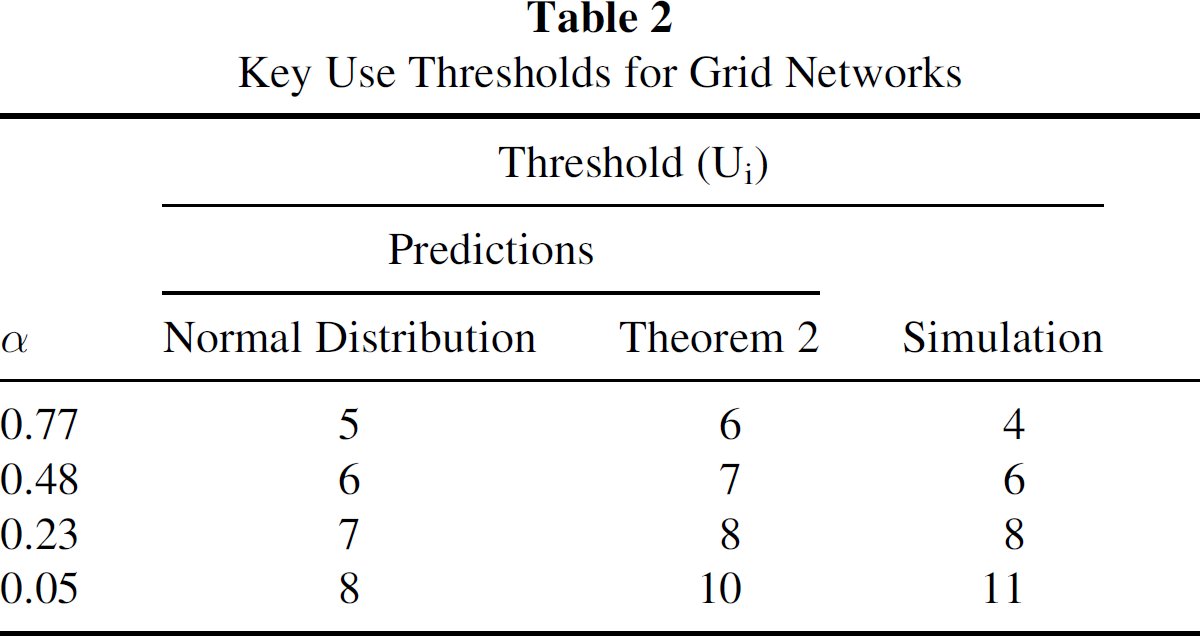
Table 2 gives threshold key use values for varying settings of the accepted false positive rate
Figure 6 gives analytical predictions of the number of keys (out of 1000 keys) detected by the algorithm as clones for different values of false positive rate

Number of keys detected as cloned as the number of clones inserted into the
Key Use Thresholds for Grid Networks
This section gives simulation results to verify our clone detection approach. We present results for both grid and
Figure 7 plots the maximum component size of the network versus the false positive rate

Maximum component size as the false positive rate
Figure 8 shows simulation results for the number of keys (out of 1000 keys) that are detected as clones for different values of

Number of keys detected as cloned as the number of clones inserted into the network varies. for (a)
Figure 9 shows the number of cloned keys detected for different

Number of cloned keys detected versus
Figures 10 and 11 present the results of running our clone detection protocol for different values of the false positive rate

Number of cloned nodes still connected to the grid network after running the protocol as

Number of cloned nodes still connected to the
The protocol is more effective for the
This paper focuses on sensor network cloning attacks where an adversary captures a sensor node, reprograms it, and adds multiple modified copies of the node to the network. We examine the feasibility of our clone detection protocol, first presented in [2] for
We detect cloned keys by looking at how often they are used to establish connections between nodes; this is proportional to the number of nodes that possess the key. Inserting clones into the network skews this distribution. Cloned keys are present on more nodes and are used more often than keys that have not been cloned. The number of cloned keys detected increases with the false positive rate
Our ability to detect and remove clones increases with the number of clones in the network. Our approach does not require any cooperation from the cloned nodes. In [2], we show that the best strategy for the clones is to ignore the protocol. Active tampering with the protocol can only increase the likelihood that the clones will be detected.
We show how to quantify the number of clones that will not be detected for various number of clones inserted into the network. This is useful, in that it indicates a number of clones that may be present even if this protocol is used. Sensor network applications and security measures should be designed in a manner that can tolerate that many malicious participants.
One drawback of the presentation here and in [2] is the use of a centralized authentication mechanism. Centralized authentication using a base station is undesirable. It introduces a single point of failure into the network and can become a significant system bottleneck. It also violates random key predistribution's support of network self-organization, which is a very appealing aspect of the approach. Using multiple key servers in [5] eliminates the need for having a centralized authentication mechanism. That approach is orthogonal to the issues addressed in this paper.
