Abstract
IoT-Fog computing provides a wide range of services for end-based IoT systems. End IoT devices interface with cloud nodes and fog nodes to manage client tasks. Critical attacks like DDoS and other security risks are more likely to compromise IoT end devices while they are collecting data between the fog and the cloud layer. It’s important to find these network vulnerabilities early. By extracting features and placing the danger in the network, DL is crucial in predicting end-user behavior. However, deep learning cannot be carried out on Internet of Things devices because to their constrained calculation and storage capabilities. In this research, we suggest a three-stage Deep Hybrid Detection Model for Attack Detection in IoT-Fog Architecture. Improved Z-score normalization-based data preparation will be carried out in the initial step. On the basis of preprocessed data, features like IG, raw data, entropy, and enhanced MI are extracted in the second step. The collected characteristics are used as input to hybrid classifiers dubbed optimized Deep Maxout and Deep Belief Network (DBN) in the third step of the process to classify the assaults based on the input dataset. A hybrid optimization model called the BMUJFO (Blue Monkey Updated Jellyfish Optimization) technique is presented for the best Deep Maxout training. Additionally, the suggested model produced higher accuracy, precision, sensitivity, and specificity results, with values of 95.26 percent, 94.84%, 96.28%, and 97.84%, respectively.
Introduction
In the development of computers, IoT [17,27] is regarded as a paradigm that is fast developing. IoT has significantly advanced in a variety of technology domains over the last several years. IoT [21] is a system of interconnected smart devices including sensors that communicate with one another online. IoT is a significantly emerging phase in the currently developing world. It is designed with a variety of connected technologies, including smart grid, surveillance, smart cars, and smart healthcare. The security requirements in an IoT network typically manifest as network anomalies [23], particularly when there is a divergence from the regular flow of network data. Attacks such as distributed denial-of-service (DDoS) and probing attacks are examples of such unusual network flows. A botnet is made up of a higher number of hacked network nodes [4] or systems that are controlled by malicious individuals. These nodes or systems are used to carry out a variety of assaults.
By using fog computing [11,24], IoT devices are brought closer to the storage and processing resources. In IoT applications, fog computing develops as the demand for quick-response tasks increases. Fog Computing [6] is a decentralized network that is sensitive to context-awareness of information connected to data sources, including response time, region, resources dispersed by the services, etc. It is made available, either physically or virtually, at the network’s edge node. To provide services with lower latency as well as less network bandwidth usage, fog computing [7], which is a distributed decentralized approach, has evolved and lies between both the cloud as well as client devices. The heterogeneity, complexity, lack of hardware resources, and IoT systems accessibility [9,18] on a worldwide scale have made IoT security difficult. To find network assaults, researchers had employed machine learning (ML) algorithms like Decision Tree (DT), Random Forest (RF), Support Vector Machine (SVM), Bayesian network, and K-Means. The trained models for machine learning techniques are built using both legitimate and malicious traffic. These strategies are classified as supervised, unsupervised, or semi-supervised based on the learning process. Due to its various levels of processing, deep learning [5] is preferred over machine learning for large amounts of data. The binary classification of typical and abnormal activity, as well as multi-label categorization provided by deep learning, which has been employed in categorizing various attacks with a high detection rate, is sent to the cloud for a node’s behavioral update. The fog computing concept is proposed to help cloud computing handle data for IoT applications. Nevertheless, privacy, security, and storage are only a few of the difficulties that fog computing must overcome.
Research questions
For what purpose Z-score normalization is used?
Why feature extraction stage is used?
For what purpose hybrid classifier is used?
So we have developed a Deep Hybrid Detection Model for Attack Detection in IoT-Fog Architecture with the below contributions:
To preprocess the input data, improved Z-score normalization is carried out. Additionally, during the feature extraction stage, enhanced MI-based features are extracted with other sets of features.
To classify detected output, a hybrid attack detection model is created by integrating models like optimized Deep Maxout and DBN.
The BMUJFO model is introduced to modify the ideal weights, providing an improvement in classification accuracy, for the Deep Maxout model’s best training.
The research work structure is: Section 1 describes the introduction to the attack detection model. Section 2 offers a literature survey. Section 3 describes the proposed model. Section 4 describes the result and discussion. Section 5 describes the conclusion.
Literature review
In 2020, Ahmed Samy et al. [25] developed a detailed architecture for detecting assaults that use distributed, reliable, and high detection rates to find various IoT cyber-attacks. The proposed scheme’s distributed nature, high processing capabilities, and close proximity to edge devices enable it to design an attack detection mechanism on fog nodes. Six Deep Learning (DL) designs were examined to find the optimal DL model.
In 2022, Surya Pavan Kumar Gudla et al. [13] suggested a fog-based IoT attack prognostication algorithm based on DL models. The system is divided into three tiers: a secure fog tier, a smart sensing tier, and a cloud tier. After that, several deep learning models, name Long Short Term Memory (LSTM), Deep Neural Multilayer Perceptron (DNMLP), Bi-directional Long Short Term Memory (Bi-LSTM), CNN + LSTM, Gated Recurrent Unit (GRU), and HEM, were evaluated to predict the model that would be installed at the fog nodes with the highest degree of accuracy. The Long short Term Memory Deep Learning (LSTMDL) classifier outperforms nature in classification tasks, with performance accuracies of 99.12%, 99.88%, 94.11%, and 99.70% in tests using the corresponding datasets.
In 2020, Bhuvaneswari Amma N.G. and S. Selvakumar [22] employed a VCDL technique to offer an anomaly detection framework in a fog environment. If the communication could be routed among the nodes within the fog layer for processing, the anomaly detection method might be scalable. This was accurately captured by the Vector Convolutional Deep Learning (VCDL) technique, which dispersed the IoT traffic training and performed calculations in the fog nodes. The fog layer’s master node provided the parameters needed for training. IoT traffic is further classified by the suggested anomaly identification system as either regular or attack traffic before being sent to the cloud for assault mitigation.
In 2020, Syed Rameem Zahra and Mohammad Ahsan Chishti [28] suggested a real-time FLFSIoT. In Fuzzy Logic and Fog based Secure Architecture for IoT (FLFSIoT), fuzzy logic is used to lessen the risk of an edge node’s participation in a single crisp cluster and to recognize several classic attacks. By minimizing latency and other problems, the Fog-based IoT design has been leveraged to make FLFS IoT fundamentally more secure than cloud-supported IoT. As a result, this work incorporates the benefits of fog computing and fuzzy logs into the development of a universal solution to the IoT security challenge. When FLFSIoT’s effectiveness was tested against DDoS as well as colluding attacks, it was found that its results were more accurate than those of the previous benchmarks.
In 2022, Surya Pavan Kumar Gudla et al. [14] suggested deep intelligent distributed denial of service attack detection scheme (DI-ADS) for IoT applications that rely on fog. A DL is primarily used by the framework to identify DDoS attacks on the network. The fog node’s calculation module, which forecasts the final IoT device behavior, has the DL installed. The effectiveness of DNMLP, LSTM, and more traditional ML models like SVM, LR, k-NN and RF are compared to choose the optimal DLM model for the fog layer. DNMLP was considered for implementation at the fog layer in the suggested scheme since it outperforms nature in the identification of DDoS attacks.
In 2020, Prabhat Kumar et al. [16] developed a distributed ensemble model-assisted IDS employing fog computing, combining first-level individual learners from KNN, NB, as well as Gaussian XG Boost. The prediction outcomes from the first level were employed by RF for the final prediction at the second level. The UNSW-NB15 dataset and a real IoT-based dataset, DS2OS, were utilized in this study to test the efficiency of the suggested approach.
In 2021, Syed Rameem Zahra and Mohammad Ahsan Chishti [29] presented a GLSF2IoT method built on the idea of “zero trust,” or the idea that everything should be regarded with suspicion. Although Fuzzy Logic was previously used to minimize uncertainty, the Fog-IoT design of GLSF2 IoT makes it fundamentally superior to cloud-IoT. After it has been recognized, to stop the malicious behavior from spreading to other devices, GLSF2IoT instantly limits network access to the IoT device that started it.
In 2021, Deepak Kumar Sharma et al. [26] suggested a design for IoT networks that detect anomalies in the fog layer. The approach, which was dependent on the CRPS measure and used only one variable, was typical of statistical algorithms. As a result, they offered a method for using many variables and explained why it was necessary in a heterogeneous system such as the IoT. In Table 1, the strengths and weakness of the existing system are given.
In 2023, Manoharan et al [20] have developed deep learning approaches for effective dengue monitoring, this article primarily addresses the aforementioned issues. With the help of IoT devices, a framework for coordinating illness monitoring is built, and the fog-cloud model effectively creates and sends reports to the healthcare institutions.
Strengths and weakness of existing systems
Strengths and weakness of existing systems
IoT has several benefits, but it also has three key issues: data gathering, data transfer, as well as data security. Authorization became a crucial problem in the IoT system as the variety of connected devices to the Internet increased. The following are some of the main challenges encountered in the examined work: In the LSTM model [25], it is necessary to evaluate the suggested attack detection against unsupervised DL models in a distributed computing setting with various datasets. Using multiclass classification [13], the attack prediction must be improved. The class imbalance problem is the main issue in the VCDL approach [22]. Passive attacks are more challenging to detect [28]. To identify specific attacks [14], it is necessary to combine multiclass classification with updated datasets. To improve the security of IoT [16], it is required to create a prototype that validates the formal security characteristics of the overall architecture. Work must be expanded to account for hardware attacks [29]. Detecting anomalies in real-time is challenging [26].
Proposed deep hybrid detection model for attack detection in IoT-fog architecture with improved feature set and optimal training
System model of IoT-fog architecture
Typically, data is routed from the edge layer to the upper layers using smart gateway technology (e.g., fog and cloud). The distance between the cloud and the edge layer makes data analysis time-consuming and subject to delays. Therefore, this procedure is inappropriate with sensitive data that demands a quick response. By dispersing the cloud to be nearer the data sources, fog computing is utilized to address these issues. As a remedy for the issues with cloud computing, CISCO proposed fog computing in 2012. The design of fog computing in an IoT network, which is split into three categories: the edge, fog, and cloud layers, is shown in Fig. 1. Many heterogeneous IoT devices, including sensors, security cameras, smart wearables, cars, smart machines, and smart home appliances, are connected at the edge layer. A lot of data are generated by this layer from several sources and activities. Between the cloud and edge layers lies the fog layer. Each fog layer domain includes routers, virtualized fog servers, small data centres, services, and applications. The fog layer is divided into several connected regions. The cloud layer, which corresponds to the layer above, is the core layer of high-performance storage devices and servers. IoT benefits from DL implementation on fog nodes include closer proximity to information-generating IoT devices for sensitive data analysis and decreased latency between data sources and data analysis devices; minimized network bandwidth; processing of both data to be processed on fog nodes and data to be transmitted to the cloud; and assistance for mobility services. Attackers in IoT infrastructure based on fog may come from IoT hardware, protocols, applications, and software. Many device components, including the web interface, storage, and firmware, are susceptible to vulnerabilities via communication routes, associated apps, and software, IoT end device protocols are also vulnerable to security problems and assaults.
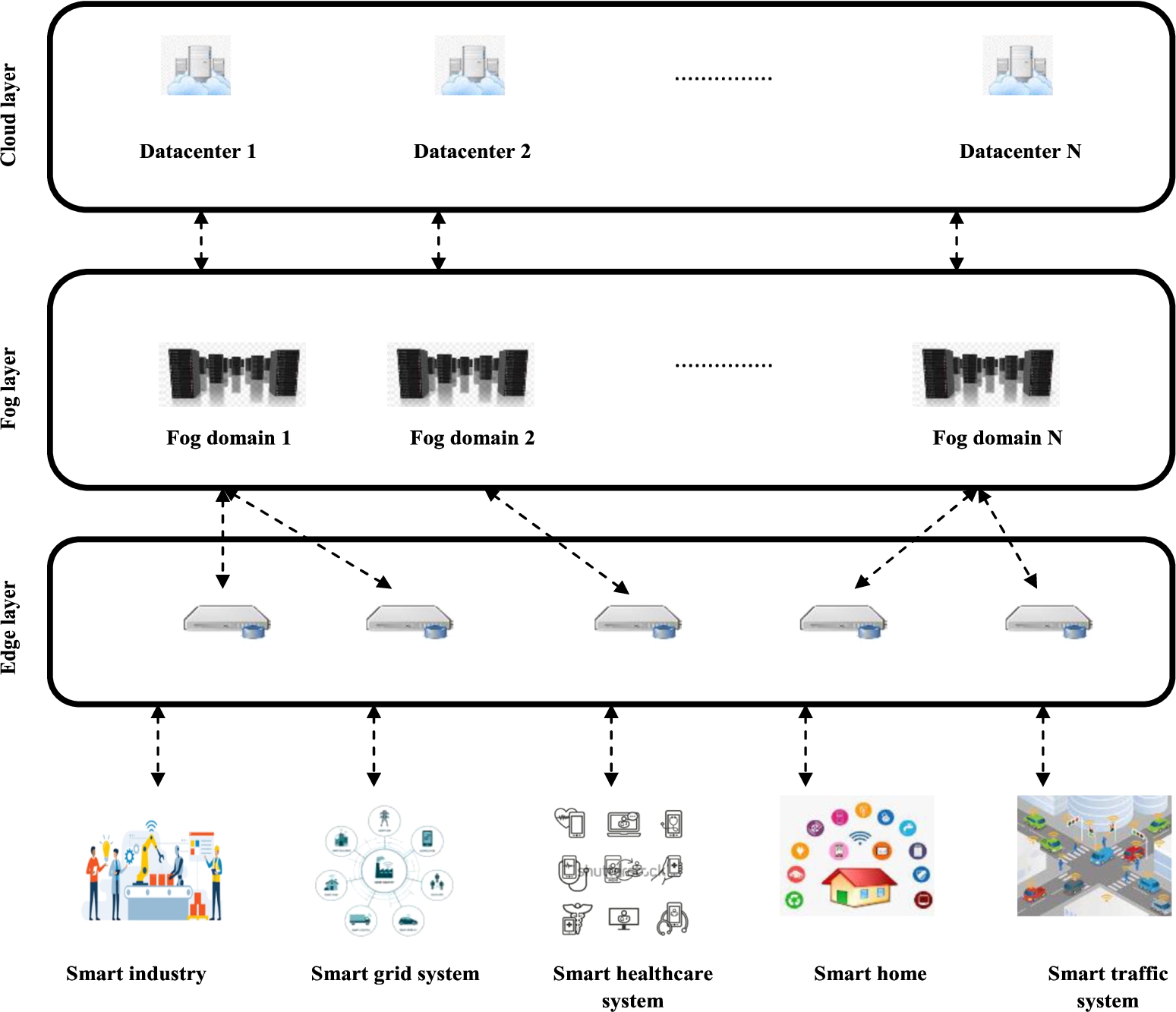
Fog computing based IoT system architecture.
To detect attacks in IoT-Fog computing, a variety of attack detection algorithms have been developed. However, due to IoT device requirements such as dispersion, low latency, resource restrictions, and scalability, obtaining relevant findings is a difficult process. To overcome this challenge, an effective attack detection process named Deep Hybrid Detection Model for Attack Detection in IoT-Fog Architecture is developed with a three-stage procedure including:
Preprocessing
Feature extraction
Attack detection
Figure 2 represents the proposed attack detection model’s overall design.
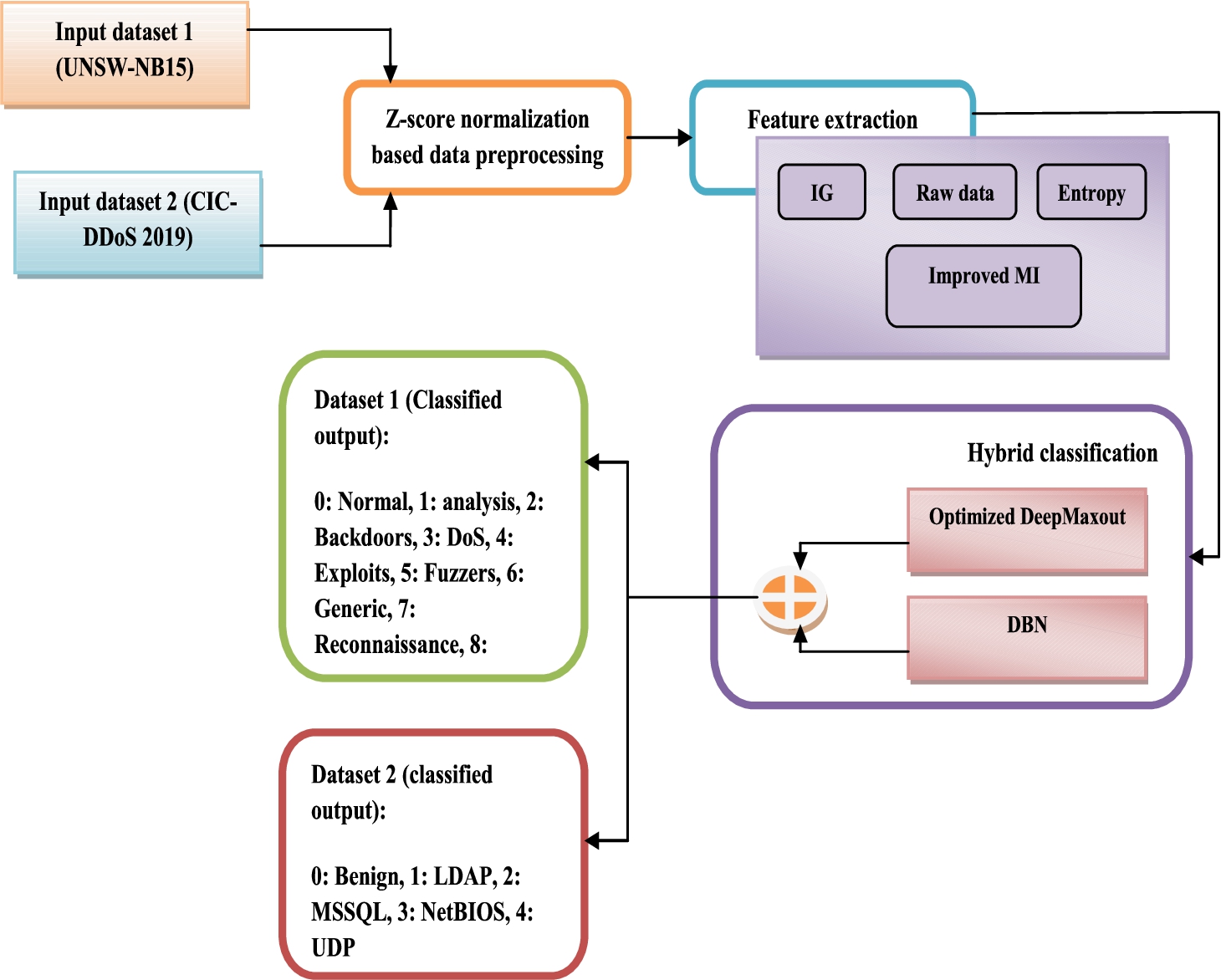
Overall design of proposed attack detection model.
The dataset 1 and 2 are provided as input to the z-score normalization based data processing. Using an updated z-score normalization procedure, the incoming data is pre-processed. The pre-processed data is provided as input to the feature extraction. The feature extraction consists of IG features, raw data, entropy and improved MI. The hybrid classification receives the obtained characteristics as inputs. The hybrid classification consists of optimized deepmax out and DBN. Finally, the result will be detected in the classification stage. A new hybrid optimization approach known as the Blue Monkey Updated Jelly Fish Optimization (BMUJFO) algorithm is introduced for optimizing the DeepMaxout classifier and enhancing classification accuracy.
The initial stage is preprocessing, where input data
Here,
Feature extraction
The second stage is called feature extraction, when a group of features, such as IG, Entropy, Improved MI, and raw data, are derived from the preprocessed data
IG feature [
1
] By dividing a preprocessed dataset corresponding to a specific value of a random variable, IG calculates the decrease in entropy or surprise. A higher IG signifies a collection or collections of samples with lower entropy, resulting in less surprise. For instance, by dividing a preprocessed dataset
Entropy The expected quantity of information that is conveyed by determining the result of a random trial is measured by entropy.In Eq. (5), the entropy formula for a discrete random variable X with n possible results as well as probabilities
Raw data Flow IAT Min, ECE Flag Count, Bwd PSH Flags, URG Flag Count, Fwd Packets/s, ACK Flag Count, CWE Flag Count, act_data_pkt_fwd, Active Min etc. are some of the raw data considered in this work.
Improved MI feature The number of information one can get from a particular random variable given another is measured by a term called MI. Formally, the MI [1] between the random variables X, Y can be written as in Eq. (6), where
The extracted final feature set F is described as follows:
Attack detection
In this phase, the attack is detected by providing the extracted features F as an input to the hybrid classifier such as optimized Deepmaxout and DBN. To achieve comparatively high accuracy in comparison to fundamental algorithms without compromising the interpretability of learning outcomes, we use a hybrid classification method. For optimizing the DeepMaxout classifier and improving the classification accuracy, a new hybrid optimization algorithm named Blue Monkey Updated Jelly Fish Optimization (BMUJFO) algorithm is introduced which is the combination of the BMO [19] and JFO algorithm [10]. Figure 3 shows the hybrid classification model combining Deep Maxout and DBN classifier.
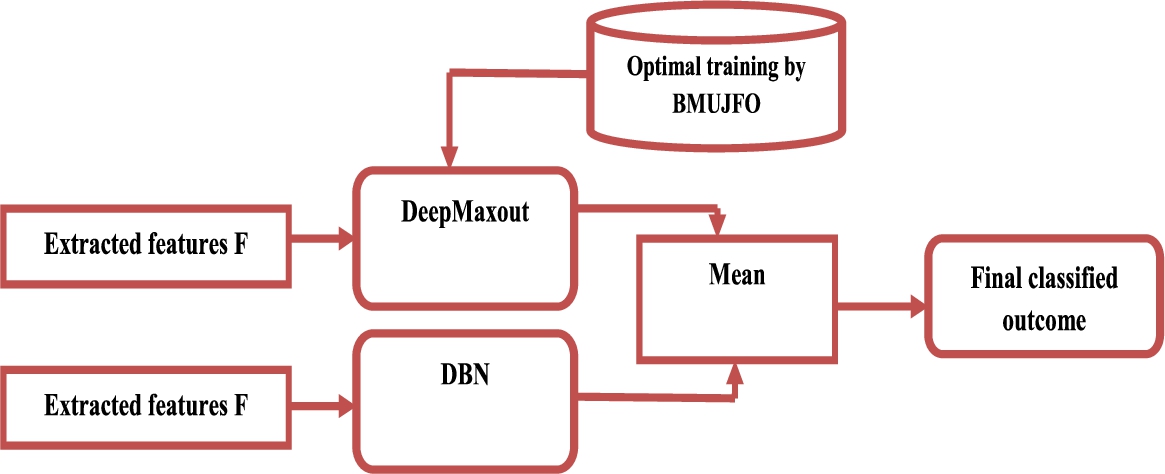
Hybrid attack detection model combining DeepMaxout and DBN model.
Optimized DeepMaxout [
12
] A max out method is a new form of activation strategy that uses the max out unit in a feed-forward design. The max out unit returns the highest value provided in Eq. (8) and accepts the output of multiple linear functions as input. Here
DBN model [
8
] DBN is a type of DNN made up of layers of the dependent variable with connectivity between the layers and not between the units inside every layer. Deep layered networks use DBN to solve problems with traditional neural networks. In more complex settings, DBN is used in replacement of deep feedforward networks or indeed CNN. They have the advantage of requiring less computation. It is less prone to the vanishing gradients problem than feed-forward neural networks since its computational difficulty rises in proportion to the variety of layers. Let
Here,
Finally, the predicted scores of the optimized DeepMaxout classifier and DBN classifier were averaged to get the final detected outcome. For dataset 1 (UNSW-NB15), the detected outcome is of 10 classes. For dataset 2 (CIC-DDoS 2019), the detected outcome is of 5 classes.
BMUJFO algorithm for optimal DeepMaxout weight
Proposed BMUJFO concept BMUJFO is a ground-breaking meta-heuristic algorithmic optimization that is based on how well blue monkey swarms function in nature. To overcome the drawbacks such as falls into local optima and improve the convergence speed the proposed model is used. The meta-heuristic optimization techniques are being more widely used to solve complex problems in a variety of fields. They may be applied to a variety of issues in a variety of fields because they (i) rely on straightforward ideas and are simple to implement; (ii) don’t need to know the gradient of the objective function; (iii) can avoid local minima; and (iv) can be used to address a wide range of issues. Advances in computer processing power have sped up the development of meta-heuristics because its use is dependent on computers. In order to create a hybrid algorithm, hybridization attempts to reduce any significant disadvantages while combining the benefits of each method. In general, the results of hybridization typically offer some gains in either computing accuracy or speed.
This is a presentation of the BMUJFO algorithm and its mathematical model:
Group division The BMUJFO model mimics blue monkey behavior. In order to imitate these interactions, each group of monkeys had to go across the search area. When broken into groups, stronger and farther-reaching monkeys start searching for food sources outside the conventional range of their vision. Cercopithecusmitis appears to have little or no interaction with its young males. It is important for young male cercopithecusmitis to travel outside as soon as possible due to its territorial nature. If they are successful in overcoming, they will become family leaders, able to provide food, shelter, and socialization for young males.
Position update Continuity Eqs (12) and (13) define the behavior of updating each blue monkey’s location based on the new location in each group, where
Equating Eq. (12) and Eq. (14), we get
Moreover, the model Eq. (18) as well as (19) are utilized to update the blue monkey’s offspring, where
Figure 4 shows the flowchart of the proposed model.
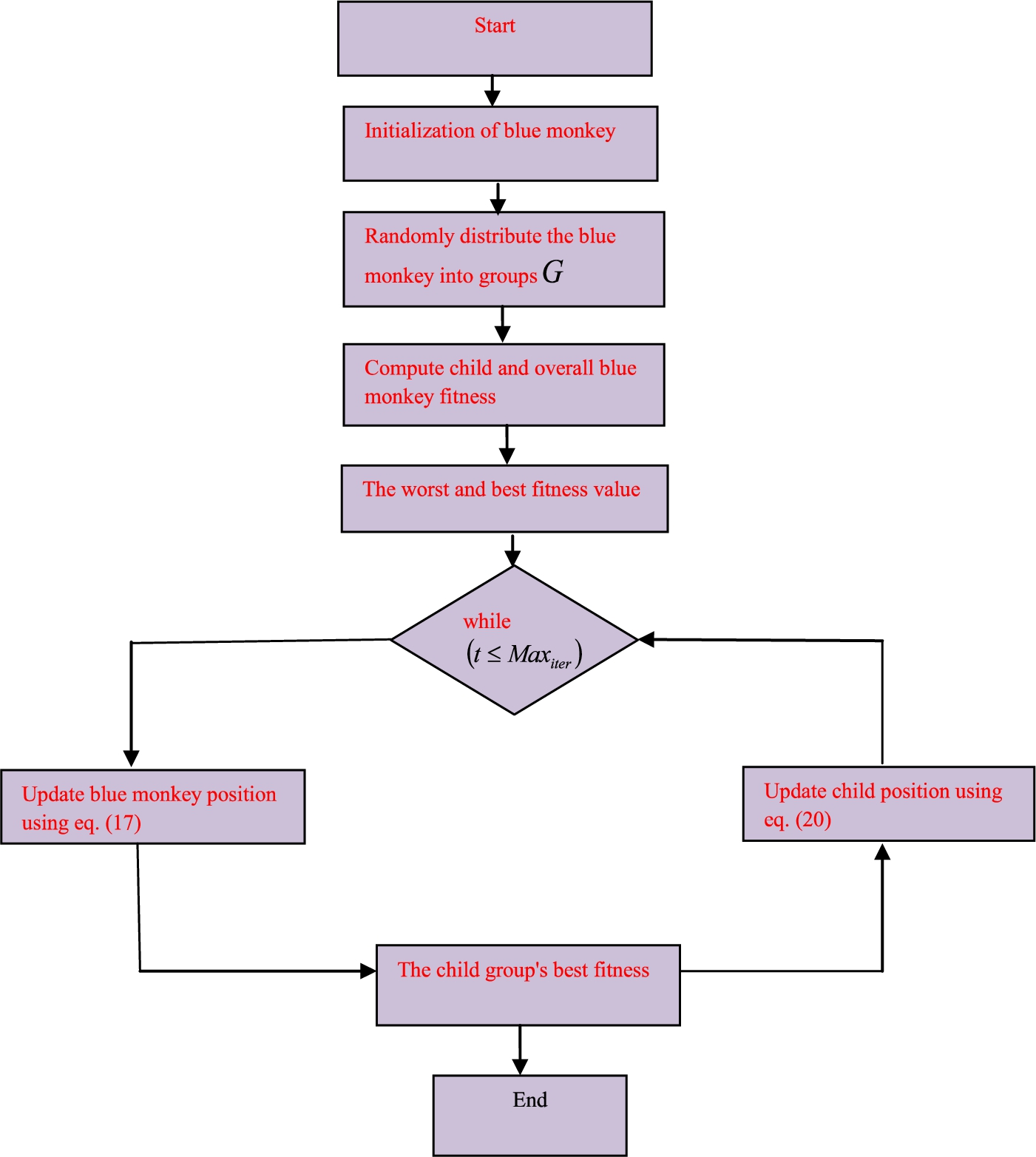
Flowchart of the proposed model.
Algorithm 1 shows the flowchart of proposed BMJUFO.
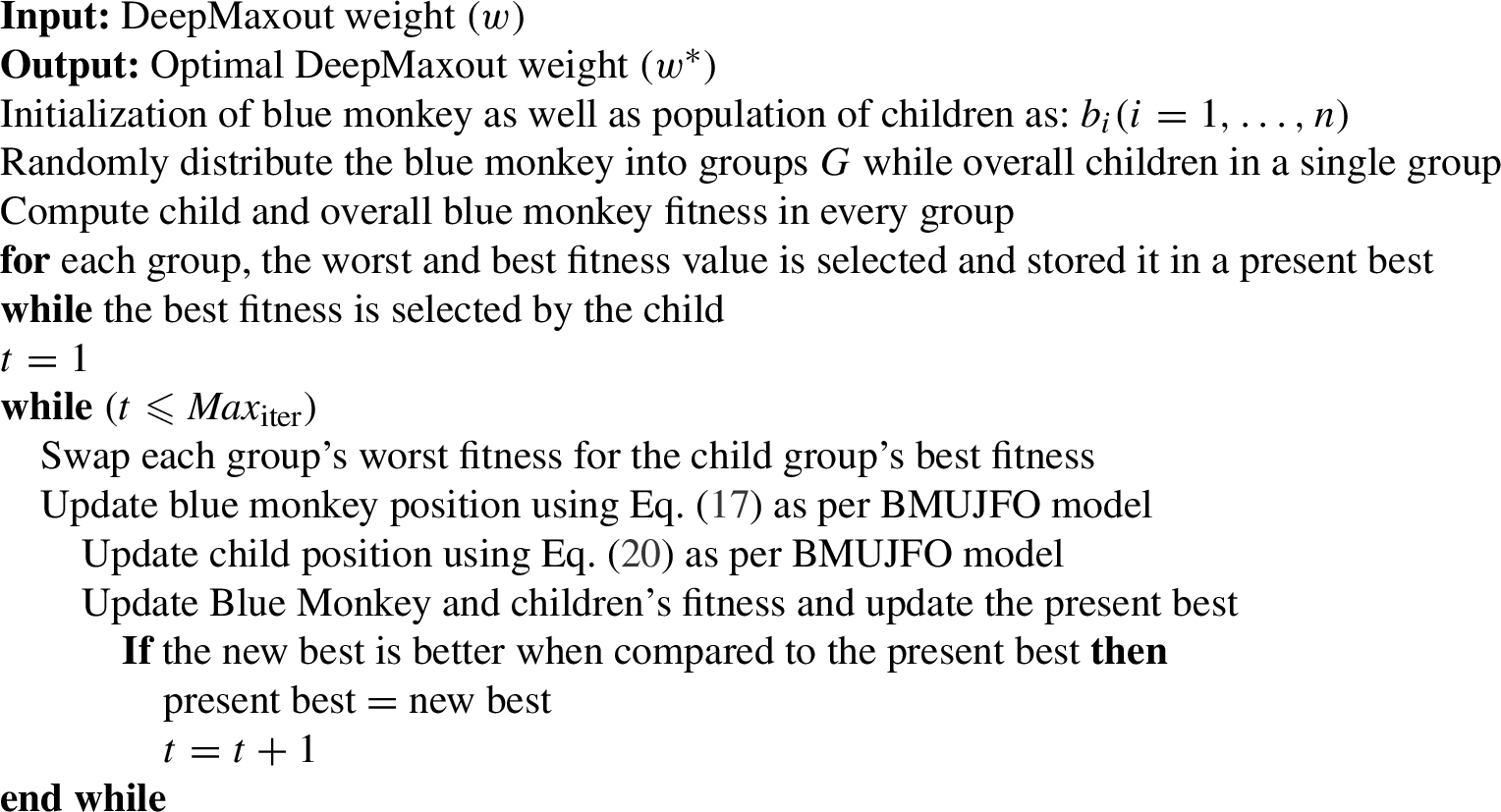
Pseudocode of proposed BMUJFO algorithm for optimal DeepMaxout weight
Simulation procedure
The proposed attack detection framework for the IoT-fog system is implemented in PYTHON and the dataset is assembled in [2] and [3]. The BMUJFO is computed over traditional methodologies like Blue Monkey Optimization (BMO), Jelly Search Optimizer (JSO), Smile Mould Algorithm (SMA), Dragonfly Optimization (DO) and Sine Cosine Algorithm (SCA). Here, our BMUJFO and the conventional approaches are analyzed by using two different datasets. Table 2 displays the experimental setup.
Dataset1 description
“The IXIA PerfectStorm tool in the Cyber Range Lab of UNSW Canberra creates the raw network packets of the UNSW-NB 15 dataset for producing a blend of real contemporary normal activities and synthetic current attack behaviors. 100 GB of the raw traffic are recorded using the tcp dump tool (e.g., Pcap files). Fuzzers, Analysis, Backdoors, DoS, Exploits, Generic, Reconnaissance, Shellcode, and Worms are among the nine attack categories in this dataset. Twelve methods are built, along with the Argus and Bro-IDS tools, to produce a total of 49 features with the class label.
Dataset2 description
“CICDoS2019 includes safe and current examples of common DDoS attacks that closely resemble actual real-world data (PCAPs).” Additionally, it has labeled flows based on the time stamp, source and destination IP addresses, source and destination ports, protocols, and attack (CSV files) from the network traffic analysis performed using CICFlowMeter-V3.
Simulation setup
Simulation setup
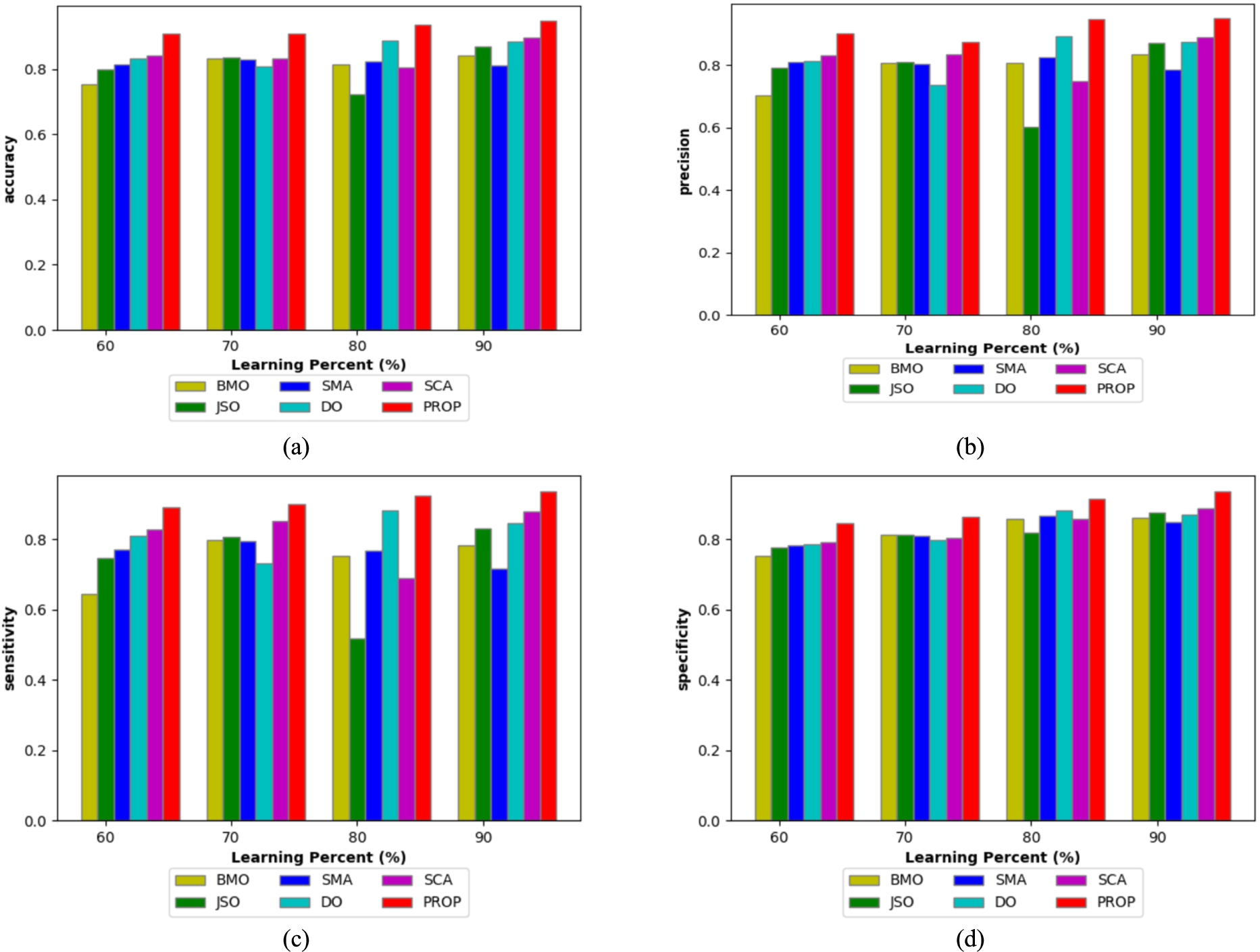
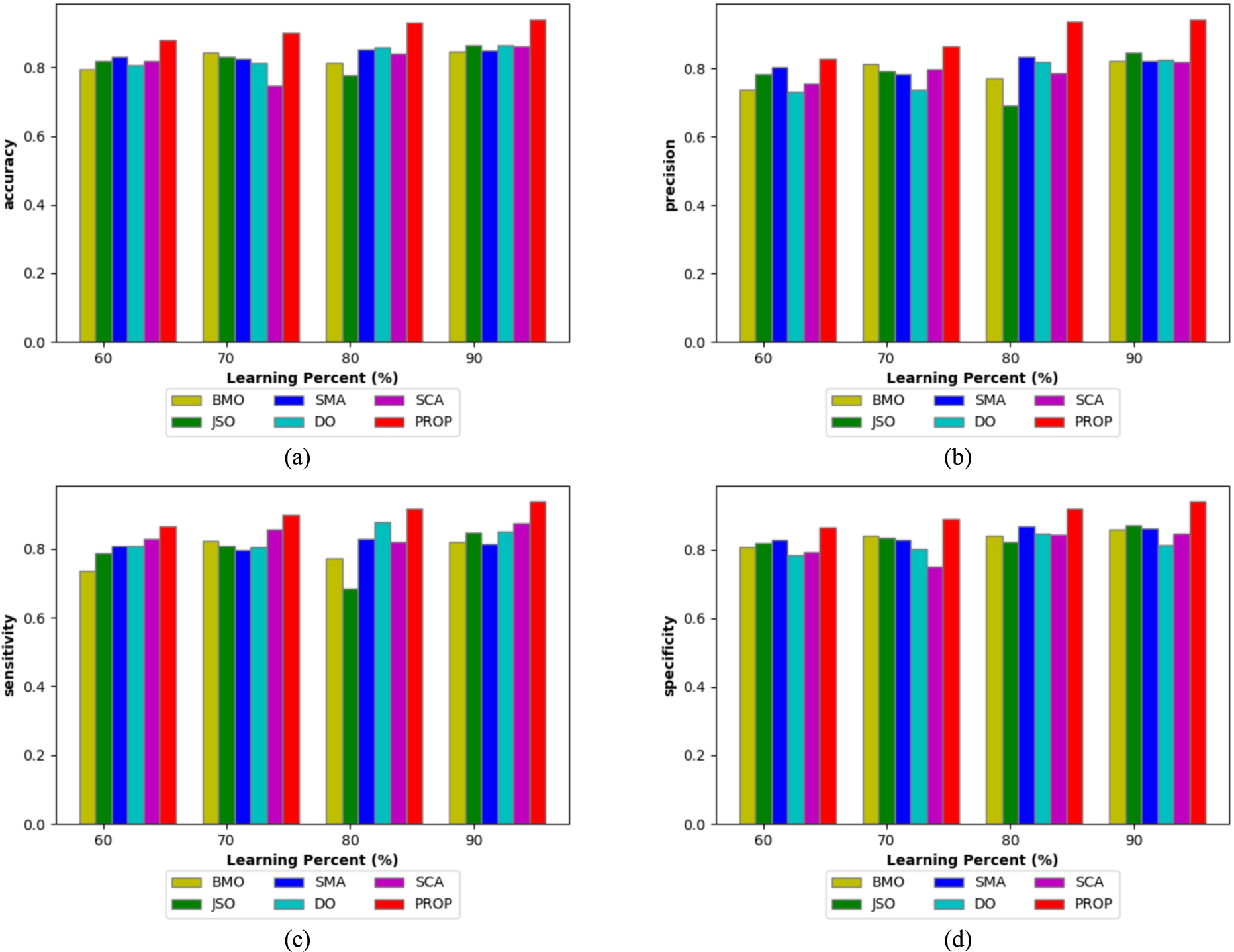
Analysis of BMUJFO and the traditional methods via positive measure architecture utilizing dataset1.
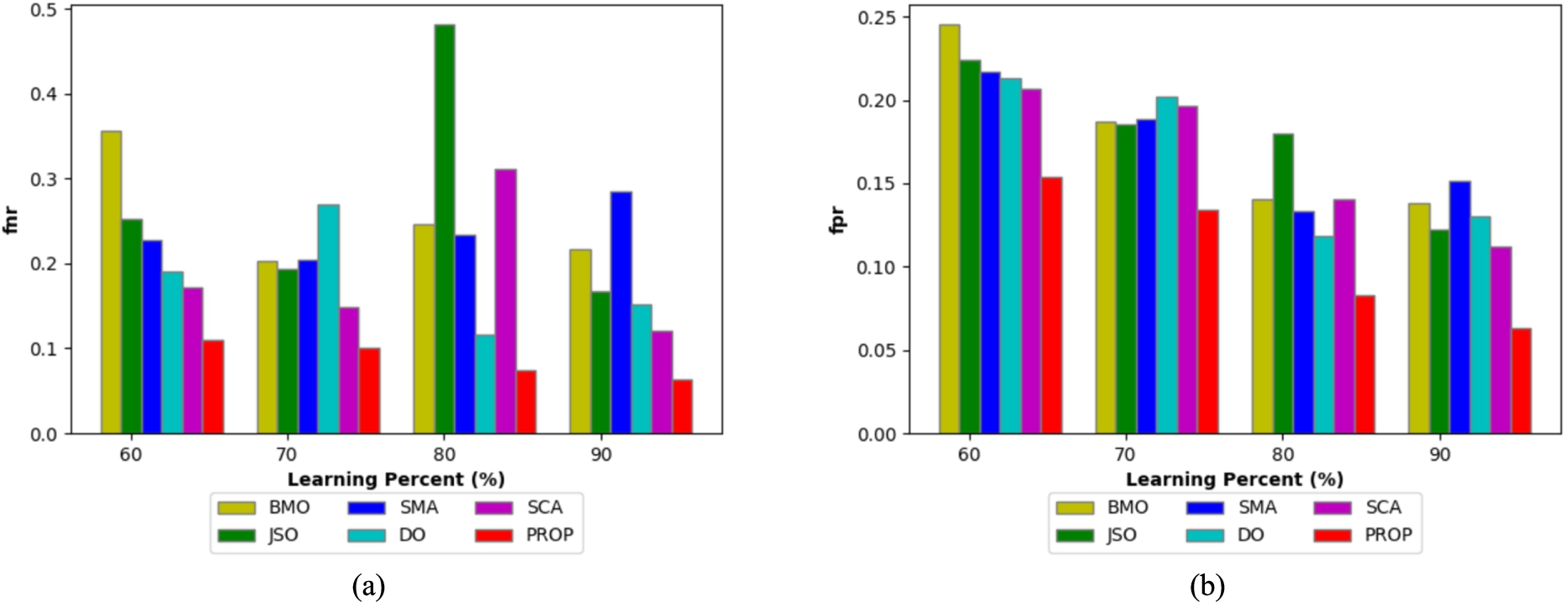
The proposed BMUJFO and the existing models via negative measure utilizing dataset1.
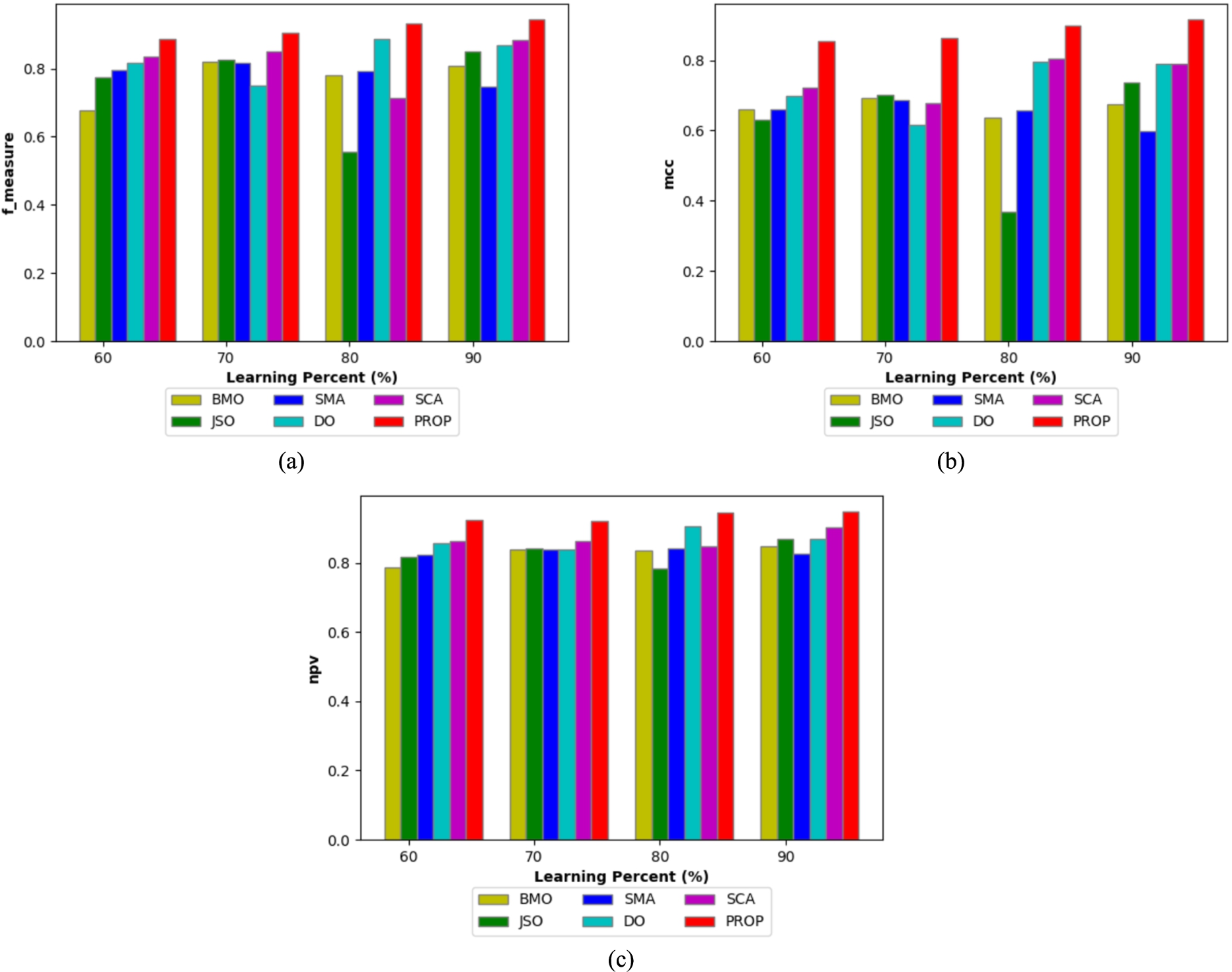
Analysis of BMUJFO and the traditional methods via other measures utilizing dataset1.
Evaluation of BMUJFO and the existing methods via positive measure utilizing dataset2.
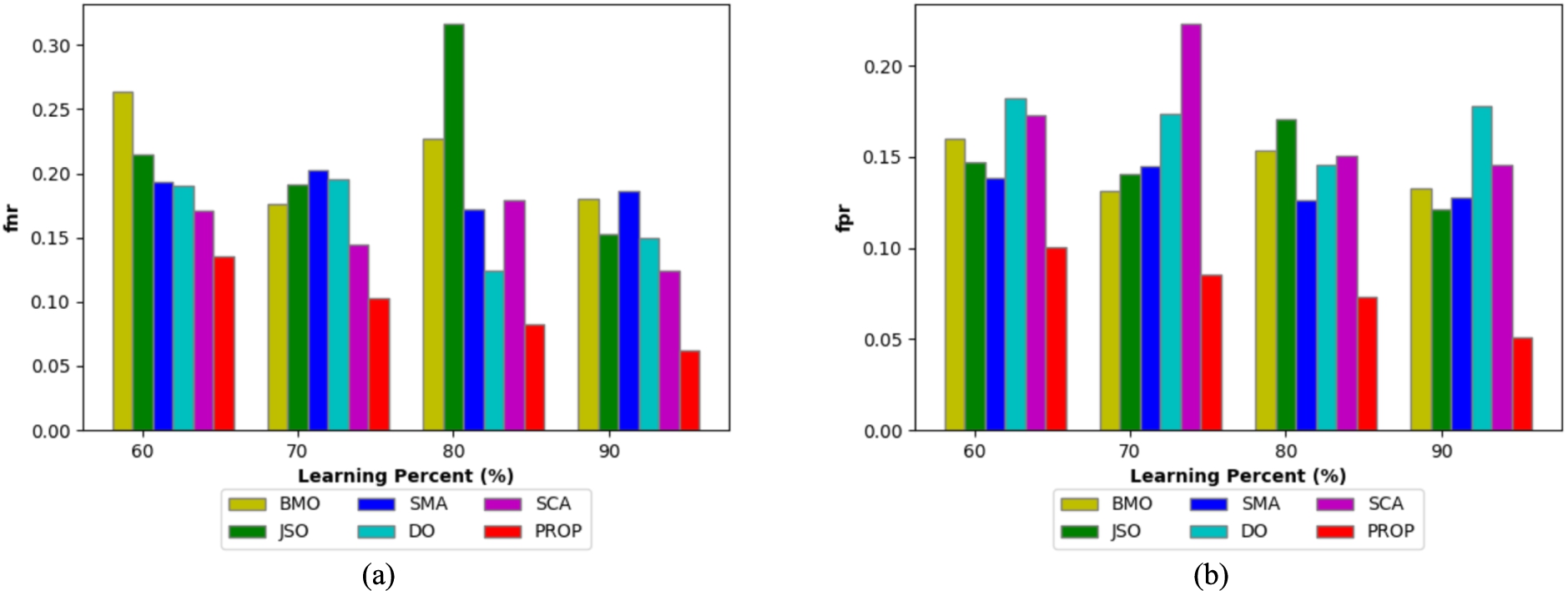
Analysis of BMUJFO and the traditional methods via negative measure utilizing dataset2.
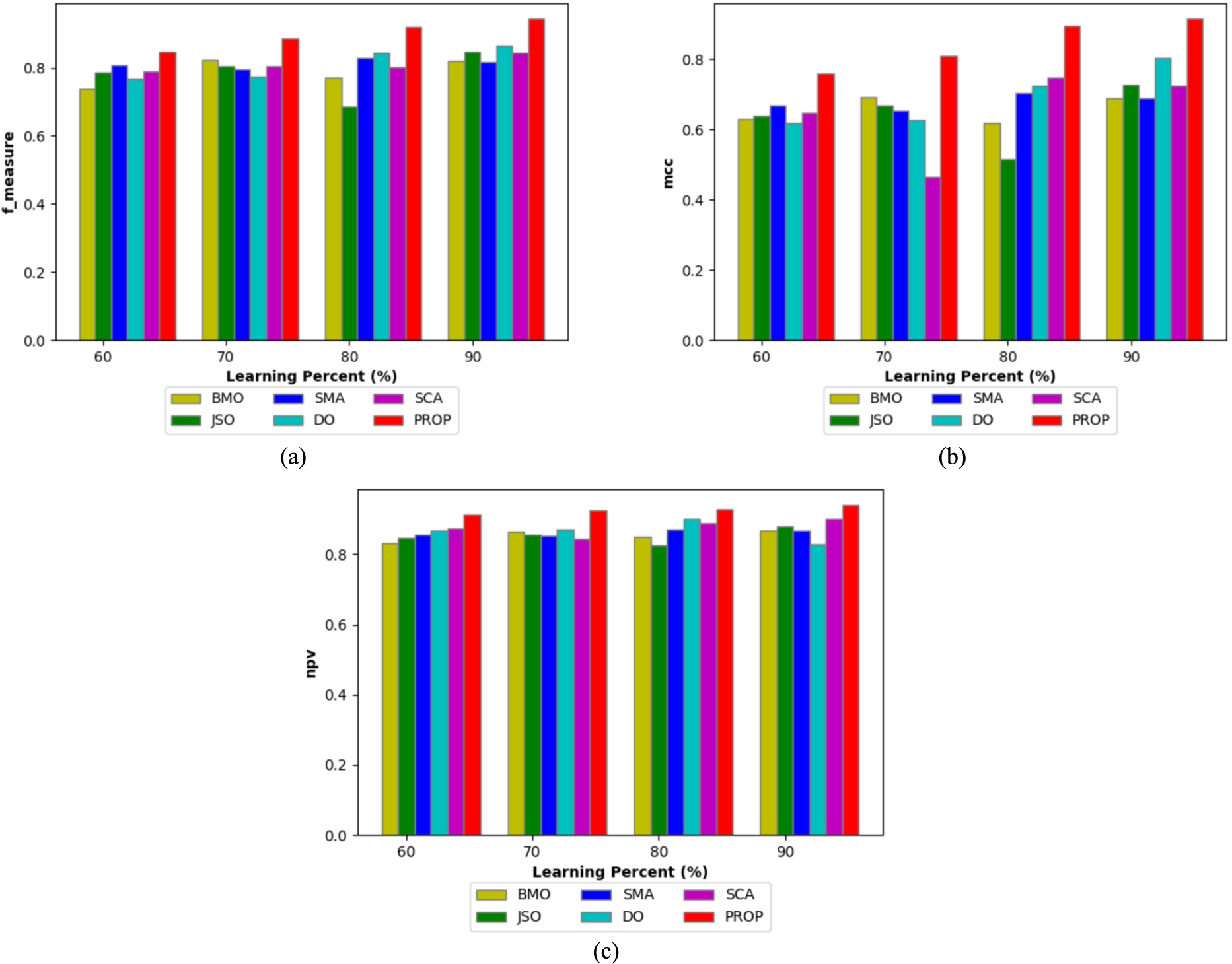
Evaluation of BMUJFO and the existing techniques via other measures for attack detection in IoT-fog architecture utilizing dataset2.
To describe the efficacy of the BMUJFO, it is contrasted with the established methodologies for attack detection in IoT-fog architecture while applying dataset1 and dataset2 is depicted from Fig. 5 to Fig. 10. In addition, the BMUJFO is compared with the JSO, BMO, SCA, DO and SMA. When examining those figures, the BMUJFO accomplished superior findings for attack detection in IoT-fog framework over the JSO, BMO, SCA, DO and SMA. More particularly, the accuracy of the BMUJFO for the 80th training rate is 92.49% as per Fig. 5(a), meanwhile, the existing strategies scored the lowest accuracy, notably, JSO = 69.26%, SMA = 79.88%, DO = 86.91%, BMO = 78.64% and SCA = 76.23%, respectively. According to Fig. 5(b), the BMUJFO has acquired a precision of 96.88% (Learning rate = 90), whereas the JSO, BMO, SMA, DO and SCA gained the lowest precision value. Mainly, the greatest sensitivity and specificity is achieved by the BMUJFO for the learning percentage 70 is 91.86% and 90.47% for the attack detection in IoT-fog framework, which is extremely greater over the JSO, SMA, DO, BMO and SCA, based on the Fig. 5(c) and Fig. 5(d).
The FNR and FPR ought to be lower for better detection of attacks in IoT-Fog architecture. Likewise, the BMUJFO generated the lower error ratings in almost all the learning percentages. In particular, from Fig. 6(a), the maximum FNR generated by the JSO method is 0.493, combined with SCA is 0.326 and BMO is 0.245, though the BMUJFO recorded the lowest FNR of 0.006 in the 80th learning rate. Additionally, examining the FPR error measure, as the training rate improved the FPR was reduced for the BMUJFO strategy. Consequently, the FPR of the BMUJFO is 0.063 as shown in Fig. 6(b), even though the JSO is 0.118, SMA is 0.148, DO is 0.139, SCA is 0.127 and BMO is 0.136.
Finally, the other measure analysis is done for BMUJFO over the traditional methods under different learning percentages as illustrated in Fig. 7. The F-measure of the BMUJFO is 94.38% (Fig. 7(a)) for accurate attack detection; this is superior to JSO, SMA, DO, SCA and BMO. Further, for the attack detection in IoT-fog, the NPV and MCC of the BMUJFO are higher over the JSO, SMA, DO, SCA and BMO, based on Fig. 7(a) and 7(b).
Similarly, for dataset 2, the BMUJFO recorded maximized positive and other metrics with lesser negative measures for the accurate attack detection in IoT-Fog architecture is displayed in Fig. 8, 9 and 10. Moreover, the outcomes revealed that the BMUJFO can accurately detect the attack in the IoT-Fog framework. Therefore, the enhanced z-score normalization, better MI-based feature extraction and the hybrid optimization including BMO and JFO are responsible for the enhanced detection accuracy and the decreased FNR and FPR error values of BMUJFO for accurate detection of attack in IoT-Fog design.
Impact on model with and without optimization, model without improved normalization for attack detection in IoT-fog architecture employing dataset1 and dataset2
Ablation examination on BMUJFO, for attack detection in IoT-Fog architecture utilizing the dataset 1 and 2 is summarized in Table 3. The BMUJFO with improved normalization and optimization can detect the attack accurately in IoT-Fog architecture. Moreover, the precision of the BMUJFO is 94.81% for the dataset1, the model without improved normalization is 78.96% and the model without optimization is 81.06%. Further, the FPR obtained by the BMUJFO, model without improved normalization and model without optimization is 0.0831, 0.2368 and 0.2443, respectively. Finally, regarding the dataset 2, the sensitivity, F-measure, FNR and accuracy of the BMUJFO is 91.79%, 92.05%, 0.0820 and 93.13%, respectively. The contrasts between the results obtained using techniques for optimization and those without are thus revealed in this section. Altogether, the BMUJFO with all the modifications upgrades the performance score on detecting the attack in IoT-Fog architecture and this is because of the improved z-score normalization and with the optimization strategy.
Ablation analysis on BMUJFO, model without improved normalization and model without optimization for attack detection in IoT-fog architecture utilizing dataset1 and dataset2
Ablation analysis on BMUJFO, model without improved normalization and model without optimization for attack detection in IoT-fog architecture utilizing dataset1 and dataset2
Table 4 shows the comparison of the Hybrid + BMUJFO classifier with the established classifiers (LSTM [25], Deep Maxout, DBN, CNN + LSTM [14], Bi-LSTM, CNN [3] and RNN) for attack detection in IoT-Fog architecture utilizing the dataset1 and dataset2. In order to demonstrate the effectiveness of hybrid + BMUJFO for attack detection in the IoT-fog structure, it is further evaluated using a variety of performance measurements. Specifically, the hybrid + BMUJFO’s F-measure is minimum at 93.15%, whereas the existing classifiers, like Deep Maxout = 72.33%, DBN = 74.94%, Bi-LSTM = 70.59%, CNN = 74.69%, RNN = 78.92%, LSTM = 75.02% and CNN + LSTM = 73.51%. Simultaneously, the FNR obtained by the hybrid + BMUJFO is 0.0749, which is much lower than Deep Maxout, LSTM, DBN, CNN, CNN + LSTM, Bi-LSTM and RNN, respectively. Likewise, for dataset 2, the hybrid + BMUJFO accomplished better findings than the conventional classifiers. Further, the specificity, NPV, accuracy, F-measure and sensitivity of the hybrid + BMUJFO are 92.19%, 92.87%, 93.14%, 92.05% and 91.79%. This indicates that the hybrid + BMUJFO with improved z-score normalization and improved MI-based feature extraction, has achieved superior outputs in assessing the attack detection in the IoT-Fog framework.
Comparative analysis on hybrid + BMUJFO and the extant classifiers for attack detection in IoT-fog architecture employing dataset1 and dataset2
Comparative analysis on hybrid + BMUJFO and the extant classifiers for attack detection in IoT-fog architecture employing dataset1 and dataset2
The statistical assessment of BMUJFO accuracy for detecting the attack in IoT-Fog architecture under five varied statistical measures is exposed in Table 5. Further, the examination is done employing two distinctive datasets. For accurate attack detection in IoT-Fog architecture, the model must generate the highest detection accuracy ratings. Similarly, the BMUJFO offered maximal detection accuracy in most of the statistical measures for both datasets. Particularly, the detection accuracy of the BMUJFO for the best statistical measure is 0.9477, in contrast, the JSO, SMA, DO, SCA and BMO acquired least accuracy of 0.8694, 0.8302, 0.8870, 0.8958 and 0.8418, respectively. Consequently, for the median statistical measure, the BMUJFO gained an accuracy of 0.9224, meanwhile, the JSO is 0.8180, the SMA is 0.8178, the DO is 0.8573 and the SCA is 0.8367. In addition, by evaluating the worst, mean and best statistical measures, the BMUJFO accomplished the greatest detection accuracy of 0.8793, 0.9132 and 0.9397. The overall findings that compared to the existing methods, BMUJFO is much more effective. for detecting the attacks in IoT-Fog architecture with excellent detection accuracy. This signifies that the BMUJFO is suitable to tackle the specified problem in an appropriate manner.
Statistical evaluation on BMUJFO and the conventional methods for attack detection in IoT-fog architecture while applying dataset 1 and dataset 2 under varied statistical measures
Statistical evaluation on BMUJFO and the conventional methods for attack detection in IoT-fog architecture while applying dataset 1 and dataset 2 under varied statistical measures
The convergence study on BMUJFO is compared with the JSO, SMA, DO, SCA and BMO for attack detection in IoT-Fog architecture is shown in Fig. 11(a) and Fig. 11(b) utilizing dataset1 and dataset2. As shown in Fig. 11, the error value is large at the initial stage of the iterations but decreases as the number of iterations increases for the BMUJFO and other JSO, SMA, DO, SCA, and BMO techniques for datasets 1 and 2. The BMUJFO and the comparable methods both have lower error rates at iterations 25 through 50. But our BMUJFO provided the smallest error value. More particularly, the smaller error value of 1.0523 is acheived for dataset1 by the BMUJFO at the 50th iteration, whereas the BMO, JSO, SMA, DO and SCA acquired the error value of 1.0525, 1.0536, 1.0538 and 1.0532. Additionally, the error rate of the BMUJFO for dataset 2 is 1.0524 in the final iteration. It has been demonstrated beyond a reasonable doubt that the BMUJFO enables better attack detection in IoT-fog architecture with a lesser error value, and that this is because of better z-score normalization and improved MI-based feature extraction with hybrid optimization.
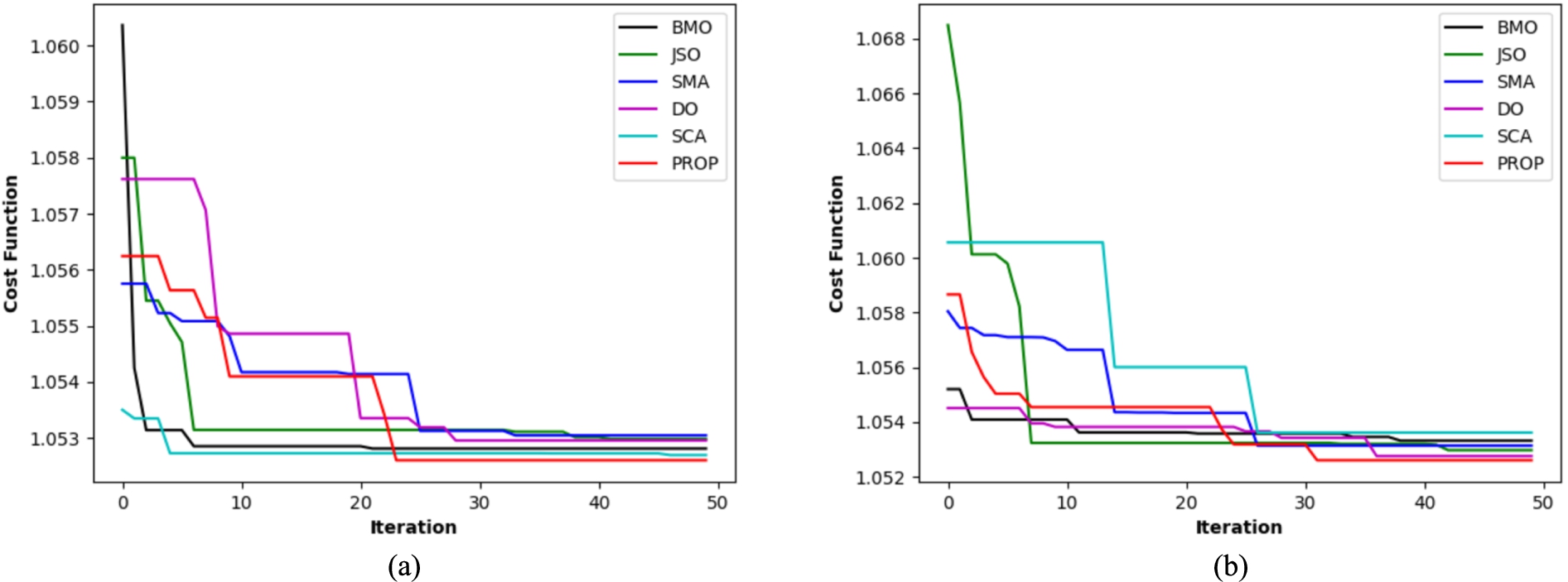
Convergence study on BMUJFO and the existing methods for attack detection in IoT-fog framework a) Dataset1 and b) Dataset2.
Table 6 shows the time complexity. The computational time of the suggested method is (∼1281.552) when compared to the BMO (∼2521.001), JSO (∼2162.584), SMA (∼2328.364), DO (∼2870.803), and SCA (∼1837.668). Thus, it is demonstrated that the suggested approach is superior to other current approaches.
Time analysis
Time analysis
A Deep Hybrid Detection Model for Attack Detection in IoT-Fog Architecture is proposed in this work with a stage procedure. Improved Z-score normalization-based data preprocessing will be done in the first stage. In the second stage, features including IG, raw data, Entropy, and improved MI are extracted based on preprocessed data. A hybrid attack detection method is employed in the third step by giving the extracted features as input to hybrid classifiers named optimized Deep Maxout and DBN for classifying the attacks based on the input dataset. For optimal training of Deep Maxout, a hybrid optimization model named BMUJFO (Blue Monkey Updated Jellyfish Optimization) algorithm was developed. Consequently, the FPR of the BMUJFO is 0.063, even though the JSO is 0.118, SMA is 0.148, DO is 0.139, SCA is 0.127 and BMO is 0.136. The benefit of the suggested model is that it can accurately and efficiently identify a variety of attacks while also demonstrating how to continuously monitor and improve the detection system to identify new attacks. Its disadvantage is that it may be challenging to label the data that was gathered at the edge layer in order to train the LSTM model in the cloud. The extensive use of IoT devices in modern technology, including IoVT, IoMT, smart grids, and smart electrical appliances, has given rise to a significant number of attacks on those systems due to their importance in resource sharing. Sensors and actuators are examples of physical devices that provide cloud administration on demand. We will assess the suggested attack detection with unsupervised DL techniques and reinforcement learning in the future utilizing a distributed computing environment like Apache Spark and additional datasets.
