Abstract
BACKGROUND:
The chaotic system with low dimensions has a low security compared to the high-dimensional chaotic system. Furthermore, major pixel-level permutations merely transform the pixel position and cannot change the intensity distribution of the original image. Bit-level permutation could change the intensity distribution, as it devotes more time to conduct bit-level computation.
OBJECTIVE:
In this study, we present a more efficient image encryption approach based on hyper-chaos and a global bit cycle shift (HC-GBCS).
METHODS:
According to the input image we adopted the SHA-256 secure hash algorithm to obtain the initial key, which served as the premier parameter of the chaotic system. Then we employed a 4D hyper-chaotic system for generating the chaotic series, on which we utilized global bit permutation to enhance the security of the encryption system. Finally, the diffusion process was conducted by using the generated chaotic series extended with a logistic map.
RESULTS:
Experimental results and analysis reveal that the presented approach encrypts plain images effectively and achieves high security and stability.
CONCLUSION:
The proposed method can deal with the problems inherently existing in encryption methods utilizing low-dimensional chaotic map. Furthermore, global bit permutation can transform the pixel distribution of plain images and enhance the cryptosystem security.
Introduction
With the increasing popularity of network and information technology, the information transfer via Internet is increasingly common. As a greatly efficient approach of privacy and security protection, image encryption has drawn considerable attention and plenty of algorithms utilizing various techniques have been explored in the past decades. Due to the fact that images are inherently bulk data with a high correlation among pixels and significant data redundancy, existing encryption methods cannot figure out real-time image encryption tasks well. Thus, amounts of chaos-based encryption methods achieved inspiring results in amounts of real tasks [1].
The fundamental structure of chaos-based approaches consists of two procedures: permutation and diffusion phases. In recent years, pixel-level based permutation methods have achieved significant results in many image encryption tasks [2, 3, 4]. Liu et al. [5] utilized one-time keys and two reliable chaotic maps, and combined MD5 algorithm with existing cycle encryption. Wang et al. [6] proposed an encryption method which associated a 4D Lorenz hyper-chaotic system with gene recombination.
To deal with the drawback inherently existing in approaches utilizing pixel-level permutation, various approaches utilizing bit-level permutation have been proposed. Zhu et al. [7] developed an algorithm that uses a logistic map and an Arnold map separately for diffusion and permutation. Li et al. [8] reported a five-dimensional multi-wing hyper-chaotic system and the permutation process divided the image into blocks, and each block is multiplied by a constant matrix. Moreover, DNA sequence has been used for image encryption [9, 10]. Unfortunately, this kind of algorithm has the same weakness as the ones using pixel-level permutation.
In order to solve the above-described problems, this study presents an efficient real-time encryption algorithm on the basis of hyper-chaos and a global bit cycle shift (HC-GBCS). Theoretical and numerical analyses indicate that the proposed method resists different attacks and owns low time complexity. In addition, the encryption test on finger-vein images shows that the proposed method has a significant performance in practical application.
The remainder of our study is summarized as follows. The basic theory of the 4D hyper-chaotic system is introduced in Section 2. In Section 3, the proposed approach is introduced in detail. Experimental results and performance analysis are presented in Section 4, and conclusions are drawn in Section 5.
Hyper-chaotic system
Although traditional low-dimensional chaotic systems are highly efficient, they suffer from inadequate key spaces and low security. On the contrary, high-dimensional hyper-chaotic systems own more positive Lyapunov exponents, more complicated and unpredictable dynamic characteristics, and higher randomness [11]. The 4D hyper-chaotic system adopted in our study can be given as follows [12]:
where
This paper presents a novel real-time image encryption algorithm based on hyper-chaos and a global bit cycle shift (HC-GBCS). First, the plain image is used to generate a 256-bit external secret key K through the SHA-256 secure hash algorithm. Then a 4D hyper-chaos system which is initialized by using secret key K is introduced to generate the chaotic sequence. Then the image is shuffled by a pixel-level permutation and decomposed into eight binary bitplane images. Finally, global bit permutation and diffusion operations are conducted to change the image intensity distribution and further enhance the security.
Generation of the secret key and chaotic sequence
Let The parameters of the chaotic system (1) are computed by Eq. (Step 2.):
where The chaotic system (1) is solved numerically using the fourth-order Runge-Kutta method, and the former
Pixel-level permutation process
Series
Chaotic series
After the permutation process, the correlations among neighboring pixels of the original image have been broken but the image histogram has not changed, so the scrambled image requires further processing.
The pixel value of a grayscale image is an integer ranged from 0 to 255, which could be converted into a binary series with eight bits, and the
The image Bitplane image cycle shift. The lower-order bits are shifted using the values of the higher-order bits. We select four numbers from the chaotic sequence
where The scrambled bitplanes are merged and the acquired image is denoted as
After the GBCS process, the image histogram has changed, but the distribution is not sufficiently uniform. This means that the statistical properties of the original image have not completely changed, so a further diffusion process is necessary.
The operation of diffusion is an extremely crucial procedure which transforms the pixel distribution and arouses an avalanche effect in case a pixel value is changed.
Reshape the image matrix The first round of diffusion is as follows. Step 2.1 Diffuse the first pixel value
Step 2.2 Set
Step 2.3 Set Step 2.4 Process the first pixel again as For the second round of diffusion, we use the sequence The encrypted image is acquired by transforming
The decryption algorithm is the reverse procedure of the above steps.
Various experiments are conducted to analyze and verify the effectiveness of the presented method. In the experiments, except the natural images with size
Key space
To ensure that the cipher text cannot be revealed by a brute-force attack, the encryption approach should own a large key space. In our presented HC-GBCS method, the secret keys consist of two parts: the original key
To ensure the reliability of an encryption system, the key space should be larger than
An efficient encryption method should be sensitive to the secret key for resisting different attacks. The plain image could not be recovered even if the key has a slight difference. The Lena image with size
Analysis of key sensitivity: (a) Lena image, (b) Encrypted image (a1 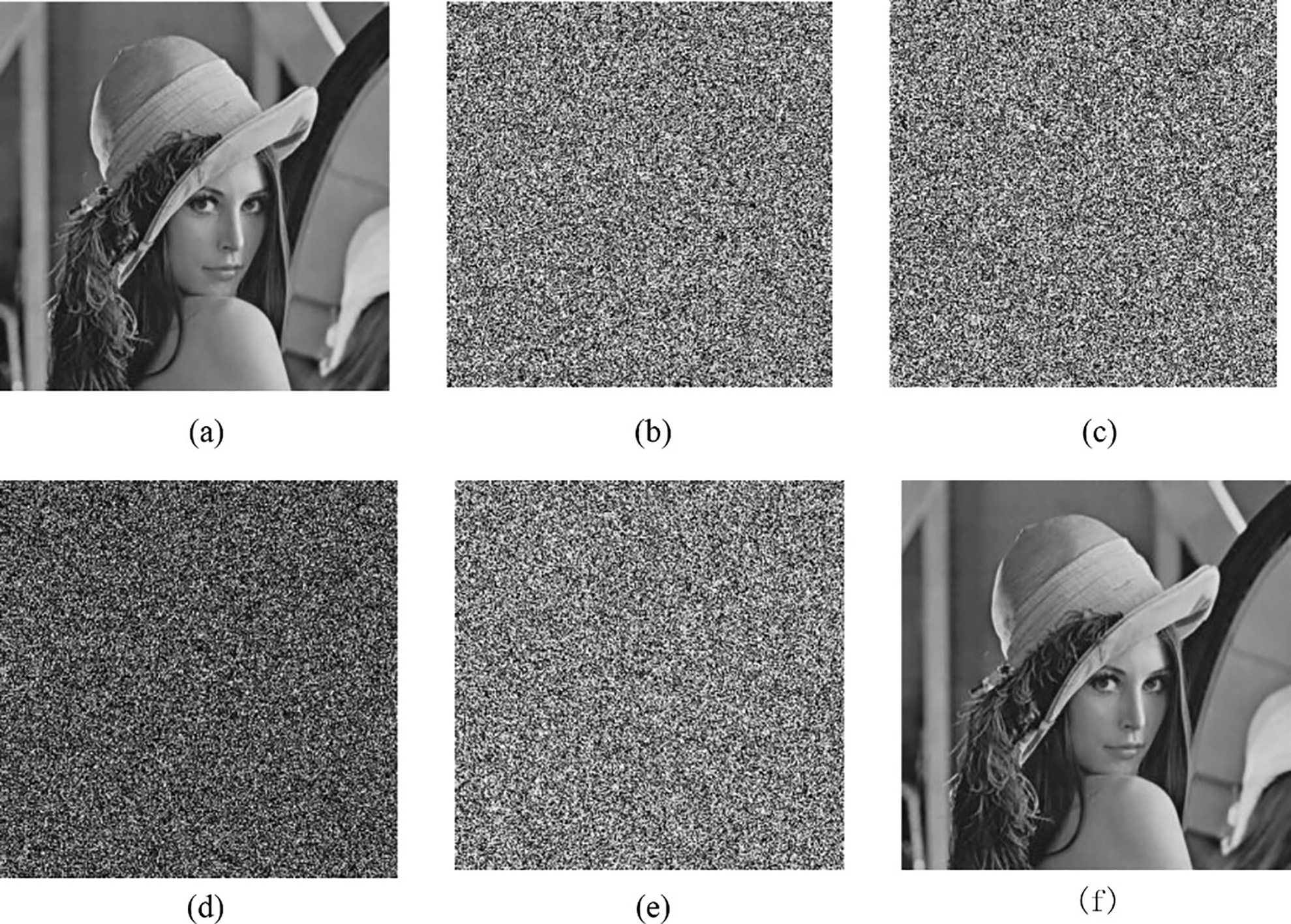
The correlation among neighboring pixels refers to similarity degree between nearby pixels. Generally, correlation among neighboring pixels along the horizontal, vertical and diagonal orientations is always high for most natural images. Thus, an excellent encryption system should significantly reduce the correlation among neighboring pixels in the cipher-image.
We randomly selected 5000 pairs of neighboring pixels along three orientations from 40 natural images and finger-vein images. We then calculated the correlation coefficients of neighboring pixels using the following formula:
where
The mean values of correlation coefficients with different algorithms are listed in Table 1, which indicates that the correlation coefficients of plain images tends to 1, whereas those of cipher-images tends to 0 in three directions. Therefore, it demonstrates that the presented encryption method has excellent confusion and diffusion traits.
Comparison results of correlation coefficients
Packet loss and packet error comparison results
We simulated the corruption of information that occurs during actual network transmission by adding salt-and-pepper noise with different densities (0.01, 0.03, and 0.05, respectively), and Gaussian noise with mean 0 and different variances (0.0001, 0.0003, and 0.0005, respectively) to 40 encrypted images, and then decrypted them.
Structural Similarity (SSIM) is an indicator to measure the similarity of two images [17], the average values of SSIM values are shown in Table 2. The proposed algorithm outperforms other algorithms except BLP, and obviously, it is robust to the packet loss and pack error.
Conclusions
This study presented a hyper-chaos-based image encryption scheme utilizing global bit cycle shift. The algorithm utilizes a 4D hyper-chaotic system whose preliminary parameters are produced by SHA-256 secure hash algorithm, and adopts global bit permutation to enhance the security of the encryption system.
The system can deal with the problems inherently existing in encryption methods utilizing low-dimensional chaotic map. Furthermore, global bit permutation can transform the pixel distribution of plain images and enhance the cryptosystem security. The amount of experiments and corresponding analysis, including key space analysis, key sensitivity analysis, correlation analysis, and packet loss and packet error analysis, validate that the presented approach is secure and reliable for image encryption. In addition, the encryption test on finger-vein images show that the proposed method has a significant performance in practical application.
Footnotes
Conflict of interest
None to report.
