Abstract
Information hiding is a crucial technology in the field of information security. Embedding capacity and stego-image quality are two key performance metrics in information hiding. In recent years, many information-hiding methods have been proposed to enhance embedding capacity and stego-image quality. However, through the study of these methods, we found that there is still room for improvement in terms of performance. This paper proposes a high-capacity information-hiding method based on a chunking matrix (CM). CM divides a 256×256 matrix into blocks, where each block contains
Introduction
With the rapid development of the Internet, more and more people enjoy the convenience brought by information technology but also suffer the threat of information leakage and network attacks. Hence, security [27, 28] is getting high attention. In the field of information security [1], cryptography [2–4], and information hiding method [5–8] are effective tools for protecting private information. However, the encrypted secret information appears scrambled and meaningless. This easily raises suspicion among attackers who may attempt to disrupt it. In contrast, information-hiding methods embed secret information in media files such as text, images, audio, and video, while leaving the original media file little changed. This protects the confidentiality of the information and achieves imperceptible transmission.
Information hiding involves embedding confidential data within daily media without arousing suspicion or attacks from third parties other than the communicating parties. It finds applications in various fields where communication security is paramount, including the domains of digital copyright protection, cybersecurity, healthcare, and the military. Information hiding plays a crucial role in enhancing data security, privacy protection, and content authentication across these diverse areas of application.
This paper uses images as carriers to embed secret information. Information hiding methods for digital images can be divided into two main categories: the spatial domain and the frequency domain. In frequency domain-based hiding methods, pixels are transformed into frequency coefficients through various discrete transform functions such as Discrete Fourier Transform (DFT) [9] and Discrete Cosine Transform (DCT) [10], and these coefficients are modified to embed secret information. Frequency domain-based hiding methods exhibit strong resistance against attacks but have a relatively low embedding capacity. In spatial domain-based hiding methods, the pixel values of an image are directly modified to embed secret information. Spatial domain information hiding is a digital image processing technique designed to embed secret information into the pixel values of digital images, aiming to achieve information concealment and protection. The primary objective of this technology is to hide data within an image without causing perceptible degradation in image quality, while ensuring that the hidden data can be extracted when needed.The spatial domain-based hiding method is easy to implement and has a high embedding capacity. In the spatial domain, after extracting the embedded secret information, information hiding can be classified into reversible information hiding [11] and irreversible information hiding [12], depending on whether the cover image can be recovered or not. In reversible information hiding, the cover image can be recovered without distortion. This method is suitable for image-sensitive fields, such as healthcare and military domains. Irreversible information hiding is a branch of digital steganography that differs from reversible information hiding. It introduces some form of irreversible transformation or loss to embed secret information into the carrier data. Unlike reversible information hiding, irreversible information hiding does not guarantee the complete restoration of the original data during data extraction, as it typically involves a certain degree of information loss, but it allows for higher information embedding capacity and ease of implementation.
This paper studies irreversible data hiding. In the past decades, many irreversible data hiding methods have been proposed. The methods can be divided into three categories, LSB-based, PVD-based, and EMD-based. Firstly, least significant bit (LSB)-based method [13], which involves embedding secret information by modifying the least significant bit of pixels, is the simplest and most well-known method. LSB is simple to implement, but the generated stego-images can be suspicious or easily detected. Mielikainen’s LSB matching revisited method [14] overcomes the shortcomings of LSB replacement and is resistant to steganographic attacks. However, it does not improve the embedding capability. Its embedding rate is 1
Through the study and analysis of the above literature, we found that there is still room for improvement in its embedding capacity and stego-image quality. To improve the embedding capability, we propose a high-capacity embedding method based on a chunking matrix while still generating images with acceptable steganographic image quality ( CM is designed and implemented by using a chunking matrix. With the method, the embedding capacity can reach 4.806 The performance and security of CM are proved by embedding capacity, image quality, and steganalysis experiments; To make it easier for other scholars to verify the work, we have uploaded all the code and other materials at https://github.com/zhangju85/CM.git.
The rest of the paper is organized as follows. Methods of related works from FEMD, RGEMD, SB, SPM, and MPM are described in Section 2. The new method (CM) is introduced and the example is given in Section 3. Section 4 provides the experimental details and experimental results of CM. The conclusion and major contributions are highlighted in Section 5.
Some information hiding schemes
After introducing the categories of information hiding, we will provide a brief review of some irreversible spatial domain information hiding algorithms to gain a general understanding of the embedding and extraction processes. Following familiarization with these algorithms’ embedding and extraction procedures, we will proceed to compare their performance with the algorithm proposed in this paper.
FEMD
In 2011, a data hiding method based on FEMD was proposed by The Duc Kieu and Chin-Chen Chang [23]. The method embeds k secret bits of a binary secret message into a cover pixel pair of the grayscale cover image. The payload of FEMD is
The inputs of FEMD are cover pixels (
Step1: Generate the matrix S sized 256×256 by using the proposed extraction function F defined by Equations (1).
Step2: Compute
Step3: Embed the secret data into cover-pixels as follows.
If
(
Else
Search from the searching square
(
Step4: Calculate
In 2018, Chun-Cheng Wang et al. [15] proposed RGEMD method based on a combination of LSB and GEMD, which achieves an embedding rate of 2
The inputs of RGEMD are
Step1: Compute
Step2: Embed secret digit
If
If
If 0 <
For
If
If
Else
If
For
If
If
Else
Step3: Embed secret digit
Transform
For
If
If
Else
Step4: Calculate
In 2019, T. D. Sairam et al. [22] proposed a data hiding method SB based on EMD, it can not only improve the embedding capacity but also maintain good quality of stego-images. SB method uses
The inputs of SB are cover pixel
Step1: For cover pixel
If
Step2: Calculate
SPM
In 2022, Wang et al. [24] proposed SPM method, which embeds
The inputs of SPM are cover pixel
Step1: Embed secret digit
For
If
Step2: Secret digit
MPM
In 2022, Zhang et al. [25] proposed MPM, a method for modulo computation using a optimization problem. The main idea of MPM is to embed confidential bits into cover image pixels while minimizing modification to original pixels. The embedding payload of this method is up to 4.3
The inputs of MPM are n adjacent pixels
Step1: Find one cover pixel with a specified index by
Step2: Transform the confidential binary bits (
Step3: Find
Embed information in stego-pixel using
Step4: Find
Embed information in stego-pixel using
Step5: Calculate
The embedding progress
Inspired by some works of literature [1, 22–25], we propose the use of a chunking matrix for embedding secret information into cover images. CM method can not only improve the embedding capacity but also maintain good quality of stego-images. The maximum embedding rate is 4.806
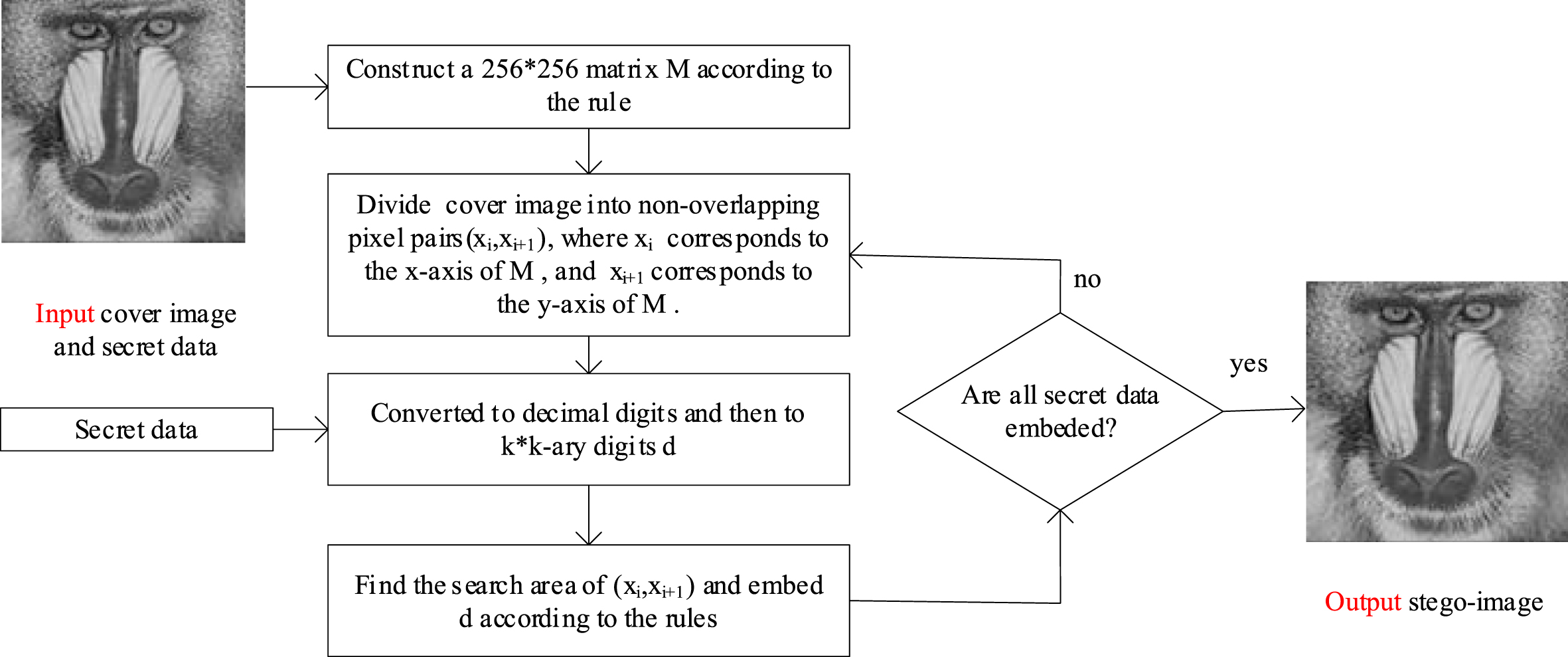
The flowchart of CM for the data embedding process.
Input: The grayscale cover image X sized
Output: The grayscale cover image Y sized
Step1: Construct a 256×256 matrix
1. Divide the matrix M into non-overlapping blocks of size
2. Assign consecutive values from 0 to
For
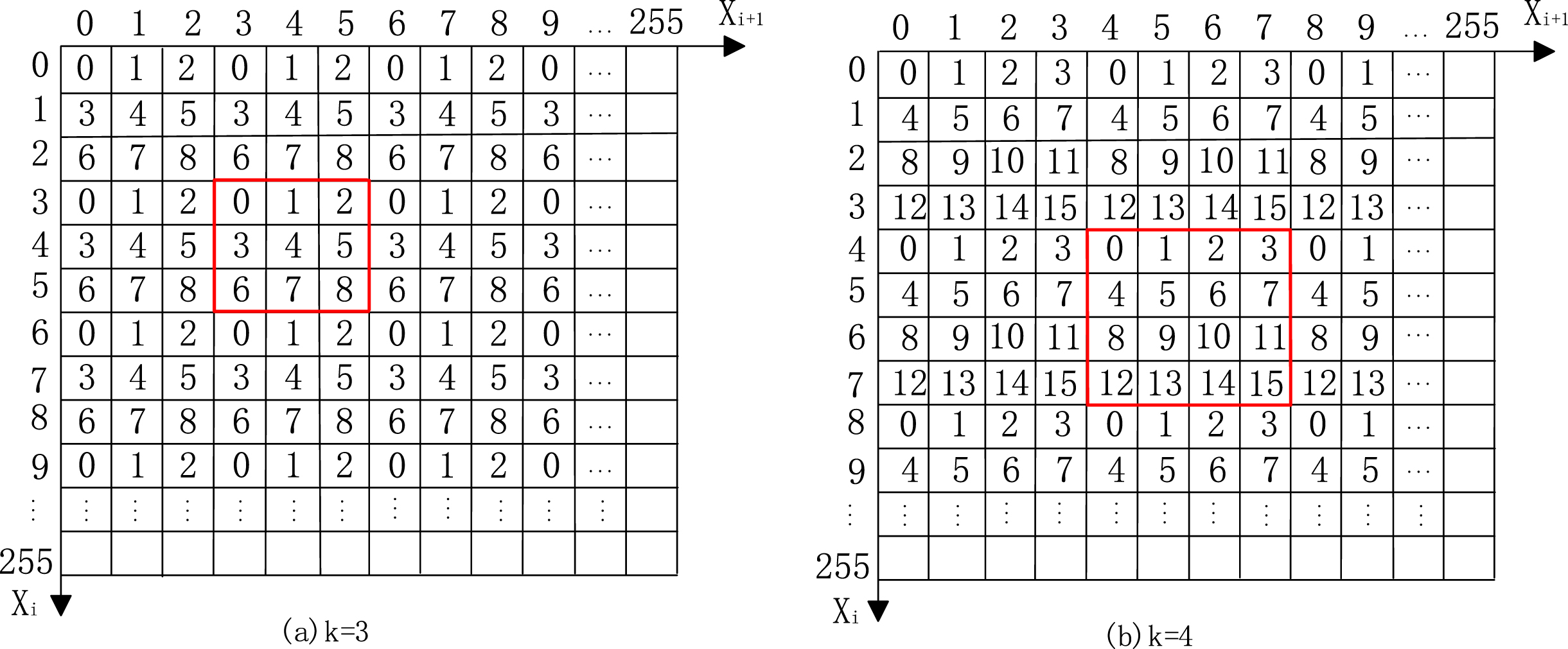
Some mapping matrices
Step2: Convert all binary secret information into a series of decimal digits, and then convert the decimal digits into
Step3: Divide the pixels of the cover image into non-overlapping pixel pairs (
Step4: Define the searching area as a
Step5: Read the
For
If
(
If
Search within the searching area for values that satisfy
(
End.
End.
According to the embedding method, the secret data is embedded in the cover image to get the stego-image. Stego-image is transmitted from the sender to the receiver. The receiver extracts the secret information from the stego-image by the following extraction algorithm.
Input: The grayscale cover image Y sized
Output: The binary secret message
Step1: Construct a 256×256 matrix
Step2: Divide the pixels of the stego-image into non-overlapping pixel pairs (
Step3: Use
In order to illustrate the steps of the CM method more clearly. Figure 3 shows a simple example:
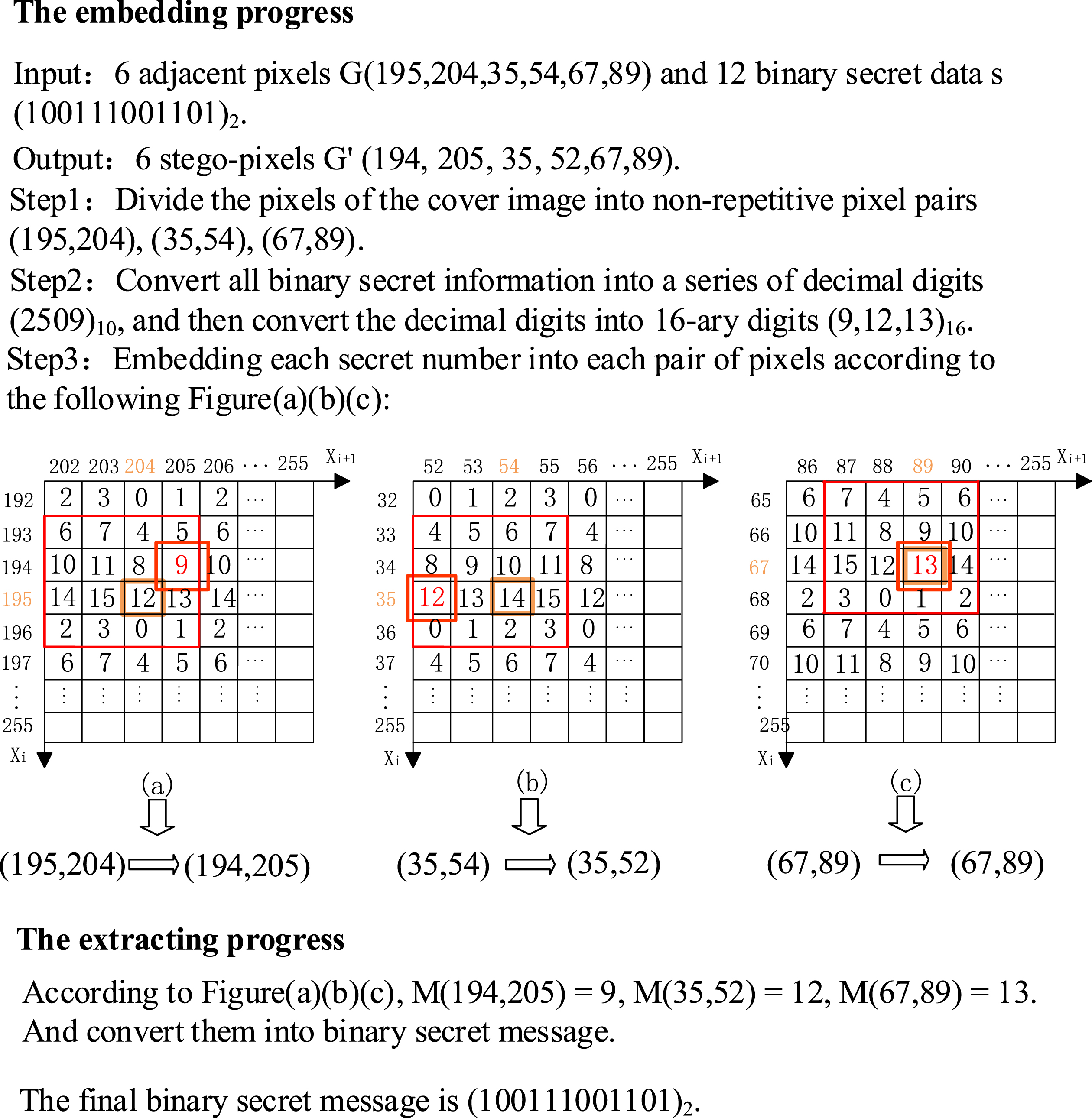
Example of the CM method.
During the process of embedding secret information, the embedding operation may lead to pixel value overflow. When embedding the secret information into an image, if proper handling is not performed, it can result in pixel values exceeding their representation range, causing significant changes in the image and making the hidden information visible. Therefore, to address this issue, the following overflow prevention measures are implemented in the proposed method:
Case1: if
Case2: if
Experimental results and discussion
In this section, the experiments are carried out to evaluate the performance of the proposed method. Our proposed method and other referenced methods are implemented in Python and run in a PC with an Intel i7-10700 CPU @ 2.90 GHz and 16-GB RAM. The operating system is Windows 10 Professional 64-bit. The images used for the experiments are a series of grayscale images of standard size 512×512 (Airplane, Baboon, Barbara, Boat, House, Lena, Peppers, and Tiffany) [26], which are shown in Fig. 4.
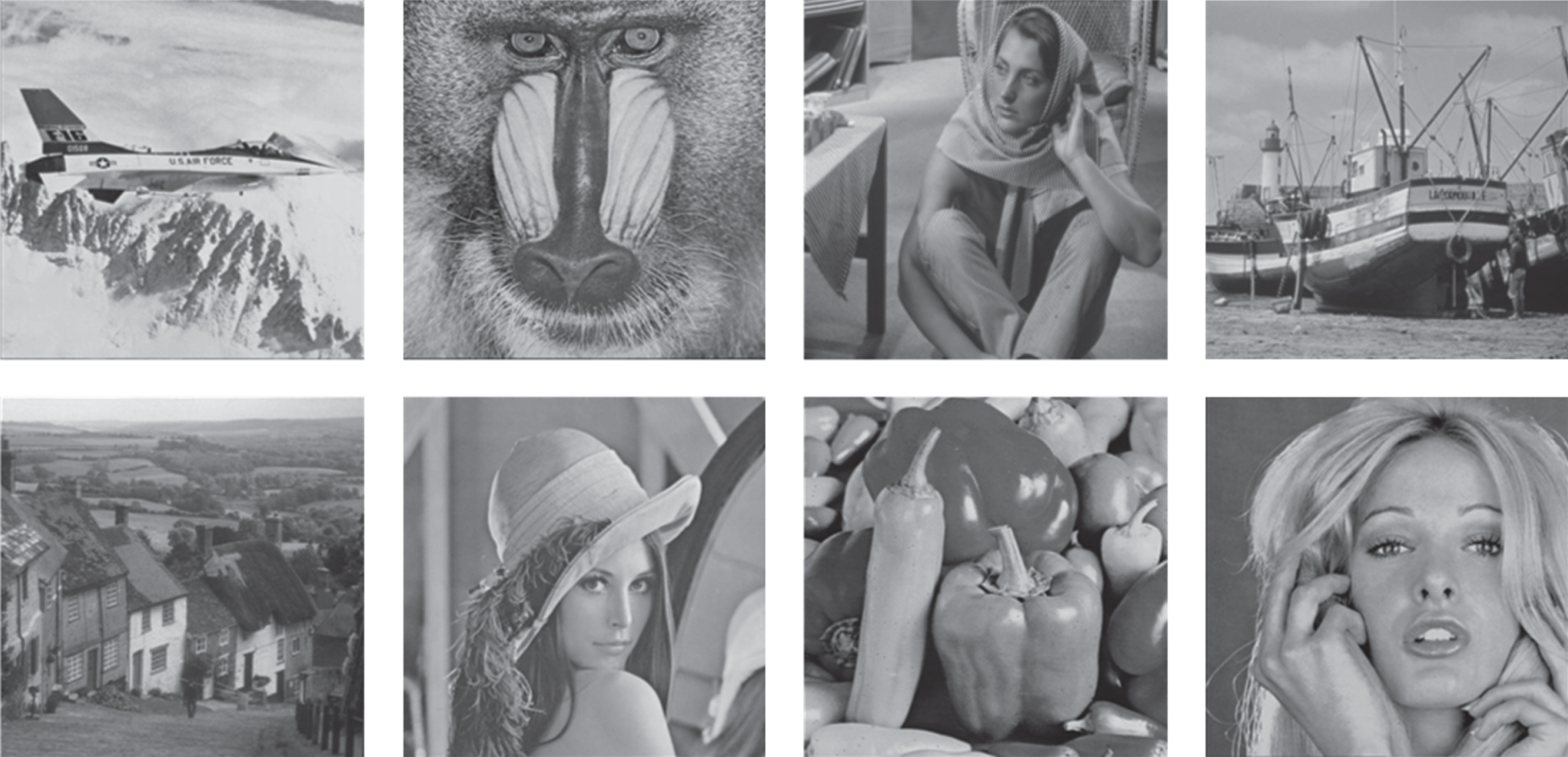
Eight 512 * 512 grayscale images (Airplane, Baboon, Barbara, Boat, House, Lena, Peppers, and Tiffany).
The performance of method in this paper includes embedding capacity, quality of stego-image, and steganalysis.
The embedding capacity is defined as the number of secret bits that can be embedded per pixel (
A larger value of
Six methods’ embedding capacity
The number of pixels in a group is different for each data-hiding method. There are 2,
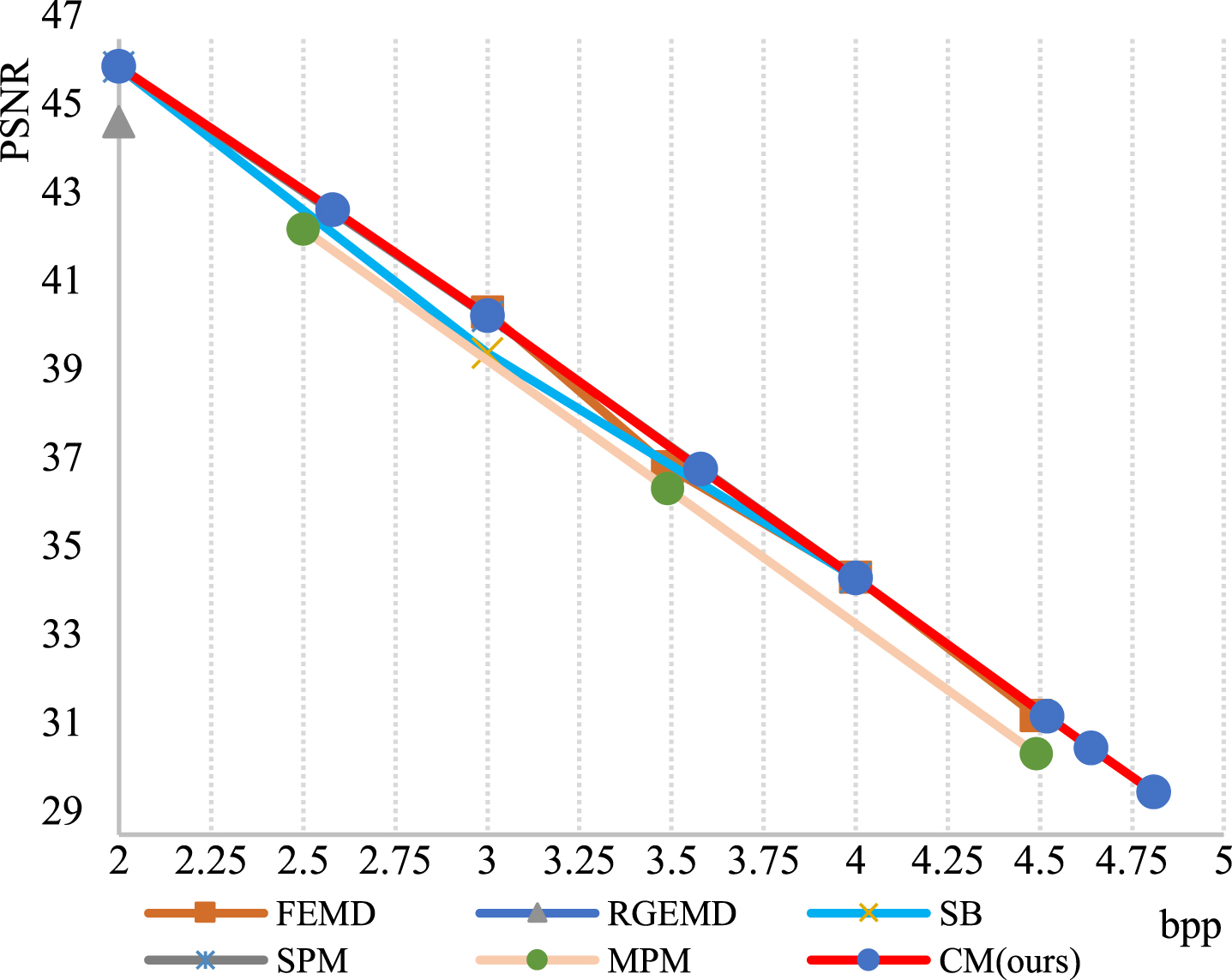
We calculate their specific values and express them in Fig. 5. In Fig. 5, it can be observed that the
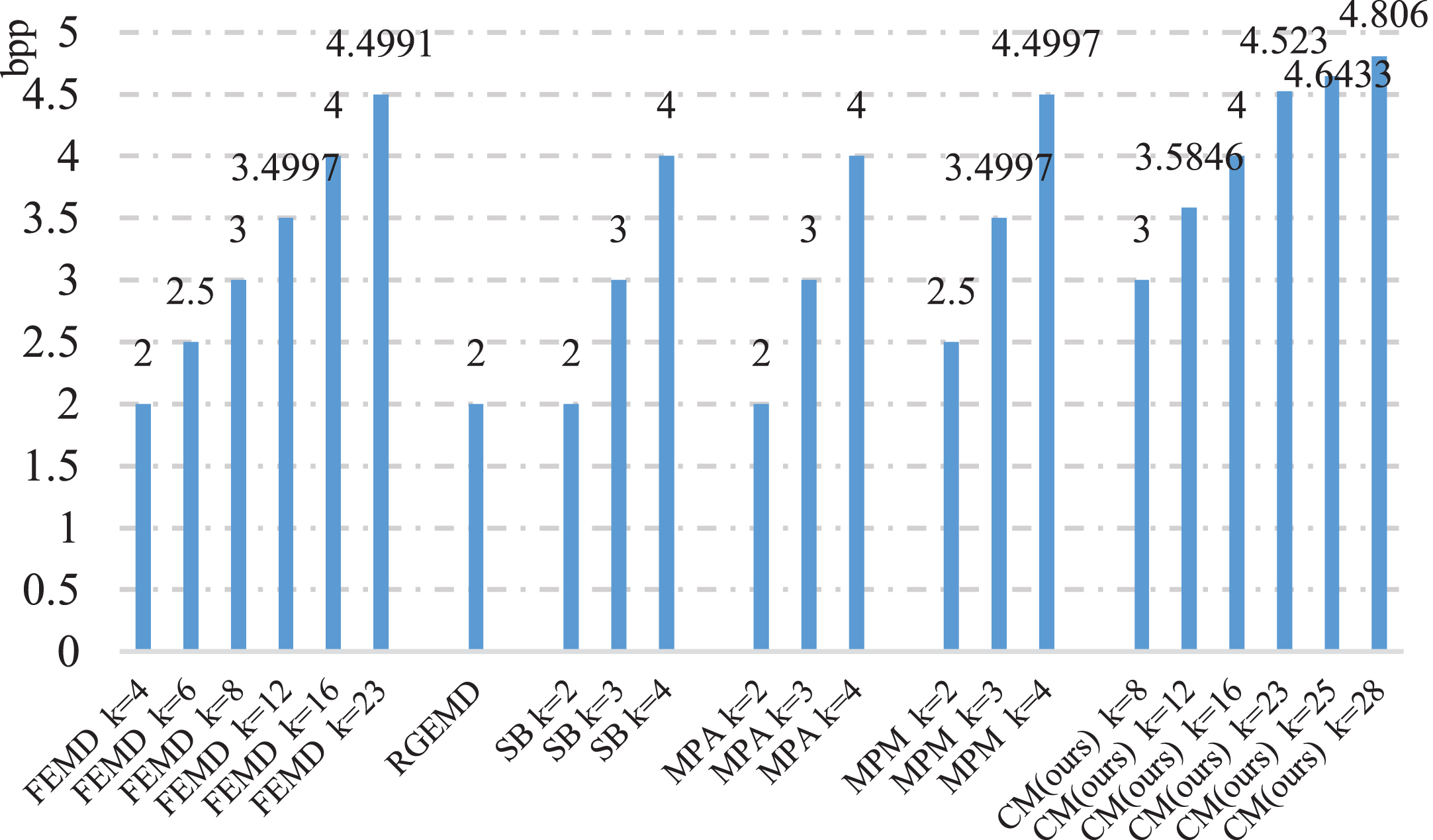
Compare six algorithms’ payloads.
Peak Signal-to-Noise Ratio(PSNR) is commonly used in the field of information security to assess the quality of an image and to measure the degree of difference between the original image and the processed image. PSNR is calculated using the following formula:
Where M and N represent the length and width of the image,
In order to compare and analyze the comprehensive performance of the proposed algorithm, we compared CM with five other algorithms. In this experiment, the embedded secret data consisted of randomly generated bit streams generated by a random number generator. The number of secret data(NSD) is set as 30720 bits and 184,320 bits, respectively. The stego-image of Lena which is embedded with 30720 bits of secret digits is shown in Fig. 6 and the stego-image of House with 184320 bits of secret data is shown in Fig. 7.
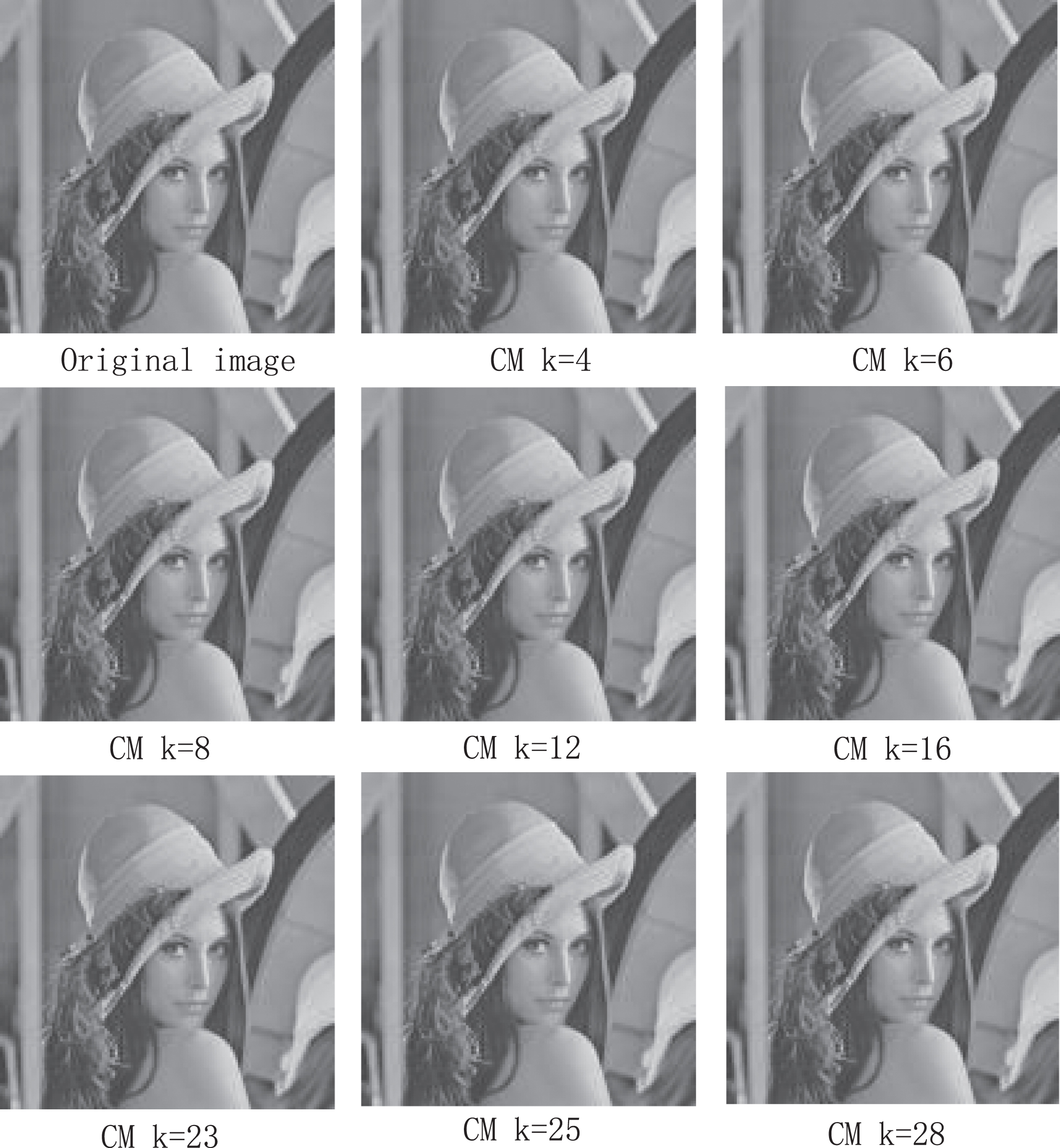
512×512 stego-images of Lena when
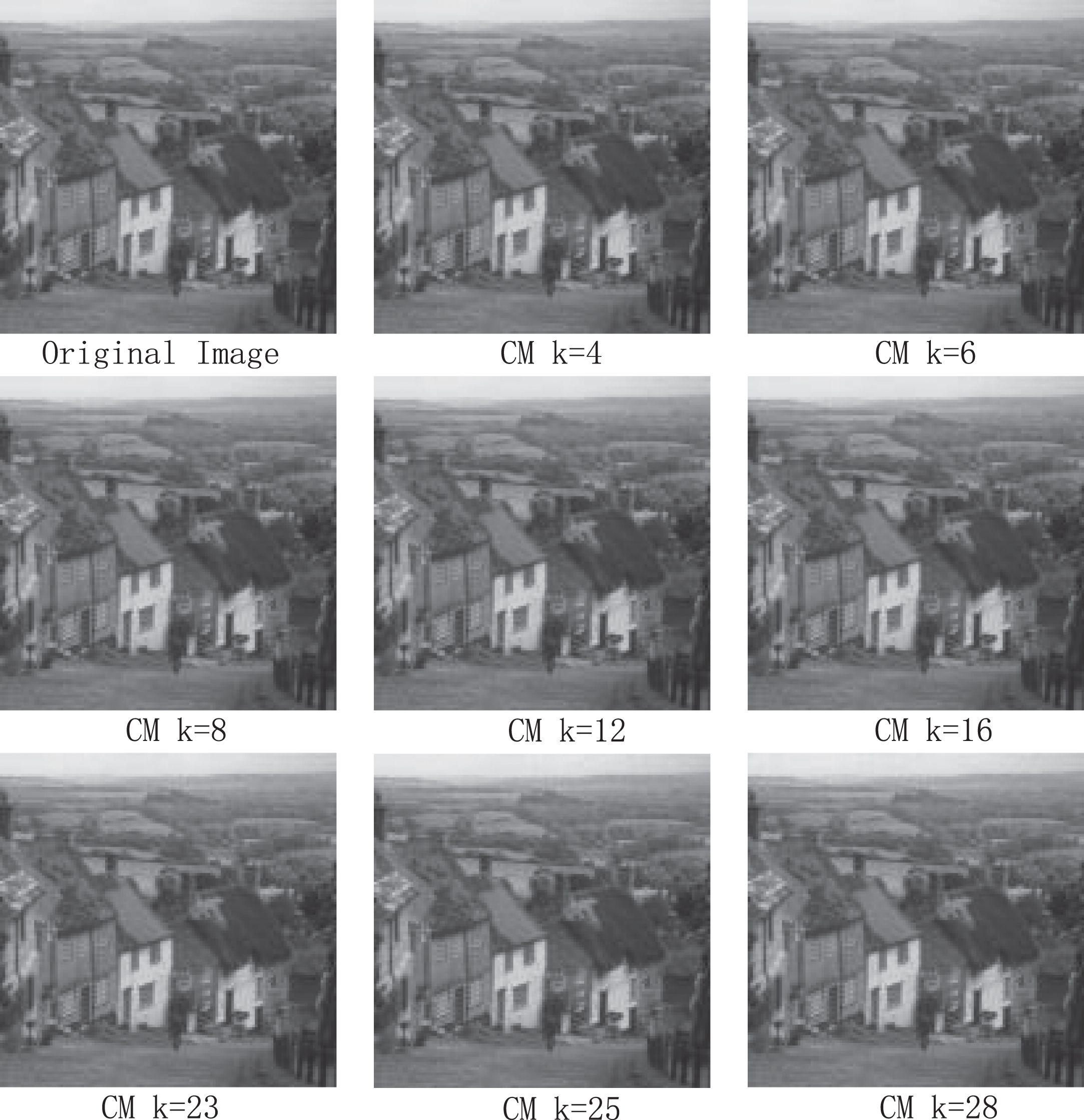
512×512 stego-images of House when
When
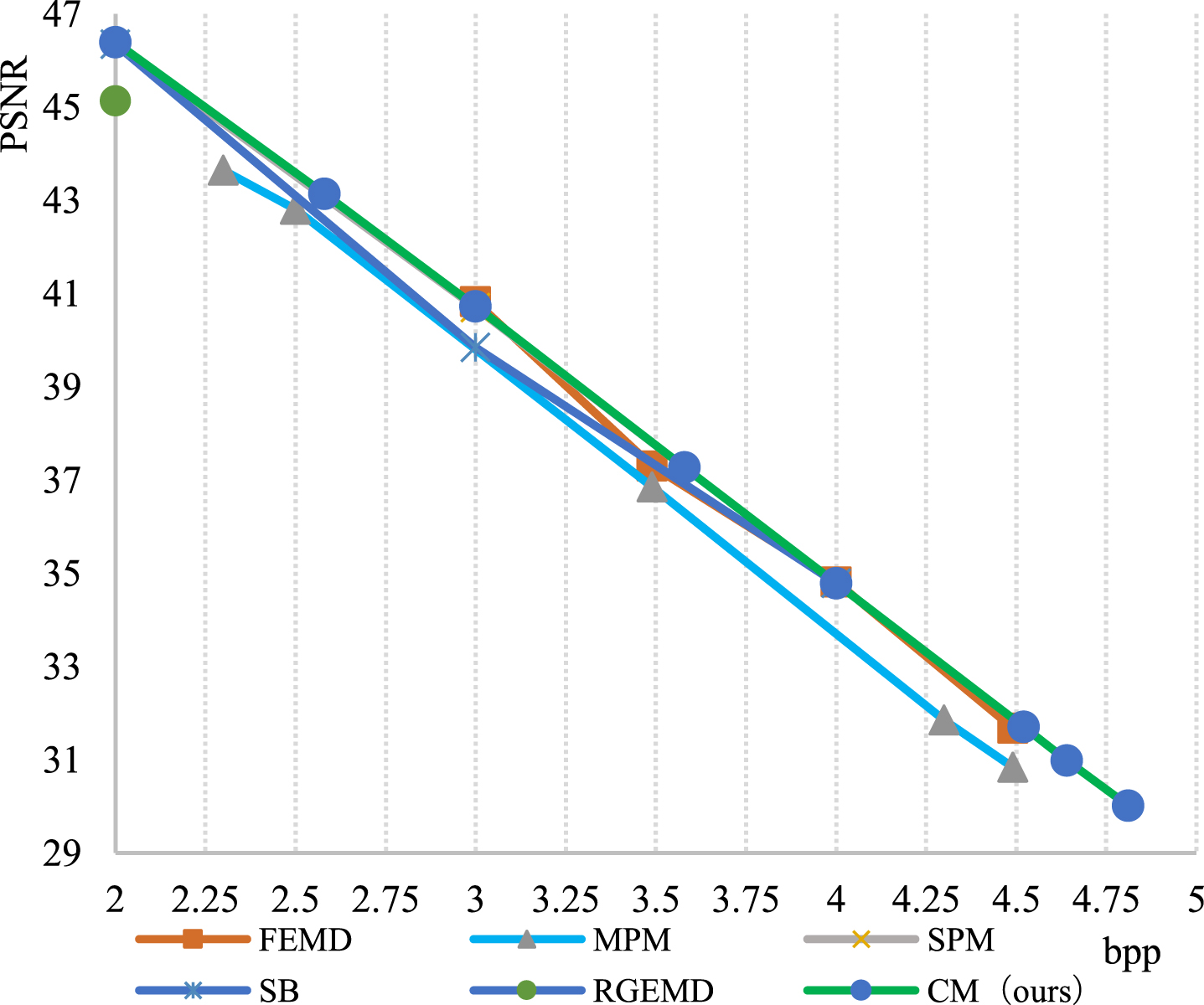
Compare PSNR of stego-image when
The results of comparison when
When
The results of comparison when
Compare PSNR of stego-image when
In summary, CM does better when both embedding capaccity and stego-image quality are considered. The results are shown in Table 2 and Table 3.
Steganalysis is also an important metric for evaluating the security performance of information hiding algorithms. Based on different information hiding algorithms, researchers have also proposed different information hiding analysis algorithms. Information hiding analysis algorithms can detect the presence of secret data in an image and may even roughly extract the secret information.
Bit-plane analysis is one of the information hiding analysis algorithms. Bit-plane analysis represents each pixel value of an image in binary form and groups the binary bits of each pixel according to their level of importance. The distribution and variation of pixels on different bit planes are analysed to reveal features and hidden information about the image. Therefore, we apply this analysis method to further demonstrate the security of the CM method. In this section, we conducted bit-plane analysis experiments on the cover image Lena and the stego images embedded with 30720 bits and 184320 bits of hidden data.
By comparing Fig. 10, Fig. 11, and Fig. 12, it can be observed that there is no significant difference between the bit planes of the original image and the cover image after the bit-plane analysis. This indicates that an attacker cannot extract the hidden data through bit-plane analysis, demonstrating that CM ensures the security of information hiding.
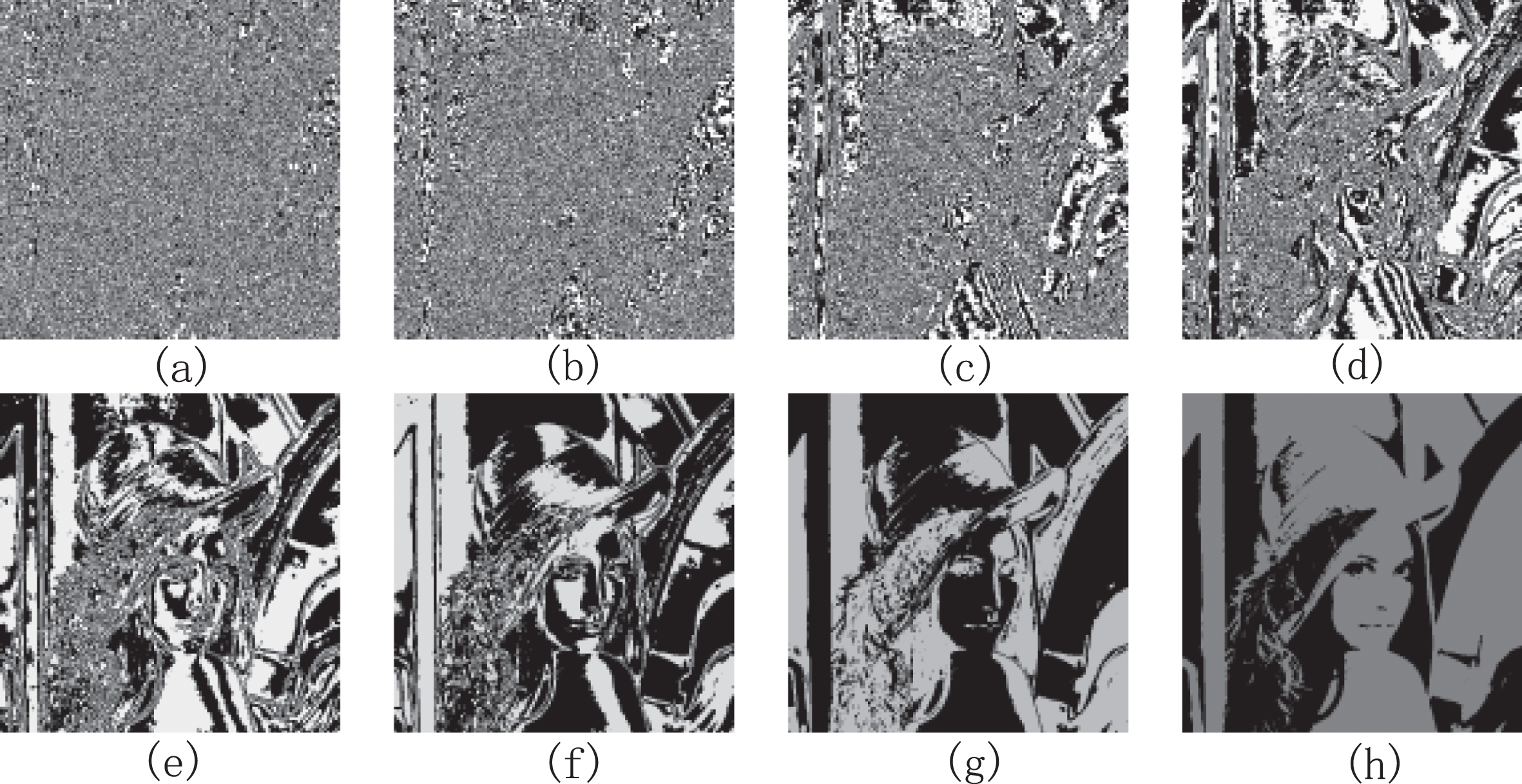
Bit-plane analysis for cover image. (a) 0th bit. (b) 1th bit. (c) 2th bit. (d) 3th bit. (e) 4th bit. (f) 5th bit. (g) 6th bit. (h) 7th bit.
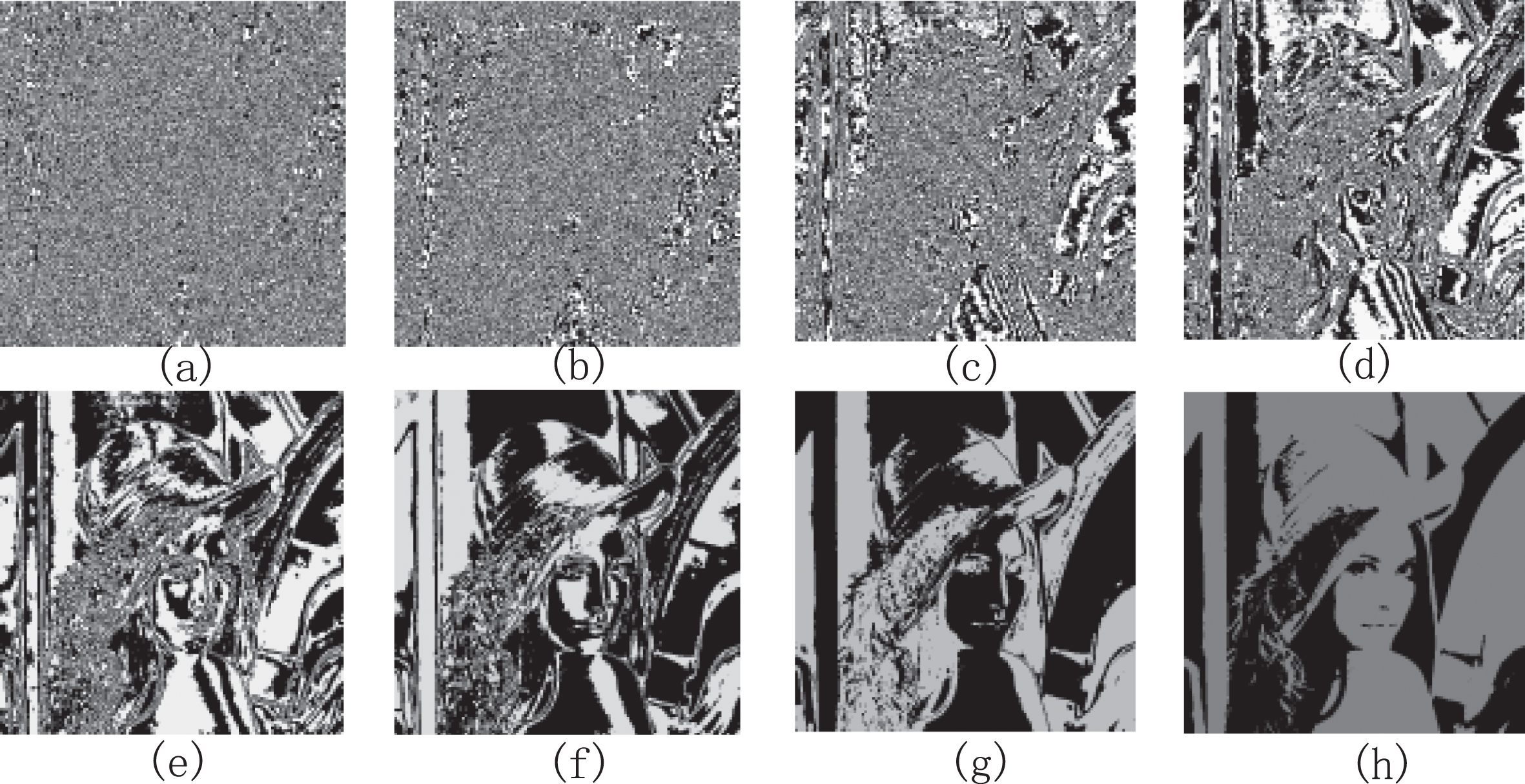
Bit-plane analysis for our method (
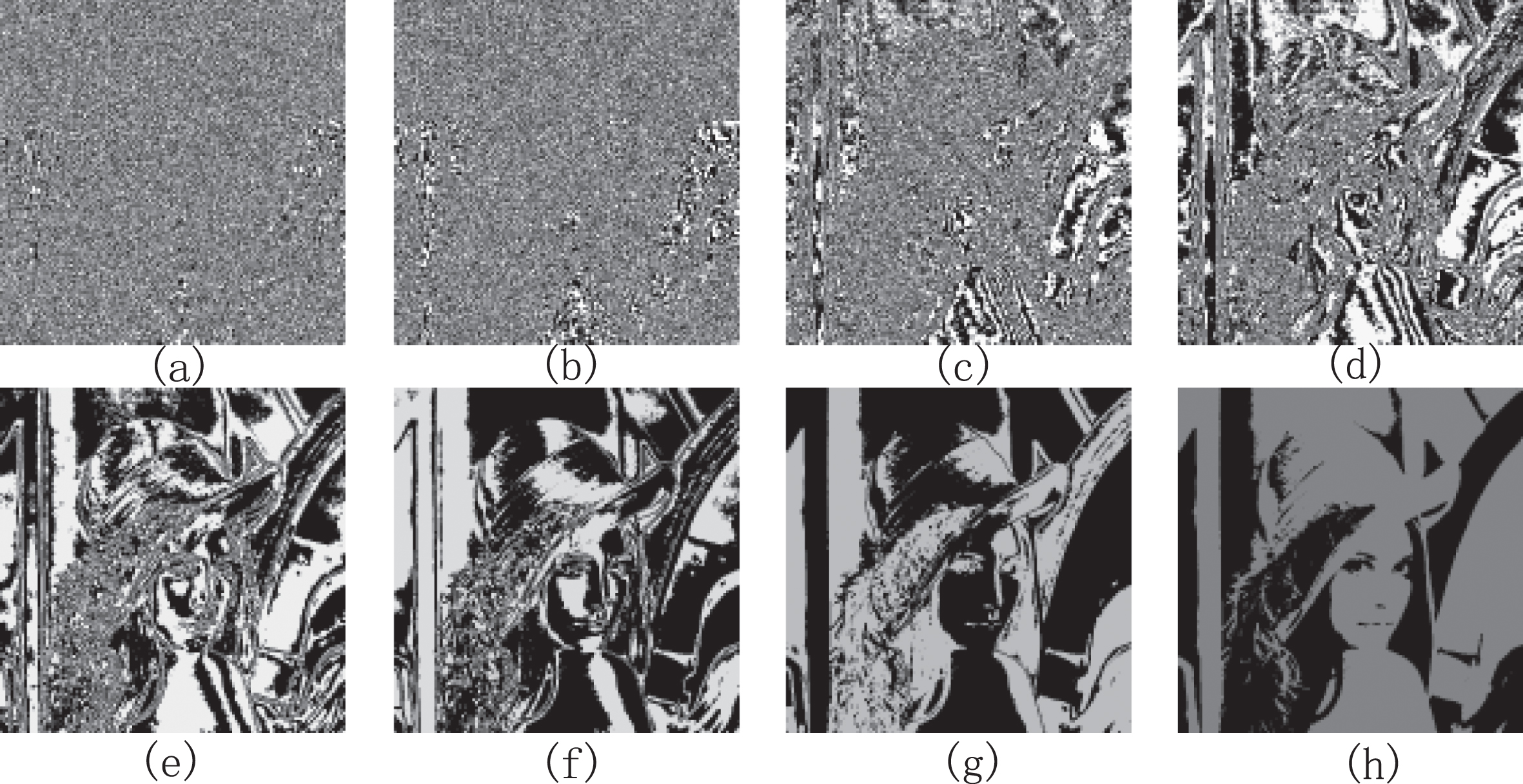
Bit-plane analysis for our method (
In this paper, a novel high-capacity information hiding algorithm CM based on chunking matrix is proposed. The main idea of this method is to divide the image into blocks, where each block represents a piece of secret information. The coordinates of a pair of pixelsfrom the original image are used as the row and column indices in the matrix.Within the search domain at that position, the algorithm searches for the secret information to be hidden and assigns the values of the coordinates at that position as the values of pixels in the stego image. From the above experiments, it can be concluded that CM exhibits advantages such as ease of extraction, high embedding capacity, good stego-image quality, and high security. We have uploaded all our code and data on https://github.com/zhangju85/CM.git. If any researcher is interested in the CM algorithm, please download it and conduct further experiments. Through this approach, we aim to foster the development of more innovative and effective information hiding methods.
