Abstract
Modern information technology has been constantly evolving, transforming the traditional power grid into a network that couples both power and information layers. Understanding the cascade failure behavior of such power communication interdependent networks is essential for effectively controlling catastrophic network failures, preventing system collapse, and ensuring normal network operation. This research can contribute to the development of tools to predict and prevent such failures, and restore normal network functions in a timely manner. This paper focuses on the modeling method and cascading fault analysis of the power-information double-layer coupling network. We construct power information interdependent networks based on IEEE30 system and England39 system, and evaluate the cascade failure results using load distribution cascade failure model and HITS algorithm. The evaluation criteria include network efficiency, residual network size, and residual network load. By analyzing these parameters, we can gain insights into the performance of the power-information interdependent networks during cascade failures. Through simulation results, we demonstrate that the type i attack proposed in this paper renders the network structure unstable and less robust compared to the degree attack, intermediate attack, and random attack. These findings provide valuable references for developing strategies to mitigate the cascading failure of power-information interdependent networks.
Introduction
With the continuous progress of society and technology, the real world is becoming increasingly interconnected, forming a complex network system. One prominent example of such interdependence is the power-information network, which has experienced significant power outages in recent years due to cascading failures. These failures occur when critical nodes within the network fail, leading to a propagation of failures from one network to another. This highlights the importance of identifying and safeguarding these critical nodes in interdependent networks, as they can have a profound impact on the overall system and its performance. It is worth noting that the characteristics of a interdependent network differ significantly from those of a standalone network. In many cases, the connectivity of a interdependent network can undergo drastic changes once a certain percentage of nodes fail. This vulnerability makes the infrastructure nodes of the actual network more prone to failure. Therefore, when assessing network robustness and developing strategies to prevent cascading failures, it is crucial to consider the unique features of interdependent networks. In conclusion, the power-information network serves as a prime example of an interdependent network, where cascading failures can have severe consequences. Identifying and protecting critical nodes is essential for maintaining the stability and reliability of such networks. Additionally, the distinct characteristics of dependent networks must be taken into account to accurately assess their robustness and implement effective preventive measures against cascading failures. The modeling method based on complex network theory has garnered significant attention from scholars worldwide. Rinaldi [1] first introduced the concept of interdependence, and Buldyrev [2] was the first to create a mathematical model of it. The model assumed that each network was characterized as a random graph, with links connecting nodes between the two networks. Through this model, it was observed that failures propagate more rapidly in dependent networks compared to isolated networks, rendering dependent networks more susceptible to attacks. The analysis presented in the literature [3] reveals that both grid and communication networks exhibit scale-free and small-world properties. The literature [4] examines how the structure of interdependent networks affects the behavior of coupled networks, particularly in terms of inter-network coupling modes. The literature [5] introduces an interdependent network model that incorporates shared links among different sub-network types to facilitate resolution computing. The abstract [6] modeling of network systems that depend on power communication is done in the literature using the stochastic network model, the scale-free network model, and the small-world network model. The research methodology of the literature [7] is based mainly on the physical and electrical characteristics of the grid, using classical circuit theory and an exhaustive analysis of the individual components of the system using mathematical analysis. The literature [8] focuses on utilizing the concepts of power law and network connectivity specifically for the analysis of robustness in power systems. The abstract [9] for the first time abstracts the power and the information networks as a stochastic network model respectively, where the information network nodes and the power network nodes are interdependent and coupled one-to-one, if the information network fails, the corresponding power network node fails, and a node of the power network fails with its coupled information network node will also fail. Based on this, domestic and foreign scholars have done a lot of extended research on this modeling method. The literature [10] considers the actual phase-dependent network function to simulate the chain failure process. The literature [11] established a system model based on complex network theory and analyzed and compared the chain failure process of randomly attacking network nodes and attacking high number of nodes, pointing out that attacking high number of nodes will accelerate the chain failure process, in addition, if the communication delay of the system is large, it will also intensify the propagation of the chain failure. The critical nature of the process has been extensively studied using percolation theory. It was then concluded that when a critical part of the network of nodes fails, the system undergoes a first-order phase transition the network of maximum components of nodes suddenly goes from a finite value to zero due to the recursive process of cascade failure. The literature [12] proposes densely coupled networks and sparsely coupled networks. The literature [13] is based on a networked approach with a cascading failure model analysis. The literature [14] investigates cascading failures that arise from node overload and inter-dependencies between different networks. The literature [15] investigates the characteristics of cascading failures in multimodal transmission networks from the perspective of network load redistribution. The literature [16] proposes three metrics of network model structural importance, functional importance and failure-related importance to identify the network critical nodes. The literature [17] used complex network theory to model and analyze cascading faults in power systems and explored the connections and effects between the various nodes in the power system. The literature [18] couples information network nodes with power network nodes one-to-one, and interdependence of this modeling approach has been extensively studied.
A cascade model with locally weighted flow redistribution rules over a weighted network is proposed in the literature [19]. The literature [20] considers the communication transmission process and the information decision process based on the steady-state tidal equation of the power grid, the communication network and information network are modeled in a hierarchical manner. The literature [21] analyzes the reliability of power information interdependent networks from the perspective of connectivity and proposes an edge-adding strategy to improve the robustness of the system. The literature [22] uses an approach based on node load distribution to describe cascading failures with overload behavior on the network based on the local characteristics of the nodes. The literature [23] proposes that cascading failures are related to the degree of centrality of a link in the k-core structure of the network by placing the nodes in the k-core by first deleting all nodes and their associated edges with degree less than k, and then repeating the process by deleting all nodes and their associated edges that now have degree less than k until all remaining nodes have a degree of at least k. The results suggest that failures of a small but variable set of links may lead to a supply network paralyzed. The literature [24] analysis of grid cascade failures has shown that transmission lines prone to overload failures tend to occupy the core of the network and are characterized by connections between highly connected nodes. The literature [25] divides the grid into multiple communities. During the cascade failure, an attack based on the community structure is used. The literature [26] proposes an edge-based dependent network connectivity perspective on a quenched network and points out that it is more robust than node-based dependent network connectivity.The literature [27] proposes the SLE algorithm to identify the important nodes,and it demonstrates that the SLE algorithm is sensitive to factors such as the number of connected components, size of giant components, and shortest distance in interdependent networks.The literature [28] addresses the problem of cascading faults in power information dependent networks, and uses complex network theory to study the topology and network characteristics of power systems, thus exploring the mechanism and law of cascading faults in power systems, and proposing corresponding prevention and control strategies.The literature [29] considers the heterogeneity of nodes in distribution-infophysical systems. By analyzing the directed dependence between heterogeneous nodes in the network, it establishes the distribution-infophysical system interdependent network model. Different network coupling models exhibit different vulnerabilities when facing different attacks. The paper investigates the high dielectric number, high degree number, and random coupling models, but it fails to capture the characteristics of the power grid.
This paper presents a more realistic model of a partially coupled power-information interdependent network based on grid topology. Additionally, it introduces a cascading fault model and HITS algorithm that capture the operational characteristics of a power-information interdependent network under different attack methods. The study analyzes the factors influencing the propagation of faults between the power and information networks, taking into account the inter-dependencies between them. By examining these propagation factors, the research provides valuable insights for optimizing the network structure and enhancing the robustness of power-information interdependent networks.
The rest of this paper is organized as follows. Section 2 constructs the power information dependent network model and cascading fault model and introduces the HITS algorithm. In Section 3,the analysis of experimental simulation results for its IEEE30 and England39 system nodes. Conclusions are made in Section 6.
Construction model construction
Power-information interdependent network model
Using complex network theory modeling, all types of power plants in the power network are abstracted as nodes without distinction, and the high-voltage transmission lines connecting each power plant are represented as connected edges in the power network. The distinctions between the connected edges in the power network are ignored and considered as undirected and unweighted edges. The power networks exhibit the same physical properties, which involve the propagation of electric energy flow. Therefore, the power network can be abstracted as a graph Gp = (Vp, Ep), where Vp represents the set of nodes in the power network and Ep represents the set of edges connecting them. And the communication network can be abstracted as a graph Gc = (Vc, Ec) comprising a set of nodes Vc and a set of edges Ec. Unlike the power network, which primarily focuses on providing power support, the information network has the main task of supervising and controlling the operation of the power network. In this interdependent relationship, when a node in the power network fails, the corresponding node in the information network also experiences failure due to the lack of power support. Thus, it can be concluded that the information network nodes are dependent on the power grid nodes. Specifically, if a power network node fails, the coupled information network node will also fail due to the absence of power supply. This highlights the critical dependency between the two networks, emphasizing the importance of ensuring a reliable and robust power supply for the proper functioning of the information network.
φ
k
denotes the state of the information network node, S denotes the degree of interdependence between the power network and the information network, and S ∈ [0, 1]. A larger value of S indicates a stronger degree of dependence between the power network and the information network. S > 0 causes the state of the information network node to be 0. If S = 0,
The topology of the system adjacency matrix is a way to using complex networks and modeling by means of dependency network theory as:
Where the adjacency matrix of the power grid is A P , the adjacency matrix of the communication network is A c , the coupling matrix of the power network and the communication network is AP-C. If the corresponding two nodes in the adjacency matrix have connections, then a ij = 1, otherwise a ij = 0.
The system consists of two interdependent power and information networks, where two network part nodes interact with their nodes. If some nodes in the power network fail, the dependent nodes in the information network fail, and vice-versa. The dependencies trigger iterative failures in both networks. When the load distribution is completed, the system reaches a steady state and no more node failures occur. The complex network load redistribution model with overload behavior consists of three main factors: load model, capacity model [30], and load redistribution mechanism [31]. In this paper, the load redistribution mechanism model is extended to a two-tier interdependent network.
Node load redistribution within the network makes the load of neighboring nodes overload leading to node failure, which causes cascading failures within the network. In this paper, a node load neighbor redistribution mechanism is used.
Faults in the information network are transmitted to the grid through the dependency relationship. If node b fails, the load of node b will be redistributed to neighboring node c in the same network; if node b is normal, the load of neighboring nodes will remain unchanged. It can be expressed as:
Removing a node in the network changes the network topology, redistributing the traffic load and causing other nodes in the network to fail due to overload. The removal of a node from this network will result in the failure of its dependent counterpart in another network. Removing a failed node will lead to similar cascades in other networks and may also lead to fragmentation of the whole system.
In this paper, the HITS algorithm is utilized to investigate cascading faults in power-information interdependent networks and identify the nodes that play a crucial role in information dissemination and connectivity. The HITS algorithm (Hubs and Authorities) is a network analysis algorithm for evaluating the authority (Authority) and the degree of hubs (Hub) of nodes in a network. The algorithm considers that nodes with high authority in a network will be referenced by other nodes, and nodes with high hubs will link to other nodes with high authority. The basic idea of the HITS algorithm is to calculate the authority and hubs of nodes by iteration. The following are the general steps of the HITS algorithm: Initialization: Given the power-information interdependent network graph, assign initial authority and hub values to each node. Iterative calculation: Calculate the node’s authority value: The authority value is calculated based on the node’s entry degree. The authority value of a node is equal to the sum of the hub values of the nodes it is connected to. Calculating the pivot value of a node: The pivot value is calculated based on the outgoing degree of the node. The pivot value of a node is equal to the sum of the authority values of the nodes it is connected to. Normalize: After each iteration, the calculated authority and pivot values are normalized so that they sum to 1. Iterative update: Repeat steps 2 and 3 until convergence or the preset number of iterations is reached. Output results: Based on the final calculated node authority values and pivot values, the key nodes in the network can be identified. Nodes with high authority values are considered as authority nodes in the network, and nodes with high hub values are considered as hub nodes in the network.
Nodes with high Authority values indicate components that are more susceptible to faults, while nodes with high Hub values indicate components with a stronger capability for propagating faults. By identifying nodes with high Authority values and Hub values, appropriate measures can be implemented to mitigate and reduce the occurrence of cascading faults, thereby enhancing the safety and reliability of the power system. Based on the Authority values of nodes, it becomes possible to determine which components in the power system exert significant influence on other components. Nodes with high Authority values suggest that their failures may result in failures in other nodes, consequently triggering cascading effects. Therefore, by identifying these nodes with high Authority values, suitable measures can be taken to enhance the system’s immunity and stability. Similarly, based on the Hub values of nodes, it can be determined which components play a bridging role in the network, connecting different subsystems or critical nodes. Nodes with high Hub values indicate that their failure could lead to the failure or disruption of the entire network. Hence, by identifying these nodes with high Hub values, their monitoring and protection can be enhanced to ensure the connectivity and reliability of the network.
This paper takes into account the impact of interdependent networks on critical nodes. The authority and hub values of node Ip in the grid and node Ic in the information network were first calculated. The importance of nodes in the coupled network is calculated from the dependency matrix.
By using the MATLAB simulation platform, a power-information interdependent network model is constructed based on the IEEE 30 and England 39 system from the IEEE standard test system database. Cascading faults are studied and analyzed using this model. To reduce the influence of randomness, each simulation experiment is conducted 1000 times. Four attack strategies are set in this paper, including degree attack, betweenness attack, I-attack, and random attack.
The power network is constructed based on the IEEE30 and England 39, the information network is constructed based on the BA model, with both networks consisting of 30 nodes and 39 nodes. The power information interdependent network model is then constructed using the aforementioned method.
The number of degrees, betweenness, and central importance of each node in the power grid and information network are calculated, and the nodes are ranked in descending order based on their values.
Based on the definition of node initial load and node capacity threshold in the load redistribution model, the initial load and capacity threshold of all nodes are calculated. Then, the initial states of nodes in the network are defined by assuming that all nodes are in a normal state.
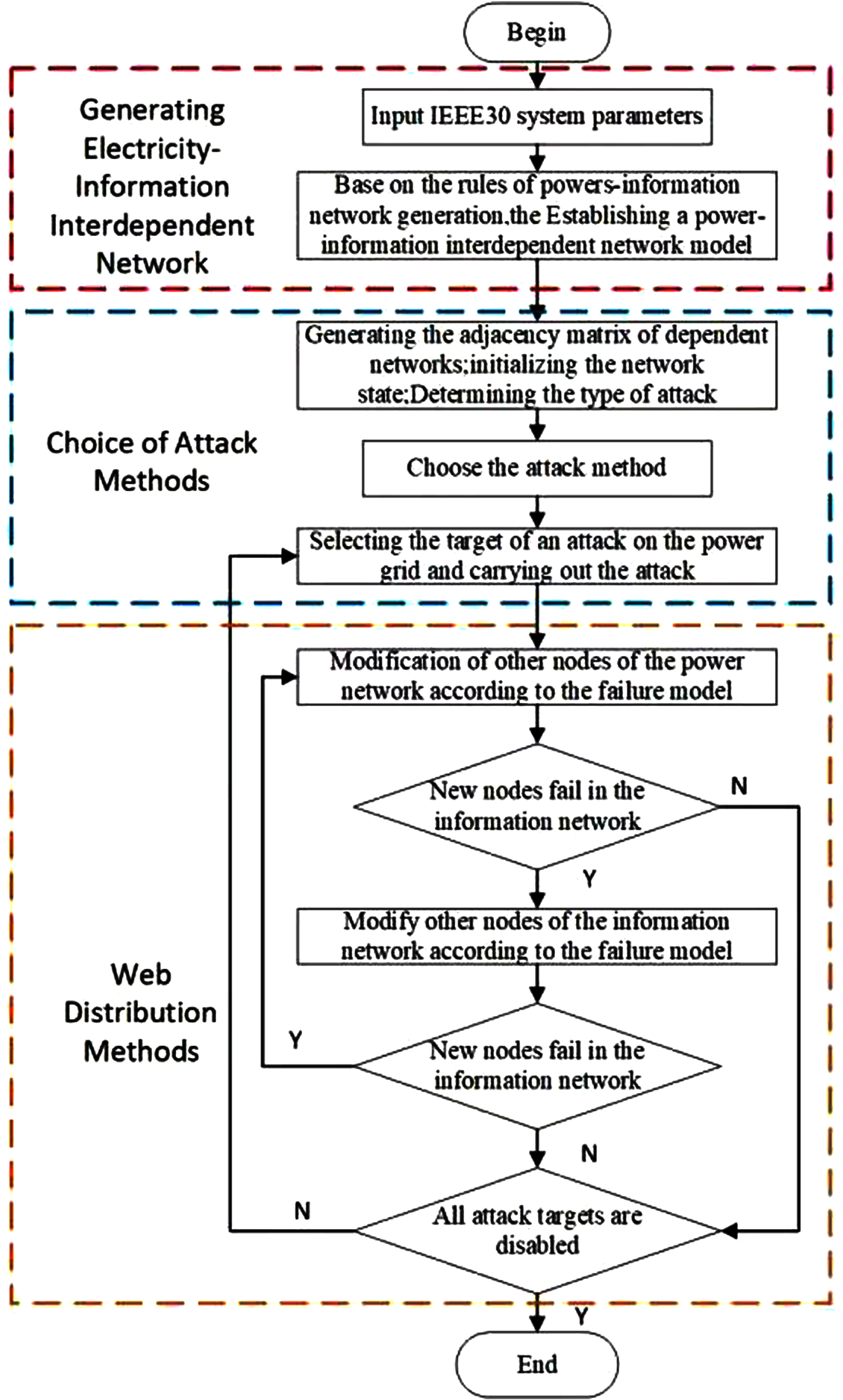
Power-information interdependent network cascade fault propagation model construction process.
The aim of the experiment is to explore the cascade failure law of the power-information interdependent network.
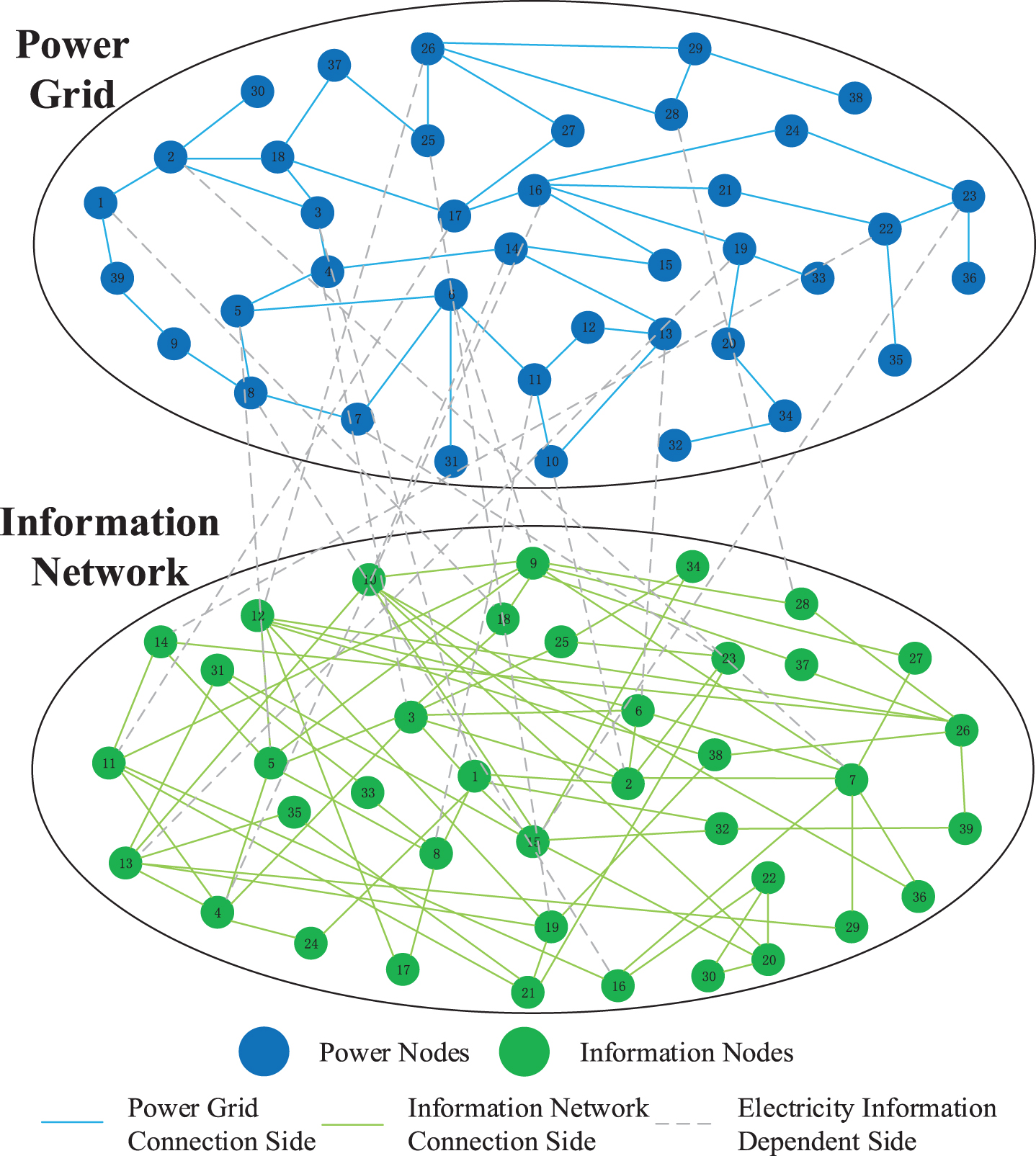
As shown in Fig. 2, blue is 30 nodes of power network, green is 30 nodes of information network, the internal connection edge of the network is represented by solid line, and the interdependent edge between power network and information network is represented by dashed line to construct the power-information interdependent network model.
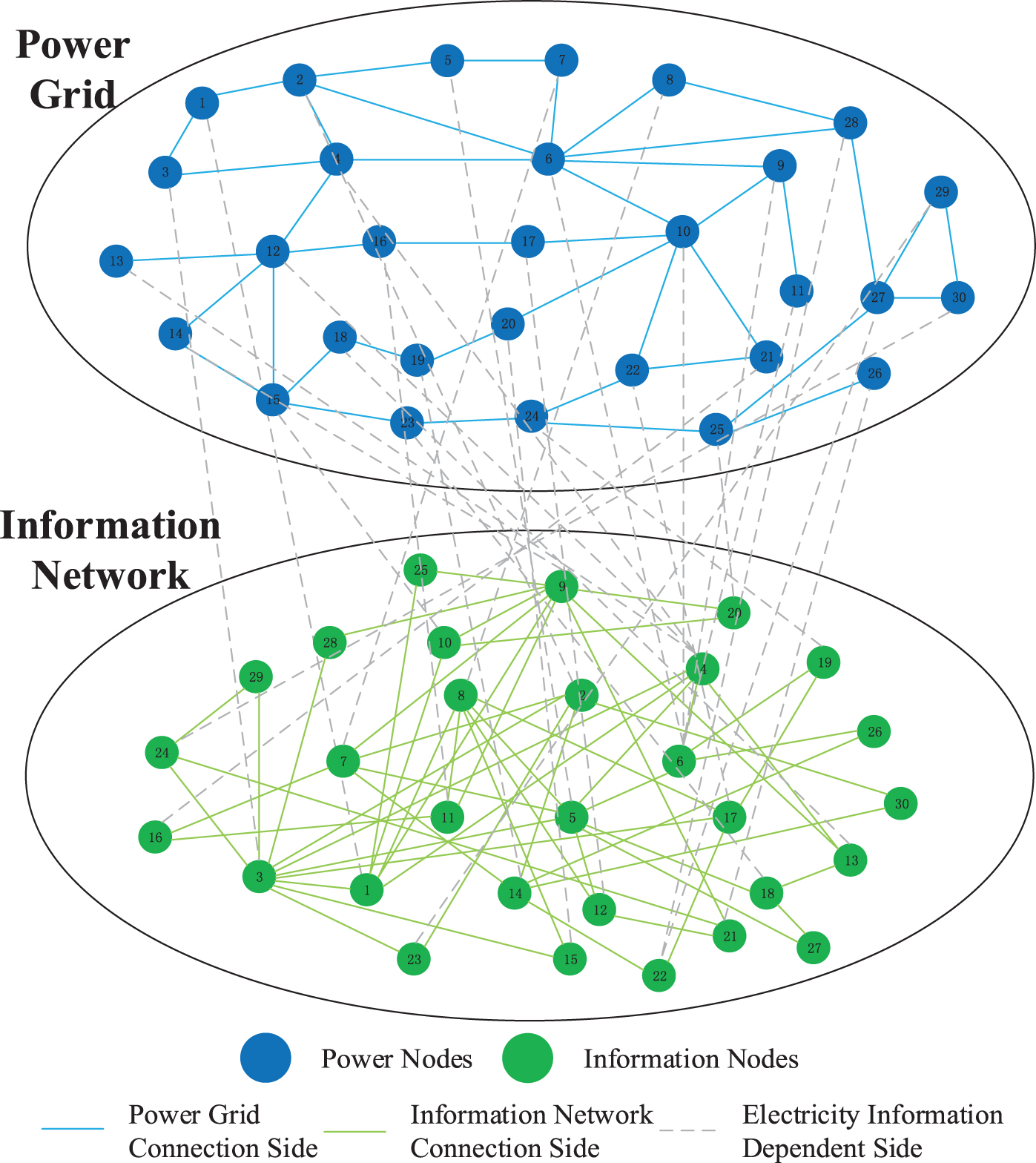
Power-information interdependent network 30 nodes visualization model.
Table 1 shows the IEEE30 node calculation authority and hub value. High authority value of generator nodes. Because generator nodes are usually directly connected to other important nodes (e.g., substations, load nodes, etc.), they transmit power to other locations through transmission lines. These connections give generator nodes more influence and authority in the power system. Nodes with high hub values have more connections or higher degrees with other nodes.
IEEE30 node calculation authority and hub value
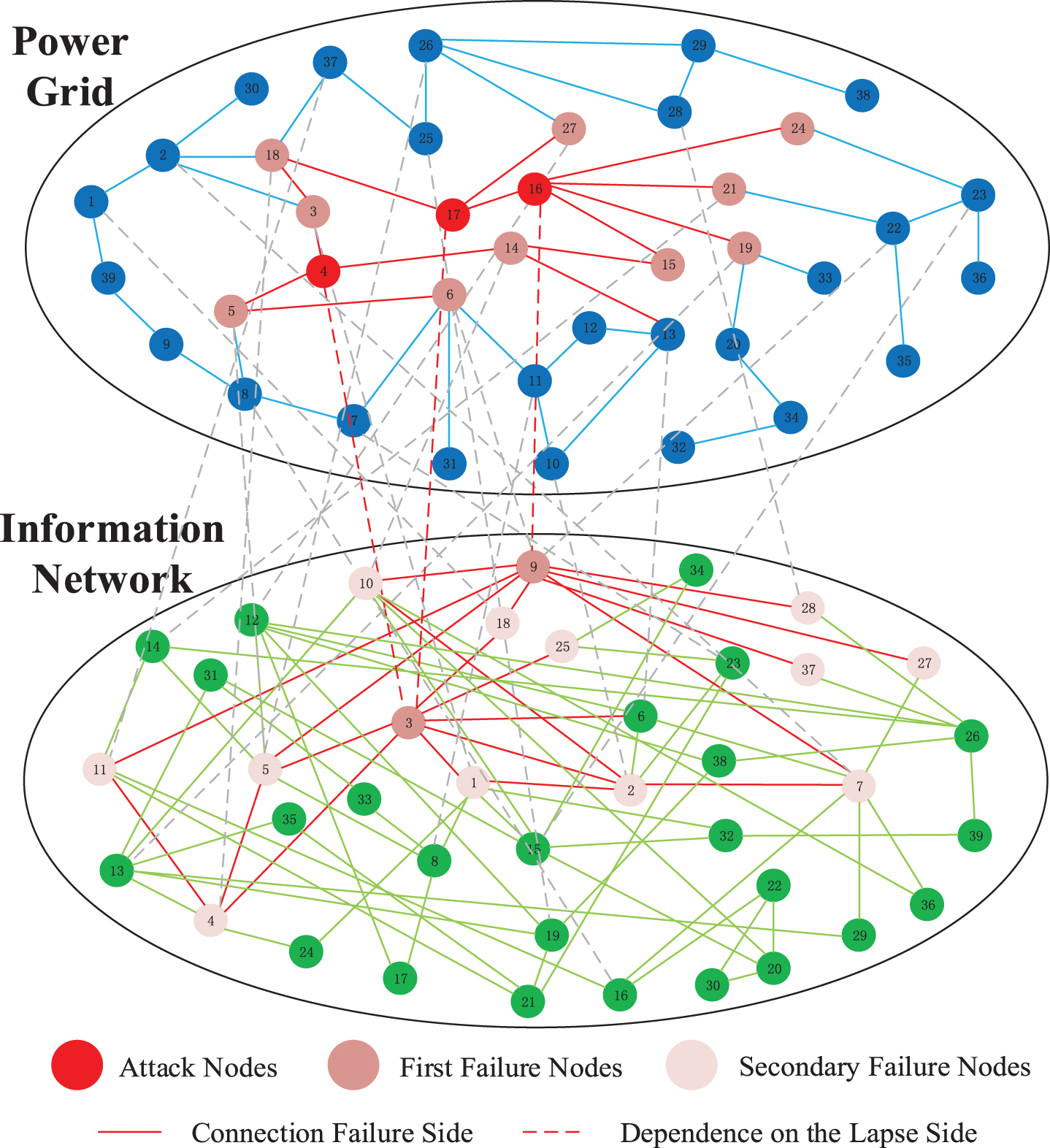
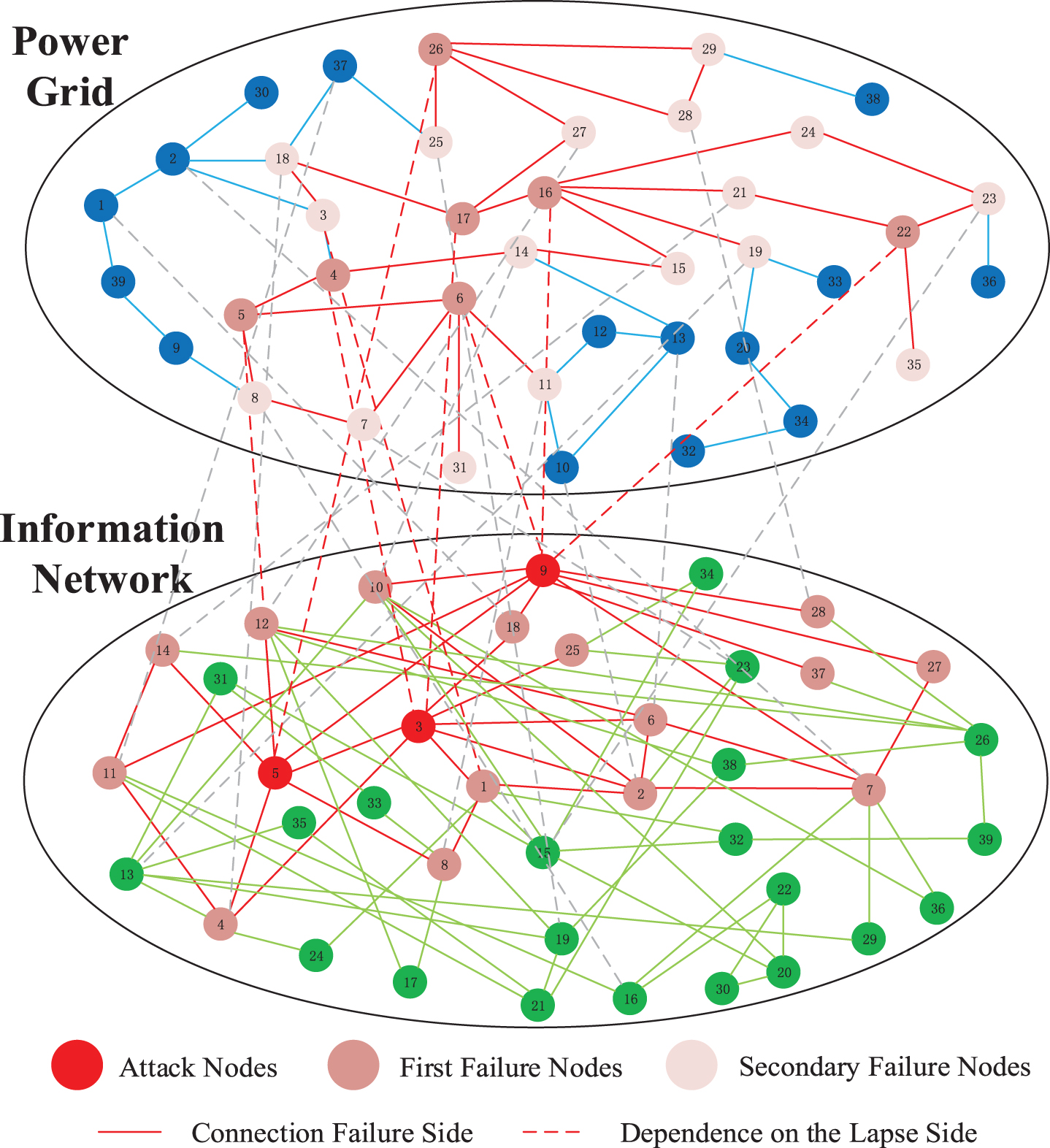
Figures 3 and 4 show the power information dependent network (30 nodes). After attacking the red node, the nodes and edges connected to it will also fail. where the connection between the information network nodes is very tight. The comparison between Fig. 3 attacking the power grid and Fig. 4 attacking the information network shows that the same attack on three nodes, attacking the information network makes the network fail more nodes and the network structure is more unstable. Attack nodes with high authority and hub values. Nodes with high hub values can quickly spread their influence to other nodes. Therefore, it is critical to protect the security and stability of the information network with appropriate protective measures, monitoring and response mechanisms for the high authority and hub value nodes of the information network, as well as strengthening the network’s robustness and resistance to attacks.
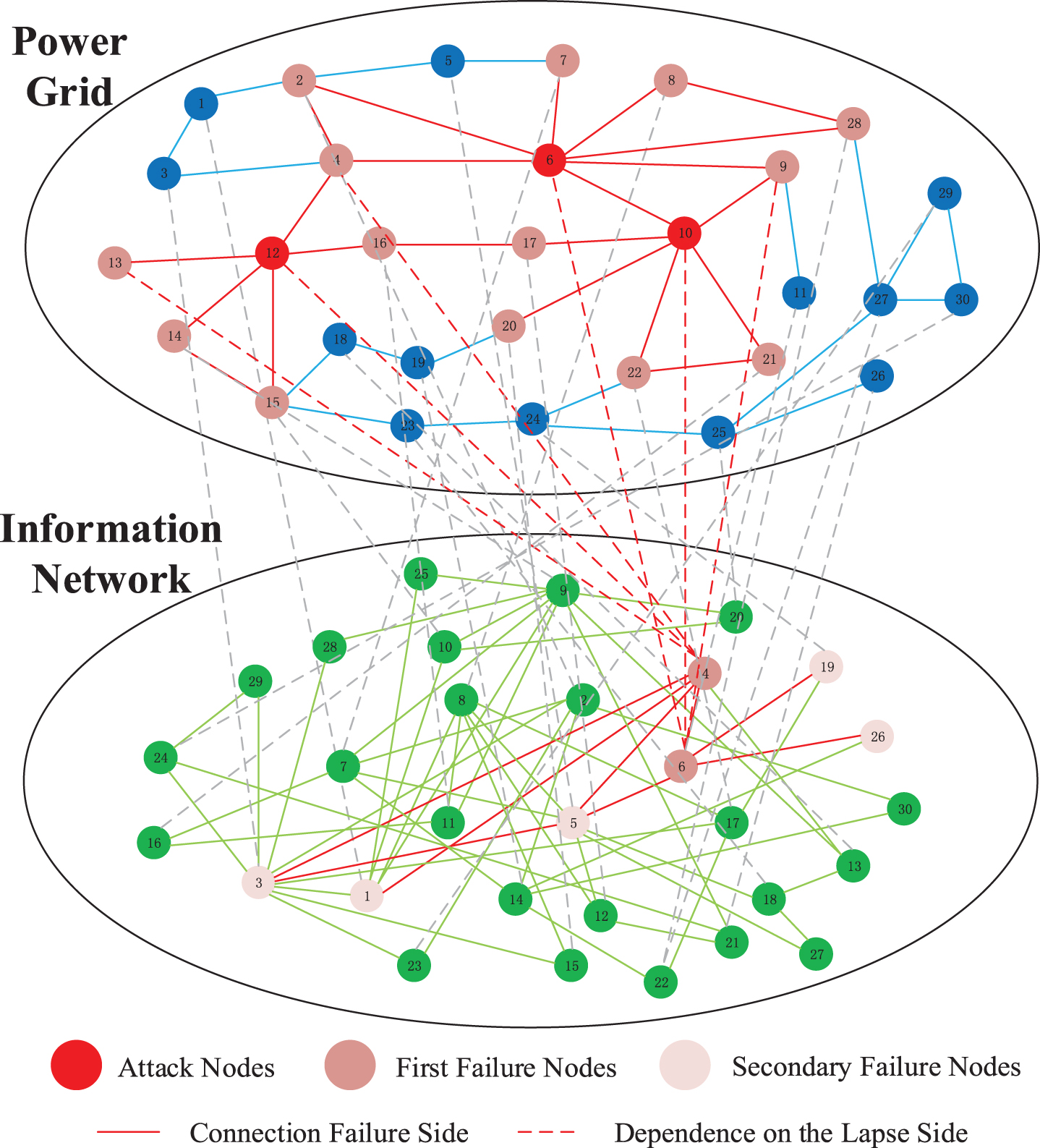
Attacking 30-node power grid.
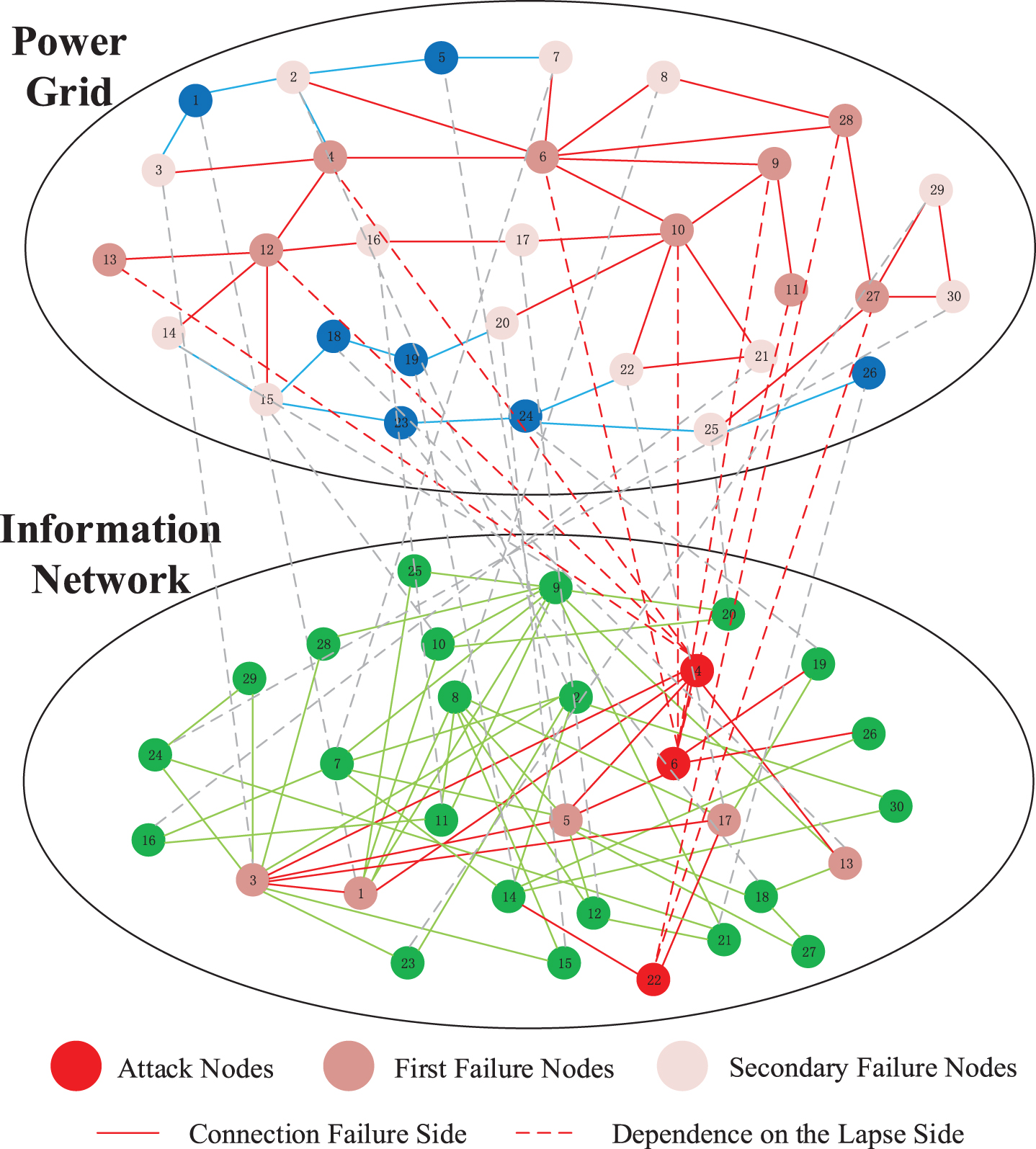
Attacking 30-node information network.
As depicted in Fig. 5, the power network comprises 39 blue nodes, while the information network consists of 39 green nodes. The internal connection edges within each network are depicted using solid lines, while the interdependent edges between the power network and information network are represented by dashed lines to construct the power-information interdependent network model. Table 2 presents the calculation results for the authority and hub values of the IEEE39 nodes. Figure 6 illustrates a diagram depicting an attack on the England39 node grid, whereas Fig. 7 presents a diagram illustrating an attack on the information network.
Power-information interdependent network 39 nodes visualization model.
Attacking 39-node power network.
Attacking 39-node information network.
IEEE39 node calculation authority and hub value
Network efficiency reflects the connectivity of a network, and the better the connectivity of the network, the more efficient the network is. Network efficiency η is defined as follows:
The rate of network efficiency degradation caused by removing nodes (edges) μ expressed as:
The residual network size refers to the number of nodes or systems in the network that are still functional in the case of cascading failures. As the number of attacks increases and more nodes fail, the network residual size becomes smaller and smaller. Usually, the smaller the remaining size of the network, the lower the stability and availability of the network, because the failure of any one node or system in the network may lead to the failure of more nodes or systems.
The residual load of the network reflects the load residual rate of the nodes in the network. As the cascade failure process evolves, the failed load is redistributed to the neighboring nodes and continues to operate within the allowed range of the node capacity, and the larger the residual load of the network represents the larger the load of the network after the node failure.
The next HITS algorithm is referred to as I. Figure 8 shows the comparison graph of attacking 30-node grid and information network to analyze the impact of power-information interdependent network cascading failure in terms of three indicators: network efficiency, network residual size, and network residual load. Figure 9 shows a comparison of the attack on the 39-node grid and the information network. The left side of the picture is the attack power network, the right side of the picture is the attack information network. (a) and (b) are network efficiency; (c) and (d) are network residual size; (e) and (f) are network residual load. The horizontal coordinates of the following images all indicate the number of attack nodes, and the vertical coordinates indicate the network efficiency, network residual load, and network residual size, respectively; the black line indicates an attack on a high number of nodes, the blue line indicates an attack on a high intermediate number of nodes, the green line indicates a random attack, and the red line indicates an attack on a high I node. The comparison in the figure shows that the other three attack strategies lead to a greater reduction in the network efficiency, network residual size, and network residual load of the system compared to the random attack strategy. In the initial stage of the attack, the I attack strategy has a greater decay in network efficiency than the other three attack strategies, which implies that the I approach has a greater degree of impact on the power-information interdependent network. In particular, when the number of consecutive attacks reaches six, the residual network size and residual network load under the I strategy drop to almost zero. Obviously, the nodes with higher I value are more important to the network. In practice, if high I-value nodes are more protected, the network is better protected from large-scale failures, the network structure is more stable, and the network is more robust. Therefore, it is necessary to implement protection measures for high I value nodes. In addition, the arrangement and protection of these nodes should be given priority during the network design and planning process to improve the robustness of the network.
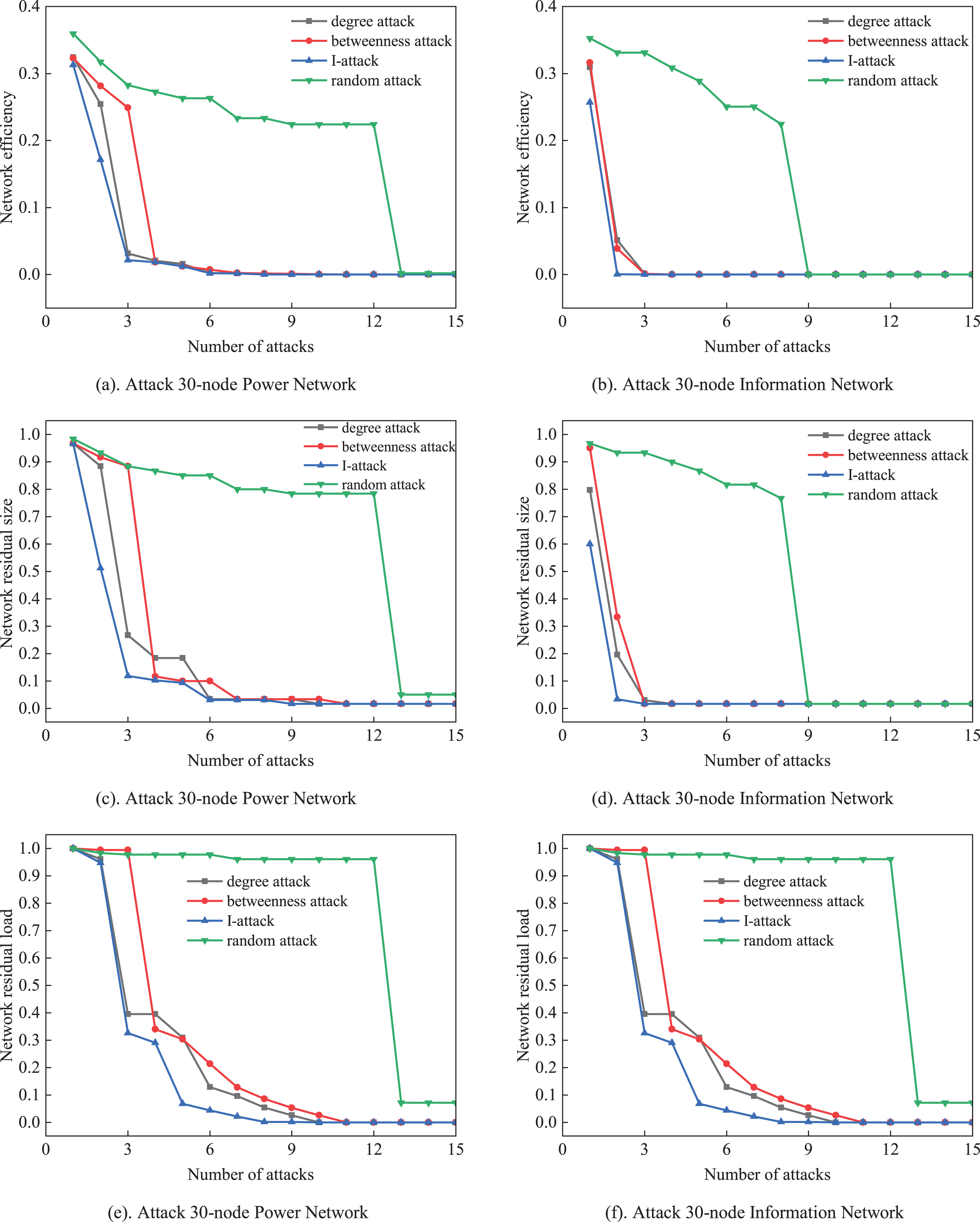
Attack 30 nodes compare of the power and information network.
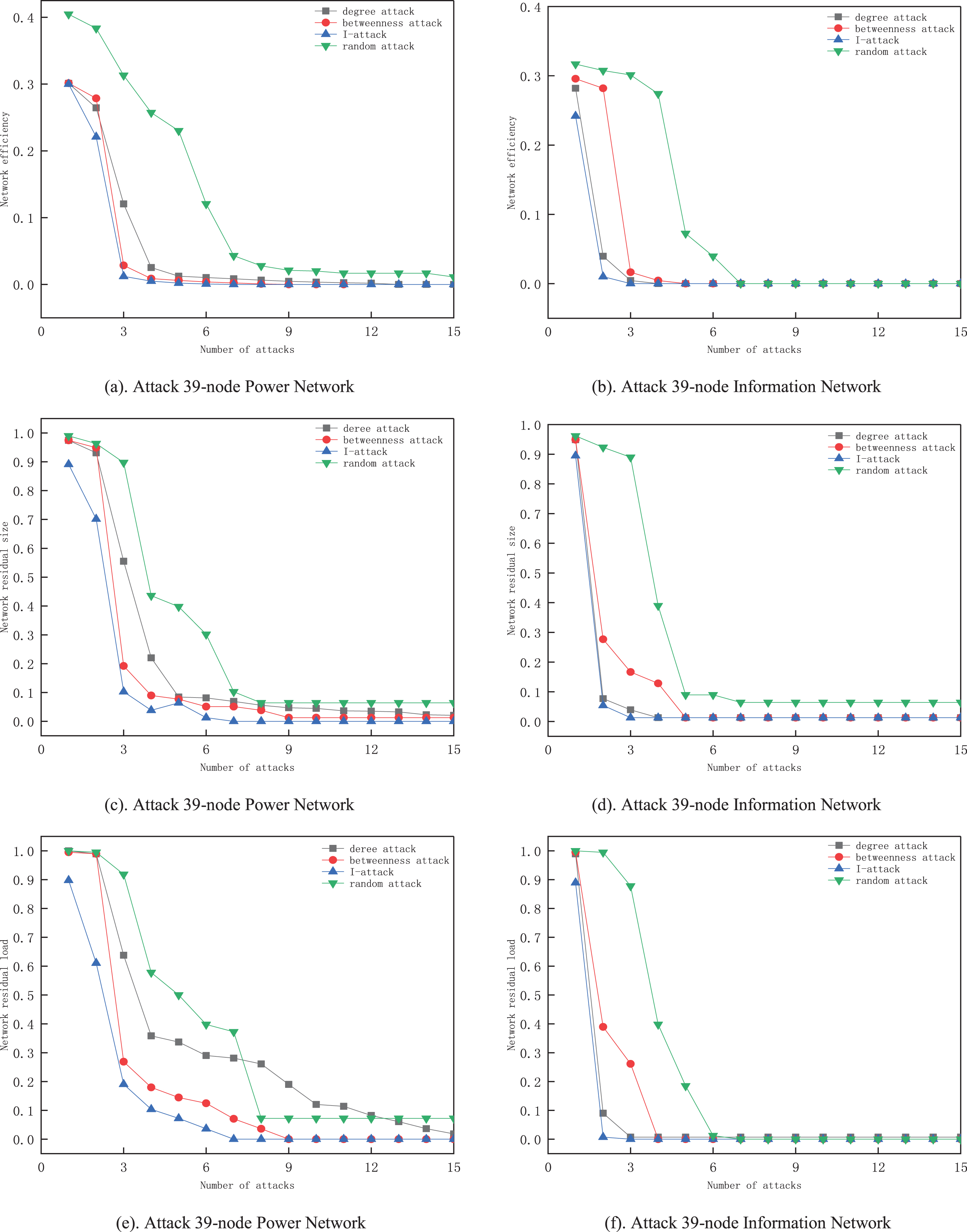
Attack 39 nodes compare of the power and information network.
By using the I method to attack the nodes in the power grid and the information network, as shown in Figs. 10 and 11, it is observed that the number of attacks on the information network is much smaller than the number of attacks on the power grid. It is clear that attacking the critical nodes in the information network causes the highest level of damage to the system. Therefore, the failure of the information network has a greater impact on the interdependent network compared to the failure of the grid. This conclusion is consistent with the actual operation of the grid, the safe and stable operation of the grid requires real-time monitoring of the grid status by the information network. In practical application, to avoid the occurrence of large-scale cascading failures, the protection of important information nodes should be strengthened. Network design and planning should give priority to the arrangement and protection of important nodes to ensure the robustness of the system
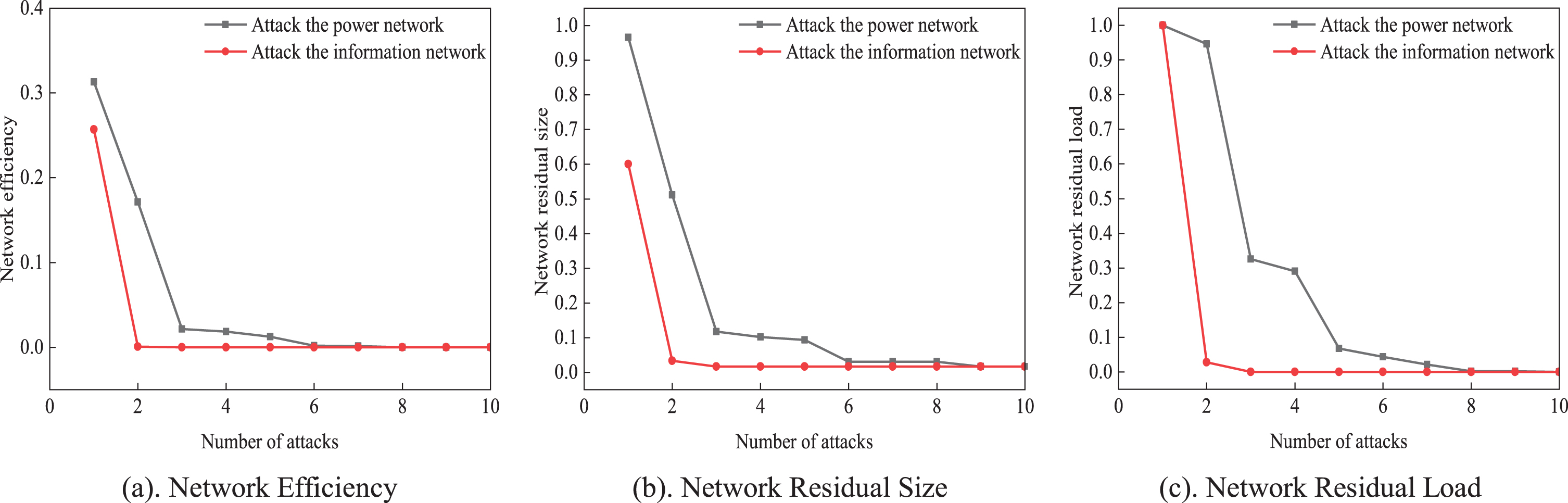
Attacking 30-node power-information network.
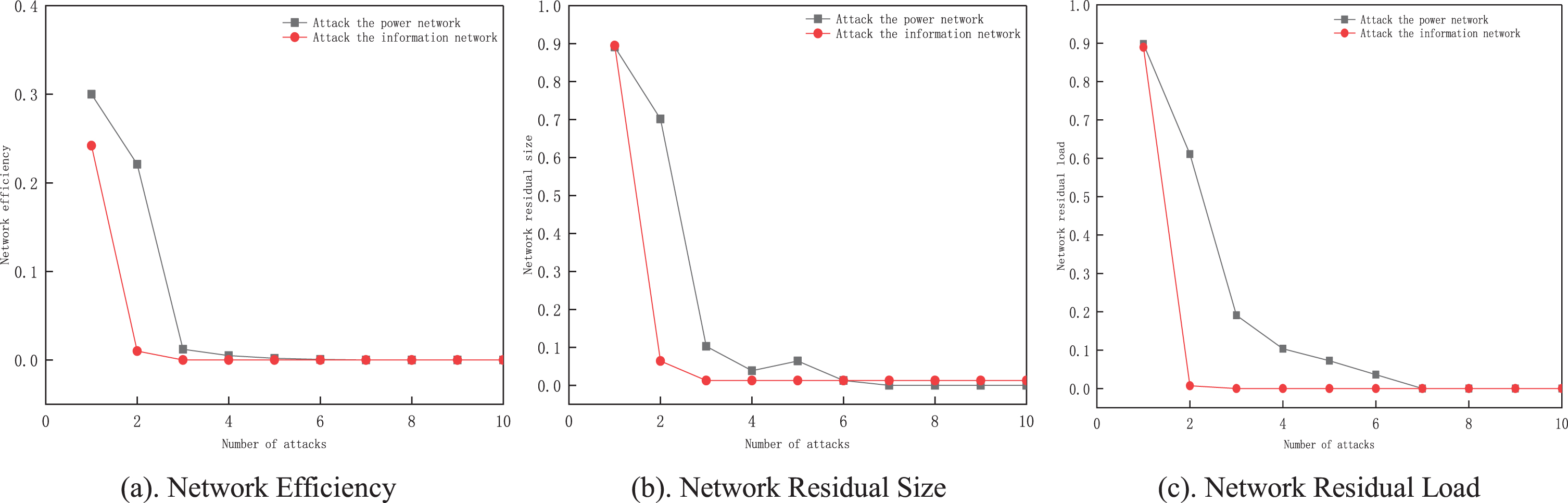
Attacking 39-node power-information network.
With the continuous development of smart grid and the deepening integration of power system and information system, it is important to study the structural characteristics of power information interdependent network and analyze the cascading faults, especially to focus on the destructiveness of deliberate attacks on interdependent network. In this paper, we analyze the interdependence and interaction between components in the power information system and construct a power information interdependent network model and a cascading failure model based on practical interdependence between components. To better analyze critical components in the practical system, we propose an attack method based on node degree, betweenness centrality, I-attack, and random strategy. Furthermore, we conduct cascading failure analysis of the power information interdependent network system under different attack strategies and targets using the MATLAB simulation platform. The simulation results show that the I-attack strategy causes higher damage to the system than the other attack strategies. The failure of the information network causes more damage to the system than that of the power network, so it is essential to strengthen the protection of critical nodes in the information network to ensure the safe and stable operation of the power system. The next direction is to determine the application of the method to larger and more complex networks and to improve the robustness of the power information dependence network.
In summary, this paper provides a new approach to evaluate the impact of cascading failures in power information systems when different attack strategies occur and highlights the importance of protecting critical nodes in the information network. The results can serve as a reference for the design and planning of power information systems, especially in ensuring their reliability and stability.
Footnotes
Acknowledgments
This work was supported by the Natural Science Foundation of Jilin Province (Grant 20230101238JC), Scientific Research Program of Jilin Provincial Department of Education in 2023 (Grant JJKH20230065KJ), and Jilin Provincial Department of Education Scientific Research (Grant JJKH20220050KJ).
