Abstract
Blockchain technology holds considerable amount of potential for all types of industries by executing transactions in a verifiable, efficient, and permanent channel. It has been widely viewed as a standard requirement for making industry ready for the future, but when it comes to practical applications, it still arouses numerous risks/challenges that need to be addressed. Therefore, it is essential to address this gap and establish a comprehensive and effective practical framework to align the information technology revolution with sustainable value creation. The purpose of this research is to realize to what extent an enterprise legacy system’s transformation benefits a blockchain-based system and to minimize its specific risk through a hybrid fuzzy MRDM (multiple rule-based decision making) model that integrates data envelopment analysis with rough set theory (DEA-RST) and the fuzzy DEMATEL approach grounded on a questionnaire derived from domain experts. We aim to point out the inherent risks of blockchain-based technology adoption and to assist senior engineers in designing or adopting a suitable architecture for practical operation and planning of any future integration and development. The potential risk evaluation of business blockchain adoption reveals that the priority improvement sequence based on dimensions is smart contract risk, value transfer risk, and standard risk. Furthermore, law and regulation are the most critical criteria.
Keywords
Introduction
Blockchain-based technology came into prominence in 2009 to support Bitcoin, focusing on decentralization and being tamper resistant. The promising advantages of blockchain-based technology have quickly gained traction over the last decade around the world. Firms have invested heavily into the new technology from the pilot phase to application, and it continues to evolve and develop across industries. The introduction of the technology helps ensure the quality, transparency, and efficiency of enterprises’ transaction activity and management processes [34, 64].
Growing numbers of experts have proven that a blockchain-based intelligent framework is an efficient and trustworthy tool and can be applied in a wide variety of business scopes. The construction and integration of blockchain technology into management information systems have increasingly been initiated in diverse areas such as financial services and government departments [17, 84]. However, any introduction of a revolutionary technology is accompanied by new risks that guide a brand-new direction in which challenges are raised by information technology [9, 36].
What is impeding blockchain development from taking over the corporate ecosystem in an intelligent way? The fundamental challenge is multiple business parties building a compatible platform, because this is difficult and incurs a higher replacement cost of legacy equipment [78]. By way of example, Walmart has mandated that all its pork suppliers construct and leverage a blockchain system, but not each entity has this financial capability in China [69]. Additionally, a blockchain indicates a complete change from the traditional way of doing business, even in corporates that have undergone significant changes from digital technology and have escaped from a single central decision-making system. This poses an irresistible challenge to corporate culture. There is a widespread lack of reasonable awareness of blockchain technology and how it works, especially in areas other than the financial industry. In other words, organizations confront a potentially large array of problems as well as new dilemmas for keeping up with advances in technology.
Nguyen et al. [55] explored blockchain technology adoption and used a directed acyclic graph model to analyze its potential risks in order to providing a safe and efficient solution. To minimize supply chain risks of manufacturing sectors in India, Chen et al. [16] utilized a fusion method that integrates big data and blockchain technology to achieve the goal. Chen et al. [17] indicated that distributed ledger technology such as blockchain could lead to emerging risks for potential users when they attempt to adopt this technology. According to Malhotra et al. [50], blockchain adoption results in strategy risks that cover business, law, and technology. They provided a strategy to mitigate these risks.
Using a two-phase MCDM (multi-criteria decision-making) method, Zhang and Song [94] proposed a sustainability risk evaluation framework of supply chain management for adopting blockchain. Zheng et al. [95] identified compliance risk of blockchain technology adoption based on the grounded theory in the context of China. Al Mallah et al. [4] introduced a combination of an actor-based analysis and a scenario-based analysis to investigate blockchain cybersecurity vulnerabilities.
Blockchain technology-based innovations and merits may also create potential risks or barriers from immature technology. Due to the characteristic of decentralization of blockchain and a generation of multiple ledgers simultaneously, the system is vulnerable to a massive cyberattack, which then may expose information security breaches in enterprises [13]. As one example, blockchain distributed ledger technology might not be completely controlled, because it does not rely on a traditional centralized control system, and so the ledger is more complicated by peers’ consensus view for maintaining its integrity [19, 20]. Distributed consensus algorithms exhibit 51% vulnerability (i.e., double spending) [28]; if the number of nodes/endpoints/miners (called “computing power”) reach the threshold value, then blockchain information can be manipulated and modified by hackers [46]. Thus, it is important to note the different risks that are relevant when adopting and implementing blockchain technology, especially in a complex socio-economic context.
The literature [5, 96] has conceptually illustrated that blockchain technology can introduce immense rewards in enterprise operation management for many fields. However, few publications [94] have empirically investigated the risks of blockchain technology utilization for revolutionary innovation. Only a few studies [4, 87] have used narrative methods on this issue. Moreover, most studies have not taken into account comprehensive risk factors such as standard risk, value transfer risk, and smart contract risk faced by enterprises via blockchain technology adoption and after transactions occur.
This study thus examines the state-of-the-art means for a low-risk blockchain system as well as a blockchain-based application with a novel robust practical framework. Because the risk factors based on blockchain technology have a complex and intertwined relationship (Fig. 1) and to address their mutual influence in the system, this study adopts the hybrid fuzzy multiple rule-based decision-making (MRDM) model to address this issue. A thoughtful approach is supported to analyze risk issues with blockchain-based applications and to avoid coping with said problems on an ad hoc basis.
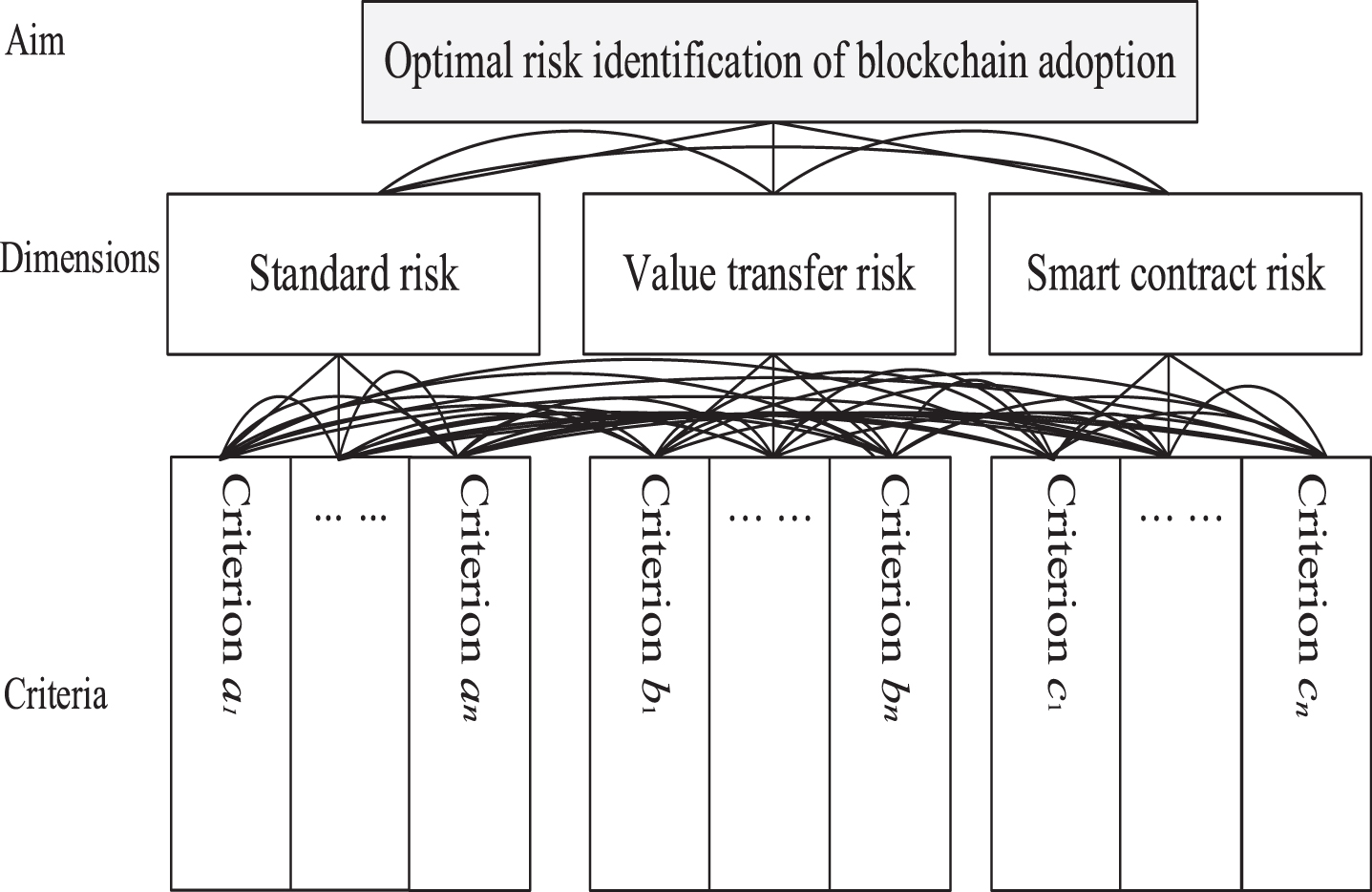
Mutual correlations of potential risks of blockchain adoption.
Compared to the content of prior literature, this study makes several contributions to the identification and improvement of risk factors of blockchain-based technology in enterprises. First, comprehensive risk factors are considered and a practical and feasible framework is recommended when an enterprise conducts blockchain-based technology implementation. Second, critical feature (risk factor or criterion) identification via DEA-RST from a massive amount of datasets on system implementation (such as ERP implementation, PLM adoption) can serve as a foundation for blockchain-based system establishment. Third, a dependence and feedback mechanism of fuzzy DEMATEL can highlight and address the entangled structures of risk factors (dimension and criteria) of blockchain-based technology in the digital age. Additionally, an influential network relationship map (INRM) can provide the rankings of influence factors and help in determining how to move from an actual situation to an aspiration/best situation.
The remainder of this study is structured as follows. Section 2 give a detailed literature review of evaluation dimensions. Section 3 introduces an integrated research methodology such as DEA-RST model and fuzzy DEMATEL method. Section 4 explains the research design and empirical analysis. Section 5 discusses findings and practical implications. Finally, conclusions and remarks are in Section 6.
The utilization of any new technology for revolutionizing business management will produce benefits that come with associated risks. When this technology becomes a part of the core infrastructure of an enterprise and seamlessly integrates multiple applications, the effective management of risks derived from the technology becomes the key to successful adoption and implementation. Therefore, the potential risks of application of blockchain-based technology must be clarified. According to past research [53, 66], the inherent risks of blockchain-based technology are summarized into the following three dimensions: standard risk, value transfer risk, and smart contract risk. An explanation of each dimension content is shown as follows.
Standard risk
Blockchain-based technologies expose entities to standard risks that are similar to those associated with original management practices. The standard risks include business continuity risk, information security risk, operational and IT risk, and supply risk. Due to the distributed nature of blockchain technology, redundancy arises, making the business processes prone to operational failures and network attacks that lead to business discontinuity [23, 43]. Although the transactional records of distributed accounts using blockchain will not be tampered with, account security is not guaranteed [92], because if a malicious attacker occupies 51% of the network nodes in the same distributed ledger, then the account could be taken over [31]. When blockchain technology is embedded into corporate IT infrastructures, it will introduce scalability and interface compatible issues as well as meet a new form of operational risk [52]. Additionally, corporates may be exposed to supplier risks [62], because their systems are mostly built by equipment vendors, and so operation information from the multidimensional data can be smoothly mined and misappropriated by them [53].
Value transfer risk
The blockchain implements a peer-to-peer value transfer of money or asset(s) without the need for centralized coordination [83], but it faces novel risks based on the new business model [51]. The new risks may be sourced from consensus protocol, key management, and data confidentiality. In a blockchain consensus protocol, such as proof-of-stake (PoS) and proof-of-deposit (PoD), most verification nodes of the next block are selected in a pseudo-random manner based on the currency age. This method may result in a failure to engender a consensus, and so the ledger will not be able to complete the value transfer [83]. Digital assets could be taken over in case of a private key theft or third-party (vendor) malicious behavior, despite no destruction of past transactions based on a consensus protocol [49]. Moreover, all participants in the blockchain framework can view all transactions in the ledger, but how the sensitive information can be kept accessible only by authorized users is a key issue, especially in a permissioned network [18, 71].
Smart contract risk
While blockchain technology moves from a physical to a digital system, the smart contracts encode the complex business operation and financial transactions on the new framework and could lead to corresponding risks of these arrangements such as regulatory risk, law and regulation, and legal liability. Smart contracts are predefined rules created by firms on a blockchain platform that apply the same requirement to all participants (nodes). Given the nature of a blockchain system across networks and cross-border regions, there are some limitations for regulatory authorities to implement their task, and so regulatory issues have attracted considerable attention [2, 22]. It is difficult to ensure and provide a legal regulation on the contract enforcement and governance that each participant can accept to substitute for physical contracts [8, 85]. Legal liability is also not easy to clarify if there is an erroneous or a malicious administration of a smart contract on the network and for any transaction issues that involve two or more entities in a cross-country situation [59].
Research methodology
Studies [11, 81] have proven that fuzzy DEMATEL is a useful approach for prioritizing influencing factors in different domains. This study sets up a two-stage fuzzy MRDM model. The first stage screens for key factors via executing DEA-RST techniques so as to complete the pre-test questionnaire. The second stage develops an official questionnaire and adopts the fuzzy DEMATEL approach to analyze the interdependent relationships among selected criteria and to determine the network influence relationship in a system and subsystems. Figure 2 shows the evaluation procedure of an advanced fuzzy MRDM model.
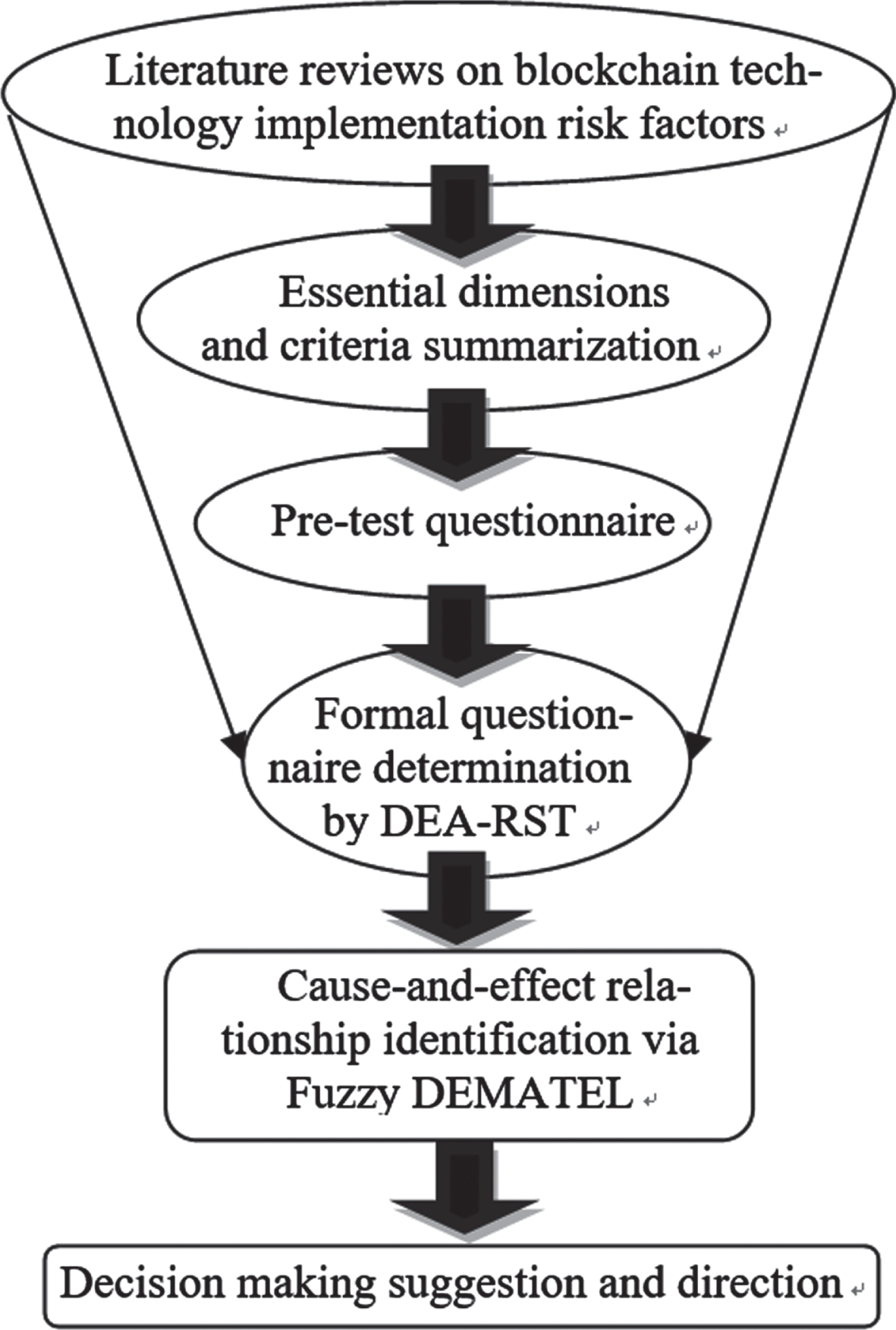
An advanced fuzzy MRDM architecture.
Data envelopment analysis (DEA), a linear programming-based non-parametric algorithm, has superior capability to handle multiple inputs and outputs without pre-decided cost production functions, reaches many successes in numerous research domains. By utilizing analyzed instances (called decision making units, DMUs), it can produce an efficient frontier. Sequentially, it calculates the distance of each DMU from the frontier, which expresses its level of efficiency [33, 43]. If the DMU falls on the efficient frontier, then its efficiency score is one; if the DMU does not fall on the efficient frontier, then its efficiency score is below one. The basic illustration of DEA is displayed as follows.
Assume DMU has e-inputs and f-outputs. The efficiency of the kth DMU is illustrated in Eq. (1).
Equation (1) can be solved via restricting it into a linear programming task shown in Eq. (2).
Here, y jp denotes the amount of jth output of DMUp; x ip denotes the amount of ith input of DMUp; and r j and s i express the weights assigned to jth output and ith input, respectively.
The performance score is decided by users who decide “a priori” what the specification of the model should be without taking any alternatives into consideration. However, it is widely acknowledged that an attribute included in the model in this way may contribute little or nothing to the outcome of the performance score [14, 15]. Thus, realizing the reasons why DMUs reach a certain degree of efficiency by considering inclusion/exclusion or a dissimilar combination of inputs and outputs turns is an essential task. Rough set theory (RST) has demonstrated its superiority in handling imprecise, vague, and uncertain data, and it can be adopted to complement the task confronted by DEA [74]. By joint utilization of DEA and RST, we can dig out much more valuable messages hidden in a large amount of datasets as well as speed up the decision-making process.
In this section the procedure of DEMATEL analysis for risk factors of blockchain-based technology is outlined as follows [37, 68].
Here, H represents the total number of experts, and k denotes the kth expert.
where:
where
Although DEMATEL is a useful evaluation method for addressing complex problems, when building a structural model that the relationships between systems are usually given by crisp values. However, in real-world scenarios, crisp values are inappropriate and unrealistic, especially in a fuzzy environment. Many evaluation criteria are ambiguous and vague in nature. Thus, fuzzy set theory (FST) can handle the vagueness in human thinking and expression in decision tasks. When dealing with uncertainties in the decision-making process, an effective approach called linguistic terms is often more suitable for estimation [57], and so the fuzzy DEMATEL method is favorable for resolving such a MCDM issue [10, 80].
To deal with the uncertainties, group decision making using linguistic terms is required via the introduction of fuzzy numbers [90]. For the transformation of fuzzy numbers to crisp scores by a defuzzification algorithm, CFCS (converting fuzzy data into crisp scores) defuzzification introduced by Opricovic and Tzeng [56] is used to give the left (l) and right (r) scores, and the total score is a weighted average. The five linguistic terms are adopted as no influence, low influence, medium influence, high influence, very high influence, and their corresponding linguistic values (l
ij
, mij,r
ij
) are shown in Table 1. Thus, using the calculation of linguistic terms originating from domain experts’ knowledge, the fuzzy direct relation matrix
Linguistic scale and the corresponding fuzzy values
Linguistic scale and the corresponding fuzzy values
The normalized fuzzy direct relation matrix
Here,
where
Finally, the CFCS method is used to provide the defuzzification of the total fuzzy relation matrix
Questionnaire design and data collection
The proposed questionnaire consists of three stages. The first stage includes 3 dimensions and 17 criteria from our review of relevant literature regarding blockchain-based technology and expert brainstorming as shown in Table 2.
Risk criteria of blockchain-based technology for the pre-test questionnaire
Risk criteria of blockchain-based technology for the pre-test questionnaire
The second stage constructs the pre-test questionnaire according to the results of stage 1. A questionnaire was disseminated to 20 domain experts in China, including 10 senior engineers with over ten years of work experience in the IT department of listed companies and 10 Certified Public Accountants (CPAs) (generally, large accounting firms assist companies in internal control work; and so a CPA is familiar with corporate risk-related issues) with approximately ten years of experience. They were asked to score the level of importance of each factor to the delivery of blockchain-based technology adoption risk on an 11-point categorical scale (from “very low” to “very high”).
A class label is next confirmed, and DEA-RST fusion technology is then adopted for feature selection. To examine the effectiveness of the introduced fusion technology (DEA-RST), we take it as a benchmark and compare it with the other four feature selection techniques (rough set theory with particle swarm optimization (RST-PSO) [86], fuzzy rough set theory with ant colony optimization (FRST-ACO) [17], filter-wrapper approach (FWA) [14], and kernel principal component analysis (KPCA) [33]. Five-fold cross-validation (CV) helps avoid the problem of over-fitting, and the accuracy or error rate is executed as an assessment measure. Table 3 displays the outcome. We see that the introduced fusion technology reaches the optimal performance. Thus, the analyzed outcome is taken to set up a formal questionnaire (see Table 4).
Comparison of results
The formal questionnaire derived from DEA-RST
The third stage sets up a formal questionnaire based on Tables 4, 5, and the information received by domain experts is collected. Respondents were required to indicate their perception of pairwise comparison of 10 criterial (factors) and performance satisfaction of the factors for blockchain-based technology adoption. The questionnaires were distributed among the 32 professionals, of whom 10 are senior engineers, 12 of them are CPAs in the Big 4 CPA firms. and 10 are chief audit executives of listed companies. A questionnaire survey assesses the direct impact of all criteria thorough a pairwise comparison using a five-level scale with 0 = absolutely no influence and 4 = very high influence based on respondents’ thoughts. Through a collection of professional data, the 32 completed questionnaires were fed into the fuzzy DEMATEL approaches described herein to support further analysis.
Description of the formal questionnaire
Implementation of the fuzzy DEMATEL technology is conducted in determining the total fuzzy relation matrix
Total average fuzzy relation matrix (
) for the criteria
Total average fuzzy relation matrix (
Notes: Average gap-ratios in consensus (%).
Cause
Theoretical implications
Assisted decision-making architectures, such as multiple criteria decision making (MCDM) algorithms, are essential and invaluable business analytics approaches that guide corporates to form a reliable judgment under complicated and volatile environments. Among the MCDM algorithms, DEMATEL, with the merit of identifying inherent cause-and-effect relations among criteria, ease of use, and highly flexibility, is one of the most broadly adopted approaches. Emrouznejad and Marra [25] and Vafadarnikjoo et al. [79] also indicated that the inclusion of subjective factors in DEMATEL is another advantage over other MCDM approaches. However, fewer studies have examined the extension of DEMATEL to other approximate reasoning theories, such as FST, that can strengthen its flexibility so as to dig out more in-depth insights. Thus, this study borrows the unique characteristics from FST and DEMATEL (i.e., fuzzy DEMATEL) and implements it to identify the essential risks when adopting blockchain-based systems.
The knowledge induction from fuzzy DEMATEL is through doing a pairwise comparison. When the analyzed indicators are increased, making a pairwise comparison turns out to be a complicated task – that is, it is very difficult for experts to reach a consensus judgment when the analyzed indicator proliferates dramatically. Thus, essential indicator identification becomes an urgent task, especially in a decision-making field. DEA has been broadly applied to determine the weight of each variable to handle the ranking tasks. Based on the contribution of each variable to the outcome, we can realize the essence of each variable. However, the ranking order from DEA will be dissimilar when it considers inclusion/exclusion or a dissimilar combination of inputs and outputs. To combat this and to make full use of the information from all indicators, RST with the capacity for data categorization and data pattern identification is considered. By joint utilization of DEA and RST, decision-makers can filter out irrelevant and redundant variables as well as speed up the decision-making procedure.
This study contributes to the MCDM literature in several aspects. First, it borrows the advantages from the MCDM field (i.e., DEA) and AI field (i.e., RST) to determine the most essential variables. By doing so, decision-makers can concentrate heavily on any “red flag (i.e., the real essential parts)” and prevent themselves from getting lost in the big data era. Second, the analyzed outcomes are then fed into fuzzy DEMATEL to describe the opaque relationships among criteria as well as assist users to reach a consensus judgment.
Practical implication
This study investigates the potential risks of corporates’ adoption of blockchain-based technology based on a survey of experts’ opinions and leverages the DEMATEL method to build INRM (Fig. 3). It delivers the hierarchies and causal relationships among the systems (dimensions) and sub-systems (criteria). According to the manifestation of INRM from the fuzzy DEMATEL analysis, the improvement priority for dimensions can be seen as follows: smart contract risk (C), value transfer risk (B), and standard risk (A).
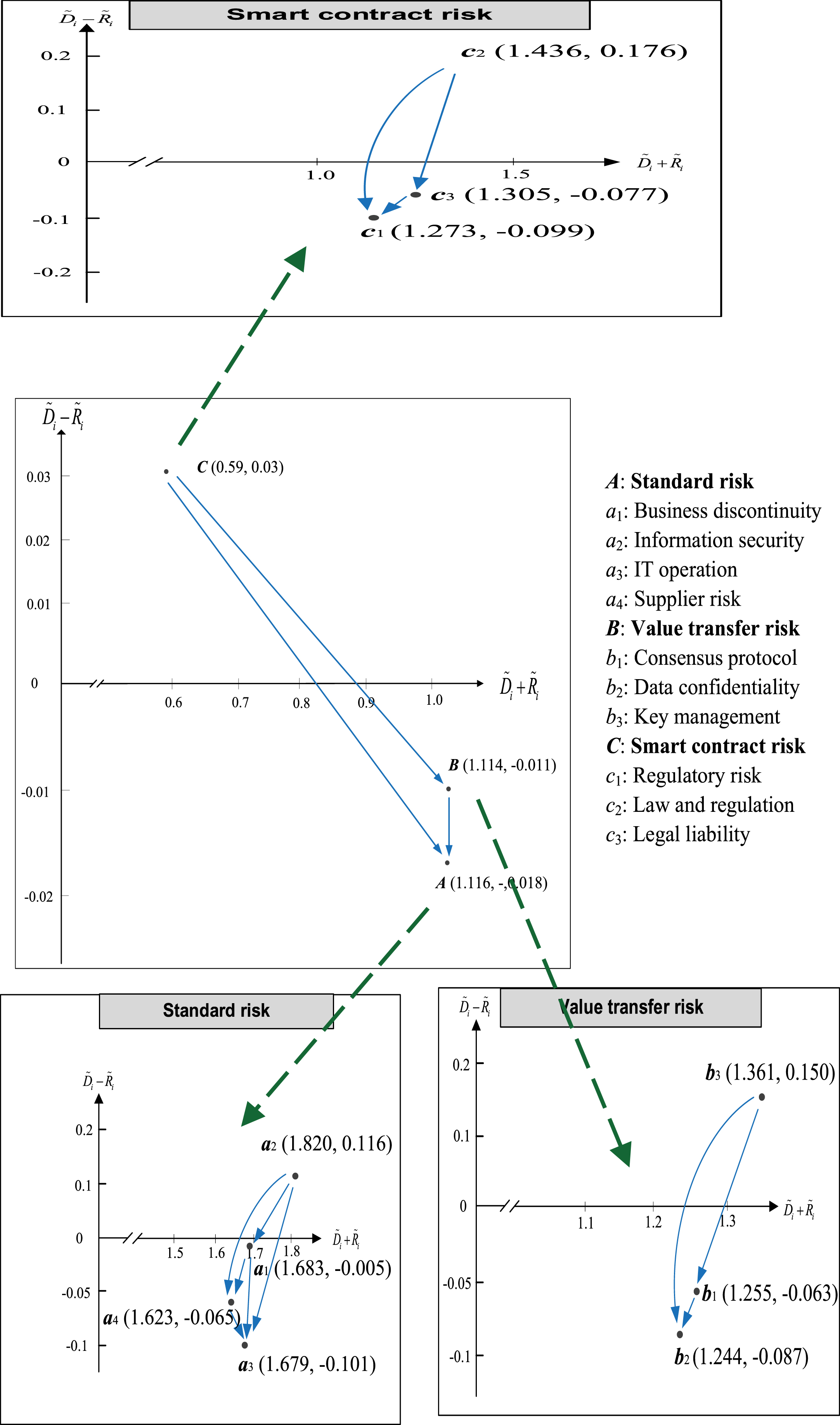
The INRM of influence correlation using fuzzy DEMATEL.
It can be observed that smart contract risk is deemed critical by decision-makers, while the application of blockchain-based technology as the primary focus illustrates the influential relation on other dimensions. In other words, if a company attempts to introduce blockchain technology into operation systems, then it needs to give priority to solving the issue of smart contract risk for reducing concerns on adoption. Consistent with Thomas [77], this is essential given the provision of secure assets for achieving reliability and effectiveness in the execution of smart contracts. However, the agreement may be unenforceable in a court of law when cross-borders are involved. In a similar vein, Arruñada [6] suggested that the novel legal questions sparked by smart contracts could derive extra risk and need to be overcome and improved immediately.
The receive results on the criteria reveal that “law and regulation” is the most considerable risk factor of blockchain technology adoption for companies. As identified by Duque and Torres [24], blockchain technology has by its nature a cross-jurisdictional deployment, and legal rules and regulations of collaborating across national borders may achieve a mitigation of potential risks for adoption. Enterprises seek to obtain the optimal layout to accomplish effective regulations and/or rules of a decentralized network environment (e.g., blockchain environment) and can trigger increased and better compliance with international requirements [97]. In a cross-border blockchain platform, such a new technology has made global transactional models more dynamic and is thus more prone to hacking as well as posing a threat to corporate stability. There is a demand by governments to supply an effective law/rule on blockchain adoption to minimize the risks associated with this innovative operational system [1]. In the context of a blockchain-based system, cross-border management taking into account the innovation of traditional law regime is an imperative and a mandatory measure in the future. Current relevant rules and regulations should be tested in order to construct a useful solution and to achieve security standards for responding to widespread applications by global enterprises.
Another important identified risk factor of blockchain technology application in business operation is key management. The role of key management is very important in implementing the goals of risk reduction in technological innovation for improving privacy and security [93]. It is based on the identification of blockchain technology goals and the specification of long-term strategies for managing potential risk [72]. A reliable key management procedure based on blockchain technology has been widely conducted in many industries and can support a secure pillar for business confidence in its adoption [63]. Lee and Ma [41] indicated that key management mechanism is one of the major considerations for blockchain adoption for enterprises, while an efficient management mechanism could minimize the information security risk and protect the open network from potential security attacks and threats. Obviously, key management is essential for improving the stability and safety of blockchainsystem.
Information security is the third focus of the criterion to identification risk of blockchain adoption by domain experts. A blockchain-based open network is vulnerable to information security risks such as illegal attacks from malicious entities and information leakage. Lu et al. [48] pointed out that information security issues significantly weaken the unique benefits of blockchain as well as indirectly affect a company’s willingness to adopt such technology. Similar results were captured by Saberi et al. [65], in that information security is a main facilitator for an organization adopting blockchain since it plays a crucial role in protecting sensitive information assets of all participants on the platform. Moreover, firms’ concerns about information security may lead entities to perceive more uncertainty and decrease their intention to utilize the blockchain systems [46]. During the transaction creation and recordkeeping processes, unforeseen vulnerabilities might be discovered on a blockchain platform, so that an appropriate information certification process is indispensable and must rapidly deploy information security updates and patches to maintain a stable operation environment [54].
The empirical results herein offer a recommendation to business sectors for a more comprehensive understanding of the potential risks of blockchain adoption in digital transformation. The contours of these possible risk factors of blockchain applications are investigated, which should be effectively decreased or eliminated using new methods. More importantly, given the dynamism of multiple environmental factors, potential risk exploration on blockchain adoption must seek to be flexible and advanced enough to adapt quickly to this changing digital landscape. In conclusion, the risk evaluation of blockchain-based solutions in this study can profoundly benefit all types of businesses and associated industries (financial industryexcluded).
This study presents a hybrid MRDM approach by combining DEA-RST technology and fuzzy DEMATEL method to evaluate potential risks of blockchain technology adoption for corporates in the real world. The application of RST-DEA is used to preliminarily screen the relatively important factors among a host of factors. The fuzzy DEMATEL model is then employed to enable the prioritization of these risk factors when considering their mutual relations. The causal relationships among factors are constructed in accordance with the outcome obtained from fuzzy DEMATEL. It is thus easy to recognize the underlying risks of blockchain adoption for corporates in technological transformation.
In terms of dimensions, the level of importance using fuzzy DEMATEL goes as follows: smart contract risk, value transfer risk, and standard risk. Law and regulation form the principal core of risk avoidance of blockchain technology adoption among all factors for enterprises, which must surmount this first in order to move forward. As blockchain technology continues to grab the attention of board members and CXOs (Chief Experience Officer) of many businesses, it becomes imperative for the internal control and internal audit function to proactively acquaint itself with the opportunities and risks emerging from the implementation of this technology. The findings of this study can be applied by decision-makers as a benchmark for providing a feasible course of action for the avoidance of these risks and can be implemented in different regions or countries.
Although this research provides available insights into how to avoid risks of blockchain application, some limitations also exist. This study examines a very limited number of readiness assessment items for the potential risk factors of blockchain adoption in China. Future works can introduce the role of other determinants (e.g., external risk) in this context. Moreover, different fuzzy membership functions such as mountain functions and trapezium functions [75] can be suggested for future research to show the robustness of fuzzy DEMATEL in different scenarios. The number of experts in some relevance fields (i.e., scholars from School of Accounting and School of Computer Science and Engineering) and more different regions will also be the focus of consideration.
Footnotes
Acknowledgments
The authors would like to thank the National Science and Technology Council (NSTC), Taiwan for financially supporting this project under contract No. 112-2410-H-034 -015 -MY2; and The author also want to thank the Department of Education of Guangdong Province, China for financially support this project under contract No. 2021ZDJS131.
