Abstract
Ensuring the security of transmitted content is an important task in network communication. Signcryption technology combines signature and encryption operations in a single step to achieve message authentication and confidentiality. In practical applications, users are usually in different cryptographic systems, the ordinary signcryption technology cannot realize communication between two different cryptographic systems. And the ciphertext structure of the existing signcryption schemes is relatively complex, signcryption is not efficient. Therefore, in order to solve the problem of efficient communication between different cryptosystems and ensure quantum security, this paper proposes a lattice-based efficient heterogeneous signcryption scheme for secure network communications. This signcryption scheme accomplishes signcryption through matrix operations and hash functions, which avoids complex signcryption structures, efficiently realizes bidirectional message communication between identity-based cryptosystems and certificateless cryptosystems.
Keywords
Introduction
Research in the fields of cryptography and network security has greatly supported the development of network content transmission. Researchers are working on realizing secure network communication, such as in the fields of vehicle network, wireless networks and 5G [1,3,7]. Signature technology and encryption technology realize the secure transmission of network content. Signcryption technology combines digital signature and public key encryption to achieve encryption and signature operations at the same time. Signcryption technology was first proposed by Yuliang Zheng [14], which is significantly better than the method of signing first and then encrypting. Signcryption technology is widely used in the fields of IoT, blockchain and machine learning [4,11]. Through signcryption technology, the protection of transmitted content in machine learning is realized. Heterogeneous signcryption technology is the key technology to realize the content communication between two different systems, but most of the heterogeneous signcryption is based on the traditional PKI cryptosystem. The traditional PKI cryptosystem requires a trusted third party to issue a digital certificate to bind the user’s identity to the public key, which results in huge communication and storage costs. The emergence of identity-based cryptography (IBC) uses the user’s unique identity as the user’s public key and no longer requires a digital certificate. In 2003, a certificateless cryptosystem (CLC) was proposed. KGC is only used to generate the user’s partical private key, and the user’s complete private key is generated from the partical private key and the secret value selected by the user. Therefore, constructing a heterogeneous signcryption scheme based on a certificateless cryptosystem and an identity-based cryptosystem can not only realize message communication between different systems, but also improve system performance and scheme efficiency.
With the development of quantum computers, traditional signcryption schemes based on the decomposition of large integers and the difficulty of discrete logarithms have been unable to resist the attack of quantum algorithms. Since quantum algorithms for solving difficult problems on lattices in polynomial time have not yet been discovered, lattice-based cryptosystems are currently believed to be resistant to quantum attacks. In 2008, Gentry et al. proposed the GPV signature scheme and encryption scheme in the Reference [2], and proved their security based on the difficulty of the SIS problem and the LWE problem respectively. In 2014, Lu et al. proposed a signcryption scheme based on lattice [5], which has the advantage of resisting quantum computer attacks. In recent years, many researchers have studied signcryption schemes based on lattice. In 2019, Yang et al. proposed a heterogeneous signcryption scheme based on NTRU lattice [12], and proved its security under the random oracle model. But their research only achieved the one-way communication from PKI public key cryptosystem to identity-based cryptosystem. In 2021, Zhu et al. proposed an efficient identity-based proxy signcryption using lattice [15], which satisfies both IND-CCA security and EUF-CMA security. This scheme can only realize signcryption under the same identity-based cryptosystem. In 2022, Yu et al. proposed a certificateless anti-quantum ring signcryption for network coding [13], which has low communication cost. Most of the above researches can only realize one-way or same cryptosystem signcryption communication, and the ciphertext structure is relatively complex. In this paper, we combine lattice cryptography with heterogeneous signcryption scheme, and propose a lattice-based efficient heterogeneous signcryption scheme for secure network communications. The scheme improves the ciphertext structure while realizing the communication between certificateless cryptosystem and identity-based cryptosystem.
The contributions of this paper are as follows:
In order to solve the problem of secure content transmission between different cryptosystems in network, this paper proposes a lattice-based efficient heterogeneous signcryption scheme, which realizes bidirectional content communication between certificateless cryptosystems and identity-based cryptosystems.
In the proposed heterogeneous signcryption scheme for secure network communications, we generate the security key based on the lattice algorithm, generate the signcryption triple through the hash function and matrix operation. The scheme realizes the encryption of the message through XOR operation, avoids the complex signcryption operation, and improves the efficiency of the signcryption process.
The rest of the paper is organized as follows. In Section 2, we give the preliminaries. In Section 3, we describe the formal definition of the heterogeneous signcryption scheme model. In Section 4, we propose a lattice-based efficient heterogeneous signcryption scheme for secure network communications. In Section 5, we analyze the correctness of this scheme. Finally, we conclude this work in Section 6.
Preliminaries
Basic knowledge of lattice
This section gives the basic definitions of lattice and LWE distribution. In algebra, lattice is a subgroup of the set Let Given a prime number q, a matrix For a vector (Lattices [6]).
Trapdoor generation and pre-image sampling algorithm
This section mainly introduces the trapdoor generation algorithm and the pre-image sampling algorithm proposed in the reference [8].
For any integer
For the matrix
For the matrix
(Trapdoor generation algorithm).
(Pre-image sampling algorithm).
(General pre-image sampling algorithm).
Discrete Gaussian distribution from lattice
(Discrete Gaussian Distribution [8]).
For any
Heterogeneous signcryption scheme model
The lattice-based efficient heterogeneous signcryption model in this paper mainly includes three entities: Certificateless Cryptosystem(CLC) user, Identity-based Cryptosystem(IBC) user, and key generation center(KGC). The model consists of eight algorithms, namely: Setup, CLC Partial Key Generation (CLCExtract), CLC Key Generation (CLCKeyGen), IBC Key Generation (IBCKeyGen), CLC-IBC Heterogeneous Signcryption (CLC-IBC HSC), CLC-IBC Heterogeneous Unsigncryption (CLC-IBC HUSC), IBC-CLC Heterogeneous Signcryption (IBC-CLC HSC) and IBC-CLC Heterogeneous Unsigncryption (IBC-CLC HUSC). The identity of CLC user is CLC-IBC CLC-IBC IBC-CLC IBC-CLC
Lattice-based efficient heterogeneous signcryption scheme for secure network communications
In this section, we propose a lattice-based efficient heterogeneous signcryption scheme for secure network communications. The section includes a communication model and a specific scheme. This section designs a secure communication model for certificateless cryptosystems and identity-based cryptosystems. The model can realize the bidirectional heterogeneous signcryption process of these two different systems. The specific scheme avoids the number of symmetric encryption operations and complex signcryption operations. By designing the ciphertext structure, the scheme reduces the number of ciphertexts and improves the efficiency of heterogeneous signcryption.
Communication model of heterogeneous signcryption schemes
In practical applications, when users are in different cryptographic systems, how to realize secure network communication between the different cryptographic systems has become the focus of attention. In this paper, we mainly focus on implementing secure network communication for certificateless cryptosystems and identity-based cryptosystems. The simple communication model is shown in the Fig. 1. In CLC system, D is the partial private key of CLC users, and
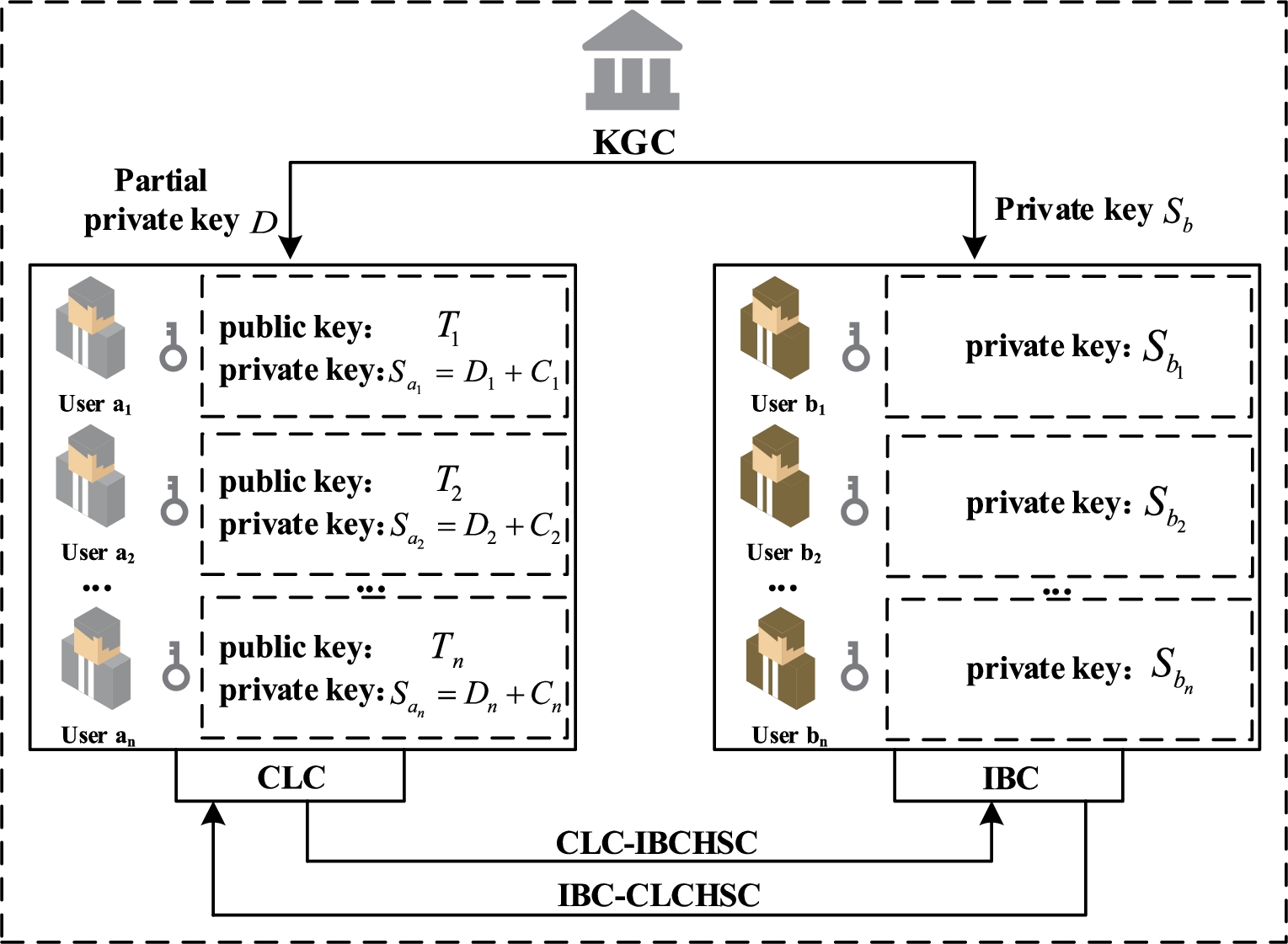
Heterogeneous signcryption communication model.
In the Lattice-based efficient heterogeneous signcryption scheme proposed in this paper, based on the signcryption scheme structure [15], we generate the master private key through the trapdoor generation algorithm on lattice. We generate the user private key through the pre-image sampling algorithm, and realize the signcryption process through matrix operation and hash operation.
In this section, we propose a lattice-based efficient heterogeneous signcryption scheme. This scheme has three entities: CLC user
Setup
KGC chooses n as the system security parameter, the prime number
KGC runs the algorithm
CLCExtract
CLC user
CLCKeyGen
After CLC user
IBCKeyGen
IBC user
CLC-IBC HSC
In this algorithm, CLC user CLC user Calculates Sends
CLC-IBC HUSC
After IBC user IBC user Substitutes the calculated value h,
IBC-CLC HSC
In this algorithm, IBC user IBC user Calculates Sends
IBC-CLC HUSC
After CLC user CLC user Substitutes the calculated value h,
Correctness analysis
In this section, we present the proof process for the correctness of the lattice-based efficient heterogeneous signcryption scheme.
CLC-IBC heterogeneous signcryption correctness
When CLC user is the sender of the heterogeneous signcryption algorithm and IBC user is the receiver, after IBC user receives
IBC user
IBC user
IBC user
IBC-CLC heterogeneous signcryption correctness
When IBC user
CLC user
CLC user
CLC user
Conclusions
A lattice-based efficient heterogeneous signcryption scheme for secure network communications is proposed in this paper. In the scheme, the security key is generated based on the algorithm on lattice, the signcryption ciphertext is generated by the hash function and matrix operation, the encryption of the message is realized by the XOR operation. The scheme realizes the secure bidirectional content transmission of identity-based cryptosystem and certificateless cryptosystem, and also achieves quantum resistance. Compared with other heterogeneous signcryption schemes, the computational complexity of the signcryption process in this paper is lower, and the ciphertext structure is relatively simple. About the future work, we consider extending this scheme to machine learning or the Internet of Things to realize secure network communications between different systems in practical application.
Conflict of interest
The authors declare that there are no conflict of interests.
