Abstract
The Software-Defined Network (SDN) with Network Slicing will be a good approach for admission control in the Fifth Generation (5G) wireless network, which is planned to be adaptable to meet user requirements. The system’s resources are limited, and the number of devices is growing much faster than it can handle. So, the overloading problem will be a very critical problem. To deal with these problems, this paper presents a Fuzzy-based Scheme for Service Level Agreement (SLA) evaluation (FSSLA). We compare two models: FSSLA1 and FSSLA2. The FSSLA1 considers three input parameters: Reliability (Re), Availability (Av), Latency (La) and the output parameter is SLA. In FSSLA2, we consider Traffic Load (Tl) as a new parameter. From simulation results, we conclude that the considered parameters have different effects on the SLA. When Re and Av are increasing, the SLA parameter is increased but when La and Tl are increasing, the SLA parameter is decreased. When the Tl value is changed from 20% to 80%, the SLA is decreased by 16.62% when Re 10%, Av 90% and the La value is 1 ms. When the Re is increased from 10% to 90% and 50% to 90% and the Tl value is 50%, the Av is 50% and the La is 1 ms, the SLA is increased by 22.76% and 11.38%, respectively.
Introduction
By the advancement of wireless technology, the customer demands for services, have rapidly increased. There will be billions of additional devices with irregular traffic patterns and enormous data rates. With the emergence of the Internet of Things (IoT), these devices will create significant volumes of data for the Internet, increasing network congestion and lowering the Quality of Service (QoS). Therefore, the Fifth Generation (5G) network should be good and capable of meeting users requirements [7,11,14,29,31]. It also can be used to fulfill the demand of several industries, including medicine, automotive, education, media, manufacturing, and transportation.
The key challenges of 5G.
In comparison to 4G, the 5G network is expected to surpass 4G. The key challenges of 5G are illustrated in Fig. 1, which have been required to include better spectrum efficiency, reduced latency, low consumption, high data rate, capacity and throughput improvement. For example, peak data rates for 5G are likely to exceed 20 Gbps [13]. Furthermore, the 5G network will provide customers new experiences such as Ultra High Definition Television (UHDT) on the Internet [30], but also support a large number of IoT devices with long battery life and high data rates in high-density hotspot [12].
The 5G is developing by considering three different usage scenarios which have been identified as enhanced mobile broadband (eMBB), ultra-reliable & low latency communications (URLLC) and massive type communication (mMTC) [1,33,37]. The eMBB is related to human-essential and has greater accessibility to multi-media content and services by enhancing seamless Quality of Experience (QoE). The URLLC can efficiently reduce the latency and enhance reliability. The mMTC can accommodate a large number of connected devices while maintaining a long battery life. In order to give a nice experience for consumers, routing and switching technologies have also been changed, and 5G technology’s coverage area is shorter than 4G [10,12,14,19].
The traditional IP networks are complicated and difficult to maintain, therefore network administrators must identify and develop new approaches to improve network performance. The Software-defined Networking (SDN) is a new networking paradigm that decouples the data plane from the control plane in the network and facilitates (logical) network control by allowing users to program the network. As a result, the SDN can improve system administration and processing performance [22]. As an example, the mobile handover mechanism with SDN can be used for reducing the delay in handover processing and improve the QoS [19,23,27,36].
Network Slicing is a new technology that leverages SDN and Network Function Virtualization (NFV) to create various services over the same physical network to fulfill the customers’ different QoS requirements [38]. A slice is a group of network resources that have been chosen to fit the demands of the services. By slicing a physical network into numerous logical networks, it is possible to provide on-demand tailored dependable service in a network with limited resources. Because multiple slices with varied priority values can satisfy diverse traffic requirements, users in the 5G system will have a better QoS than users in the 4G system [17,21,31,38].
In our previous work [2–5], we presented a Fuzzy-based system for admission decision considering four input parameters: Quality of service (QoS), Slice Priority (SP), Service Level Agreement (SLA) and Slice Overloading Cost (SOC). The output parameter was Admission Decision (AD). In this paper, we present two models for SLA: FSSLA1 and FSSLA2. The FSSLA1 considers three input parameters: Reliability (Re), Availability (Av), Latency (La) and the output parameter is SLA. In FSSLA2, we consider Traffic Load (Tl) as a new parameter.
The rest of the paper is organized as follows. In Section 2 is presented an overview of SDN. In Section 3 is presented the network slicing enabling SDN technology. In Section 4, we present application of Fuzzy Logic for admission control. In Section 5, we describe the proposed Fuzzy-based scheme and its implementation. In Section 6, we explain the simulation results. Finally, conclusions and future work are presented in Section 7.
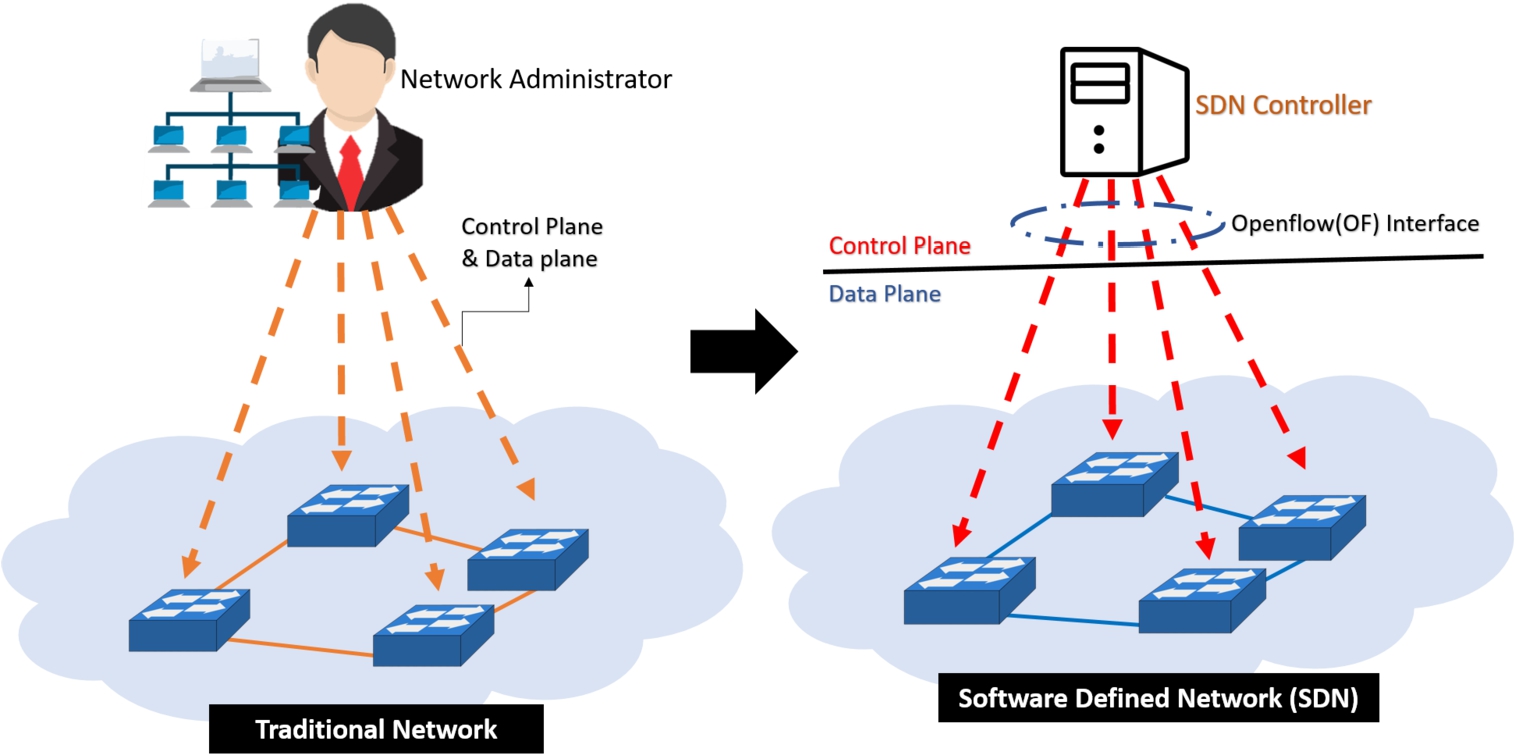
The comparison of traditional network and SDN.
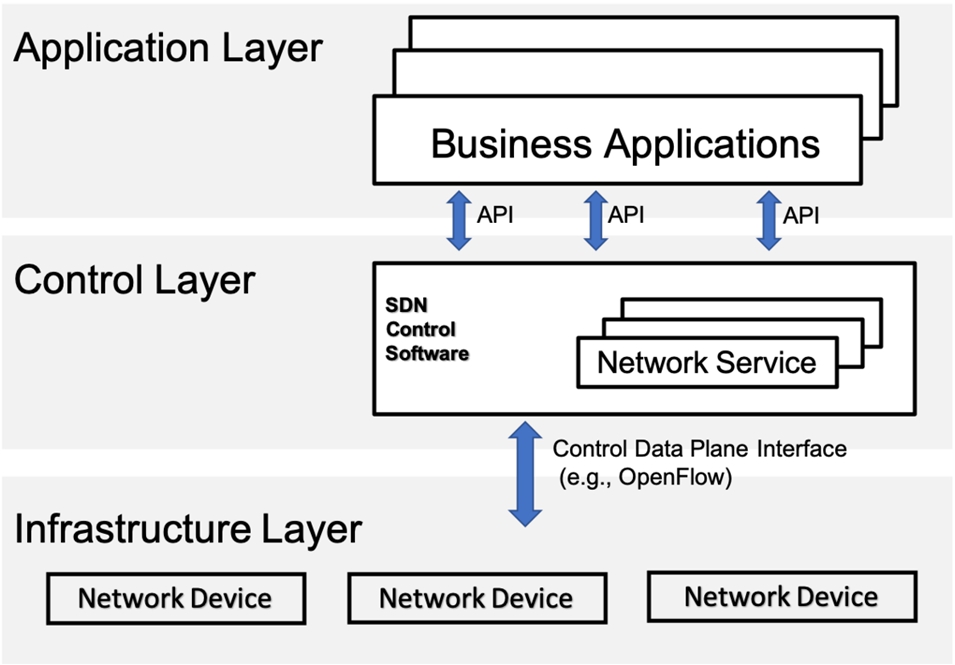
Structure of SDN.
The SDN is a new networking paradigm that decouples the data plane from control plane in the network and promotes (logical) centralization of network control that have ability to program the network. This separation can be flexible and centralized management with a global view of entire network. In Fig. 2 is shown the traditional network and SDN approaches. The traditional networks are hard to manage and control since they rely on physical infrastructure. It is difficult to configure the network according to predefined policies and to reconfigure it to respond to faults, load, and changes because the processes must be based on the setting of each device and making controlling and operation on each device. In contrast, SDN creates virtualized control plane with intelligent management decisions, when network administrators can control and reconfigure the overall network by managing on virtualized controller. Thus, the SDN is easy to manage and provide network software-based services from a centralized control plane. The SDN control plane is managed by SDN controller or cooperating group of SDN controllers. The SDN structure is shown in Fig. 3 [8,24,25,28].
The SDN can manage the network while enabling new services. In congestion traffic situation, the management system can be flexible, allowing users to easily control and adapt resources appropriately throughout the control plane. Mobility management is easier and quicker in forwarding across different wireless technologies (e.g.5G, 4G, Wifi and Wimax). Also, the handover procedure is simple and the delay can be decreased [34]. But, when the administrator wants to implement SDN protocol and SDN controller, the entire network infrastructure needs to be changed. If the SDN controller fails, the entire system also fails.
5G network slicing enabling SDN technology
The network slicing is a technique that divides a single virtualized infrastructure into several virtual end-to-end networks, referred to as “Slices”, that are configured into virtualized functions to adapt to the user’s demands. Each slice is conceptually distinct and has no impact on the other virtual logical networks [6,9,18].
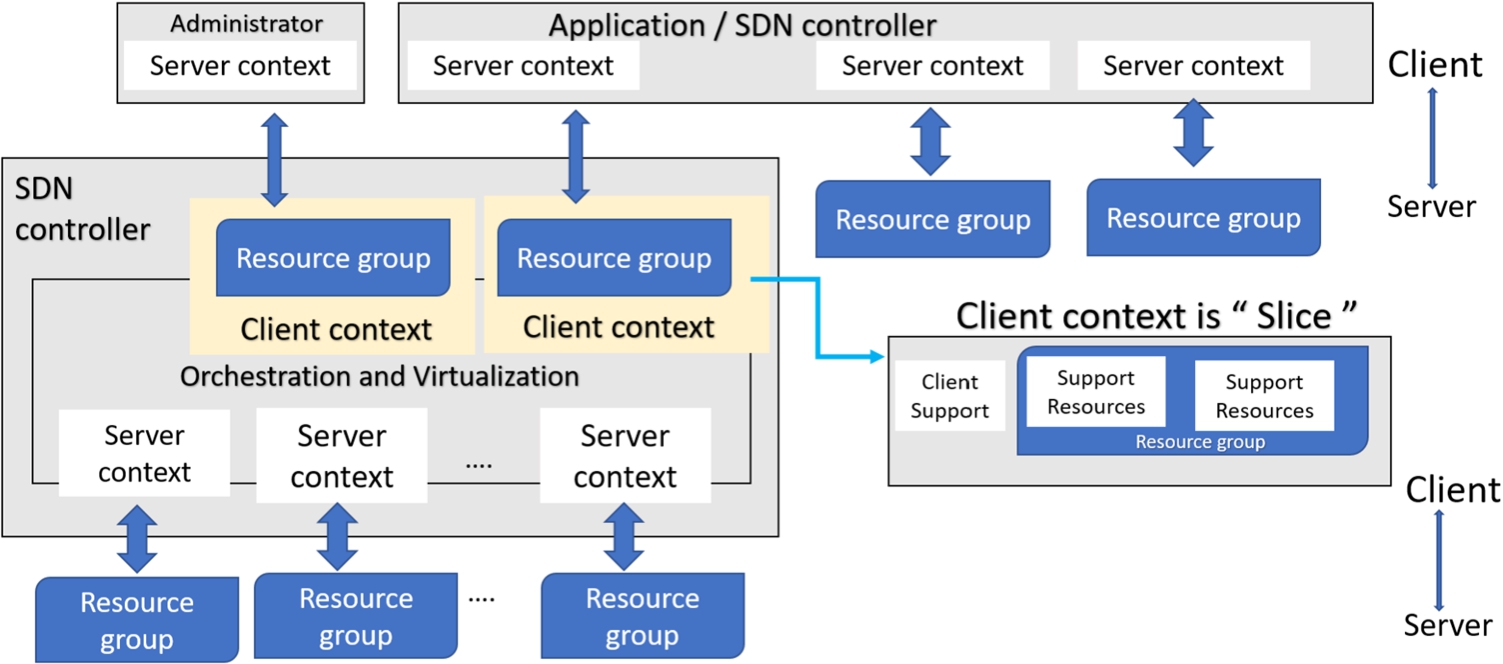
ONF SDN network slicing architecture.
The SDN network slicing architecture is provided by the Open Network Foundation (ONF). In SDN network environment, the main components of SDN architecture are resources and control. In Fig. 4, the SDN controller dynamically manages network slice by using a set of policies and grouping slices that belong to the same context [32]. The ONF SDN network slicing architecture has the following components.
Client support: It contains support information of client operation.
Resource group: It contains the customized view of all resources that the controller offers to client based on service demands and facility.
A Fuzzy Logic (FL) system is a nonlinear mapping of an input data vector into a scalar output, which is able to simultaneously handle numerical data and linguistic knowledge. The FL can deal with statements which may be true, false or intermediate truth-value. These statements are impossible to quantify using traditional mathematics. The FL system is used in many controlling applications such as aircraft control (Rockwell Corp.), Sendai subway operation (Hitachi), and TV picture adjustment (Sony) [16,26,35].
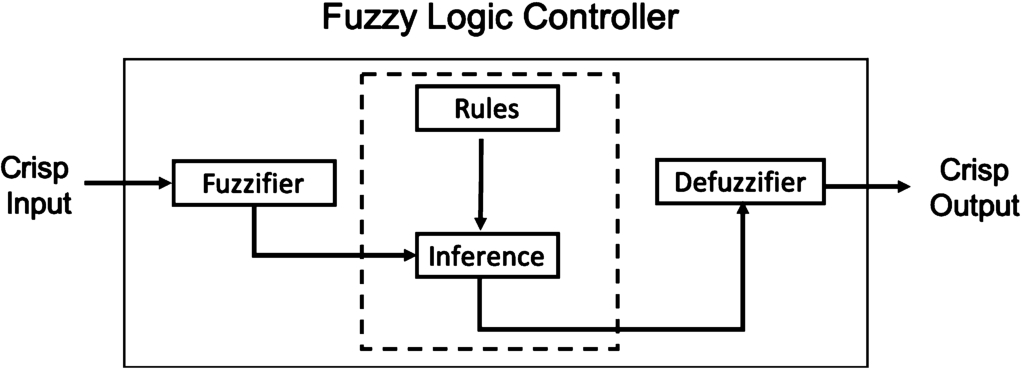
FLC structure.
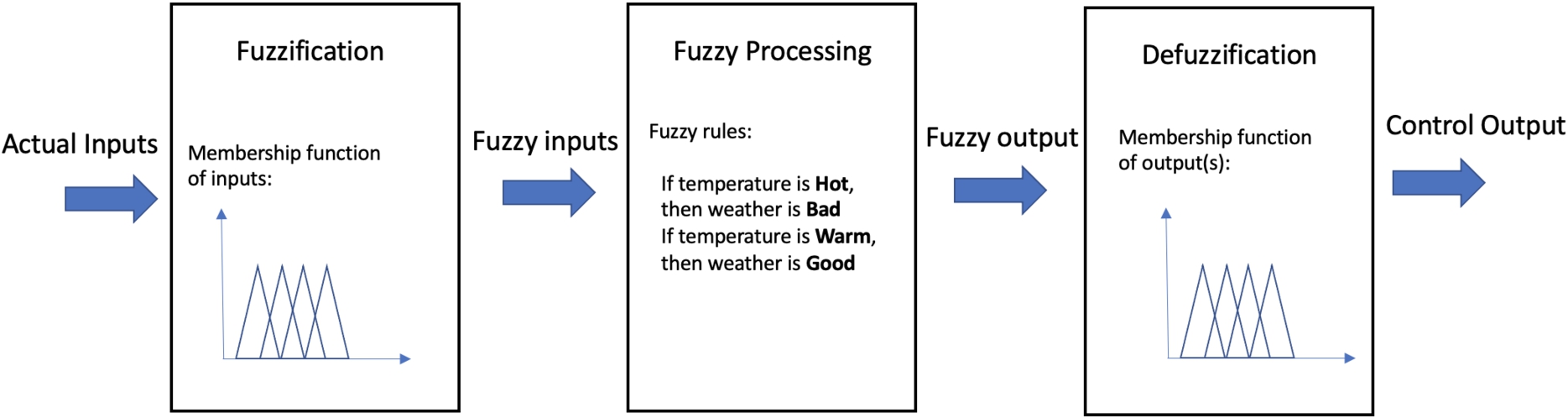
Operation of a fuzzy controller.
In Fig. 5 is shown Fuzzy Logic Controller (FLC) structure, which contains four components: fuzzifier, inference engine, fuzzy rule base and defuzzifier. In Fig. 6 is shown the operation of the fuzzy controller. In the first step, the Fuzzification fuzzified the actual inputs to obtain fuzzy inputs. Then, Fuzzy Processing will process fuzzy inputs according to the rules set and produces fuzzy outputs. Finally, the Defuzzification produces a crisp real value from fuzzified inputs for control output.
A concept that plays a central role in the application of FL is that of a linguistic variable. The linguistic variables may be viewed as a form of data compression. One linguistic variable may represent many numerical variables. It is suggestive to refer to this form of data compression as granulation.
The same effect can be achieved by conventional quantization, but in the case of quantization, the values are intervals, whereas in the case of granulation the values are overlapping fuzzy sets. The advantages of granulation over quantization are as follows:
it is more general;
it mimics the way in which humans interpret linguistic values;
the transition from one linguistic value to a contiguous linguistic value is gradual rather than abrupt, resulting in continuity and robustness.
For example, let Temperature (T) be interpreted as a linguistic variable. It can be decomposed into a set of Terms: T (Temperature) = {Freezing, Cold, Warm, Hot, Blazing}. Each term is characterised by fuzzy sets which can be interpreted, for instance, “freezing” as a temperature below 0°C, “Cold” as a temperature close to 10°C.
Fuzzy control rules
IF
The canonical form for a fuzzy rule-based system
The canonical form for a fuzzy rule-based system
In Table 1 are showing several simple canonical rules from decomposing and reducing any compound rule structure. These rules are based on natural language representations and models, which are represented based on fuzzy sets and FL. The fuzzy level of understanding and describing a complex system is expressed from the form of a set of restrictions on the output with the condition of the input (
There are many defuzzification methods as follows:
The Centroid Method;
Tsukamoto’s Defuzzification Method;
The Center of Are (COA) Method;
The Mean of Maximum (MOM) Method;
Defuzzification when Output of Rules are Function of Their Inputs.
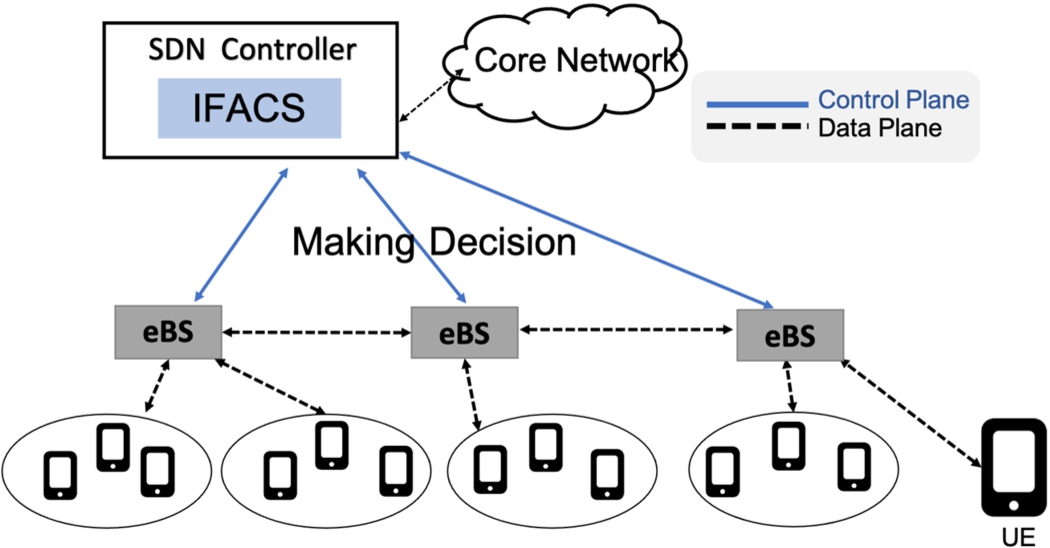
Proposed system overview.
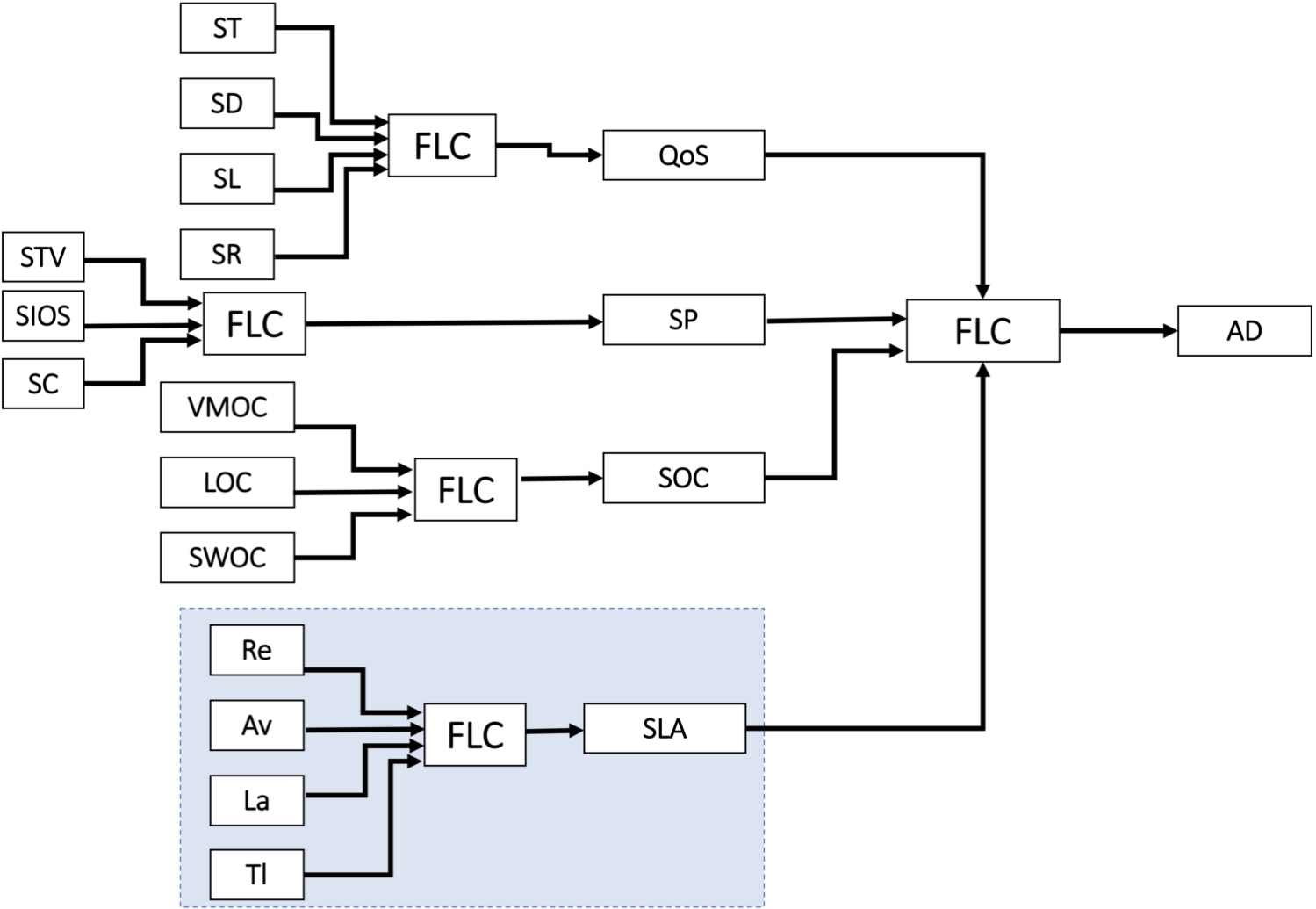
Proposed system structure.
In this work, we use FL to implement the proposed system. In Fig. 7, we show the overview of our proposed system. Each evolve Base Station (eBS) will receive controlling order from SDN controller and they can communicate and send data with User Equipment (UE). On the other hand, the SDN controller will collect all the data about network traffic status and controlling eBS by using the proposed Fuzzy-based system. The SDN controller will be a communicating bridge between eBS and 5G core network. The proposed system is called Integrated Fuzzy-based Admission Control System (IFACS) in 5G wireless networks. The structure of IFACS is shown in Fig. 8. For the implementation of our system, we consider four input parameters: Quality of Service (QoS), Slice Priority (SP), Slice Overloading Cost (SOC), Service Level Agreement (SLA) and the output parameter is Admission Decision (AD). We applied FL to evaluate QoS, SP, SOC and SLA. The QoS is considering four parameters: Slice Throughput (ST), Slice Delay (SD), Slice Loss (SL) and Slice Reliability (SR). The SP is considering three parameters: Slice Traffic Volume (STV), Slice Interference from Other Slices (SIOS) and Slice Connectivity (SC). The SOC is considering three parameters: Virtual Machine Overloading Cost (VMOC), Link Overloading Cost (LOC) and Switches Overloading Cost (SWOC).
In this paper, we propose a Fuzzy-based Scheme for SLA evaluation (FSSLA). The structure of FSSLA is shown in Fig. 8. We compare two models: FSSLA1 and FSSLA2. The FSSLA1 considers three input parameters: Reliability (Re), Availability (Av), Latency (La) and the output parameter is SLA. In FSSLA2, we consider Traffic Load (Tl) as a new parameter.
The Re value is the required user reliability. When Re value is high, the SLA is high.
The Av is the required user availability. When Av value is high, the SLA is high.
The La is the required user latency. When La value is high, the SLA is low.
The Tl is the total traffic of users in a slice. When Tl value is high, the SLA is low.
The SLA is described based on these four parameters. The user request is characterized by its required SLA.
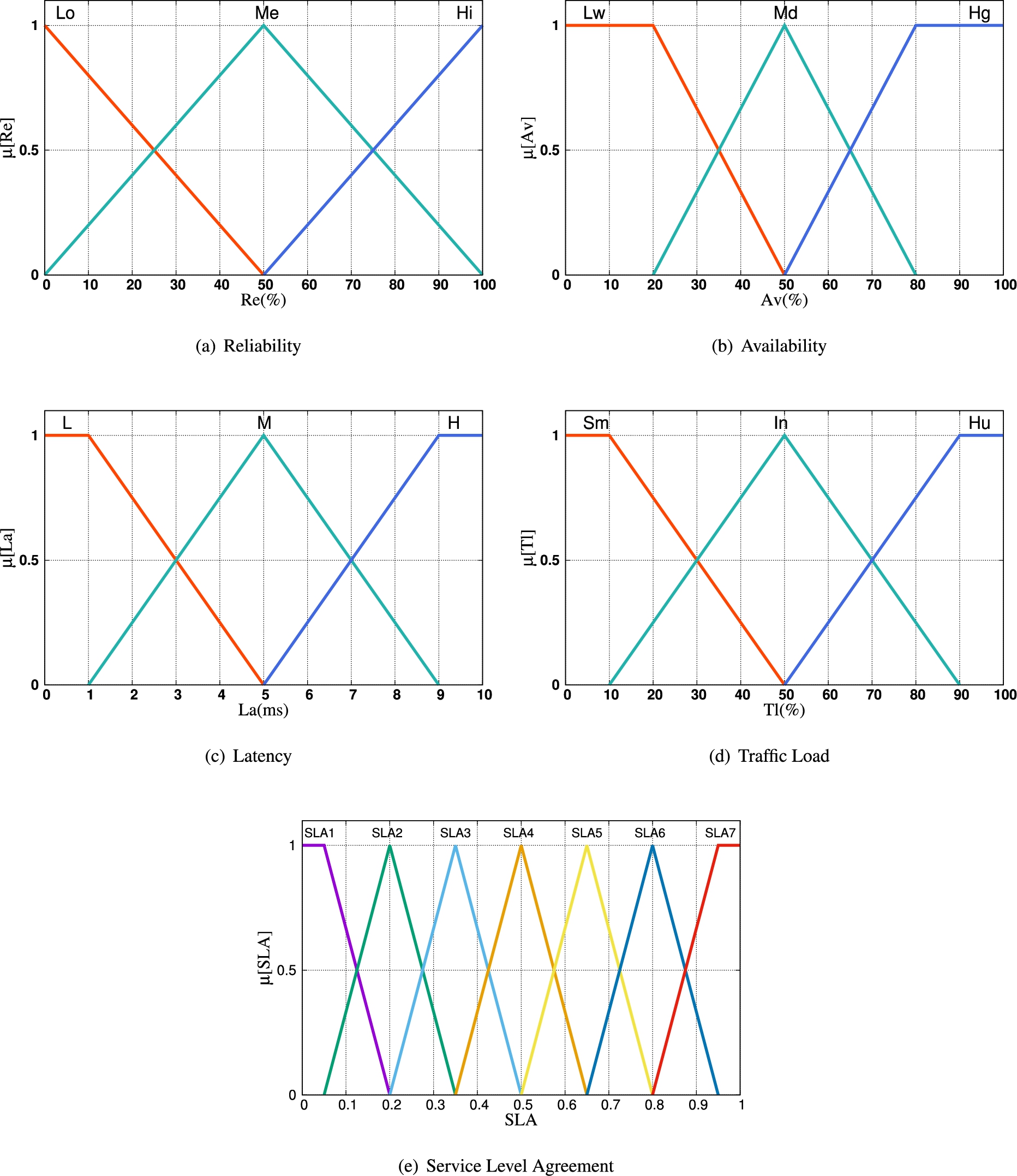
Membership functions.
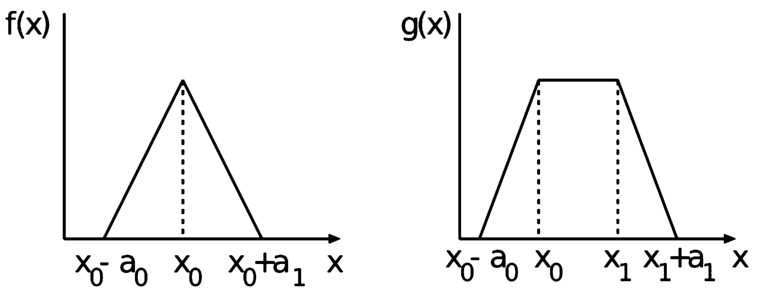
Triangular and trapezoidal membership functions.
The membership functions are shown in Fig. 9. The proposed fuzzy system can be used for different applications. We consider the values of Reliability, Availability and Traffic Load from 0 to 100% in order to easily fuzzify them. In the case when we want to use the proposed system in a real scenario, we require from the applications the maximum value, which will be 100%. For the value of Latency, we consider the maximum value 10 ms based on the results shown in [20]. In this paper are shown the Latency values for different use cases: eMBB (5 ms to 10 ms), Massive IoT (10 ms) and Critical Communications (1 ms or 5 ms). We use triangular and trapezoidal membership functions as shown in Fig. 10 because they are more suitable for real-time operations. We explain the design of FLC in following.
We use three input parameters for FSSLA1 and four input parameters for FSSLA2:
Reliability (Re); Availability (Av); Latency (La); Traffic Load (Tl).
The term sets for each input linguistic parameter are defined respectively as shown in Table 2.
The membership function for input parameters are defined as follows.
Parameter and their term sets for FSSLA1 and FSSLA2
Fuzzy rule base for FSSLA1
Fuzzy rule base for FSSLA2
The output linguistic parameter is Service Level Agreement (SLA).The term set for the output parameter SLA is defined as follows.
The membership functions for the output parameter SLA are defined as follows.
The Fuzzy Rule Base (FRB) for FSSLA1 and FSSLA2 is shown in Table 3 and Table 4, respectively. The FRB is formed by a fuzzy set of dimensions (
The simulation results are presented in this section. The simulations are run on a Linux Ubuntu OS computer with the following specifications: 8 GB RAM, i5 (3.2 GHz × 4) processor, and SSD (650 GB). We used our FuzzyC system that we had implemented for simulation. The FuzzyC simulation system is written in C and includes the Fuzzy library [15].
Figure 11(a), Fig. 11(b), and Fig. 11(c) illustrate the simulation results for FSSLA1. They represent the relationship between SLA and La. The Re and Av are considered as a constant parameters. We alter the Av value from 10% to 90%. We choose 10% for the Re value in Fig. 11(a). We can see that when La increases from 0 to 10 ms, the SLA decreases. When La is 5 ms, the SLA increases by 15% when Av increased from 10% to 50% and from 50% to 90%, respectively.
To understand how Re has impacted SLA, we compare Fig. 11(a) and Fig. 11(b). When La is 5 ms and Av is 50%, SLA is raised by 11.38% by increasing Re from 10% to 50%. When Av is 90%, all SLA values are greater than 0.5, as shown in Fig. 11(b). We raise the value of Re to 90% in Fig. 11(c). When comparing the results of Fig. 11(a) and Fig. 11(b), we can observe that the SLA values have grown significantly.
The simulation results for FSSLA2 are shown in Fig. 12, Fig. 13 and Fig. 14. They show the relation of SLA with Tl for different La values considering Re and Av as constant parameters.
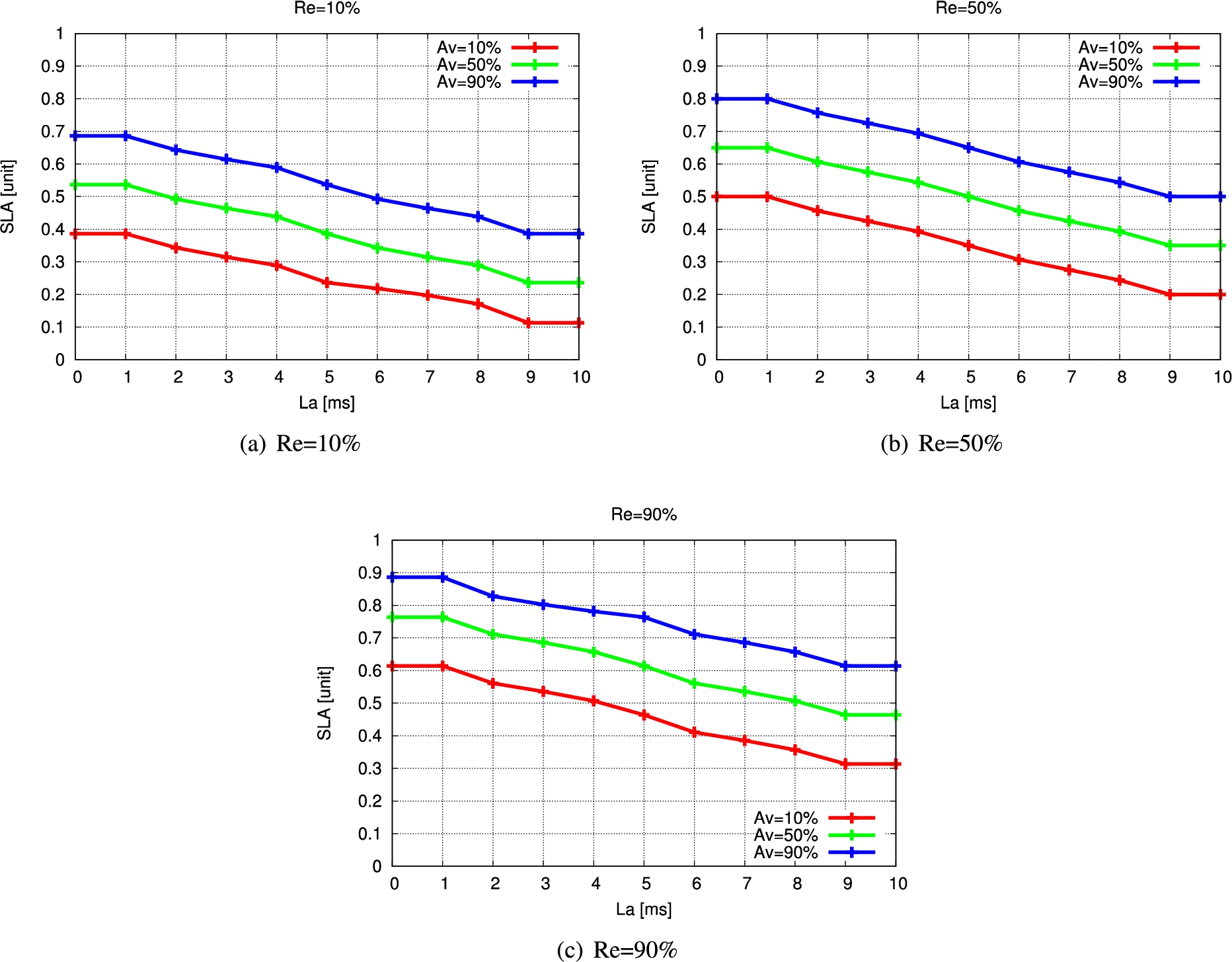
Simulation results of FSSLA1.
The Re and Av values are 10% in Fig. 12(a). We can see that when Tl is increased, SLA is slightly reduced. When La is increased from 1 ms to 5 ms and 5 ms to 9 ms, the SLA is decreased by 15% and 11.84%, respectively, for Tl 30%. To see how Av has influenced SLA, we compare Fig. 12(a) and Fig. 12(b). In case when the Av is increased from 10% to 50%, the Tl value is 50% and the La is 1 ms, the SLA is increased by 15%. When the Tl value is changed from 20% to 80%, the SLA is decreased by 18.75% when the La value is 1 ms, as shown in Fig. 12(b). This is because when the system have a lot of traffic load, it will degrade the required SLA. In Fig. 12(c), when we changed the Av value to 90%, all SLA values are higher than Fig. 12(a) and Fig. 12(b) because the required user availability is higher and the SLA should be high for supporting the user requirement.
In Fig. 13, we have increased the value of Re to 50% and the SLA values are higher than in Fig. 12. The SLA is increasing by 11.38% when the Tl values is 50%, La value is 1 ms and Av value is 10%. When the Av increases from 10% to 50% and 90%, the SLA increases by 15%, respectively when the Tl value is 60% and the La value is 5 ms. When La values are 5 ms and 1 ms, all SLA values are greater than 0.5, as shown in Fig. 13(c). This means that users fulfill the SLA requirements.
We have increased the value of Re to 90% in Fig. 14. In comparison to the results of Fig. 12 and Fig. 13, we can see that the SLA values have increased significantly. When the Re is increased from 10% to 90% and 50% to 90% and the Tl value is 50%, the Av is 50% and the La is 1 ms, the SLA is increased by 22.76% and 11.38%, respectively.
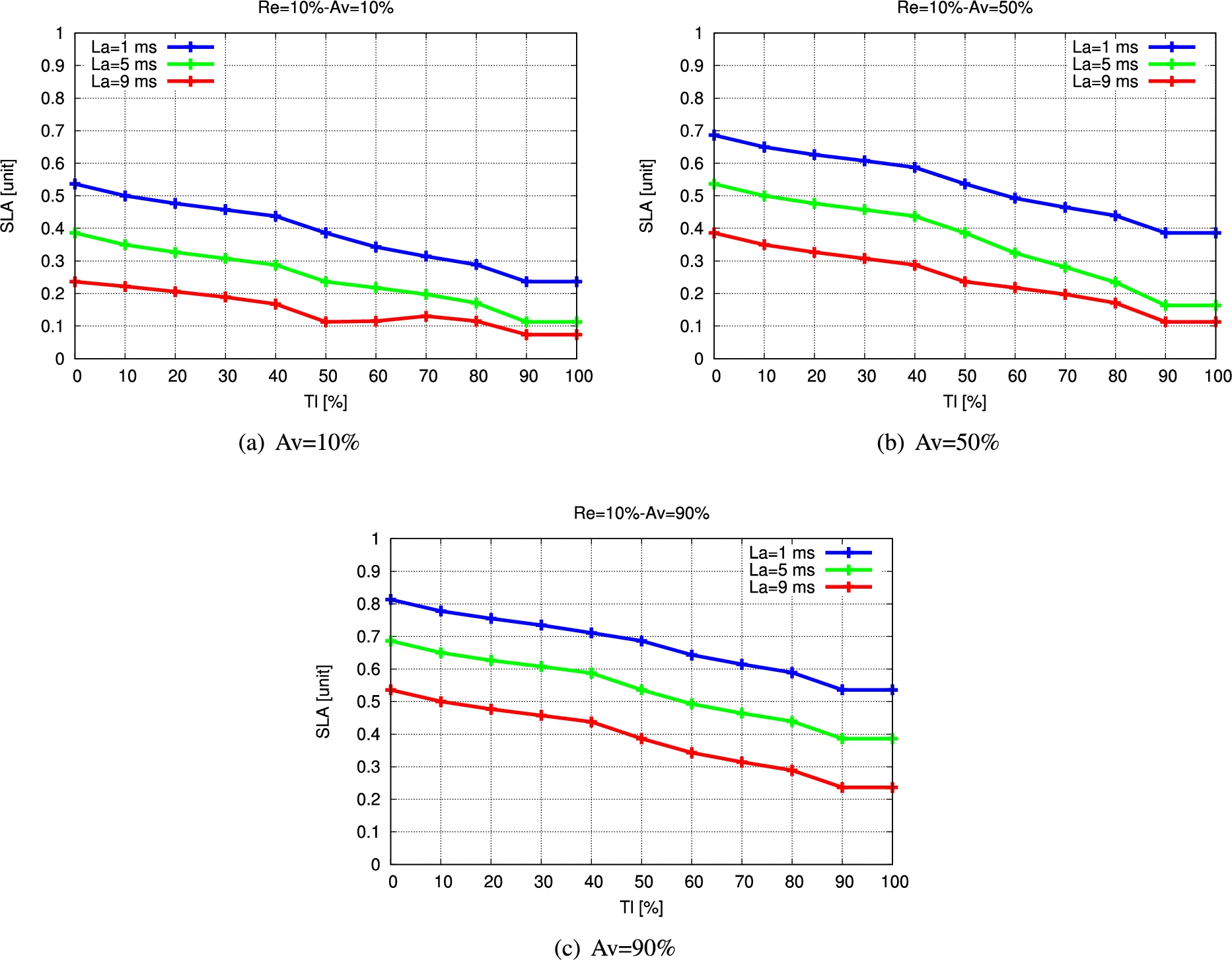
Simulation results for FSSLA2 (Re = 10%).
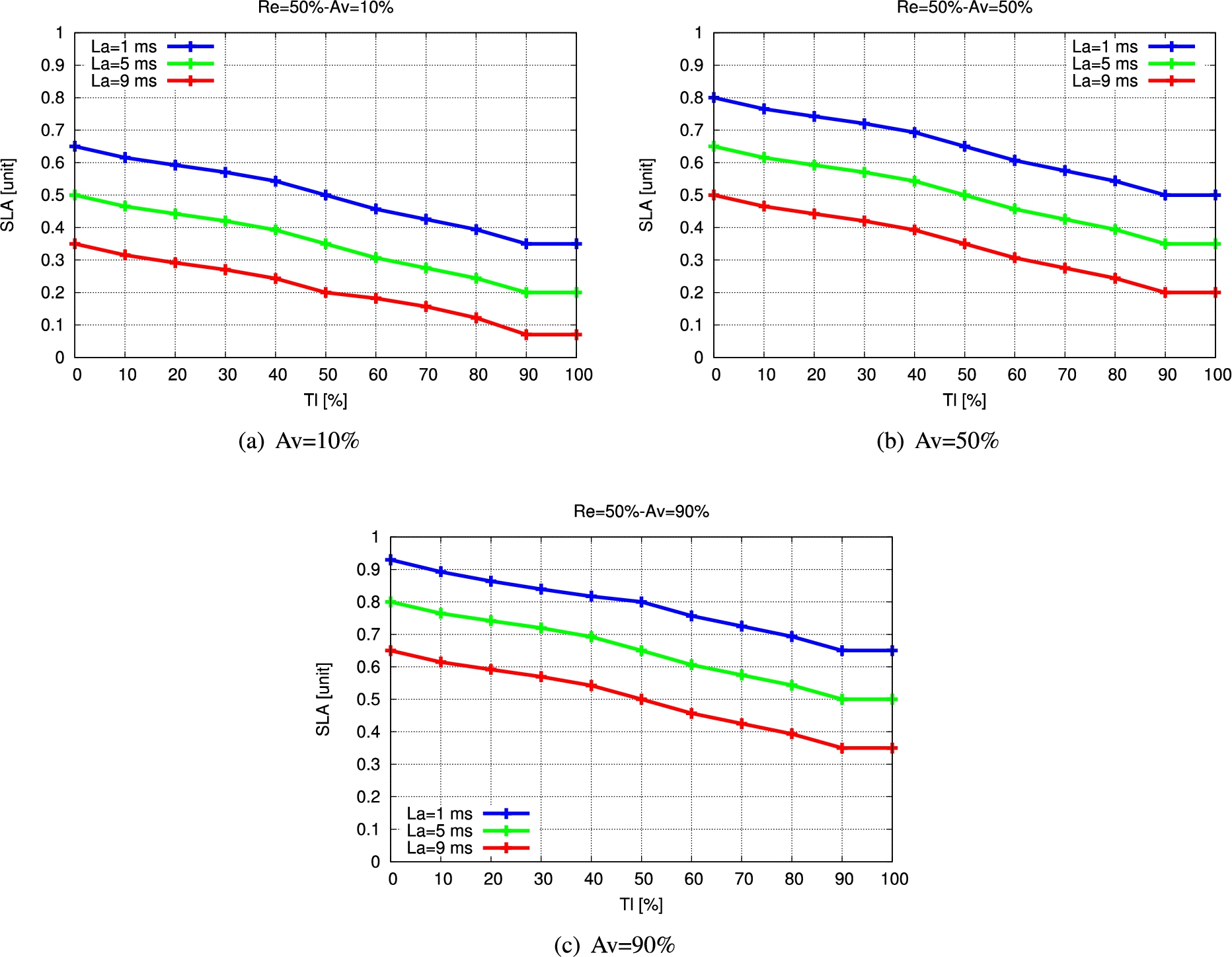
Simulation results for FSSLA2 (Re = 50%).
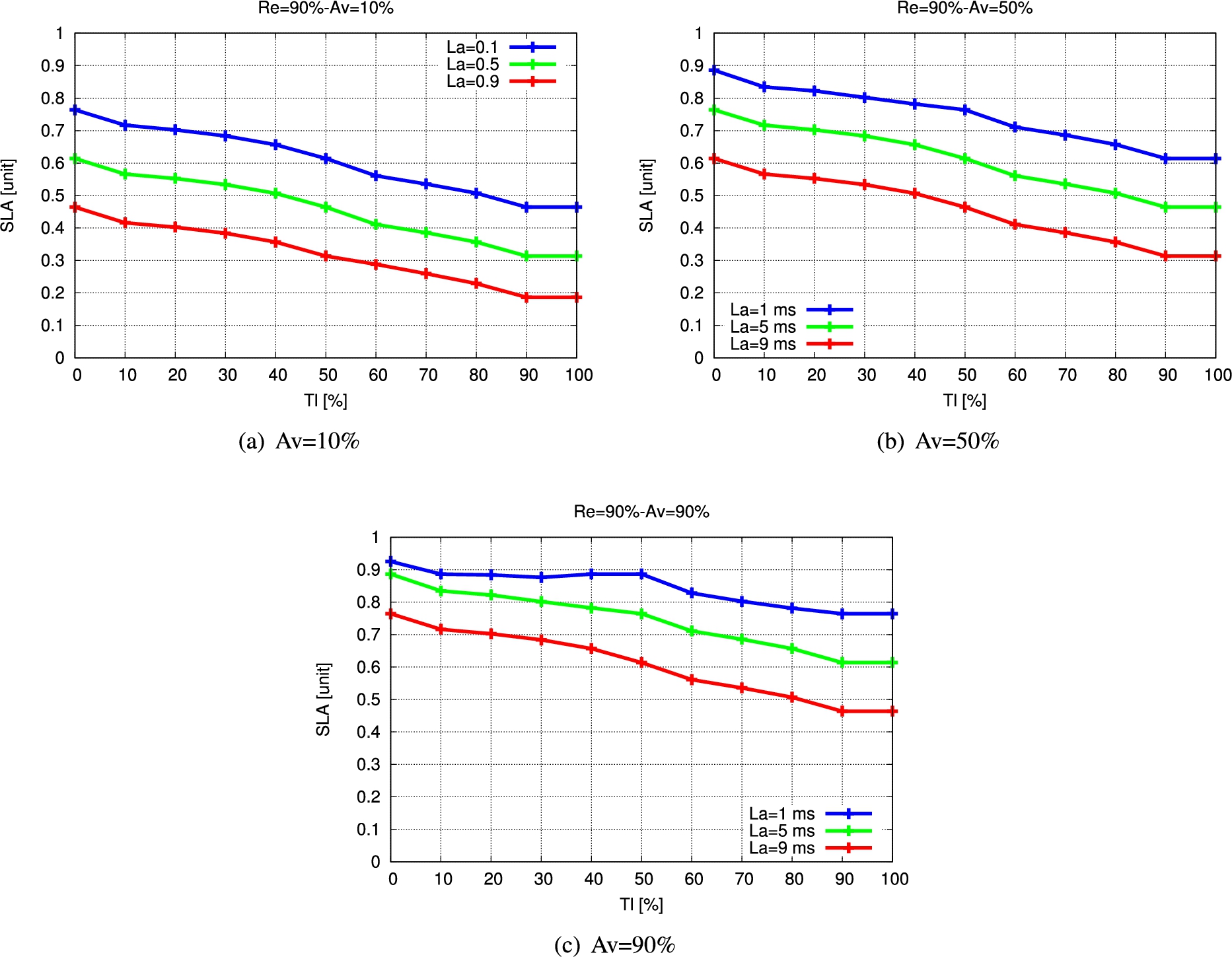
Simulation results for FSSLA2 (Re = 90%).
In this paper, we proposed and implemented a Fuzzy-based scheme for user SLA. The admission control mechanism will find a set of slices that match the required SLA and attempt to connect a new user to one of the slices. As a result, in 5G wireless networks, the SLA parameter will be utilized as an input parameter for admission control. We evaluated the proposed system by simulations. We discovered that four parameters have varied effects on the SLA based on the simulation results. The SLA value increases as the Re and Av values increases, but when the La and Tl values increase, the SLA value decreases. When comparing FSSLA1 with FSSLA2, we find that FSSLA2 is more complex than FSSLA1, but it performs better for admission control since the Tl parameter is considered.
In the future, we will consider other parameters and make extensive simulations to evaluate the proposed system.
Conflict of interest
The authors have no conflict of interest to report.
