Abstract
In text-based authentication, the passwords along with user names are maintained in the Authentication Data Table (ADT). It is necessary to preserve the privacy of passwords in ADT to avoid offline attacks like brute force attacks, lookup table attacks, etc. In this paper, three password protection schemes, namely Encrypted Image Password (EIP), Dynamic Authentication Data Table (D-ADT), and Extended Encrypted Image Password (EEIP) are proposed for secure authentication. In EIP, the input passwords are first converted to hashed passwords and then transformed into images. Next, these image passwords are encrypted using a novel image password encryption system using chaos functions and confusion-diffusion mechanisms. In D-ADT, the hashed passwords are encrypted using a random key. The major highlight of this scheme is that during every log, the hashed password is encrypted with a new random key while keeping the plain password same as it is. So, during each login of the user, the old encrypted password is replaced with a new encrypted password in the authentication data table. The EEIP scheme combines both approaches. Passwords are converted to images and image passwords are encrypted with the new random key at every login. Performance and security analysis are carried out for the proposed algorithm concerning correlation analysis, differential analysis, entropy analysis, computation time, keyspace, and offline attack analysis.
Introduction
Nowadays, in this internet world, common people are becoming regular internet users as compared to the previous decade. Two reasons are behind this: i) availability of smartphones at lower prices because of growth in mobile technology and ii) growth in high-speed internet technology. Hence, businesses but also common people are also far more attracted to online. Today, the availability of mobile apps is increasing such that it is producing a remarkable change in the way common people feel and experience technology. People prefer online services in every sector like banking, shopping, transport, finance, health, marketing, and many more. So, people’s efforts are reduced, and comfort is guaranteed. However, while accessing such online services, the security protocol plays a key role. To access any device or service in this digital world, the first step is authentication i.e. validating the user. But it is observed that a secure authentication mechanism is still challenging because of the hacker’s intelligence. At the same time, the researchers are also continuously providing solutions for secure access through complex computational logic and different input factors. Anyhow all these are ongoing parallel activities taken by hackers and researchers. The solution methodologies include passwords, PINs, hashed passwords, salted passwords, key stretching, graphical passwords, one-time passwords, biometric passwords, and more variations of biometrics (fingerprint, iris, ECG, palm print, etc.). Among these various solutions, passwords and their variations are popular because of their convenience and easy implementation. Unfortunately, this becomes the greatest opportunity for cyber-criminals to focus on this area. Because users have to generate their passwords, there is often a chance that they are unable to create strong and secure credentials.
On the other hand, if passwords are highly secure, then there is a threat of attacks on ADT (Authentication Data Table) on the server side. ADT contains user credentials like user id and password. Hence, it is mandatory in high-security systems that the passwords need to be well protected against attacks. ADTs are much more vulnerable to precomputed table attacks. Due to the high availability of high computation processing units at a low cost, it is becoming easy to construct such precomputed tables. Also, on the internet, there are software tools available that convert a hash value to plain text (e.g., http://reverse-hash-lookup.online-domain-tools.com/). Using such tools, it is possible to create a precomputed table that consists of hashed passwords and corresponding plain passwords. If such precomputed tables are already created, then it is less challenging to find plain passwords from the ADT and break the security system. The attacker may apply faster search techniques like binary search to reveal passwords. After getting ADT, to reveal the passwords from ADT, an attacker may perform attacks such as brute force attack, dictionary attack, lookup table attack, reverse lookup table attack, rainbow table attack, or advanced dictionary attack. Depending on whether precomputation logic is used or not, these attacks are divided into two types: lookup and rainbow table attack comes under theprecomputation based attacks andremaining comes under non-precomputation based attacks. In the first type, because of the precomputation logic, both rainbow and lookup table attacks are easy ways to reveal passwords. In the second type, all four attacks simply try each given password from the password list. In the brute force attack, the password list contains all combinations of characters from a given character set, whereas the dictionary and reverse lookup table often contain frequently used passwords. The advanced dictionary contains the words based on the user practices to construct passwords.
The paper is organized as follows: in Section 2, the related work concerning the authentication and image cryptosystem techniques are discussed, in Section 3, the framework and working of proposed schemes are described. Performance and Security analysis is performed concerning the NIST randomness test, correlation analysis, differential analysis, information entropy analysis, the privacy of the ADT concerning off-line attacks, key space analysis, computational complexity analysis and comparison, and known/chosen plain text attack in Section 4. The conclusions are made in the last Section.
Literature survey
In this paper, three password protection schemes, namely Encrypted Image Password (EIP), Dynamic Authentication Data Table (D-ADT), and Extended Encrypted Image Password (EEIP) are proposed for secure authentication. The proposed methodologies use an image cryptosystem for password encryption. Hence, password-based authentication systems, traditional and existing chaos-based image encryption approaches are elaborated.
Backgound
Researchers have categorized authentication into five types: 1) text-based; 2) graphical-based; 3) biometrics-based; 4) Web-based; and 5) hardware-based solutions [4,5].
Text-based authentication using a password is more popular because of its low cost and easy implementation. The Authentication Data Table (ADT) is available on the server. It contains user credentials such as userid, password, and additional informative attributes. The way in which the user credentials are stored in ADT is important from a security point of view. But, it is observed that passwords are easily cracked because of users’ careless nature [2]. Generally, the user selects familiar words which are easy to remember as a password, and the same password is continued for different systems. The ADT contains userids and passwords which could be stolen by attackers in case of a weak security system or compromised system. Attackers continuously try to leak the security of the system, and at the same time, the corresponding application system should also focus on how to strengthen the security. In reality, the systems that are not strengthening their security protocols regularly are more vulnerable. Since the same passwords are usually used by the user for a long time, attackers may access high-security systems using cracked passwords. Next, after getting ADT, attackers may proceed for off-line attacks [24]. Normally, the ADT contains passwords in the hashed form. Hashed passwords are generated using a cryptographic hash function [3]. The hash function is a one-way mapping function that transforms any length of data into fixed-length data. It is difficult to find plain values directly from hashed values because of one-way mapping. But, researchers found that hashed passwords are not protected well against precomputation table attacks, such as lookup table attacks and rainbow table attacks [22]. Due to decreasing costs and the high availability of high computing, processing, and storage resources, the creation of precomputed tables is possible. These kinds of precomputations are used in the lookup table and rainbow table. So, the above two attacks are increased to more extent. Hence, an attacker could become more successful in cracking the hashed passwords. To protect from such precomputation attacks, the salting of passwords [26] is done. Salt is an array of characters that are inserted into the plain value and then hashed which acts as a noise. The size of the salt and the strength of password security are directly proportional, i.e., if salt is more, then security is also more. Next, to improve the level of security, salt can be dynamic [7]. On the other hand, it is observed that salted passwords are not strong under dictionary attacks. In these attacks, an attacker attempts all the possible passwords from the predefined list, i.e., the dictionary. To protect from a dictionary attack, the key stretching method is useful. In this, weak passwords are converted to enhanced passwords. But, these mechanisms are vulnerable to attacks like Narrow-Pipe Attack [12]. Luo et. al. [17], given an Encrypted Negative Password (ENP) solution. In this, the hash value of the original password is calculated. Next, the negative password is calculated. At last, the negative password is converted into an Encrypted Negative Password using an asymmetric cryptosystem. ENP could protect against lookup table attacks and dictionary attacks. But, the generation of negative passwords is time-consuming. All these techniques with their own advantages and limitations are summarised in Table 1.
Summary of existing methodologies
Summary of existing methodologies
In the proposed system, plain passwords are converted into images, then image passwords are encrypted using a novel image encryption system. Hence, various image encryption techniques are studied here.
Mostly, image encryption follows a chaotic map-based confusion-diffusion model. The idea is based on Fridrich’s substitution-permutation network [10]. Fridrich’s model consists of two phases- confusion and diffusion. In confusion, the pixels of the image are repositioned, and in diffusion, pixel values are modified. The confusion and diffusion operations are made reversible so that decryption is possible. Chaotic map functions are used to generate keystreams required for confusion and diffusion operations. Confusion-diffusion operations are repetitively executed for m and n times to increase the security level. The 1D, 2D, and 3D variations of chaotic functions have been used in different systems. As dimensions increase, the complex, chaotic behavior produced by the chaotic system also increases and the guessing of chaotic behavior becomes complex. On the other hand, the implementation cost of these more dimensional techniques is high due to their complexity [11]. 1D chaos is preferable because of its simplicity, but it has drawbacks like, (1) limited domain for chaos generated values (2) low computational complexity leading to cryptanalysis using correlation and repetitive functions, and (3) the chaos function spreads output sequence values non uniformly [32]. The common approach to encrypt an image is as follows: a two-dimensional digital image is transformed into a byte array, and the required keystreams for confusion and diffusion are produced by chaotic functions. As an example, for confusion, 2-D maps such as the Arnold Cat map, and Henon map are used in [21]. Also, to increase the quality of the cipher image, the rounds of confusion-diffusion are increased. Due to this, the computation time grows. On the other hand, to achieve similar results in fewer confusion/diffusion rounds, operations on the bits are defined. [14,27,31,33] designed the cryptosystem that operates on the bits. In this system, first, the input image is transformed into a bitstream. Next, confusion and diffusion operations are applied. 3-D map along with gray code logic for image encryption is applied in [8]. Next, a Five-dimensional multi-wing hyper-chaos-based system is designed by Li et al. [14]. Here, the keystream is produced by a hyper-chaotic system where the key is derived from the original image. Next, bit/pixel level confusion and diffusion are applied. However, the computational time complexity of such a more dimensional chaotic system is much more. To decrease computational complexity, Zhi–Liang et al. [34] proposed a solution using the logic of bit positions of the pixel. According to information theory, in the image, the most significant 4 bits of pixel contain around 94.125% information. Taking advantage of this, confusion of most significant bits is done while a group of least significant 4 bits is treated as one unit and repositioned individually. Using a Logistic map, each pixel is changed during diffusion. Next, a more efficient method based on BBD (Binary Bit-plane Decomposition) is proposed in [27,31,33].
In addition to the above methodologies, a random number embedding and DNA-level self-adaptive confusion-diffusion is applied in [29]. The magic square theorem is applied for confusion at the pixel level and the octree principle is invoked to achieve pixel bit shifting in [28]. Block-based preprocessing, postprocessing, and shuffling are used in [16]. But, it may require padding because of the fixed size of the blocks. An input image-related rows and columns shuffling, a pixel-level roll shift, and a bit-level cyclic shift are applied in [15]. Focusing on medical image encryption, simple random shuffling, and XOR operations are used in [20] for encryption logic.
Hence, from the above, it is observed that various researchers have designed various logic. The core part is confusion and diffusion of image components that can be block, pixel, or bit. Every method has pros as well as cons. The limitation includes small key space, high computational power, suffering from differential attack and chosen/plain text attacks, fixed keys, etc.
To overcome limitations of the existing authentication schemes as shown in the Table 1, in this paper, three password-based authentication methodologies are designed and implemented for secure authentication through SHA256 and novel image cryptosystem. The proposed scheme EIP is based on image encryption using Fridrich’s confusion-diffusion model. Here, input passwords are initially converted to hashed passwords using the Secure Hash Algorithm (SHA256) and then embedded into the binary image. Next, these image passwords are encrypted using a novel image password encryption system to get grayscale Encrypted Image Passwords as a result. Arnold’s cat map and logistic map are used to generate encryption key streams. The control parameters used for these Chaotic maps are calculated from the value of the hashed password. In the second scheme, D-ADT, initially, input passwords are hashed using SHA256, and the hash value of passwords is ciphered using Random Key. The Random Key is generated using the RANDOM() function. Random Key is encrypted with the key calculated from the hashed password. In this case, the ADT preserves three values, i.e., UserID, Encrypted Password, and Encrypted Random Key. The major highlight of this scheme is that during every login, the hash value of the password is ciphered using a new random key while keeping the plain password the same as it is. The third scheme, EEIP, is a combination of the above two approaches. Here, the passwords are converted to images, and image passwords are encrypted with a new random key at every login. The ADT contains UserID, Encrypted Image Password, and Encrypted Random Key.
Motivation and contribution
Existing methodologies like hashed password [3], salted password [26], dynamic salted password [7], key stretching [6] are vulnerable to precomputation table attacks, dictionary attacks, and Narrow pipe attack. The overhead of Encrypted Negative Password scheme (ENP) [17], is the generation of negative database for the passwords.
The process of generating negative database passwords is complex and time consuming. The proposed EIP uses a simple and effective procedure of image password. In various authentication techniques, the authentication data table is static. Hence, ADT offline attacks are possible. To overcome these attacks, Dynamic ADT (D-ADT) scheme is proposed. Next, to increase the level of security, the EIP and D-ADT are combined together and a novel Extended EIP (EEIP) scheme is proposed. This EEIP can be used in an application where high security is required like defence, finance etc. To design the above algorithms, a novel image cryptosystem is proposed. Here the key parameters depend on the input image.
The contributions of the proposed paper are:
Passwords are well protected in ADT against offline attacks using novel encryption techniques. Proposed EIP and EEIP are alternative schemes for Encrypted Negative Password (ENP). ENP requires a negative database password to generate ENP. The process of generating negative database passwords is complex. The proposed EIP uses a simple and effective procedure of image password. Decryption of encrypted passwords is not required during authentication; rather, a comparison is made in the cipher domain itself. A novel image cryptosystem whose encryption parameters depend on input image is implemented to achieve a higher level of security. Passwords are stored in encrypted image form, and encrypted image passwords change during every login by keeping the plain password the same as it is.
Proposed system design
In the following subsequent subsections, the proposed three authentication schemes are described and compared.
Scheme 1-encrypted image password
Figure 1 shows the flow of the proposed Encrypted Image Password (EIP). Initially, the user gives a plain password which is hashed, and the corresponding bitstream is generated. Using this bitstream, three keys are generated. These keys are used to create encrypted image passwords. The detailed working flow of the proposed system is described through subsequent subsections.
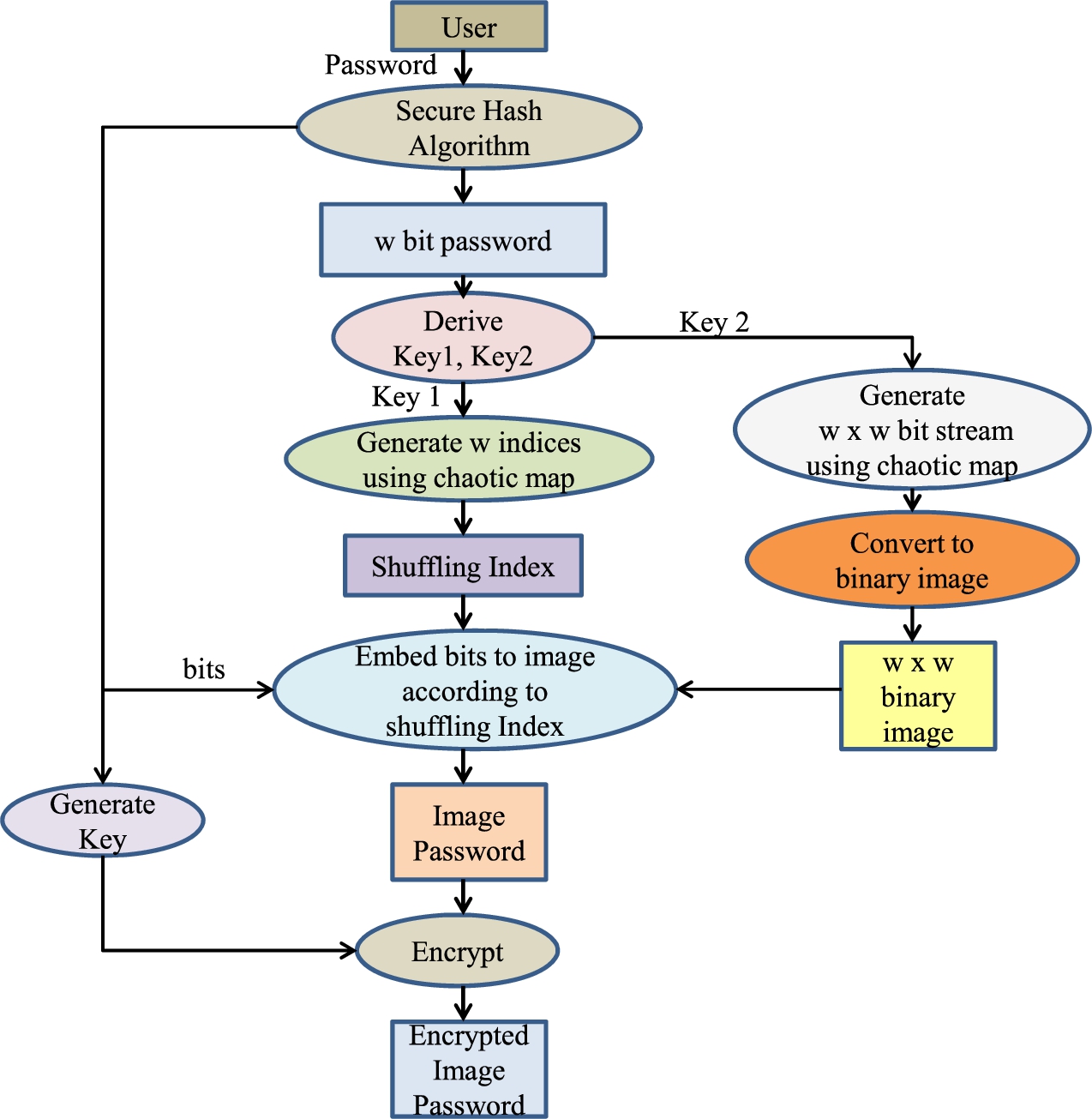
Data flow diagram of encrypted image password (EIP).
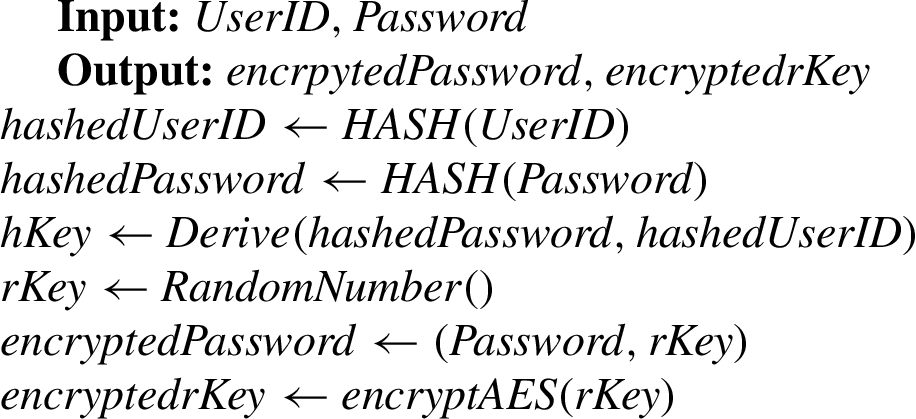
The registration process for a new user is done as given below:
On the user machine, the user inputs the credentials, including UserId and Password. Next, the entered credentials are sent to the Authentication Server (AS) through a secure channel.
AS calculates the hash value of UserID using SHA256 and searches UserId in the ADT for the calculated hash. If UserId already exists, AS rejects the registration request and returns a Negative Acknowledgment to the client. Otherwise, step (iii) is executed.
The received password is hashed using SHA256 and hashed password of length w is obtained.
Image password is encrypted to get EIP using the proposed
AS inserts a record for UserId in the authentication data table and returns Positive Acknowledgment to the client.
PasswordToImage
ImagePasswordEncrypt
On the user machine, the user inputs the credentials, including UserId and Password. Next, the entered credentials are sent to the Authentication Server (AS) through a secure channel.
AS calculates the hash of UserId using SHA256 and searches UserId in ADT for the calculated hash. If the user does not exist, it stops the authentication process and returns a Negative Acknowledgment to the client. Otherwise, step (iii) is executed.
The encrypted image password is found from ADT named EIP1.
The received password is hashed using SHA256, and
Image password is encrypted through Algorithm 2
EIP1 and EIP2 are compared by taking bitwise XOR. If the XOR operation gives ZERO, then return Positive Acknowledgment. Otherwise, return Negative Acknowledgment. The advantage is that the comparison is made in an encrypted domain, and there is no need for decryption for matching.
Image password could be obtained through the following steps as denoted in Fig. 1. First, the received password is hashed using SHA256. Next, the hashed password, i.e., w-bit sequence, is transformed into
Generation of image password
Generation of image password
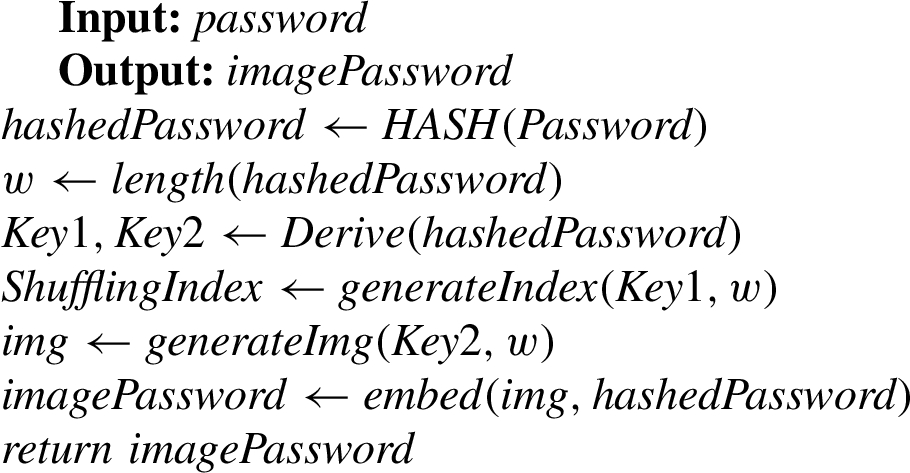
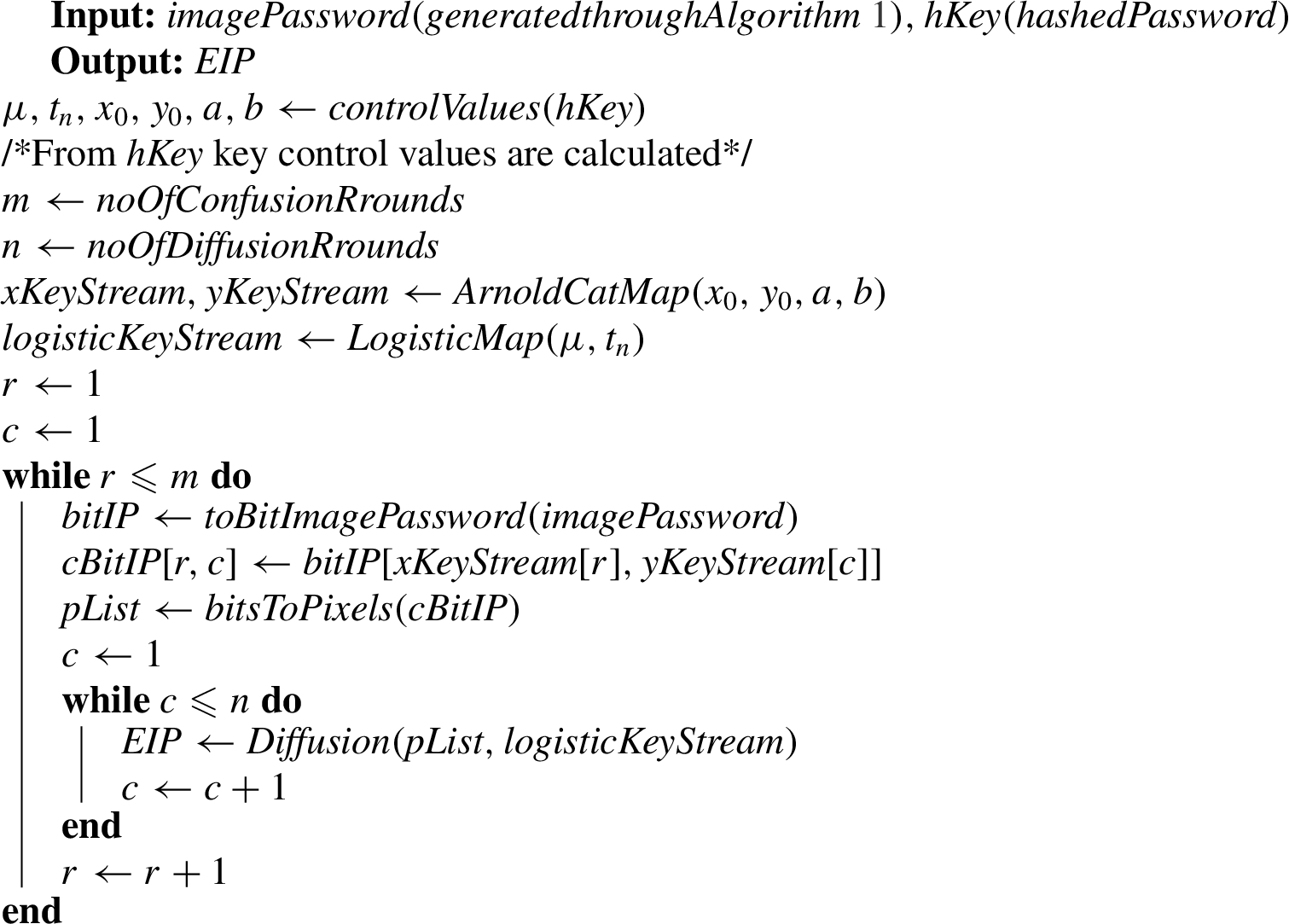
The block diagram of the proposed image password cryptosystem is shown in Fig. 2. The cryptosystem is based on Fridrich’s confusion-diffusion model. It uses two chaotic maps, viz. Arnold cat map and Logistic map to generate keystreams.
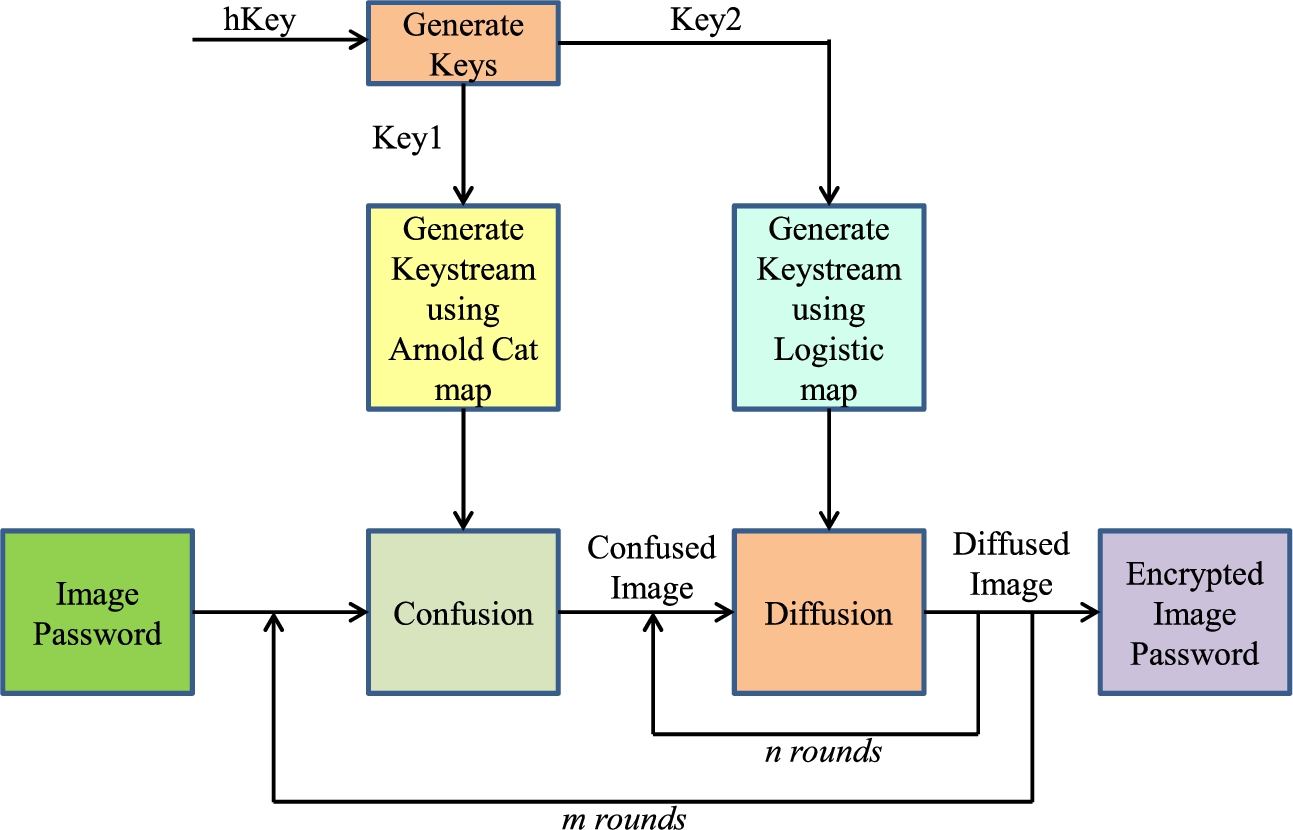
Image password encryption.
For image password encryption, initially, the image password is converted into a bit image. Using Arnold’s cat map (1), keys
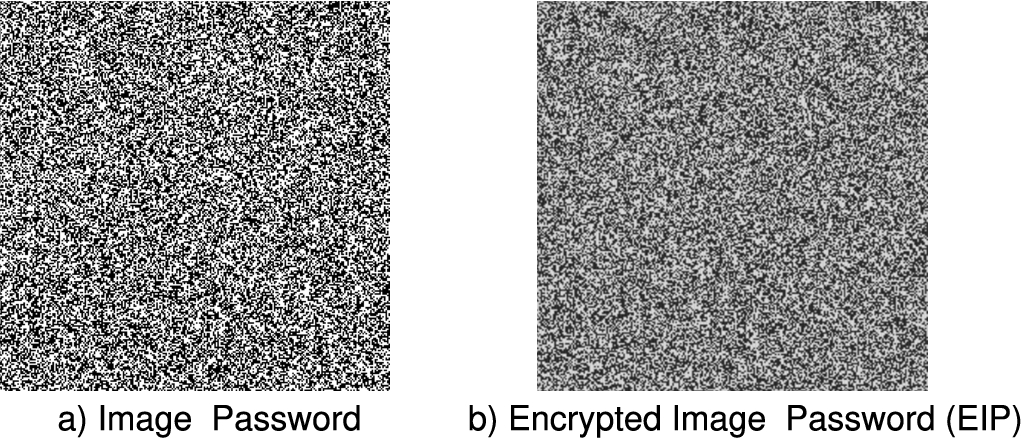
Image password and encrypted image password.
In this approach, a trick based on the user’s login is used to change the encrypted password without modifying the original plain password. Figure 4 describes the flow of this scheme. At every successful login, a plain password is hashed using SHA256. The
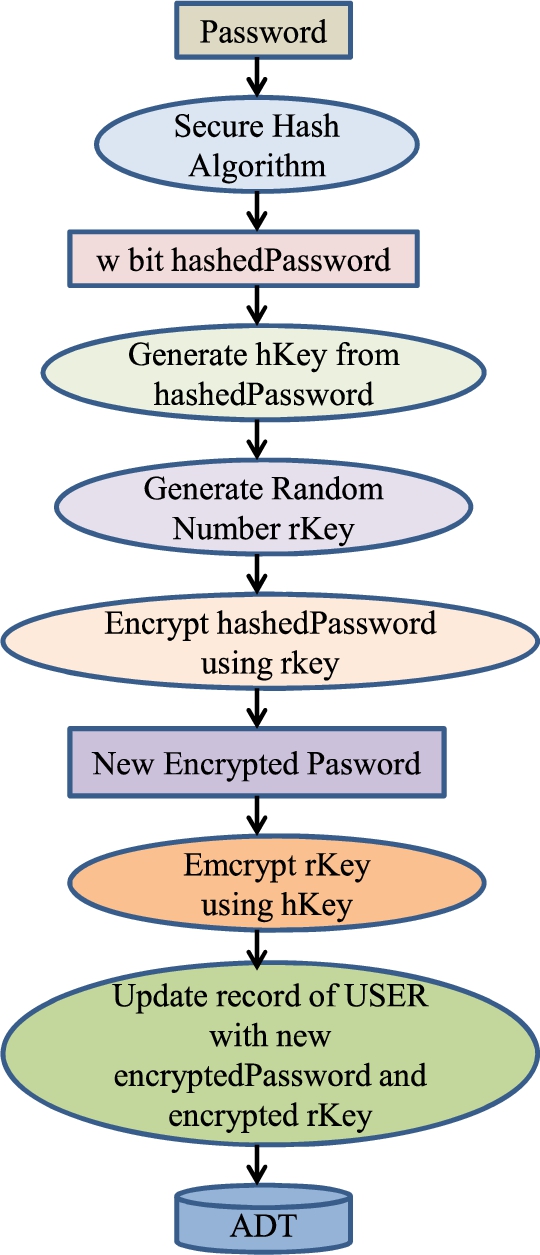
Flow of ADT update during each successful login.
During authentication(login), the user gives plain UserId and Password. The password is hashed, and the corresponding
Dynamic ADT method-ADT update during login
Dynamic ADT
In this solution, the previous two approaches are combined. In EIP, during image password encryption, the
Algorithm 4 shows working of Extented EIP. Table 5 illustrates the instances of ADT at different times.
Extended EIP-ADT update during login
Extended EIP-ADT update during login
Extended EIP-ADT
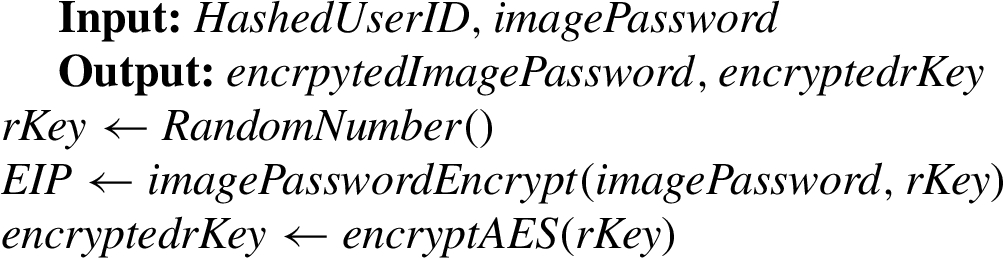
Extended EIP
The proposed schemes are compared with key points as described in Table 6. From this table, it is observed that the EEIP is advantageous in high-security systems because of its enough key space and complex encryption logic. On the other hand, EIP is advantageous in applications where the login frequency is less. In the case of D-ADT, the key space is less, so it is not preferred for high-security systems. If frequent logins are required in a single day, then D-ADT is advantageous.
Comparative analysis
Comparative analysis
The proposed system is implemented on Ubuntu 16.04 LTS OS using Python 3.6.3 in a PC having an Intel Core i5-4570, 3.20 GHz × 4, 16 GB RAM, and MySQL 5.5 as a back end.
Algorithms 1 and 2 show the time complexity of password-to-image conversion as
NIST (national institute of standards and technology) randomness test
The NIST [23] created a statistical test suite with 15 distinct sub-tests to assess the randomness of the binary sequence. For the randomness test, NIST employs the
NIST gives two methods for interpreting test results [23]:
(i) Calculation of the pass rate
(ii) To calculate the
NIST randomness test
NIST randomness test
The range [0, 1] is partitioned into 10 equal sub-ranges and
If
For the experiment, the random number sequence of length
The correlation among connected pixels of the encrypted images is calculated through a random selection of 6000 samples of connected pixels from the encrypted
Correlation analysis
Correlation analysis
A number of Pixels Change Rate (NPCR) and Unified Average Changing Intensity (UACI) are the testing methods to check the sensitivity of a little modification in the plain image as given by (8) and (10). Assume,
Differential analysis
Differential analysis
Information entropy measures randomness. For gray images, if the pixel spread is uniform, then the highest entropy is eight. Assume
Information entropy analysis
Information entropy analysis
To analyze computational time, the notations used are described in Table 11. All the operations are executed on the same machine as specified at the beginning of this section. The comparison of computation time analysis of the proposed system (D-ADT) and other systems is shown in Table 12. From the comparison, it is noticed that the proposed D-ADT is almost faster than other systems. The major highlight of the scheme is the passwords are updated during each login without changing the original password. Ultimately, the level of security is very high.
Notations
Notations
Analysis of computation time during authentication
ADT contains user credentials. Suppose, the hacker has pre-obtained the ADT. To reveal the hashed/ciphered passwords, the off-line attacks which could be made available are given below:
Bruteforce attack
Here, the attacker has to check all possible combinations of symbols to reveal the password. But, to make such an attack is very hard.
Dictionary attack
The attacker creates a dictionary consisting of familiar words or words of daily routine. Next, the matching of words from the dictionary to ADT is done.
Advanced Dictionary attack
In this attack, an attacker has to create a dictionary containing words that are predicted by the users’ nature of designing passwords.
Lookup table attack
In this attack, initially, an attacker prepares a list of passwords. The list normally consists of regularly used passwords. Next, he constructs the lookup table containing tuples of hashed passwords and its password in the plain form of the prepared list. An attacker applies a search operation between the lookup table and ADT entries.
Rainbow table attack
Rainbow tables consist of hash chains. Through alterations of the hash and reduction function, a series of alternating passwords and hash values are produced. Only the initial and the endmost plain value produced is entered in the rainbow table.
The common thing in the above off-line attacks is that the hacker has to compare the hash value of the password from ADT with the precomputed hash value of the password except for brute-force attacks. To illustrate how these attacks are executed, consider the attacker has prepared a table as in Table 13 containing the password and corresponding pre-computed password digest. The password digest may be obtained by applying cryptographic hashing techniques such that MD5, SHA256, Whirlpool, etc. The attacker simply searches the table for the target cipher password. If the target cipher password is matched with the password digest in the prepared table, then the password is cracked. The attacker may perform a binary search to find the password digest from the look-up table. However, in proposed schemes, such attacks are very hard because the ADT contains encrypted passwords. For the attacker, the proposed schemes are very hard to obtain encrypted password as depicted in Fig. 5. The attacker has to obtain a corresponding encrypted password. The used encryption logic and key generation logic in proposed schemes are secure enough to protect against these attacks.
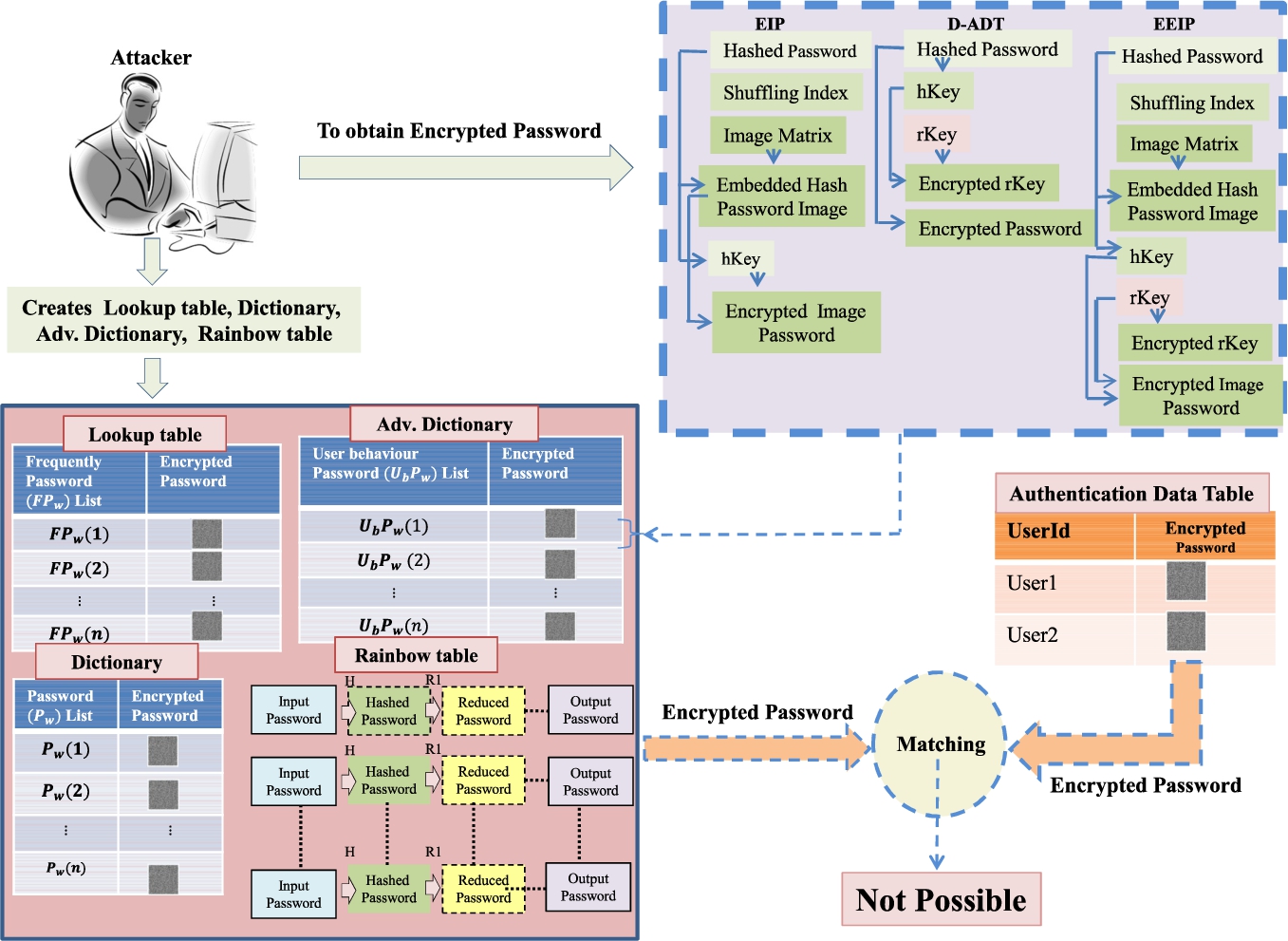
Illustration of attacks.
Sample password digest table
In the proposed EIP and EEIP schemes, Arnold’s cat map and the logistic map take a total of six control values
Analysis and comparison of attack complexity
In this section, the time complexities concerning lookup table attack and dictionary attack of the proposed schemes are discussed and compared with the Encrypted Negative Password approach (ENP1, ENP2) [17] and shown in Table 14. Here, the complexity generated by key space is ignored for simplicity. The comparison shows that the proposed schemes are very hard to perform lookup table attacks and dictionary attacks.
Notations
w Length of the hashed password
Comparison of time complexity with attacks
Comparison of time complexity with attacks
In the proposed system, if an attacker wants to crack EIPs using a lookup table attack, the attacker must first compute all possible EIPs for each password from the list. To find EIP for a single password from the list, the following steps are taken by the attacker. First, to find shuffled passwords totally
Dictionary table attack analysis
To verify the password from the password list in the case of EIP and EEIP, the following steps are done:
Obtaining Obtaining Shuffling Index ( Obtaining Embedding hashedPassword into binary image to get Encrypt Match EIP1 with EIP2. EIP2 is taken from ADT. If EIP1 and EIP2 are matched then solution found (
Hence, the complexity to crack passwords is given by
In the case of D-ADT, the following steps are taken
Obtaining Obtaining rKey( Encrypt Match EHP1 with EHP2. EHP2 is taken from ADT. If EHP1 and EHP2 are matched then solution found (
Hence, the complexity to crack passwords is given by
Analysis of known/chosen plain text attack
In the chaotic cryptosystem, an attacker is mainly interested in getting the intermediate results [21]. The required intermediate results to be computed from the proposed cryptosystem can be found by dividing the
Comparative analysis
Table 15 shows the comparative analysis of ENP and EEIP concerning standard parameters. From the comparison table, it is observed that EEIP is more advantageous as compared to ENP. The highlighted key point in EEIP is dynamic ADT. Because of this, it can be useful in highly secure applications like the military, finance, etc.
Comparative analysis
Comparative analysis
In this paper, three protection schemes are proposed for secure authentication. In scheme-1 EIP, the plain password is converted to an encrypted image password. In scheme-2 D-ADT, the plain password is hashed and encrypted using the different random keys at every login. So, ADT contains a new encrypted password for an original plain password during each login of a particular user. By taking advantage of this beautiful logic, scheme-3 EEIP is proposed that combines described two schemes so that ADT contains a new EIP for each login. For the encryption of image passwords, novel image encryption is designed and implemented. The encryption keys depend on the input plain password. In the end, the analysis and comparison of ENPI, ENPII, and proposed schemes (EIP, D-ADT, EEIP) are made. Additionally, the key-space analysis and chosen/plain text analysis are also performed. The performance shows that EIP is sufficiently secure to protect against attacks like brute force, lookup table, dictionary, and rainbow table. The advantage of the proposed schemes is that there is no need for the decryption of encrypted image passwords during authentication.
