Abstract
Currently, international trade (Int’l Trade) often faces risks such as privacy data leakage and transaction security during transactions, which seriously affect the protection of privacy data in trade. Therefore, this article used the Internet of Things and blockchain to attempt to address these risk issues and improve the security of privacy data. By analyzing the security threats in Int’l Trade transactions, this article used additive aggregation functions to analyze the protection effect of privacy data and studied the core issues of Int’l Trade privacy data. This article analyzed the privacy protection model using the Internet of Things blockchain and proposed corresponding Int’l Trade privacy data protection strategies. Among the five surveyed enterprises, data audit and data backup were all above the standard value, while data query only exceeded the standard value for enterprises 2, 3, 4, and 5. The average abnormal value of the enterprise in data anomalies decreased by 0.06 compared to the standard value. Through experimental testing, it has been found that Internet of Things blockchain can effectively improve the privacy data protection effect of Int’l Trade and promote the convenience of Int’l Trade transactions.
Introduction
In today’s increasingly developed Int’l Trade, the flow of data is no longer limited to a single region, but is showing a global trend. However, in Int’l Trade, government departments, enterprises, and individuals not only enjoy the convenience and dividends brought by technological progress, but also face a crisis of personal privacy data due to various reasons. With the intensification of data flow in Int’l Trade transactions and the frequent occurrence of data privacy security incidents, countries are actively exploring relevant protection measures. Therefore, studying the application of Internet of Things blockchain in Int’l Trade privacy data has important practical significance.
Blockchain can facilitate transactions in Int’l Trade, and its application in Int’l Trade is very extensive. Many scholars have conducted analysis and research on the relationship between blockchain and Int’l Trade. Konstantina Siountri and others focused on applying new technologies in the construction industry, such as BIM, the Internet of Things, and blockchain. They also took architecture (museums) as an example to study their interconnection and interoperability on the proposed system architecture. In this architecture, efficient security, management, and monitoring were considered key factors for the smooth operation of the host organization [1]. Modern medical systems process a large amount of clinical data collected using Internet of Things (IoT) devices. In addition, the collected data needs to be classified for immediate retrieval and processing. Eirini Zoumi and other scholars focused on collecting big data from three types of sensors, namely body sensors, indoor and outdoor sensors. The collected data is stored in the cloud infrastructure. A classification algorithm has been proposed. For each type of sensor, the algorithm categorizes the received data to effectively organize them into virtual machine (VM) clusters [2]. Vasileios Tsoulchas and others proposed a model to monitor the health status of patients with melitus diabetes. The incidence rate of this disease is high, mainly in the elderly, but also in young people. Specifically, he described a study on the existing medically approved continuous measurement technology for diabetes. Subsequently, he described a model used to monitor patient blood glucose levels. Whenever a patient’s blood sugar level is low or high, the model triggers an alert to the cloud infrastructure for remote healthcare workers to provide immediate treatment to the patient. In addition, to ensure immediate response from remote healthcare workers, the proposed model is deployed on a 5G wireless network architecture [3]. The purpose of Belu Mihaela Gabriela was to showcase the potential advantages of blockchain technology in the Int’l Trade field and emphasize the potential benefits of this technology [4]. Chang Shuchih Ernest aimed to explore the applicability of blockchain technology in the Int’l Trade process from the perspective of letter of credit payment. Through comparative analysis and feasibility studies, he identified and validated the prospects of the proposed blockchain based Int’l Trade process model in promoting processes and improving overall trade performance [5]. Hooper Amanda analyzed the applications of blockchain in fields such as international finance, banking and insurance, supply chain management and logistics, marketing, and advertising [6]. Sinha Deepankar proposed an Int’l Trade smart contract framework based on blockchain technology, establishing international standards for smart contracts based on blockchain technology [7]. Md Nur Alam Siddik studied the connection between blockchain and Int’l Trade. The research findings are of great significance for policy makers to develop policies to promote the use of blockchain applications as facilitators of Int’l Trade [8]. Macedo Leonardo introduced blockchain, commented on blockchain platforms such as Ethereum, and provided examples of private sector initiatives. He shared his ideas on blockchain applications and discussed regulatory issues [9]. Darcy W E Allen outlined the potential economic consequences and a series of policy challenges faced by the blockchain supply chain, and proposed the establishment of a high-level policy forum in the Asia Pacific region to coordinate issues such as open standards and regulatory compatibility [10]. VILKOV A introduced the applicability of blockchain in the timber trade between Russia and China based on a situation analysis of internal and external competitive environments and conditions. Decentralization based on smart contracts can ensure transparency in the wood supply chain by encrypting each log [11]. The above studies have all discussed the role of blockchain in Int’l Trade, but there are still issues such as inadequate privacy data protection in transaction data privacy protection.
To study the specific effects of privacy data management under the Internet of Things blockchain, this article analyzed the encryption effect of privacy data through additive aggregation functions. In the experimental section, the proportion of storage, backup, audit, and abnormal situations of privacy data under privacy data protection policies were analyzed. This article investigated the proportion of security threats faced by data under different transactions in Int’l Trade. It was found that transaction methods had a significant impact on data security threats, and the reliability, systematicness, and sensitivity of private data had also been significantly improved.
Threats to data security in Int’l Trade
According to the different security threats that exist in transactions in Int’l Trade, they can be mainly divided into user privacy security threats, data leakage, and security threats under different transaction modes.
User privacy security threats
With the development of network technology, Int’l Trade trading activities would be subject to data attacks and spam data streams from the network, posing a serious threat to users’ personal privacy. Unsensitized data sharing and openness can lead to the leakage of user privacy information. Although desensitized data has already been made public, when a large amount of non sensitive data is gathered together, it is still possible to generate sensitive data, and there is still a risk of loss, leakage, and destruction of user privacy data.
Data leakage security threats
At present, Int’l Trade lacks regulations related to data transactions, making it difficult to effectively guarantee the security of enterprise privacy data. Trust and security of data in the Int’l Trade environment are very important issues to consider, especially when the collected data is fraudulent or dishonest [12]. Open data exchange platforms pose a risk of data loss due to unauthorized data access, user damage or theft, as well as network attacks such as system vulnerabilities, network viruses, and Trojan horses. Moreover, malicious and erroneous behavior by administrators and operators may lead to data loss and damage.
Security threats under different transaction modes
In the online data processing process, the service platform does not store the data, but only performs real-time desensitization, cleaning, auditing, and security testing on the data. As a service platform for transaction channels, it provides data for various types of users, thereby achieving management of the transaction process. Blockchain has the potential to change Int’l Trade data [13]. In transactions, insecure user interfaces, unreasonable access controls, and unencrypted data copies can all cause security risks such as data leakage, illegal access, and transmission. In the process of offline data processing, data security is an important issue [14]. Managed data needs to be approved by the relevant data owner and must be copied and registered.
Based on the security threats existing in private data, this article randomly selected the proportion of security threats faced by data under six types of transactions in Int’l Trade, in order to determine the frequently occurring data security threats in Int’l Trade. On this basis, corresponding privacy data adjustments were made. The privacy data security threat problem is divided into three levels, with negligible threats below 0.6, mild threats ranging from 0.6 to 0.7, moderate threats ranging from 0.7 to 0.8, and severe threats ranging from 0.8 to 0.9.
Proportion of security threats faced by data in international trade transactions
Proportion of security threats faced by data in international trade transactions
According to the data in Table 1, among the six types of transactions surveyed, the most common security threat faced was the transaction mode security threat, and the least common was the data leakage threat. This indicated that the transaction mode seriously endangers the security of private data, and the transaction mode also has a certain impact on users’ personal privacy and data storage. Among these six types of transactions, Transaction 5 had the lowest overall security threat, with a level of mild threat; Transaction 1 had the highest overall security threat, with a level of severe threat. In Int’l Trade, user privacy, data leakage, and other transaction modes can all have a certain impact on privacy data, so the privacy data in its trade also needs to be encrypted using blockchain and other technologies. Therefore, it is necessary to create a key for the user, which needs to be updated in real-time over time to ensure the security performance of private data.
Blockchain is of great significance for privacy protection of Int’l Trade data, so it can be combined with additive aggregation functions to analyze the effectiveness of blockchain in data privacy protection of Int’l Trade. The data fusion function for calculating privacy data based on additive aggregation function is:
Among them,
Among them,
Among them,
Among them,
The capture and fusion of privacy data are related to the encryption effect of Int’l Trade privacy data. Therefore, this article investigated the changes in transaction privacy data of a certain Int’l Trade enterprise over a period of 10 days. The specific survey results are shown in Fig. 1.
Changes in transaction privacy data of the international trading company.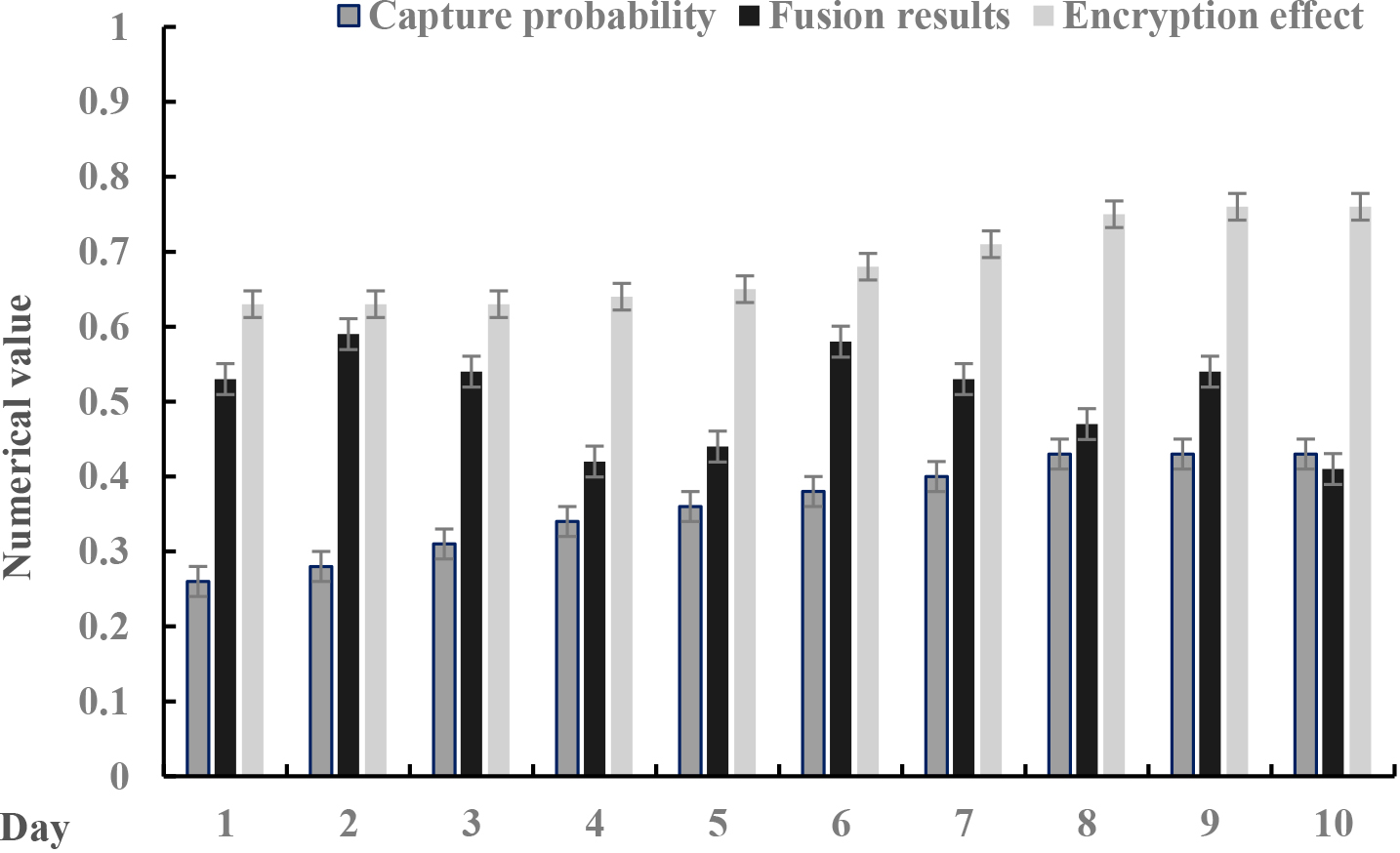
According to the data described in Fig. 1, the capture probability of private data gradually increased over time, indicating that the capture speed of private data under the blockchain was faster, which could prevent the invasion or leakage of private data. In this survey, the encryption effect of private data was also continuously increasing over time, which confirmed that blockchain can use its own immutability to improve the encryption effect of private data in the transmission and storage of private data, thereby enhancing the security of private data. The trend of the fusion effect of private data was not obvious, and the overall stability was between 0.41 and 0.59, indicating that the fusion effect of private data and blockchain may fluctuate due to incompatibility.
Main judgment criteria for Int’l Trade data flow
With the continuous development of communication equipment and other infrastructure, as well as the development of network communication technology, the level of collaboration between various units continues to improve. The value of information can be identified, classified, utilized, and preserved, and the value of information resources can be better utilized. The restrictions on the flow of Int’l Trade data mainly involve personal data [15]. Private data refers to various types of data that can be identified and related to individuals, and these data have a high degree of correlation with individuals. Once data leakage occurs, it would bring some problems to the data subject in terms of personal privacy security, economic security, and other aspects. During the process of Int’l Trade data exchange, the data would be circulated between relevant institutions. In Int’l Trade and data exchange, the main focus is on data flow in regulatory agencies. For example, in Int’l Trade, consumers’ receipt addresses, purchase invoices, retrieval records, financial information, and other information generated during the transaction process are recorded and stored after the Int’l Trade process begins. Like Int’l Trade, accessing social network services and other activities also stores personal data in institutions.
Due to excessive personal data, regulations are relatively strict. Social media providers must establish physical facilities or network centers to transmit relevant personal data to their parent company or country of registration, which may include confidential information. When users access social media, data transmission must occur between the user terminal and the service provider. Independent third-party institutions typically sign contracts with users or service providers to protect data and ensure the security of Int’l Trade’s privacy data.
Classification management of Int’l Trade data
For the classification management of Int’l Trade data, Int’l Trade data can be divided into three categories. The first is to clearly define the cross-border flow of data. Usually, this type of data belongs to significant data, and countries may formulate various regulations for the purpose of maintaining national security, safeguarding their own interests, or other considerations. With the rapid development of information technology and the frequent occurrence of leakage incidents, countries have begun to attach importance to the localized collection, processing, access, and storage of data [16, 17, 18]. Secondly, the flow data of Int’l Trade is limited. There would be no absolute restrictions on the flow of trade data, production technology data, etc. However, in many countries or regions, the flow of these data is subject to orderly, restricted, and limited restrictions. The third is to grant legal cross-border circulation rights to general, non private, and private information, but it does not mean allowing the free circulation of this information. There must be corresponding regulations for the circulation of this information.
Changes in Int’l Trade privacy data flow
Changes in sensitivity, reliability, and systematicness of privacy data.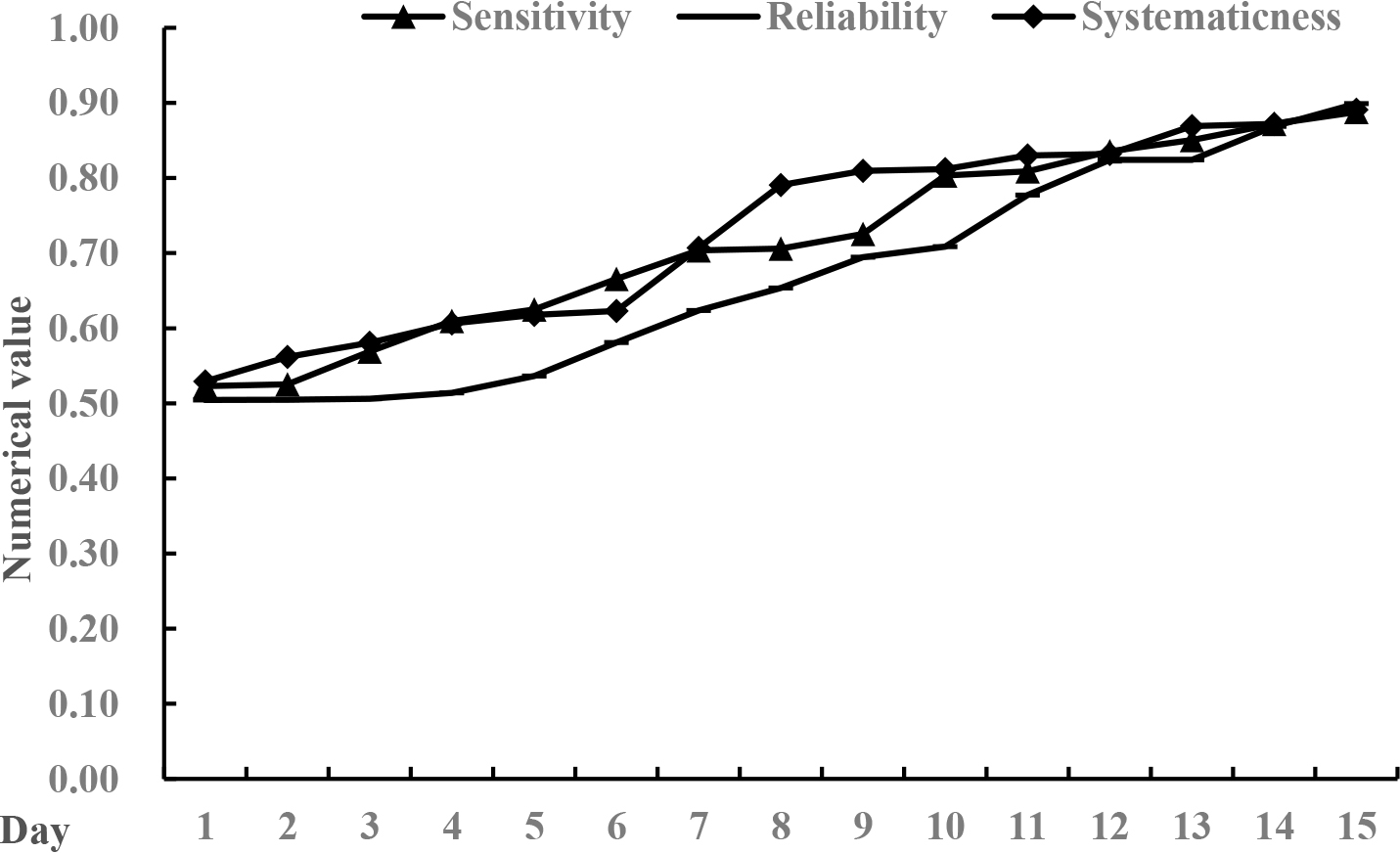
With the development of information technology and the opening of data transmission channels, a large amount of data and information resources cross national borders. The characteristics of data protection in data streams are different from those in the past, and the significance and breadth of privacy in Int’l Trade data streams have also been expanded to varying degrees. There are three main types of data flow changes related to privacy data protection.
The first is high sensitivity. The main source of information for data flow in Int’l Trade is mobile internet users. Although the privacy information generated by individuals is insignificant for the entire society, they do not want their personal information to be arbitrarily collected. In addition, the high sensitivity to personal privacy stems not only from the user’s personal wishes, but also from the convenience of obtaining information in the information society and the low threshold for obtaining information.
The second is high reliability. In the Int’l Trade data stream, the information from the user himself is the true record and reflection of the user’s behavior, which is often difficult to forge. At the same time, it is important to ensure the authenticity of personal life, the efficiency of data exchange, and the interoperability of the Int’l Trade data stream [19].
The third is strong systematicness. Throughout the entire Int’l Trade chain, data streams, data processing, or processes are interrelated and have strong logical connections. Due to the absence of personal data in the data, personal data within the region may be dispersed in regional data centers. Data processing must be carried out between regions and centers, so the processed data is very systematic, fast, and easy to process. In addition, there are similarities in the protection of personal privacy data, and data processing focuses on handling these similarities.
There are three main changes in the flow of privacy data in Int’l Trade, all of which can reflect the management effectiveness of privacy data. Therefore, this article investigated the changes in privacy data of an Int’l Trade enterprise over transaction time for a total of 15 days. The standard values for sensitivity, reliability, and systematicness were all 0.60, as shown in Fig. 2.
According to the data described in Fig. 2, the sensitivity, reliability, and systematicness of privacy data in the flow process of Int’l Trade were constantly increasing. In the analysis of the sensitivity of private data, the private data of the enterprise were lower than the standard value in the first three days of the survey, and gradually increased from the the fourth day. The average sensitivity in the whole process was 0.11 higher than the standard value of the sensitivity of private data. In the reliability analysis of privacy data, the company’s privacy data began to exceed the standard value on the seventh day. The improvement in reliability also indicated that the protection of privacy data in Int’l Trade was gradually reliable, and it was also in an encrypted state during the flow process, gradually reducing the risk of leakage. In terms of systematic privacy data, the average systematic value of the company’s privacy data was 0.73, which was 0.13 higher than the standard value.
Int’l Trade privacy data protection model under the internet of things
In the blockchain system of the Internet of Things, information abstracts are stored in the blockchain. It can store records of data usage and changes, and separate data storage from rights, effectively preventing arbitrary use of user data in data storage. Compared to centralized storage, using distributed storage in Int’l Trade for storing authenticated information greatly reduces the risk of forgery or theft in data protection. In terms of privacy information, the multiple private keys and composite permissions of blockchain can be used to save it. Individuals can choose their own data usage permissions and use them with the user’s permission to achieve privacy protection for Int’l Trade transaction data. Blockchain technology can be applied to study the privacy protection of Int’l Trade data. The distribution, verification, and response of encryption keys would greatly affect the execution efficiency of the entire protocol. Therefore, in model analysis, this paper divided the system into four parts: blockchain layer, cloud storage layer, data layer and user layer. The specific model is shown in Fig. 3.
Model interface for international trade privacy data protection under the internet of things.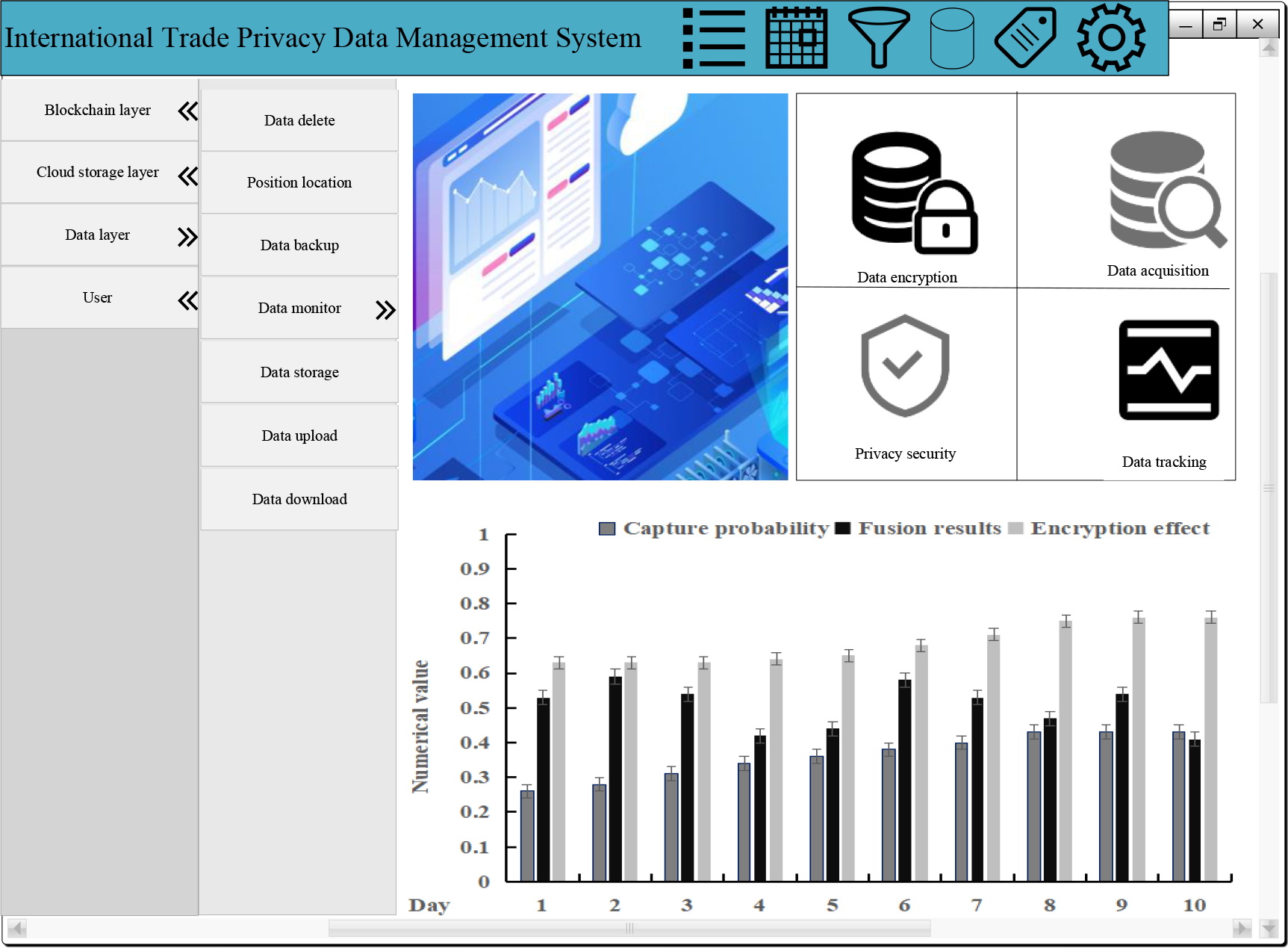
The blockchain layer is a powerful support for distributed cloud computing. The cloud storage server can write the Int’l Trade privacy data content to the blockchain layer, and can read the relevant content from the blockchain layer. When the content accessed by the cloud storage layer is blocklinked, it cannot be changed or deleted. Its permanent storage record attribute is determined by the blockchain itself. Users of the Int’l Trade system can use an encrypted algorithm to write private transaction data into the blockchain. For example, certain transaction data can be encrypted using a cryptographic system and decrypted with the user’s permission. To ensure user privacy, data needs to be encrypted and stored in the cloud.
Data layer and user layer
The data layer represents the user’s demand for information, which can be shared and guaranteed. To ensure the data privacy of Int’l Trade trading users, the system encrypts the data through a password system and uploads it to a cloud server. This method uses a threshold homomorphic cryptosystem, allowing users to decrypt the obtained information according to their own requirements and actual situation. Due to the fact that central users have the same type of data, data sharing can be adopted to enable data exchange between node users. By using blockchain technology, users can effectively avoid data tampering, thereby achieving privacy protection for Int’l Trade data and tracking of executed transactions.
Collection of Int’l Trade privacy data
In Int’l Trade transactions, a data collector is used to collect account information in Int’l Trade. This project divides the collected data into two types: account balance information stored in the blockchain public ledger and account transaction information stored in the network. The data collector collects account information stored in the public account through centralized collection. Through the open nature of the ledger, data transmission to computers has been achieved, and corresponding databases have been established based on this, achieving the comparison of cross-border transaction data. In Int’l Trade transactions, the data collection machine mainly uses position recognition method for data collection. When a transaction information flow appears on a blockchain, the collector would track its running route and determine the content of the information in the data flow. On this basis, by locating the starting point, the account information of both parties to the transaction is confirmed, and the identified transaction data is sent to the processor.
Homomorphic encryption of Int’l Trade privacy data
On this basis, using regulatory agencies to generate a shared key can effectively solve the privacy and security issues of Int’l Trade data. During the process of matching data by the processor, if the result of the data matching is empty, it would be considered an illegal transaction. The processor can use the private key of Int’l Trade transaction data held by regulatory authorities to decrypt the data and make the transaction information public, ensuring that the transaction can proceed normally. This article encrypted the privacy information in Int’l Trade to store hash values on the blockchain, effectively protecting the privacy information in Int’l Trade transactions and ensuring its security. In order to obtain data with privacy protection, users must first obtain a key. By setting hash values, users can be effectively prevented from modifying their privacy information, thereby achieving protection of their privacy information. After encrypting the data, multiple users must share the password in order to decrypt the password. In this case, there must be a key to distribute and at least one user must agree, so that the encrypted ciphertext can be obtained and the decryption of the data can be completed.
Storage of Int’l Trade privacy data
In international transactions, the protection of privacy data involves inputting the original privacy data document in the form of a hash algorithm. After calculating the hash value and storing it, the integrity of the document is checked. On this basis, a new cryptosystem was proposed and applied to the cryptosystem of symmetric encryption algorithms. When encrypting the plaintext of private data files, a key and symmetric cryptographic algorithm are used to generate the corresponding ciphertext. After inputting the obtained ciphertext into the cryptosystem, the public key of the cryptosystem is obtained. In asymmetric cryptosystems, a new cryptosystem is formed by combining cryptosystems with user passwords. In order to obtain the private key of the asymmetric algorithm, users need to first obtain a user password, and then obtain the value of the private key and the plaintext of the data.
Experimental study on the storage, collection, and tracking effects of Int’l Trade privacy data
The Int’l Trade privacy data management system implements the collection, upload, encryption, decryption, and storage of privacy data. Therefore, the analysis of the collection, tracking, and storage effects of privacy data can also reflect the performance of the Int’l Trade privacy data management system. This article investigated the data storage, data collection, and data tracking effects of privacy data from eight Int’l Trade enterprises in the Int’l Trade privacy data management system. The specific survey results are shown in Fig. 4.
Analysis of data storage, data acquisition, and data tracking effects in the international trade privacy data management system.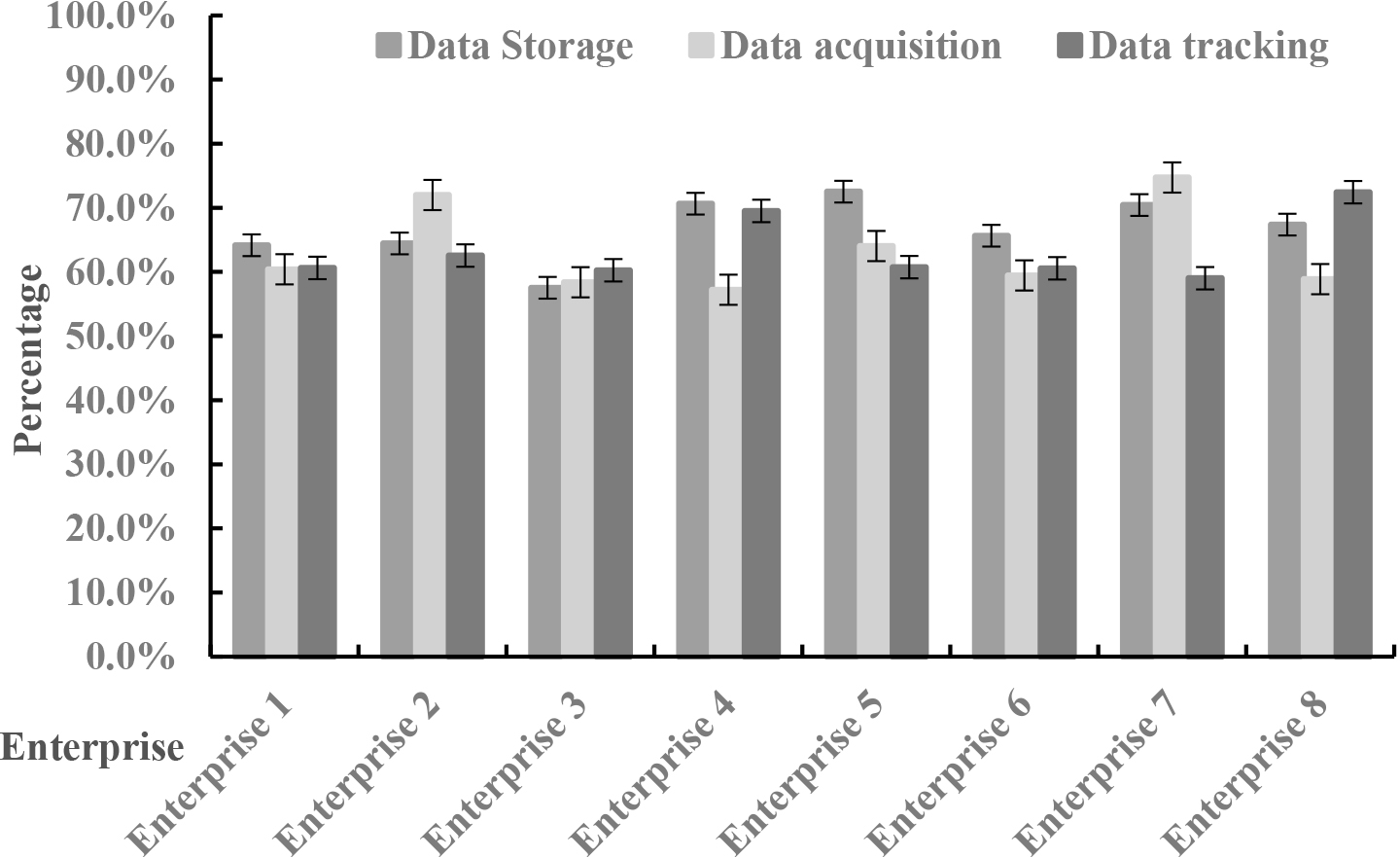
According to the data in Fig. 4, among the data storage effects, Enterprise 3 had the worst storage effect, while Enterprise 5 had the best storage effect; in data collection, Enterprise 7 had the best collection effect; in data tracking, the tracking effect of Enterprise 8 was the best. The reason for this situation may be that Enterprise 5 had a large number of databases and could also be uploaded to the cloud, improving data storage efficiency; Enterprise 8 had many cloud servers for private data, and could use the Internet of Things to achieve real-time monitoring of private data in Int’l Trade, in order to detect the real-time flow of data, thereby reducing the issue of privacy data leakage.
Improvement of regulatory standards for Int’l Trade ttransactions
In international trade, in order to regulate the legal compliance of secure transactions and privacy protection in international trade, regulations must be formulated and the formulation of international trade transaction security business standards or guidelines must be accelerated to ensure effective law enforcement. It is also necessary to establish an international trade regulatory agency responsible for data protection and strengthen administrative supervision of data protection and data security. In addition, it is necessary to strengthen criminal prosecution for data leakage to prevent data theft and loss [20].
Transaction privacy data security and protection
As for the threats to data and privacy, the Int’l Trade data management platform must first set up appropriate user identification for both parties involved in data transactions in order to identify users, and establish necessary authentication mechanisms for all users. Individuals performing identity verification during user transactions and managing transactions must prevent identity impersonation and ensure the authenticity and validity of their identities [21]. When conducting data transactions, both data supply and demand parties should also adopt data and personal information security protection technologies. For example, data encryption technology can be used to encrypt data in the storage and transmission stages of big data, reducing the probability of information leakage from a technical level. This makes it difficult for data thieves to obtain critical information even if the data is leaked. On this basis, the anonymity protection technology released by the Internet of Things can effectively protect users’ privacy. In addition, in the process of international transactions, real-time recording of data transactions is required, and a transaction log of the data is established to facilitate data query and backup.
Int’l Trade privacy data management system security
It is necessary to strengthen the security function of the privacy data protection management system, and integrate the Internet of Things and blockchain technology to ensure the network security, system security, host security and application security of the data protection management system. In addition, it is also necessary to update various security plans in a timely manner. At the same time, data mining technology can be used to analyze network attacks, identify abnormal behaviors, and establish a comprehensive data security warning system, thus effectively addressing data security and retrospective threats. The security enhancement of the data protection management system should also ensure the security control and audit of data operations, as well as the control and tracking of processes and personnel.
Privacy data evaluation under Int’l Trade privacy data security protection policy
The audit, exception, query, and backup of privacy data under the privacy data security protection policy of Int’l Trade can reflect the actual application effect of the protection policy. Therefore, this article investigated the actual situation of privacy data auditing, exceptions, queries, and backups of five enterprises under the Int’l Trade privacy data security protection policy. The standard values for data review, query, and backup were all 0.60, and the standard values for data anomalies were 0.30. The specific investigation results are shown in Table 2.
Analysis of data status under international trade privacy data security protection strategies
Analysis of data status under international trade privacy data security protection strategies
According to the data in Table 2, it can be seen that among the five surveyed enterprises, data review and data backup were all above the standard value, while data query only showed that enterprises 2, 3, 4, and 5 were above the standard value. This indicated a significant decrease in the abnormal rate of private data under privacy protection policies, and a significant improvement in the audit and query backup of private data. In addition, under the privacy data protection strategy, the tracking and control of privacy data were also more precise.
Data leakage is a common problem in different industries and fields, and data protection is becoming increasingly important. With the development of blockchain technology, many enterprises have begun to adopt blockchain to protect their internal privacy data. The application of blockchain technology not only needs to protect the privacy and security of Int’l Trade data, but also to ensure the legality of its private data. It is also necessary to strike a balance between privacy protection and regulatory requirements, and to facilitate users while severely punishing some illegal transactions. On this basis, homomorphic encryption is adopted to enhance the security of heterogeneous data in Int’l Trade, thus effectively protecting the privacy in Int’l Trade. On this basis, this project can also simulate and analyze the proposed privacy protection method, and verify its practicality through different attack modes.
