Abstract
Due to the abundance of the Internet of Things (IoT), smart devices are widely utilized which helps to manage human surroundings and senses inside and outside environments. The huge amount of data generated from the IoT device attracts cyber-criminals in order to gain information from the significant relationship between people and smart devices. Cyber-attacks on IoT pose a severe challenge for forensic experts. Researchers have invented many techniques to solve IoT forensic challenges and to have an in-depth knowledge of all the facts internal as-well-as external architecture of IoT needs to be understood. In this paper, an attempt has been made to understand the relationship between security and forensics incorporating its strengths and weaknesses, which has not been explored till date to the best of our knowledge. An attempt has also been made to classify literature into three categories: physical level, network level, and cloud level. These include evidence sources, areas of IoT forensics, potential forensic information, evidence extraction techniques, investigation procedures, and legal issues. Also, some prominent IoT forensic use cases have been recited along with providing the key requirements for forensic investigation. Finally, possible research problems in IoT forensic have been identified.
Introduction
In today’s digital world, Internet of things (IoT) is a new environment evolving physical objects and a network consisting of embedded communication technology and associated sensors. IoT helps to make contact with physical objects and provides control of sensors from distinct locations to the users. This access generates a huge amount of data in terms of timestamps, voice messages, text messages, control signals etc. The rapidly growing involvement of IoT in human surroundings stores data including the login credentials, location, and personal information which attracts cyber-criminals to attack these small devices with limited security to breakthrough and extract useful information which can ultimately be misused. IoT forensics plays a very important role in the aforementioned scenario, as it enables us to identify cyber criminals and fix the damage due to cyber-attacks. Forensic on IoT devices become imperative by revealing its heterogeneous architecture and technology because it consists of different networks and frameworks. Smart electronic gadgets like mobile phones, computers, tablets, sensors, medical devices, television, wearable watches, and smart home applications are good examples of IoT applications.
In contemporary times, each individual is dependent upon, and limited to the utilization of internet connected devices. The global IoT market is expected to reach a value of USD 1,386.06 billion by 2026 from USD 761.4 billion in 2020 which is compound annual growth (CAGR) of 10.53% during the period 2021–2026 [44]. It can be easily inferred that in future, criminal activity on IoT devices may increase proportionally to the growth rate. IoT is a well-known paradigm that is closely handed out by people either directly or indirectly with the ever-growing use of the Internet and technology.
IoT devices are widely integrated with i) wearable technologies like health care bands, smart watches, and smart glasses, ii) home automation like smart lights, smart switches, smart plugs, sensors for temperature, Wi-Fi enabled air conditioners, iii) smart office equipment like Wi-Fi printers, smart routers, and Wi-Fi cameras, iv) smart automated vehicles like smart cars and drones, v) Industrial IoT, vi) Agriculture IoT, and vii) Environmental IoT, e-health, etc. Interconnected devices share a massive amount of data through a wired or wireless network. IoT associated with billions of gadgets can produce a tremendous volume and assortment of information that opens doors for digital criminals or offenders, who can access the user data and use it for their own benefits. To comprehend all such data that is generated from IoT devices, it has become a necessity to forensically examine all devices, so that it can be determined what sort of data these devices have, and if it relies on another device, how it is connected, as well as how it operates. The investigator also needs to know whether these devices hold any information about connected devices. If the investigator can access all the information related to IoT device, then in case of any incident or breach related to IoT, that extracted information can help law enforcement agencies to apprehend the criminal. IoT forensics is an important research area that finds the security breaches of the smart device at various levels, i.e., cloud, network, and physical level. Managing these gadgets can prompt various difficulties from security and forensics points of view.
IoT forensics is a growing area for all researchers in the field of security and IoT. Moreover, it is crucial to understand IoT forensics in-depth to help track down cybercriminals using digital evidence. As IoT devices are increasing exponentially, and so are the threats, therefore the area of cyber security is crucial not only to make people aware of threats, but also for identifying and fixing the cyber criminals. In this study, an attempt has been made to review all the technologies and techniques which are relevant to IoT forensics and its role in cybercrime investigation.
(a) Motivation behind this study IoT forensics is an emerging topic among researchers. The exponential growth has given rise to a plethora of new applications and the security and forensic issues have also increased manifold. Billions of devices which communicate with poor security built-ins are linked, making them an easy target for attackers. Moreover, the IoT system consists of varied and heterogeneous components, making it difficult to use conventional digital forensic investigation techniques [108]. The large volume of data generated by IoT devices also motivates our research. In the past, many researchers have described various forensic investigation models. However, automated data extraction techniques are required for huge data investigations. Vast volumes of data generated by IoT devices are often categorized into a few smartphone applications. For example, most smart home gadgets are compatible with Google Home, Alexa, and wearable healthcare devices, enabling them to communicate data with smartphone applications. Smart homes are gaining popularity every day due to their ability to provide smooth and desirable automation services. User activity recognition plays a vital role in the smart home system, allowing it to precisely deliver the necessary services and possesses numerous fascinating features and advantages [9].
Similarly, a single application Kasa can control HVAC, indoor/outdoor security cameras, smoke detectors, and other smart home equipment [40]. One can understand that IoT devices are the gold mine to collect digital evidence because of wireless communication. Servida and Casey [123] highlighted how digital footprints saved in smartphone apps are utilized to access and manipulate IoT devices including cached picture thumbnails and parts of camera streams, cached events triggered by sensors, and entire event logs stored in the application database. These traces alert the investigators about what happened, when it happened, and whose user account delivered instructions to a smart device. Furthermore, integrating AI with IoT forensics is essential to successfully collect required evidence from the vast volume of data produced by IoT devices. Few studies have addressed artificial intelligence (AI) in forensics. For example, Karie et al. [67] have developed a generic framework for integrating deep learning, (which is a subset of AI) into forensics. They have used deep learning to address problems by simulating human decision-making with neural networks. Solutions include avoiding bias in forensic investigations and disputing the admissibility of evidence in the court. Wooyeon et al. [63] demonstrated five different digital forensic analysis methodologies for four distinct AI speaker models and developed a forensic application that collects and records user command history. This work is also motivated by Baggili and Behzadan [15], who suggested the need to establish AI forensics as a new discipline within the field of AI security and facilitated a conversation about the fundamental issues.
More recently, Atlam et al. [13], Hemdan et al. [62] and Chin et al. [32] enhanced the survey approach by considering the state of the art, graphical representation, and a more significant number of factors. Nevertheless, the above-mentioned papers does not assess all parameters at the same time, as shown in Table 1. As a result, there is a scarcity of study and scrutiny about the forensics of IoT. Therefore, a comprehensive study on evidence extraction and investigation challenges for IoT forensics is eagerly needed to align with the current and developing research in the field of digital forensics. There is a need for more in-depth physical research of IoT devices, such as chip-off procedures typically used in mobile devices, also used for IoT devices. For example, as all smart devices use wireless modules for communication, hence through forensics of the wireless module, we may extract some network-related artifacts. Hence, more research is required on the most prevalent home security systems, smart assistants, smart firewalls, and other IoT devices.
(b) Contributions of this study Although forensics on IoT devices have a significant impact on digital investigation as we know, essential approaches and backgrounds of the area are yet to be comprehensively and systematically reviewed. Accordingly, this research aims to evaluate and analyze digital forensic techniques for IoT devices to explore more digital evidence. Concisely, the current study might help pave a further way for the area to move forward by supporting young researchers and practitioners in applying existing IoT forensics techniques or approaches to devise new ones.
The year-wise comparison, forensics investigation model, evidence acquisition technique, forensic issues, legal challenges, and AI based techniques were included in Table 1. The several key topics that can be explored in the future, along with some recommendations for emerging new trends in the IoT forensic area has been discussed. Figure 1 is created to succinctly describe the structure of this study. The primary focus of this study is summarized in the following points:
IoT forensic and investigative techniques are analyzed with a focus on three-level forensics of IoT devices. Digital evidence classification and forensic investigation process in IoT with legal issues are discussed.
Potential forensic evidence found in different IoT devices are highlighted and various tools used in digital forensics are presented and compared.
A state-of-the-art of IoT forensics techniques, issues, and solutions are addressed that will help in drawing a roadmap for potential future research.
Differentiating between present studies and existing studies
Differentiating between present studies and existing studies
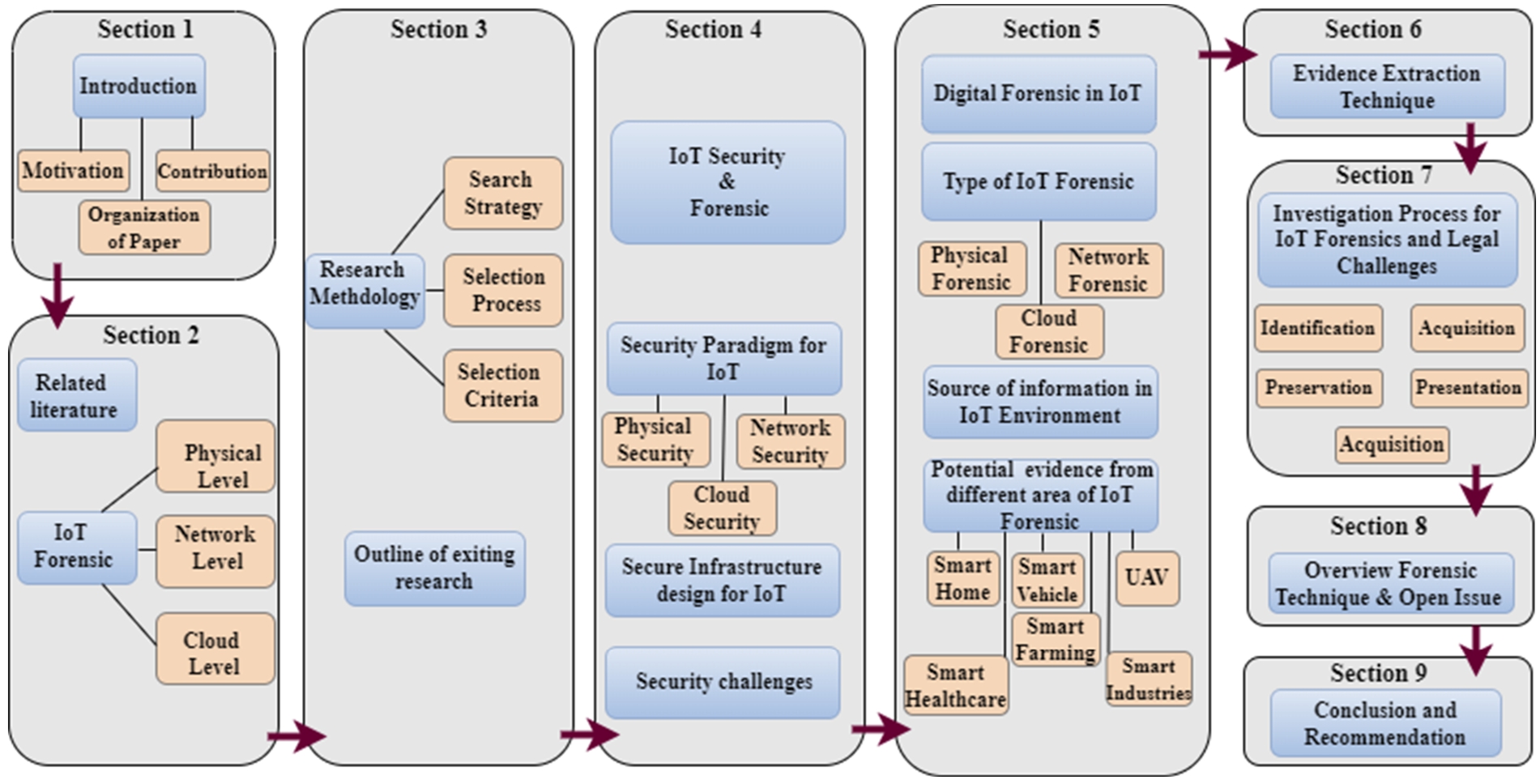
The structure of the study.
(c) Organization of the paper The paper is organized as follows: Section 1 gives the introduction Section 2 presents the work related to IoT forensics at three-levels. Section 3 draws the research methodology and literature selection procedure. Section 4 defines the IoT security and forensics, security paradigms for IoT with three-layer structure, secure infrastructure design, and security challenges. Section 5 Digital forensics in IoT three-level forensic, along with detailing the sources of information in IoT environment, different areas of IoT forensics and highlights the potential forensic artifacts in IoT devices. Section 6 introduces the evidence extraction techniques. Section 7 presents the Investigation process for IoT forensics and its challenges. Section 8 gives an overview of forensic techniques and solutions for open challenges. Section 9 concludes the paper.
Securing IoT devices has always been a key objective for the researchers. The security and forensics of IoT devices are extremely difficult due to its vulnerable environment. Further, IoT structure has three different levels, i.e., physical level, network level, and cloud level. The detailed description of each level is given below:
Zawoad and Hasan [150] recommended a model called Forensics-aware IoT model (FAIoT) that is used to physically access the computing device such as hard disk, network router, etc. In this, an investigator collects data from the local memory of the IoT devices. When a crucial piece of evidence needs to be collected from the IoT device, it involves device-level forensics at the physical level. A white paper by the smart card alliance suggested that embedded hardware security for IoT applications is used to protect the “identity” of each device from unauthorized access [39]. Netherlands Forensic Institute (NFI) Memory Toolkit II (MTK II) is an overall forensic solution that empowers examiners to read memory chips and possibly remove client information, for example, instant messages, telephone numbers, images, and program history from a wide assortment of electronic gadgets. MTK II is a mix of hardware and programming. In some circumstances, data that has been “erased” or devices that have been damaged can potentially be recovered using NFI Memory Toolkit. The equipment makes a physical association, creates signals, and supplies capacity to a memory chip. At the same time, the product runs the important order sets of commands to get to the information in the different sorts of memory chips [97]. There is also a need for an autonomous digital forensic solution for the home IoT. A speculative IoT crime situation was completed by a presume who utilized different IoT ware to perpetrate violations.
In the light of these situations, the researcher additionally elucidated the source of digital evidence at a physical level. To supplement understanding, another significant examination point is the internal unstable (volatile) memory of the Smart TV, which contains essential data, for example, passwords, keep going actions on the smart TV [19]. However, almost all IoT devices have a common point like a log-on and log-off timestamp that carries information about the device activation state, which is related to the IoT forensics due to its different architecture and operating system. This information is important evidence for digital investigation [91].
The data synchronization between devices has both advantage and challenges, i.e., the data cannot be located if examined device synced the data with another device is an advantage, however, there is a possibility that the reviewed device has data that may be synced with another device is a challenge [18]. Shin et al. [125] described the existing method for data collection that consists of different types of information extracted and alternative tactics of data acquisition.
We can consider a research gap that limits maximum input and availability concerns of machine to machine communication, including replication of network, addressing space issues, and safety compliance issues in IoT device [145]. A searching technique is used by Mascarnes et al. [90] to check certain keywords from a large set of text databases. The digital evidence acquisition model can solve various issues of evidence obtained in the context of IoT, as brought out by Harbawi and Varol [48]. The privacy aware IoT forensics model (FAIoT) discussed by Nieto et al. [98] indicates the log of the router when some external device wants to induce malware inside the network. Due to this, Ma et al. [89] proposed the first scalable architecture for balancing accountability and privacy in large-scale content-based networks (APCN). In particular, an innovative method for identifying content is proposed to effectively distinguish the content issued by different senders and from different flows, enabling the accountability of content based on any of its packets.
This is done through identification, collection, preservation, examination, interpretation and reporting of digital evidence. In a digital forensic investigation process, arising innovation in the IoT era has consistently introduced a new challenge. The author [135] depicts that the principles by which evidence is judged in digital forensics examinations may be modified as digital evidence stored in a distributed cloud computing environment. The extraction and protection of crucial information from electronic gadgets and services running in the IoT platform will introduce new challenges. Exclusive information contains proprietary data formats, protocols, and physical interfaces convolute the evidence extraction cycle [93].
To give an overview of cloud forensics, the basic rule for forensics is to investigate the data stored at the cloud level and collect meaningful artefacts over the cloud. However, many traditional and basic procedures of digital forensic investigation don’t work in the cloud environment, so crimes committed on the cloud are very hard to investigate [116,118]. Ruan et al. [117] argue that “the application of digital forensic science in cloud environments is a subset of network forensics because it is a mix of traditional computer forensics and small-scale digital device forensics. Cloud forensics is described in three main aspects: legal, organizational, and technical. Legal aspects are treated with different jurisdictional situations. The Organizational aspects deal between cloud actor and investigator. Technical aspect involves forensic tools, techniques, and mechanisms [8]. It is important for digital forensic practitioners to have an up-to-date knowledge of relevant data artifacts that could be forensically recovered from the cloud product under investigation. The types and locations of the artifacts relating to the installation and uninstallation of CloudMe [136] client application, logging in and out, and file synchronization events from the computer desktop and mobile clients are described by Teing et al. [136] But, another issue at the cloud level is “time” which is difficult to analyze because activity during the investigation can be complicated due to the different file systems since the client and cloud storage server may reside in different time zones [71]. The cloud may store data for a limited period and delete the data after this period expires. The deleted data may be very important from investigation perspective [64]. Table 2 shows the segregation of literature in three categories physical, network, and cloud level, as well as the corresponding forensic techniques are also presented.
Tabulation of literature classification forensic techniques
Tabulation of literature classification forensic techniques
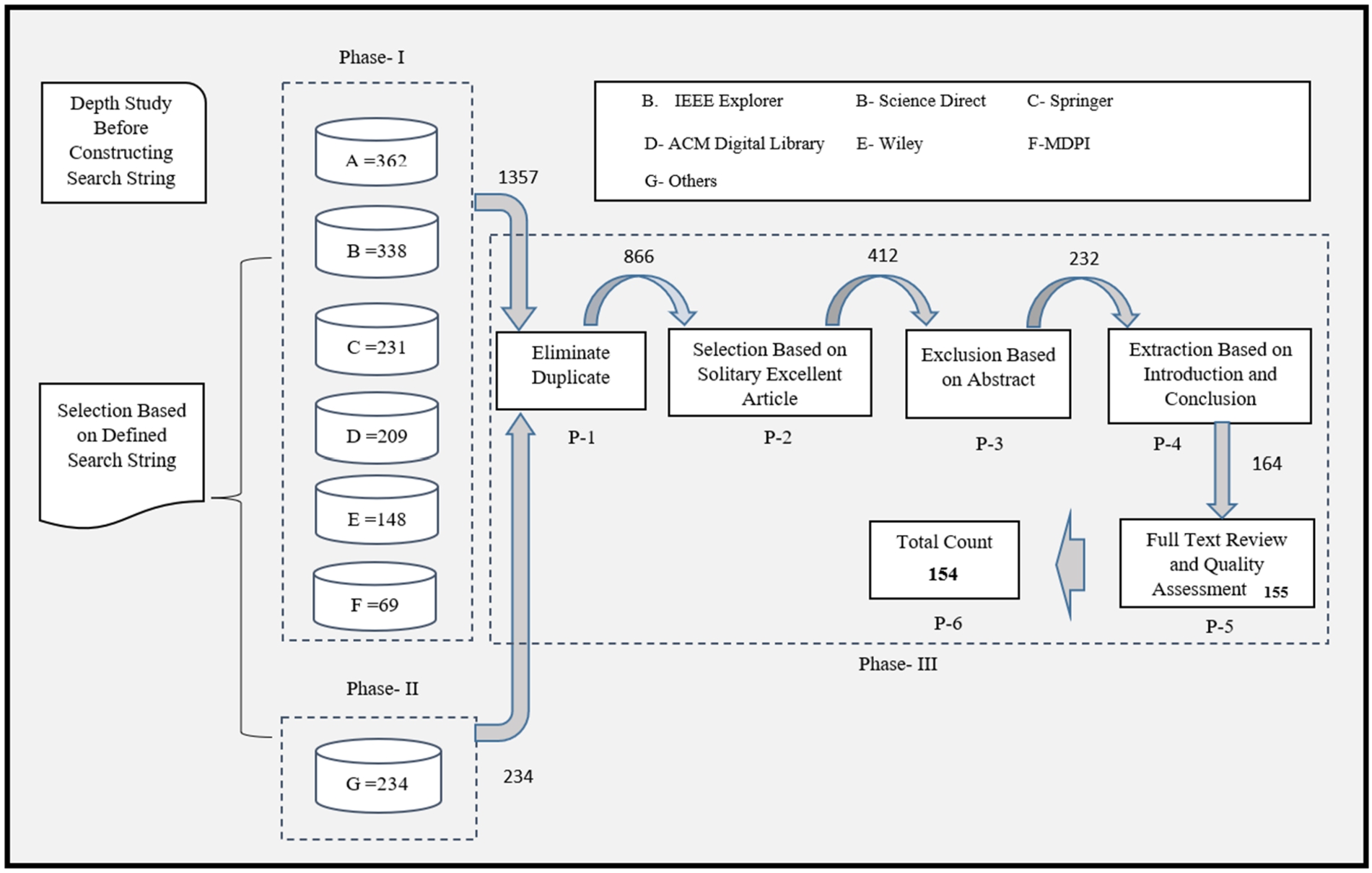
Article selection procedure.
This section describes the detailed methodology to better understand the role of digital forensics on the IoT. A novel search strategy has been used to extract relevant literatures from a wide variety of available electronic sources from the year 2006 to 2023. In which, articles are considered based on the inclusion and exclusion parameters of selection criteria. At the end of selection procedure, a detailed article distribution is given for opting a study or article.
Search strategy
The graphical representation of this section is given in the Fig. 2 In which, search keywords and strings have been used to search primary articles from electronic databases. The optimal method to construct a search string is to rank terms by popularity and importance. The phase P-1 eliminate duplicate, P-2 select solitary excellent article, P-3 exclusion based on abstract, P-4 extraction based on introduction and conclusion, P-5 full-text review and quality assessment, and the last is P-6 total selected papers for the Review. The screening is achieved by setting the inclusion and exclusion criteria of studies acquired during the third phase.
It includes (a) relevance of the study (b), the electronic database (c) the time period, and (d) language constraints. P-3 in phase III involves keywords, abstracts and developing classification techniques and needed two phases. In the first, the abstracts are scanned for keywords and in the second phase, the concept are identified which reflect the importance of research. When the abstract does not contain important keywords, then in P-4-point extraction based on introduction and the conclusion is examined. Whenever categories are unknown in the literature, multidimensional categorization is introduced that includes the main focus of research, proposed technique used, and proof for validation of evidence. This helps to distinguish between both categories that have been researched and needed for further study.
Literature selection process
This study has examined the variety of research from the academic and corporate world perspective, which includes both the publishing era 2006 as well as 2023. The peer reviewed journals, conference of repute and workshops has been considered for this study. Articles were selected by applying search strings in six well-known databases: IEEE Xplore; Science Direct; Springer Link; ACM Digital Library; Wiley Inter-Science; MDPI; and ISI Web of Science. Both database searches and snowballing are an integral part of search strategy. In addition, to conduct a manual search, snowball tracking reviews help in searching through the citations of each primary research paper. Each electronic data source has been mentioned separately, since the format in which search queries are entered varies from one to the other. To verify that the inquiries were semantically equivalent, we examined that the phrase structure of each query was distinct from the others. In order to produce additional surveys, we used the Boolean OR and AND operators to add alternative synonyms and link key terms. The following grammatical structure describes the Wiley Inter scientific database’s search string. Supplementary Table 1 provides the search strings for each of the electronic databases tested for this research. These databases provide systematic research in the area of IoT and forensics.
Selection criteria
For article selection, the following exclusion and inclusion criteria has been applied for the selection of research articles.
Exclusion criteria of the study
1. Study submitted in a language other than English has not been considered.
2. Study that did not cover IoT environment standards (device identity, authentication, and verification) or that does not offer adequate information on digital forensics models for the IoT was eliminated from the study.
3. Incomplete work and duplicate work has been eliminated.
Inclusion criteria of the study
1. English language is the criteria for selection of articles for the study.
2. Published articles, papers, reports, book chapters, case studies, conference proceedings, peer-reviewed journals, or reputed workshops from 2006 to 2023 has been considered.
To reduce a clear picture of digital forensics in the IoT environment, this study gives a broad literature review of the exploration of IoT forensics. Overall, 1591 studies have been revealed from the search plan by combining database and snowball as search methodology shown in Supplementary Table 2.
Step I. Evaluating relevant studies by applying search strings in a specific repository.
Step II. Exclusion depends upon title of the article.
Step III. Expulsion through the abstract of the manuscript.
Step IV. Exclusion after deep study of introduction and conclusions of article.
Step V. Removal after complete analysis and quality evaluation of article.
By using the above-mentioned points of inclusion and exclusion of the work described in the related literature following the restriction between the year 2006 to 2023, have resulted in 1591 studies. Approximately 725 of these studies have been identified as duplicates. Further, out of 866 studies, 454 articles have been rejected based on a solidarity of the articles and the title. The remaining 180 findings have been excluded based on the abstract, and 68 research works have been again excluded after reading the introduction and conclusions. All of the aforementioned result in 155 key studies for full review and assessment of quality, 1 study are of slightly lower quality, and thus we are left with a final total of 154 studies. Finally,154 papers distributed between 2006 and 2023 have been extracted through the seven stages for review (see year-wise diagram in Fig. 3).
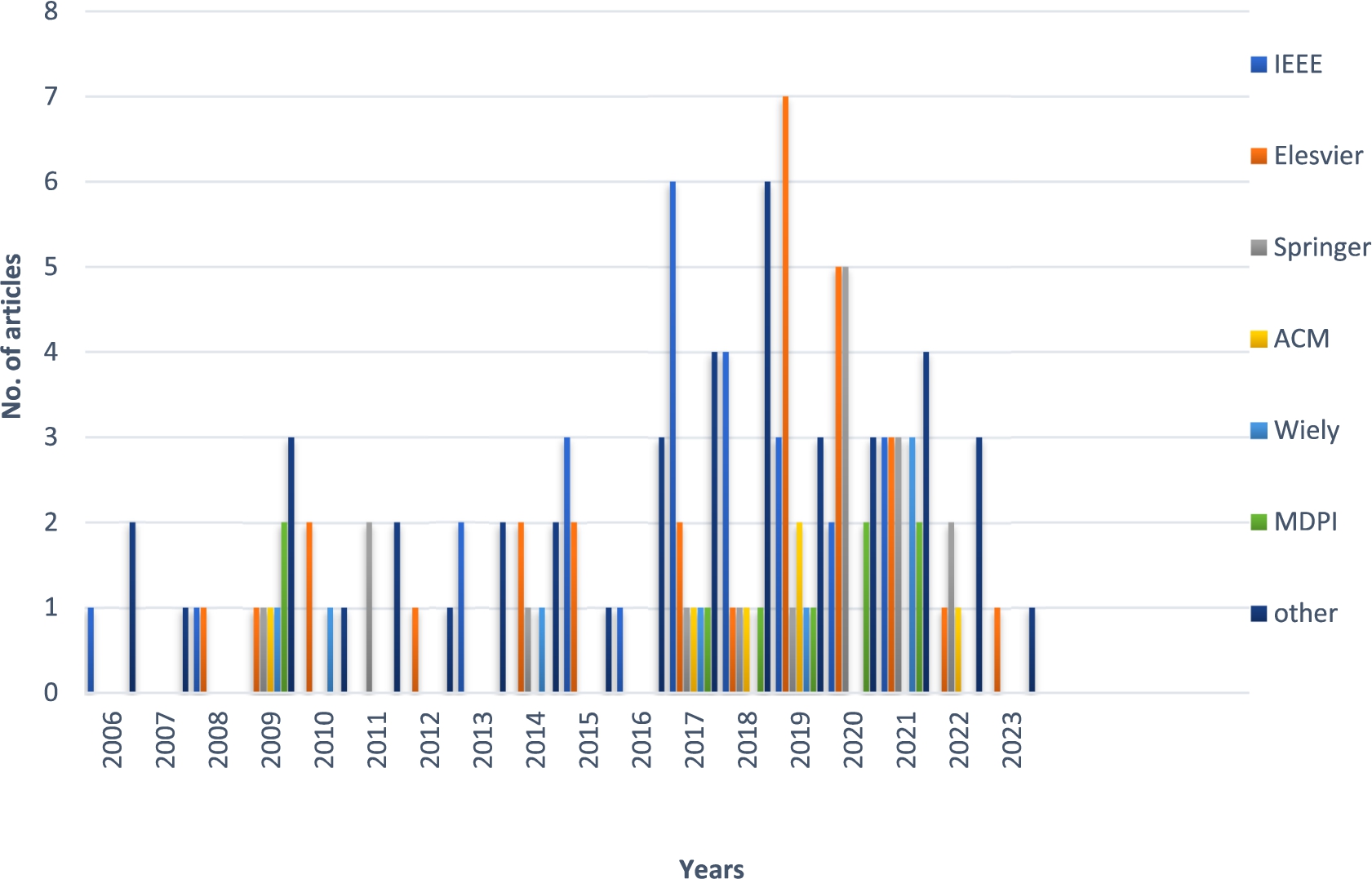
Journal-wise and year-wise distribution of final articles.
From the appropriation of the papers continuously distributed from the year 2006 to 2023, there is a sharp increment in the number of papers from 2017 onwards. The wide range of various years witness a progressive increment in the field of IoT forensic. Examination of IoT forensics has entered another time of huge development since 2015 with the broad utilization of IoT gadgets underway. One hundred twenty-two papers are ordered under seven classes including review papers from different publications IEEE, Elsevier, Springer, ACM, Wiley, MDPI, and other.
IoT security and forensics in ambient intelligence environments
Developed in the late nineties of the past century, the ambient intelligence (AmI) paradigm presents a vision for digital systems beyond the year 2010. New research perspectives on Ambient Intelligence indicate that the threat lies in the complexity of AmI environments, which may not be easily manageable, making the implementation of this vision potentially infeasible [1]. AmI creates adaptive electronic environments that cater to individuals’ needs by using interconnected devices and sensors. These devices record information like lighting, temperature, and vital signs, allowing the environment to behave intelligently. AmI recognizes individuals, learns from their behavior, and acts in their best interest, enhancing their surroundings [2].
In this context, Ambient Intelligence aims to enhance interactions between humans and their environments, promoting safety and enrichment. It extends beyond Smart Homes to various settings such as hospitals, transportation, factories, etc. The achievement of Ambient Intelligence relies significantly on the technology deployed, which includes sensors and interconnected devices through networks, as well as the intelligence of the software used for decision-making [14].
The application of ambient intelligence in smart environment is crucial because many time app does not ask the user but understands the user context and it can maintain and enhance the quality of life. IoT sensors and smart device collects sensitive data that leads to attract cyber criminals for malicious activity. Hence, IoT forensics is required to catch the criminal in smart ambient intelligence environments and aid in identifying the impropriety [17].
Security and forensics are two essential parts of the ambient environment, both focus on the protection of digital assets. In an ambient environment, while performing the digital investigation process some important information is openly available and can cause security leakage of personal information [95]. Such as health-related data residing in the smartwatch e.g., heart rate, waking information, location, login credentials, etc. Therefore, forensic investigation helps to identify security vulnerabilities and suggests manufacturers to deploy security measures where secure data exists. Here, we can conclude that security and forensics are two essential sides of the same coin. The work they do is very similar but different in a few ways. With digital forensics, cyber security companies have been able to develop technology that prevents hackers from accessing a website, network, or device. By knowing the trends of how cyber criminals steal or exploit data, cyber security software firms are able to protect relevant data and scan networks to ensure that outside parties cannot access it.
Security is about prevention and forensics is about a response after a breach is found. Incident response (IR) represents a set of information security rules and procedures for the detection and elimination of cyberattacks. The purpose of incident response is for an organization to be able to immediately identify and stop attacks, minimizing damage and avoiding such attacks in the future. Digital forensics deals with the aftermath of the incident in an investigation role, whereas security is more focused on the prevention and detection of attacks including design of the secure system. The cybersecurity team is responsible for implementing and maintaining a robust information security system with the goal of protecting an organization from cyberattacks; if efforts fail and a breach occurs then the computer forensics team will be responsible for identifying the vulnerability, determining the source, and to recover the compromised data and to identify person responsible for the breach. IoT forensics and IoT security are closely intertwined as illustrated in Fig. 4 and security would be less impactful if security gaps cannot be considered that were found during the digital investigation. IoT forensics comes into existence because of weak IoT security paradigms. Due to heterogeneity of protocols, heterogenous architecture, limited storage, poor security measures, and lack of common standards. Similarly, IoT forensics exists because of failed or weak IoT security tactics.
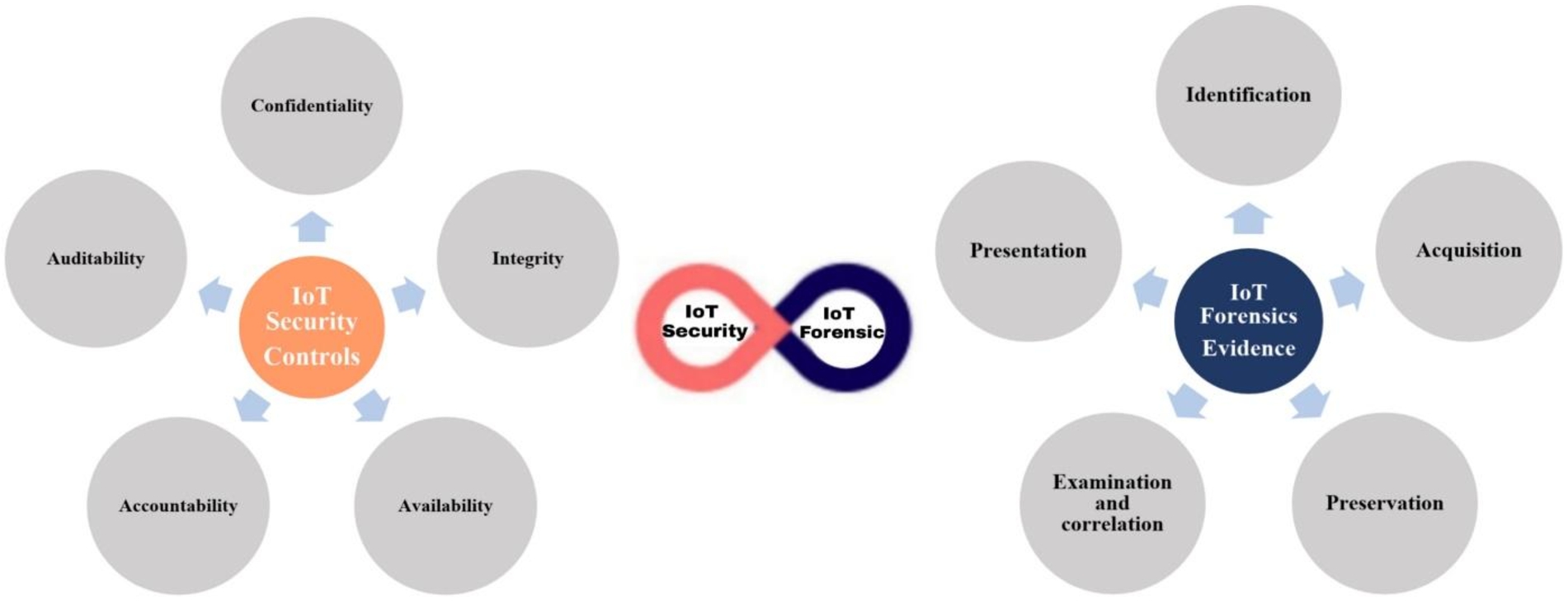
IoT security and forensics.
IoT security is the primary concern for today’s digital environment, which differs from traditional security techniques. With the exponential or rapid enhancement in IoT devices, the security challenge has been increased. Hence, three tier security architecture having physical level security, network level security, and cloud level security has been considered and shown in Fig. 5.
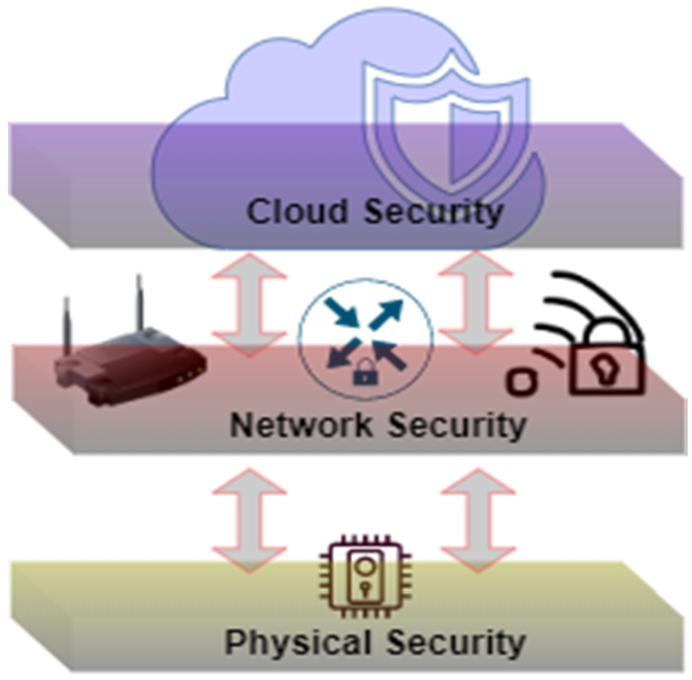
Three tier security architecture.
Maintaining security at each of three levels is of the utmost significance. In this section, the issues associated with security at different layers have been discussed in brief:
Security and privacy are the elementary needs to design a secure infrastructure for the ambient environment. Security ensures protection against threats and vulnerabilities, while privacy safeguards individuals’ personal data, making them essential considerations in the development of a reliable and trustworthy ambient environment infrastructure [37]. Hence, the adaptation of security and privacy principles have become the essential parameters which can be possible by using hardware devices and security software [51]. In a word, privacy is about control empowering people to keep up close to personal control of their recognizable data regarding its assortment, use, and revelation. Privacy is embedded into end-to-end encryption for communication between IoT devices, and machines. Data must be protected both from unauthorized access and from being altered. Uses of strong authentication and identity management of all human interactions with the IoT devices must be secure and data generated while interaction should be encrypted enough.
Secure infrastructure design for IoT means the Security at hardware level and safety of electronic chip that can be protected at manufacturing level. Hardware security must be implemented before the compromise of IoT device, not after accessed or affected by the unauthorized activity.
Even though protection necessitates that recognize data about an individual should be shielded from unauthorized access, and therefore, strong safety efforts are essential for implementing it. Privacy protection means guaranteeing secure access of information. In a word, privacy is about control empowering people to keep up close to personal control of their recognizable data regarding its assortment, use, and revelation. Information security demanding great attention due to a large number of discovered vulnerabilities in IoT devices. To enhance the security mechanism in IoT systems following points are shown in Table 3:
Security mechanism for IoT systems
Security mechanism for IoT systems
The widespread adoption of IoT technology has raised concerns about data privacy and security, particularly with regard to sensitive personal information. If data is not properly secured, it can be easily intercepted, tampered with, or deleted, which can hinder forensic investigations. The author Chin et al. [32] primarily focuses on the user-centered and smart environment perspective of IoT, which limits the scope of the discussion to a specific area of IoT environment. The paper discusses privacy and security concerns related to IoT but does not give insight into investigation challenges. The use of threat modeling to identify potential threats and vulnerabilities in smart city infrastructure, with a focus on cybercrime and digital forensic opportunities. Smart cities use a range of technologies and interconnected systems to manage and optimize city operations, such as traffic management, public safety, and energy usage [138].
Security is the key perspective for IoT, and the increased use of IoT in ambient intelligence has led to a heightened concern for cybersecurity. Hackers could exploit vulnerabilities in the software or firmware of IoT devices to gain control of the devices or the networks they are connected to. They could also use ambient intelligence systems to collect sensitive data from IoT devices for admissible digital forensic investigation [113]. According to Statista, there will be over 75 billion IoT connected devices in use by the end of 2025. This is an almost threefold growth over the number of users of IoT compared to 2019. Sensors and processors are used by IoT devices to collect and interpret data from their surroundings. The information gathered by the sensors will be stored in the cloud or analyzed locally. The amount of data generated by IoT connections is expected to reach 79.4 zettabytes by 2025 [130].
From the above statistic, it can be inferred that the number of IoT devices will continue to proliferate in the years to come; however, there will also be an increase in the prevalence of certain security risks, such as
Emerging security issues of IoT in ambient intelligence environments
As the number of IoT devices increase in the ambient environment, the challenges related to security also increase, uses of IoT devices has also enhanced the uses of smart technology in all aspects of smart cities, which will lead to more challenges in smart cities [77]. With the rise of automation and autonomous systems, artificial intelligence and data privacy have emerged as major issues in smart cities [132]. Figure 6 shows the security issues of IoT in ambient intelligence environments.
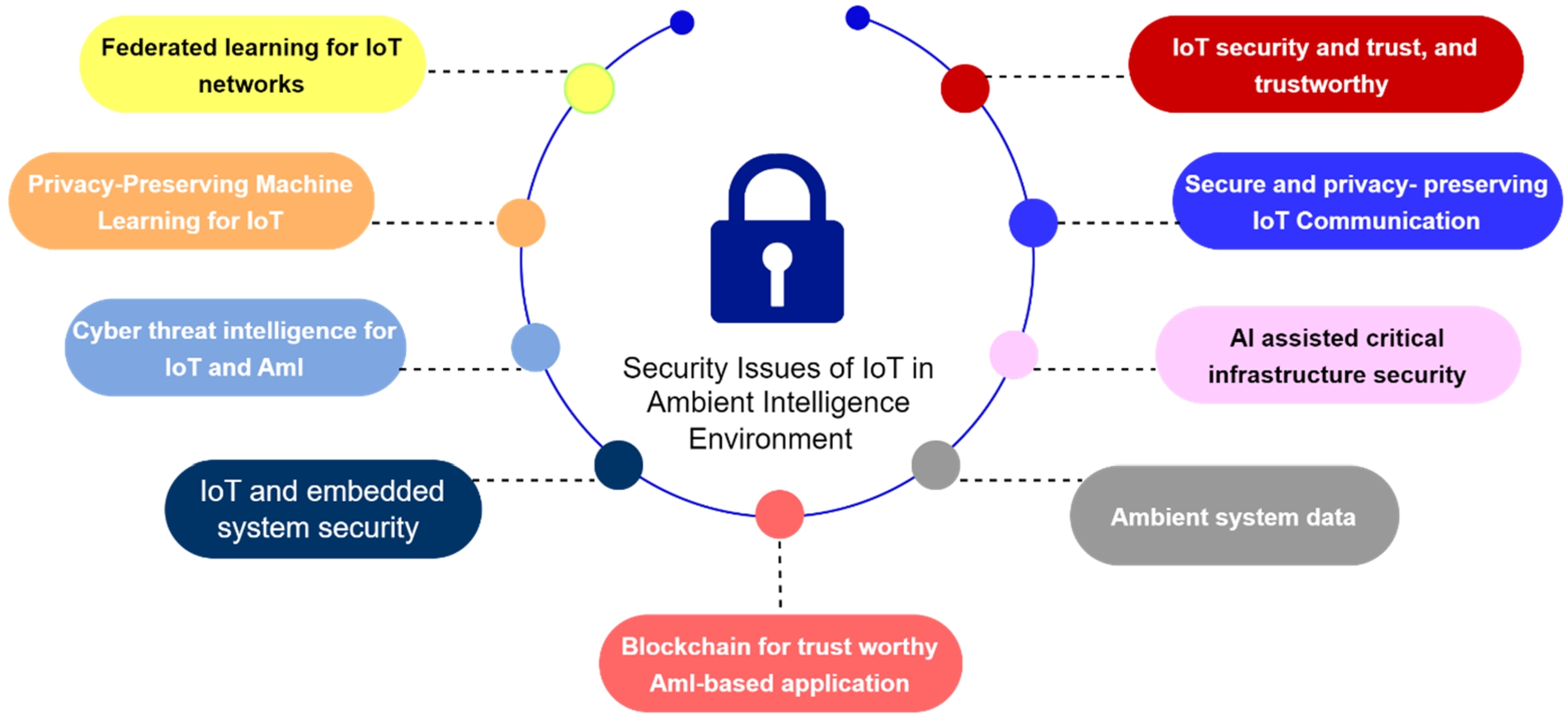
Security issues of IoT in ambient intelligence environments.
With the proliferation of IoT devices, huge amounts of private user data will be created. High connectivity, storage costs, and privacy issues will challenge the conventional IoT ecosystem of cloud-based learning and processing. Federated Learning (FL) is a viable alternative strategy. However, some challenges still exist with real FL system implementation on IoT networks [153].
IoT devices may provide sensitive information about people’s private activities and locations. To encourage widespread use, IoT-ML must prioritize user privacy. However, system designers often struggle to ensure privacy. There have been numerous studies on privacy-preserving ML in cloud computing, but it is important to determine whether these solutions can be adapted for the IoT context [154].
IoT systems generate high volumes of data, with a high velocity and variety, commonly referred to as the “3 V’s.” This heterogeneous data comes from various equipment and devices, making it difficult to trace the source of a cyber-attack. As a result, authentication of IoT data can be challenging [30].
Embedded security protects components and software in IoT devices. IoT device manufacturers face challenges to securing their devices against cyberattacks. This includes: Third-Party Components, Lack of Standardization, Unmanaged and Unpatched Devices, Insecure Network Connectivity [32].
Managing and maintaining trust while transmitting information through IoT is significant. The primary issue with AmI-based applications and blockchain is the working principle and architecture difference. Size of Blockchain, Processing Power, Security, Anonymity of Users and their Privacy, speed of transaction are all problems that need to be addressed [78].
Ambient system data refers to the information collected by electronic devices and sensors that are embedded in the ambient environment, such as smart homes, workplaces, and public spaces. These devices are designed to monitor and collect data on various aspects of the environment, such as temperature, humidity, light levels, air quality, and movement. The data collected by these devices can be used to provide insights into how people interact with their environment and can be used to optimize and improve the design and functionality of buildings, infrastructure, and other systems [56].
It is challenging to modernize the old buildings into new technologies which is cost-effective. Complex autonomous systems are difficult to understand, and sometimes it’s difficult to identify human emotions [119].
Privacy-preserving in IoT communication is a critical issue because privacy can easily be breached using certain attacks like sybil attack, message spoofing, linking attack etc. So, it increases the computational cost while applying security to each device as numbers of IoT device used in ambient environment [49].
Due to a shortage of computational and storage resources to analyse and store IoT data, it adopts a cloud-based architecture. The trustworthiness of cloud service providers (CSPs) has become one of the most significant challenge in cloud-based IoT [83].
Another important issue is various parts of an IoT device are manufactured at different countries, and all these parts have different security standards. For example, the maximum smart IoT device company used a Wi-Fi module (TYWE3L, TYWE3S, TYWE2L, TYWE2S etc.) from a China-based company called Tuya but on product details, they had mentioned manufacturing details of a different country [141]. This type of security standards are dangerous and create a significant cause for an IoT device to be vulnerable. Digital forensics is an important part to finding out the vulnerability in IoT devices. So, it require a more structured or standardized framework that allows digital forensic investigators to evaluate risk assessment for better communication and the capacity to more effectively exchange data [115]. To better understand IoT forensics, the next section highlights the need of digital forensic in IoT.
Digital Forensic Research Workshop (DFRWS) defined Digital forensics as, “The use of scientifically derived and proven methods toward the preservation, collection, validation, identification, analysis, interpretation, documentation, and presentation of digital evidence derived from digital sources to facilitate or further the reconstruction of events found to be criminal or helping to anticipate unauthorized actions shown to be disruptive to planned operations” [13,106]. Digital forensics is the process where legal investigation can be assisted by analyzing digital sources of evidence and preserves the privacy and security of data [122]. An effective digital forensic process entails routine protocols, such as the identification of equipment containing evidence, separate processing of digital data, examination and retention of vital evidence, and systematic documentation of crime-related evidence that is admissible in the court of law in compliance with requirements [8,125]
Digital forensics has become a requisite in IoT environment due to the expansion of attacks on IoT devices which may the fragile security. So, IoT forensics comes into the light to bridge the overarching scope of IoT devices through digital forensics tools and methods. IoT forensics can help to turn down the occurrence of the trace of source, track root causes, and design correlated countermeasures [100]. Different examples of sub-categories in digital forensics are computer forensics, network forensics, mobile forensics, and cloud forensics. The capability to carry out the investigation is related to the availability of digital evidence [100]. Consequently, along with various security and privacy challenges, the exponential development of IoT devices provides numerous advantages. Thus, IoT forensics has become one of the well-known areas for upcoming researchers. The diverse nature of IoT devices and the absence of common standards make IoT environment hard to investigate [7]. In fact, the challenging part of the investigation is the testing phase due to a slight change in evidence can make a different meaning, or it will destroy the originality of the evidence. So, to avoid this challenge dump image of the device memory is required for forensic investigation.
Disk acquisition tools create a bit-by-bit copy of the memory. Therefore, if the size of the obtained media is 2 terabytes (TB), the resulting disc image will also be 2 TB in size. Grier et al. [101] presented a technique for forensics of those images that contain evidence for investigation purposes. The dump image will include even blank, unused, or irrelevant regions. It will also contain the portion devoted to operating systems (e.g., Windows, Android, Mac OSX, IoT Operating systems like Contiki), third-party apps, and Microsoft or Apple programs and their digital artifacts. These regions are often unimportant. Most computer forensic investigations focus on a user’s documents, emails, internet history, and illicit photographs.
Dynamic analysis tools can give investigators a more accurate and consistent picture of current and previously running processes, whereas the traditional approach provides investigators with partial evidence. Numerous important system-related data stored in volatile memory cannot be properly retrieved using static analytical techniques.
To know the facts behind the evidence, we need to analyze the artifacts either in traditional or modern ways. Today’s forensic software can often find hidden data storage locations – Swap files, unallocated disc space, and file “slack” (data padded to the end of files are all examples of ambient system data that may include useful information, such as email history, document fragments, Web surfing histories, and user timelines) [73].
With the help of dynamic and static analysis, the key factors of digital evidence for the investigation purposes can be understood in a better manner.
Table 4 categories the tools with their platform for collecting digital artifacts that contain essential information about criminals.
Static and dynamic tool for digital forensics of IoT
Static and dynamic tool for digital forensics of IoT
The IoT forensics has also a three level architecture similar to IoT security categories (refer Section 4.1) However, all the tools that have been used till date are divided and into hardware, network, and cloud levels. The tool used for digital forensic, and the evidence extracted from them cannot be divided efficiently into three parts. This section helps to know what kind of data is present and which tool is required to extract meaningful artifacts from three level of IoT forensics. Figure 7 depicts the three levels of IoT forensic.
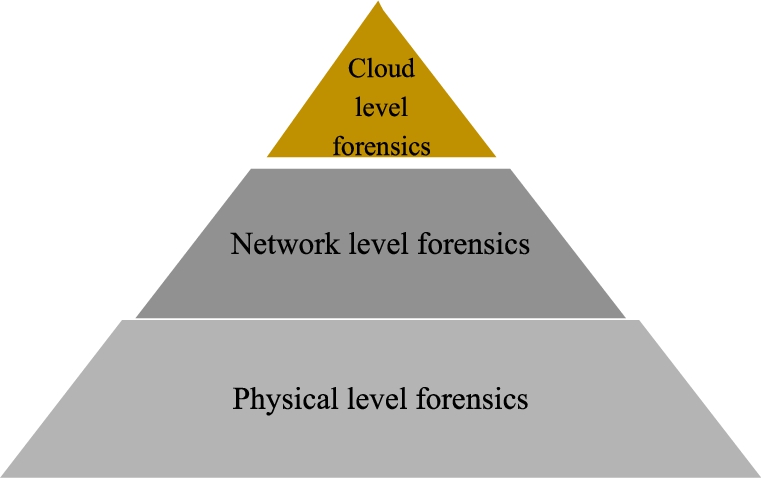
Levels of IoT forensics.
In most of the cases, device level forensics is the primary source of information because investigators first acquire data from the device. In some cases, cloud level artifacts can be located at the device level, e.g., cloud Id, etc. Therefore, it is the most significant source to collect the information. In this level, the investigator collects artifacts from the local memory of the device by creating dump images from memory, pictures and video from a camera, a connected device like Alexa, smart sensors, automated cars, drones, RFID devices, a specific parameter from smart health care devises etc. Clinton et al. [35] presented their examination on investigating Amazon Echo at device level. The authors Merit summed up their trials to figure out the device through accessible methodologies, for example, eMMC Root, JTAG, and debugging ports. Even though they clarified some potential techniques for empowering admittance to the internal parts, including soldered memory chips, they didn’t show the data inside the device. Thus, this perspective can be used for future investigations. A few IoT devices might be tough to find by the experts due to the tiny size of medical sensors for example the blood pressure measurement sensors by Merit Sensors system Inc. could be only 8.1 × 10.5 mm big and less than 2 grams heavy [92].
Network-level
Unlike other branches of digital forensics, network forensics deals with volatile and dynamic information that may easily be lost after transmission in any network environment. Whereas an attacker may be able to wipe all log files on a compromised server, network-based evidence may be the only evidence accessible for forensic analysis [68]. A network containing several IoT devices, associated devices, and the cloud can be connected via different wired and wireless network protocols. In such network, miscellaneous threats can be detected and retrieved to perform the digital data analysis from network traffic logs in the investigation process. As a result of traffic analysis using the Charles web debugging proxy (XK72), it is confirmed that most traffic associated with forensically meaningful artifacts is transferred over an encrypted connection after creating a session with a valid user ID and password. With this network analysis, the infrastructure of IoT networks such as Personal Area Network (PAN), Local Area Network (LAN), Wide Area Network (WAN), Body Area Network (BAN), Bluetooth, (ZigBee) are most commonly used for home automation. Significant information can be extracted from the external and internal networks as shown in Fig. 8.
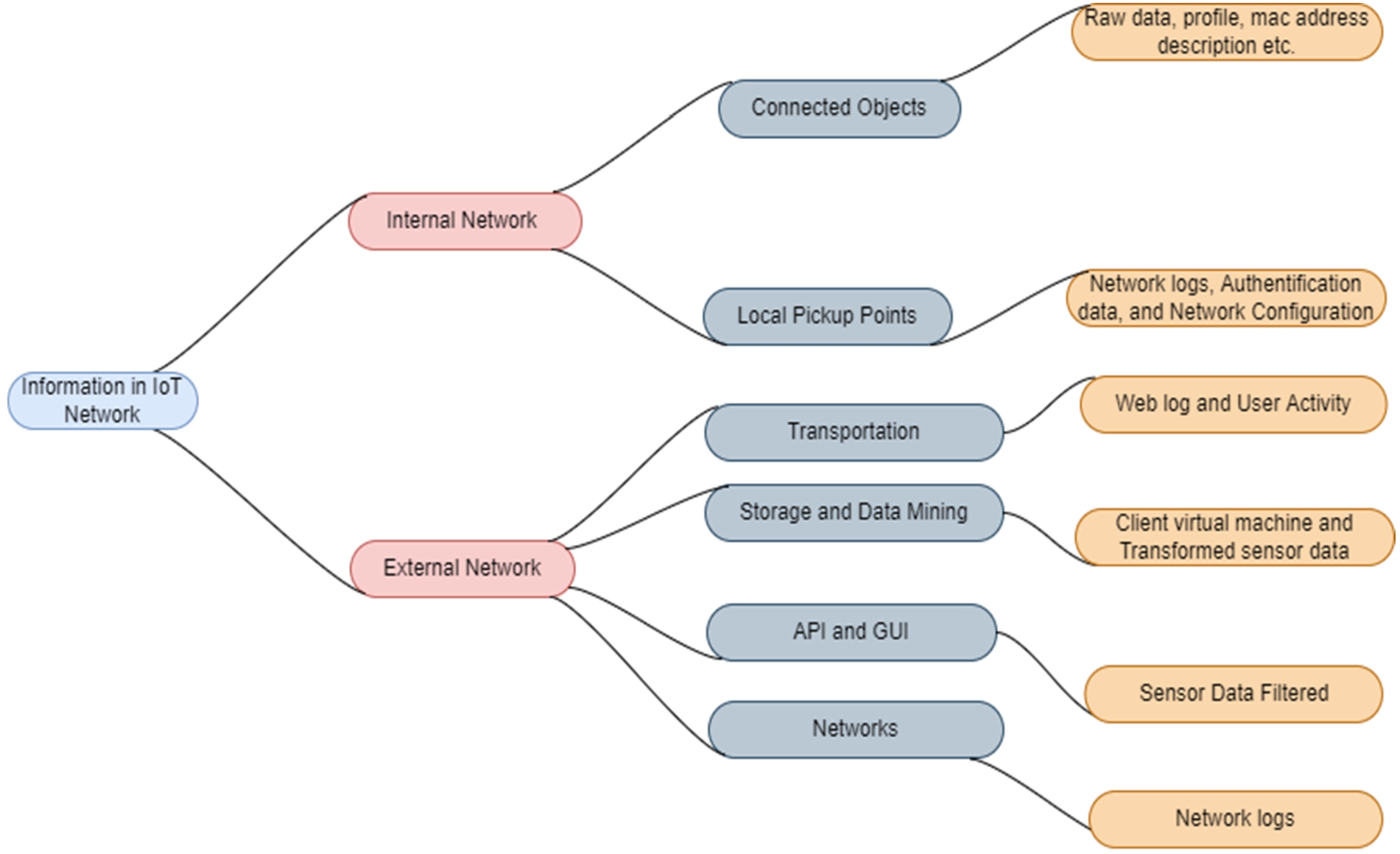
Information in IoT network.
Type of evidence and its source in various IoT applications at cloud level
Evidence at the cloud level is another essential part of the IoT Domain. Most internet-connected devices store their data on the cloud because of the low storage medium available at the physical level and has less computational power. Logging details generated by IoT devices are stored in a distributed way in the fog environment. Information correlated to history logs can also collect access logs, chat logs, session data, system logs, location information, user permission, and access information from the cloud. Therefore, at the cloud level, the forensics investigation process is essential. IoT devices have different types of evidence that can be extracted from various sources at the cloud level, as shown in Table 5.
Source of information in IoT forensics
Different crime scenes have various sources of evidence and contain the information related to crime as the criminal will bring something into the crime scene and leave something there, and both can be used as forensic evidence [26]. In IoT environment, digital evidence can be collected by focusing on the primary sources related to malicious activity that can reside at different levels of forensics [74]. The main source of information that can be extracted from the network and connected device is divided into three levels as shown in Fig. 9.
Data exists predominantly in the various IoT devices such as sensor nodes, medical devices, embedded systems, home appliances, and automated vehicles. Although the information storage power in IoT devices is significantly low because of the compact size, this information is directed to a central computer through the network to process valuable data. Evidence related to the system logs and temporary files is a good source of evidence. This data can be extracted by tracing volatile memory of various network devices such as routers, SDN, switches, etc. [149]. Google Assistant devices like Alexa, echo, and Miko are good sources of information in the IoT environment. Figure 9 shows the connected device in the IoT network. Table 6 describes the various tools and sources of information used in three-level IoT forensics.
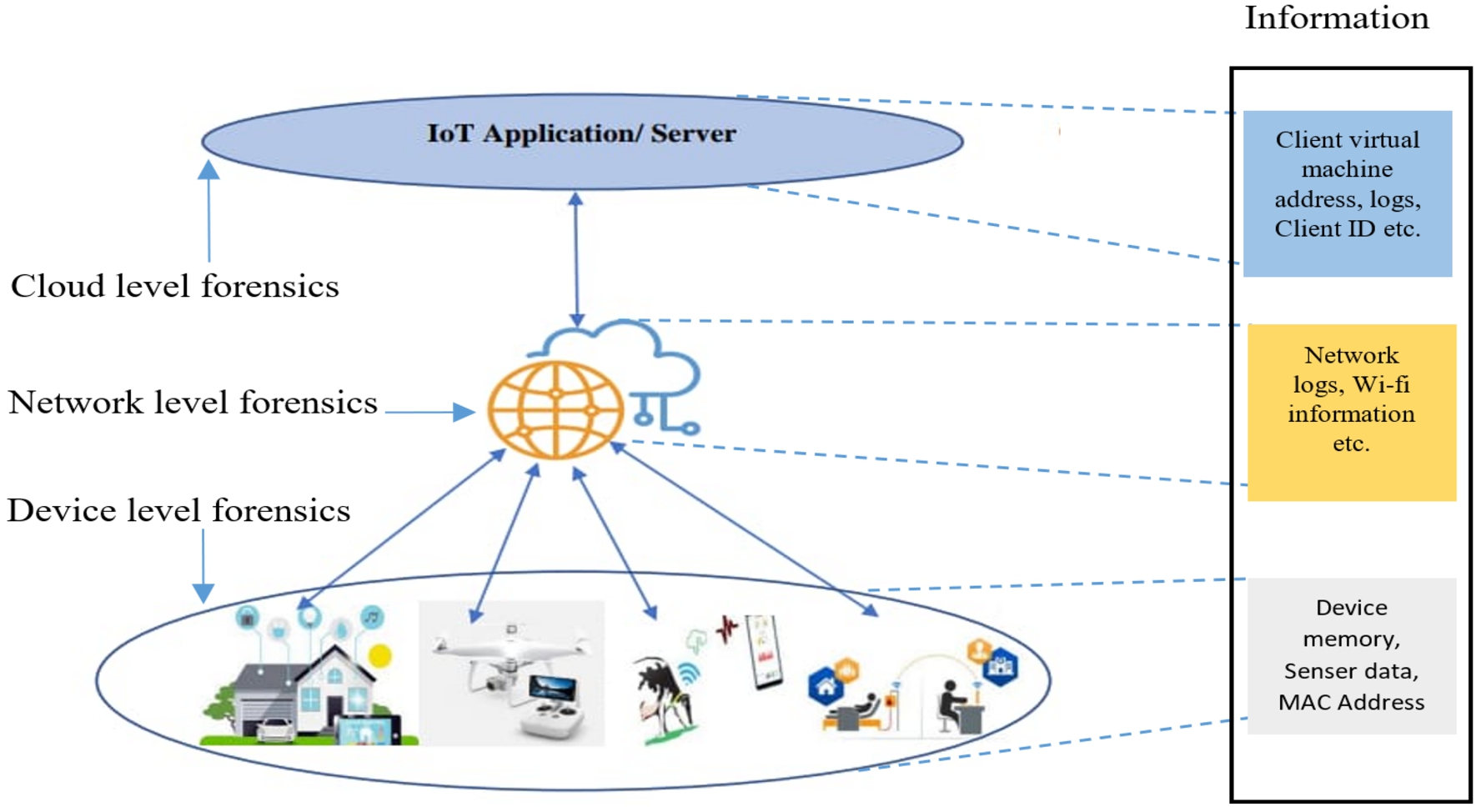
Source of information in IoT environment.
Tools and source of evidence in three-level layer IoT forensics
For better understanding, investigators can detect digital evidence from IoT devices by partitioning into three levels with the help of different forensic tools that can help to retrieve important information. Potential evidence can be collected in various areas of IoT forensics as illustrated in the next paragraph.
Internet-of-Things have become an essential part of today’s life to ease human life. It is emerging into all sectors of daily routine with smart interaction between humans and things. The communication among smart devices generates a vast amount of decentralized data, including personal and behavioral information. Table 7 highlights the types of potential forensic evidence in different IoT devices, which can help the forensics researchers to collect related artifacts and related information.
Types of potential forensic evidence in different IoT devices
Types of potential forensic evidence in different IoT devices
Each IoT device operates in a unique environment, so all IoT device produce a unique set of forensic evidence. The various domains of IoT forensics are illustrated in Fig. 10.
Over the years, many smart home devices have been utilized to complete various valuable tasks such as monitoring and controlling home appliances, Therefore, IoT devices contain data about users and their surroundings. These devices may be used for digital investigation. The data generated by smart home devices give crucial information about user activities that may be examined by extracting the data from the smart home devices. The data stored in smart home applications pertaining to smart TVs, smart speakers, smart lighting, and smart door sensors, etc., is helpful for crime investigation [19,131]. The activity and behavior of users can be analyzed through forensics of Smart TV as it contains the history logs. The development of such forensic tools, including methods for acquiring root privileges, pre-imaging, testing, post-imaging, and comparing binary data from smart TV forensics to trace user behavior is described by Stoyanova et al. [131], Kim et al. [72] and Boztas et al. [20,72,131]. There are some examples where smart home evidence helps to identify the criminal and shows the importance of IoT forensics. One prominent example involved amazon echo recording to be used as evidence where an Arkansas man was accused of killing his friend in a murder case [82]. In another case, Husband Confesses to Murdering Wife As Smartwatch Data Exposes His Cover-up [57].
IoT forensics for smart vehicle
A smart vehicle that operates and controls its primary function remotely using the Internet and connected frequencies. The Internet of Vehicles (IoV) system allows the exchange of information between vehicle and their surrounding sensors that are linked with the smartphone [149]. Nowadays, smart vehicles have their infotainment system, including a music system, smart plugs, and other digital features that can be controlled through hands-free personal devices. Smart vehicles can be attacked either to damage the infotainment system or steal information. There are several incidents where cars were attacked and caused damage [13] Internet of vehicles system has a trustworthy investigation framework called Trust IoV. This framework can be used to collect and preserve reliable evidence from highly disseminated smart vehicles [54] A case study of vehicle forensics has been proposed by examining data and forensics acquirement of the entertainment system on Volkswagen cars. It also acquires forensics artifacts from potential hardware and software solutions [81]. The associated vehicle can be a decent source of information where cybercriminals can utilize GPS gadgets, connected versatile data like contact numbers, bluetooth, email information, last login subtleties, and sensor information. Electronic control unit (ECM) information incorporates speed records, airbag, and brake light sensor information to characterize the true cause of an event. This type of information provides a good source that can be used as digital evidence in a court of law [41].

Fields of IoT forensics.
The healthcare industry in an ambient intelligence environments includes IoT-based equipment such as temperature humidity sensors, blood pressure sensors, and other monitoring devices and software applications. These gadgets may gather data automatically and continually inform doctors on the vital statistics of crucial patients [22,109]. The new and more intrusive devices will emerge and this area requires urgent attention from digital forensic perspective. The growing number of health information fraud cases are increasing day by day. Generally, the business of Health applications and administrations were estimated over USD 84.08 billion in 2019 and will raise 220.94 billion with 14.8% annual CAGR growth during the forecast period of 2021–2026 [45]. With the COVID-19 pandemic, the health industry is turning towards IoT technologies [142]. As IoT devices in healthcare proliferate, so chances for the occurrence of cyber-attacks increases. Among all IoT-based spaces, the medical services division is likely to be the most powerless against significant security assaults. According to IT security firm SonicWALL, global ransomware attacks have doubled in 2021, with the healthcare industry seeing a 755% surge in intrusion attempts and malware attacks on healthcare IoT devices have increased by 71% [129] Healthcare IoT devices can be easily controlled from a remote location. As a consequence, by putting security on medical equipment may lead to secure patient health information [135].
A fitness tracker tracks the routine activity by calculating distance traveled by the user, calorie intake, body temperature, biometric information, GPS data (with timestamp), heartbeat, and sleep quality [65]. In addition to that, IoT devices like smart bands are the most significant wearable devices that can be used to collect physical variables of a human body, which is valuable for forensics purposes [60]. For example, fitness trackers store important health information, and malicious actors can use this data to illicit financial profit. Also, the data can be sold out to the criminal mind person for other benefits or to the insurance companies or blackmailing the owner of the attacked device [3].
Wearable devices such as Armbands have additionally picked up significance as a source of digital proof in crime scene investigations. IoT health care devices work actively in the foundation of the user’s everyday life activity and produce information with built-in sensors. The information generated by the health care IoT device attracts cyber criminals for illegal activities [4]. It also helps to catch false statements given by the suspect and trace the activity of the person close to the crime incident. The rising number of security and privacy protection cases highlights the need for more innovative and dynamic methodologies than traditional digital forensics approaches [146]. In some instances, it may be easier to acquire the necessary data from the connected devices than from the primary embedded devices. But it is very difficult to extract data from the encrypted mobile operating systems that are installed into new embedded devices like wearables and automobiles. Recovery of data from some of these new technologies may not be possible, or if it is possible, then the data may not be in a readable format. At the same time, privacy concerns should be of exceptional consideration as health-related data collection continues to grow rapidly. Therefore, the study of smartwatches, smart bands, and other smart healthcare devices have become even more important for forensic practices.
IoT forensics for unmanned aerial vehicle
UAVs have been used for activities like remote surveillance of prohibited areas, drug smuggling, terrorist activity, etc. The digital investigation process can be improved by using a generic drone forensic model after analyzing the basic architectural design of the drone [61]. Drones are part of unmanned systems that include connected mobile or remote controllers, batteries, sensors, base stations, and other connected devices that maintain the drone (Drone motor, propellers, GPS module, Drone flight controller). Usually, researchers work with two primary log sources, i.e., the drone and the mobile device (act as a remote controller for UAV). Still, it adds more information about the user’s activities, such as logging details, connected device information setting waypoints, and changing views in the application. Both sources have the following essential information: the serial number of the UAV, version numbers for critical firmware, launch/ land mode information, manual/waypoint operation, GPS availability report, Geo-location information, home point, and Flight track information.
Drones will never be used everywhere equally to mobile devices, as the design and technology of UAV forensics are at the point where mobile device forensics were ten years ago. The drone market size grows from USD 4.2 Billion in 2021 to USD 33.61 Billion by 2030, at a CAGR of 26% during the forecast period 2022–2030. In drone forensics, investigators can’t retrieve all of the important information from a single forensic tool because a drone has at least five different file systems, many of which aren’t recognized by commercial tools. So, more research needs to be done on drone forensics. To further complicate the situation, each manufacturer will employ a separate collection of components, which will change within their product line, and new vendors will introduce new products monthly. But they will undoubtedly play essential roles in our society. It is necessary for law enforcement agencies, security, and military professionals [75].
IoT forensics for smart industries
With recent advancement in smart industries and the continuous rise in the smart ecosystem, the quintessential requirement for process automation have expanded the spectrum of cyber-threats and attack methods in addition to creating enormous opportunities. Among other things, these revolutions have resulted in a paradigm shift, a transformation of industrial ecosystems and processes, and an improvement in operational efficiency. Operational Technologies (OT) such as Supervisory Control and Data Acquisition (SCADA), Industrial Control Systems (ICS), and Distributed Control Systems (DCS), which were previously stand-alone, have been able to not only converge with ICT-based technologies but also have led to the automation of smart ecosystems that comprise a wide variety of networked devices, applications, and systems. This has been made possible as a result of the aforementioned. This has resulted in the creation of Industrial Internet of Things (IIoT) technology [133]. Currently, the worldwide market size prediction for IIoT is anticipated to reach over USD 950 billion by 2025 [58]. Smart manufacturing and process automation have forgotten the concept of IIoT forensics in their pursuit of industry 4.0. The study primarily emphasizes susceptible cross-cutting IoT technologies that have accelerated the emergence of IIoT, as well as the necessity of digital forensics standards, techniques, and procedures in IIoT.
IoT forensics for smart farming
Smart Agriculture involves the use of IoT devices and sensors to collect data, analyze, and make informed decisions to improve crop yield, reduce costs, and increase efficiency [114]. Precision farming refers to managing farms using modern techincal (IoT based) infrastructure to improve product quality and quantity while minimizing the need of manpower. IoT is a boon for the agriculture sector which provides modern assistance to the farmer and at the same time secures his crop and increases the yield. Through Smart Farming, the farmer can get information about the soil fertility, moisture, and crop quality of his field. If any deficiency is found in the soil or in the crop, then that deficiency can be known through smart farming. The author [114] highlights the need for further research and development of IoT technologies to improve their effectiveness and efficiency in agriculture. The paper also discusses the importance of data security and privacy in Smart Agriculture and the need for appropriate regulations to protect farmers’ data. But this collected information must be secure otherwise, it can be changed or tampered by any cyber criminal and he can even damage your devices or crops. Through IoT forensics in smart farming, we are able to identify all of these vulnerabilities that aid in apprehending offenders. In smart farming, sensor collects some parameters in the greenhouse and send them to the control center, then the control center can conduct some operations according to the analysis required from the collected parameters [46]. But sometimes this transformation of data between sensors and the control center is not secure, which helps an intruder to interact and manipulate. IoT forensics in smart agriculture helps to identify such criminal activity.
Evidence acquisition/extraction techniques
Extraction of artifacts from IoT devices needs various tools and techniques. Different digital forensic fields, along with hardware forensics (working with primary memory and secondary memory), network forensics (for retrieving and observing the transmission medium) cloud forensics (for investigating the unknown storage) requires a different methodology. A variety of open-source tools are available for digital forensics relevant data extraction [31]. To get evidence from an IoT system with both known and unknown devices, the collection of evidence needs to be prioritized. This sorting process is often called triage. During the evidence collection phase, a triage must decide if the devices are likely to have evidence, how easy it is to get the data from the devices, and how quickly the evidence changes [120]. The speed at which data disappears from a system is called its “volatility,” and it is a key part of figuring out how likely it is to get the best evidence. Hard disk drive (HDD) is the easiest method of acquiring data, then the encrypted data on HDD. Moreover RAM (Random access memory) is more difficult to manage since it loses data when the device is switched off whereas, SSD stores data on flash memory chips and the main challenge of forensic investigators is SSD’s file recovery of deleted items. The data retrieval is more difficult when the write blocker is connected to the SSD before taking an image, because the memory controller and garbage collector erase unallocated memory cells. Cloud storage is more challenging since data is stored across the nation or possibly the globe. Data collection becomes very difficult if data is encrypted before uploading and is kept on many locations. There is a need for suitable tools to collect significant contents from IoT devices, such as RFID and NFC devices. Different evidence extraction techniques are discussed in Table 8.
Analysis of evidence acquisition/extraction techniques
Analysis of evidence acquisition/extraction techniques
Further, different devices have alternate techniques and methodologies to retrieve data and same has illustrated in Table 8. But the process of data acquisition in the IoT environment is still challenging. With the increase of attacks related to IoT, there is a tremendous demand for the successful prosecution of culprits [88]. This gives rise to opportunities for research communities to develop new age digital forensics methodologies, techniques, and tools.
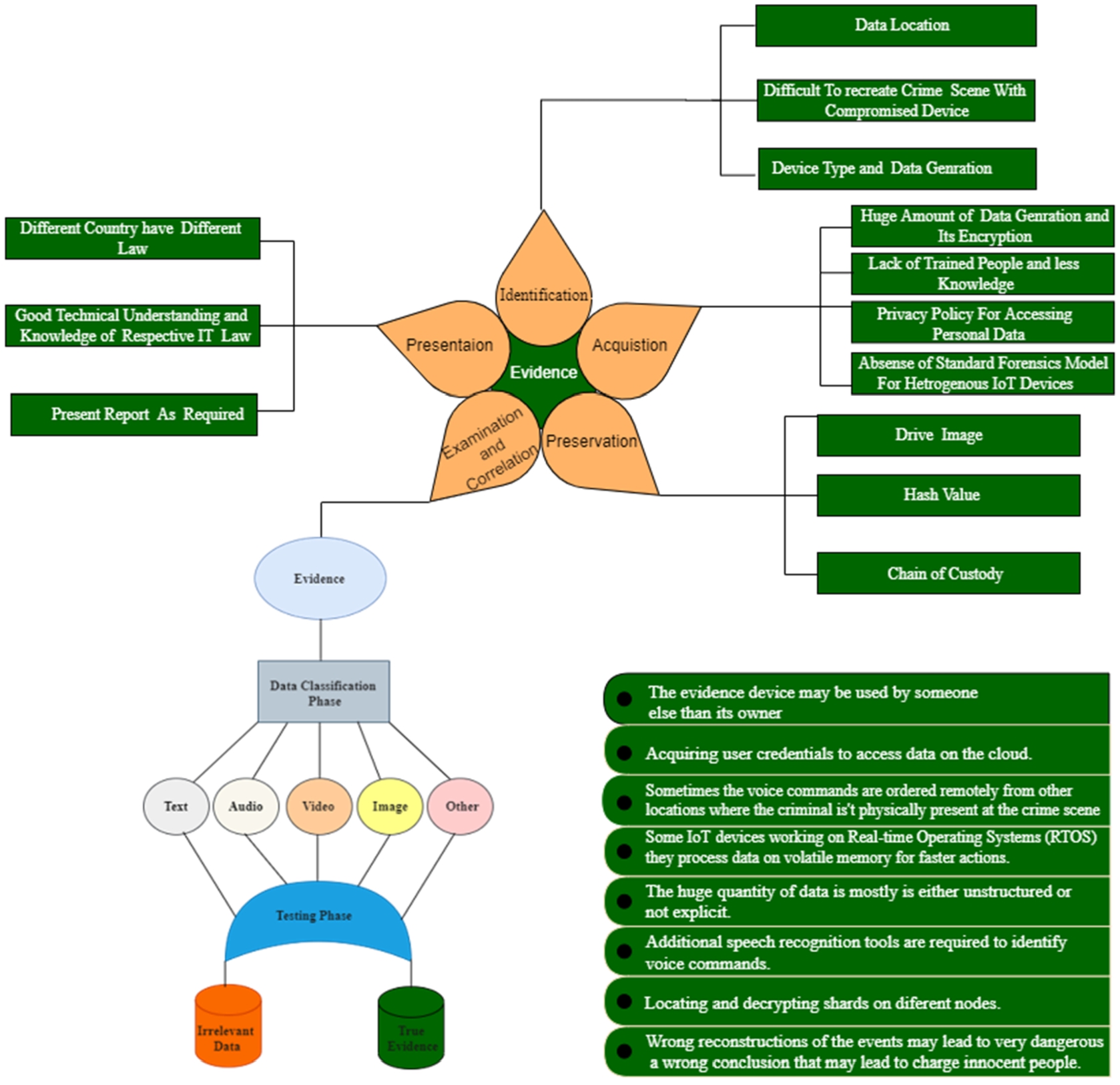
Various researchers have observed and laid out forensic methods that can be tracked distinctly during digital forensics examinations. In a cloud environment, the distribution of computation and storage poses a unique and complex challenge for investigators. As in cloud forensics, extraction of evidence from the distributed environment is far more difficult as computation performs at different locations [11]. For IoT this might be very disruptive as devices are broadly distributed to people such that interference with them is interference in their lives. Instead of this, plenty of well-known standards can be helpful for the investigation, such as the National Institute of Justice (NIJ), National Institute of Standards and Technology (NIST), Integrated Digital Investigation Process (IDIP), Digital Forensics Research Workshop (DFRW). A few researchers and practitioners [116,118] have concurred on the stages discussed in the NIJ cycle, as shown in Fig. 11 The steps involved in the above said process are as follows:
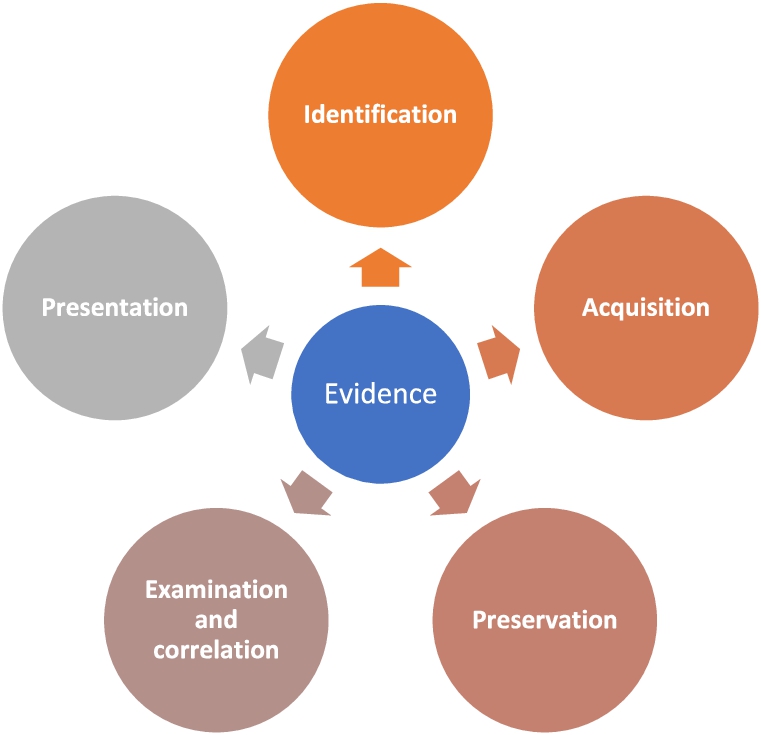
Investigation process of forensics artifacts.
The first and the key aspect of all kinds of forensics assessment is searching for evidence [36]. The most prominent challenge for cloud forensics is that potential evidence resides in scattered places all over the world in a virtualized environment [71] Hegarty et al. [50] assert that recognizing evidence in the IoT context is hard to find. The first and most fundamental aspect of any forensics valuation is the searching of evidence since the analysts might not know where the researched information is physically located [148] Finding the compromised IoT device is a simple operation, however, reorganizing and linking the crime scene might be difficult because evidence that originates at the crime scene will provide a picture of events for the court to consider in its deliberations. The below-mentioned points explain what type of issues the analyst experience during the evidence identification phase.
Data location
IoT devices usually change their location when people carry their electronic gadgets while moving. For example, data descending from smartwatches, fitness trackers, smart outfits, or moveable objects like an automatic car, bike, and drones, do not stay in specific geographic locations [121]. In this way, when the investigator wants to find evidence, digital forensics experts [27] face impressive difficulties. It is possible that a country doesn’t allow the evidence of IoT devices to be used in the judicial decision because maximum IoT devices process and store their data on distributed servers which gives criminals an extra edge for exploiting these IoT devices as the servers are difficult to locate. Moreover, the evidence may be subject to different jurisdictions with conflicting guidelines on information security and unapproved interruptions [5].
Difficult to recreate crime scenes
In past years, digital forensics has been restricted with boundary lines where the target environment can be almost completely isolated, acquired and under the investigator control. So, the investigator could be able to track the persons that were using the compromised device, the data might be located on various platforms like a virtual machine (VMs), which implies that significant forensic information such as registry keys or certain temporary records can be wiped out as the virtual machine gets shut down or rebooted [84]. Real-time and self-sufficient communication between different nodes makes it tough to recreate the crime scene and to recognize the extent of the destructions.
Device type and data generation
The increasing research interest in smart cities has been continuously growing in recent and upcoming years and economically justified by state-of-the-art technologies [21]. However, the growing number of IoT devices with different architectures and the immense amount of data they generate creates a significant challenge for investigators in identifying suspected artifact. A report directed by the International Data Corporation (IDC) states that the number of internet-connected devices like machines, sensors, and cameras that make up the IoT grows steadily. A new forecast from International Data Corporation (IDC) estimates that there will be 41.6 billion connected IoT devices, or “things,” generating 79.4 zettabytes (ZB) of data in 2025 [126]. Hence, enduring digital forensics tools cannot control such remarkable growth in volume, variety, and velocity [151]. Forensic experts need to distinguish what is valuable for the examination and dispose of the inappropriate data, which makes the fortunate investigation difficult [110].
Evidence acquisition
The second phase of the investigation is evidence collection. The suspected IoT device already identified the valid data is to be extracted, but presently no standard method for collecting evidence from an IoT device [36]. An investigation of a hundred arbitrary digital forensics claims demonstrated that in 8/100 cases, there was an error in data collection [12]. In such a manner, the proof collection stage is among the most significant steps of the forensic procedure because any mismatch could make evidence data invalid and influence the entire examination measure. While collecting the evidence from the device, there must be a specific procedure to create a report that remains useable in court. Such as, the steps of evidence collection must go into the legal means, denoting that the respective establishments should generate a printed order to start the investigation process [38]. Besides, there is some challenge related to evidence acquisition which is explained below.
The huge amount of data generation and its encryption
Considering that IoT systems are working continuously, these devices generate massive amounts of data. It becomes tough to extract relevant evidence from an enormous volume of data. Besides that, IoT data may store in distributed locations and servers under the jurisdiction of several nations [99].
Nowadays, many working frameworks and stages offer coordinated support for encryption to improve customer trust. The cryptographic algorithm permits clients to encode the information or data to be transferred to the cloud and then decrypt it later to get back to their framework. The presence of simple cryptographic contraptions has prepared it and accommodated customers to ensure their data security. Accordingly, the degree of the end-to-end encrypted records has been extended [28]. The encrypted information is also available, which is not good enough “in a forensically sound manner” this means that first decrypt the file and change it to a readable format. Hence, more research is required to extract relevant information from encrypted data.
The absence of a standard forensic model for heterogeneous IoT devices
There are no standards defined for IoT environment and that will lead to challenges in the category of evidence collection from a distributed IoT environment. The traditional technique used for forensics like memory forensics, network device investigation, email header forensics, etc. is not sufficient with the varying nature of IoT devices. Therefore, attackers take benefit from heterogeneous IoT environments to steal crucial information. In terms of safety using the vulnerability of those devices, the evidence collected may not be acceptable in the courts of law. Despite that, another technical challenge related to the extraction of evidence from IoT devices is that every manufacturer accepts different hardware and different operating systems for their device [85]. Now at present, the complexity of hardware and communication protocols of IoT devices can be equally varied, be it ZigBee, Wi-Fi, Bluetooth, etc. [6], and this type of communication medium is the basic requirement for transmission of data in IoT devices. However, outer state crime requires collaboration between investigation agencies of the different countries to reduce cyber-related crime. In general, the higher-ranking research organization may work together and introduce some standards for IoT devices because smart devices have a rich source of information [25].
Lack of trained people and less knowledge
The process to pick evidence together must start legally, implying that the authorities must give a written order to create the investigation. Still, conventionally people are not aware of the required way of data collection. As suggested by Rana et al. [112], law enforcement departments should conduct workshops and training programs for the people and the employees of their organization to teach them how to get digital evidence in a forensics way. The investigating officers often unplug or shut down the system directly, without first creating the basic forensic image. It shows that the evidence extraction from IoT devices is one of the most challenging steps because of no coordination between experts and law enforcement agencies [24].
Privacy policy for accessing personal data
In the IoT environment, different devices collect users’ data like behavioral data, chats, biological information, financial account data, passwords, etc. On account of a cybercrime investigation, this information will be utilized by a forensic professional. When an incident occurs, the investigators can collect the data from these devices without guaranteeing the owner’s privacy through the investigation lifecycle [98]. Consequently, clients must know that their information is being utilized for a legal examination. Users must be utterly mindful of who got to their information and used it for inspection. Besides that, the investigators who access user data must guarantee the security of data from unauthorized access misfortune and manipulation. However, the significant features require privacy improvement technologies with advanced methods to protect the confidentiality and security of IoT, RFID-based device data [147].
Evidence preservation
Evidence obtained during computer forensics has traditionally been more prevalent but now, as technology increases, several IoT devices are also involved in the investigation process. These devices contain enormous data with less security and high complexity as because of less storage capacity and low computational power IoT devices use the web and mobile applications for cloud storage. It is more challenging to preserve artifacts from the compromised machine and guarantee its integrity. Every law enforcement agency needs a chain of custody, when and where the incident occurred, with information about how essential evidence was collected, protected, examined, and presented. Furthermore, it ensures that data retrieved from the evidence has not been altered throughout the entire process of a forensics investigation [86]. There are three steps to preserve the digital evidence shown in Fig. 12 directed during the transfer of media.
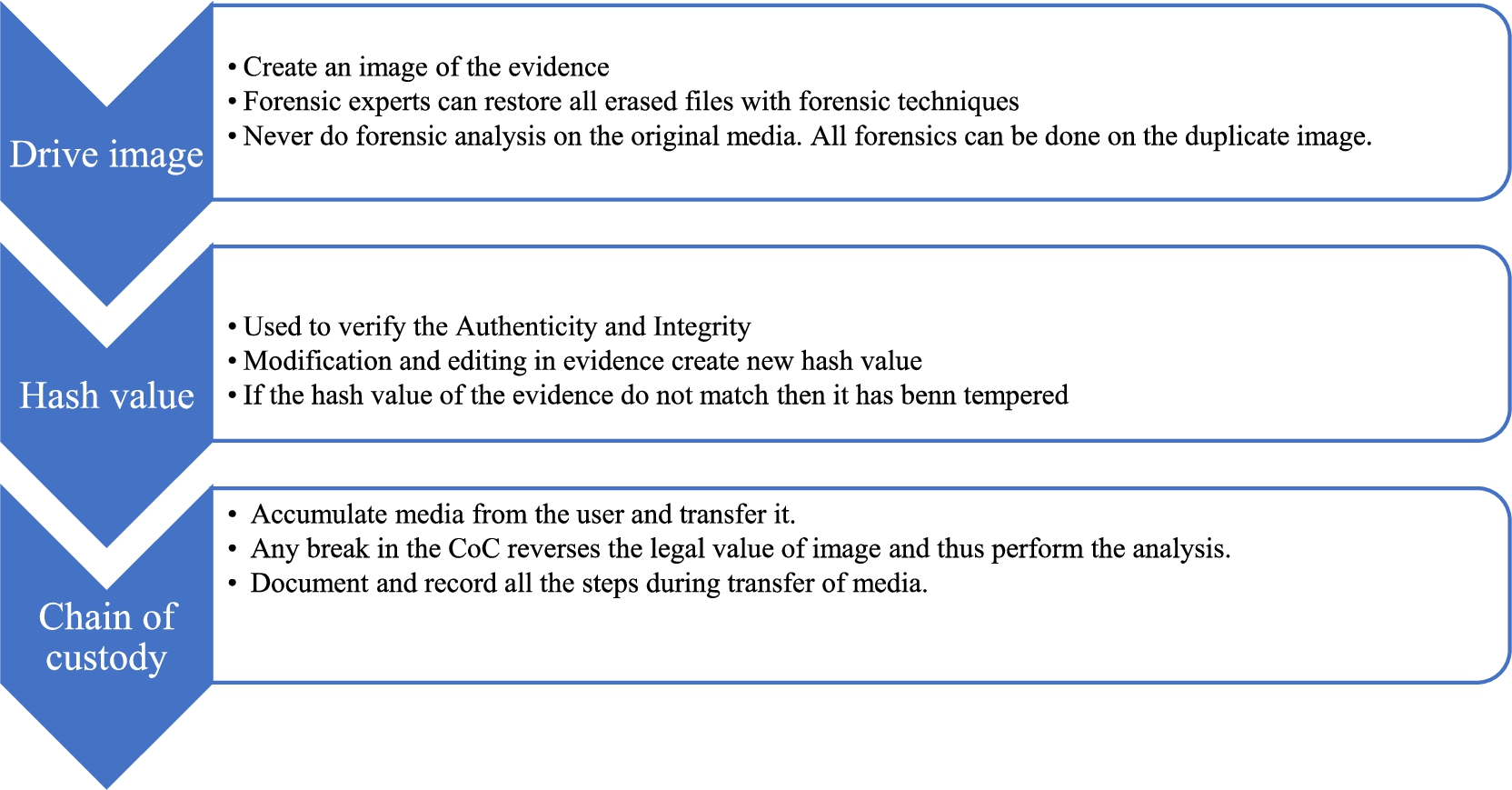
Methods for the preservation of digital evidence.
The fast development of IoT gadgets and the exponential increment in information produced by these gadgets make a genuine need to determine and deal with the created data. Accordingly, IoT devices have a large amount of data, so it is essential to develop practical analytical methods to examine the data. It will assist the specialists in extracting significant proof and settling on the necessary choices rapidly and successfully. As we know, most IoT devices work continuously and produce a large volume of data, and it is very challenging to analyze encrypted data.
Usually, digital forensics examination of IoT systems is uncertain about where data came from, who stored it/modified it/or created the data object. To know about all the details of data origin could be clarified, depending upon the data model [105]. Experts reviewed present and future lawful worries that are corresponding to IoT security and legal sciences [87]. One of the central matters alludes to the clashing lawful direction if a transnational crime should arise, with the nonappearance of transparent procedural and authoritative contracts. Although tempered evidence also keeps extensive information even if that information can be separated into various parts and due to which such evidence has to go through many legal procedures. Digital forensics is a necessary part of cybercrime investigation. In some cases, a tiny bit of evidence is distributed among several locations which creates a challenge for the investigator. After studying the evidence examination phase of various researches, now we concluded that an efficient testing technique is needed which classifies data and segregates irrelevant information from the evidence. Figure 13 gives the best illustration for evidence examination and testing.
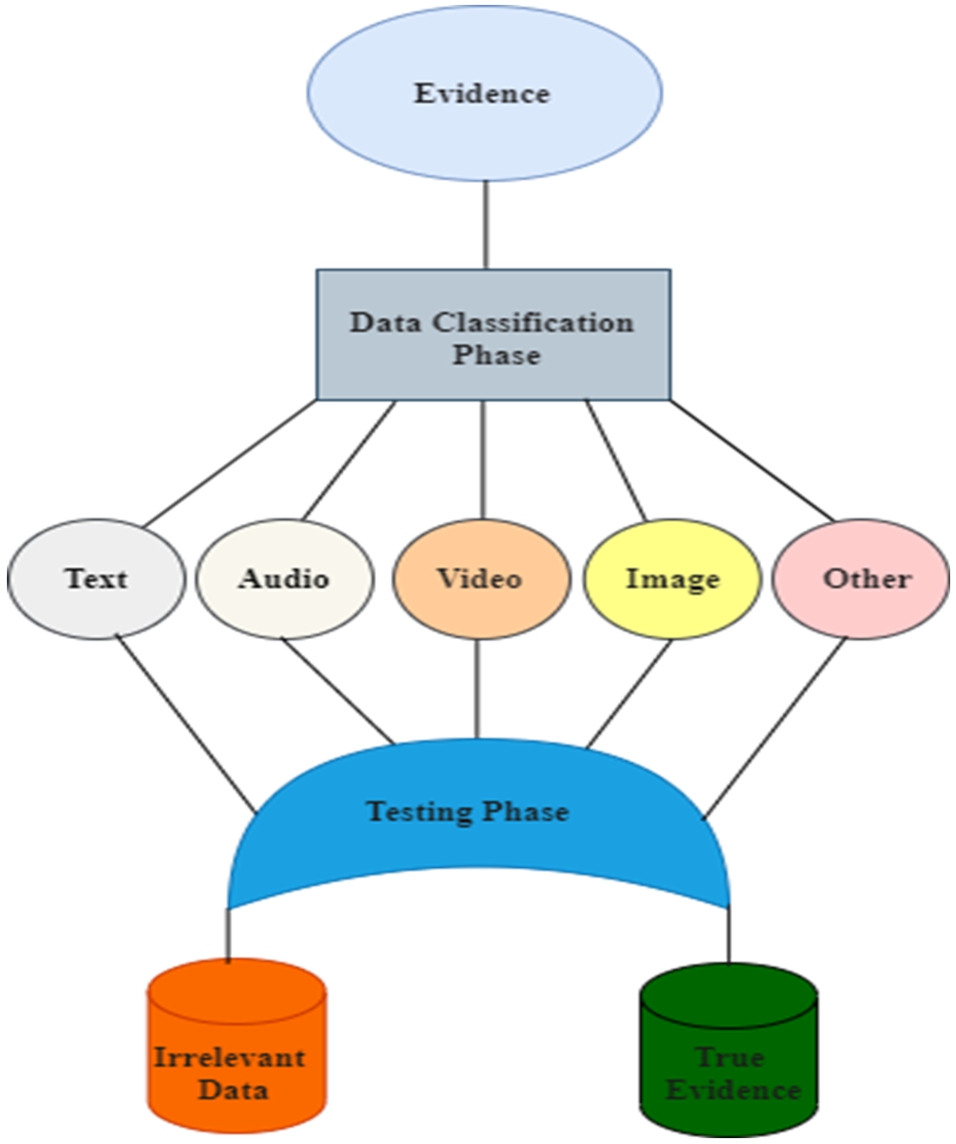
Evidence examination and testing.
The presentation of facts and their reporting depends upon the authority who investigates the case and the respective jury where the investigator presents the report. IoT-based evidence is a new challenge that requires sound technical understanding and knowledge of the individual Information technology laws of a country. It would be an arduous task to elaborate the minor findings of such a specialized case with complex architecture in a short time [151,152] Different IoT devices have various parameters for sensing the environment like temperature, movements, activities, etc. so it is more challenging to observe the data because every piece of information is stored in a different file format. Sometimes information gathering and progression using other analytic functions may convert the meaning of the data and modify its structure [36,87] To resolve the evidence investigation issues and legal challenges, an efficient technique is required for the digital forensics of IoT devices that classifies the evidence according to the need of the investigators. Our study elaborates the evidence investigation procedure and legal challenges as shown in Fig. 14.
Challenges in the investigation process of IoT forensics.
There have been numerous researchers presented different forensics techniques for IoT device like memory acquisition, cloud based data extraction etc. and several issues related to digital forensic of IoT device. In this, a complex hardware architecture with less computation power, storage dependency leads to insecure data, and heterogeneity of IoT devices is to be discussed with some solutions. Table 9 summarizes forensic techniques and open issues in detail.
Conclusion and recommendations
The Internet-connected devices are being incorporated nearly in all the areas of human life ranging from medical care, home automation, education, industry, to business and so forth resulting in billions and billions of such devices. The smart devices store their data on the cloud and share the same with one another. The interactive nature of IoT devices enables human beings to communicate with things that use various communication mediums such as Wi-Fi, Bluetooth, near-field communication (NFC), etc. The omnipresence of IoT has become an attractive target for attackers, due to the massive number of smart devices and the continuous flow of data. IoT devices are susceptible to cyberattacks, due to their reliance on the internet for communication. This survey aimed to explore recent studies on IoT forensics and their open challenges. Here we have investigated the state of art literature available on IoT forensics by analyzing their strengths and weaknesses. Security and forensics of IoT devices were discussed by classifying the literature at three levels. The study discusses the relationship between IoT forensics and IoT security, requirements, and challenges by analyzing the source of evidence at different levels. The need of forensics in different areas of IoT applications and the type of devices with potential forensic evidence have been evaluated. We also enumerate several tools and techniques for evidence extraction, investigation process for IoT forensics, and legal challenges.
Furthermore, the study highlights open research issues and solutions related to IoT forensics. The work concludes that forensic solutions need to be integrated into current IoT devices to ensure that they can be investigated in the case of an incident.
Forensic technique and open issues
(Continued)
In future, there is need for more in-depth research of IoT devices at physical layer, such as chip-off procedures used in mobile devices. More research is required on the most prevalent home security systems, smart assistants and smart firewalls, etc. Selective evidence collection from huge amount of IoT data may improve the speed of investigation. The process of forensics cannot be fully automated. However, a semi-automated approach to the investigation’s analysis phase might be beneficial. In IoT forensics, the application of machine learning techniques, such as the correlation of logs and meta-data analysis, is gaining importance. We will also work on proposing a framework for a multipurpose digital investigation model used to extract artifacts from IoT devices in the future.
Ethical approval
Not applicable.
Conflict of interest
The authors have no conflict of interest to report.
Author contributions
Pankaj Sharma wrote the manuscript and designed the framework and methodology. Lalit Kumar Awasthi validated the manuscript and gave suggestions. Both authors reviewed and approved the final manuscript.
Funding
None to report.
Availability of data and materials
Not applicable.
