Abstract
Firewalls are an important tool in the assurance of network security. Packet filtering firewalls are configured by providing a set of rules that identify how to handle individual data packets that arrive at the firewall. In large firewall configurations, conflicts may arise between these rules. Argumentation provides a way of handling conflicts such that their origin is illuminated, and hence can help a system administrator understand the effects of a given configuration. To show how argumentation might help in this domain we examine the use of a system of metalevel argumentation for firewall configuration, showing how it makes conflicts and their origins clear, and showing how different instantiations of a metalevel argumentation system provide alternative ways to resolve conflicts.
Introduction
Assuring network security is a major problem today. It is a problem that is considered both in academic computer science, which aims to come up with new techniques for securing networks, and in the practical world of information technology, where system administrators struggle to prevent unauthorised users from breaking into the networks that they manage. Firewalls, first introduced in 1987 [25], are one of the core components of a network security implementation. A
As we will discuss below, firewall policies are set by specifying a set of rules, and there are a number of well-recognised problems in doing this. These problems relate to rules conflicting, having domains that overlap, and include redundancy (where the effect of a policy differs from that intended because some rules can never have any effect). Such
In this paper, we discuss how an argumentation-based framework can be used to analyse a firewall policy. In particular, we examine the use of the metalevel argumentation framework of [32], choosing this system as the basis of our investigation because we believe that the metalevel reasoning about the acceptability of arguments helps to make the reasons for conflict between policies especially clear, and makes it easy to understand how different strategies for resolving such conflicts work.
The remainder of this paper is organised as follows. Section 2 provides a brief introduction to firewalls and issues in their configuration. Section 3 introduces the specific metalevel argumentation system that we employ. Section 4 describes several ways in which this metalevel system can be used to represent firewall configurations and potentially resolve conflicts in the firewall rules. Section 5 discusses related work. Then Section 6 concludes.
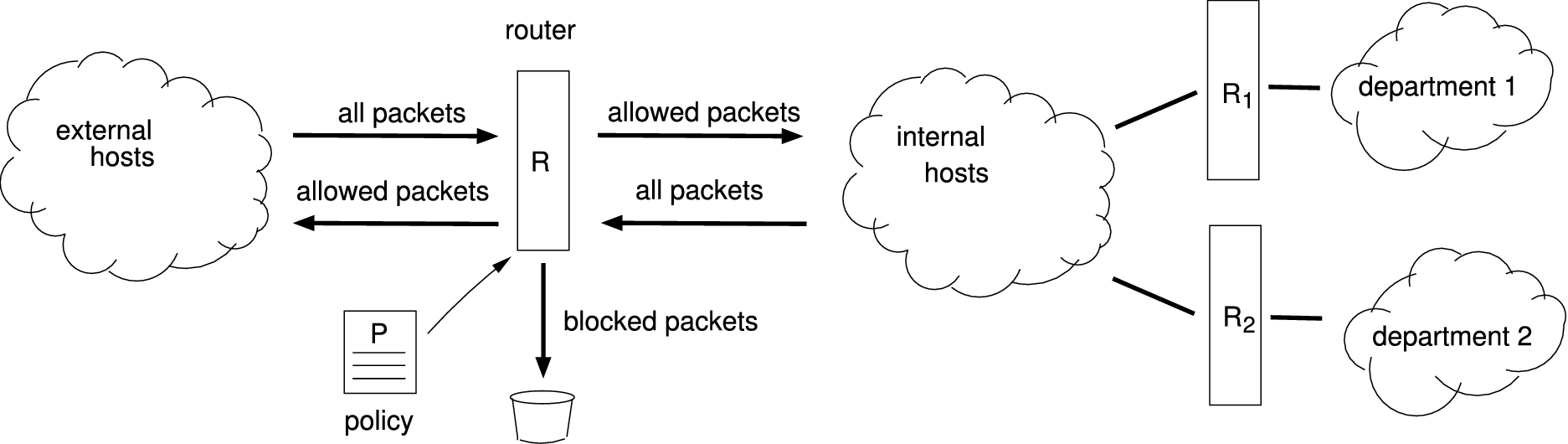
A packet-filtering firewall.
There are different types of firewall which function in different ways – packet-filtering firewalls, application/proxy firewalls, and network address translation. Packet-filtering firewalls operate at the network layer, not allowing packets to pass through the firewall unless they match the established policy rule set. Routers can provide a very common form of packet-filtering firewall. Packet-filtering usually makes decisions based on the following characteristics:
Source and/or destination IP1 Internet Protocol. Source and/or destination port numbers Protocol types Other parameters within the IP header
A network administrator configures the firewall based on the policy, for example blocking and allowing packets based on what protocol they match and which IP address they have as their destination. A schematic of a packet-filtering firewall is given in Fig. 1. Here the firewall is implemented by router
Application firewalls, as indicated by the name, work at the application layer. These devices act as proxy machines for requested services. Requests are sent to a proxy machine, which then makes those requests to the Internet on behalf of the local client. A proxy machine acts as a buffer between “bad” remote users and the internal network client machines. Network address translation (NAT) also operates at the network layer, providing the capability to change the source and/or destination IP address. This is common when a private address space is used internally. The simplest type of NAT provides a one-to-one relationship between inside and outside IP addresses. In this type of NAT, only the IP header related to the IP address needs to be changed. The rest of the packet can be left unchanged. In the remainder of this paper, we concentrate on packet-filtering firewalls, but we believe that the techniques developed here could be applied to the other types we have listed above.
Table 1 lists some possible polices for a packet-filtering firewall and how they could be implemented. In particular, each row of Table 1 presents a rule for a single packet. A set of such rules makes up a firewall configuration. The first column in Table 1 numbers the rule for reference. The second column states the policy that the rule is intended to implement. The third, fourth, fifth and sixth columns break the policy implemented by a rule into the action that the firewall can perform (block or allow the packet) and the data that is available about each packet (the protocol it relates to, the source IP address, and the port the packet arrives at). The final column shows how a given rule would be implemented in the Linux
Examples of firewall polices and corresponding filtering rules. Each row lists an example of what might be required of a firewall, the corresponding firewall settings, and the implementation of these settings using the Linux
If a firewall were to be implemented with this set of rules, when a packet comes in it would be checked against rule 1. If rule 1 applied to that packet, then the action specified by rule 1 would be taken. Otherwise, the packet would be compared to rule 2. This process is repeated until one of the rules correctly specifies the packet; the first rule that does is the one that’s applied, ignoring all rules after it. If no rule matches an incoming packet, some default rule (which might, for instance, be to let the packet pass since there is no specific rule to block it), would be applied. Imagine a packet arriving that uses TCP, coming from 55.55.55.55 on port 80. Rule 1 specifies blocking it, while rule 2 says to allow it. Since rule 1 is positioned before rule 2, the ultimate action is to block, but it is clear that there is some kind of a conflict occurring. As another example, a packet using UDP from 55.55.55.55 on port 53 would be blocked; while three of the rules say to block it, only the first one is actually “enforced”.
The situations highlighted in both of these examples could be considered problematic, and both are what [2] calls an Rule In shadowing, the two rules are in conflict on Rule In correlation, the rules conflict on Redundancy occurs in two cases. In the first case, redundancy occurs if two rules In the second case, redundancy occurs if all packets that satisfy In both cases of redundancy, the lower priority rule will never be applied. Rule In generalization there is shadowing but the conflict is resolved by the priority.
Now, in a small set of firewall rules such as these, it is easy enough to detect and fix anomalies. However, firewalls, especially in large organizations with many machines on a network, can include many hundreds of rules. In such a case, detection and correction of anomalies is much harder. The problem is even more complex when firewalls are composed of different components, each requiring some part of a policy that is applied to a whole organisation, and as we shall discuss below, one can easily imagine scenarios in which decisions about whether to accept or reject specific packets requires complex reasons that need to combine information from a group of autonomous individuals. See [13] for a similar scenario in the domain of B2B applications. It is the need to deal with these complicated cases that is the reason we are using argumentation. In the remainder of the paper, we will describe how this can be done. In particular, we will use the
The metalevel argumentation framework of [32] is constructed on top of the standard Dung framework [20]. The idea is to make the conditions under which arguments are classified – for example as justified, rejected and defeated – and the definition of extensions – such as grounded, preferred and stable – expressible in a logical language. The advantage of doing this is that it becomes possible not just to have arguments about objects in some domain, but arguments (meta-arguments) about the status of those arguments. In this section, we introduce enough of this material to apply it to our firewall scenario. The description is an abbreviation of the presentation [32] with some minor modifications and additions (though naturally any faults in the interpretation of the original are ours).
Argumentation
The formal structure, taken from [32] is as follows. As [32] points out, the formalization is based not on Dung’s classic presentation, but on the more recent labelling approach [15,16,45,48] (nicely summarised in [10]). The basic notion is that of a
In Dung’s approach, as in [32], arguments are taken to be completely abstract entities with no internal structure, and the attack relation We discuss a specific
Given a set of arguments and attacks between them, the core of Dung’s idea is that not all arguments are equal. It is possible to identify some arguments that we should consider
Defined in this way, there is no relationship between a labelling and the attack relation over a set of arguments. The two are combined through the idea of legality. For a labelling
Note that the
With the notion of legality tying labellings to attack relations, it is possible to recover Dung’s idea that
If
Based on extension membership, we can then define the
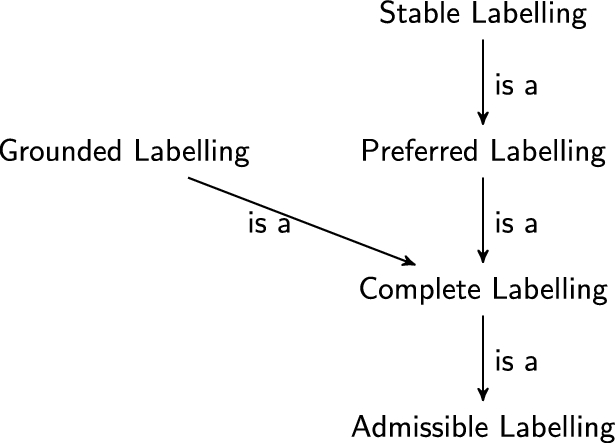
The relationship between labellings.
In [32], a This is a less general subset of the system presented in [32], but sufficient for our purposes. If If If If If
In other words, the language
We next need to define if if if
which together define the contents of
As presented so far, and as described in [32], this metalevel argumentation system, just like Dung’s system [20], has an abstract notion of an argument. The members of
Having introduced some of the issues in firewall configuration, and the metalevel argumentation approach of [32], in this section we discuss how the latter can be used to model some aspects of firewall configuration in order to illuminate anomalies and potentially provide a means to support system administrators in solving them.
Scenario
We consider a simple scenario in which an organization operates a hierarchical network of routers (see Fig. 1 again). The root node,
Currently this merging of policies would be done by hand. In the simplest case, this is done by just concatenating the firewall rules. It is not hard, though, to imagine the process being automated with the routers being under the control of software agents.
The model of structured argumentation that we use in the following examples is that of [28], which is a defeasible subset of
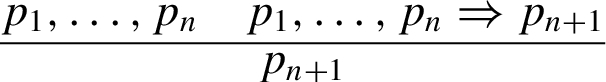
If
A simple metalevel model of a firewall
Now suppose that
In addition to the justification of
We can imagine that The form of attack here is a This is the weather example from [32, p. 19] without the preference argument.
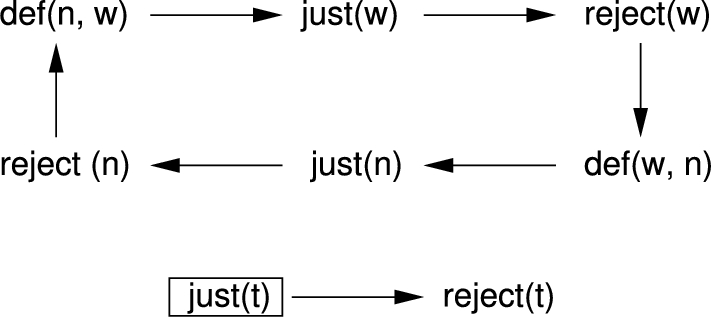
The metalevel argument graph for the basic firewall example. Each argument corresponds to an argument or an attack at the object level. A box is drawn around arguments that can legally be labelled
An understandable question to ask at this point is what the metalevel framework brings over a formulation of the problem using a standard Dung framework, or a structured argumentation system like
In a standard Dung framework, the output is a set of labellings, telling us which arguments are justified (
While the resolution of the conflicting policies achieved above is correct from the perspective of argumentation theory, it is not very satisfying from an application point of view – the resulting policy is unhelpful since it provides no decision on UDP traffic. A natural way to improve the situation is to express some kind of preference between web services and security (in our case) to resolve the conflict between
As discussed in [32], preferences can easily be introduced into a metalevel argumentation framework. If we follow the approach described in [32], we consider that stating a preference
The formal description of the metalevel system is that of the previous section, with the same set of arguments and attacks at the object level:
This section of the argument graph is now exactly the weather example from [32, p. 19].
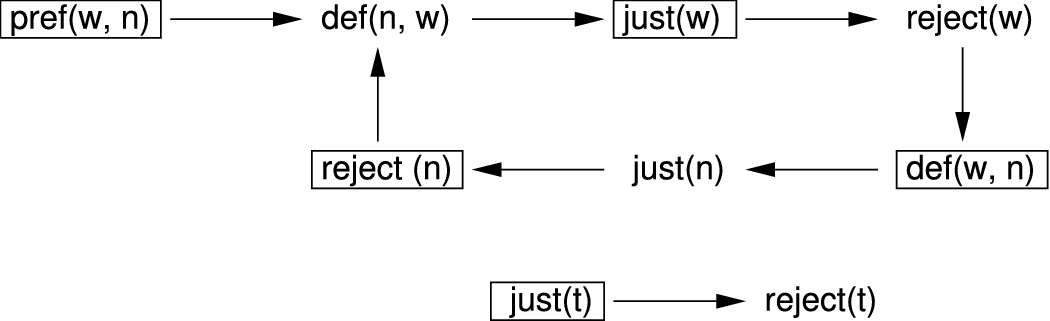
The metalevel argument graph for the firewall example with preferences. Each argument corresponds to an argument or an attack at the object level. A box is drawn around arguments that can legally be labelled
Again, we believe that this metalevel structure provides a means to explain the outcome to the administrator. Comparing Fig. 4 and Fig. 3, it is clear that the preference for
Metalevel argumentation can capture more than just the application of preferences. In this section, we briefly consider how we can use the same metalevel argumentation framework to apply ideas from value-based argumentation [12] to capture a situation in which different parties have different views about which policy to adopt.
In a This is, of course, a fictional university and bears no ressemblance to any institution at which any of the authors work or may have worked.
Let
We can formulate this as a value-based argumentation framework in the language of metalevel argumentation as (following [32]):
As noted above, the idea of using preferences to resolve conflicting arguments is not new, and the same is true of values. The new aspect that the metalevel approach brings is the ability to clearly see what the preferences and values are doing, that is
However, the models that we have discussed so far do not fully exploit the power of the metalevel framework. The astute reader will have spotted that though we have described how structured arguments can be used at the object level to connect firewall rules to arguments – as in the argument labelled (1) for example – we have yet to explore the construction of arguments at the metalevel. Allowing reasoning at this level allows us to construct arbitrary arguments at the metalevel that can resolve conflicts at the object level.
Consider, as an example, this variation on the use of preferences, where
From this information, it is clear that
One kind of reasoning that one might perform at this level that is of particular interest to us is reasoning about trust.
Discussion
The examples in the previous section have demonstrated how metalevel argumentation can be used to represent firewall policies in such a way that a conflict in the rules is exposed at the metalevel. They have further shown how metalevel argumentation can capture the way that existing approaches, such as preference-based and value-based reasoning, can be used to resolve such conflicts. The key advantage that we see to using metalevel argumentation is that conflicts and their resolution are exposed at the metalevel, rather than being buried in the computation of justified arguments. The metalevel approach does not provide any reasoning that is not provided by existing approaches, but by handling arguments at the metalevel as objects that can be themselves the subject of arguments, reasoning about those arguments, and the conflicts between them, becomes explicit. In firewall configuration, the final decision about how to set the firewall up is going to be taken by a human system administrator – someone who is probably not an expert in argumentation – and our hypothesis is that any additional clarity will make their job much easier. We already have some evidence that providing arguments for and against decision options helps users to become more confident in their decisions [43], albeit in the domain of intelligence analysis rather than firewall configuration. More recent work [1], provides some support for the use of argumentation in maintaining secure services. In particular, this latter work showed that using argumentation to support the definition of firewall policies provided more complete and correct policies at the cost of some additional effort. However, we do not yet have any empirical evidence concerning the use of metalevel argumentation in handling firewall policies.
We also note that we started by discussing four kinds of anomaly in firewall rules – shadowing, correlation, redundancy and generalization. Our examples are all instances of shadowing. Before we can claim that metalevel argumentation can, in general, help with detecting and resolving firewall anomalies we must first also demonstrate that the approach can deal with the other forms of anomaly.
Finally, we point out a further extension of the approach we have been detailing in this paper. In [35], we identified a number of argumentation schemes for reasoning about trust. In particular, we identified two broad classes of scheme: schemes for deriving trust and schemes for propagating trust. The schemes for deriving trust are exemplified by the scheme for direct experience: if
These trust schemes and the relevant critical questions could be implemented in the same metalevel argumentation framework that we have been discussing. At the object level we encode the schemes as defeasible rules that allow the relevant arguments to be constructed, for example capturing transitivity with the rule:
Now, one important difference between the example above, and that in Section 4.5, is that in the latter example, reasoning about trust was at the metalevel, and in our example here it is at the object level. There need be no conflict between the two approaches. As [51] points out, it is possible to have many levels of metalevel reasoning. We can easily construct a system in which arguments about policy happen at level 0, then level 1 contains rules, facts and arguments making inferences about trust, just as in Section 4.5. These level 1 arguments treat arguments at level 0 as object level arguments. Level 2 then contains fact rules and arguments about the applicability of arguments about trust (capturing critical questions about the schemes that generated level 1 arguments), and treating level 1 arguments as object level elements to be manipulated.
Related work
Given the importance of security, the central role that firewalls play in ensuring security, and the complexity of configuring firewalls, there has been considerable work on approaches to support firewall configuration. [2] implemented a set of algorithms in “Firewall Policy Advisor”, a user-friendly tool. These algorithms use a firewall policy tree to deal with centralized and distributed firewalls [3]. [52] introduced
Similar work has been carried out based on the use of formal logic. [22] proposed a formal logic for reasoning about the meaning of the firewall rules. Logic may be used to prove properties of a rule set and to detect a number of anomalies within a rule set. [23,24] used ordered binary decision diagrams (BDD’s) to represent rule sets as a boolean expressions, again proving a means to analyze the rule sets. However, the system does not allow the definition of rules using a logic programming syntax. In contrast, [21] presented a tool based on constraint logic programming (CLP) for analyzing firewall rules. This tool was implemented using Eclipse CLP, which makes it easy to express and extend the knowledge base of the system. [11] used a related approach, modelling firewall policies using a spatio-temporal logic that makes it possible to use model checking to find anomalies.
Argumentation-based firewall configuration has been studied by several authors. [8] described a technique based on Argumentation for Logic Programming with Priorities, allowing administrators to use high-level abstractions in specifying their network security requirements. In [9], this work was extended to automatically generate firewall policies from higher-level requirements; and in previous work, we [6,42] have discussed how to use argumentation to handle firewall anomalies and, more generally, to address cyber-security. [41] applied Defeasible Logic Programming (DeLP) for validation and reconfiguration of a firewall, while [14] used and argument-based logic programming engine to enforce security requirements dynamically. Similarly, [29] showed how to analyze security systems using abstract argumentation framework.
More work associated with firewall configuration has been published that goes beyind the use of logic. [19] developed models for policy conflict analysis, taking into account semantic information about policy specifications. [53] proposed a policy algebra framework for security policy enforcement in hybrid firewalls, making use of the basic algebra used in rule sets, such as addition, conjunction, subtraction and summation. [30] presented a firewall analysis engine named Fang, based on a combination of a graph algorithms and a rule-base simulator.
Our use of metalevel argumentation sets our work apart from all of the work cited. All approaches to reasoning about firewall rules yet published have concentrated on object level reasoning. Our work is the first we are aware of to look at reasoning about firewall rules at the metalevel. Indeed, there is very little that has been written on metalevel argumentation. As already mentioned, metalevel argumentation was formally introduced in [32], and the idea of metalevel argumentation has been used [31] to provide an abstract integration of accrual and dialectical argumentation and to integrate argumentation-based reasoning about preferences with the object level arguments. [44] presented an argumentation-based model of social interaction integrating both object-level and metalevel argumentation, and, as already mentioned, [34] integrated structured argumentation and metalevel argumentation to express argumentation schemes. Both these latter papers are a close fit with what we discuss here, though neither addresses our firewall domain.
Finally, where our work touches on the idea of bringing in reasoning about trust at the metalevel, we are clearly beginning to overlap with the work of Villata et al. [46,47] who have written quite extensively about how to represent and resolve arguments that attack arguments about the trustworthiness of agents. If this kind of reasoning were to be incorporated into our framework, it would require a second level of metareasoning – the first metalevel would be used to make statements about the trustworthiness of arguments and the effect of such statements on object-level defeats, and the second metalevel would make statements attacking these statements of trustworthiness. Resolving arguments at the second level would then inform which statements hold at the first level, and hence what arguments were preferred at the object level.
Conclusions
This paper has discussed the application of metalevel argumentation to the problem of modelling firewall configurations. In particular, we have shown how to use the metalevel argumentation system of [32] such that object level arguments are concerned with which packets to accept and block in a firewall, and the metalevel arguments identify – and potentially resolve – conflicts between these object level arguments due to shadowing anomalies in the firewall rules. We have argued that since a human system administrator will ultimately have to set the firewall policy, the use of a metalevel formalism – which makes explicit the (metalevel) arguments that explain
Footnotes
Acknowledgements
Research was partially funded by the National Science Foundation, under grant CNS 1117761 and Army Research Laboratory and Cooperative Agreement Number W911NF-09-2-0053. The views and conclusions contained in this document are those of the authors and should not be interpreted as representing the official policies, either expressed or implied, of the Army Research Laboratory, the National Science Foundation, or the U.S. Government.
Thanks to Sanjay Modgil and the anonymous reviewers for their helpful comments on the paper.
